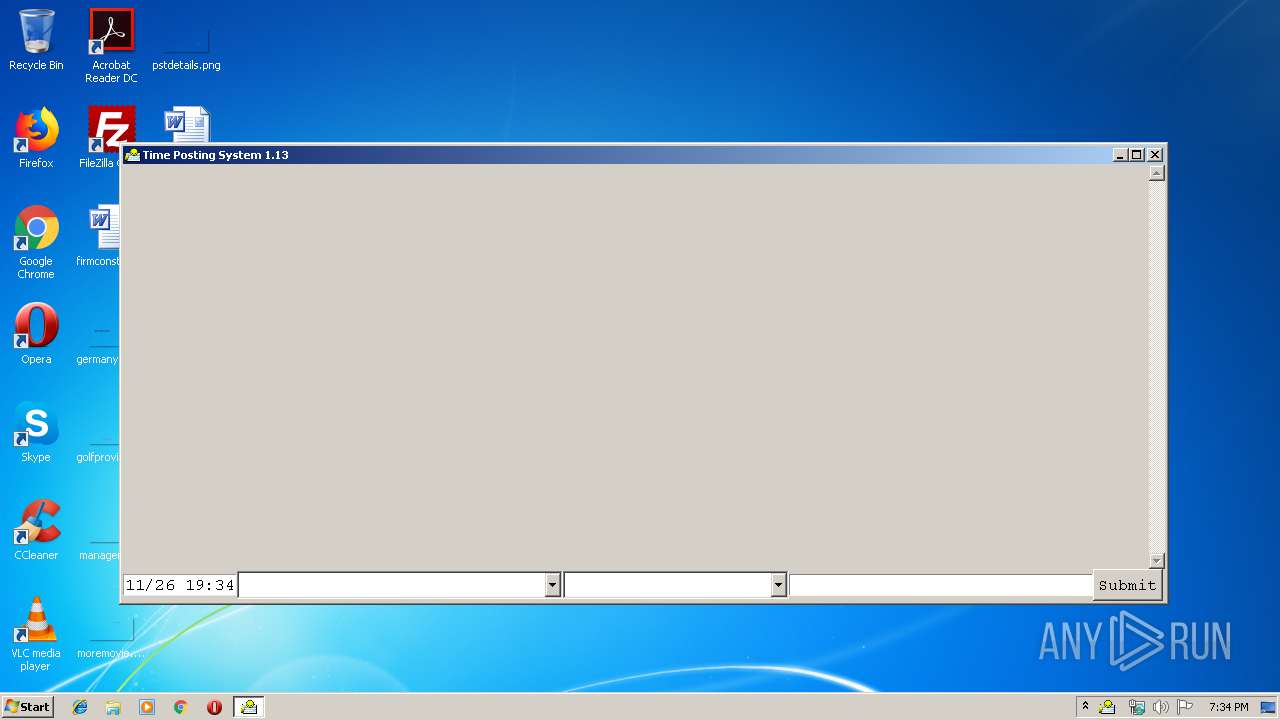
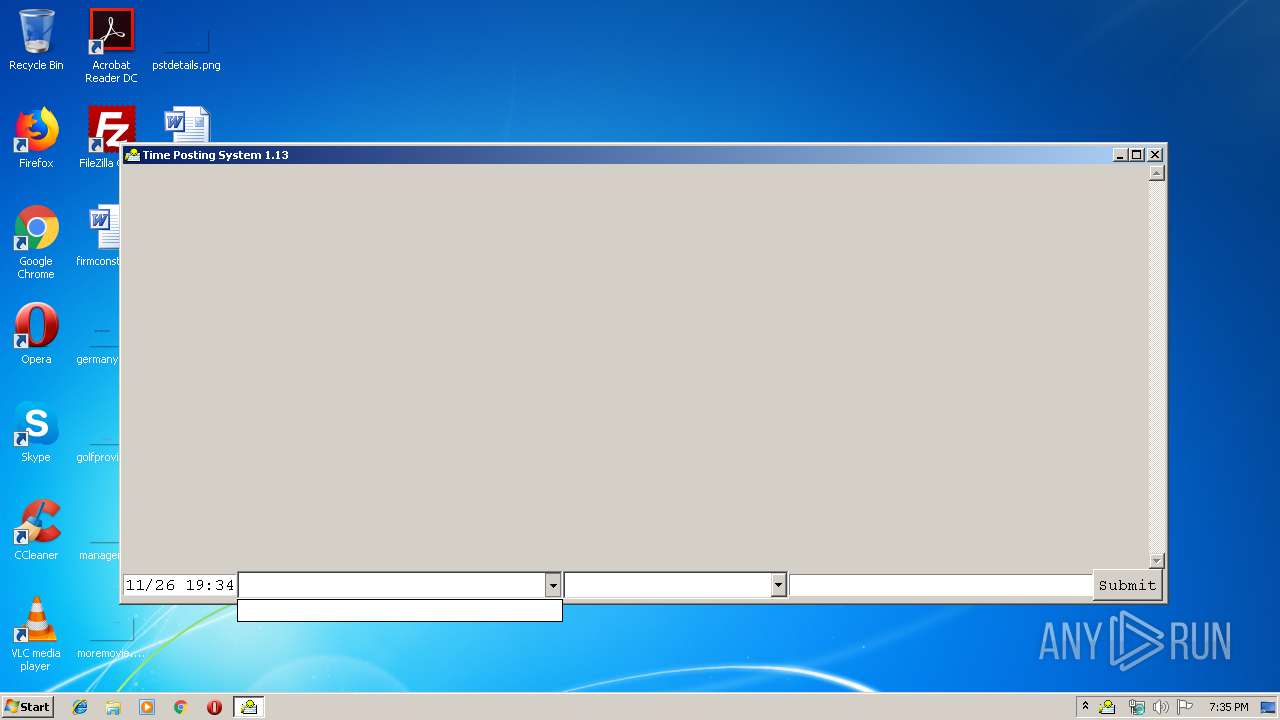
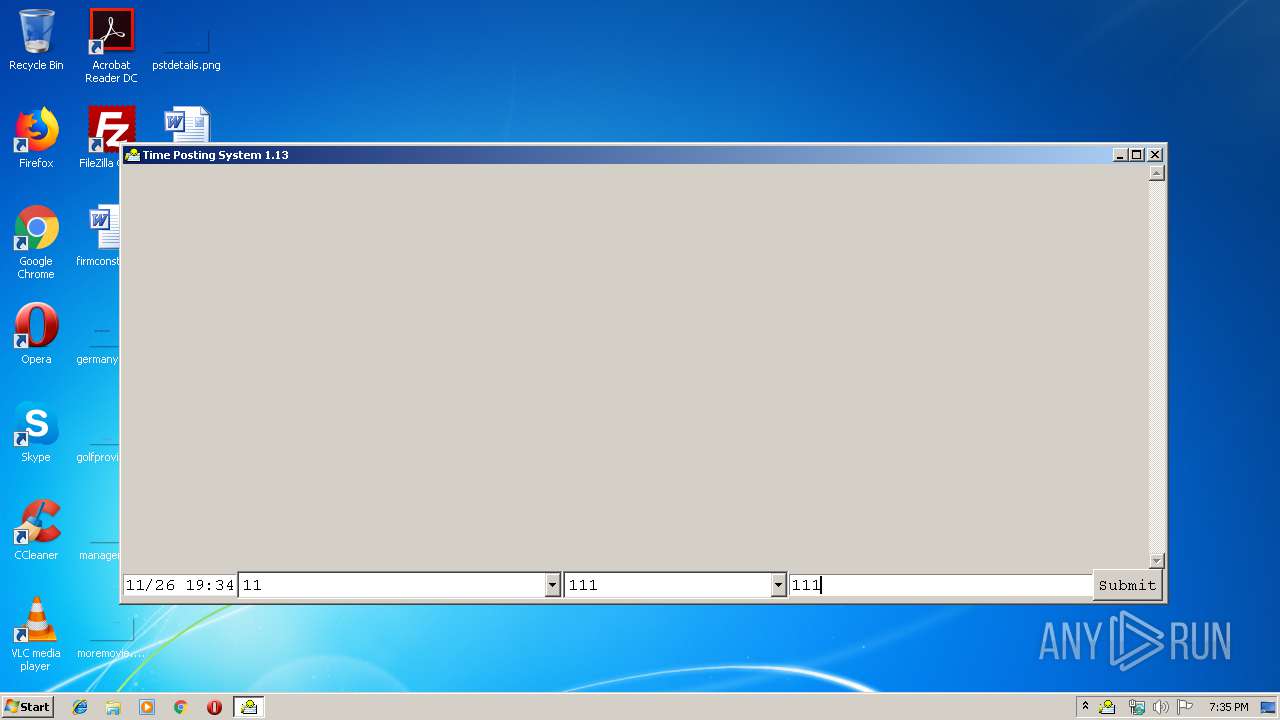
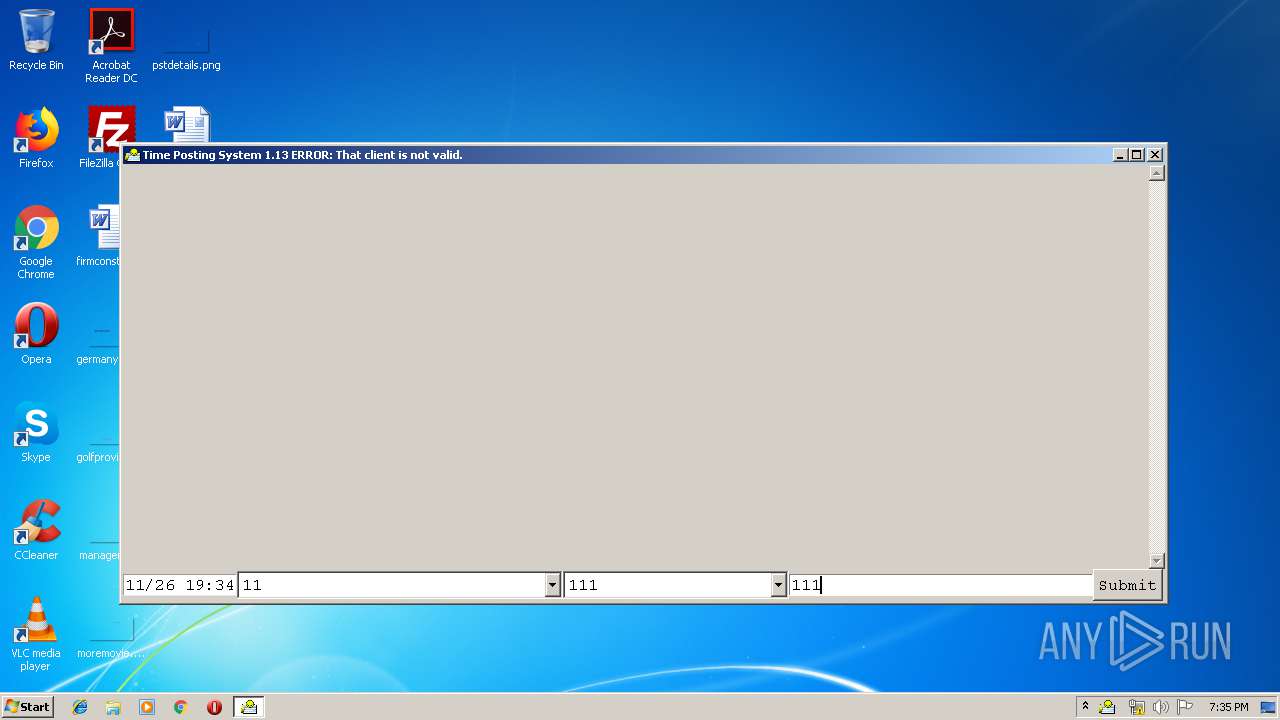
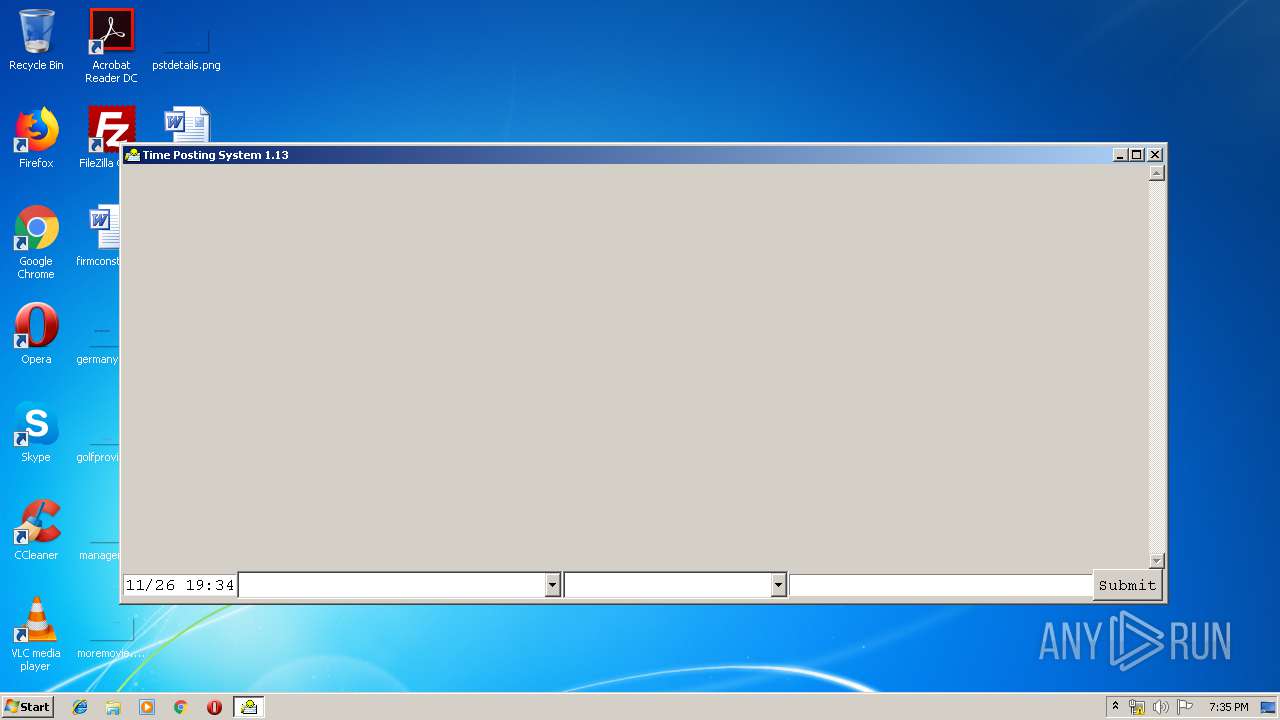
| File name: | tps.exe |
| Full analysis: | https://app.any.run/tasks/bbd275dc-f1e6-4267-8dea-bf2ba381e683 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2019, 19:34:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 19AEA29B513706A67989BE526FE28443 |
| SHA1: | D1FE89D881122F36853999D281790E87EDE8593D |
| SHA256: | 898DA6BF65F2651EEB8F769E3BA4295C80A822BB4E26F8C62A1825542DD59866 |
| SSDEEP: | 196608:OP1Q2jWptLDNIUJHaCNQ1uLi2Dm/gR0u3lq6zJMGB:4yNOcG2Dm/mrFzl |
MALICIOUS
Changes the autorun value in the registry
- tps.exe (PID: 1400)
Loads dropped or rewritten executable
- tps.exe (PID: 1400)
- tps.exe (PID: 3280)
SUSPICIOUS
Starts itself from another location
- tps.exe (PID: 1400)
Executable content was dropped or overwritten
- tps.exe (PID: 1400)
- tps.exe (PID: 3280)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.3) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.1) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:01:03 16:59:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 2266624 |
| InitializedDataSize: | 3161088 |
| UninitializedDataSize: | 37376 |
| EntryPoint: | 0x1284 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jan-2014 15:59:28 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 03-Jan-2014 15:59:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0022948C | 0x00229600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.14546 |
.data | 0x0022B000 | 0x0000EC5C | 0x0000EE00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.05898 |
.rdata | 0x0023A000 | 0x00057C00 | 0x00057C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.74262 |
.eh_fram\xcc\xe8\x04 | 0x00292000 | 0x0004E8CC | 0x0004EA00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.91837 |
.bss | 0x002E1000 | 0x000091F8 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.edata | 0x002EB000 | 0x00000096 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.84398 |
.idata | 0x002EC000 | 0x00004378 | 0x00004400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.55034 |
.CRT | 0x002F1000 | 0x00000018 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.114463 |
.tls | 0x002F2000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.231158 |
.rsrc | 0x002F3000 | 0x00009B68 | 0x00009C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.42284 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.34894 | 744 | UNKNOWN | English - United States | RT_ICON |
2 | 4.10929 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 5.4814 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 2.11093 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 1.57307 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.29164 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.17695 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.18099 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.15567 | 308 | UNKNOWN | English - United States | RT_CURSOR |
10 | 1.88729 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.dll |
IMM32.DLL |
KERNEL32.dll |
NETAPI32.DLL |
OLE32.dll |
OLEAUT32.DLL |
SHELL32.DLL |
Exports
Title | Ordinal | Address |
|---|---|---|
Dde_Init | 1 | 0x0012F988 |
Dde_SafeInit | 2 | 0x0012FA74 |
Registry_Init | 3 | 0x0012C9F4 |
Registry_Unload | 4 | 0x0012CA98 |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1400 | "C:\Users\admin\AppData\Local\Temp\tps.exe" | C:\Users\admin\AppData\Local\Temp\tps.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3280 | C:\Users\admin\tps\tps.exe | C:\Users\admin\tps\tps.exe | tps.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
36
Read events
11
Write events
25
Delete events
0
Modification events
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | FontName |
Value: Courier New | |||
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | Warn2Color |
Value: #edd1d7 | |||
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | AwayColor |
Value: #e1ecdd | |||
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | WidthClients |
Value: 30 | |||
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | Warn1Hours |
Value: 6 | |||
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | SummarizeInReverseOrder |
Value: 1 | |||
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | ShowZerosAsBlankInSummary |
Value: 1 | |||
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | WidthComments |
Value: 30 | |||
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | WidthCategories |
Value: 20 | |||
| (PID) Process: | (1400) tps.exe | Key: | HKEY_CURRENT_USER\Software\tps |
| Operation: | write | Name: | AwayIfSuspendedAfter |
Value: 30 | |||
Executable files
4
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3280 | tps.exe | C:\Users\admin\tps\tps.db-journal | — | |
MD5:— | SHA256:— | |||
| 1400 | tps.exe | C:\Users\admin\AppData\Local\Temp\TCL00000578\sqlite380.dll | executable | |
MD5:— | SHA256:— | |||
| 1400 | tps.exe | C:\Users\admin\tps\tps.exe | executable | |
MD5:— | SHA256:— | |||
| 1400 | tps.exe | C:\Users\admin\AppData\Local\Temp\1323849386-twapi.dll | executable | |
MD5:— | SHA256:— | |||
| 3280 | tps.exe | C:\Users\admin\AppData\Local\Temp\TCL00000cd0\sqlite380.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
intranet.wic.west.com |
| unknown |