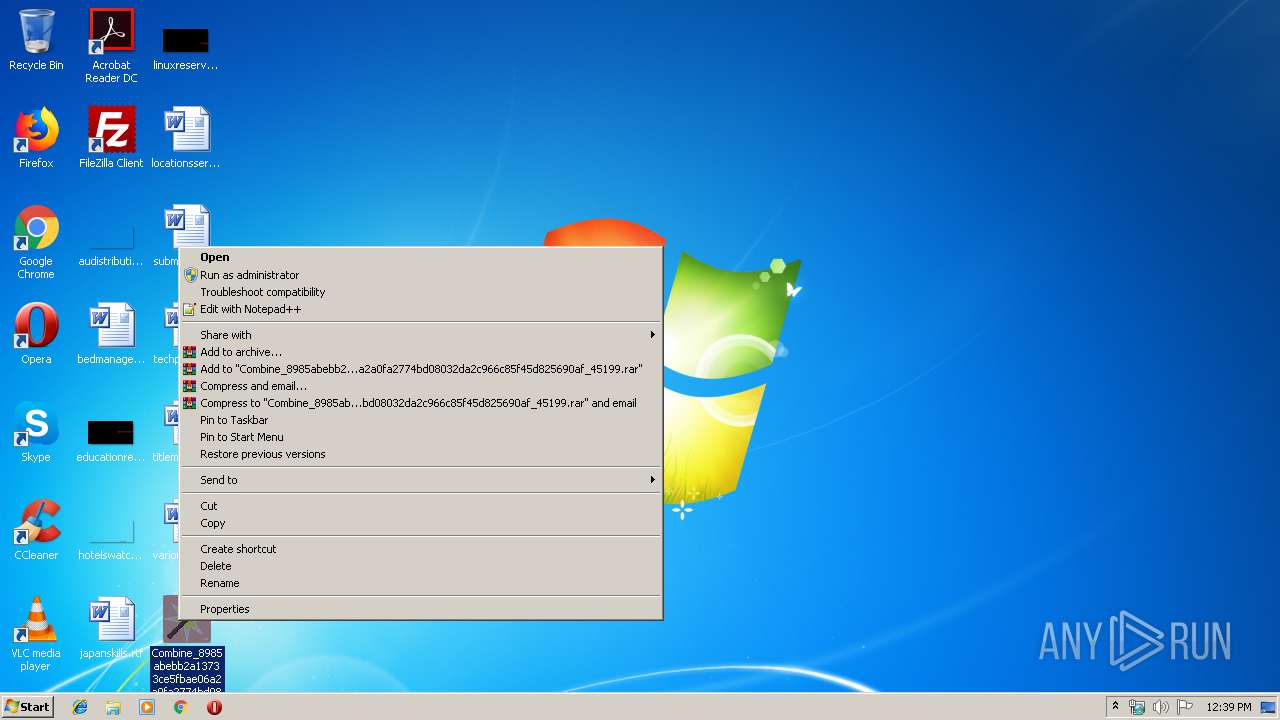
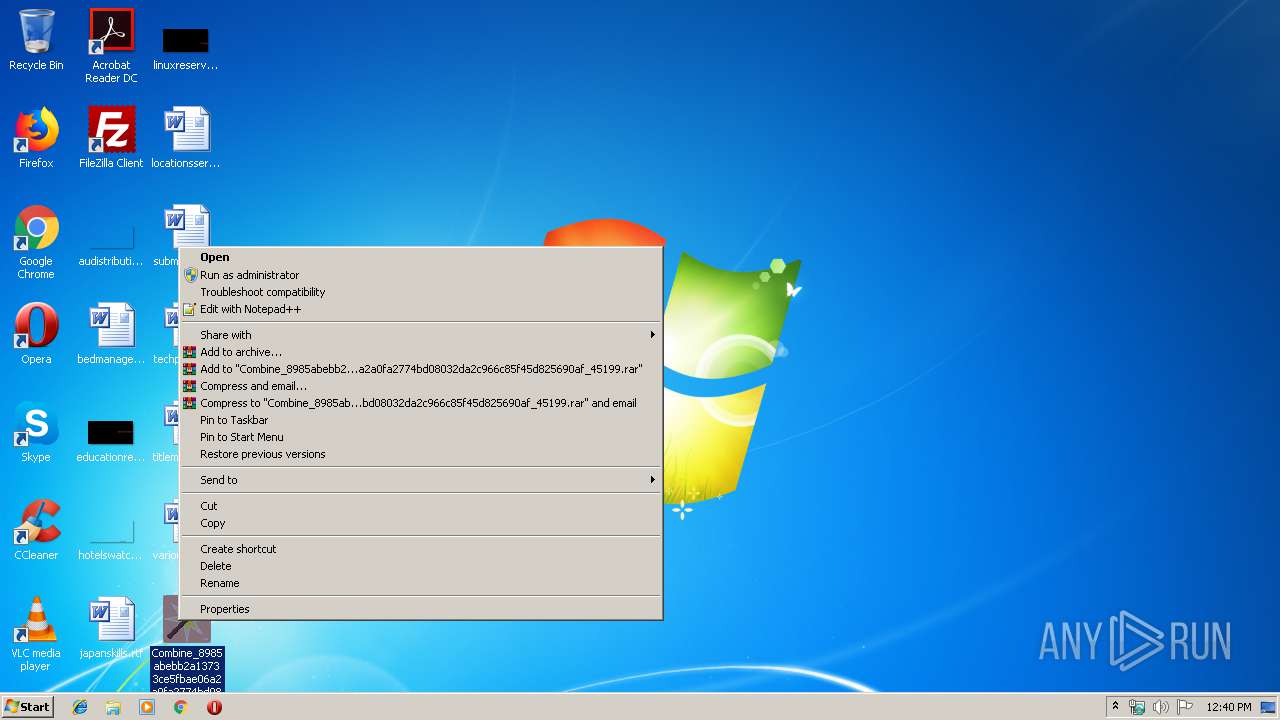
| File name: | Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe |
| Full analysis: | https://app.any.run/tasks/89f647dd-6b6e-42a3-b873-4453b97d09a2 |
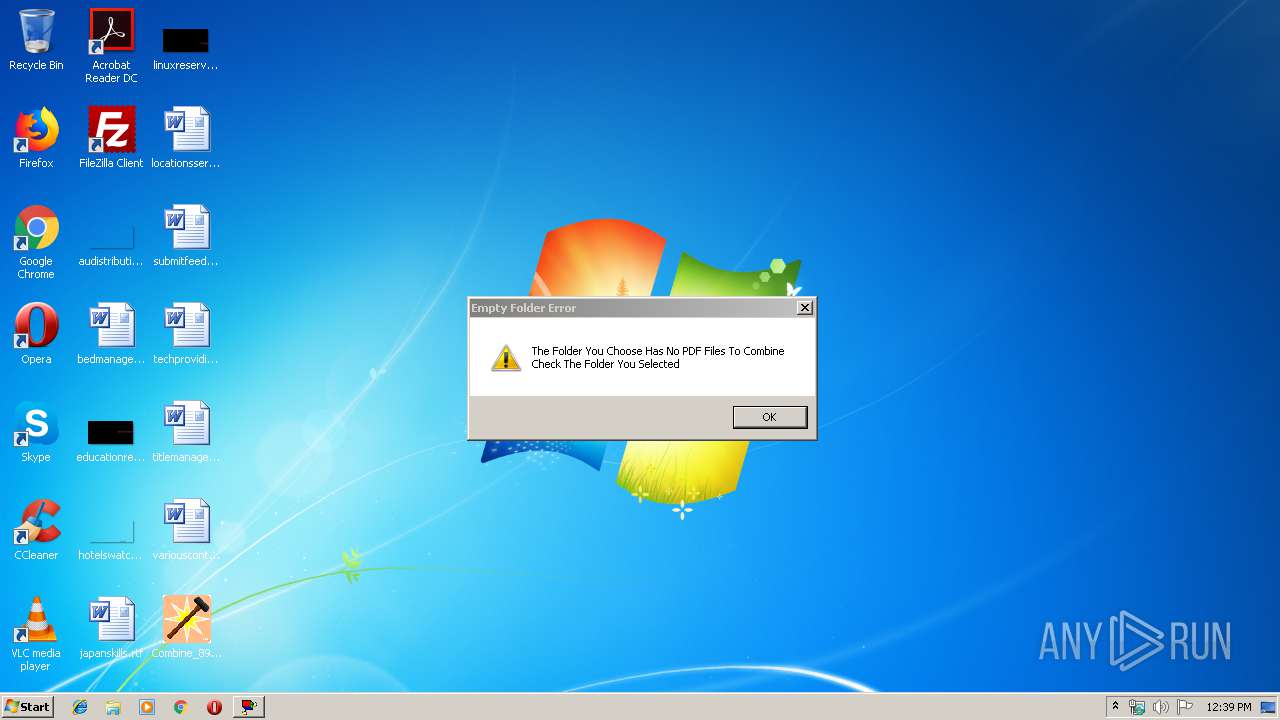
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 12:39:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FF209AA2F66B293764E73ACE6177329B |
| SHA1: | 49A1C8289DD9EE532E803A86D6BEFBE9F02E3C10 |
| SHA256: | 8985ABEBB2A13733CE5FBAE06A2A0FA2774BD08032DA2C966C85F45D825690AF |
| SSDEEP: | 3072:EliUPXC8k1nJrX+fNTBfOSki8vNqOIE2p3t:EzBkLL2NTBGbJvAOj2p9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes scripts
- cmd.exe (PID: 2620)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 3136)
- cmd.exe (PID: 2156)
- cmd.exe (PID: 2932)
- cmd.exe (PID: 1040)
- cmd.exe (PID: 3732)
- cmd.exe (PID: 2404)
- cmd.exe (PID: 3116)
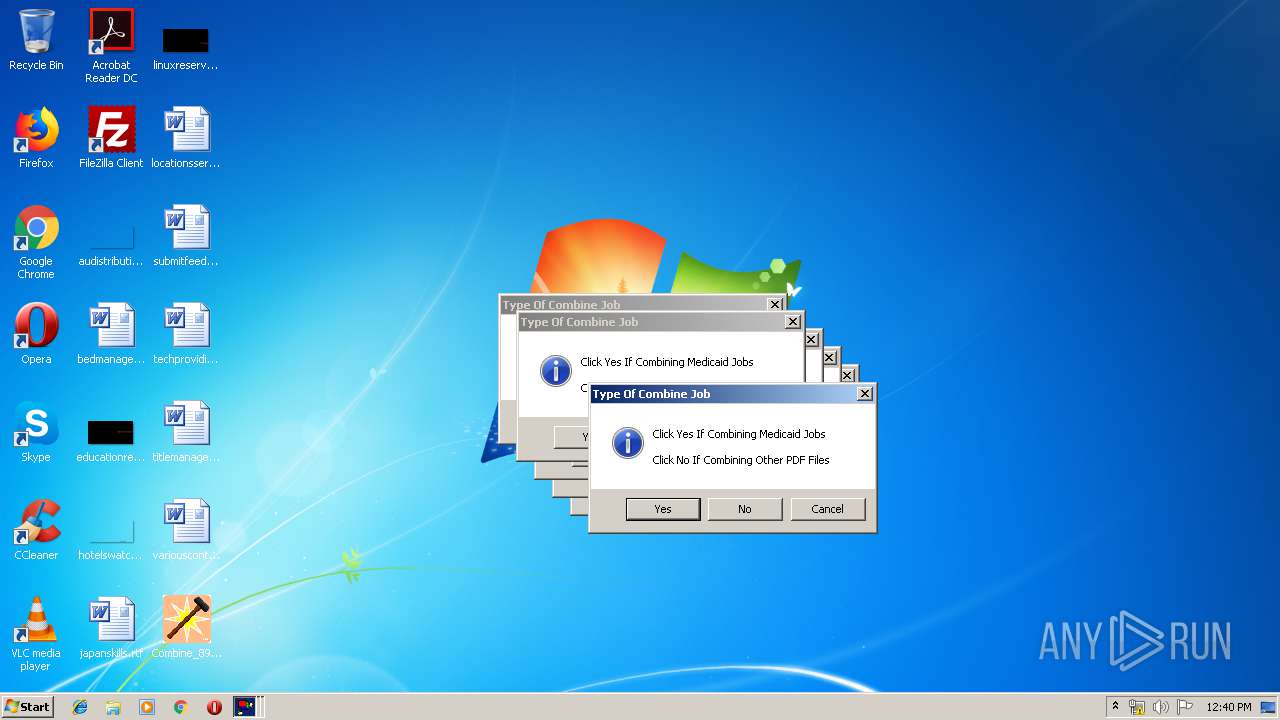
Application launched itself
- cmd.exe (PID: 2620)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 3724)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2620)
- Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe (PID: 3632)
- Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe (PID: 2488)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 3512)
- Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe (PID: 1308)
- cmd.exe (PID: 2236)
- Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe (PID: 3752)
- cmd.exe (PID: 2820)
- Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe (PID: 2968)
- Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe (PID: 2656)
- cmd.exe (PID: 3724)
- Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe (PID: 2256)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 1796)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2620)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 21:18:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 67584 |
| InitializedDataSize: | 82432 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 2 |
| ProductVersion: | 2 |
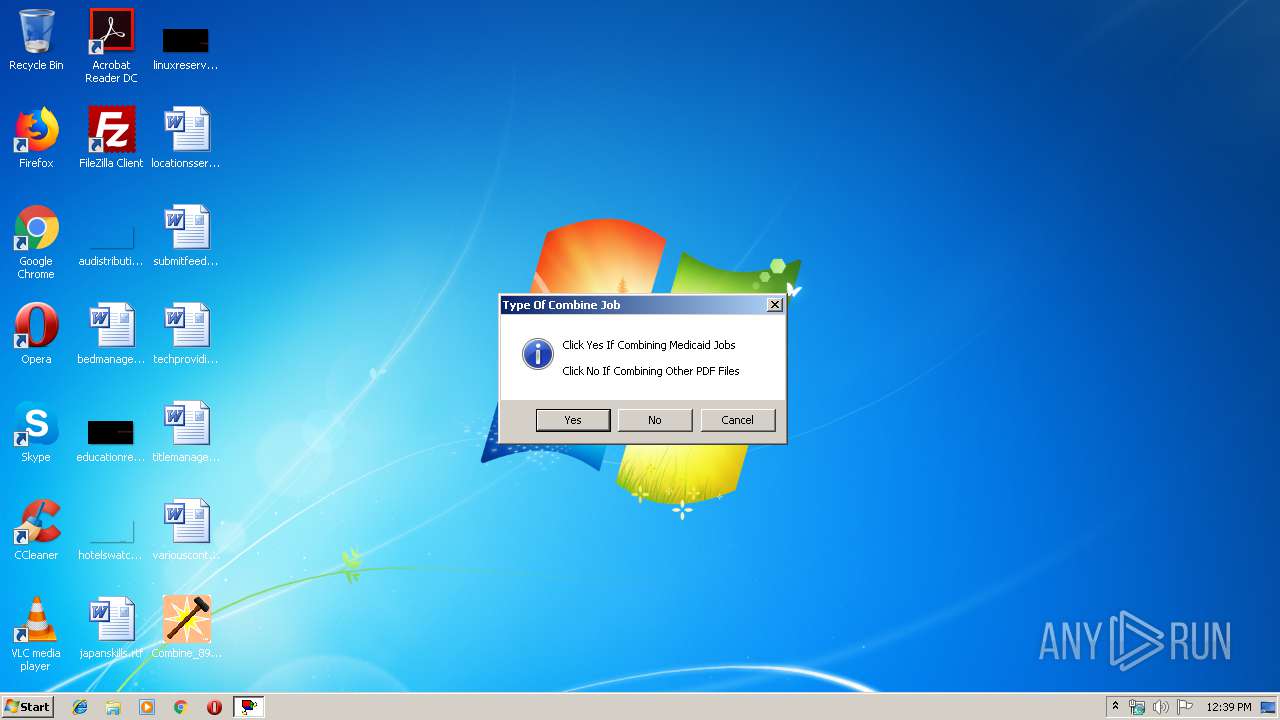
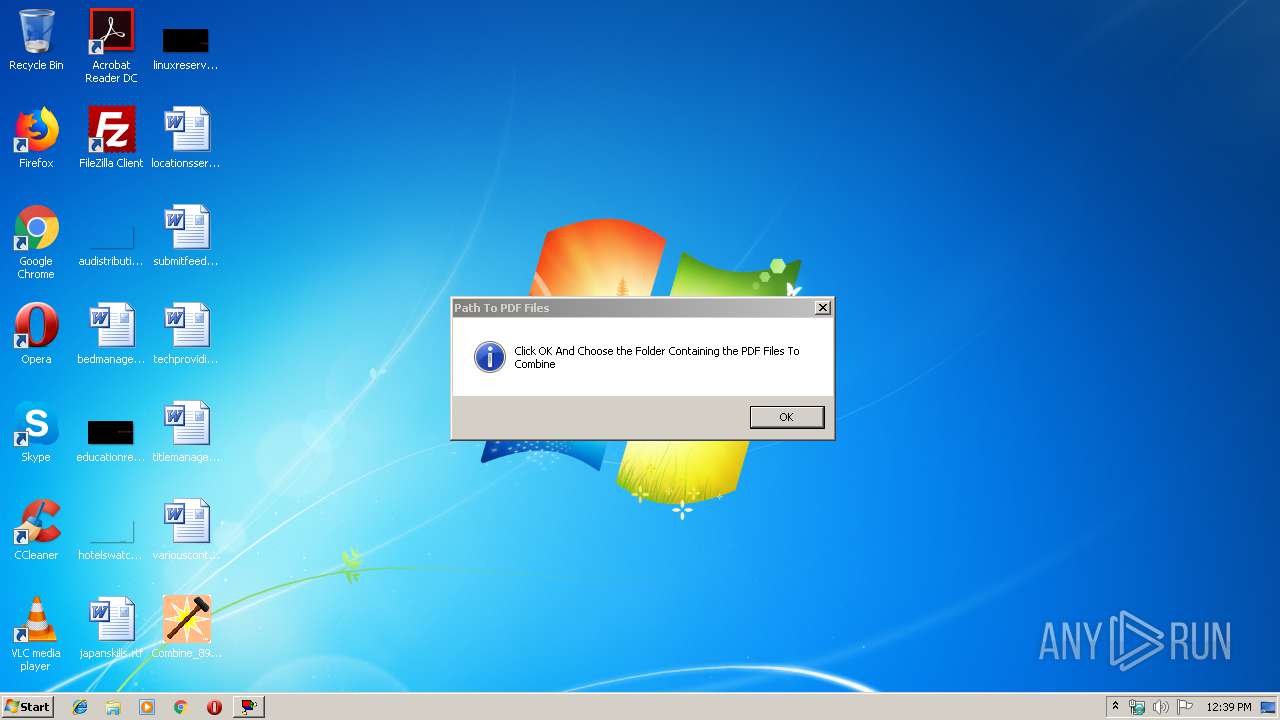
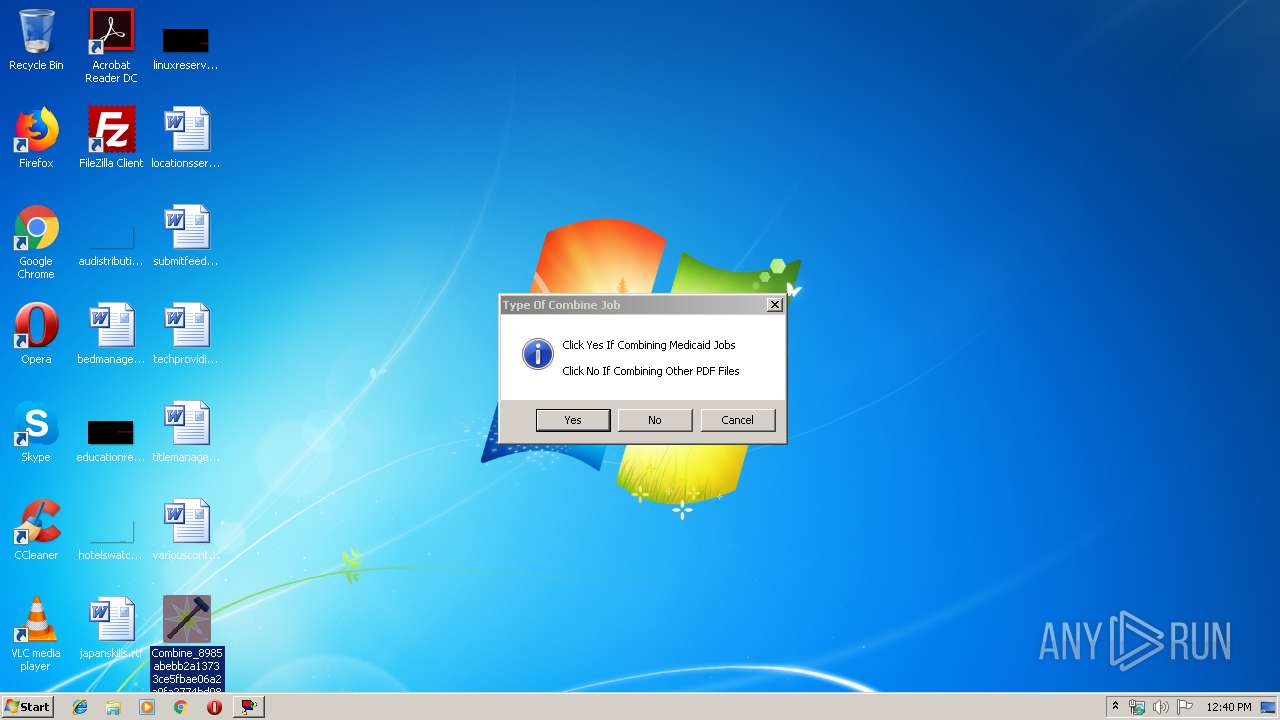
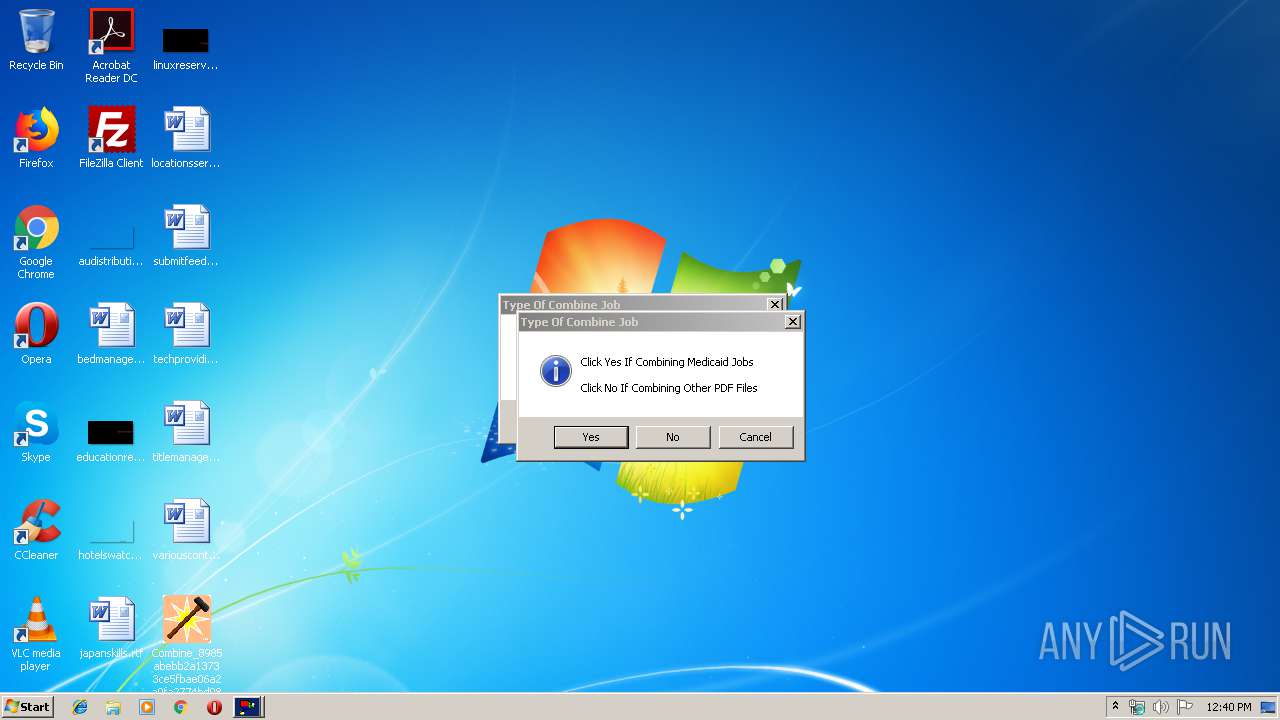
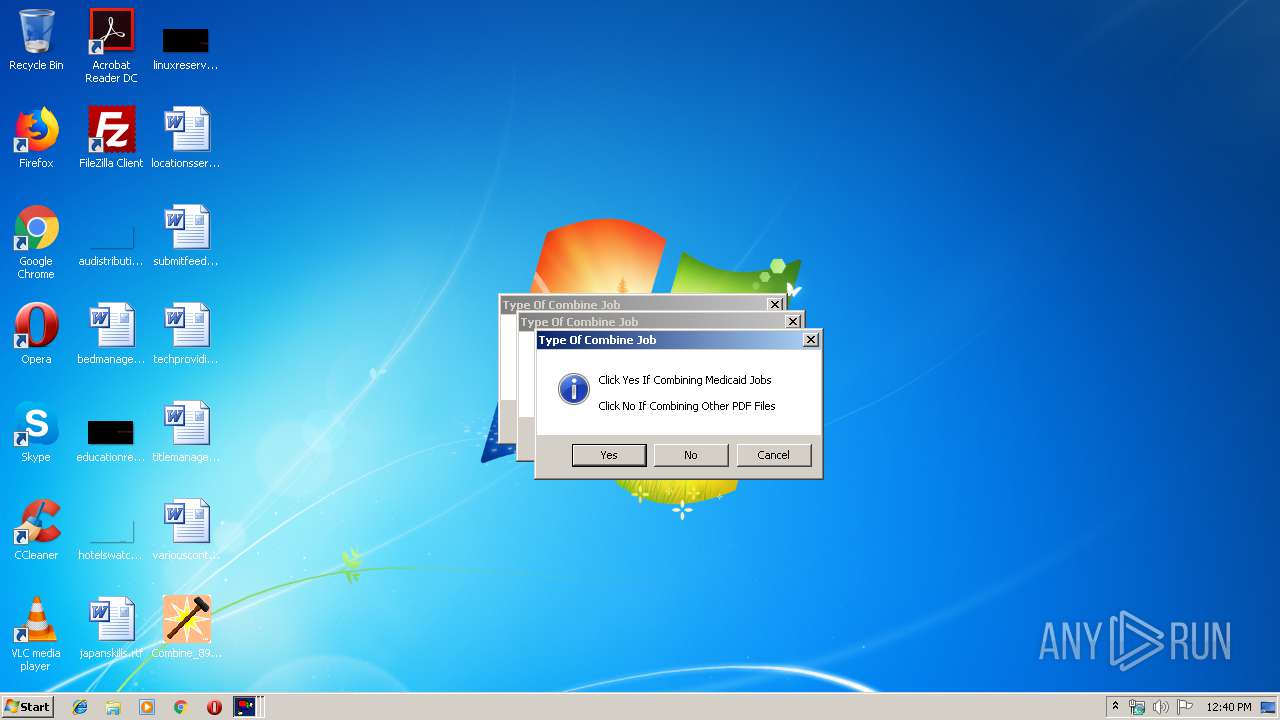
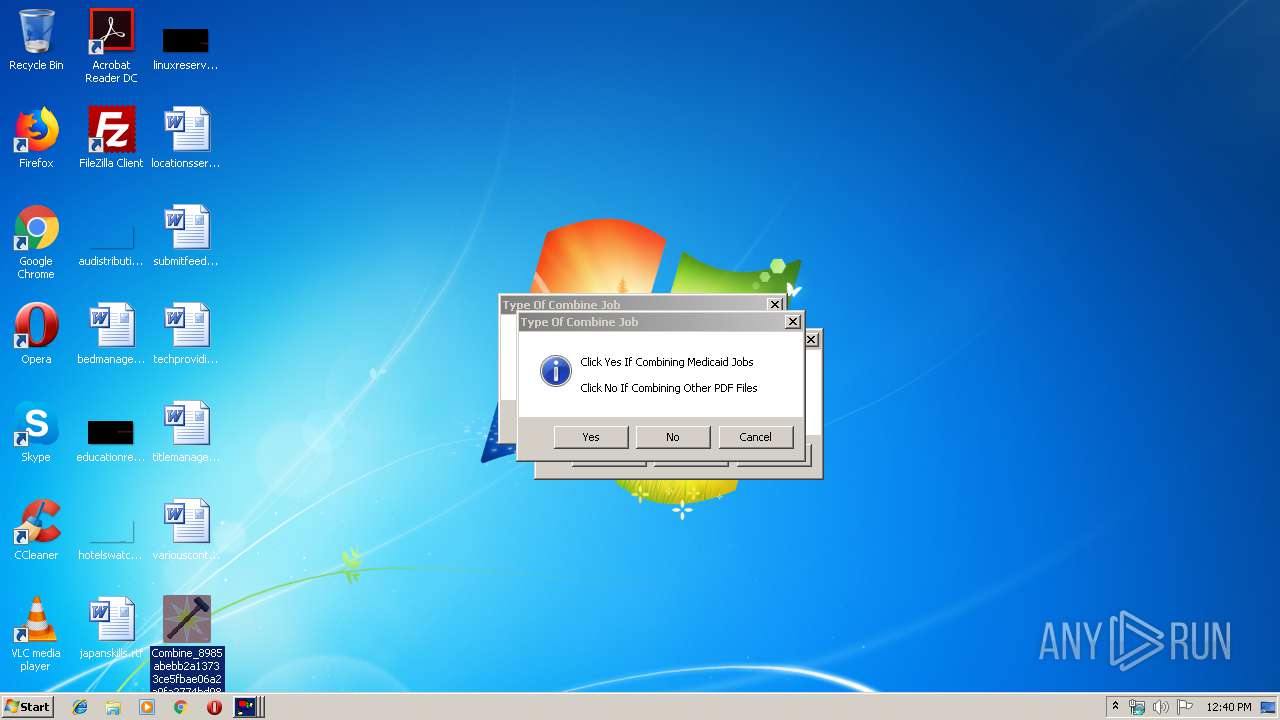
| ProductName: | Medicaid Combine |
| FileDescription: | Combines PDF Files for Medicaid Group |
| CompanyName: | Teva Pharmaceuticals |
| LegalTrademarks: | Nick Norbeck |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2018 20:18:00 |
| Detected languages: |
|
| FileVersion: | 2.0 |
| ProductVersion: | 2.0 |
| ProductName: | Medicaid Combine |
| FileDescription: | Combines PDF Files for Medicaid Group |
| CompanyName: | Teva Pharmaceuticals |
| LegalTrademarks: | Nick Norbeck |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Feb-2018 20:18:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x000037F0 | 0x00003800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.61236 |
.text | 0x00005000 | 0x0000CFA2 | 0x0000D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58582 |
.rdata | 0x00012000 | 0x000033A0 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11024 |
.data | 0x00016000 | 0x00001724 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93687 |
.rsrc | 0x00018000 | 0x0000FA44 | 0x0000FC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.42402 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
3972FB79FA9408A5DE9FCFEE684817D948BE59C9 | 3.58496 | 12 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
54C199C2A4A74372490F1F62ABDA8994 | 3.46132 | 18 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
5B1076573F63E07EB14FC107A09257DD | 7.99454 | 29940 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D5B1BB41BE | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
75
Monitored processes
36
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1040 | C:\Windows\system32\cmd.exe /c cscript//nologo C:\Users\admin\AppData\Local\Temp\#.vbs | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1308 | "C:\Users\admin\Desktop\Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe" | C:\Users\admin\Desktop\Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1796 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\D90C.tmp\D90D.tmp\D90E.bat C:\Users\admin\Desktop\Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe" | C:\Windows\system32\cmd.exe | — | Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2156 | C:\Windows\system32\cmd.exe /c cscript//nologo C:\Users\admin\AppData\Local\Temp\#.vbs | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2236 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\8416.tmp\8417.tmp\8418.bat C:\Users\admin\Desktop\Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe" | C:\Windows\system32\cmd.exe | — | Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2256 | "C:\Users\admin\Desktop\Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe" | C:\Users\admin\Desktop\Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2388 | C:\Windows\system32\cmd.exe /c dir "C:\Users\admin\Desktop"\*.pdf | find "File(s)" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2404 | C:\Windows\system32\cmd.exe /c cscript//nologo C:\Users\admin\AppData\Local\Temp\#.vbs | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2428 | cscript //nologo C:\Users\admin\AppData\Local\Temp\#.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2488 | "C:\Users\admin\Desktop\Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe" | C:\Users\admin\Desktop\Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
610
Read events
578
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3632) Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3632) Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3348) cscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
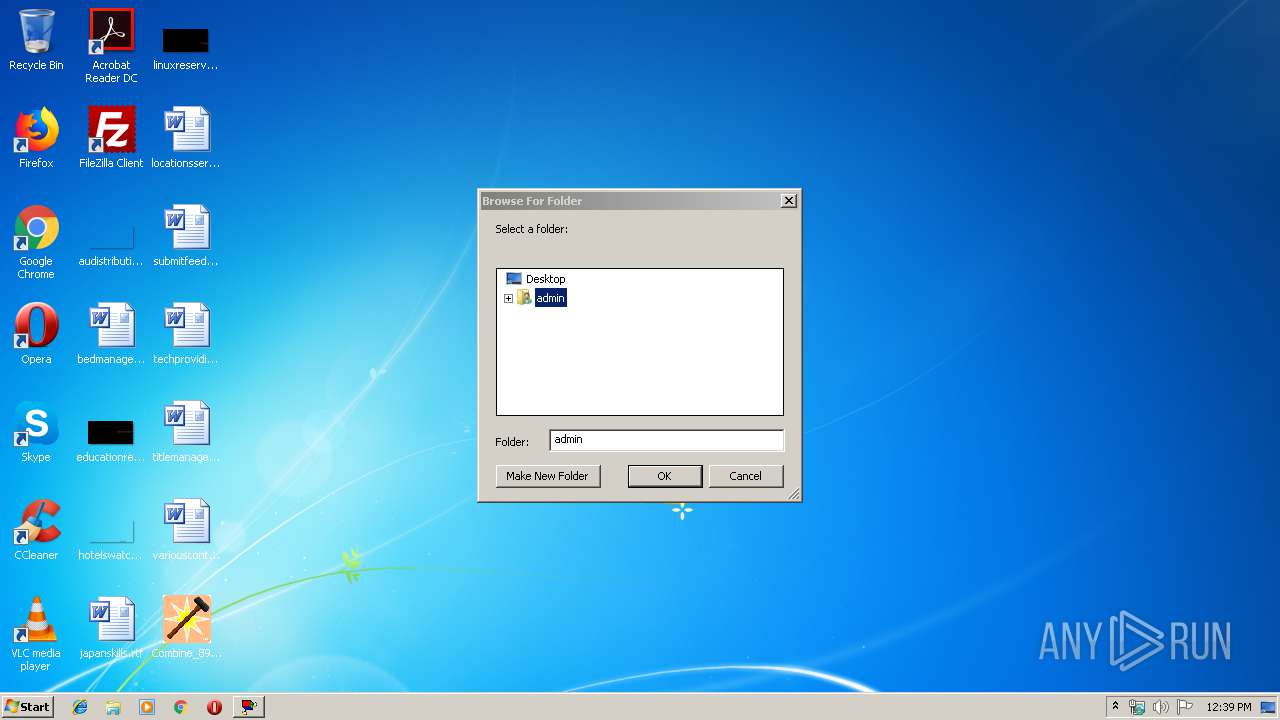
| (PID) Process: | (3348) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (3348) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (2488) Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2488) Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1308) Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1308) Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2656) Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
113
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | cmd.exe | C:\Users\admin\AppData\Local\Temp\$.vbs | text | |
MD5:— | SHA256:— | |||
| 3632 | Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | C:\Users\admin\AppData\Local\Temp\68A.tmp\68B.tmp\68C.bat | text | |
MD5:— | SHA256:— | |||
| 2656 | Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | C:\Users\admin\AppData\Local\Temp\A356.tmp\A357.tmp\A358.bat | text | |
MD5:— | SHA256:— | |||
| 2256 | Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | C:\Users\admin\AppData\Local\Temp\C843.tmp\C844.tmp\C845.bat | text | |
MD5:— | SHA256:— | |||
| 2620 | cmd.exe | C:\Users\admin\AppData\Local\Temp\#.vbs | text | |
MD5:— | SHA256:— | |||
| 2620 | cmd.exe | C:\Users\admin\AppData\Local\Temp\##.vbs | text | |
MD5:— | SHA256:— | |||
| 2488 | Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | C:\Users\admin\AppData\Local\Temp\7EE6.tmp\7EE7.tmp\7EE8.bat | text | |
MD5:— | SHA256:— | |||
| 3512 | cmd.exe | C:\Users\admin\AppData\Local\Temp\#.vbs | text | |
MD5:— | SHA256:— | |||
| 1308 | Combine_8985abebb2a13733ce5fbae06a2a0fa2774bd08032da2c966c85f45d825690af_45199.exe | C:\Users\admin\AppData\Local\Temp\8416.tmp\8417.tmp\8418.bat | text | |
MD5:— | SHA256:— | |||
| 2236 | cmd.exe | C:\Users\admin\AppData\Local\Temp\#.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report