| File name: | 32bit Patch.exe |
| Full analysis: | https://app.any.run/tasks/38d2f4e8-506a-4a74-b7f9-b5e60ad28d0e |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 05:29:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 097D7F2111B5517B6FC7531AF252C0EB |
| SHA1: | 924F2B289F9E3F4A789F560F1A54F22CD31BECF5 |
| SHA256: | 897FD2CDEEEF2509081A622D8100270F82D27E7C6ED1F7950CDE577187B7499D |
| SSDEEP: | 49152:OAI+lMuIxV3m78qbdz/e0v5mpjxyqAU2xhO0b1adQ:OAI+yuIxAnZzh5mpj2x5adQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3852)
- iexplore.exe (PID: 1396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 1992-Jun-19 22:22:17 |
| Detected languages: |
|
| Comments: | - |
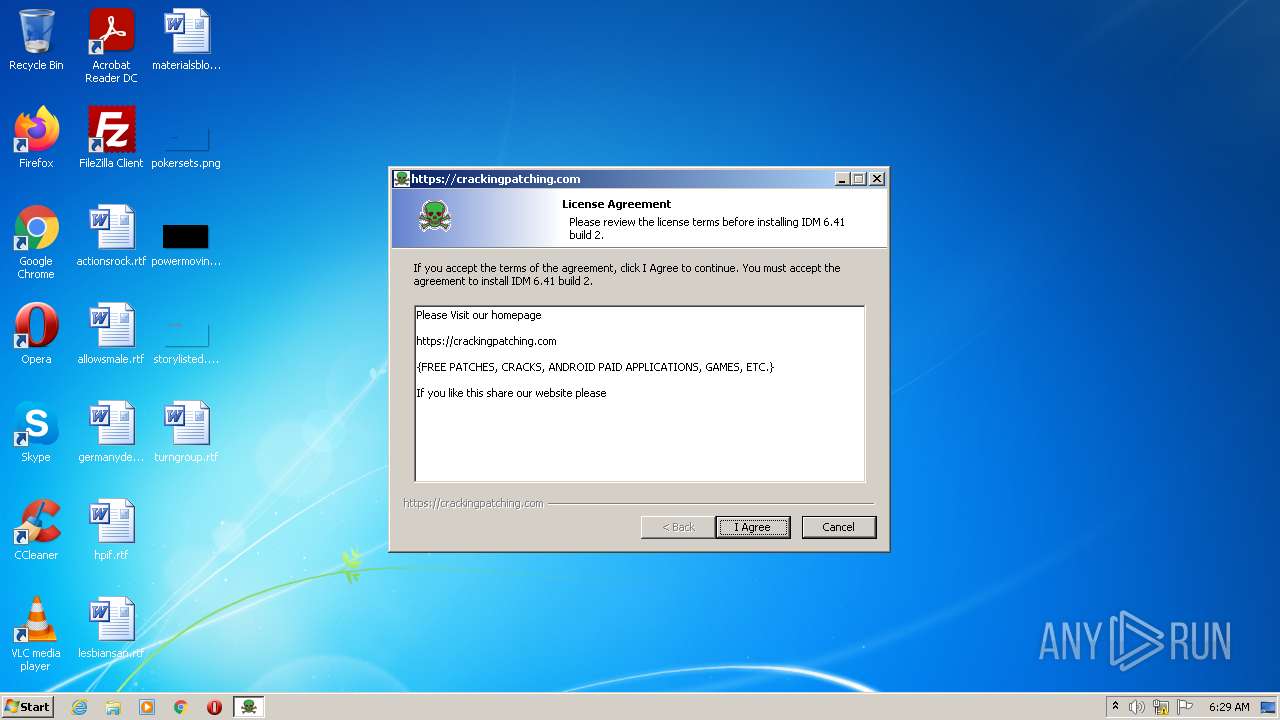
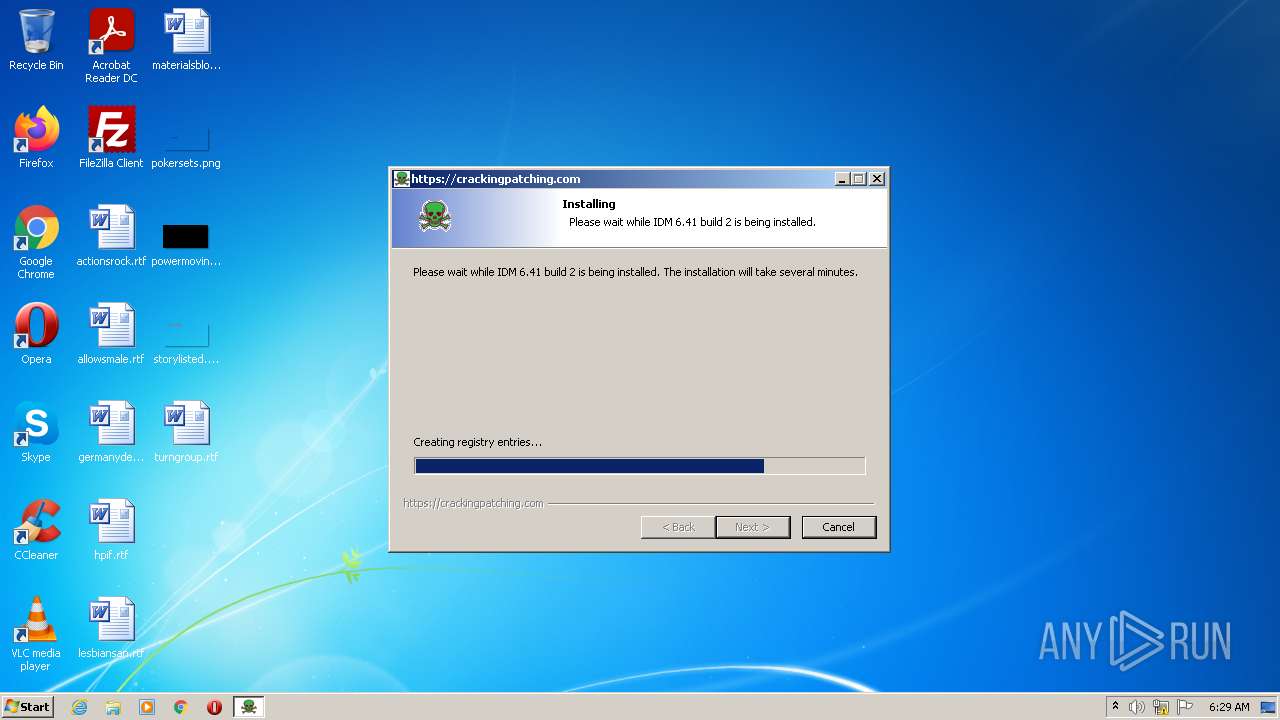
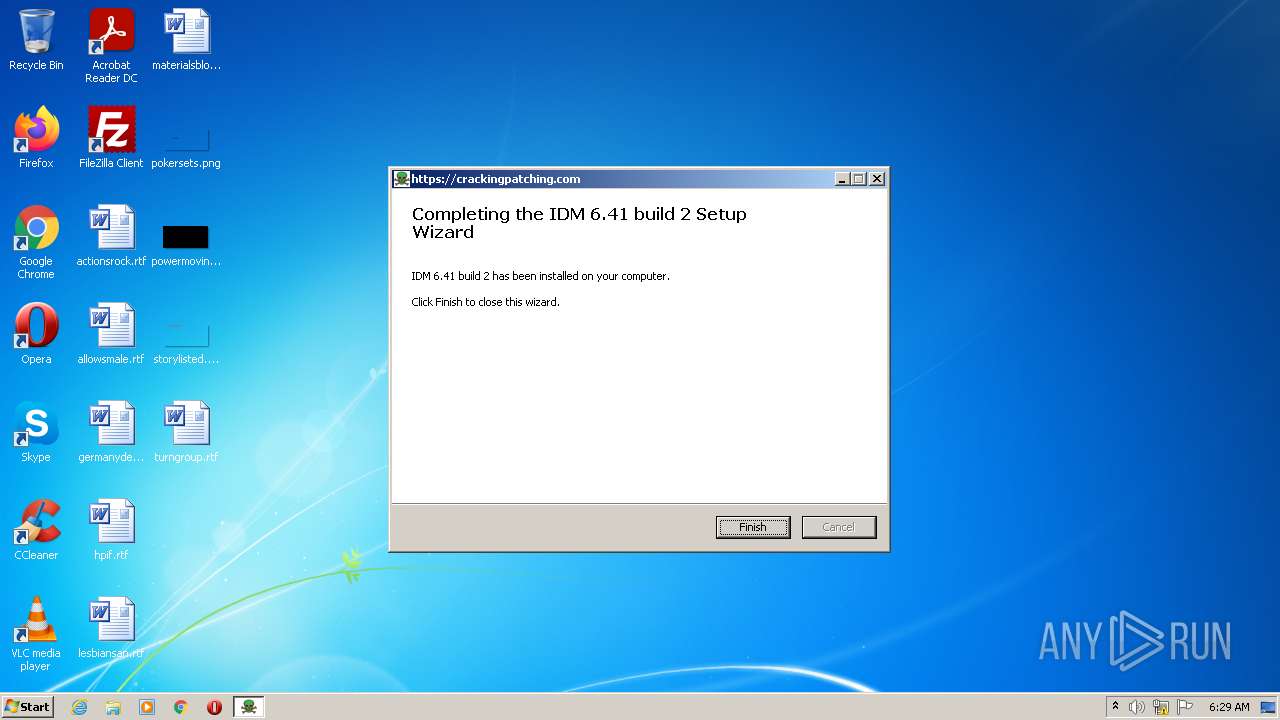
| CompanyName: | CrackingPatching |
| FileDescription: | IDM 6.41 build 2 1.0.0 Installation |
| FileVersion: | 1.0.0 |
| LegalCopyright: | CrackingPatching |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 80 |
| e_cp: | 2 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | 15 |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | 26 |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 256 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 8 |
| TimeDateStamp: | 1992-Jun-19 22:22:17 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 4096 | 148684 | 148992 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 155648 | 10388 | 10752 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 167936 | 4341 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.idata | 176128 | 6040 | 6144 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 184320 | 8 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rdata | 188416 | 24 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 192512 | 6276 | 6656 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 200704 | 290656 | 290816 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.14034 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.78849 | 884 | UNKNOWN | Russian - Russia | RT_VERSION |
50 | 5.24025 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.94231 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 4.73718 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 4.51902 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 4.05378 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.75922 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 (#2) | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
Imports
advapi32.dll |
advapi32.dll (#2) |
advapi32.dll (#3) |
cabinet.dll |
comctl32.dll |
gdi32.dll |
gdi32.dll (#2) |
kernel32.dll |
kernel32.dll (#2) |
kernel32.dll (#3) |
Total processes
44
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1396 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
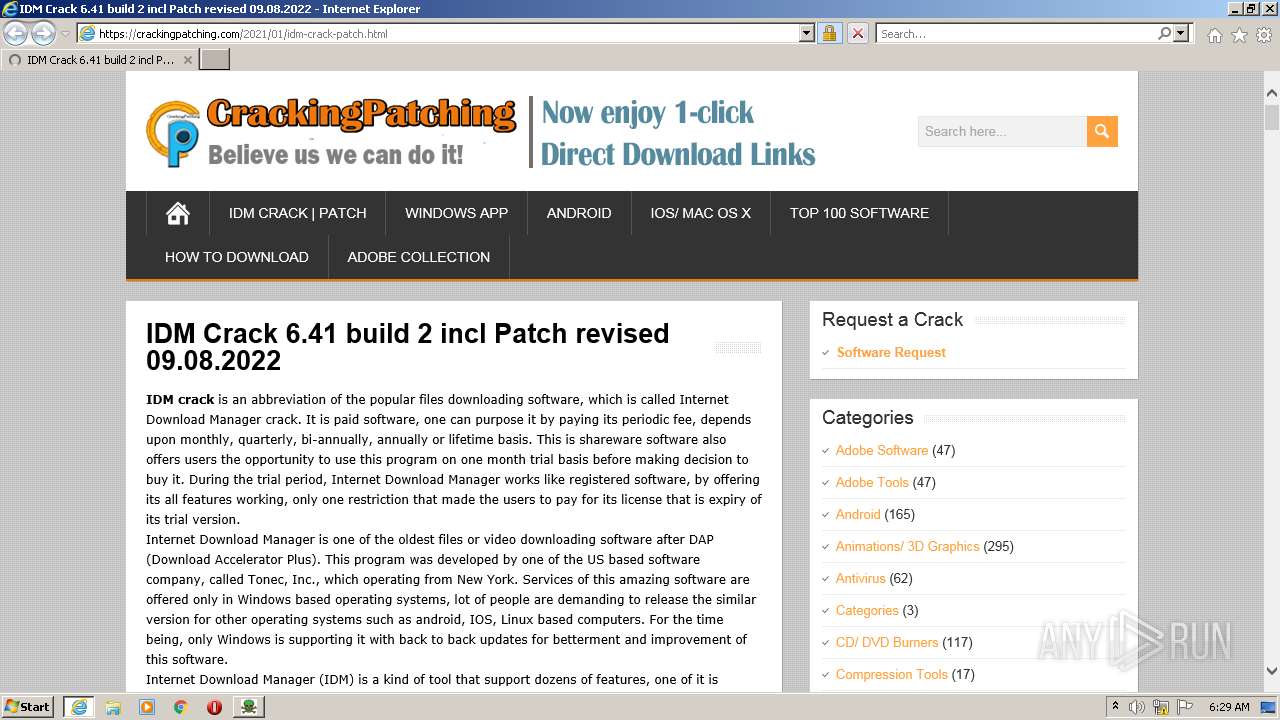
| 1396 | "C:\Program Files\Internet Explorer\iexplore.exe" https://crackingpatching.com/2021/01/idm-crack-patch.html | C:\Program Files\Internet Explorer\iexplore.exe | 32bit Patch.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3852 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\AppData\Local\Temp\32bit Patch.exe" | C:\Users\admin\AppData\Local\Temp\32bit Patch.exe | — | Explorer.EXE | |||||||||||
User: admin Company: CrackingPatching Integrity Level: MEDIUM Description: IDM 6.41 build 2 1.0.0 Installation Exit code: 3221226540 Version: 1.0.0 Modules
| |||||||||||||||
| 3852 | "C:\Program Files\Internet Explorer\iexplore.exe" https://crackingpatching.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | 32bit Patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3904 | "C:\Users\admin\AppData\Local\Temp\32bit Patch.exe" | C:\Users\admin\AppData\Local\Temp\32bit Patch.exe | Explorer.EXE | ||||||||||||
User: admin Company: CrackingPatching Integrity Level: HIGH Description: IDM 6.41 build 2 1.0.0 Installation Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
Total events
21 205
Read events
20 759
Write events
443
Delete events
3
Modification events
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202 | |||
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlot |
Value: 19 | |||
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1 |
| Operation: | write | Name: | 1 |
Value: 940031000000000009553268110050524F4752417E3200007C0008000400EFBEFA40C02C095532682A000000890B0000000001000000000000000000520000000000500072006F006700720061006D002000460069006C0065007300200028007800380036002900000040007300680065006C006C00330032002E0064006C006C002C002D0032003100380031003700000018000000 | |||
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1 |
| Operation: | write | Name: | NodeSlot |
Value: 18 | |||
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1\1 |
| Operation: | write | Name: | 0 |
Value: 6400310000000000095532681000455053494C4F7E3100004C0008000400EFBE09553268095532682A0000007938010000000300000000000000000000000000000045007000730069006C006F006E0020005300710075006100720065006400000018000000 | |||
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1\1 |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1\1 |
| Operation: | write | Name: | NodeSlot |
Value: 17 | |||
| (PID) Process: | (3904) 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1\1\0 |
| Operation: | write | Name: | 0 |
Value: 5C00310000000000095532681000494E5354414C7E310000440008000400EFBE09553268095532682A0000007A38010000000100000000000000000000000000000049006E007300740061006C006C005200690074006500000018000000 | |||
Executable files
2
Suspicious files
29
Text files
85
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3852 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{A5FE87AB-446E-11ED-8F0B-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3904 | 32bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3852 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Last Active\RecoveryStore.{A5FC2554-446E-11ED-8F0B-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3904 | 32bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | compressed | |
MD5:— | SHA256:— | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{A5FC2551-446E-11ED-8F0B-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3852 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Last Active\{A5FC2555-446E-11ED-8F0B-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3852 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7B55E468FC4B8224.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3852 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF14FD9FD5958807D1.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3852 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDF9153724E14AFBA.TMP | gmc | |
MD5:— | SHA256:— | |||
| 580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
77
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
580 | iexplore.exe | GET | 301 | 142.250.181.238:80 | http://developers.google.com/ | US | — | — | whitelisted |
580 | iexplore.exe | GET | — | 216.58.212.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGOlwNI5ZtyUEgHpNAgRyd0%3D | US | — | — | whitelisted |
580 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 2.18 Kb | whitelisted |
580 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
580 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEB%2Fvu3PmotRDEvKn%2FiRyWpo%3D | US | der | 471 b | whitelisted |
1396 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
580 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
580 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECY%2B0YL3%2ByMOCtPdrqPffYg%3D | US | der | 471 b | whitelisted |
580 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
580 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0329d72939cb3c27 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
580 | iexplore.exe | 142.250.185.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
580 | iexplore.exe | 172.217.23.98:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
580 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | FACEBOOK | IE | whitelisted |
580 | iexplore.exe | 192.0.77.2:443 | i0.wp.com | AUTOMATTIC | US | suspicious |
580 | iexplore.exe | 93.184.220.66:443 | platform.twitter.com | EDGECAST | GB | whitelisted |
580 | iexplore.exe | 192.0.76.3:443 | stats.wp.com | AUTOMATTIC | US | suspicious |
580 | iexplore.exe | 142.250.186.110:443 | apis.google.com | GOOGLE | US | whitelisted |
580 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | CLOUDFLARENET | US | suspicious |
580 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | CLOUDFLARENET | — | suspicious |
580 | iexplore.exe | 142.250.186.46:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crackingpatching.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
i0.wp.com |
| whitelisted |
apis.google.com |
| whitelisted |