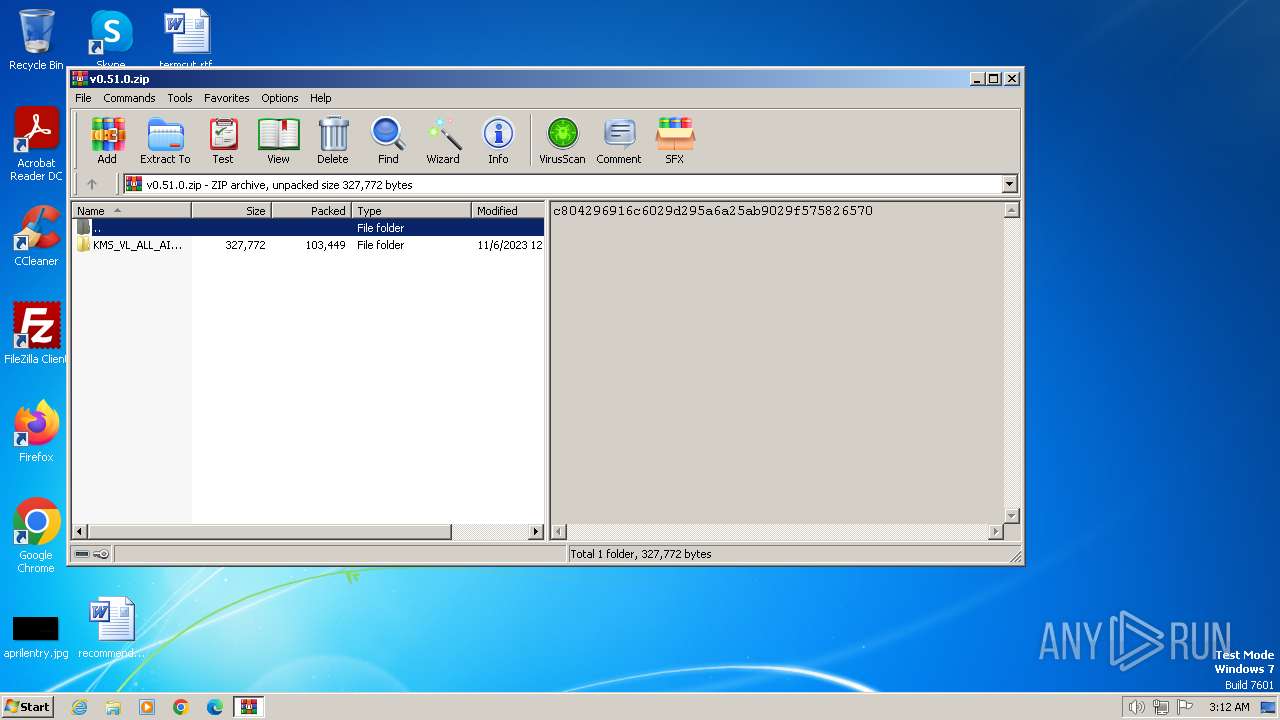
| download: | /abbodi1406/KMS_VL_ALL_AIO/archive/refs/tags/v0.51.0.zip |
| Full analysis: | https://app.any.run/tasks/027c541a-e175-4267-9f36-4d907f360780 |
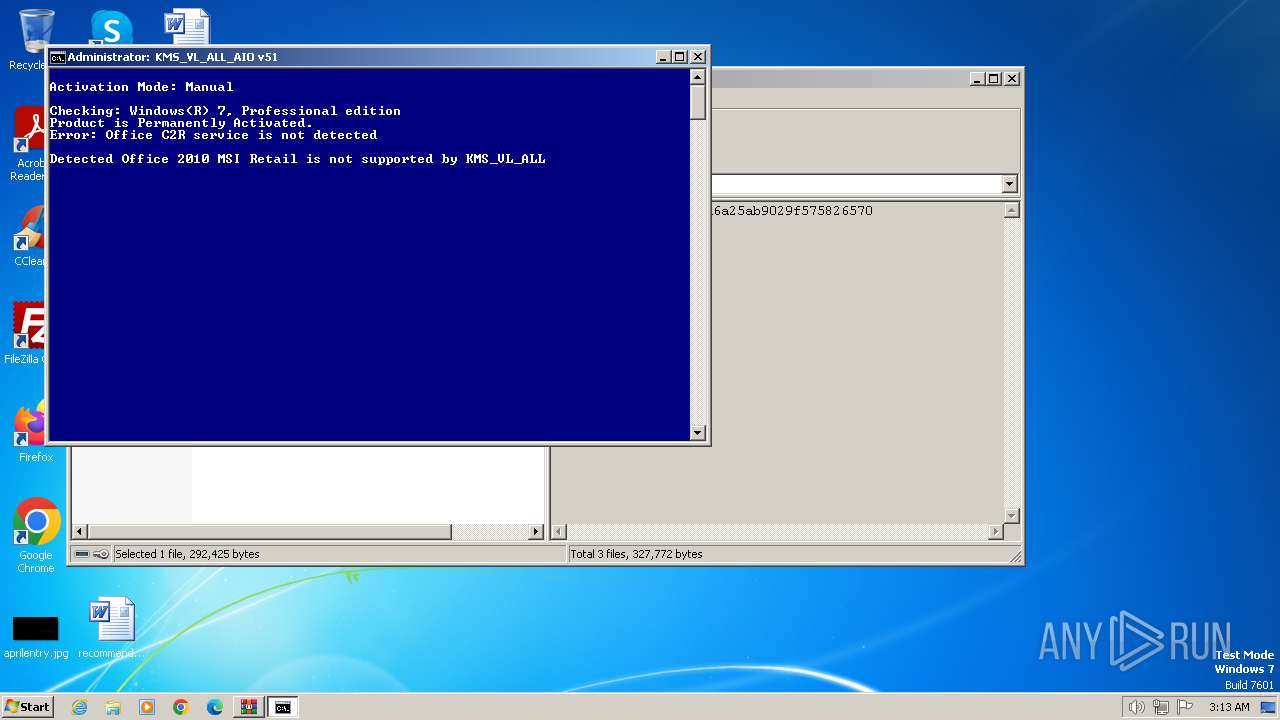
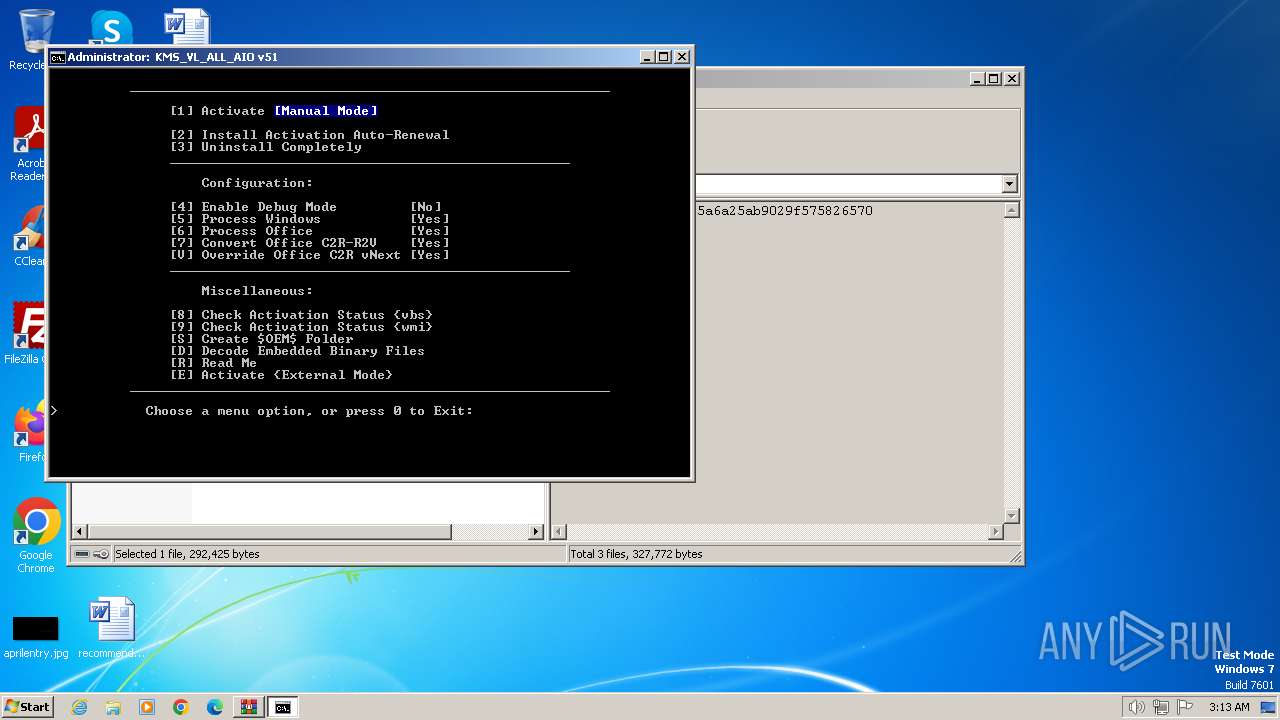
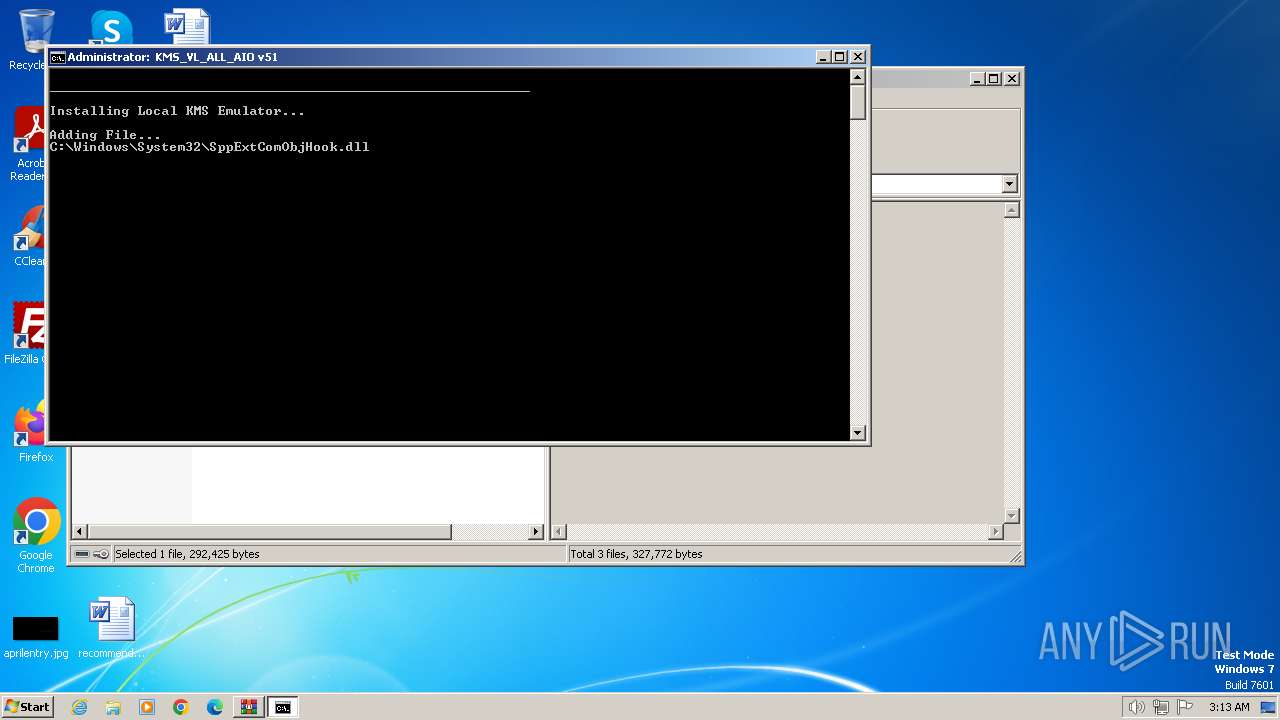
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2024, 02:12:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 481696AD54760E38B953E65878A48790 |
| SHA1: | E498259551D6BB6D5CCCDB67D924B311FD3D6EC3 |
| SHA256: | 896D62868DC33EE5A4BEFCA8B20AC286E39E03450170123161018736A453B03C |
| SSDEEP: | 3072:aHL4KsSFyl/4ncEoXhak9wc9zHt7VB5shtJGoA0TVeu2nIaTc:ajgen1yhak9w+HthzUKoAUhtaTc |
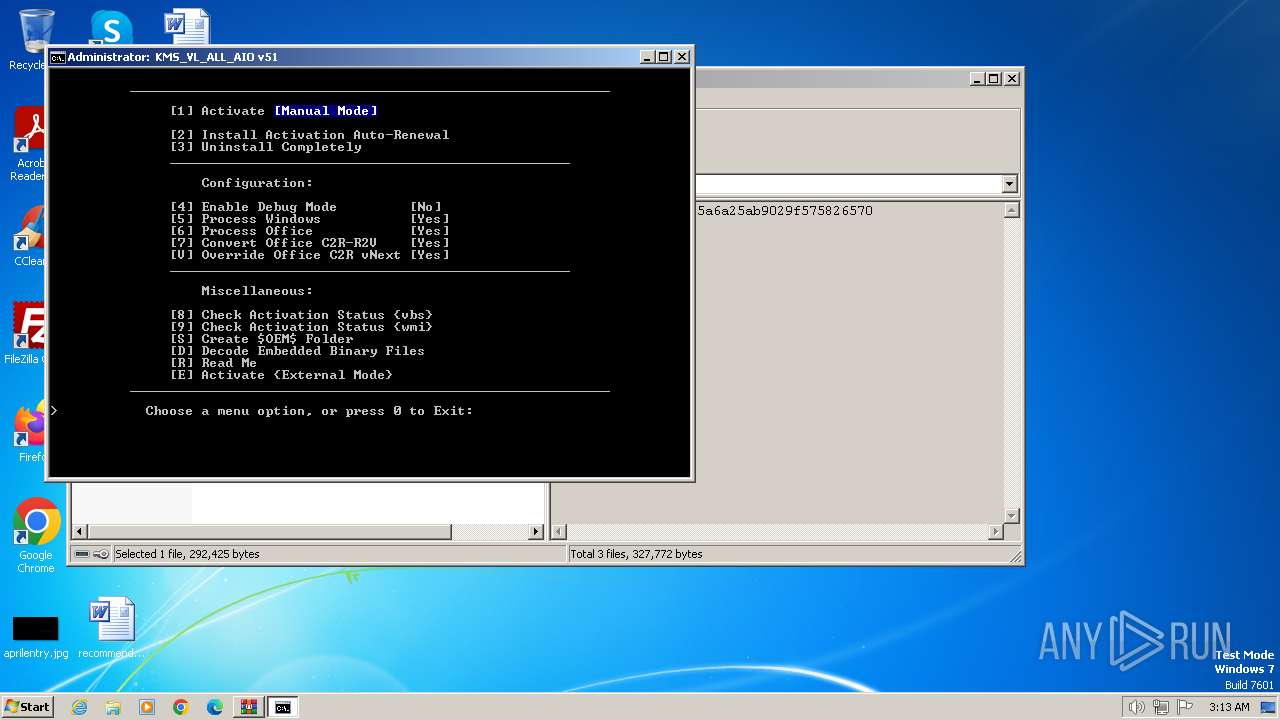
MALICIOUS
Creates a writable file in the system directory
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2444)
Drops the executable file immediately after the start
- csc.exe (PID: 2492)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2444)
- csc.exe (PID: 2124)
Starts Visual C# compiler
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2444)
Starts NET.EXE for service management
- net.exe (PID: 3772)
- cmd.exe (PID: 1844)
- net.exe (PID: 2972)
- net.exe (PID: 3260)
- net.exe (PID: 4072)
- net.exe (PID: 392)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2120)
Reads the Internet Settings
- WMIC.exe (PID: 3940)
- cscript.exe (PID: 3508)
- WMIC.exe (PID: 680)
- WMIC.exe (PID: 3892)
- WMIC.exe (PID: 3684)
- WMIC.exe (PID: 2636)
- WMIC.exe (PID: 2016)
- WMIC.exe (PID: 2892)
- WMIC.exe (PID: 2440)
- WMIC.exe (PID: 2432)
- WMIC.exe (PID: 2832)
- WMIC.exe (PID: 1344)
- WMIC.exe (PID: 3620)
- WMIC.exe (PID: 3800)
- WMIC.exe (PID: 1220)
- WMIC.exe (PID: 3780)
- WMIC.exe (PID: 532)
- WMIC.exe (PID: 2080)
- WMIC.exe (PID: 2028)
- WMIC.exe (PID: 1732)
- WMIC.exe (PID: 3492)
- WMIC.exe (PID: 2508)
- WMIC.exe (PID: 3844)
- WMIC.exe (PID: 1376)
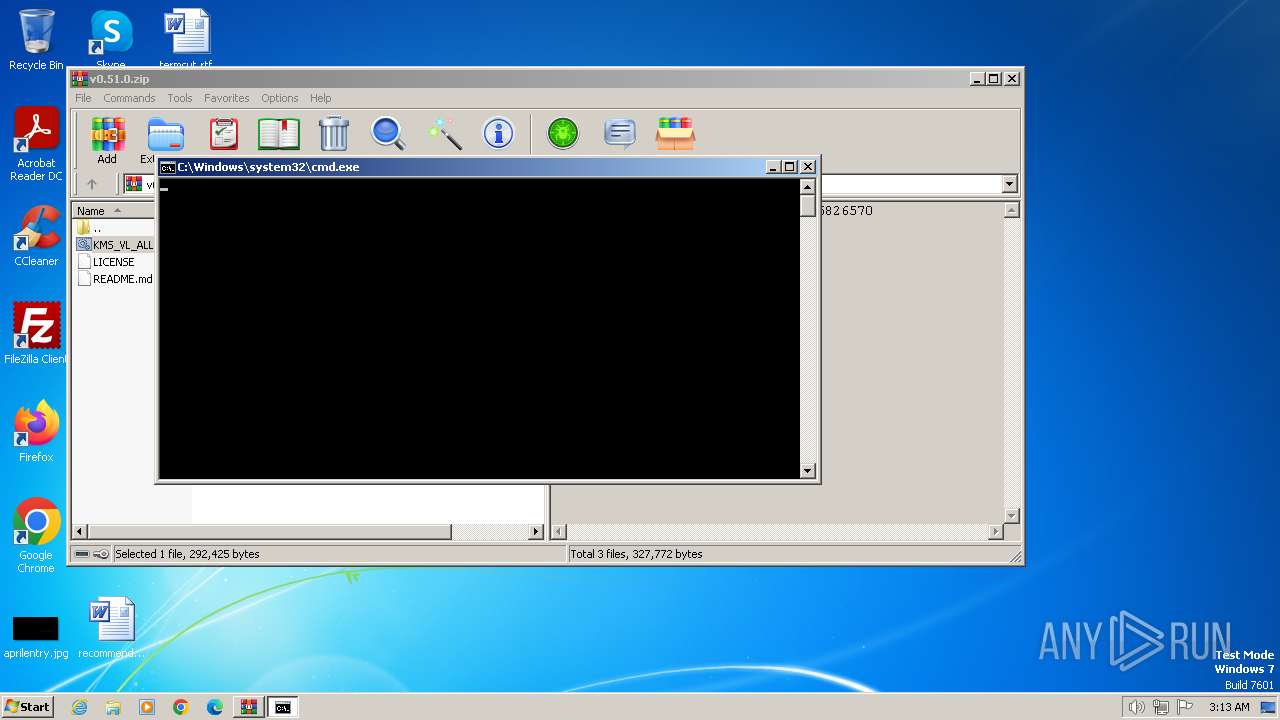
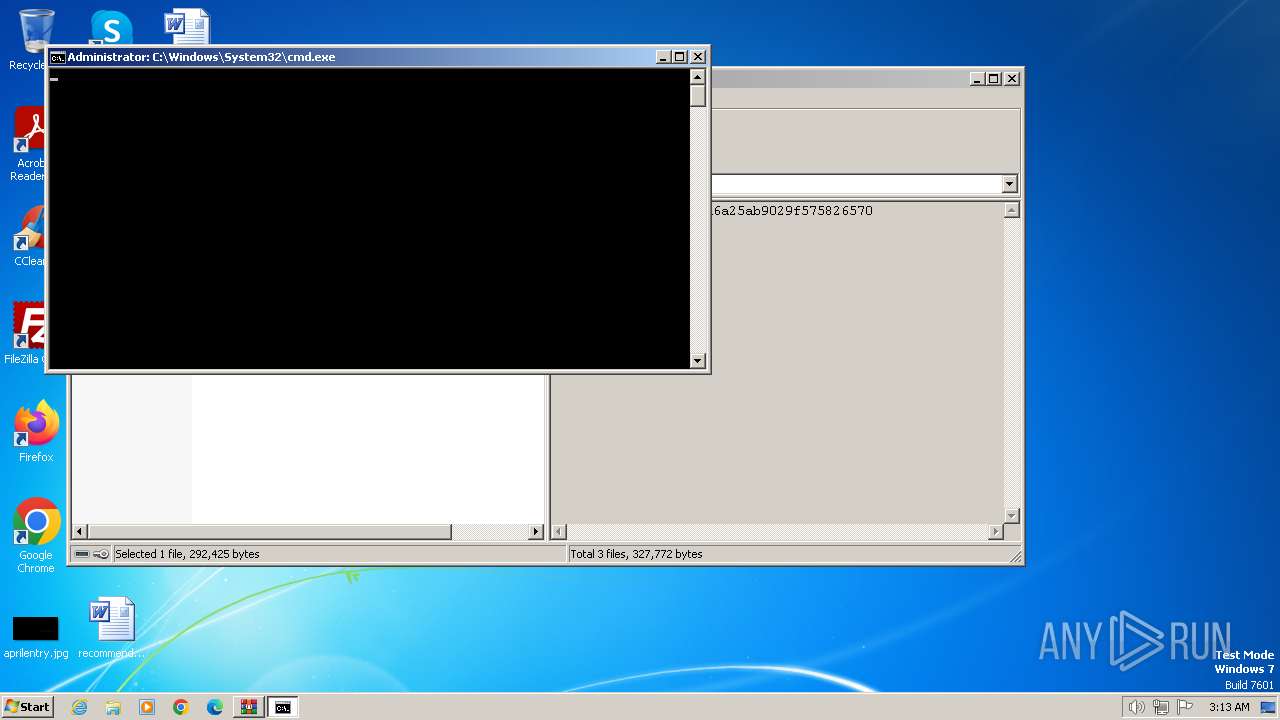
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2120)
- cscript.exe (PID: 3508)
- cmd.exe (PID: 1844)
Executing commands from ".cmd" file
- WinRAR.exe (PID: 2120)
- cscript.exe (PID: 3508)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 2580)
- cmd.exe (PID: 1844)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2580)
- cmd.exe (PID: 1844)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2580)
- cmd.exe (PID: 1844)
Runs shell command (SCRIPT)
- cscript.exe (PID: 3508)
Hides command output
- cmd.exe (PID: 1232)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2036)
- cmd.exe (PID: 4032)
- cmd.exe (PID: 3692)
- cmd.exe (PID: 2808)
- cmd.exe (PID: 1628)
- cmd.exe (PID: 1832)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 1368)
- cmd.exe (PID: 1340)
- cmd.exe (PID: 1308)
Starts SC.EXE for service management
- cmd.exe (PID: 1844)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1844)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1844)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1844)
Application launched itself
- cmd.exe (PID: 1844)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 3508)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2444)
Uses .NET C# to load dll
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2444)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1844)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2444)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2444)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1844)
- cmd.exe (PID: 3764)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 1956)
- cmd.exe (PID: 3136)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 3732)
- cmd.exe (PID: 2656)
INFO
Reads security settings of Internet Explorer
- cscript.exe (PID: 3508)
Checks supported languages
- mode.com (PID: 2588)
- csc.exe (PID: 2492)
- cvtres.exe (PID: 3492)
- mode.com (PID: 3440)
- mode.com (PID: 3644)
- cvtres.exe (PID: 2692)
- csc.exe (PID: 2124)
Checks operating system version
- cmd.exe (PID: 1844)
Reads the machine GUID from the registry
- csc.exe (PID: 2492)
- cvtres.exe (PID: 3492)
- cvtres.exe (PID: 2692)
- csc.exe (PID: 2124)
Reads Microsoft Office registry keys
- reg.exe (PID: 3568)
- reg.exe (PID: 2780)
- reg.exe (PID: 1376)
- reg.exe (PID: 2556)
- reg.exe (PID: 1584)
- reg.exe (PID: 924)
- reg.exe (PID: 2308)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2444)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:11:06 04:13:26 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | KMS_VL_ALL_AIO-0.51.0/ |
Total processes
330
Monitored processes
283
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | C:\Windows\system32\cmd.exe /c "prompt $H&for %B in (1) do rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 124 | find /i "Office 16" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 128 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe" /f /v KMS_ActivationInterval /t REG_DWORD /d 120 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 268 | find /i "STOPPED" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | find /i "Office 16" "C:\Windows\Temp\sppchk.txt" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /f /v KMS_RenewalInterval /t REG_DWORD /d 43200 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /v Office2010 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | reg query HKCU\SOFTWARE\Microsoft\Office\16.0\Common\Licensing\LicensingNext /v MigrationToV6Done | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | net start osppsvc /y | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe" /f /v KMS_ActivationInterval /t REG_DWORD /d 120 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
28 772
Read events
28 671
Write events
80
Delete events
21
Modification events
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\v0.51.0.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
4
Suspicious files
5
Text files
8
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2120.6447\KMS_VL_ALL_AIO.cmd | text | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ka5dcscb.4wp.ps1 | binary | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Local\Temp\4h2bx0ba.cmu.psm1 | binary | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:— | SHA256:— | |||
| 1816 | powershell.exe | C:\Users\admin\AppData\Local\Temp\nd354zyk.rdo.ps1 | binary | |
MD5:— | SHA256:— | |||
| 1816 | powershell.exe | C:\Users\admin\AppData\Local\Temp\02rvk4sa.nfh.psm1 | binary | |
MD5:— | SHA256:— | |||
| 1844 | cmd.exe | C:\Windows\Temp\' | binary | |
MD5:— | SHA256:— | |||
| 1844 | cmd.exe | C:\Windows\Temp\`.txt | binary | |
MD5:— | SHA256:— | |||
| 948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\w3g1uph3.ryo.ps1 | binary | |
MD5:— | SHA256:— | |||
| 948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1vyqm431.sql.psm1 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |