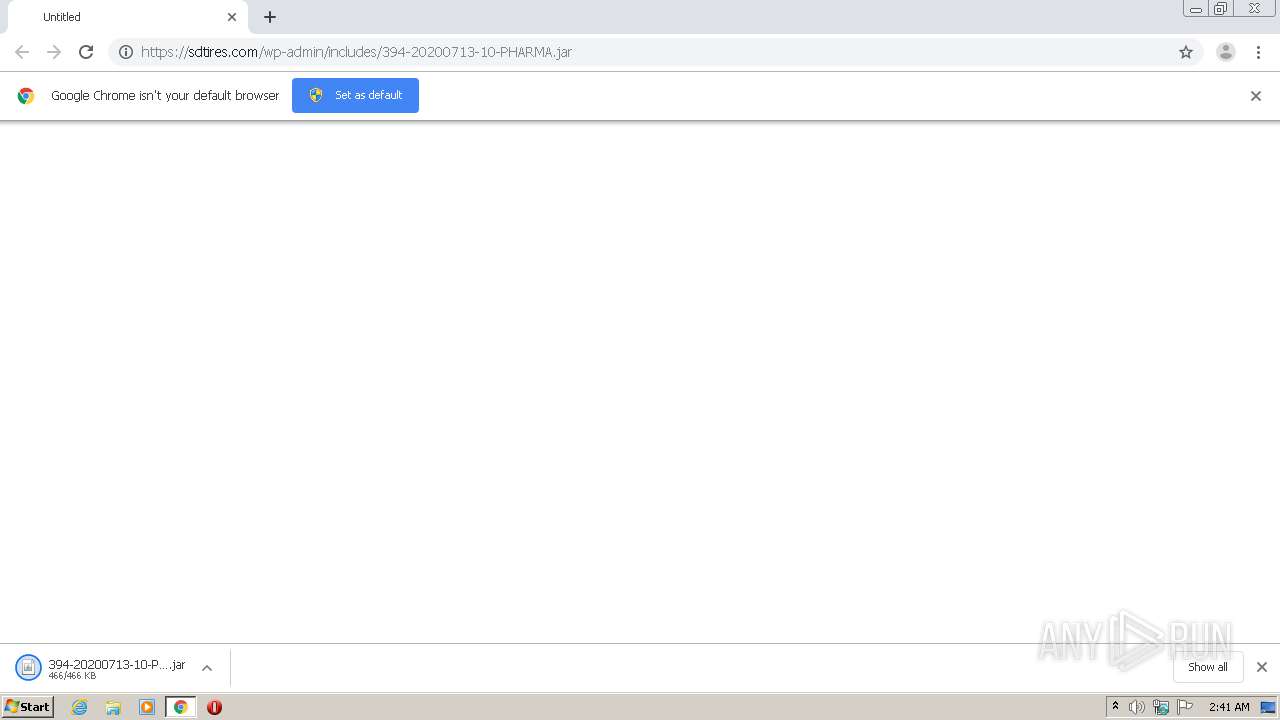
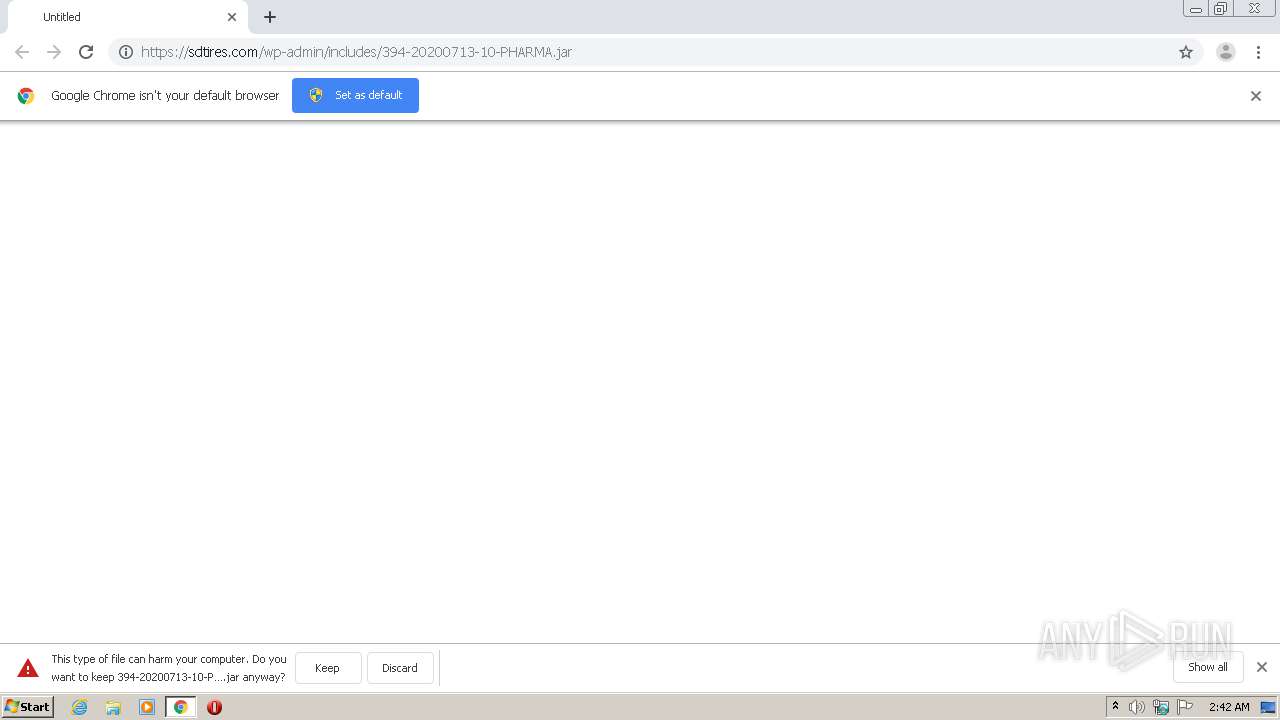
| URL: | https://sdtires.com/wp-admin/includes/394-20200713-10-PHARMA.jar |
| Full analysis: | https://app.any.run/tasks/a0f35b94-8851-48fc-b6e2-0fc1505751b4 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | July 13, 2020, 01:41:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0D0FCC99935DBE301C321034F00CD47D |
| SHA1: | 292C862B31C9942FC658867E5EB0E750CE025DDB |
| SHA256: | 8966C18CB38544CA39C3349FB75C1AC8748C7FA796C58665FD47DA0D1A748BC1 |
| SSDEEP: | 3:N8MAZiVgzeBA1JP9FPEX:2MAZiVgzeA1JlFG |
MALICIOUS
Loads dropped or rewritten executable
- javaw.exe (PID: 2508)
- javaw.exe (PID: 1248)
QEALLER was detected
- javaw.exe (PID: 1248)
- javaw.exe (PID: 2508)
Actions looks like stealing of personal data
- javaw.exe (PID: 1248)
- javaw.exe (PID: 2508)
Executes PowerShell scripts
- cmd.exe (PID: 3312)
- cmd.exe (PID: 1824)
Stealing of credential data
- javaw.exe (PID: 2508)
Connects to CnC server
- javaw.exe (PID: 1248)
- javaw.exe (PID: 2508)
SUSPICIOUS
Executes JAVA applets
- chrome.exe (PID: 3292)
Creates files in the user directory
- javaw.exe (PID: 1248)
- powershell.exe (PID: 864)
- powershell.exe (PID: 2164)
Executable content was dropped or overwritten
- javaw.exe (PID: 1248)
- javaw.exe (PID: 2508)
Starts application with an unusual extension
- cmd.exe (PID: 3312)
- cmd.exe (PID: 1824)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 1248)
- javaw.exe (PID: 2508)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3292)
INFO
Application launched itself
- chrome.exe (PID: 3292)
Reads the hosts file
- chrome.exe (PID: 3292)
- chrome.exe (PID: 2128)
Reads Internet Cache Settings
- chrome.exe (PID: 3292)
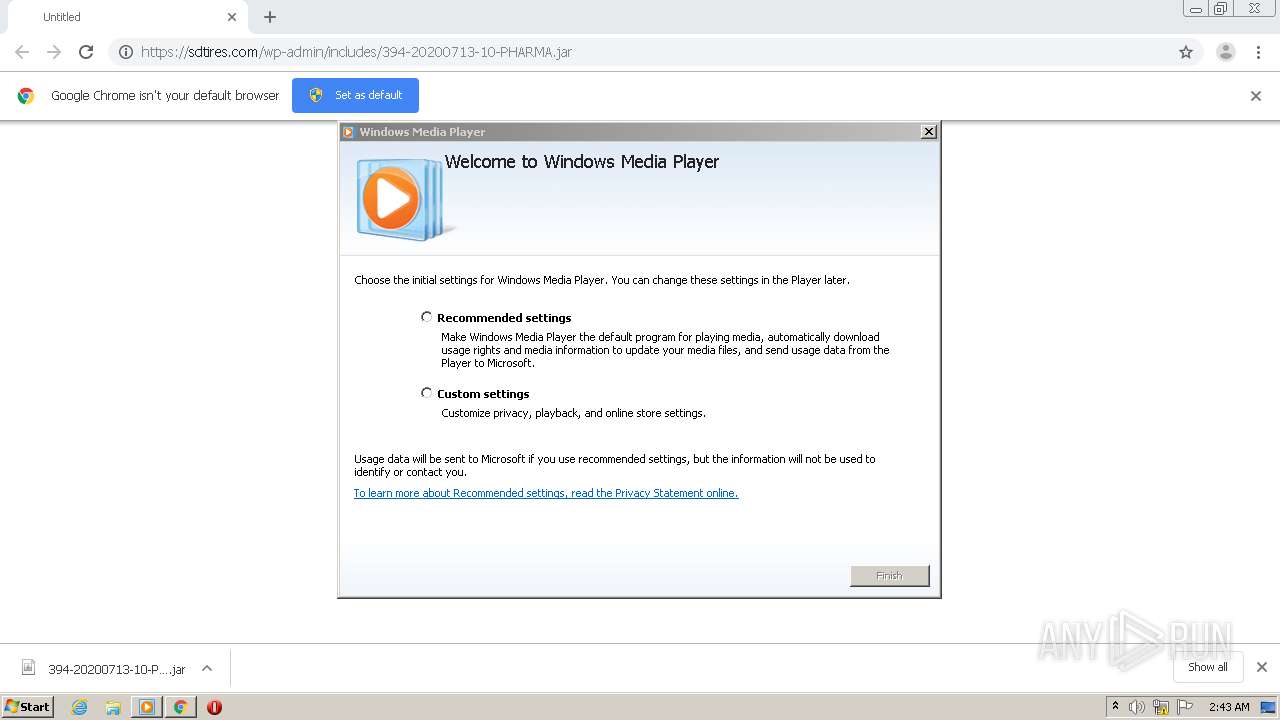
Manual execution by user
- wmplayer.exe (PID: 3208)
Reads settings of System Certificates
- chrome.exe (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
36
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | powershell.exe -ExecutionPolicy Bypass -NoExit -NoProfile -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\394-20200713-10-PHARMA.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | chrome.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,9594937253302162837,3652009559622254554,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16119042560905623425 --mojo-platform-channel-handle=3540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ee8a9d0,0x6ee8a9e0,0x6ee8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1824 | cmd.exe /c chcp 1252 > NUL & powershell.exe -ExecutionPolicy Bypass -NoExit -NoProfile -Command - | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,9594937253302162837,3652009559622254554,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18195552115658767680 --mojo-platform-channel-handle=4632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,9594937253302162837,3652009559622254554,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5953542988094908301 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,9594937253302162837,3652009559622254554,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13404084278340072716 --mojo-platform-channel-handle=1644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2164 | powershell.exe -ExecutionPolicy Bypass -NoExit -NoProfile -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,9594937253302162837,3652009559622254554,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7165549539202105284 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 611
Read events
1 394
Write events
212
Delete events
5
Modification events
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3292-13239078089587000 |
Value: 259 | |||
| (PID) Process: | (3292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3292-13239078089587000 |
Value: 259 | |||
Executable files
9
Suspicious files
33
Text files
217
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0BBBCA-CDC.pma | — | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\15b03d3e-b3fb-421d-a383-73a58bca2328.tmp | — | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF27cab4.TMP | text | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF27cab4.TMP | text | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF27cc6a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
41
DNS requests
15
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2128 | chrome.exe | GET | 200 | 173.194.5.203:80 | http://r5---sn-aigl6n76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.217.117.48&mm=28&mn=sn-aigl6n76&ms=nvh&mt=1594604595&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
2128 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
2128 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2128 | chrome.exe | GET | 200 | 173.194.5.215:80 | http://r1---sn-aigl6n7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.217.117.48&mm=28&mn=sn-aigl6n7d&ms=nvh&mt=1594604595&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2128 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
1248 | javaw.exe | 198.199.119.212:80 | — | Digital Ocean, Inc. | US | malicious |
2508 | javaw.exe | 198.199.119.212:80 | — | Digital Ocean, Inc. | US | malicious |
2128 | chrome.exe | 172.217.21.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2128 | chrome.exe | 172.217.16.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
— | — | 173.194.5.215:80 | r1---sn-aigl6n7d.gvt1.com | Google Inc. | US | whitelisted |
2128 | chrome.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2128 | chrome.exe | 173.194.5.203:80 | r5---sn-aigl6n76.gvt1.com | Google Inc. | US | whitelisted |
2128 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2128 | chrome.exe | 167.172.50.76:443 | sdtires.com | — | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
sdtires.com |
| unknown |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients4.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1248 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
1248 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
1248 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
1248 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
1248 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
1248 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
2508 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
2508 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
2508 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
2508 | javaw.exe | A Network Trojan was detected | STEALER [PTsecurity] Pyrogenic.Qealler |
22 ETPRO signatures available at the full report