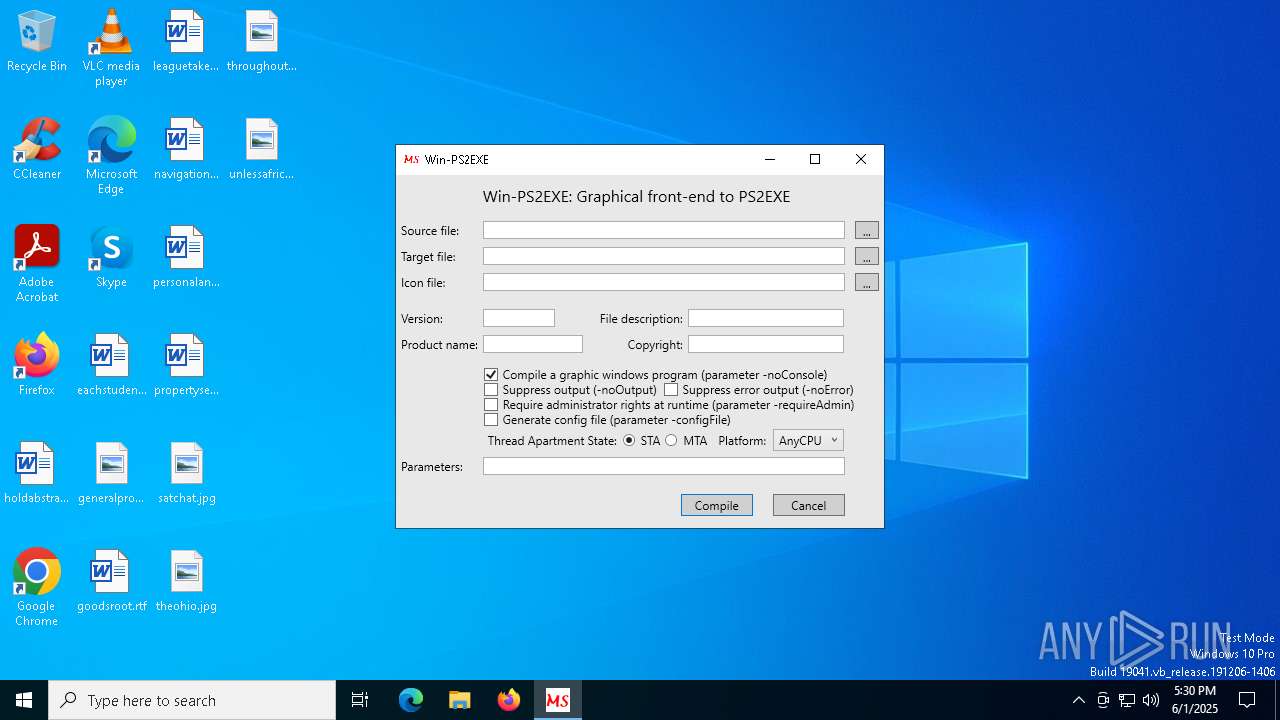
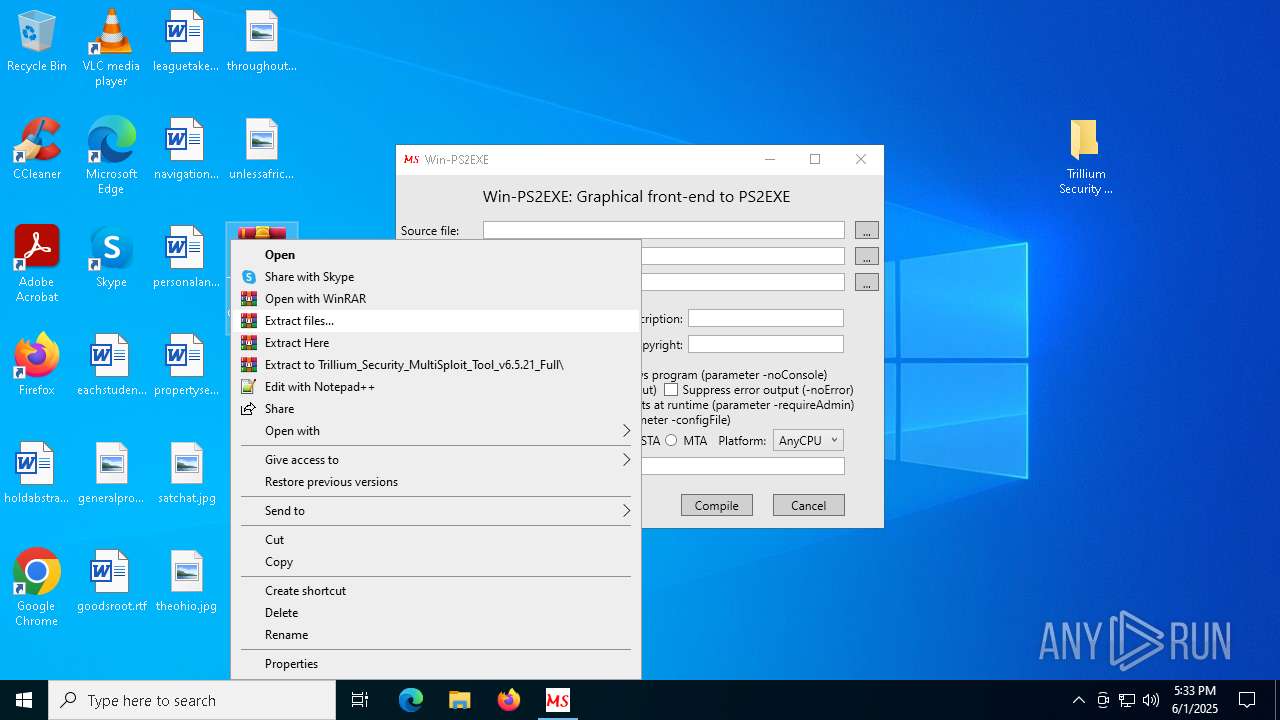
| File name: | Win-PS2EXE.exe |
| Full analysis: | https://app.any.run/tasks/d7e7e3e0-54da-4373-8f6c-9fdba9be0c4c |
| Verdict: | Malicious activity |
| Analysis date: | June 01, 2025, 17:30:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | A14CD9701168DC0FD0EDC5D4550330F4 |
| SHA1: | 032EBF36E0B57F0A622A6390B000D56E39C5C332 |
| SHA256: | 8965FEB0301C9970FA3C867882B51883F72109199703950D9F9F57F0DA3AA261 |
| SSDEEP: | 768:4Y7dPDOZdWGazzzLwnmmmmmmmmmmmmrNgOuKY3o3tGkduqVC+Obac9q/fLuU:4Y9GgOuKY3o3tGkduqVC+ObzifLuU |
MALICIOUS
No malicious indicators.SUSPICIOUS
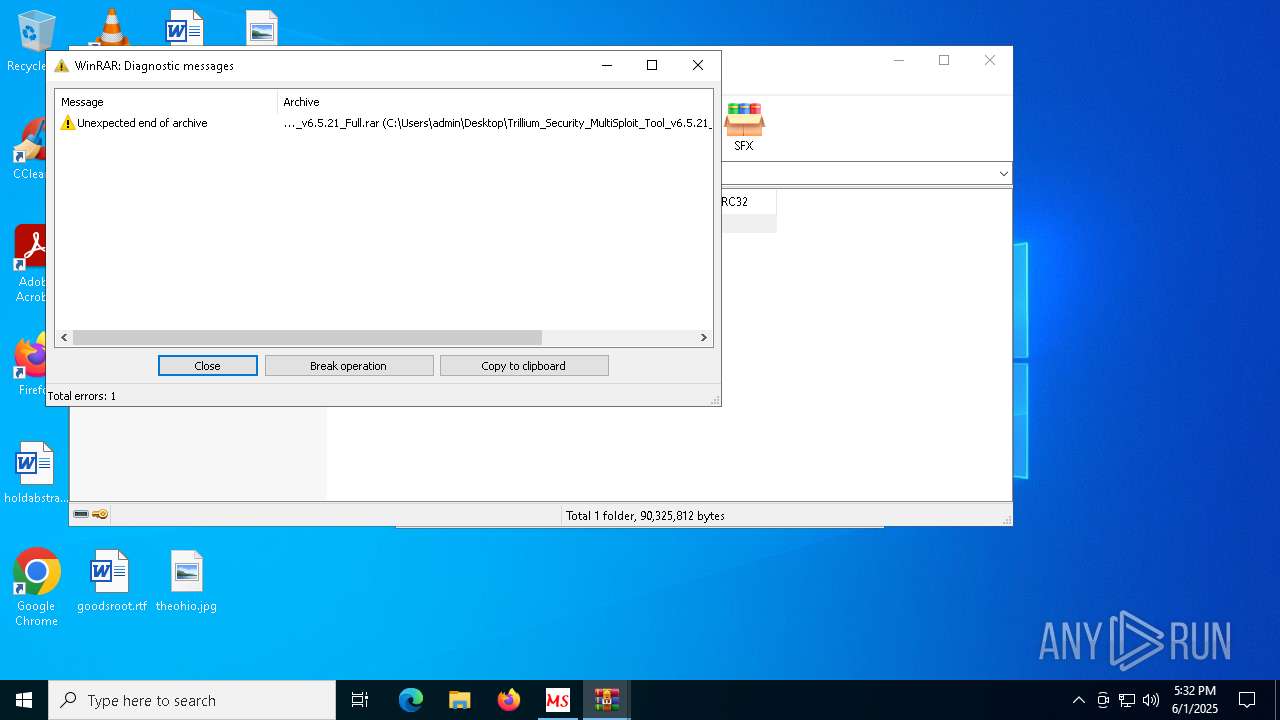
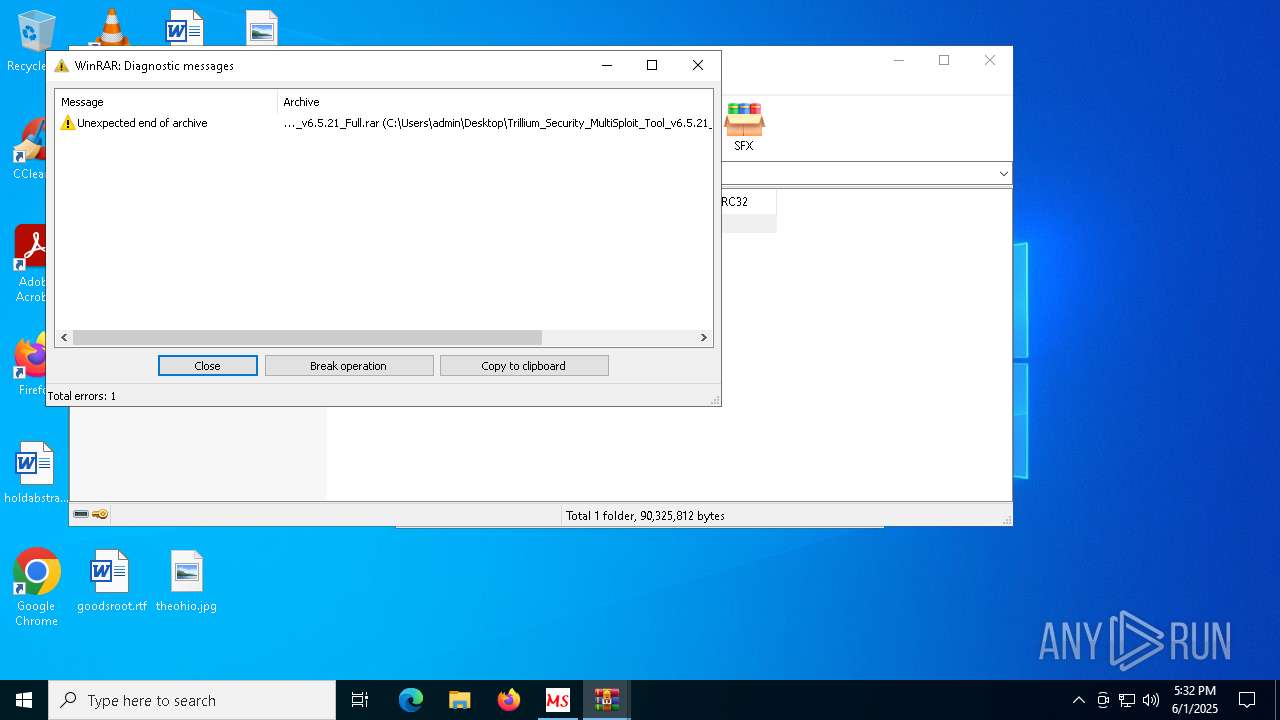
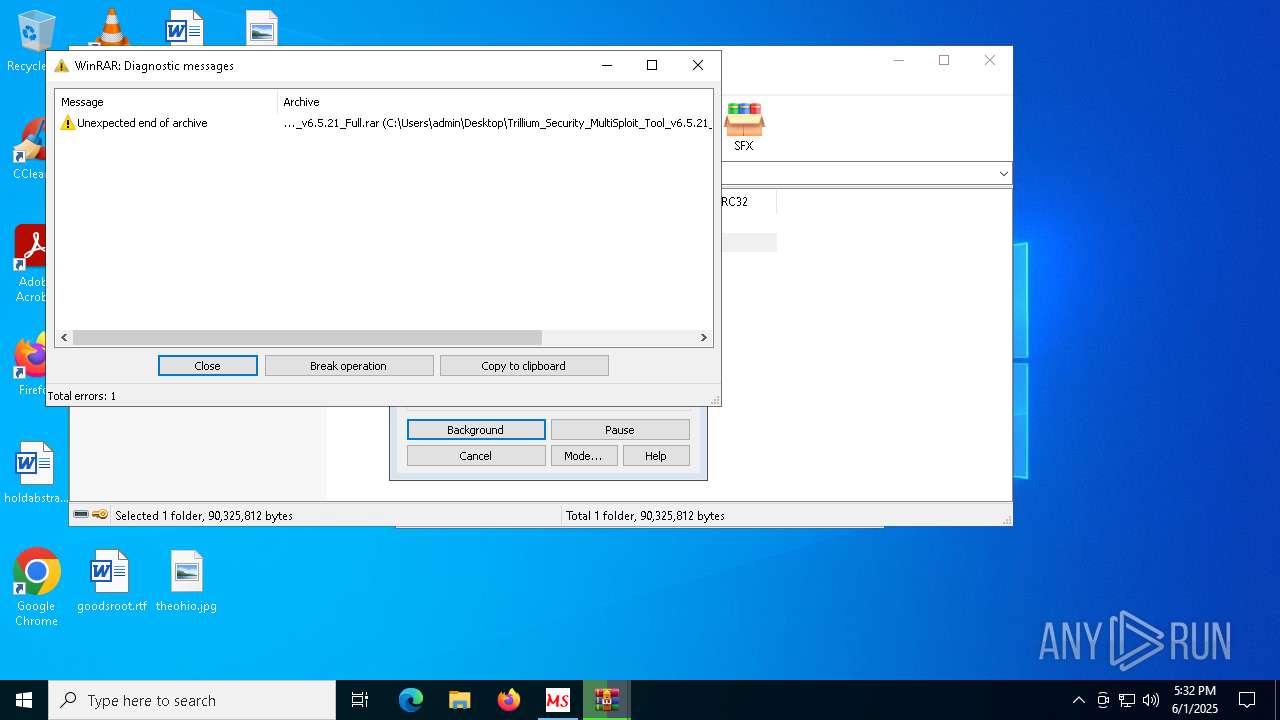
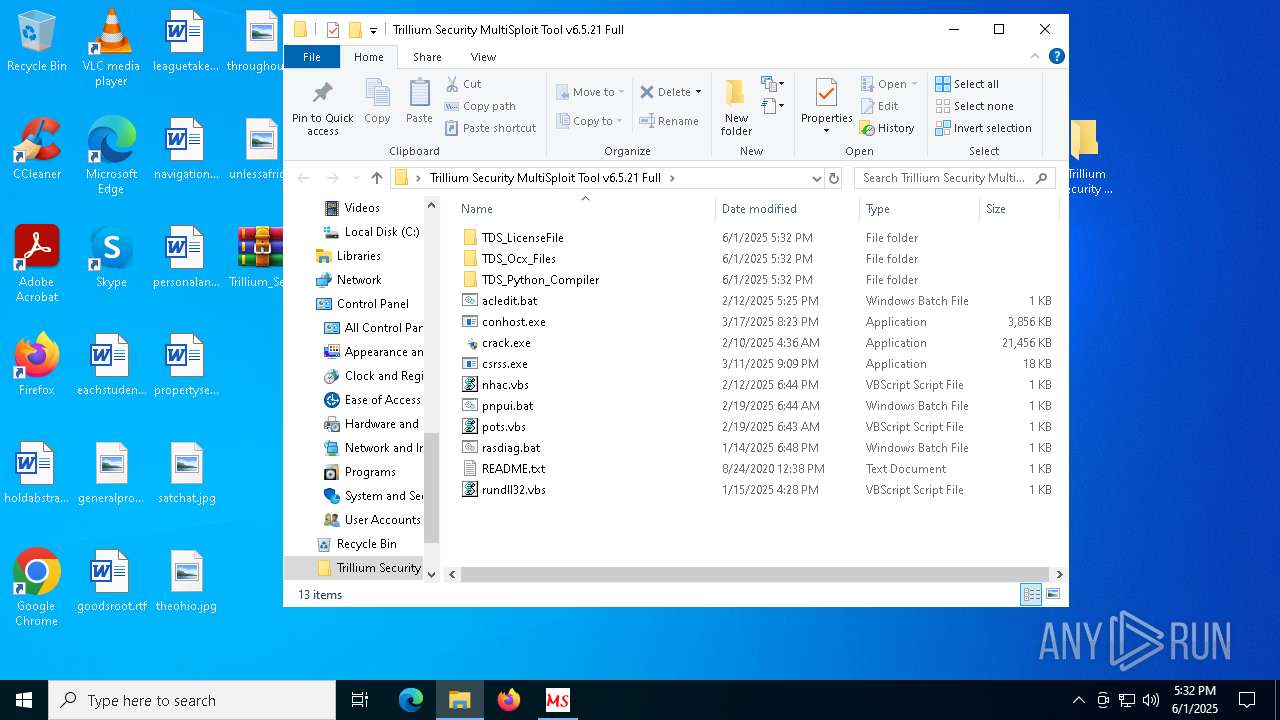
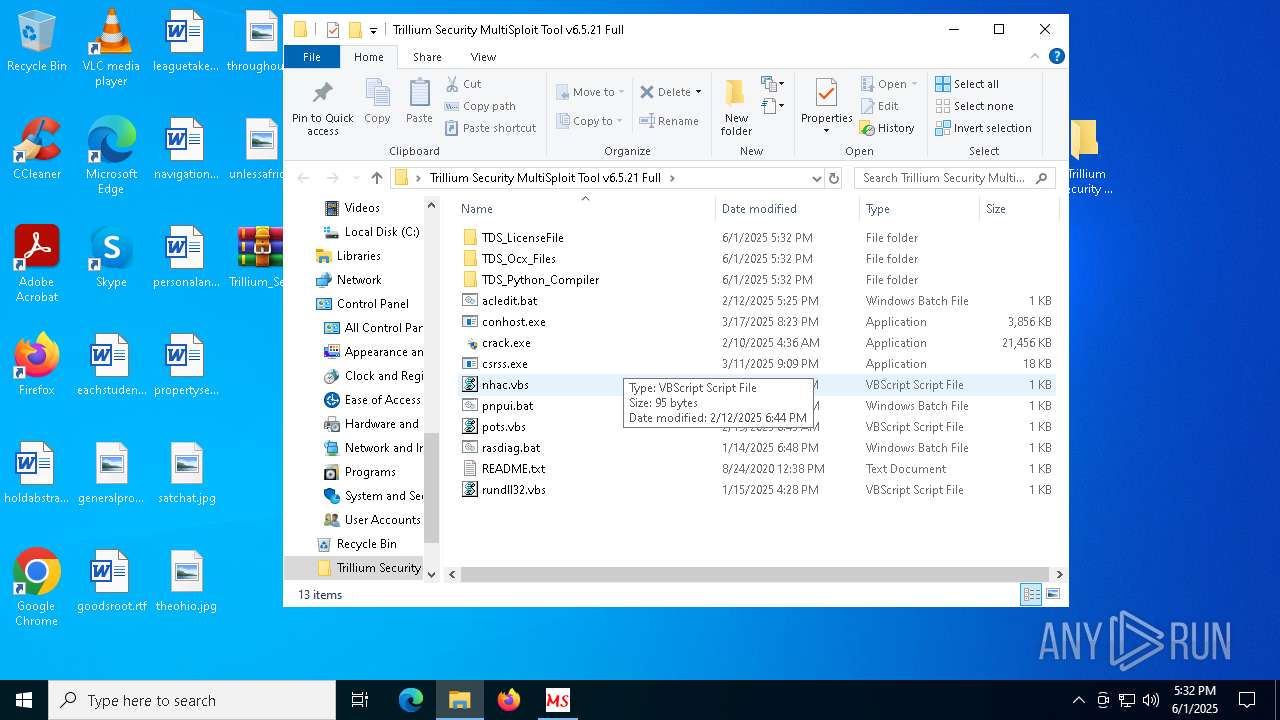
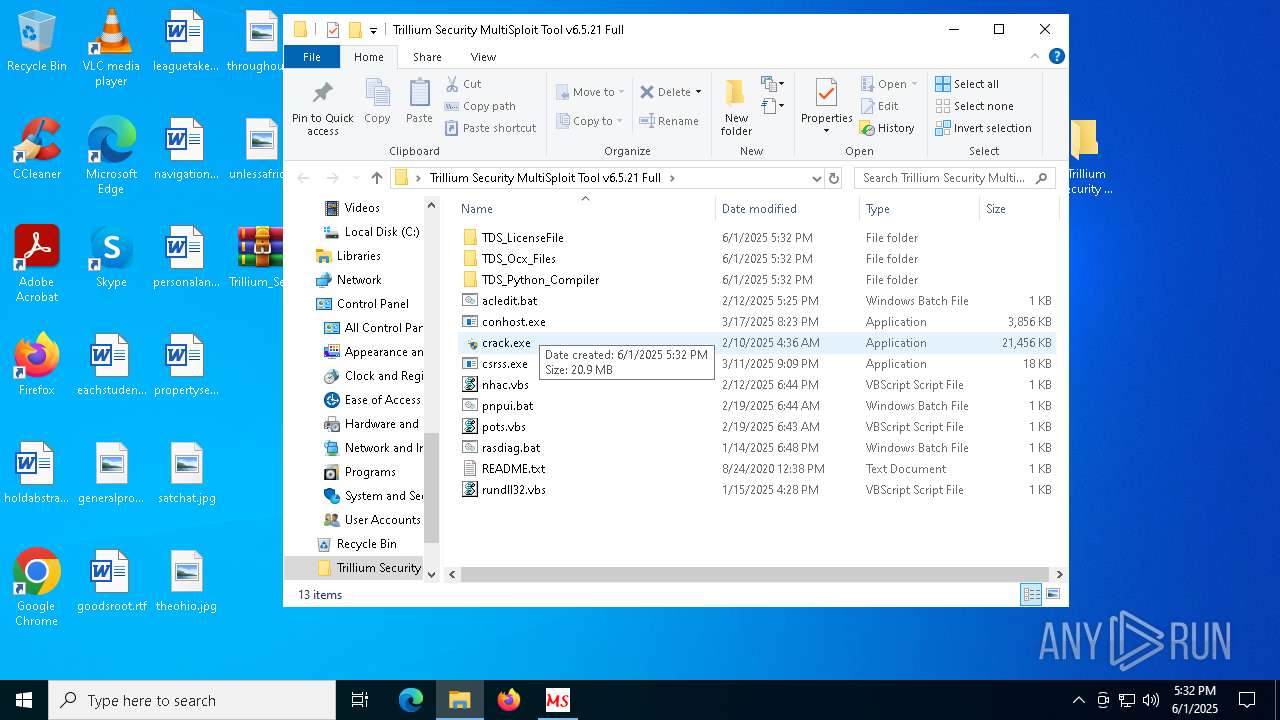
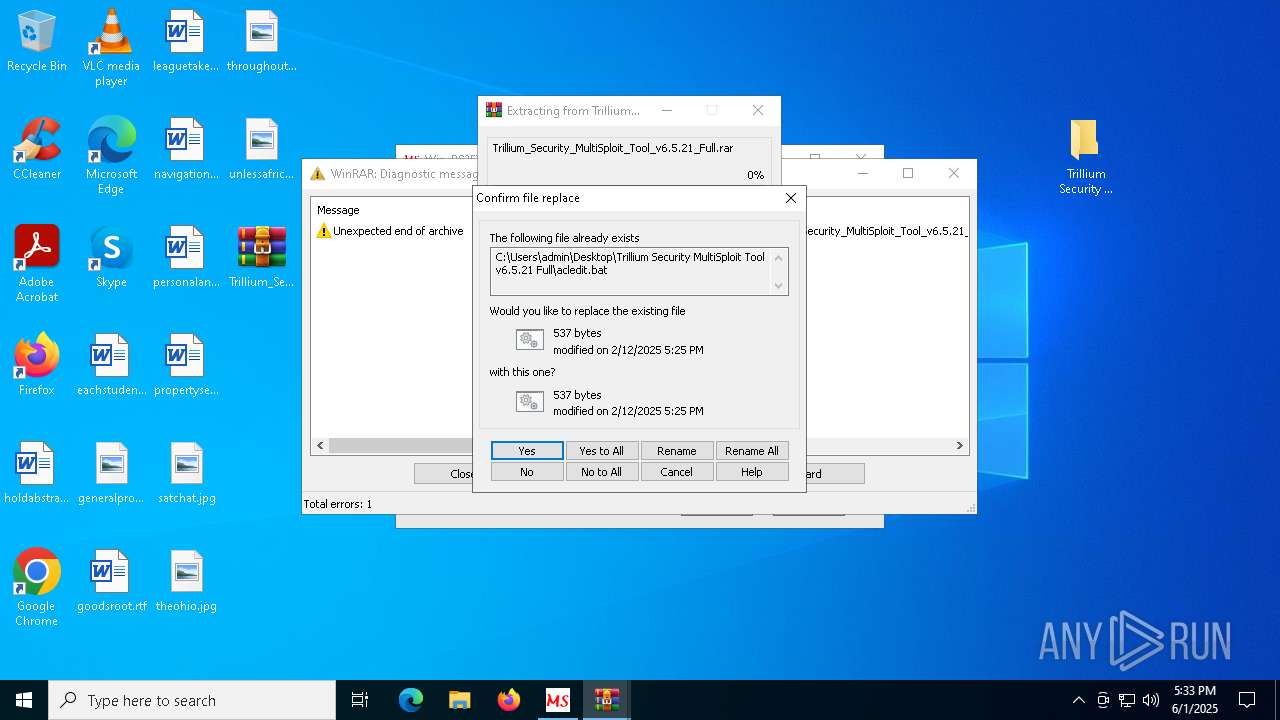
The process creates files with name similar to system file names
- WinRAR.exe (PID: 8028)
Process drops python dynamic module
- WinRAR.exe (PID: 8028)
Process drops legitimate windows executable
- WinRAR.exe (PID: 8028)
INFO
Checks supported languages
- Win-PS2EXE.exe (PID: 1176)
Reads the computer name
- Win-PS2EXE.exe (PID: 1176)
Manual execution by a user
- WinRAR.exe (PID: 8028)
- WinRAR.exe (PID: 6132)
- WinRAR.exe (PID: 2092)
Reads the software policy settings
- slui.exe (PID: 6584)
- slui.exe (PID: 4008)
Reads the machine GUID from the registry
- Win-PS2EXE.exe (PID: 1176)
Checks proxy server information
- slui.exe (PID: 4008)
The sample compiled with english language support
- WinRAR.exe (PID: 8028)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8028)
The sample compiled with german language support
- WinRAR.exe (PID: 8028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:09:26 14:30:36+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 26112 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x846e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.1.2 |
| ProductVersionNumber: | 1.0.1.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
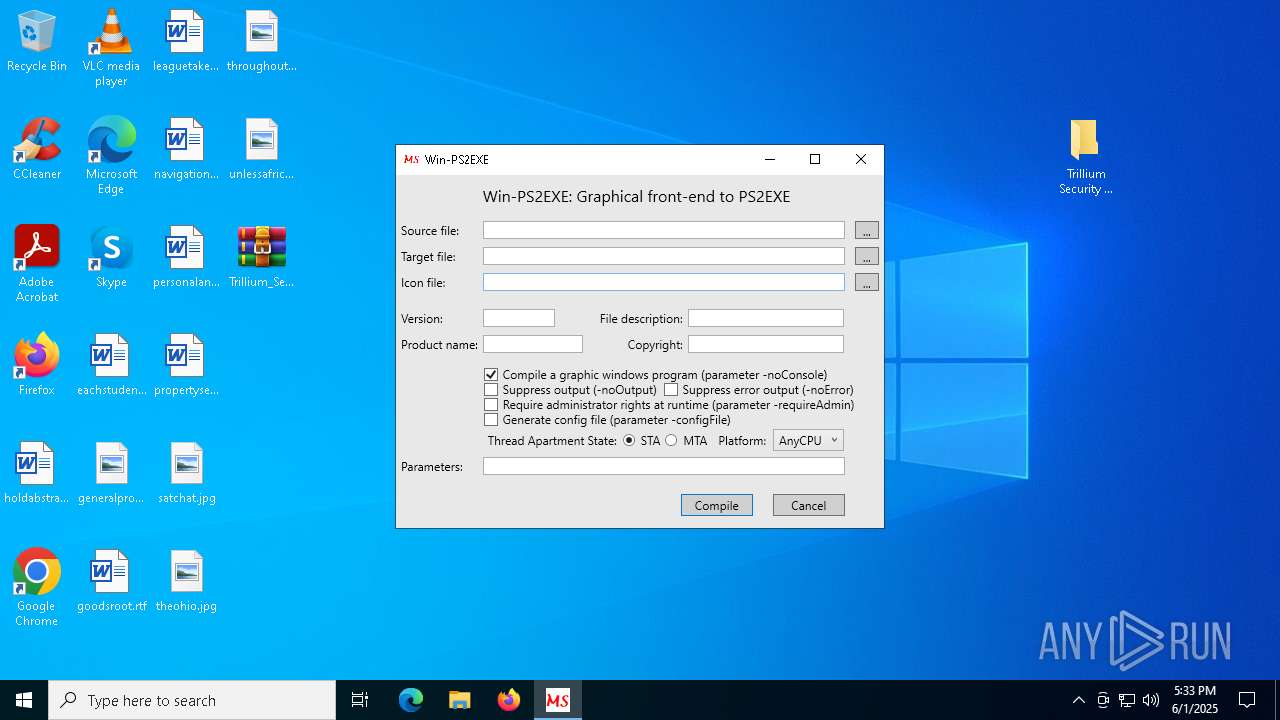
| Comments: | Graphical front end to Invoke-PS2EXE |
| CompanyName: | MS |
| FileDescription: | Graphical front end to Invoke-PS2EXE |
| FileVersion: | 1.0.1.2 |
| InternalName: | Win-PS2EXE.exe |
| LegalCopyright: | © Markus Scholtes 2023 |
| OriginalFileName: | Win-PS2EXE.exe |
| ProductName: | Win-PS2EXE |
| ProductVersion: | 1.0.1.2 |
| AssemblyVersion: | 1.0.1.2 |
Total processes
136
Monitored processes
8
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
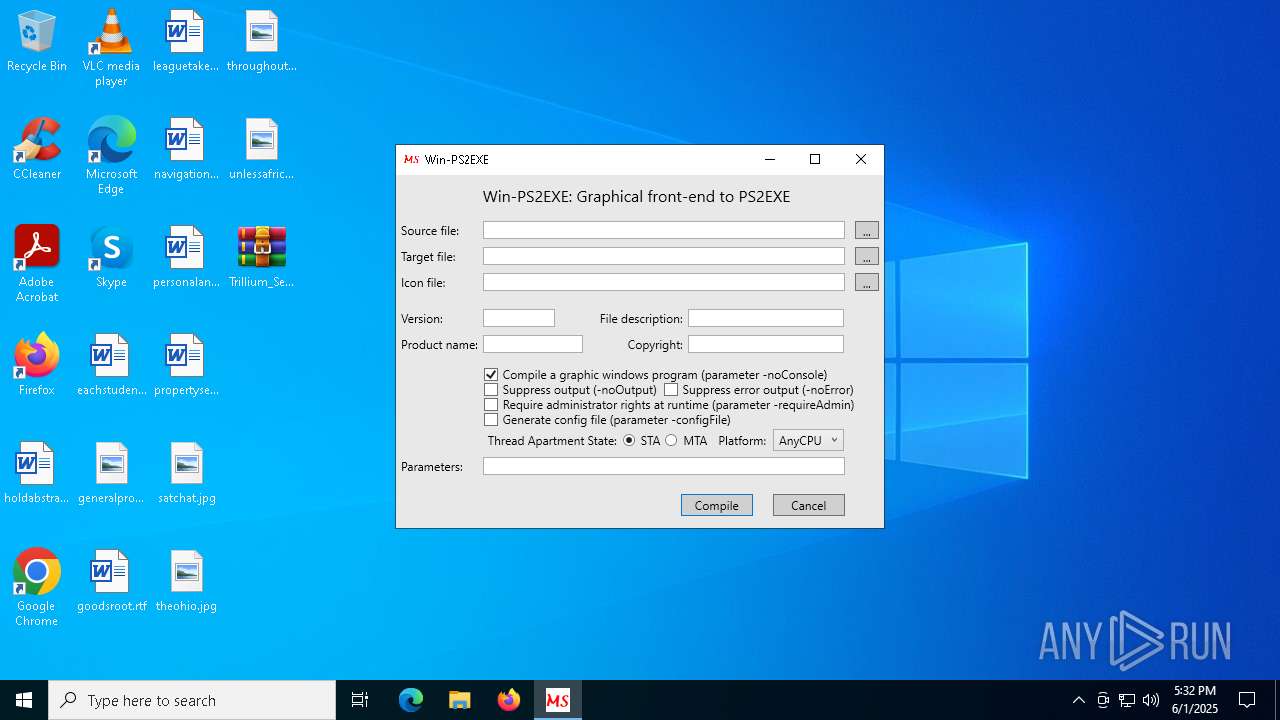
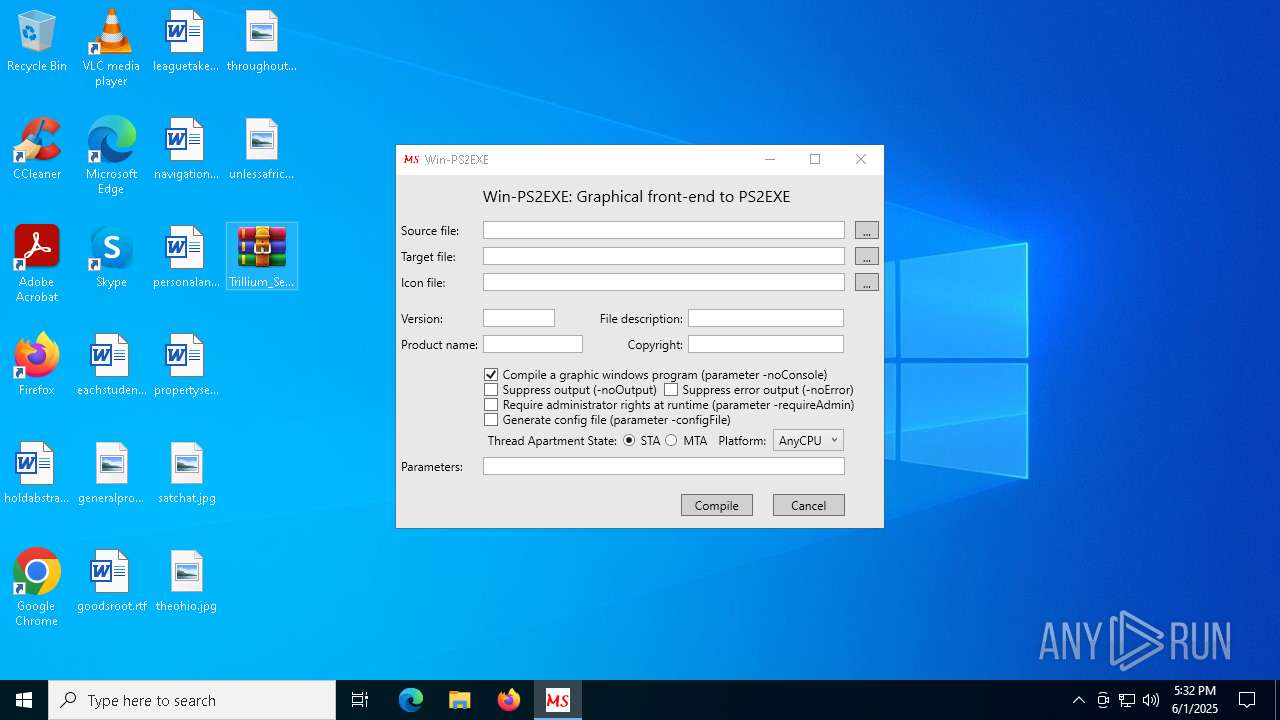
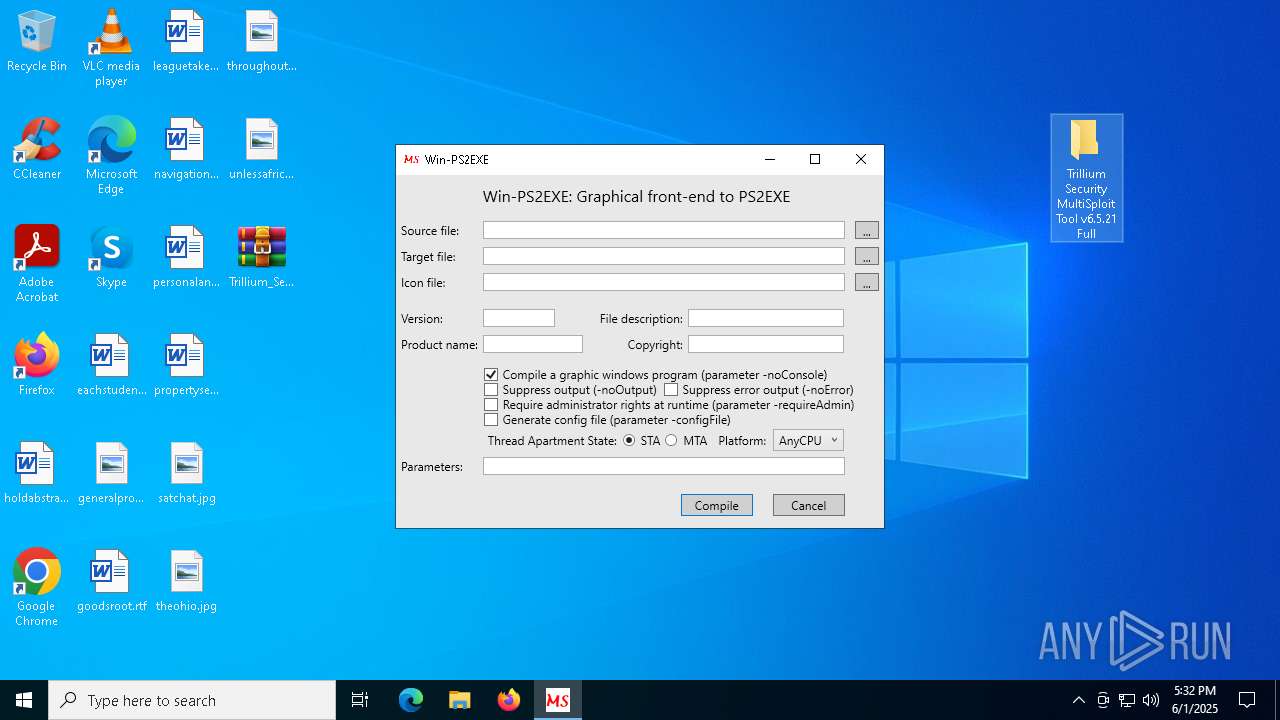
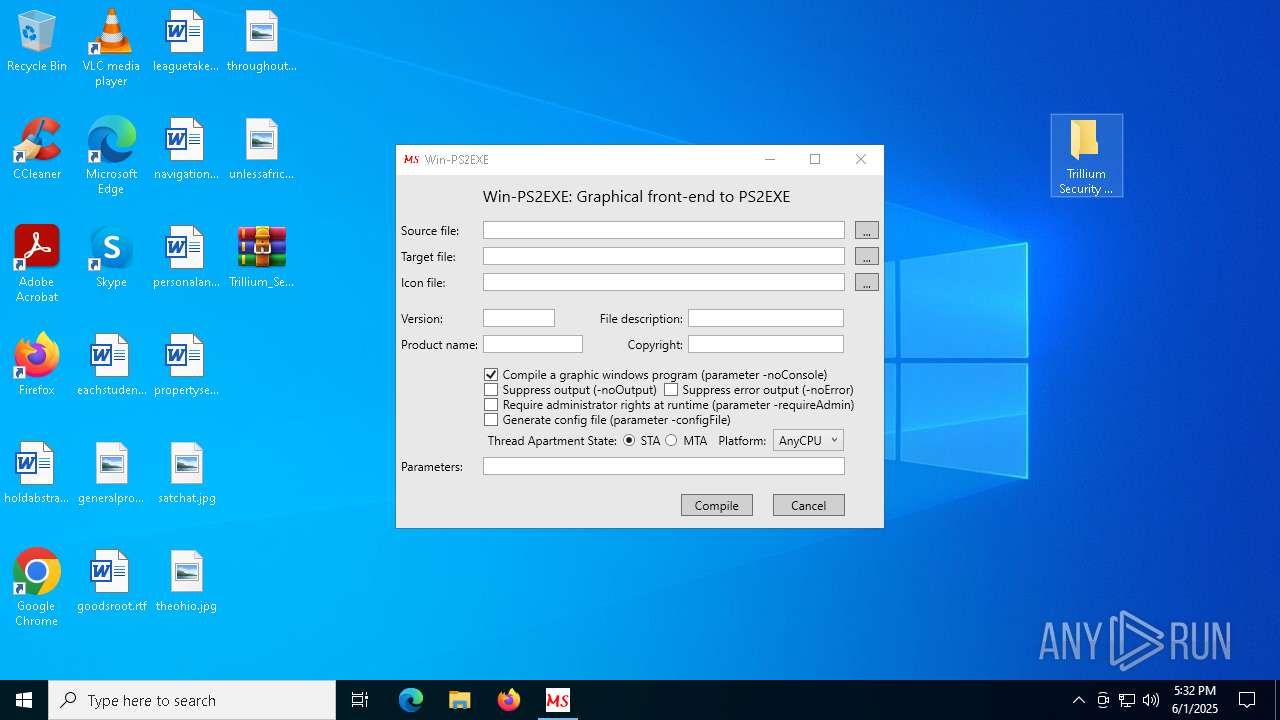
| 1176 | "C:\Users\admin\AppData\Local\Temp\Win-PS2EXE.exe" | C:\Users\admin\AppData\Local\Temp\Win-PS2EXE.exe | — | explorer.exe | |||||||||||
User: admin Company: MS Integrity Level: MEDIUM Description: Graphical front end to Invoke-PS2EXE Version: 1.0.1.2 Modules
| |||||||||||||||
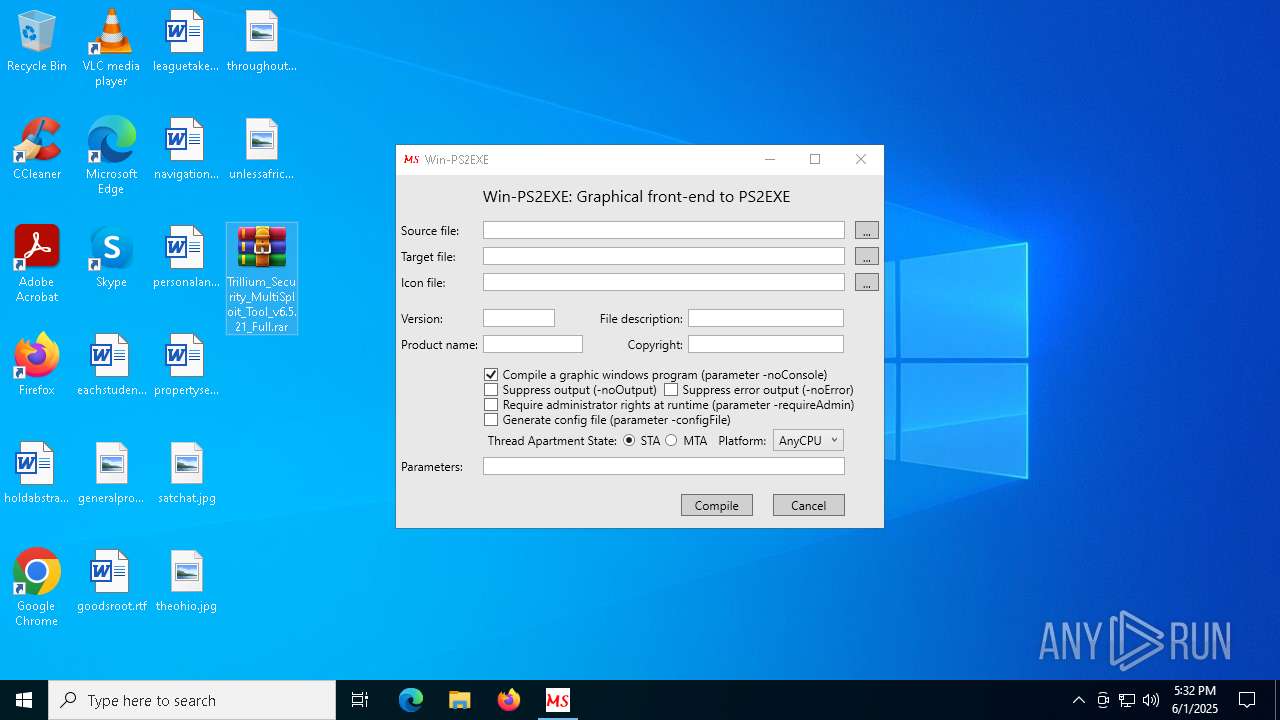
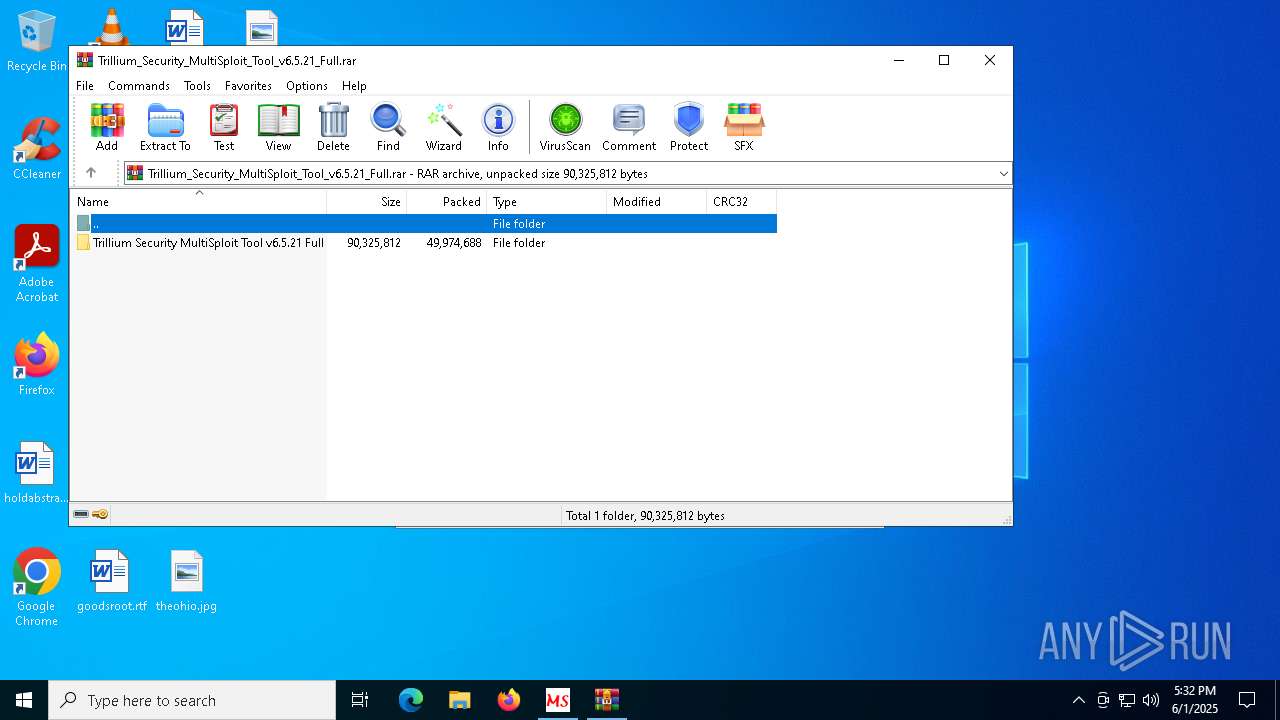
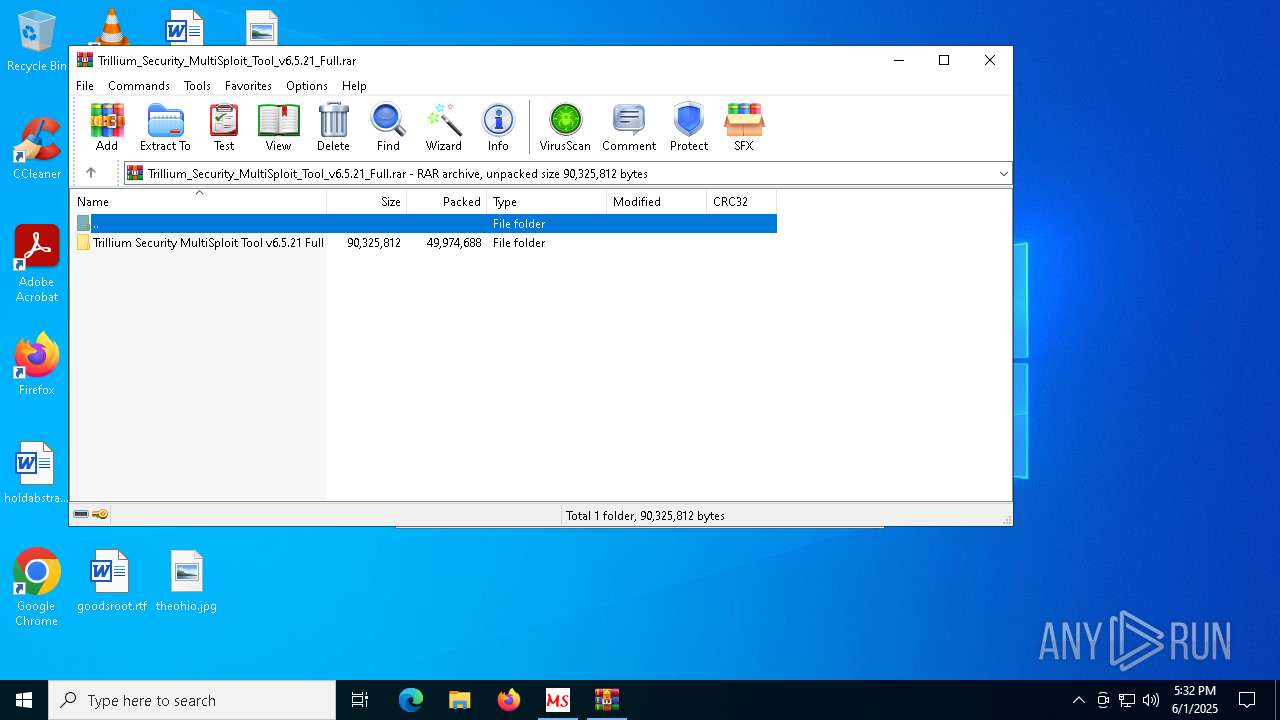
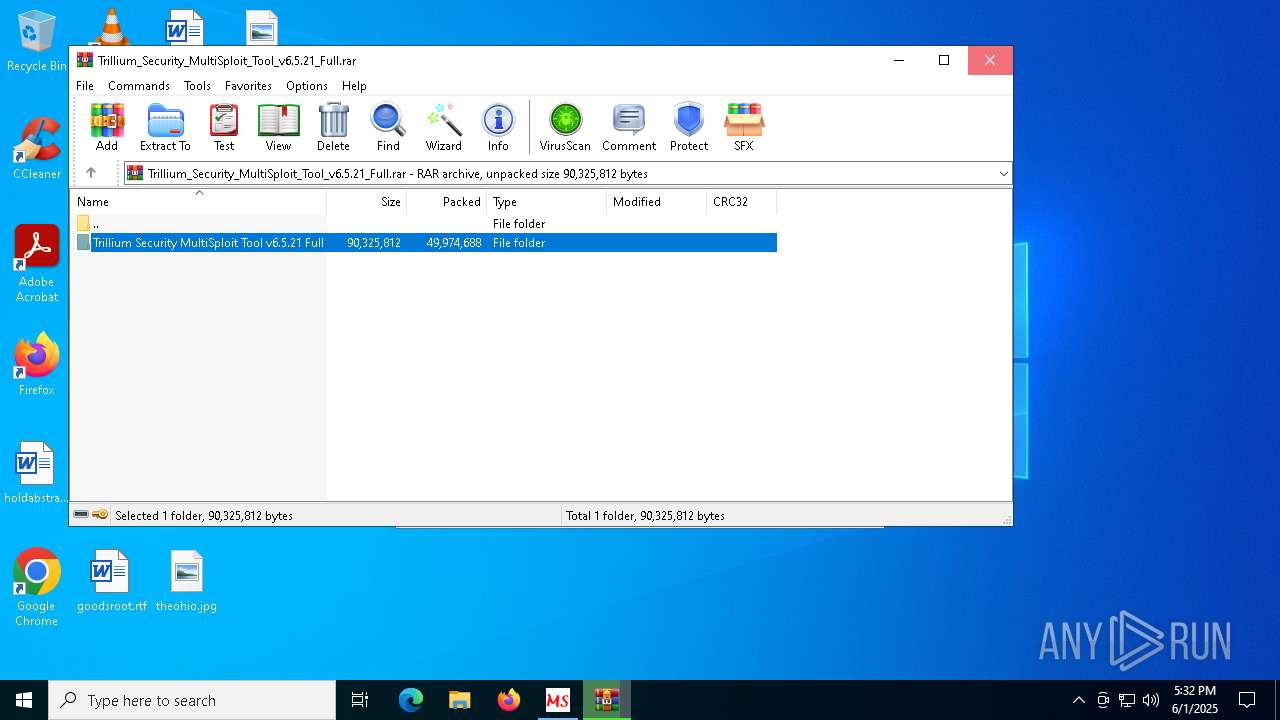
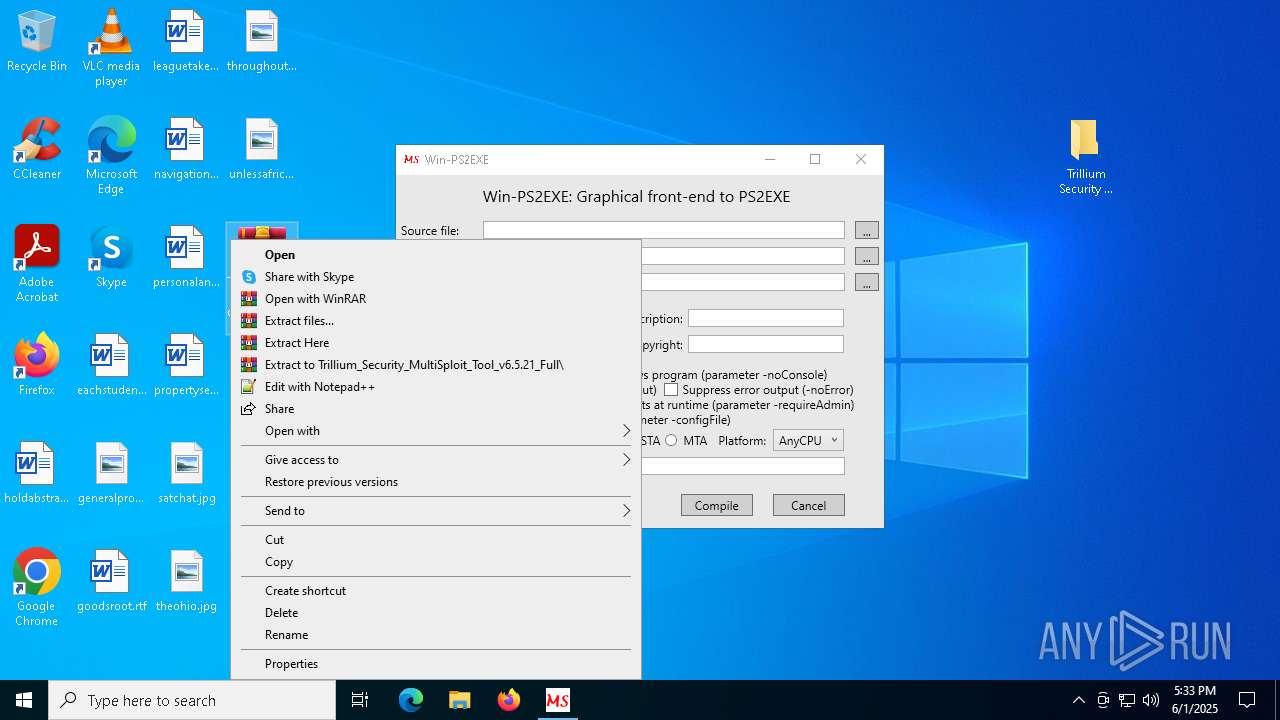
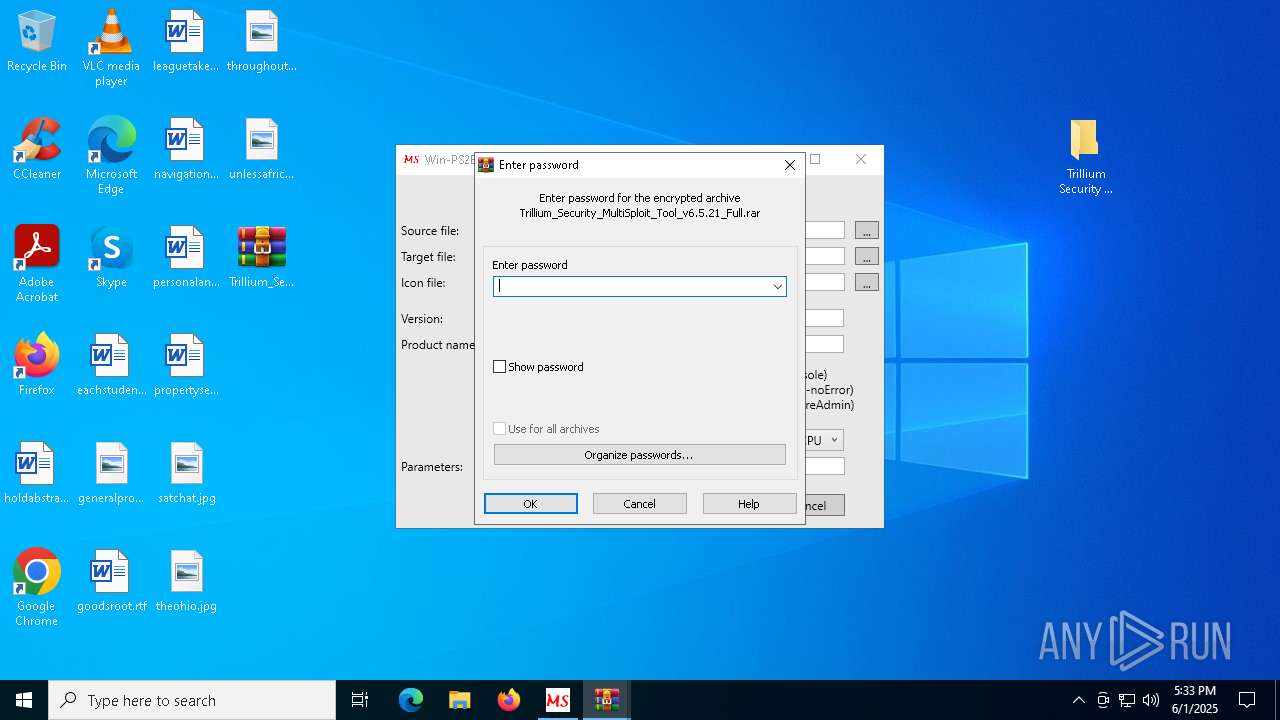
| 2092 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Trillium_Security_MultiSploit_Tool_v6.5.21_Full.rar" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4008 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6072 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 6132 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Trillium_Security_MultiSploit_Tool_v6.5.21_Full.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6584 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7572 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8028 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Trillium_Security_MultiSploit_Tool_v6.5.21_Full.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
4 114
Read events
4 078
Write events
36
Delete events
0
Modification events
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Trillium_Security_MultiSploit_Tool_v6.5.21_Full.rar | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
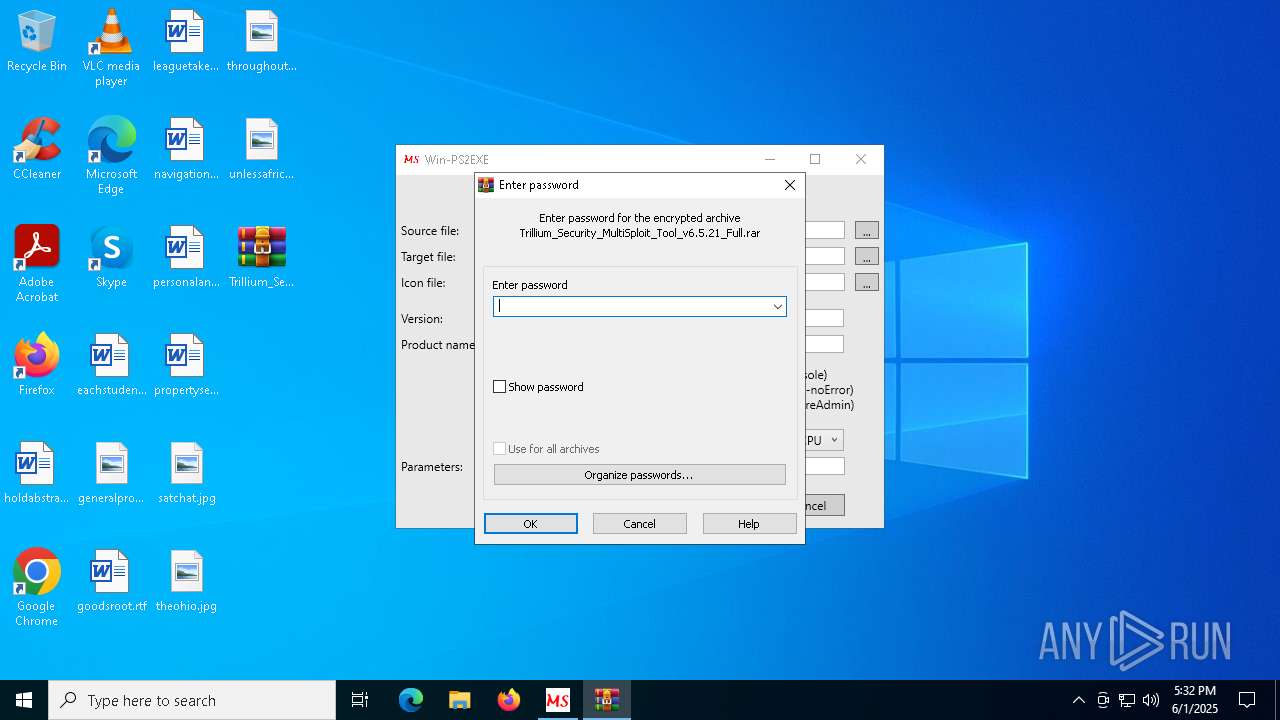
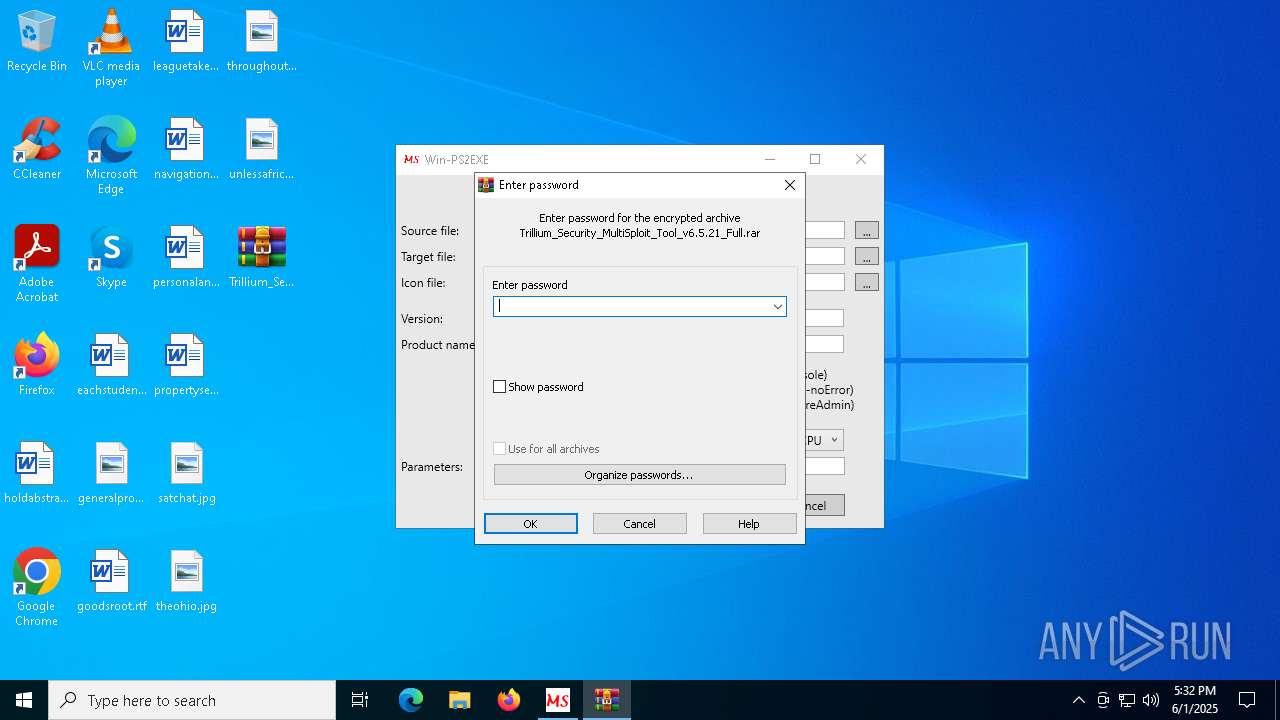
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
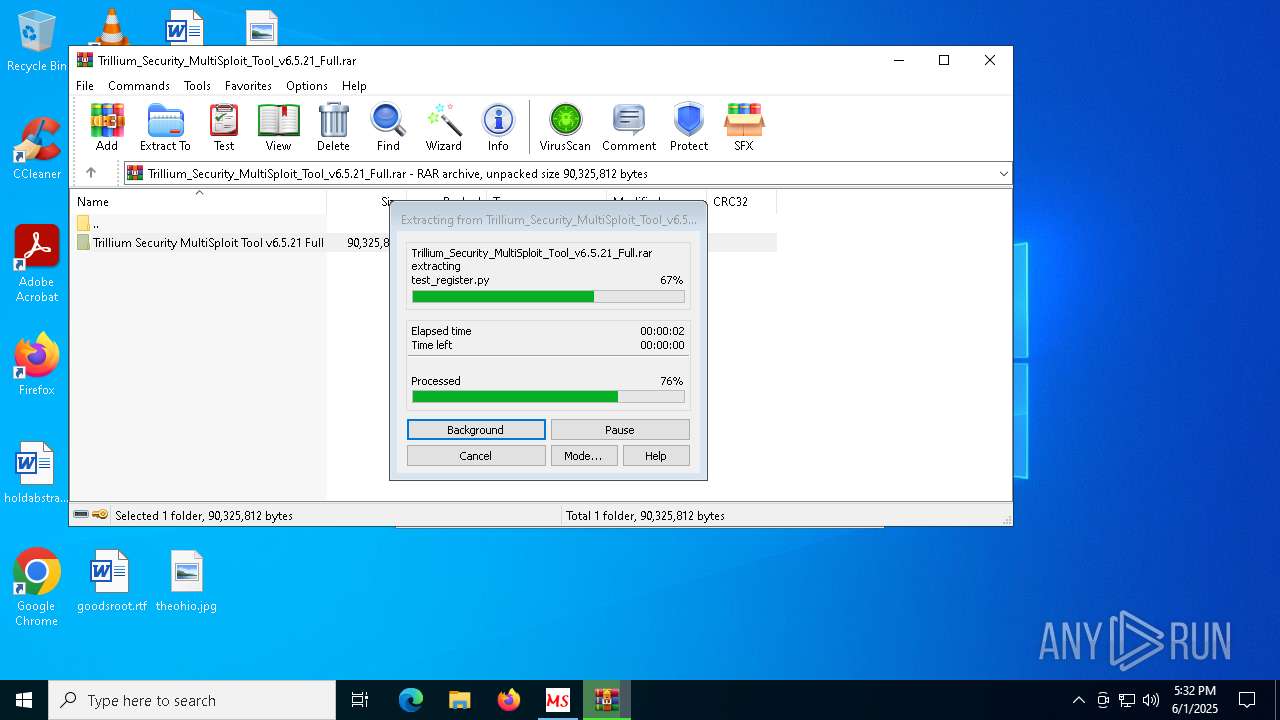
Executable files
36
Suspicious files
92
Text files
391
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\acledit.bat | text | |
MD5:3B33446A78CFF74B5FB4E9A19599D174 | SHA256:85CB802D09069E128067E809F25AC0850EC356DE280E67F1DC44469025ECF621 | |||
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\conhost.exe | executable | |
MD5:4964C1751F6DB917B5C285338EFC4687 | SHA256:6353B1218561A746BB3E009B611A1945BC2367B4D3FFEF7849D4AF4D369F184C | |||
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\TDS_Ocx_Files\Codejock.CommandBars.Unicode.v15.2.1.ocx | executable | |
MD5:B4379ADDC623DE30530471F91072921D | SHA256:0EB80EC5D996FB90B93FE8306CED53EE4CA67CA8A767C1693205296775C4E2A7 | |||
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\TDS_Ocx_Files\Codejock.Controls.Unicode.v15.2.1.ocx | executable | |
MD5:0C6C023BD2EFD2D1BEB322DA33326301 | SHA256:70F64D6AFA9299FF84C1A4BC8F11B07B17E7C75C1FF4E21981300608D4775CC1 | |||
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\TDS_Ocx_Files\RICHTX32.OCX | executable | |
MD5:045A16822822426C305EA7280270A3D6 | SHA256:318CC48CBCFABA9592956E4298886823CC5F37626C770D6DADBCD224849680C5 | |||
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\TDS_Ocx_Files\MSCOMCTL.OCX | executable | |
MD5:F7BBB7D79ADB9E3ADC13F3B3C33D3D4D | SHA256:18A83D7A420A17FCB6F56EB3BA5362C975D32E5DED7553C6FD407F07BDB7B006 | |||
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\TDS_Ocx_Files\MSWINSCK.OCX | executable | |
MD5:9484C04258830AA3C2F2A70EB041414C | SHA256:BF7E47C16D7E1C0E88534F4EF95E09D0FD821ED1A06B0D95A389B35364B63FF5 | |||
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\TDS_Ocx_Files\Trillium_Security_OCX_Registrator.exe | executable | |
MD5:0732C318475AD1197E9B4191B912A514 | SHA256:B2E7D11309C60AEF82B52F3244C14BBC999905B6A25EE3E127D55F463C4C2482 | |||
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\TDS_Python_Compiler\Python27\DLLs\bz2.pyd | executable | |
MD5:43D5EA96E94B44E0FBEBB13EABD3AA78 | SHA256:5C577A784C00A099CFDB2C0CE05C5A46612D5B36BC4E5158CE34BA58355B1CDB | |||
| 8028 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8028.47508\Trillium Security MultiSploit Tool v6.5.21 Full\TDS_Python_Compiler\Python27\DLLs\py.ico | image | |
MD5:79FB3436099FE00487BC874FD0313D13 | SHA256:AE74EB8119AA88532734A84DD782830F8F5CB4DFF01CFA4372B1E4AFA3565313 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
35
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3096 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3096 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7512 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7548 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |