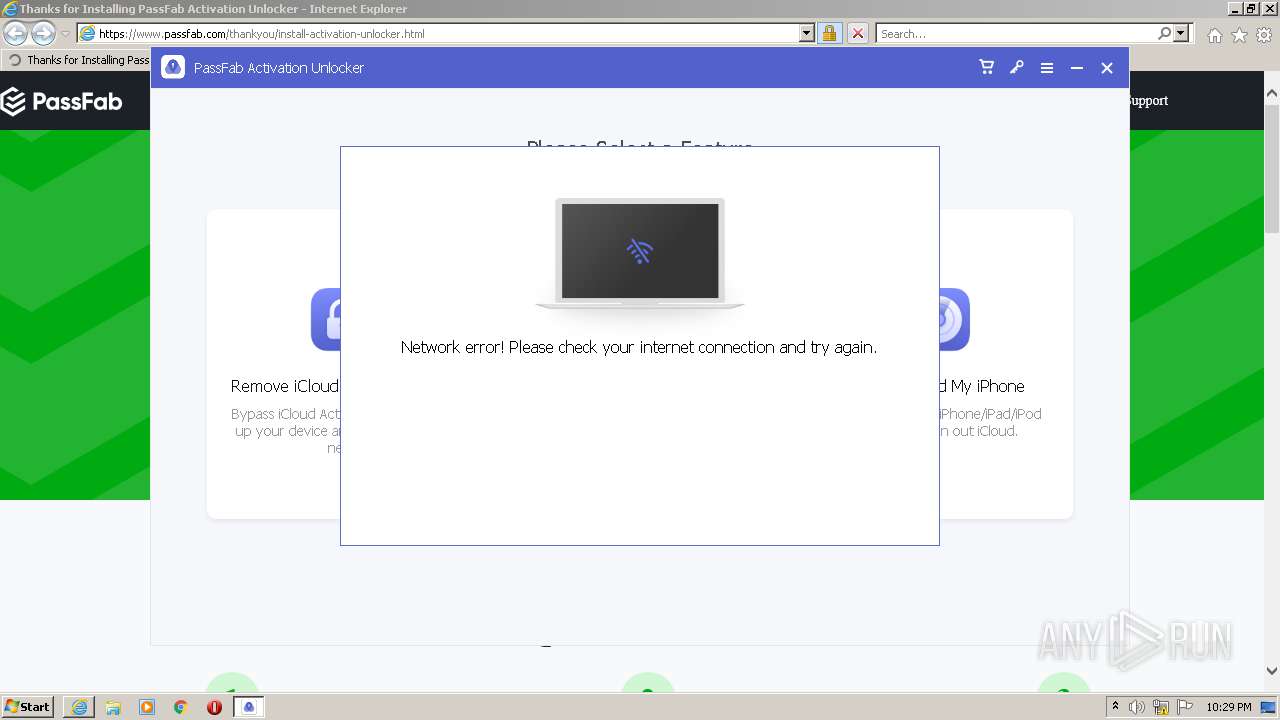
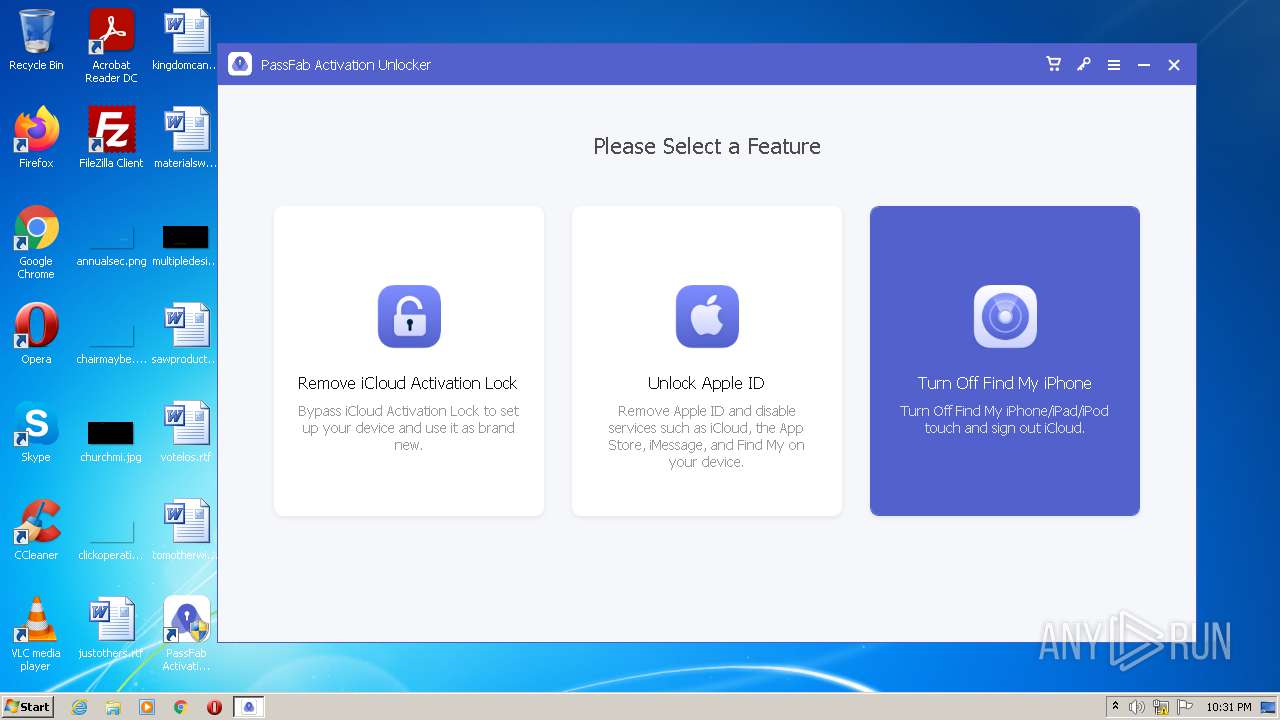
| URL: | https://www.passfab.com/products/remove-activation-lock.html |
| Full analysis: | https://app.any.run/tasks/0920f450-9178-4315-8c3c-1f34ad612c50 |
| Verdict: | Malicious activity |
| Analysis date: | October 10, 2021, 21:27:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5744DE64F49B7369D9FDF372FD97D7F8 |
| SHA1: | F49F619F2BCB9D064248CF4EE6EAF13AFA5DFDE6 |
| SHA256: | 89509DFAB41345A220BFDA36ACE69EDC97D4366004BA2A63A0DD515AC8FD37AE |
| SSDEEP: | 3:N8DSLoDErdIKVXaQGRWMf5sLqO8:2OLowKKQRW0qq |
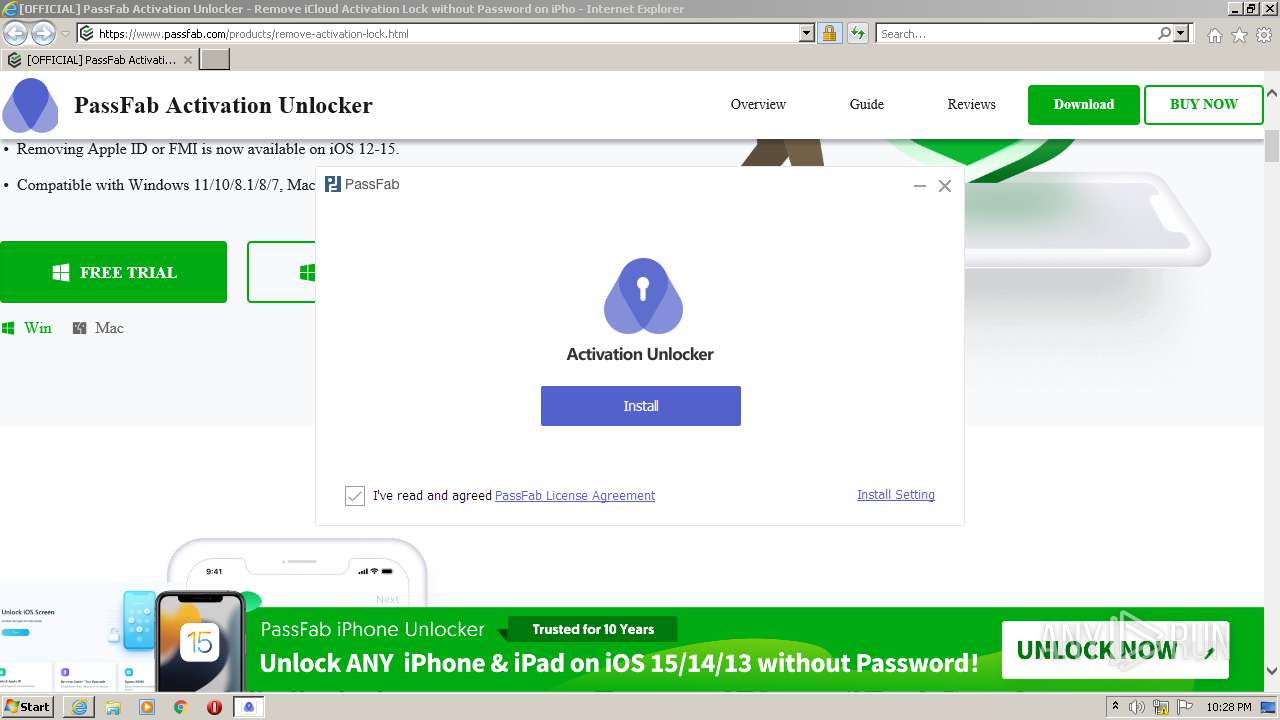
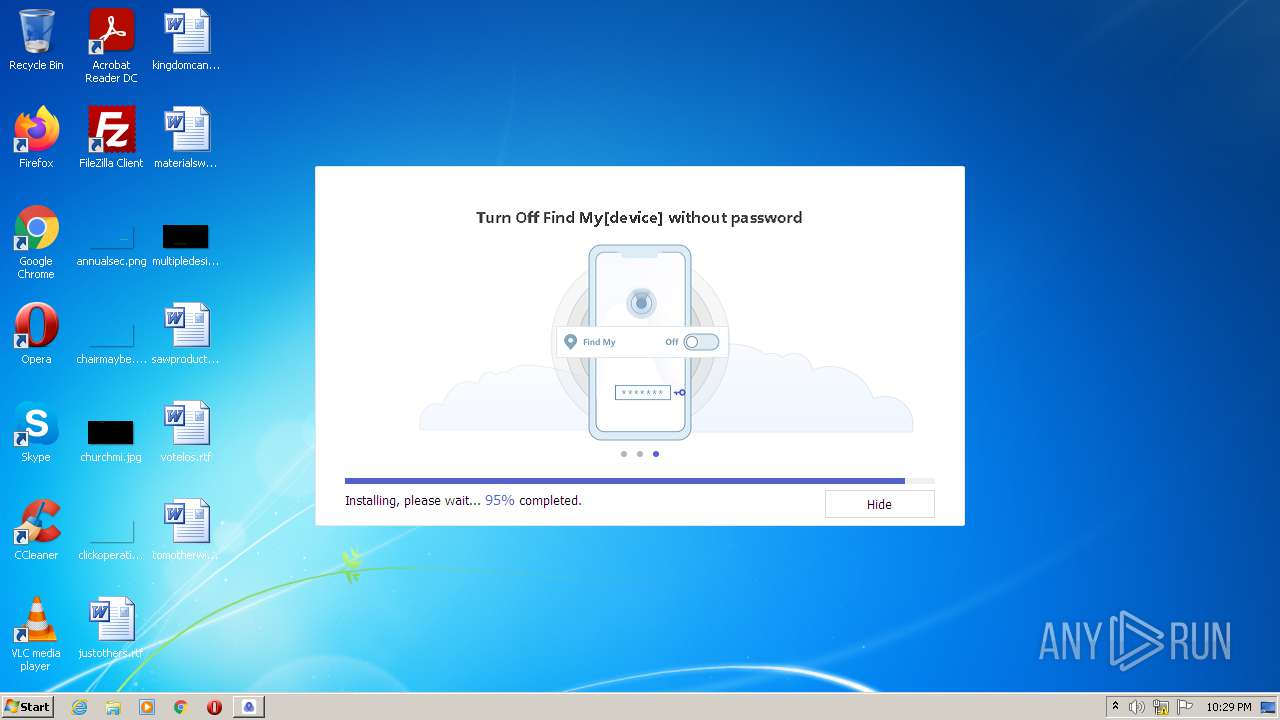
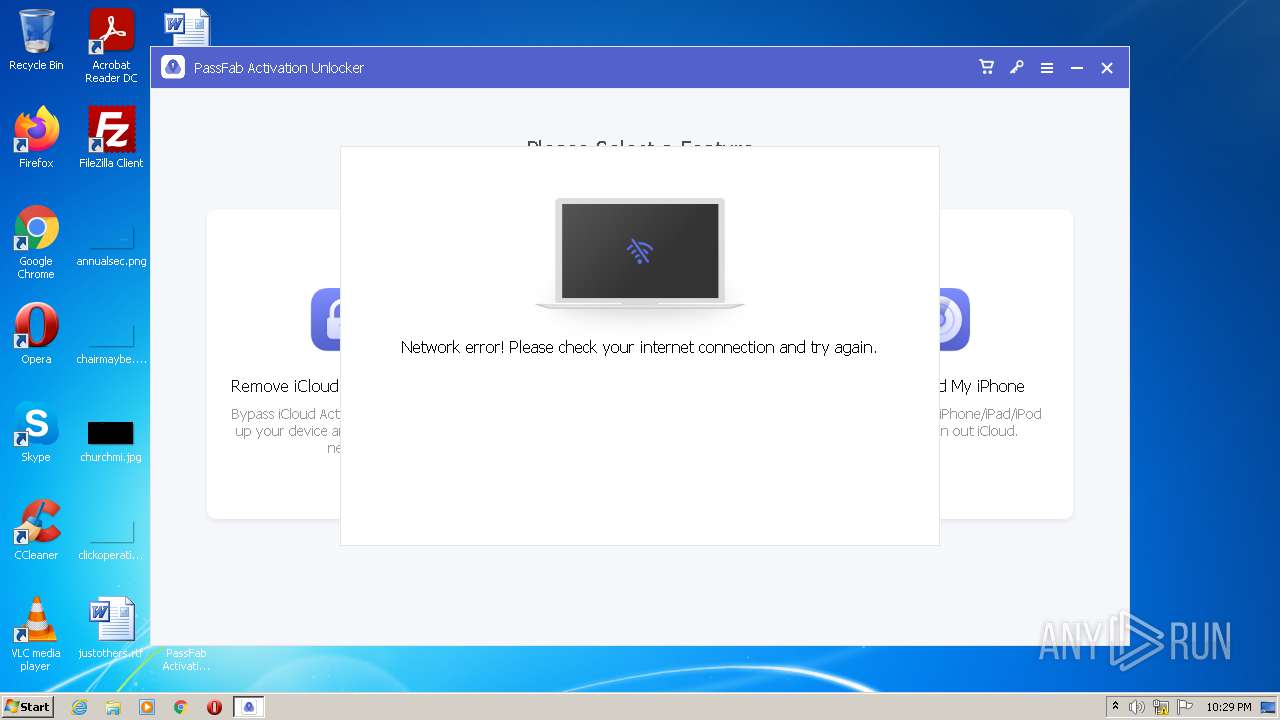
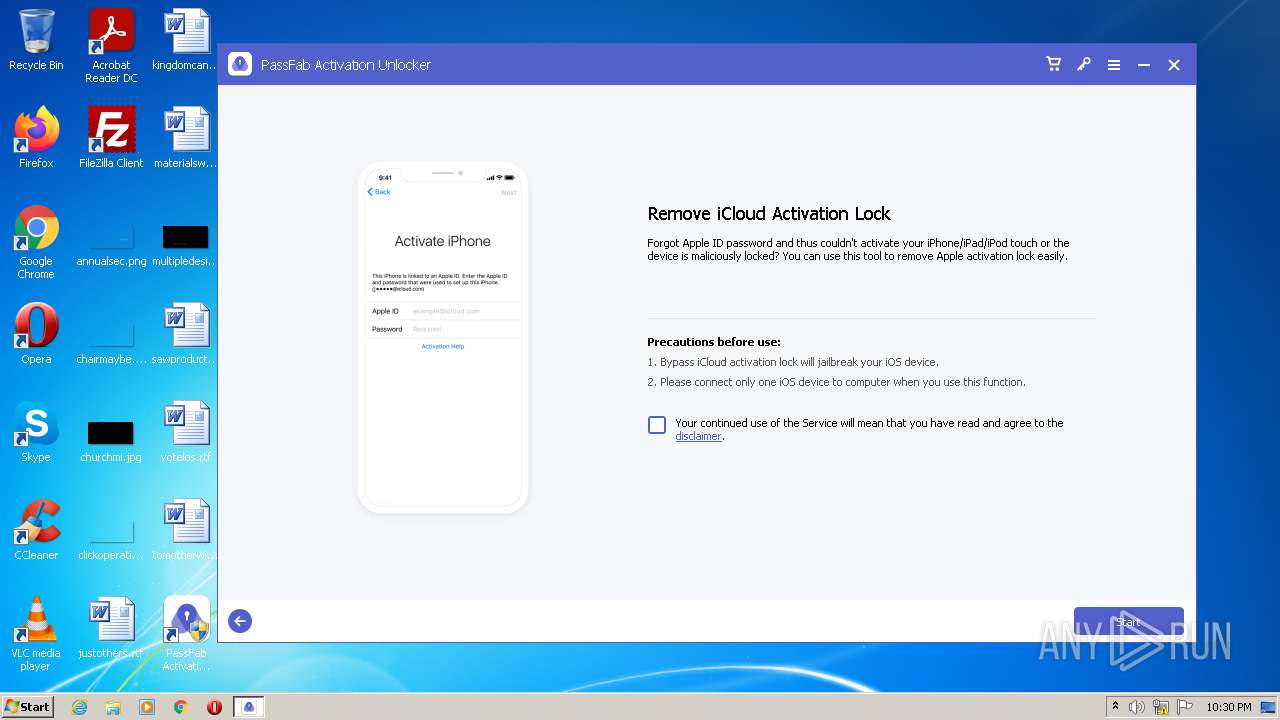
MALICIOUS
Application was dropped or rewritten from another process
- activation-unlocker.exe (PID: 2884)
- activation-unlocker.exe (PID: 2468)
- NetFrameCheck.exe (PID: 2420)
- Monitor.exe (PID: 2680)
- NetFrameCheck.exe (PID: 2116)
- NetFrameCheck.exe (PID: 2420)
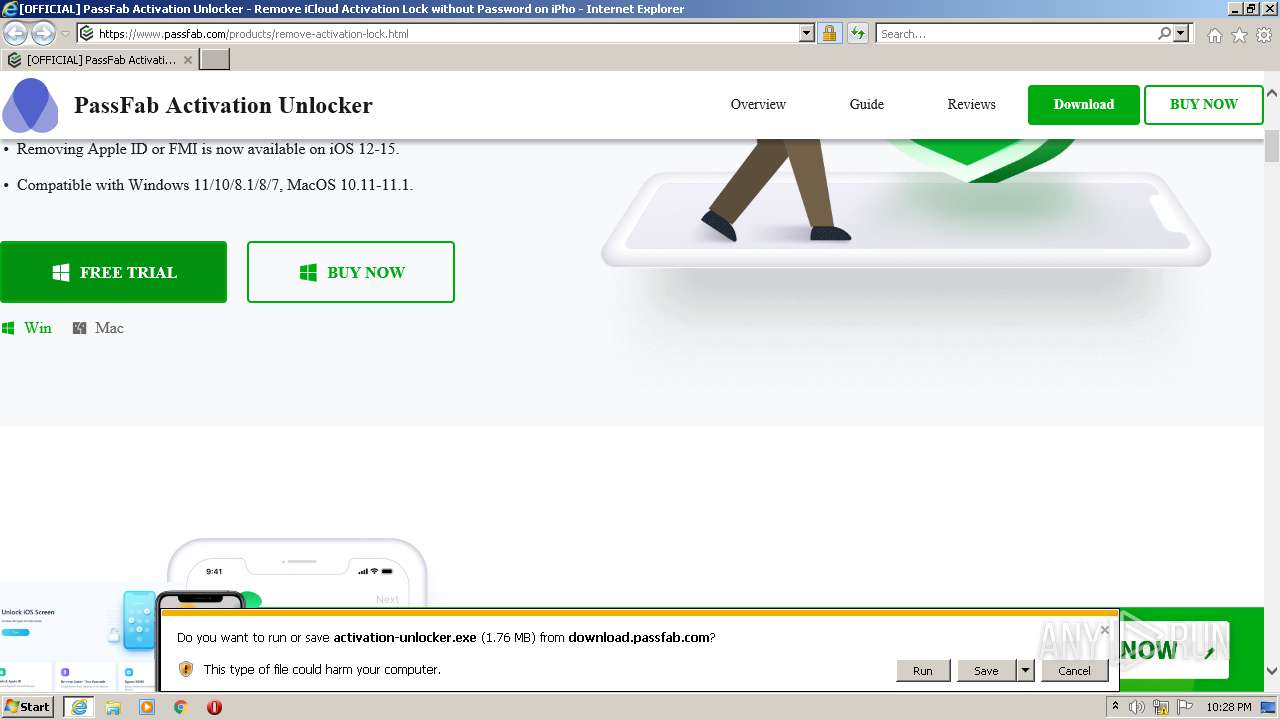
Drops executable file immediately after starts
- 4mekey_passfab3.0.4.exe (PID: 1036)
- 4mekey_passfab3.0.4.tmp (PID: 2972)
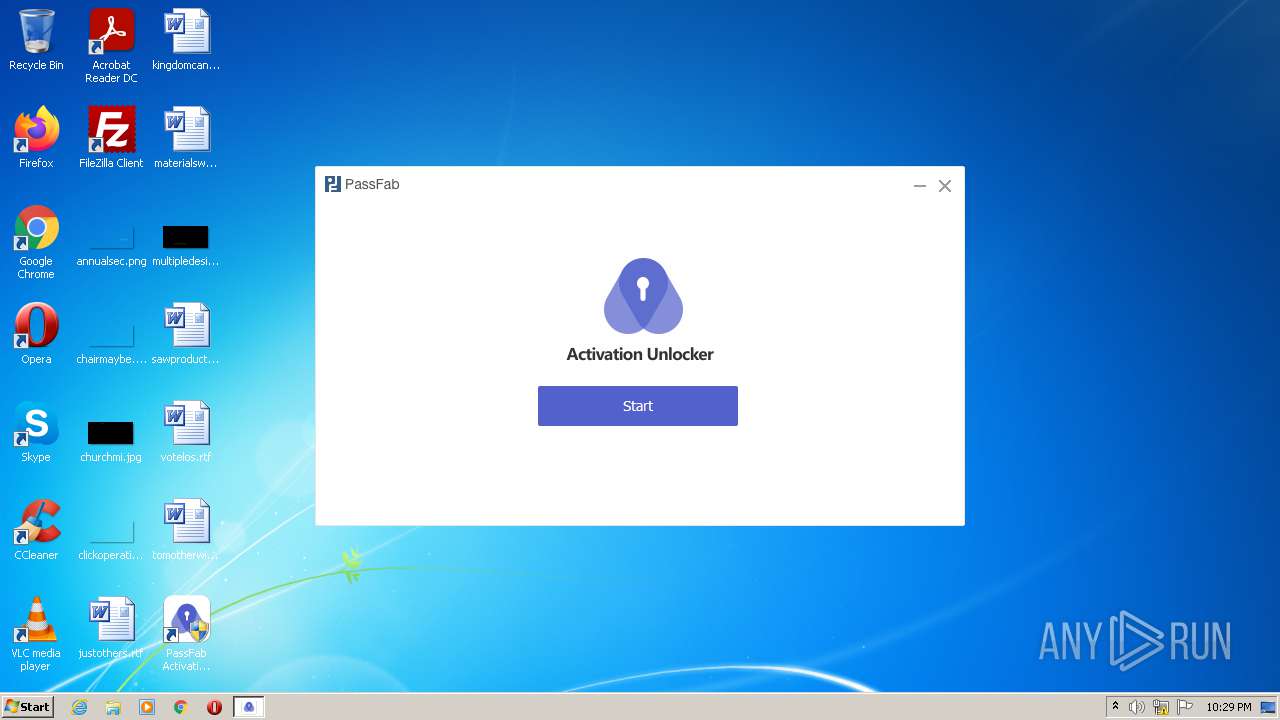
Loads dropped or rewritten executable
- PassFab Activation Unlocker.exe (PID: 3428)
- Monitor.exe (PID: 2680)
- PassFab Activation Unlocker.exe (PID: 3044)
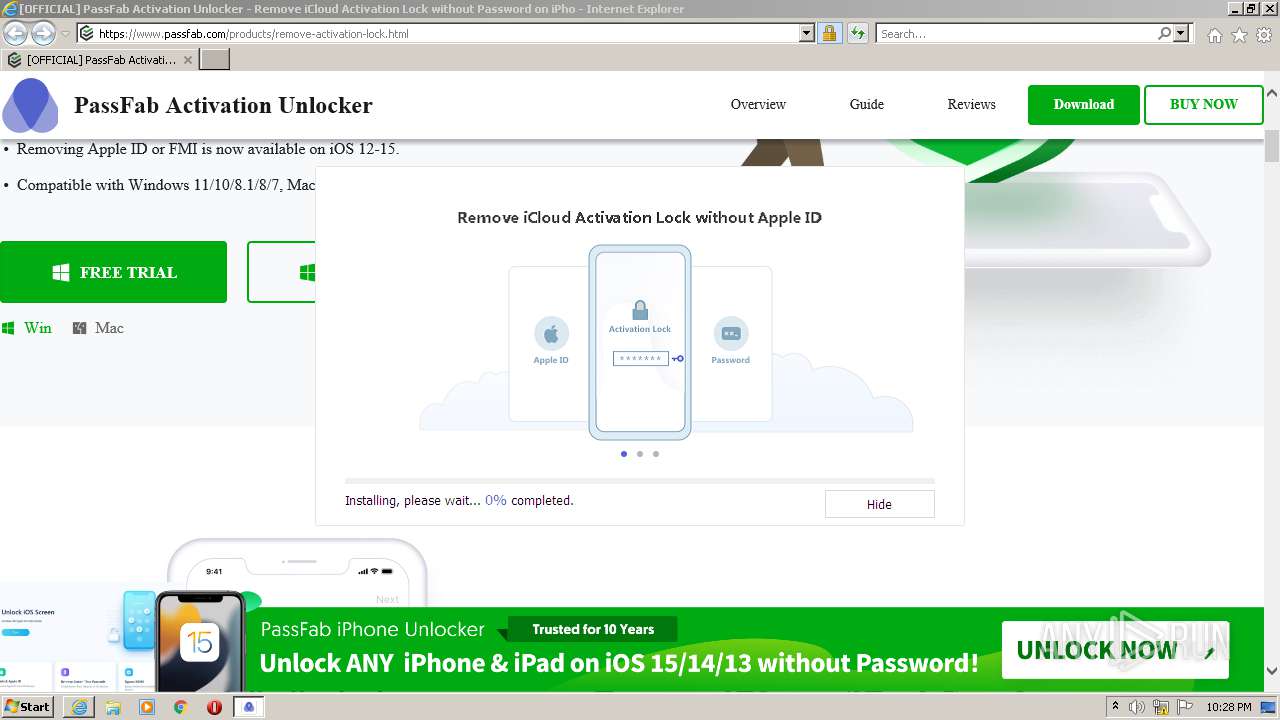
Changes Windows auto-update feature
- PassFab Activation Unlocker.exe (PID: 3428)
Disables Windows Defender
- PassFab Activation Unlocker.exe (PID: 3428)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 2520)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 4072)
- 4mekey_passfab3.0.4.exe (PID: 1036)
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Checks for external IP
- activation-unlocker.exe (PID: 2884)
Checks supported languages
- activation-unlocker.exe (PID: 2884)
- 4mekey_passfab3.0.4.exe (PID: 1036)
- 4mekey_passfab3.0.4.tmp (PID: 2972)
- NetFrameCheck.exe (PID: 2420)
- PassFab Activation Unlocker.exe (PID: 3428)
- Monitor.exe (PID: 2680)
- NetFrameCheck.exe (PID: 2420)
- PassFab Activation Unlocker.exe (PID: 3044)
Creates a directory in Program Files
- activation-unlocker.exe (PID: 2884)
- 4mekey_passfab3.0.4.tmp (PID: 2972)
- PassFab Activation Unlocker.exe (PID: 3428)
Reads Windows owner or organization settings
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Reads the computer name
- activation-unlocker.exe (PID: 2884)
- 4mekey_passfab3.0.4.tmp (PID: 2972)
- NetFrameCheck.exe (PID: 2420)
- PassFab Activation Unlocker.exe (PID: 3428)
- Monitor.exe (PID: 2680)
- NetFrameCheck.exe (PID: 2420)
- PassFab Activation Unlocker.exe (PID: 3044)
Creates files in the user directory
- activation-unlocker.exe (PID: 2884)
- PassFab Activation Unlocker.exe (PID: 3428)
Reads the Windows organization settings
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Drops a file with too old compile date
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Drops a file with a compile date too recent
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Creates a software uninstall entry
- activation-unlocker.exe (PID: 2884)
- PassFab Activation Unlocker.exe (PID: 3428)
Creates files in the program directory
- NetFrameCheck.exe (PID: 2420)
- PassFab Activation Unlocker.exe (PID: 3428)
Reads Environment values
- PassFab Activation Unlocker.exe (PID: 3428)
- PassFab Activation Unlocker.exe (PID: 3044)
Searches for installed software
- PassFab Activation Unlocker.exe (PID: 3428)
Drops a file that was compiled in debug mode
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Changes IE settings (feature browser emulation)
- PassFab Activation Unlocker.exe (PID: 3428)
Starts Internet Explorer
- PassFab Activation Unlocker.exe (PID: 3428)
INFO
Changes internet zones settings
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 2316)
Reads the computer name
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 2316)
- iexplore.exe (PID: 2520)
- WISPTIS.EXE (PID: 2964)
Checks supported languages
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 2316)
- iexplore.exe (PID: 2520)
- WISPTIS.EXE (PID: 2964)
Reads settings of System Certificates
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 2304)
- activation-unlocker.exe (PID: 2884)
- iexplore.exe (PID: 2520)
- PassFab Activation Unlocker.exe (PID: 3428)
Creates files in the user directory
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 2520)
Application launched itself
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 2316)
Reads internet explorer settings
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 2520)
Checks Windows Trust Settings
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 4072)
- activation-unlocker.exe (PID: 2884)
- iexplore.exe (PID: 2520)
- PassFab Activation Unlocker.exe (PID: 3428)
Modifies the phishing filter of IE
- iexplore.exe (PID: 4072)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 2520)
Changes settings of System certificates
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 2520)
Reads the date of Windows installation
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 2316)
Application was dropped or rewritten from another process
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Creates a software uninstall entry
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Dropped object may contain Bitcoin addresses
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Creates files in the program directory
- 4mekey_passfab3.0.4.tmp (PID: 2972)
Manual execution by user
- NetFrameCheck.exe (PID: 2116)
- NetFrameCheck.exe (PID: 2420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
16
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | /VERYSILENT /SP- /NORESTART /DIR="C:\Program Files\PassFab\PassFab Activation Unlocker\" /LANG=en /LOG="C:\Users\admin\AppData\Local\Temp\PassFab Activation Unlocker_Setup_20211010222858.log" | C:\Users\admin\AppData\Local\Temp\4mekey_passfab\4mekey_passfab3.0.4.exe | activation-unlocker.exe | ||||||||||||
User: admin Company: Tenorshare, Inc. Integrity Level: HIGH Description: PassFab Activation Unlocker Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1208 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | PassFab Activation Unlocker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2116 | "C:\Program Files\PassFab\PassFab Activation Unlocker\NetFrameCheck.exe" | C:\Program Files\PassFab\PassFab Activation Unlocker\NetFrameCheck.exe | — | Explorer.EXE | |||||||||||
User: admin Company: PassFab Integrity Level: MEDIUM Description: PassFab Activation Unlocker Exit code: 3221226540 Version: 2.0.0.1 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4072 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Internet Explorer\iexplore.exe" http://cbs.passfab.com/go?pid=2424&a=i&v=3.0.4 | C:\Program Files\Internet Explorer\iexplore.exe | — | PassFab Activation Unlocker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2420 | "C:\Program Files\PassFab\PassFab Activation Unlocker\NetFrameCheck.exe" | C:\Program Files\PassFab\PassFab Activation Unlocker\NetFrameCheck.exe | — | activation-unlocker.exe | |||||||||||
User: admin Company: PassFab Integrity Level: HIGH Description: PassFab Activation Unlocker Exit code: 0 Version: 2.0.0.1 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\PassFab\PassFab Activation Unlocker\NetFrameCheck.exe" | C:\Program Files\PassFab\PassFab Activation Unlocker\NetFrameCheck.exe | Explorer.EXE | ||||||||||||
User: admin Company: PassFab Integrity Level: HIGH Description: PassFab Activation Unlocker Exit code: 0 Version: 2.0.0.1 Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\activation-unlocker.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\activation-unlocker.exe | — | iexplore.exe | |||||||||||
User: admin Company: PassFab Co., Ltd. Integrity Level: MEDIUM Description: PassFab Activation Unlocker Exit code: 3221226540 Version: 2.5.1.4 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2316 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2680 | "C:\Program Files\PassFab\PassFab Activation Unlocker\Monitor\Monitor.exe" 3428(#-+)UA-167618528-2(#-+)PassFab Activation Unlocker(#-+)3.0.4.3(#-+)&cd1=3.0.4.3&cd2=0&cd3=PF&cd4=EN(#-+)1 | C:\Program Files\PassFab\PassFab Activation Unlocker\Monitor\Monitor.exe | PassFab Activation Unlocker.exe | ||||||||||||
User: admin Company: TS Integrity Level: HIGH Description: Monitor_20210728 Exit code: 0 Version: 1.0.0.10 Modules
| |||||||||||||||
Total events
38 517
Read events
38 048
Write events
427
Delete events
42
Modification events
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30916125 | |||
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30916125 | |||
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
370
Suspicious files
43
Text files
123
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2304 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab4F10.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab4F0E.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar4F0F.tmp | cat | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar4F11.tmp | cat | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 4072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 4072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\AD85261C04F6BA97CCBABAE2EDF85AB4 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
157
DNS requests
41
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2304 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECRXdf7EU7SwCgAAAAD%2FZgs%3D | US | der | 471 b | whitelisted |
2304 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHE9M93bDAqpCgAAAAD%2FYCw%3D | US | der | 471 b | whitelisted |
2304 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDcT7pkfCURlwoAAAAA%2F2RA | US | der | 472 b | whitelisted |
2884 | activation-unlocker.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/csv | unknown | text | 152 b | malicious |
4072 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2884 | activation-unlocker.exe | GET | 301 | 104.18.24.249:80 | http://www.tenorshare.com/downloads/service/softwarelog.txt | US | html | 469 b | whitelisted |
2304 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDWojVyl%2F4MzgoAAAAA%2F2Au | US | der | 472 b | whitelisted |
2304 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2304 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2304 | iexplore.exe | 104.18.25.142:443 | www.passfab.com | Cloudflare Inc | US | unknown |
2304 | iexplore.exe | 8.248.145.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2304 | iexplore.exe | 67.27.158.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2304 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
4072 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4072 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2304 | iexplore.exe | 92.123.224.124:80 | r3.o.lencr.org | Akamai International B.V. | — | unknown |
2304 | iexplore.exe | 142.250.185.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2304 | iexplore.exe | 74.125.133.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2304 | iexplore.exe | 142.250.185.196:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.passfab.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
www.tenorshare.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2884 | activation-unlocker.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
2884 | activation-unlocker.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
2884 | activation-unlocker.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2884 | activation-unlocker.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3428 | PassFab Activation Unlocker.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
PassFab Activation Unlocker.exe | log4net:ERROR XmlHierarchyConfigurator: No appender named [ConsoleAppender] could be found.
|
PassFab Activation Unlocker.exe | log4net:ERROR Appender named [ConsoleAppender] not found.
|
PassFab Activation Unlocker.exe | Note: UAC is active
|
PassFab Activation Unlocker.exe | log4net:ERROR XmlHierarchyConfigurator: No appender named [ConsoleAppender] could be found.
|
PassFab Activation Unlocker.exe | log4net:ERROR Appender named [ConsoleAppender] not found.
|