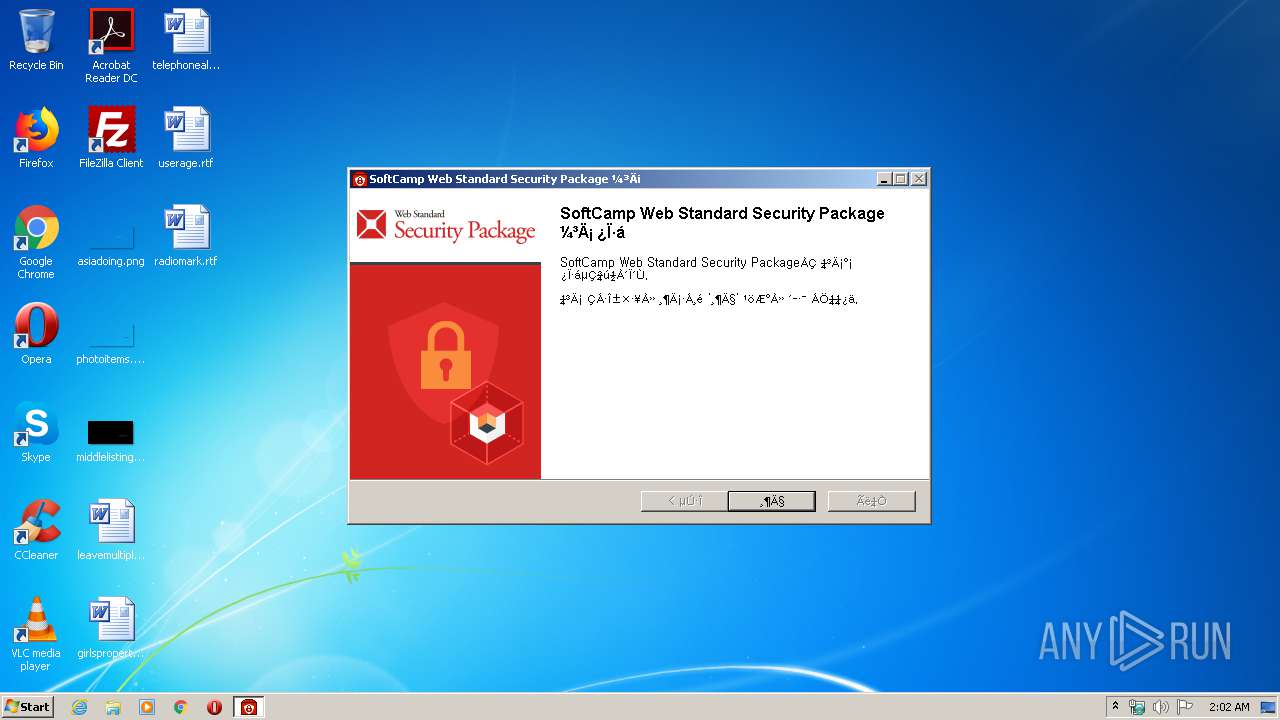
| File name: | SCWSSPSetup.exe |
| Full analysis: | https://app.any.run/tasks/b455aa66-f906-4dc7-867d-404f0b81331c |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2020, 02:02:25 |
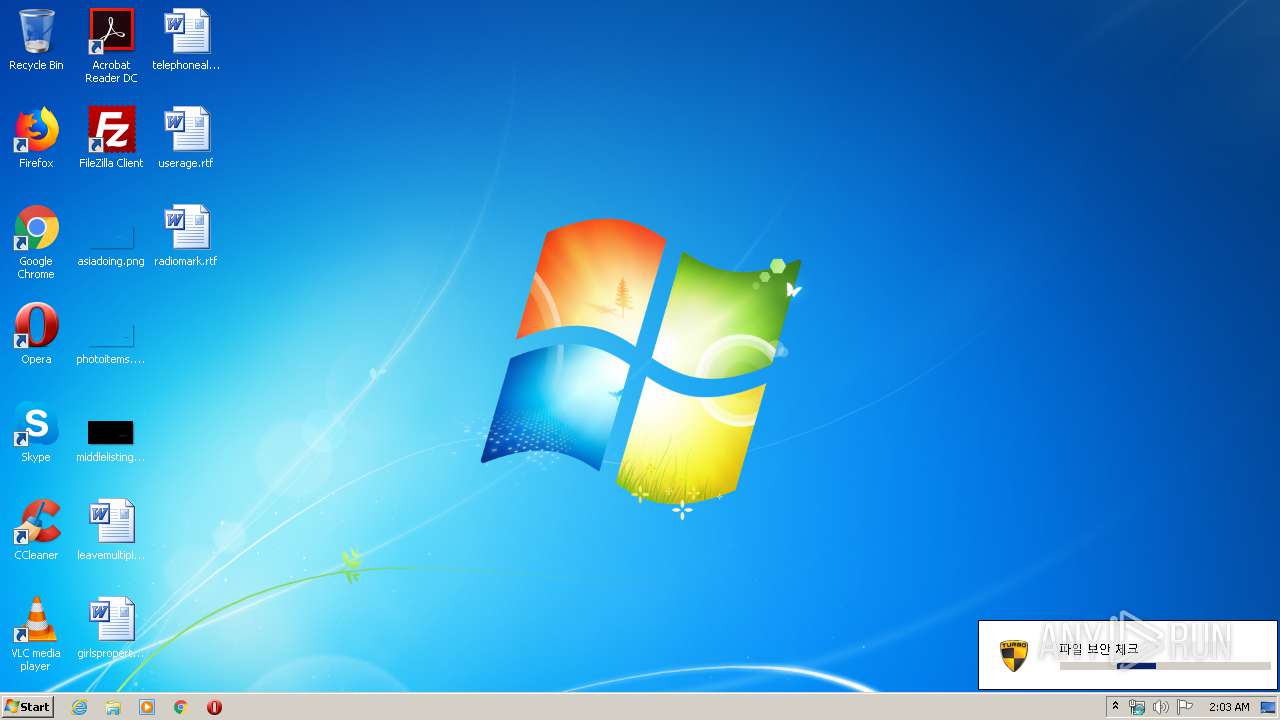
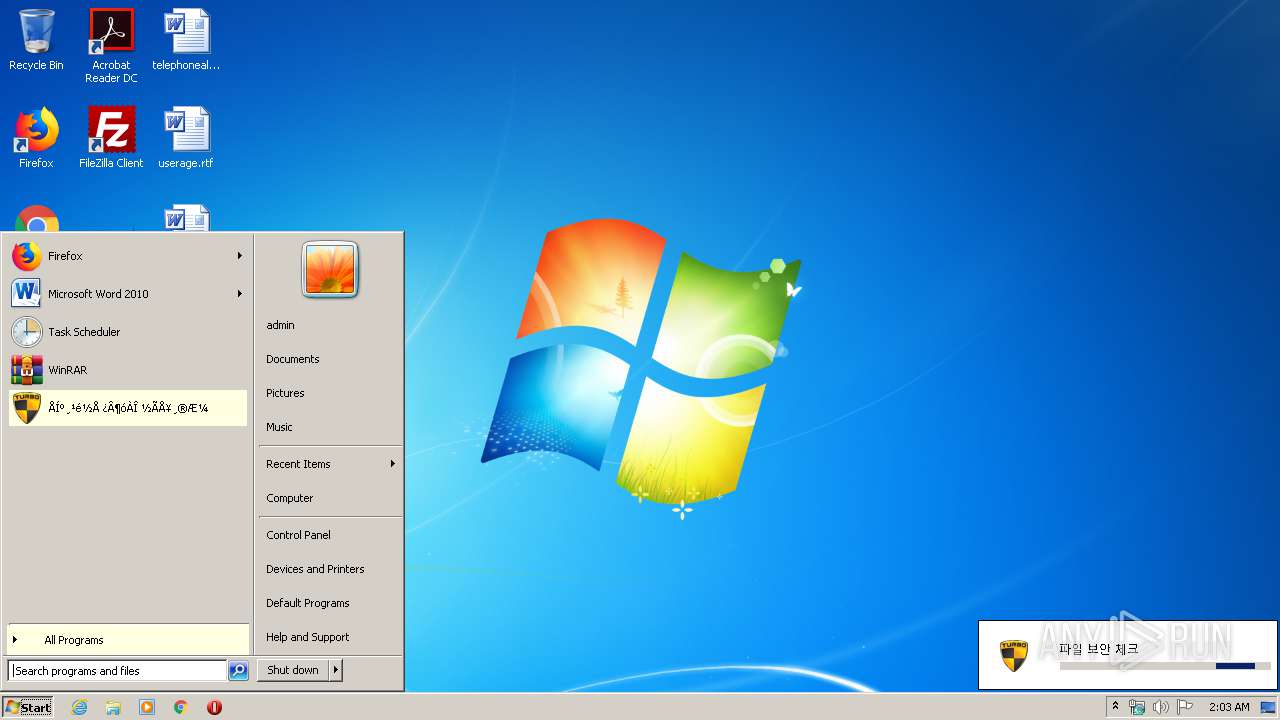
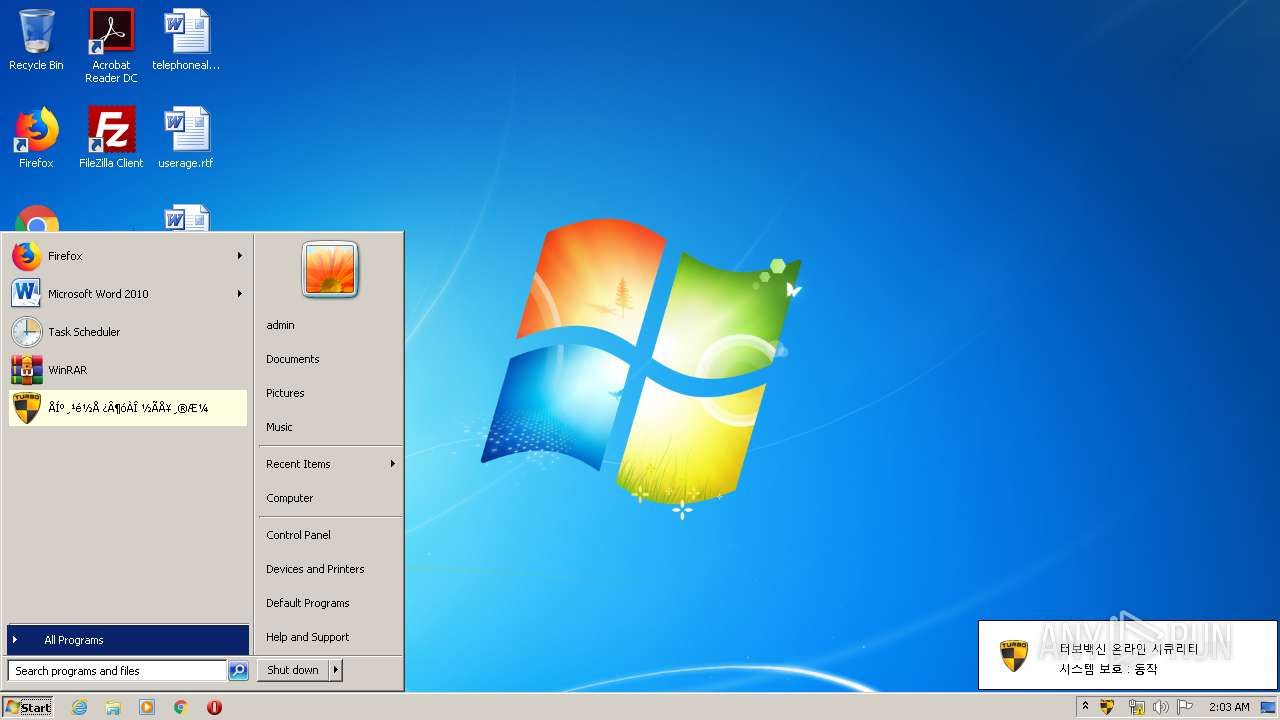
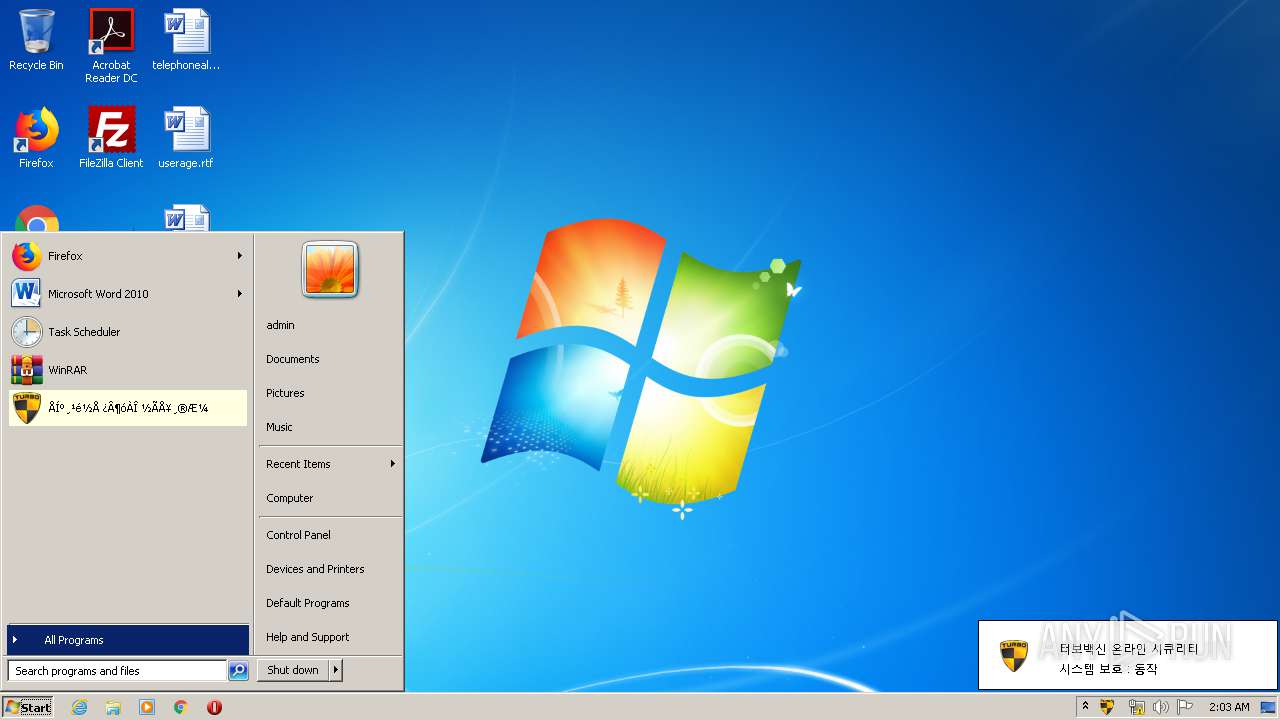
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | C66806528B25C03CAD007B756DE6896F |
| SHA1: | CD68195862F6ABFE4BEDFE0D74E4B66D4F413CE6 |
| SHA256: | 8942C745BA9671BFCFE5D133F4D4FF79728148A33F57493486A6B52E24711F94 |
| SSDEEP: | 393216:uqRIclQcMJXyfBN9mvV5N9PgAv8rGY/F59xMn9gB:rRpAXY8N/iAvCF59xTB |
MALICIOUS
Loads dropped or rewritten executable
- SCWSControl.exe (PID: 3212)
- SCWSSPSetup.exe (PID: 3244)
- TvOSecSetup.exe (PID: 2312)
- certutil.exe (PID: 2464)
- SCWSControl.exe (PID: 3356)
- SCWSControl.exe (PID: 3044)
- certutil.exe (PID: 3832)
- SCSKLSrd.exe (PID: 3576)
- conhost.exe (PID: 4032)
- explorer.exe (PID: 372)
- taskeng.exe (PID: 3332)
- SCWSHLdr.exe (PID: 2352)
- TvOSec.exe (PID: 1092)
- TvOSec.exe (PID: 2376)
- TvOSecUp.exe (PID: 1456)
Application was dropped or rewritten from another process
- TvOSecSvc.exe (PID: 2808)
- SCWSControl.exe (PID: 3212)
- certutil.exe (PID: 2464)
- TvOSecSetup.exe (PID: 2312)
- SCWSConSvc.exe (PID: 940)
- SCWSControl.exe (PID: 3044)
- SCWSControl.exe (PID: 3356)
- certutil.exe (PID: 3832)
- SCSKLSrd.exe (PID: 3576)
- TvOSec.exe (PID: 3792)
- TvOSec.exe (PID: 2376)
- SCWSHLdr.exe (PID: 2352)
- TvOSec.exe (PID: 1092)
- TvOSec.exe (PID: 660)
- TvOSecUp.exe (PID: 1456)
- TvOSecSvc.exe (PID: 3732)
- TvOSec.exe (PID: 3040)
Loads the Task Scheduler COM API
- TvOSec.exe (PID: 3040)
- TvOSec.exe (PID: 660)
- TvOSec.exe (PID: 3792)
Changes settings of System certificates
- certutil.exe (PID: 3872)
SUSPICIOUS
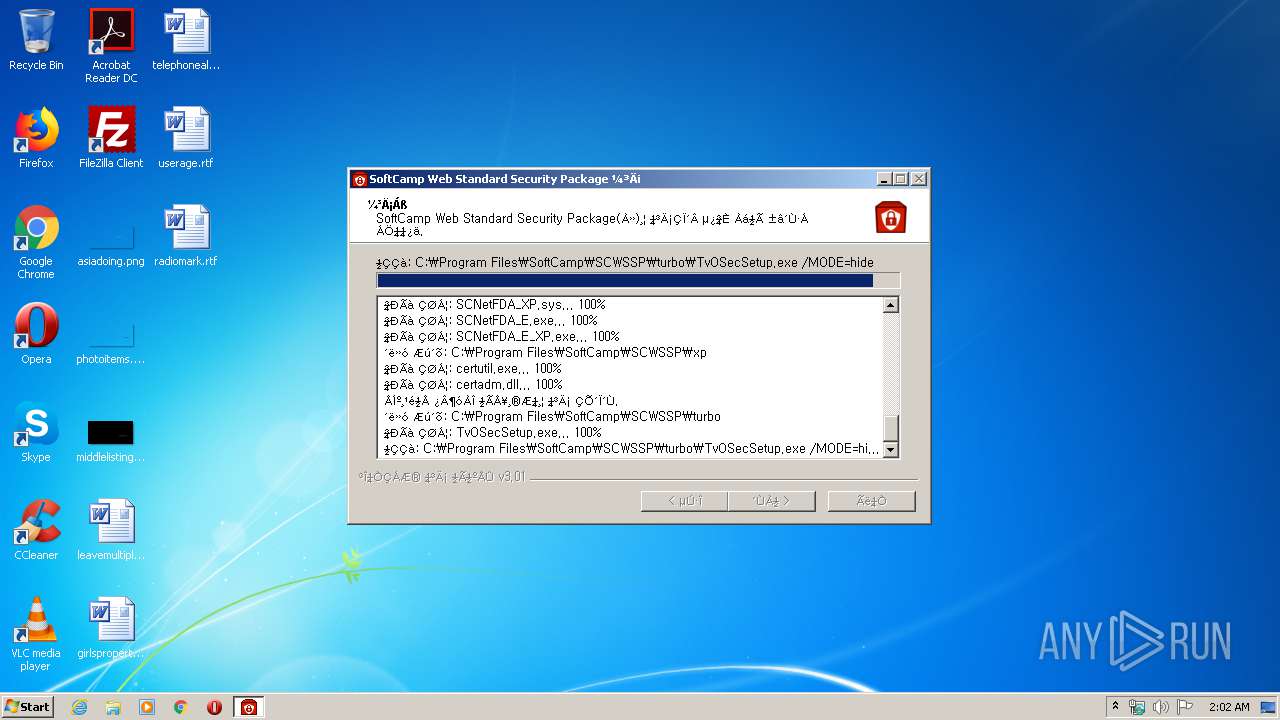
Executable content was dropped or overwritten
- SCWSSPSetup.exe (PID: 3244)
- TvOSecSetup.exe (PID: 2312)
Creates files in the program directory
- TvOSecSetup.exe (PID: 2312)
- SCWSSPSetup.exe (PID: 3244)
- SCWSControl.exe (PID: 3044)
- TvOSecUp.exe (PID: 1456)
Creates files in the driver directory
- SCWSSPSetup.exe (PID: 3244)
Creates files in the Windows directory
- SCWSSPSetup.exe (PID: 3244)
- certutil.exe (PID: 3872)
Creates a software uninstall entry
- SCWSSPSetup.exe (PID: 3244)
Creates files in the user directory
- certutil.exe (PID: 2464)
Removes files from Windows directory
- certutil.exe (PID: 3872)
Executed as Windows Service
- SCWSConSvc.exe (PID: 940)
- TvOSecSvc.exe (PID: 3732)
Starts CMD.EXE for commands execution
- SCSKLSrd.exe (PID: 3576)
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 2888)
Executed via Task Scheduler
- TvOSec.exe (PID: 2376)
Reads Internet Cache Settings
- TvOSecSetup.exe (PID: 2312)
INFO
Dropped object may contain Bitcoin addresses
- SCWSSPSetup.exe (PID: 3244)
- TvOSecSetup.exe (PID: 2312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31a3 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006071 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43434 |
.rdata | 0x00008000 | 0x00001352 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.2373 |
.data | 0x0000A000 | 0x000254F8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03725 |
.ndata | 0x00030000 | 0x0000C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003C000 | 0x00010CF8 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.78514 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.91137 | 14378 | UNKNOWN | English - United States | RT_ICON |
3 | 4.3378 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.52052 | 6760 | UNKNOWN | English - United States | RT_ICON |
5 | 4.79661 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.6316 | 3752 | UNKNOWN | English - United States | RT_ICON |
7 | 5.25497 | 2440 | UNKNOWN | English - United States | RT_ICON |
8 | 6.07556 | 2216 | UNKNOWN | English - United States | RT_ICON |
9 | 5.3721 | 1720 | UNKNOWN | English - United States | RT_ICON |
10 | 4.60396 | 1384 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
64
Monitored processes
26
Malicious processes
14
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 660 | "C:\Program Files\TurboVaccineOnlineSecurity\TvOSec.exe" /register | C:\Program Files\TurboVaccineOnlineSecurity\TvOSec.exe | TvOSec.exe | ||||||||||||
User: admin Company: Everyzone Inc. Integrity Level: HIGH Description: Turbo Vaccine Online Security.exe Exit code: 0 Version: 2016, 2, 0, 1 Modules
| |||||||||||||||
| 940 | "C:\Program Files\SoftCamp\SCWSSP\SCWSConSvc.exe" | C:\Program Files\SoftCamp\SCWSSP\SCWSConSvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: SoftCamp Co., Ltd. Integrity Level: SYSTEM Description: SCWSConSvc Service Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\TurboVaccineOnlineSecurity\TvOSec.exe" /run | C:\Program Files\TurboVaccineOnlineSecurity\TvOSec.exe | TvOSecUp.exe | ||||||||||||
User: admin Company: Everyzone Inc. Integrity Level: HIGH Description: Turbo Vaccine Online Security.exe Exit code: 0 Version: 2016, 2, 0, 1 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\TurboVaccineOnlineSecurity\TvOSecUp.exe" | C:\Program Files\TurboVaccineOnlineSecurity\TvOSecUp.exe | TvOSec.exe | ||||||||||||
User: admin Company: Everyzone Inc. Integrity Level: HIGH Description: Turbo Vaccine Online Security Update.exe Exit code: 2 Version: 2015, 12, 0, 3 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\SoftCamp\SCWSSP\turbo\TvOSecSetup.exe" /MODE=hide | C:\Program Files\SoftCamp\SCWSSP\turbo\TvOSecSetup.exe | SCWSSPSetup.exe | ||||||||||||
User: admin Company: Everyzone Inc. Integrity Level: HIGH Description: 터보백신 온라인 시큐리티 설치 마법사 Exit code: 0 Version: 2016, 2, 0, 1 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\softcamp\SCWSSP\SCWSHLdr.exe" | C:\Program Files\softcamp\SCWSSP\SCWSHLdr.exe | — | SCWSControl.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\TurboVaccineOnlineSecurity\TvOSec.exe" $(Arg0) | C:\Program Files\TurboVaccineOnlineSecurity\TvOSec.exe | taskeng.exe | ||||||||||||
User: admin Company: Everyzone Inc. Integrity Level: HIGH Description: Turbo Vaccine Online Security.exe Exit code: 0 Version: 2016, 2, 0, 1 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\softcamp\SCWSSP\cert\certutil.exe" -A -n SCSKLSCA@softcamp.co.kr -t "CT,c,c" -d "C:\Users\admin\AppData\Roaming\Mozilla\FireFox\Profiles\qldyz51w.default" -i "C:\Program Files\softcamp\SCWSSP\SecureKeyStrokeWS_CA.crt" | C:\Program Files\softcamp\SCWSSP\cert\certutil.exe | — | SCWSControl.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2472 | "C:\Users\admin\AppData\Local\Temp\SCWSSPSetup.exe" | C:\Users\admin\AppData\Local\Temp\SCWSSPSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
2 548
Read events
2 412
Write events
134
Delete events
2
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2312) TvOSecSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TurboVaccineOnlineSecurity |
| Operation: | write | Name: | Start Menu Folder |
Value: TurboVaccineOnlineSecurity | |||
| (PID) Process: | (2312) TvOSecSetup.exe | Key: | HKEY_CURRENT_USER\Software\TurboVaccineOnlineSecurity |
| Operation: | write | Name: | InstDir |
Value: C:\Program Files\TurboVaccineOnlineSecurity | |||
| (PID) Process: | (2312) TvOSecSetup.exe | Key: | HKEY_CURRENT_USER\Software\TurboVaccineOnlineSecurity |
| Operation: | write | Name: | Caption |
Value: Åͺ¸¹é½Å ¿Â¶óÀÎ ½ÃÅ¥¸®Æ¼ | |||
| (PID) Process: | (2312) TvOSecSetup.exe | Key: | HKEY_CURRENT_USER\Software\TurboVaccineOnlineSecurity |
| Operation: | write | Name: | UpdateVersion |
Value: 160202 | |||
| (PID) Process: | (2312) TvOSecSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2312) TvOSecSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2312) TvOSecSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2312) TvOSecSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2312) TvOSecSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
53
Suspicious files
8
Text files
27
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3244 | SCWSSPSetup.exe | C:\Users\admin\AppData\Local\Temp\nss80F1.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3244 | SCWSSPSetup.exe | C:\Program Files\SoftCamp\SCWSSP\SCWSConSvc.exe | executable | |
MD5:— | SHA256:— | |||
| 3244 | SCWSSPSetup.exe | C:\Program Files\SoftCamp\SCWSSP\SCWSLink.dll | executable | |
MD5:— | SHA256:— | |||
| 3244 | SCWSSPSetup.exe | C:\Program Files\SoftCamp\SCWSSP\SCWSControl.exe | executable | |
MD5:— | SHA256:— | |||
| 3244 | SCWSSPSetup.exe | C:\Users\admin\AppData\Local\Temp\nss80F1.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 3244 | SCWSSPSetup.exe | C:\Program Files\SoftCamp\SCWSSP\scskls.dat | der | |
MD5:21BBE6F6D2EC9E44EDE546F22BEB5D52 | SHA256:812ED75D11AE386BF175A59D6A8298B7CCB6F56D0AA75A3717C063B1724CAFD3 | |||
| 3244 | SCWSSPSetup.exe | C:\Users\admin\AppData\Local\Temp\nss80F1.tmp\InstallOptions.dll | executable | |
MD5:3E277798B9D8F48806FBB5EBFD4990DB | SHA256:FE19353288A08A5D2640A9C022424A1D20E4909A351F2114423E087313A40D7C | |||
| 3244 | SCWSSPSetup.exe | C:\Program Files\SoftCamp\SCWSSP\SecureKeyStrokeWS_CA.crt | text | |
MD5:90E1710ECEADBDAB0C3FBB596A3D73FA | SHA256:F05B8905F48130951A9C22D7EF204A8936CF7487A44994B6654AF3F5EDEB9555 | |||
| 3244 | SCWSSPSetup.exe | C:\Users\admin\AppData\Local\Temp\nss80F1.tmp\SimpleSC.dll | executable | |
MD5:D63975CE28F801F236C4ACA5AF726961 | SHA256:E0C580BBE48A483075C21277C6E0F23F3CBD6CE3EB2CCD3BF48CF68F05628F43 | |||
| 3244 | SCWSSPSetup.exe | C:\Program Files\SoftCamp\SCWSSP\ProcessKillPrevent64.dll | executable | |
MD5:876B953A8DA5F0B559D3E9F440284A8D | SHA256:E053C41E10E6708032ABAA7231DF712464023C255383748AB9E067FD4D5E189D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1456 | TvOSecUp.exe | GET | 200 | 211.171.245.2:80 | http://www.everyzone.com/StatLog/StatLog60.asp?Adid=3&partner=ts | KR | — | — | malicious |
2312 | TvOSecSetup.exe | GET | 200 | 211.171.245.2:80 | http://www.everyzone.com/StatLog/StatLog60.asp?Adid=1&partner=ts | KR | — | — | malicious |
1456 | TvOSecUp.exe | GET | 200 | 211.171.245.9:80 | http://www.turboupdate.com/TurboVaccineOnlineSecurity/TvOSecSrv.asp | KR | text | 95 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1456 | TvOSecUp.exe | 211.171.245.9:80 | www.turboupdate.com | LG DACOM Corporation | KR | suspicious |
1456 | TvOSecUp.exe | 211.171.245.2:80 | www.everyzone.com | LG DACOM Corporation | KR | malicious |
2312 | TvOSecSetup.exe | 211.171.245.2:80 | www.everyzone.com | LG DACOM Corporation | KR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.everyzone.com |
| malicious |
www.turboupdate.com |
| suspicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2312 | TvOSecSetup.exe | A Network Trojan was detected | ET MALWARE User-Agent (HTTP) |
Process | Message |
|---|---|
TvOSecSetup.exe | ¼³Ä¡ : OS üũ |
TvOSecSetup.exe | ¼³Ä¡ : Ç÷§Æû : X86 |
TvOSecSetup.exe | Áõº¹ ½ÇÇà üũ |
TvOSecSetup.exe | .onInit |
TvOSecSetup.exe | ---> ¼³Ä¡ : (7)(Service Pack 1)(86) |
TvOSecSetup.exe | ¼³Ä¡ : ÃʱâÈ ¿Ï·á!!! |
TvOSec.exe | TVOSEC : Success! Task successfully registered. |
TvOSec.exe | TVOSEC : Success! Task successfully registered. |
TvOSecSvc.exe | TVOSECSVC : ?? |
SCWSControl.exe | [SCSK] [Control] cmdLine[/Install]
|