| File name: | result.exe |
| Full analysis: | https://app.any.run/tasks/be4e0ee6-2546-4725-8f23-12c9c6d5181b |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 21:37:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C9E885CDF538D3AAEFEE55598D183698 |
| SHA1: | EF2B53248BAFC91798F4FAFDE08A57E2F351BAE4 |
| SHA256: | 8940595E02619F9A23985C66E68F47879D263F7A0D97F8F408D3621D73CFD5B8 |
| SSDEEP: | 768:K4ayZ1UfcfmudY7M1WEF3bJhwdZnvpsk:KTWUcm+VhF3bsPvf |
MALICIOUS
Steals credentials from Web Browsers
- result.exe (PID: 2144)
Actions looks like stealing of personal data
- result.exe (PID: 2144)
SUSPICIOUS
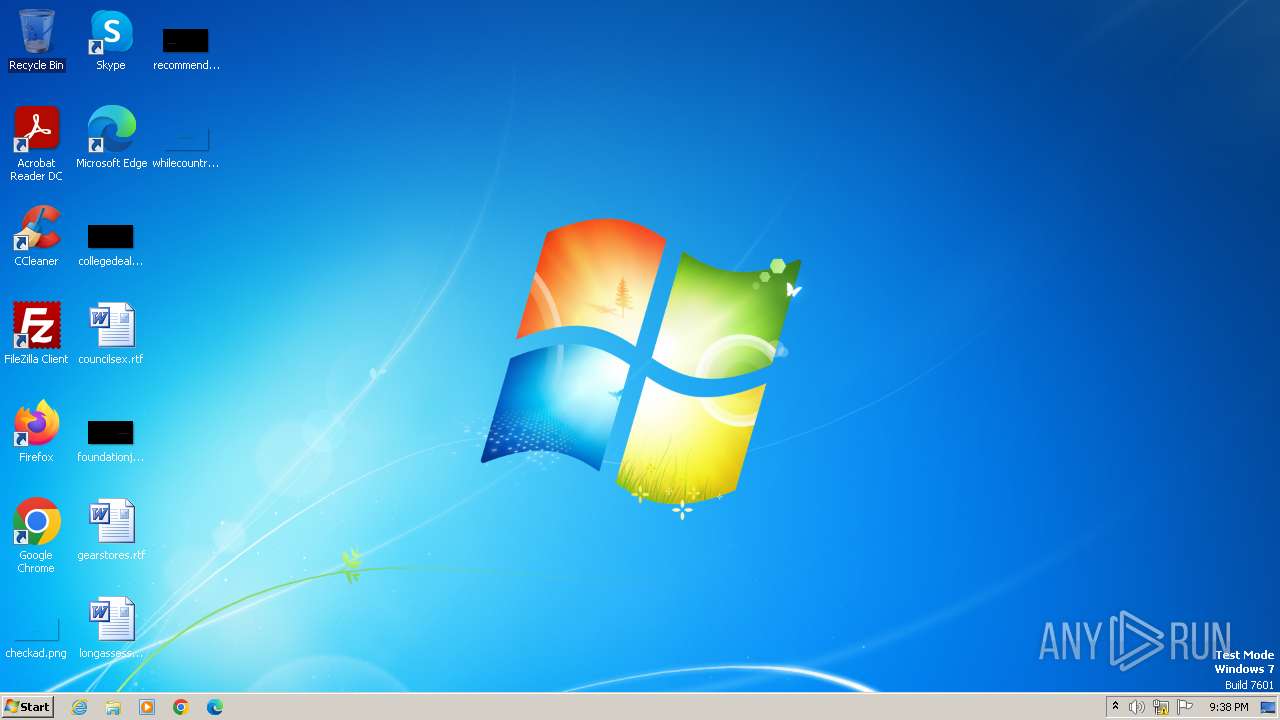
Searches for installed software
- result.exe (PID: 2144)
Loads DLL from Mozilla Firefox
- result.exe (PID: 2144)
Reads Mozilla Firefox installation path
- result.exe (PID: 2144)
Reads the Internet Settings
- result.exe (PID: 2144)
INFO
Checks supported languages
- result.exe (PID: 2144)
Reads the computer name
- result.exe (PID: 2144)
Reads the machine GUID from the registry
- result.exe (PID: 2144)
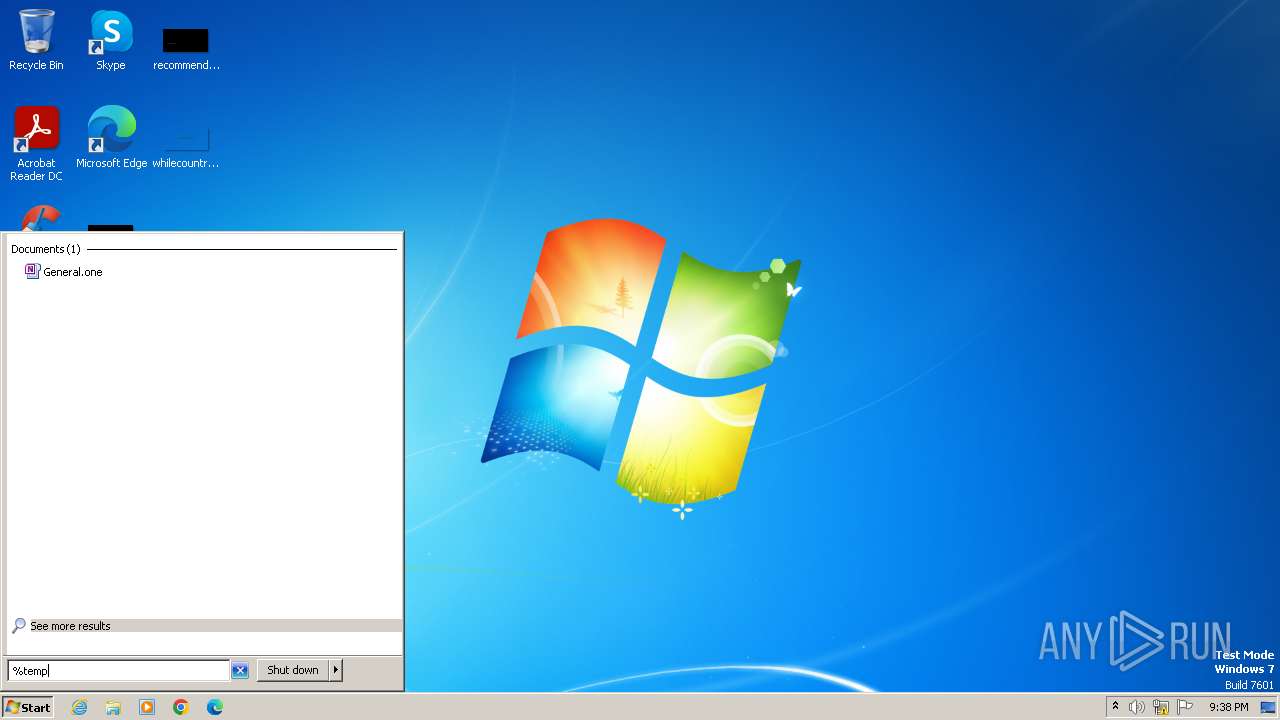
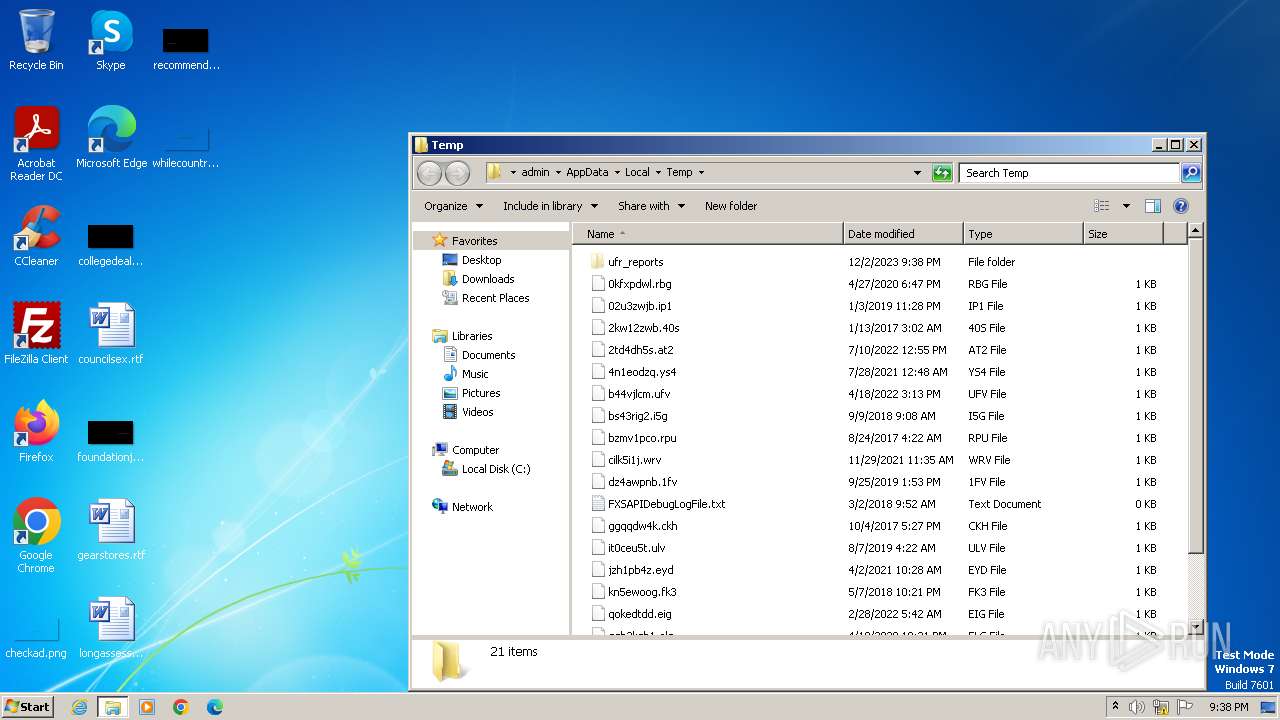
Create files in a temporary directory
- result.exe (PID: 2144)
Reads Windows Product ID
- result.exe (PID: 2144)
Reads CPU info
- result.exe (PID: 2144)
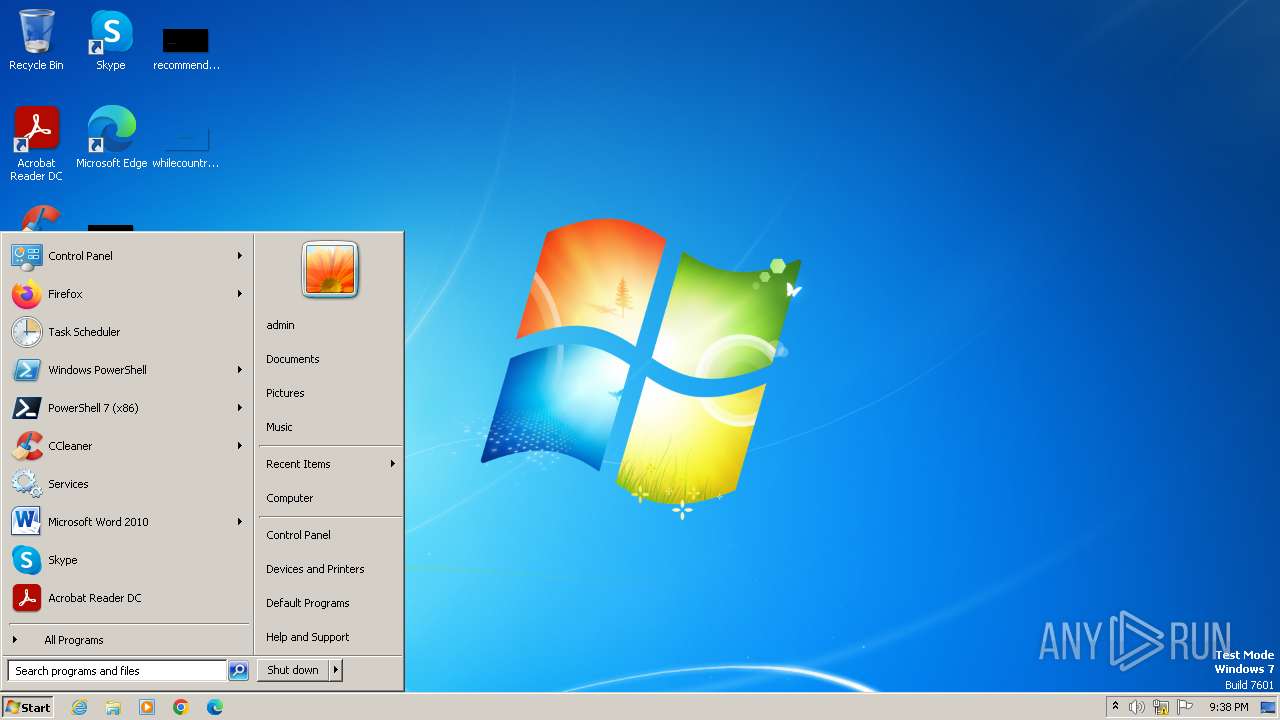
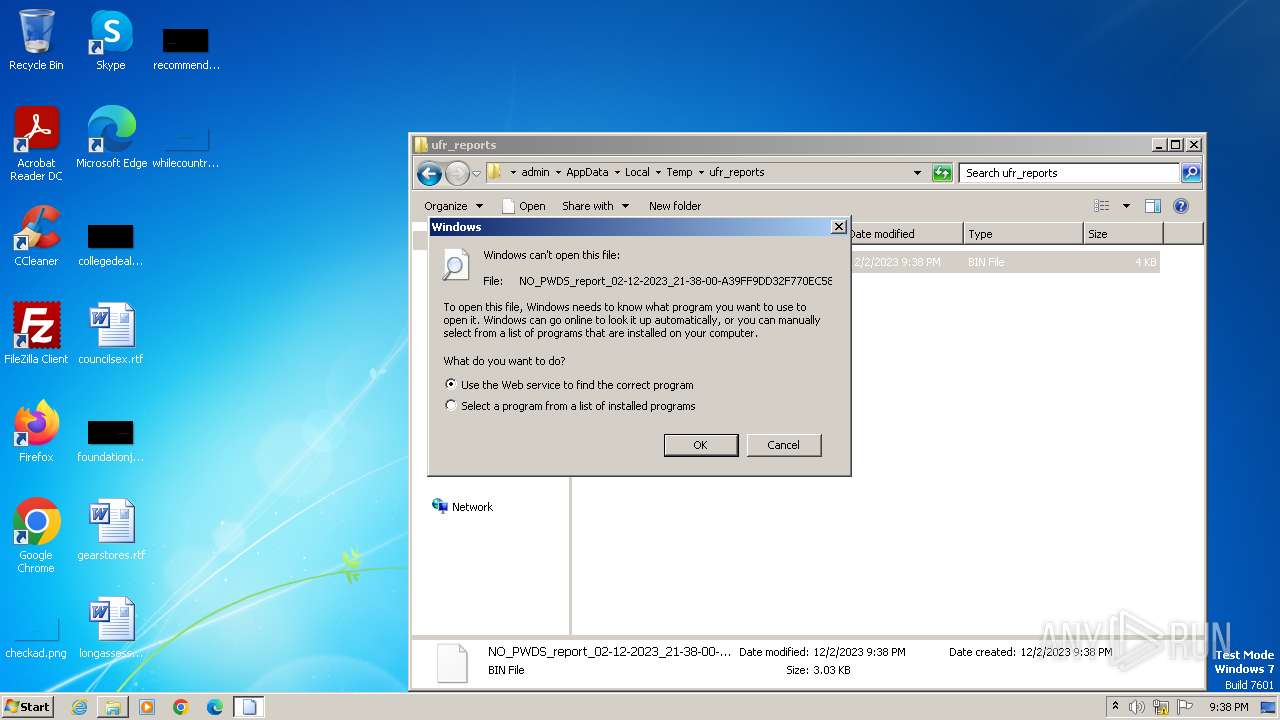
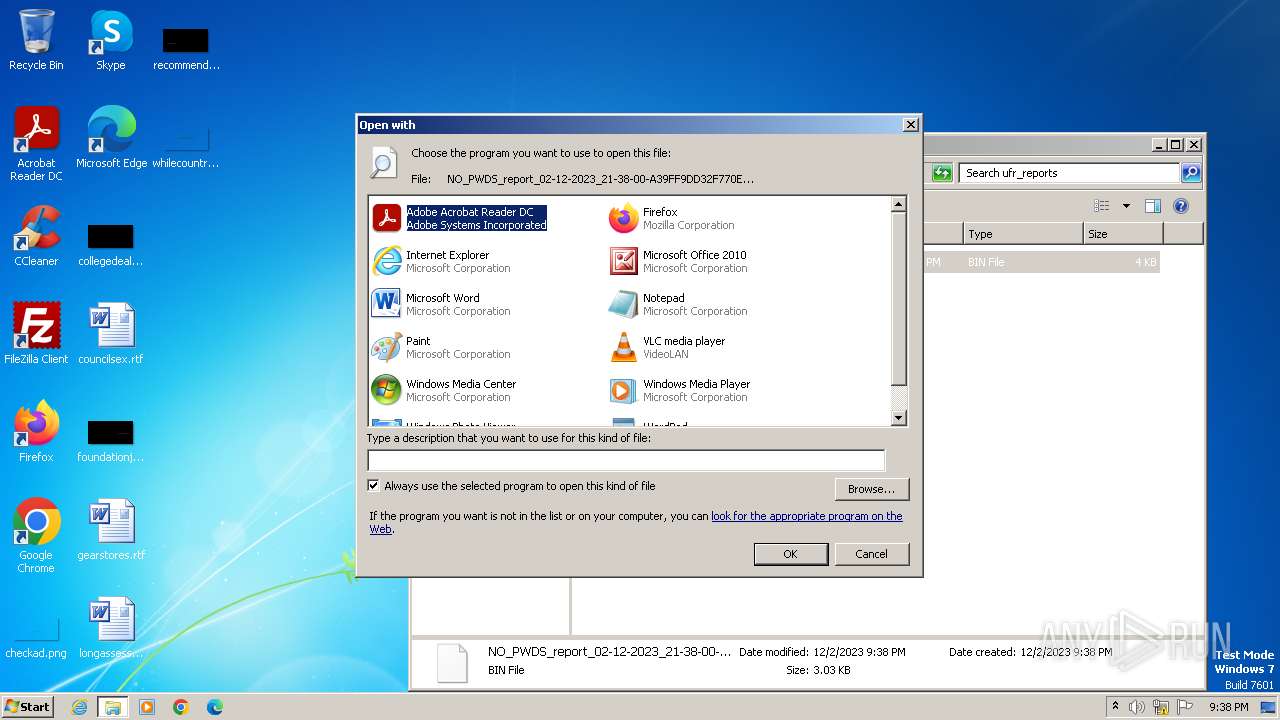
Manual execution by a user
- rundll32.exe (PID: 2928)
- verclsid.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE Yoda's Crypter (63.7) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.7) |
| .exe | | | Win32 Executable (generic) (10.8) |
| .exe | | | Generic Win/DOS Executable (4.8) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2089:07:17 06:39:20+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 24576 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 348160 |
| EntryPoint: | 0x5b9a0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | "C:\Users\admin\AppData\Local\Temp\result.exe" | C:\Users\admin\AppData\Local\Temp\result.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2780 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\System32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
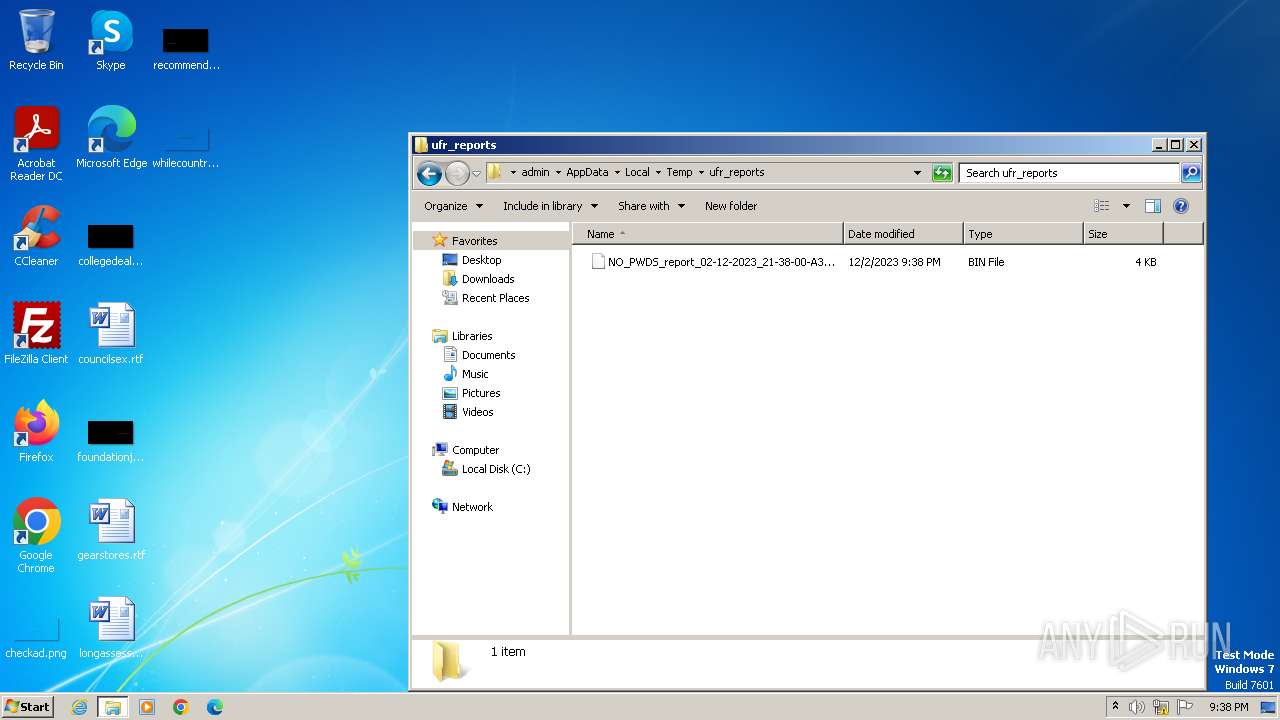
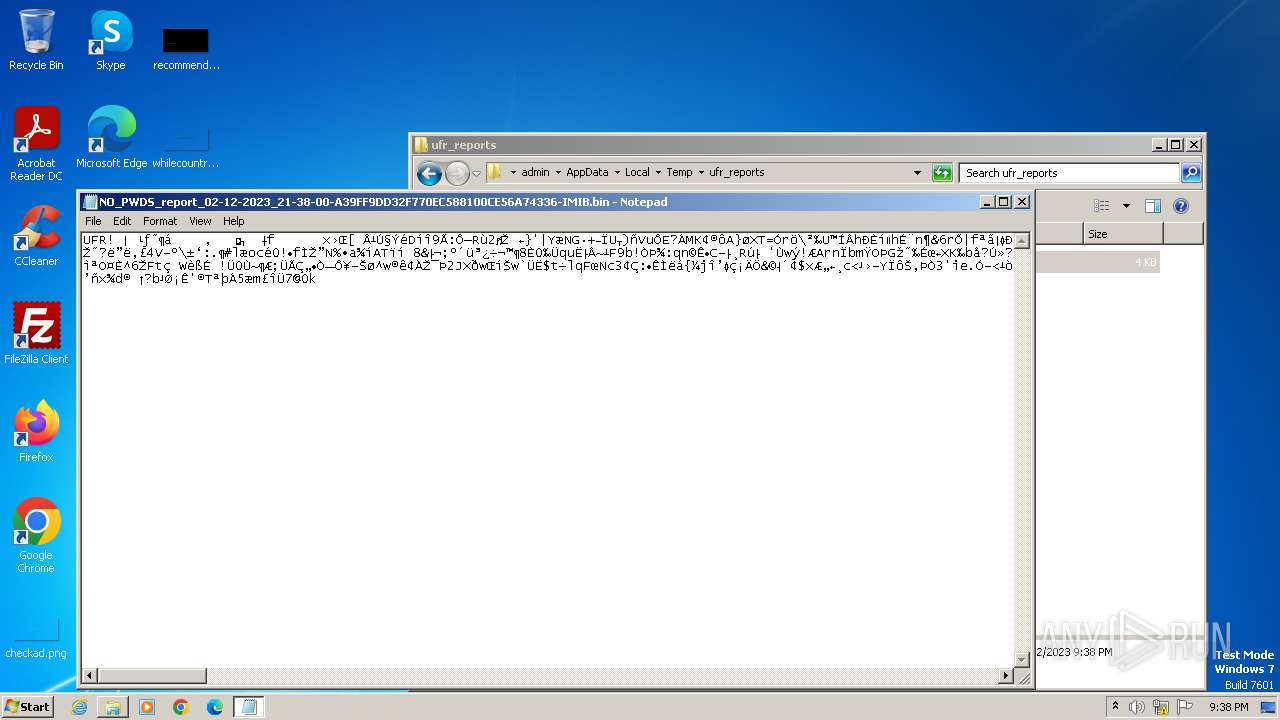
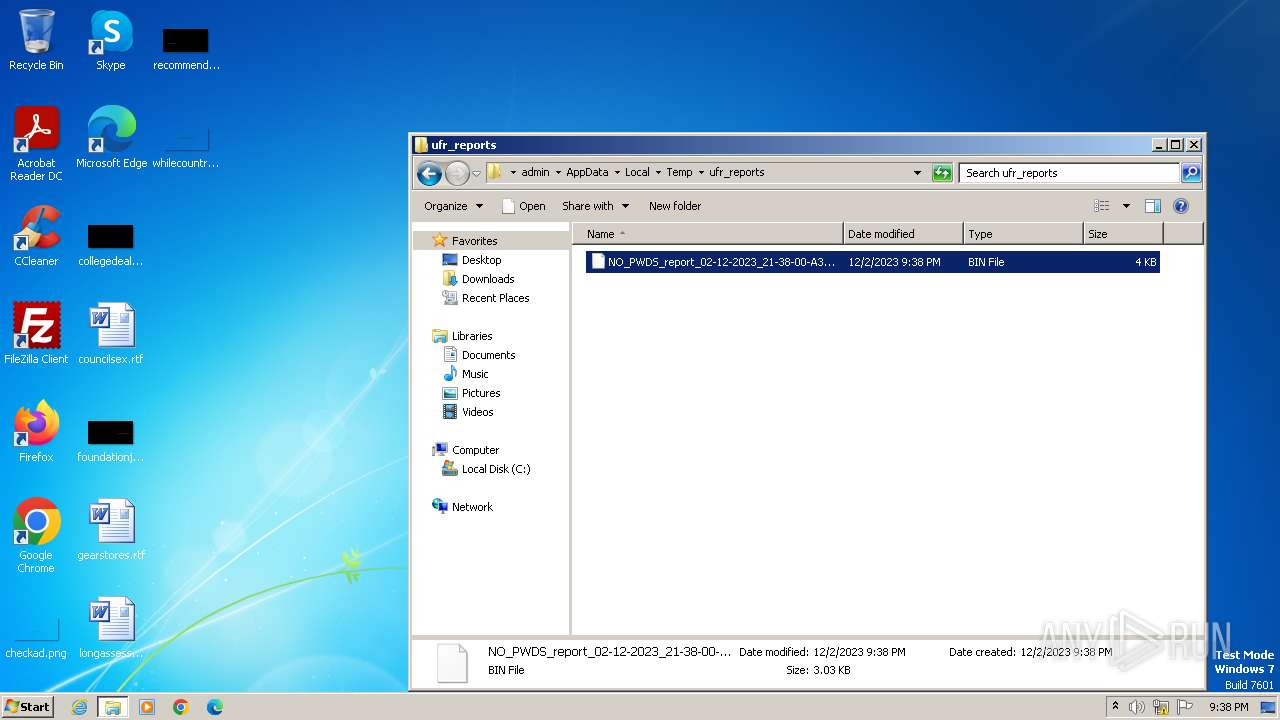
| 2928 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\ufr_reports\NO_PWDS_report_02-12-2023_21-38-00-A39FF9DD32F770EC588100CE56A74336-IMIB.bin | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\ufr_reports\NO_PWDS_report_02-12-2023_21-38-00-A39FF9DD32F770EC588100CE56A74336-IMIB.bin | C:\Windows\System32\notepad.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 536
Read events
2 473
Write events
57
Delete events
6
Modification events
| (PID) Process: | (2144) result.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2144) result.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2928) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | delete value | Name: | C:\Windows\system32\WFS.exe |
Value: Microsoft Windows Fax and Scan | |||
| (PID) Process: | (2928) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | delete value | Name: | C:\Program Files\Google\Chrome\Application\chrome.exe |
Value: Google Chrome | |||
| (PID) Process: | (2928) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | delete value | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: Firefox | |||
| (PID) Process: | (2928) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | delete value | Name: | C:\Program Files\FileZilla FTP Client\filezilla.exe |
Value: FileZilla FTP Client | |||
| (PID) Process: | (2928) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | delete value | Name: | C:\Program Files\CCleaner\CCleaner.exe |
Value: CCleaner | |||
| (PID) Process: | (2928) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | delete value | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2928) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2144 | result.exe | C:\Users\admin\AppData\Local\Temp\NO_PWDS_report_02-12-2023_21-38-00-A39FF9DD32F770EC588100CE56A74336-IMIB.bin | binary | |
MD5:E4D026C720B63F14929143DBA8547487 | SHA256:FA42FD22069B982154972E0AB7A1436AC4BFCB01C820D517D0CB78DE982F7CF9 | |||
| 2144 | result.exe | C:\Users\admin\AppData\Local\Temp\report_02-12-2023_21-38-00-A39FF9DD32F770EC588100CE56A74336-IMIB.bin | binary | |
MD5:E4D026C720B63F14929143DBA8547487 | SHA256:FA42FD22069B982154972E0AB7A1436AC4BFCB01C820D517D0CB78DE982F7CF9 | |||
| 2144 | result.exe | C:\Users\admin\AppData\Local\Temp\ufr_reports\NO_PWDS_report_02-12-2023_21-38-00-A39FF9DD32F770EC588100CE56A74336-IMIB.bin | binary | |
MD5:1EC5FB9A0A43E8A80CA8E4D626D20741 | SHA256:7D92EDE045ADE8C429BBECE316E2644392F73E82F51B7DD3BF45F6B93FC21A43 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |