| File name: | Bypass (2).exe |
| Full analysis: | https://app.any.run/tasks/cd00ad4e-0112-4d9d-9996-e82dcf5b1d15 |
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2024, 13:49:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | CB683F37F0902CE6620EB94F0CCD8A87 |
| SHA1: | 53A9DCD66067278D83A69DDA13B11923DF65494E |
| SHA256: | 893B07A3803D12A3F68B7BA487EC3C89B832604880B08374B543913C68E181D3 |
| SSDEEP: | 98304:EdXfa2WGKrBwzcfVPdIG0MJsEMMKabn9i7UiOcgpFCpTzCbw0mK6EaEBcODRZrgm:hjpjFn |
MALICIOUS
Drops the executable file immediately after the start
- Bypass (2).exe (PID: 3208)
Creates a writable file in the system directory
- Bypass (2).exe (PID: 3208)
SUSPICIOUS
Reads the BIOS version
- Bypass (2).exe (PID: 3208)
Executable content was dropped or overwritten
- Bypass (2).exe (PID: 3208)
Starts CMD.EXE for commands execution
- Bypass (2).exe (PID: 3208)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3100)
Starts SC.EXE for service management
- cmd.exe (PID: 3100)
INFO
Checks supported languages
- Bypass (2).exe (PID: 3208)
- wmpnscfg.exe (PID: 2952)
Process checks whether UAC notifications are on
- Bypass (2).exe (PID: 3208)
Reads the computer name
- Bypass (2).exe (PID: 3208)
- wmpnscfg.exe (PID: 2952)
Reads the machine GUID from the registry
- Bypass (2).exe (PID: 3208)
Manual execution by a user
- wmpnscfg.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2041:10:27 13:24:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 399360 |
| InitializedDataSize: | 5120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5b2058 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
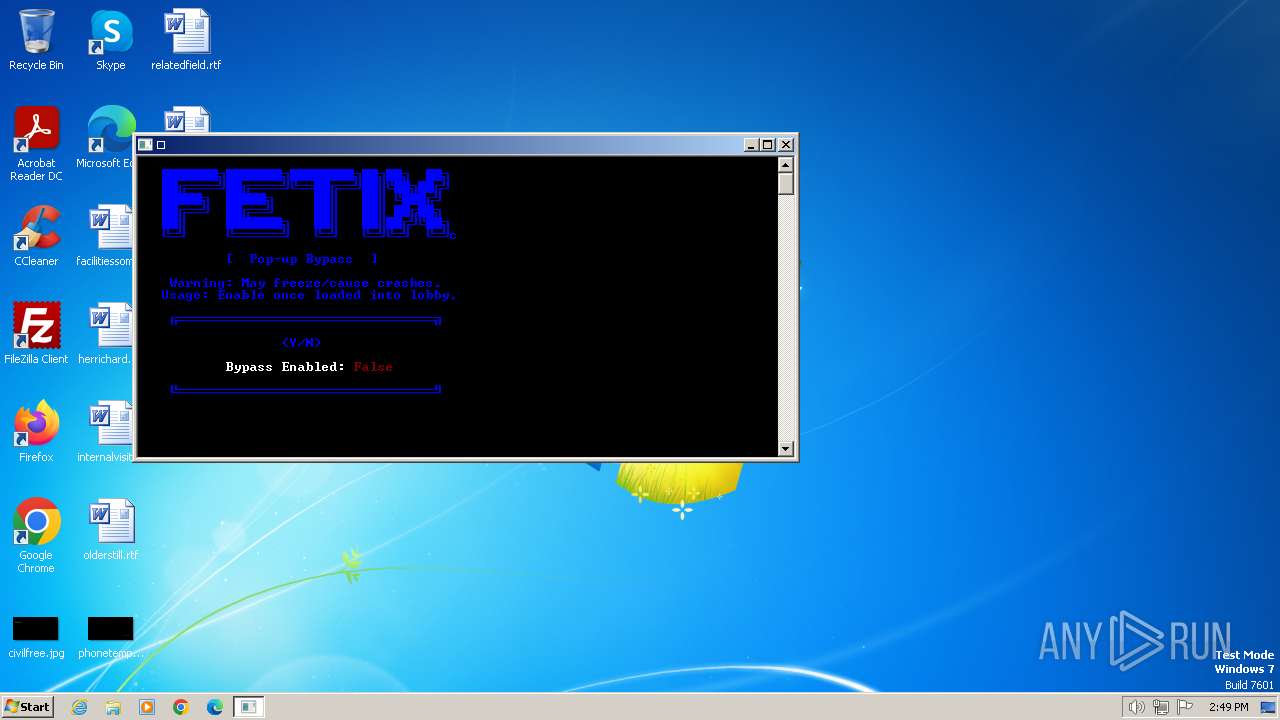
| FileDescription: | Pop-up Bypass |
| FileVersion: | 1.0.0.0 |
| InternalName: | Pop-up Bypass.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | Pop-up Bypass.exe |
| ProductName: | Pop-up Bypass |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
50
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | sc queryex BrokerInfrastructure | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3100 | "cmd.exe" /c sc queryex BrokerInfrastructure | findstr PID | C:\Windows\System32\cmd.exe | — | Bypass (2).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3144 | findstr PID | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3208 | "C:\Users\admin\AppData\Local\Temp\Bypass (2).exe" | C:\Users\admin\AppData\Local\Temp\Bypass (2).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Pop-up Bypass Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
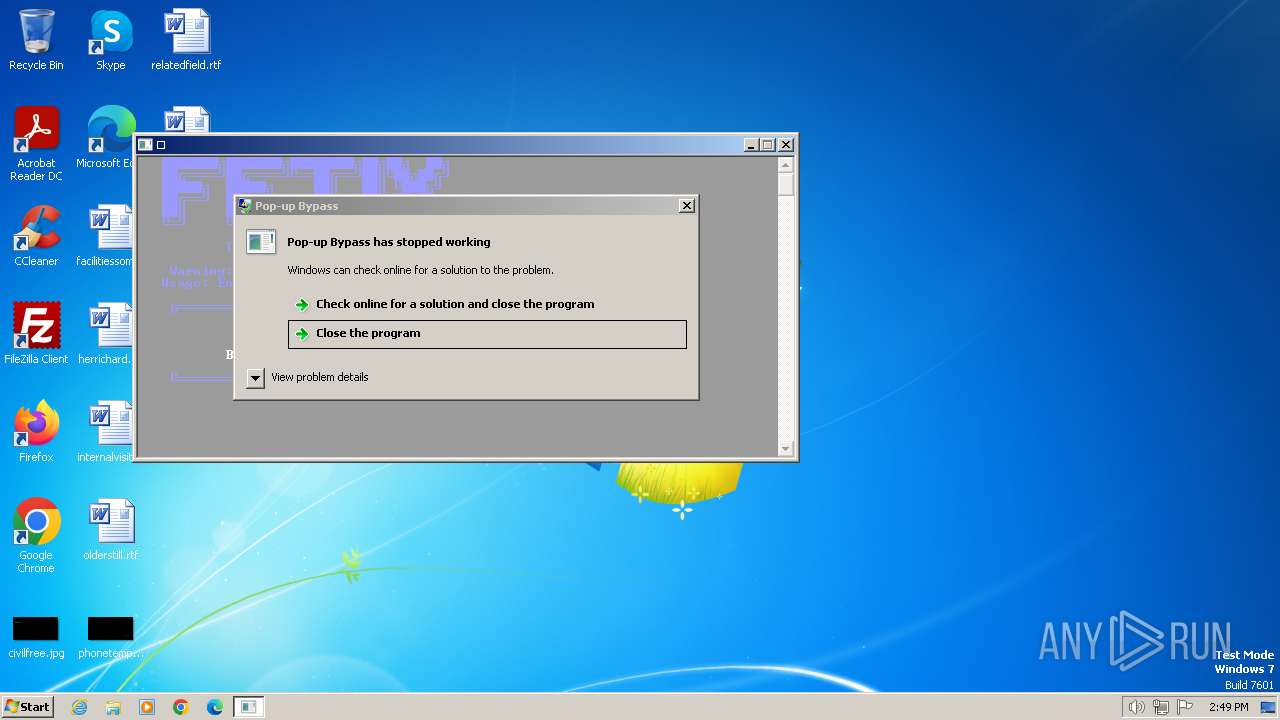
| 3416 | "C:\Users\admin\AppData\Local\Temp\Bypass (2).exe" | C:\Users\admin\AppData\Local\Temp\Bypass (2).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Pop-up Bypass Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
306
Read events
306
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3208 | Bypass (2).exe | C:\Windows\system32\PsSuspend.exe | executable | |
MD5:1B9F1A75593DFC670FA7C54659AB5796 | SHA256:95A922E178075FB771066DB4AB1BD70C7016F794709D514AB1C7F11500F016CD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 217.20.57.34:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 217.20.57.34:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbe613066ac7852b | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 104.84.57.181:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 217.20.57.34:80 | ctldl.windowsupdate.com | — | US | unknown |
1372 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1372 | svchost.exe | 104.84.57.181:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 217.20.57.34:80 | ctldl.windowsupdate.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |