| File name: | fscan.zip |
| Full analysis: | https://app.any.run/tasks/6de46e6b-fade-4da4-a76c-12de31ffa1ef |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2025, 08:12:22 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | A48846BFACDD8908D8AE4A9B2C1B6C81 |
| SHA1: | 8B4FC60002ADDED8869CFF29885FADF01AABC657 |
| SHA256: | 8922EA1DAB573B365887D5ABABC0E48CC0CD6A6D62C96AE1A344C4AC08111E38 |
| SSDEEP: | 98304:Fb+LYHTVzsDVo3EpmCKMB7EtGk4SuTddqj2k3bX2gT3WloldKjM8ALAL3mfH45zj:K7Gz0ZhTmITh |
MALICIOUS
GENERIC has been found (auto)
- 7z (PID: 39521)
SUSPICIOUS
Executes commands using command-line interpreter
- sudo (PID: 39493)
- gnome-terminal-server (PID: 39540)
Reads passwd file
- file-roller (PID: 39494)
Reads profile file
- file-roller (PID: 39494)
INFO
Checks timezone
- 7z (PID: 39509)
- file-roller (PID: 39494)
- 7z (PID: 39521)
- python3.10 (PID: 39532)
- python3.10 (PID: 39568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:09 05:45:34 |
| ZipCRC: | 0x112810f2 |
| ZipCompressedSize: | 8322114 |
| ZipUncompressedSize: | 8585724 |
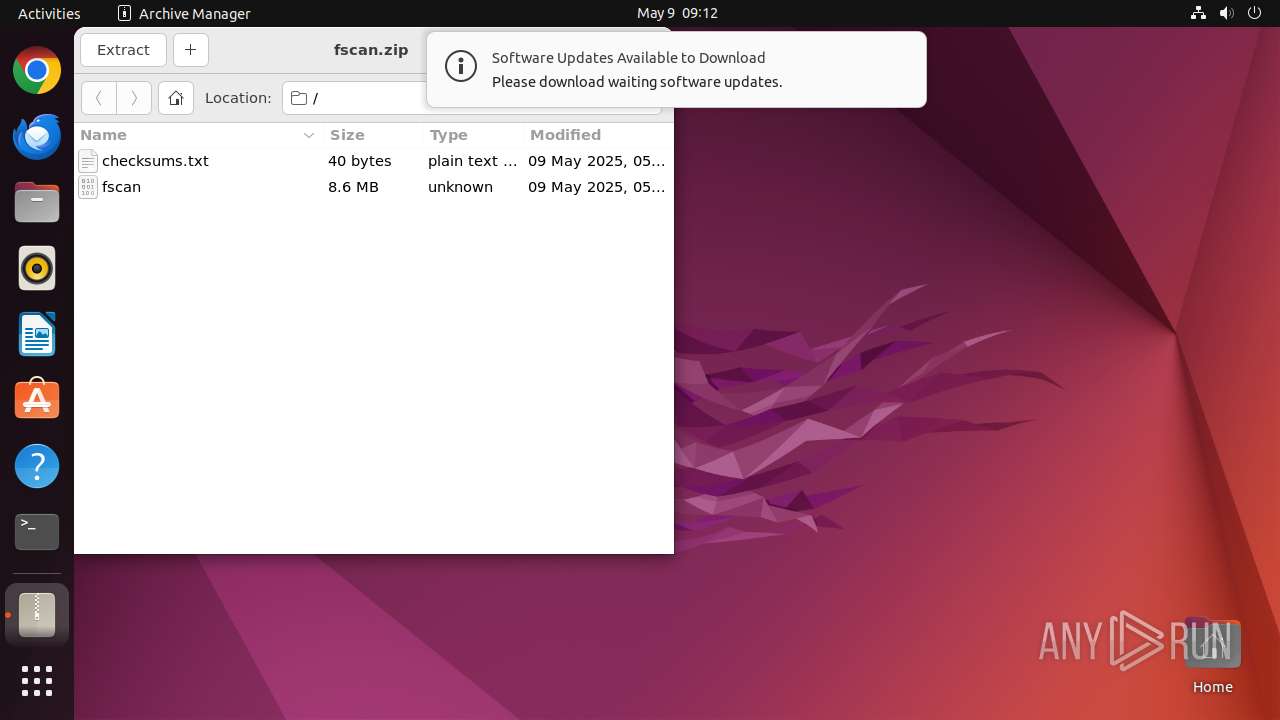
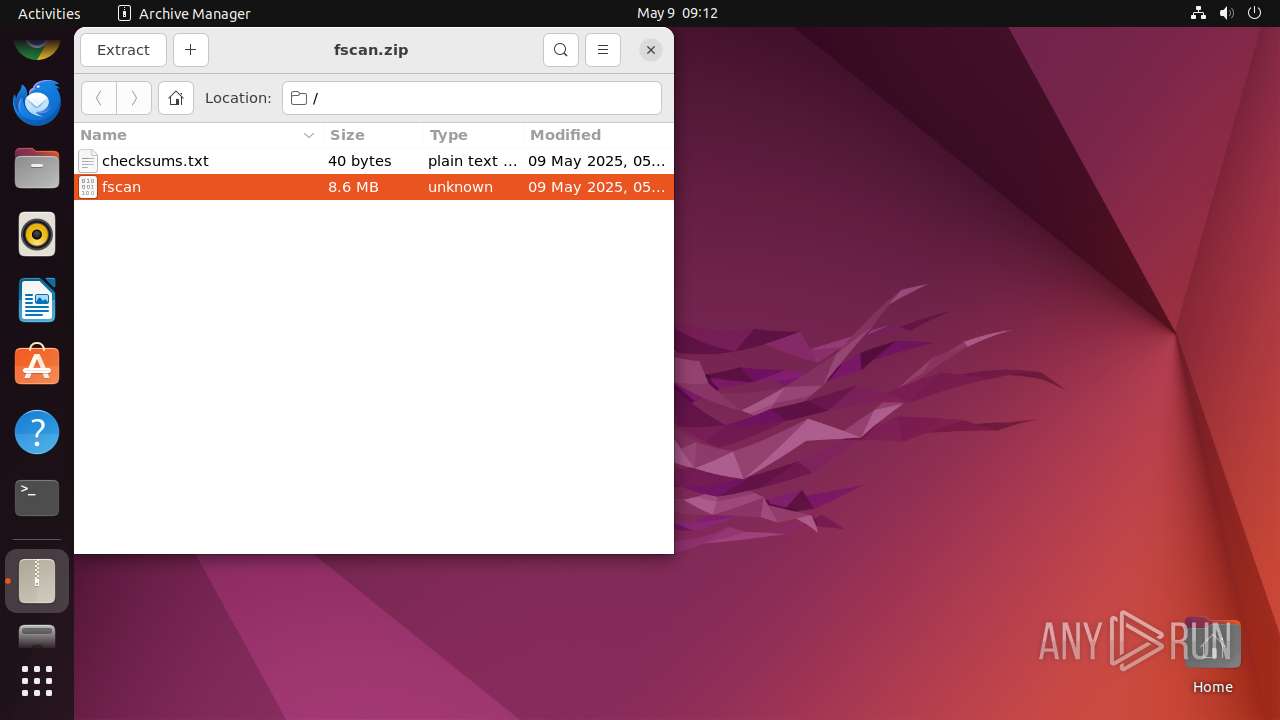
| ZipFileName: | fscan |
Total processes
241
Monitored processes
18
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 39492 | /bin/sh -c "DISPLAY=:0 sudo -iu user file-roller /tmp/fscan\.zip " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39493 | sudo -iu user file-roller /tmp/fscan.zip | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
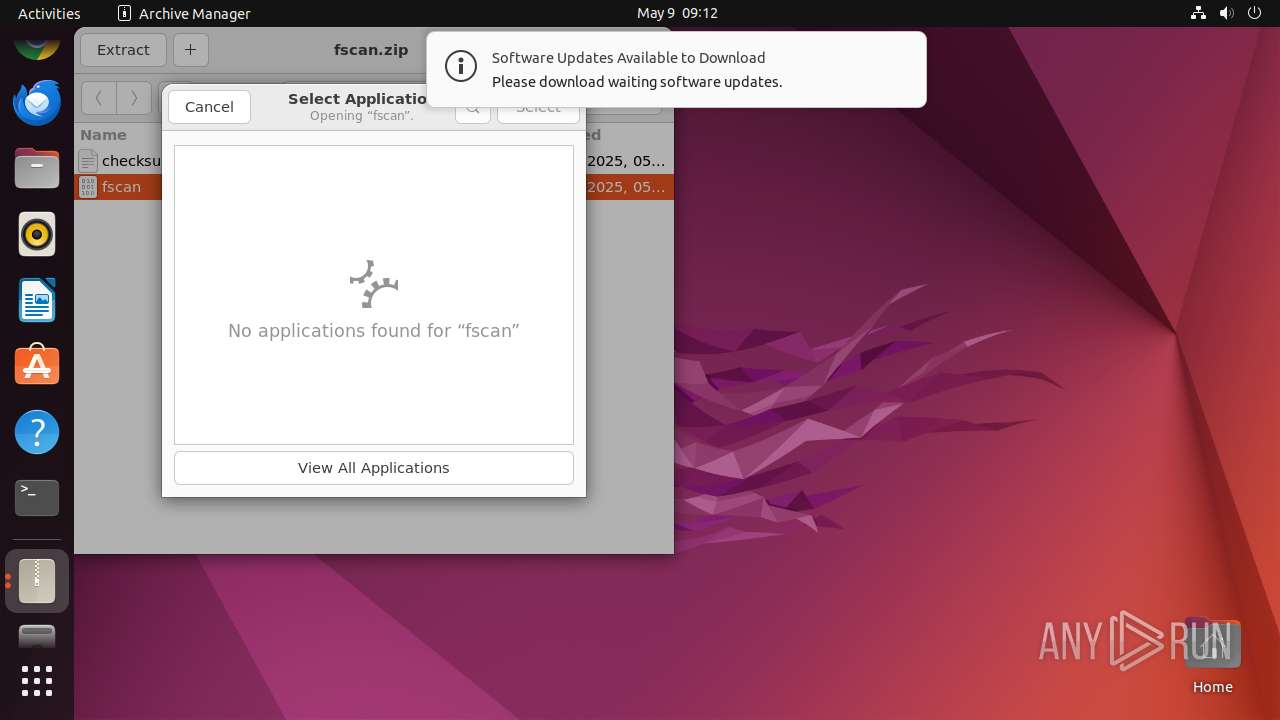
| 39494 | file-roller /tmp/fscan.zip | /usr/bin/file-roller | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39495 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39509 | /usr/lib/p7zip/7z l -slt -bd -y -- /tmp/fscan.zip | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39521 | /usr/lib/p7zip/7z x -bd -bb1 -y -o/home/user/.cache/.fr-e36KmZ -- /tmp/fscan.zip fscan | /usr/lib/p7zip/7z | file-roller | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39532 | /usr/bin/python3 /usr/bin/gnome-terminal | /usr/bin/python3.10 | — | gnome-shell |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39535 | /usr/bin/gnome-terminal.real | /usr/bin/gnome-terminal.real | — | python3.10 |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39540 | /usr/libexec/gnome-terminal-server | /usr/libexec/gnome-terminal-server | — | systemd |
User: user Integrity Level: UNKNOWN | ||||
| 39558 | bash | /usr/bin/bash | — | gnome-terminal-server |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39521 | 7z | /home/user/.cache/.fr-e36KmZ/fscan | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
10
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 204 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 169.150.255.180:443 | odrs.gnome.org | — | GB | whitelisted |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.57:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
7.100.168.192.in-addr.arpa |
| unknown |