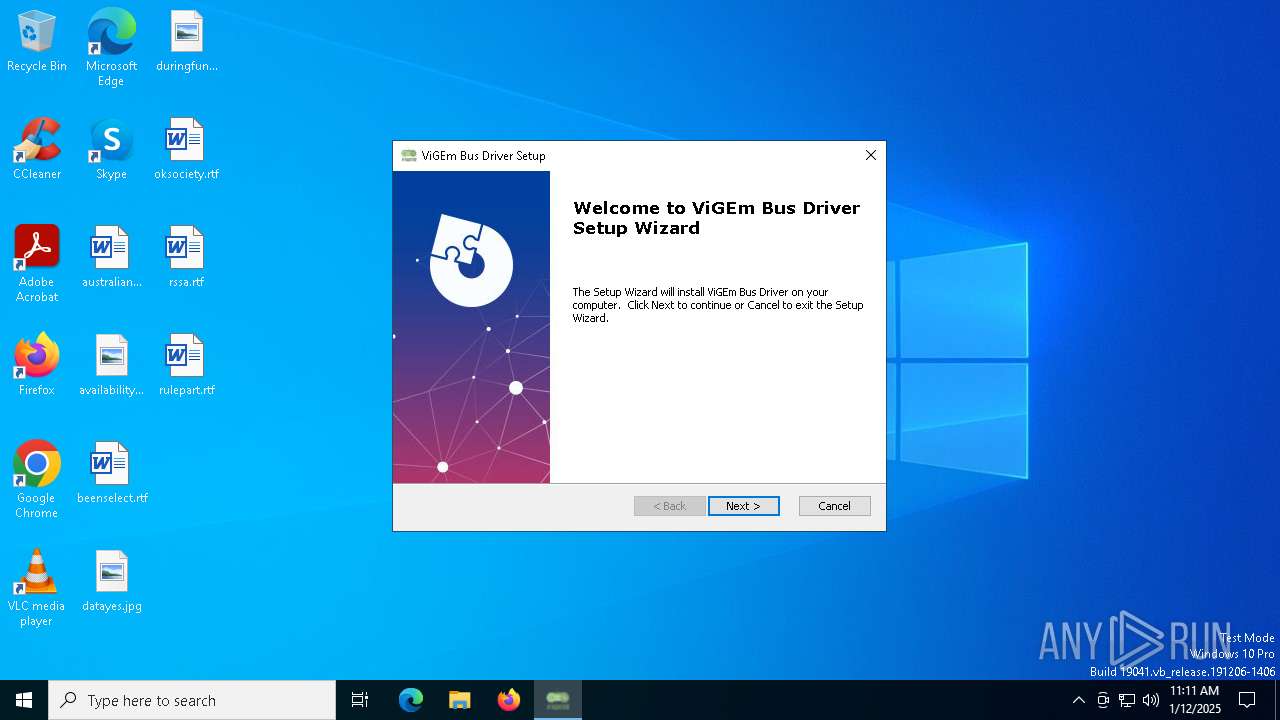
| File name: | ViGEmBus_1.22.0_x64_x86_arm64.exe |
| Full analysis: | https://app.any.run/tasks/8f7a32dd-e700-40dd-9ca8-7dfa20711c71 |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2025, 11:11:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | A62717E3E4306DE1DCA4FB5C2FA0AC6C |
| SHA1: | 5EC1B1077B43E82C2D3712909C7ED80DD59504DD |
| SHA256: | 89220A7865076B342892F98865F3499FB7C4CFD673159E89D352C360FD014C6A |
| SSDEEP: | 98304:0zfyVMcz9E685gGpJaiTpH8qknpcM6f2DHvqMmAziOKyxjdLBTTpIDPz0Ur/Y21e:5/3ya1cAr |
MALICIOUS
Executing a file with an untrusted certificate
- nefconw.exe (PID: 6868)
- nefconw.exe (PID: 6788)
SUSPICIOUS
ADVANCEDINSTALLER mutex has been found
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
Checks Windows Trust Settings
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
- msiexec.exe (PID: 6280)
- drvinst.exe (PID: 6904)
Executable content was dropped or overwritten
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
- nefconw.exe (PID: 6788)
- drvinst.exe (PID: 6904)
Process drops legitimate windows executable
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
Reads security settings of Internet Explorer
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
Reads Internet Explorer settings
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
Application launched itself
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
Reads the Windows owner or organization settings
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
- msiexec.exe (PID: 6280)
Executes as Windows Service
- VSSVC.exe (PID: 7088)
Drops a system driver (possible attempt to evade defenses)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- msiexec.exe (PID: 6280)
- nefconw.exe (PID: 6788)
- drvinst.exe (PID: 6904)
Creates files in the driver directory
- drvinst.exe (PID: 6904)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 872)
INFO
The sample compiled with english language support
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
- msiexec.exe (PID: 6280)
- nefconw.exe (PID: 6788)
- drvinst.exe (PID: 6904)
Reads the computer name
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- msiexec.exe (PID: 6280)
- msiexec.exe (PID: 6472)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
- msiexec.exe (PID: 6548)
- nefconw.exe (PID: 6868)
- nefconw.exe (PID: 6788)
Checks supported languages
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- msiexec.exe (PID: 6280)
- msiexec.exe (PID: 6472)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
- nefconw.exe (PID: 6868)
- nefconw.exe (PID: 6788)
- drvinst.exe (PID: 6904)
- msiexec.exe (PID: 6548)
Reads the machine GUID from the registry
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
- msiexec.exe (PID: 6280)
- drvinst.exe (PID: 6904)
Checks proxy server information
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
Reads the software policy settings
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
- msiexec.exe (PID: 6280)
- drvinst.exe (PID: 6904)
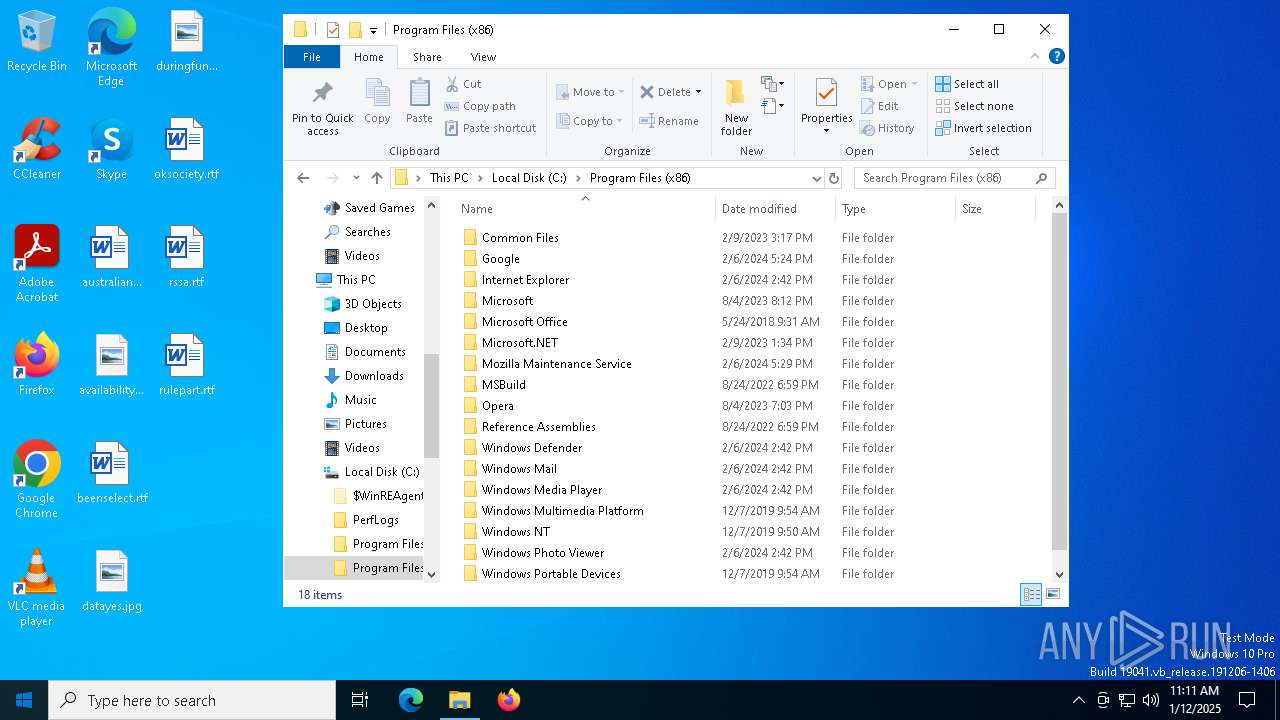
Creates files in the program directory
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
Reads Environment values
- msiexec.exe (PID: 6472)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
- msiexec.exe (PID: 6548)
Create files in a temporary directory
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 7012)
Process checks computer location settings
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6280)
Manages system restore points
- SrTasks.exe (PID: 4164)
The process uses the downloaded file
- ViGEmBus_1.22.0_x64_x86_arm64.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:04 08:42:22+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 2600448 |
| InitializedDataSize: | 1169920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f0006 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.22.0.0 |
| ProductVersionNumber: | 1.22.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
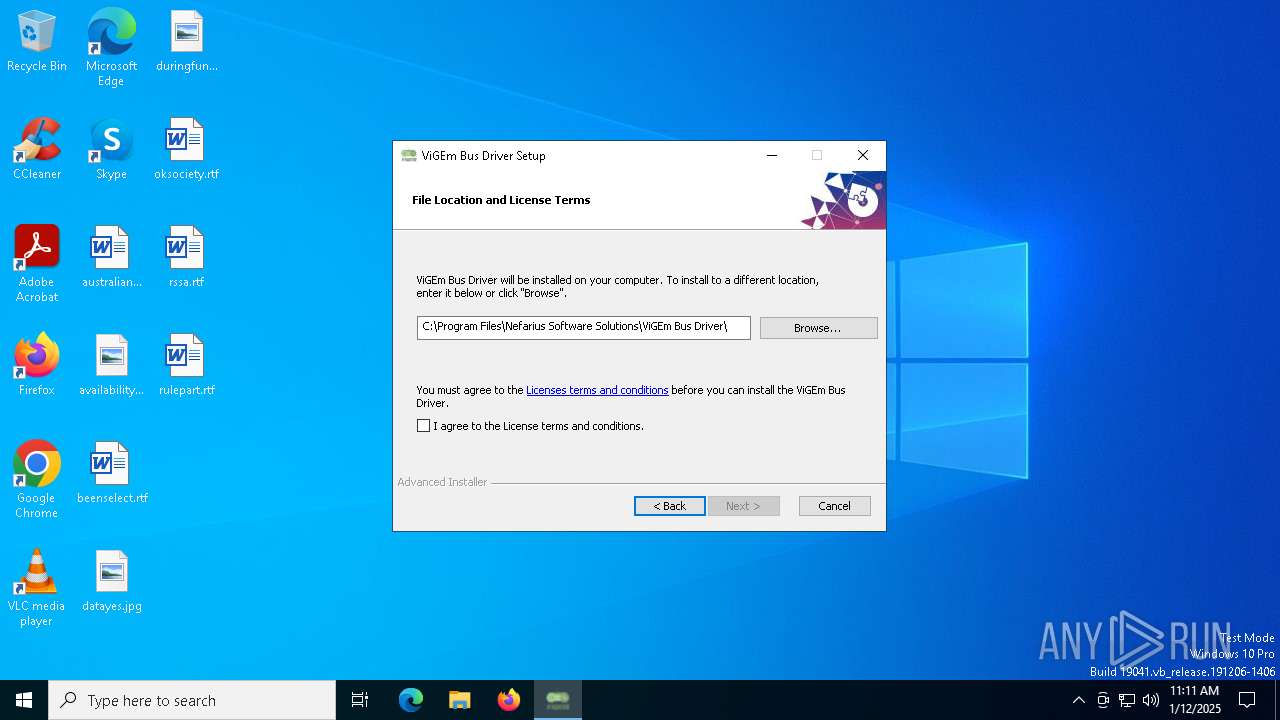
| CompanyName: | Nefarius Software Solutions e.U. |
| FileDescription: | ViGEm Bus Driver Installer |
| FileVersion: | 1.22.0 |
| InternalName: | ViGEmBus_1.22.0_x64_x86_arm64 |
| LegalCopyright: | Copyright (C) 2023 Nefarius Software Solutions e.U. |
| OriginalFileName: | ViGEmBus_1.22.0_x64_x86_arm64.exe |
| ProductName: | ViGEm Bus Driver |
| ProductVersion: | 1.22.0 |
Total processes
253
Monitored processes
14
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
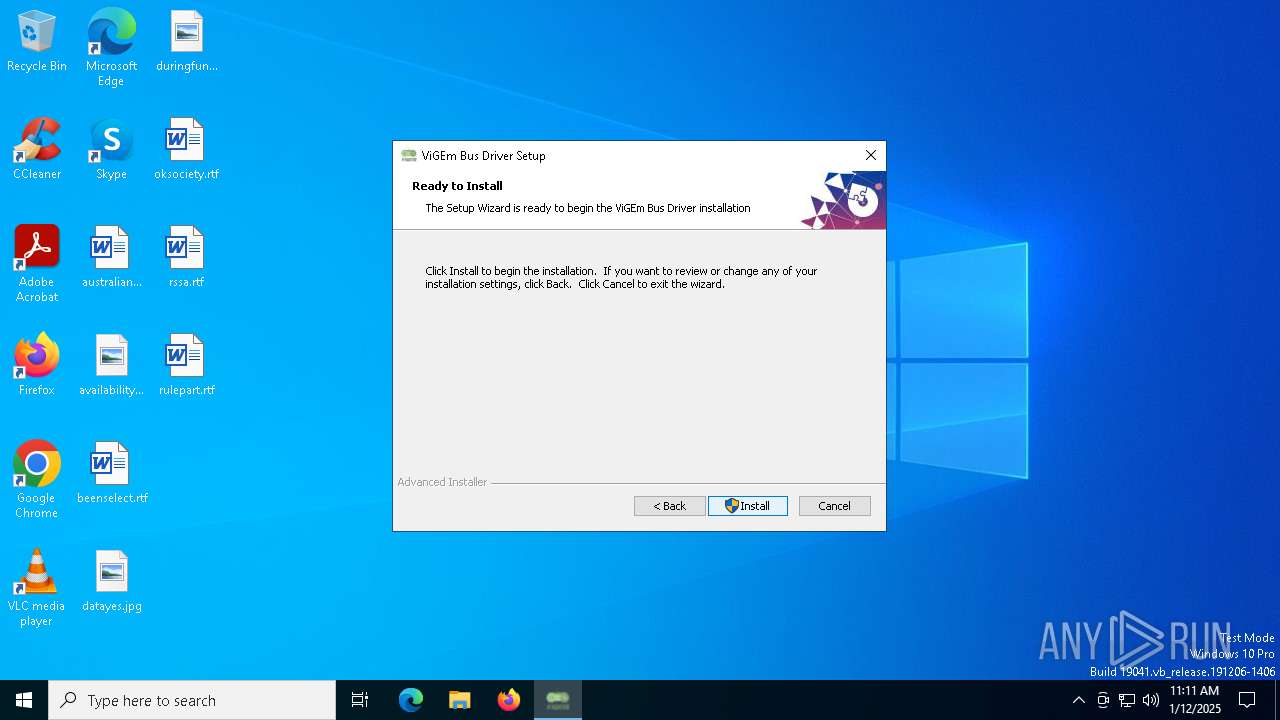
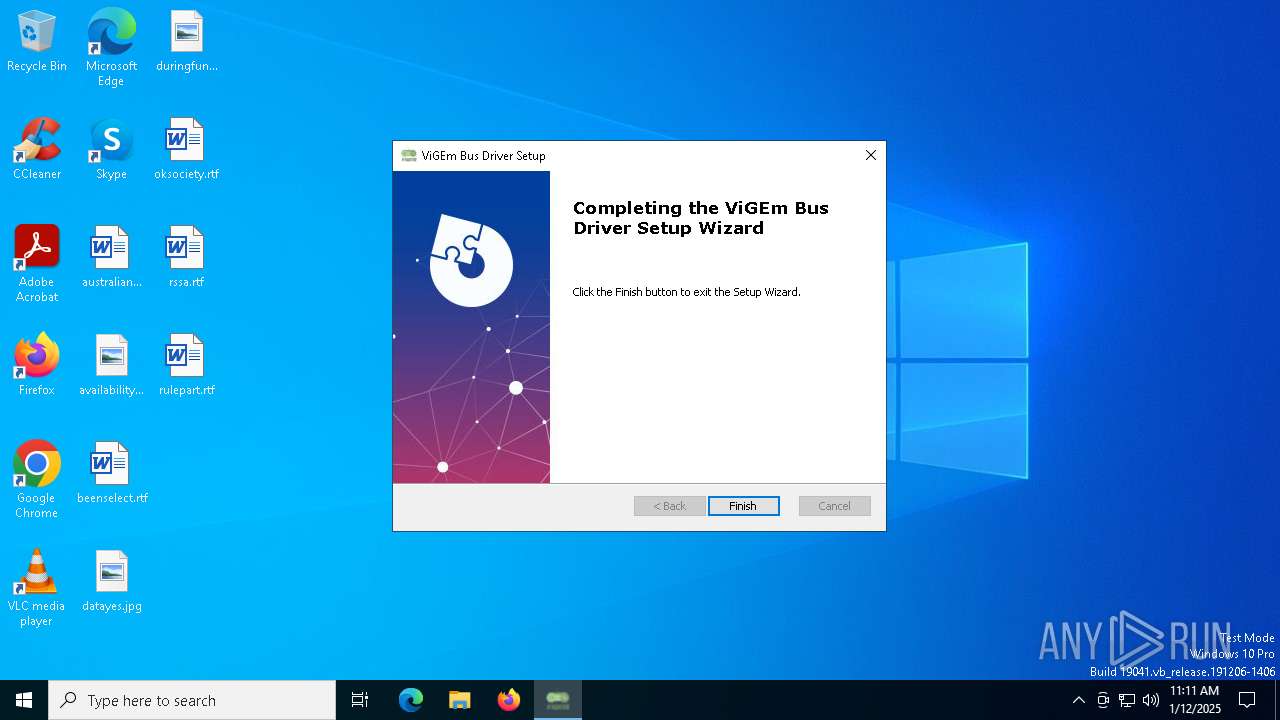
| 2600 | "C:\Users\admin\AppData\Local\Temp\ViGEmBus_1.22.0_x64_x86_arm64.exe" | C:\Users\admin\AppData\Local\Temp\ViGEmBus_1.22.0_x64_x86_arm64.exe | explorer.exe | ||||||||||||
User: admin Company: Nefarius Software Solutions e.U. Integrity Level: MEDIUM Description: ViGEm Bus Driver Installer Exit code: 0 Version: 1.22.0 Modules
| |||||||||||||||
| 4164 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6280 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6472 | C:\Windows\syswow64\MsiExec.exe -Embedding 5051914E48C3ADF5C1C0A92CE54EABDB C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6548 | C:\Windows\syswow64\MsiExec.exe -Embedding D29ED436C8E3A20EAA85C1B0B1E8C85B | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
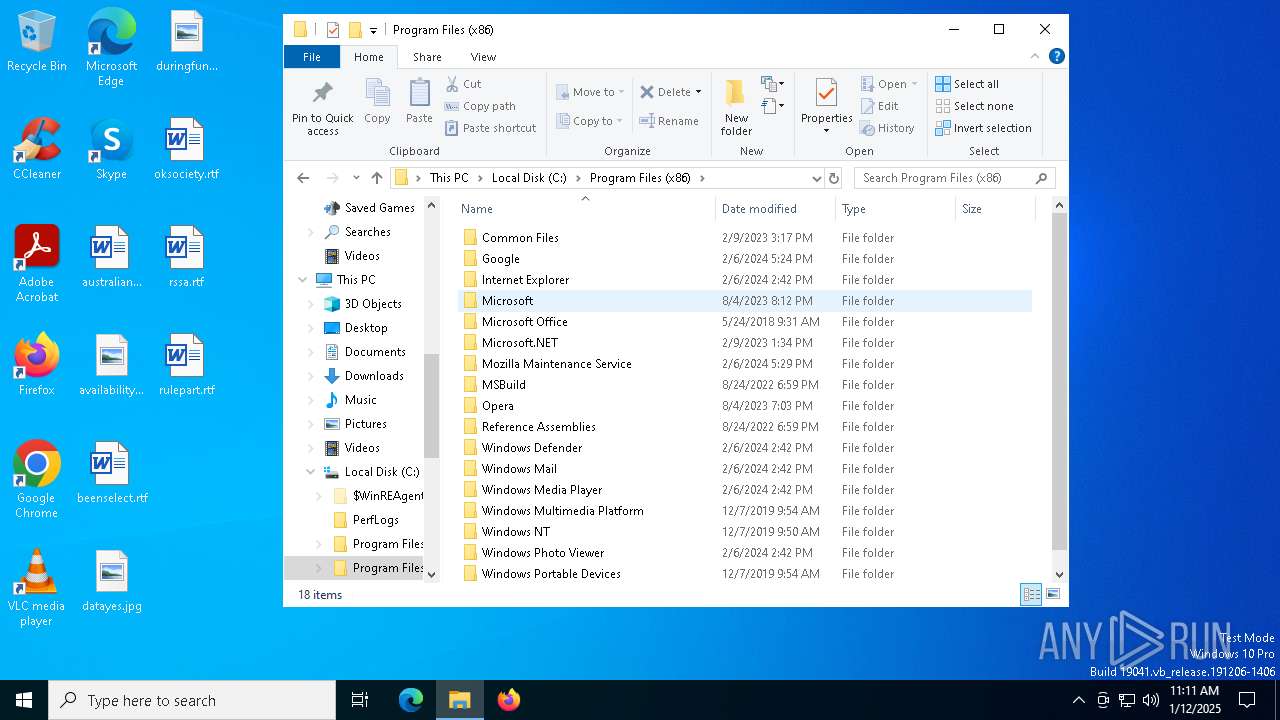
| 6788 | "C:\Program Files\Nefarius Software Solutions\ViGEm Bus Driver\nefconw.exe" --install-driver --inf-path "C:\Program Files\Nefarius Software Solutions\ViGEm Bus Driver\ViGEmBus.inf" | C:\Program Files\Nefarius Software Solutions\ViGEm Bus Driver\nefconw.exe | msiexec.exe | ||||||||||||
User: admin Company: Nefarius Software Solutions e.U. Integrity Level: HIGH Description: Nefarius' Device Console Utility Exit code: 0 Version: 1.6.0 Modules
| |||||||||||||||
| 6868 | "C:\Program Files\Nefarius Software Solutions\ViGEm Bus Driver\nefconw.exe" --create-device-node --hardware-id Nefarius\ViGEmBus\Gen1 --class-name System --class-guid 4D36E97D-E325-11CE-BFC1-08002BE10318 | C:\Program Files\Nefarius Software Solutions\ViGEm Bus Driver\nefconw.exe | — | msiexec.exe | |||||||||||
User: admin Company: Nefarius Software Solutions e.U. Integrity Level: HIGH Description: Nefarius' Device Console Utility Exit code: 0 Version: 1.6.0 Modules
| |||||||||||||||
Total events
15 912
Read events
15 610
Write events
274
Delete events
28
Modification events
| (PID) Process: | (6280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000053CA28B9E264DB0188180000A01B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000053CA28B9E264DB0188180000A01B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000CBE16DB9E264DB0188180000A01B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000DCA972B9E264DB0188180000A01B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000EB7012BAE264DB0188180000A01B0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000A2C214BAE264DB018818000014090000E803000001000000000000000000000036A6C4B05D4DC645865BF56213435B6100000000000000000000000000000000 | |||
| (PID) Process: | (7088) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4800000000000000267D25BAE264DB01B01B0000D01B0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7088) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7088) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (7088) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
34
Suspicious files
81
Text files
27
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\ProgramData\Nefarius Software Solutions\ViGEm Bus Driver 1.22.0\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\ProgramData\Nefarius Software Solutions\ViGEm Bus Driver 1.22.0\install\A4E9077\ViGEmBus.msi | executable | |
MD5:9012F08F3131F64B46CF73990F8FBB42 | SHA256:F12295FA3BE5F820ADDBEAB6EE23F4EA8980F3913AC19661A408E9221DD1AB00 | |||
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | der | |
MD5:01469D86975D80DA48C7ADBE1C3727CF | SHA256:902833A88C63BF18BC32BAEBF9F2F987380A740F21A6E1F7EA60D0FF0554638B | |||
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_35E9AC8BDBFF76B8DAD6DDAFD42E3BC2 | der | |
MD5:C66986636A54197DB46DB3F0EE71579F | SHA256:CBDAA1D89CC502E7D86B918B8A045BA6592A3FC7574DC489F6E0D415985AA119 | |||
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\Users\admin\AppData\Local\Temp\MSI5E22.tmp | executable | |
MD5:C9C085C00BC24802F066E5412DEFCF50 | SHA256:A412B642DE0E94DB761EBD2834DDE72EED86E65FC4A580670A300015B874BA24 | |||
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2600\dialog.jpg | image | |
MD5:5F6253CFF5A8B031BFB3B161079D0D86 | SHA256:36D9BAB35D1E4B50045BF902F5D42B6F865488C75F6E60FC00A6CD6F69034AB0 | |||
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | der | |
MD5:760573CE1A12683F473B76BFE22C6B43 | SHA256:0D861E3AB4E6F20C901785F10E14617841F665C8EB36EF2ED5CBA6DCE364683F | |||
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:22E7E7DAF7E54C61D1472902399DB8B8 | SHA256:75ACC31450699F39E16107128713824293D16EFD3D67D4244BA443E2280C0A08 | |||
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\Users\admin\AppData\Local\Temp\shi5DC3.tmp | executable | |
MD5:84A34BF3486F7B9B7035DB78D78BDD1E | SHA256:F85911C910B660E528D2CF291BAA40A92D09961996D6D84E7A53A7095C7CD96E | |||
| 2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:A3467F77BB0BD9C3C5DCEC954A483A40 | SHA256:22F38545EC5DB042596F2D7C1CFEAEE0E599AC8D5EBB2ADDAE104FEEB1C592D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
52
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | US | binary | 471 b | whitelisted |
2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | US | binary | 727 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
4716 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA4sR33wtnOE7yQZOQX4O%2F0%3D | US | binary | 727 b | whitelisted |
4716 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5432 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5564 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.65.132:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
2600 | ViGEmBus_1.22.0_x64_x86_arm64.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |