| File name: | hrvoje.sitar Vertex b.s. d.o.o. Contract & Payoff Aqreement_928.pdf |
| Full analysis: | https://app.any.run/tasks/21abb3e7-f16b-4550-bac9-70cc6476d5cf |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2026, 12:05:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.4, 2 page(s) |
| MD5: | 338BE6625925166F127F8F3790067078 |
| SHA1: | 24DFEC128056F2F9A804785AD3016B44F59B90E1 |
| SHA256: | 89111F28DD0D9ABB7CC5E460A3D7D839B913225BA446EE88CC013CE950316C79 |
| SSDEEP: | 3072:p6aRBjzfrSsBpAtQOf8vph/4OV/gVATzW:p6KBjwZkxqYgVP |
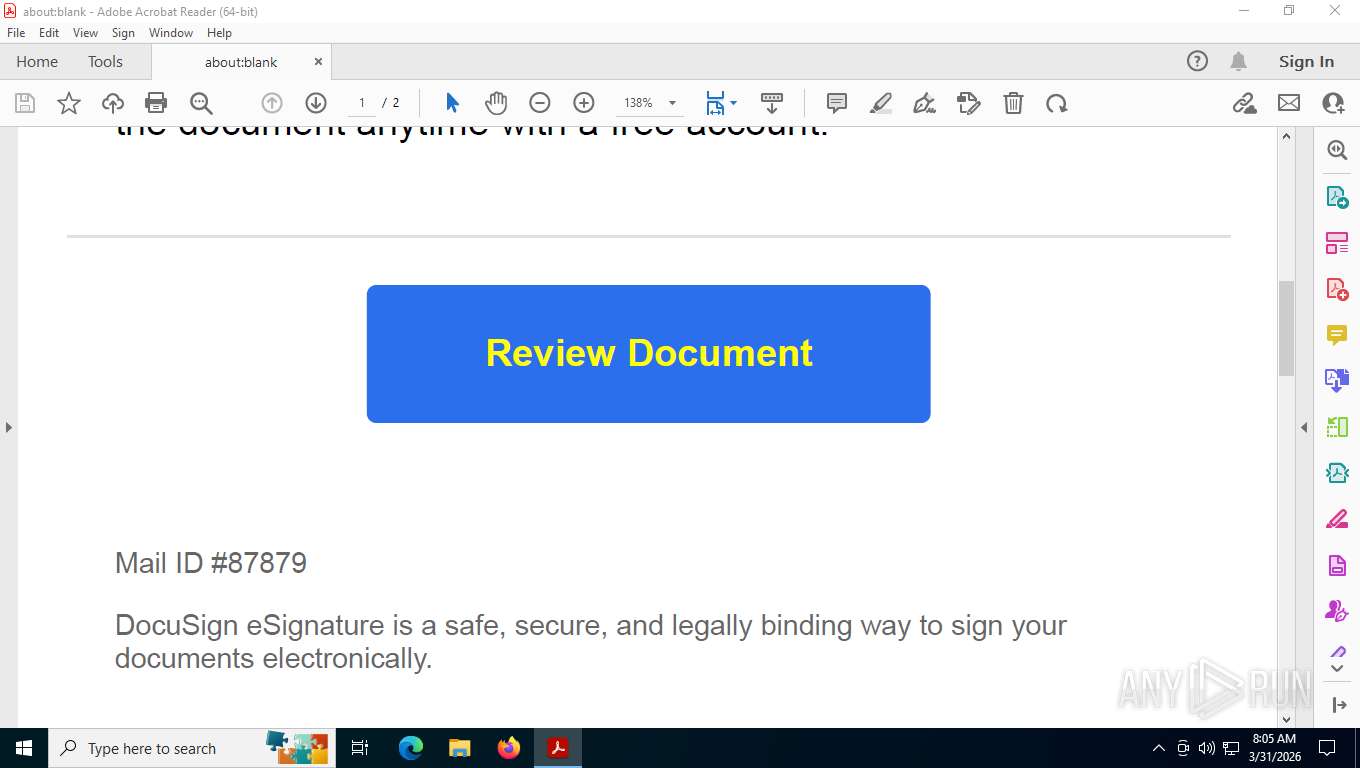
MALICIOUS
Detects suspicious words and phrases in PDF content (generic)
- Acrobat.exe (PID: 7664)
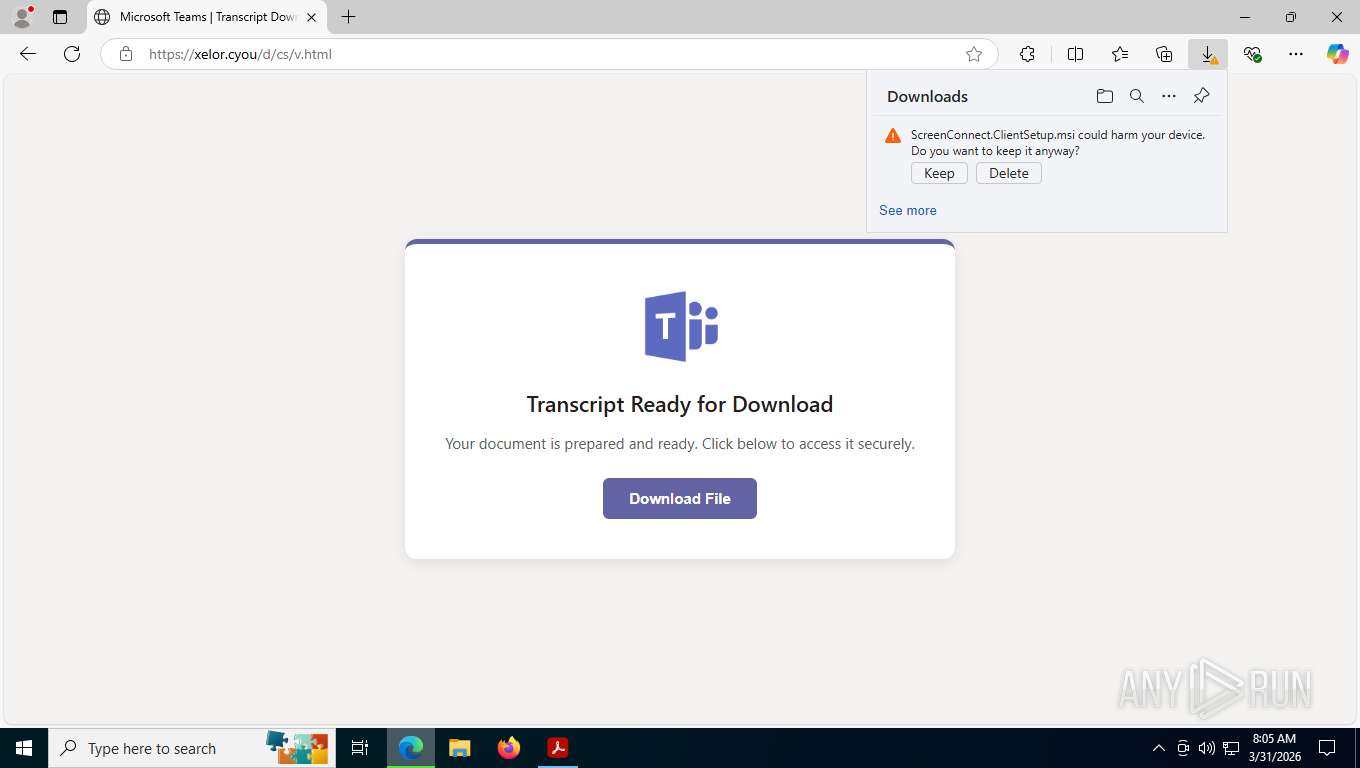
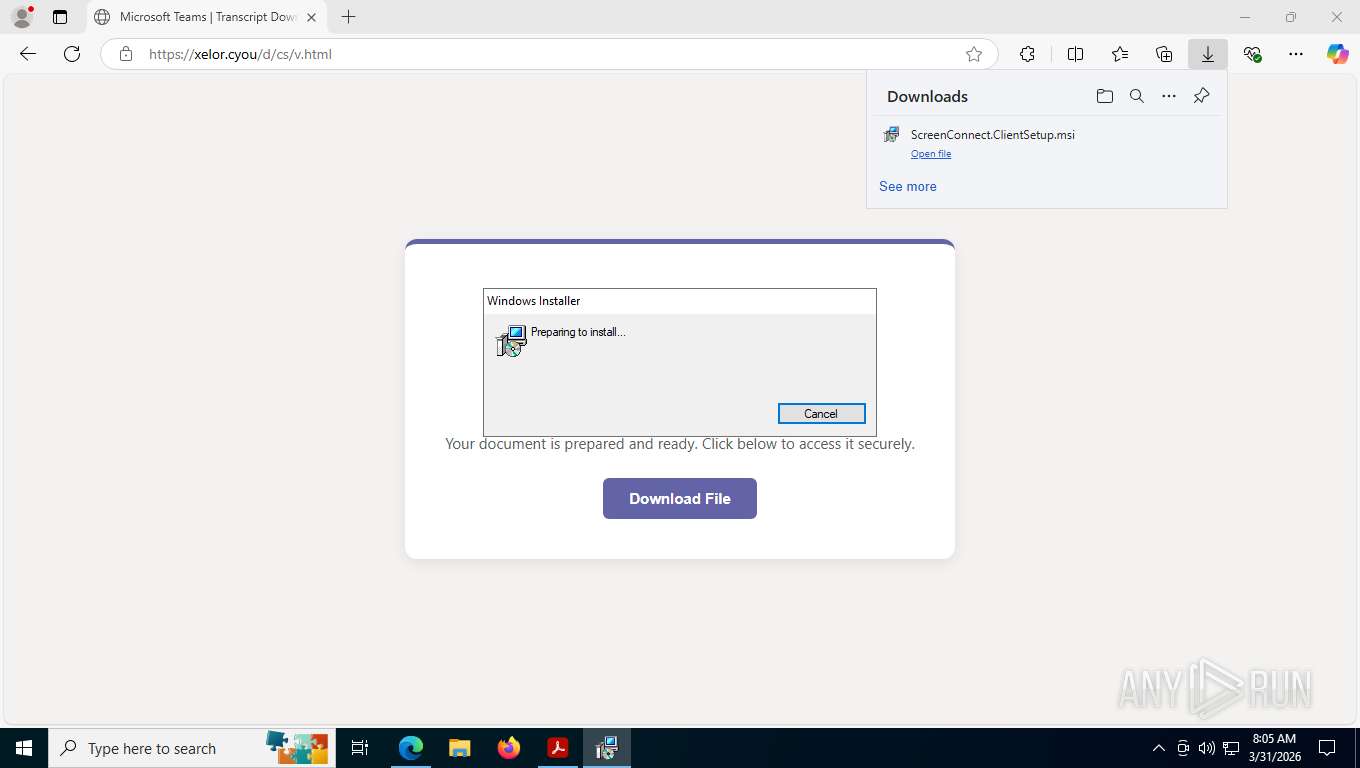
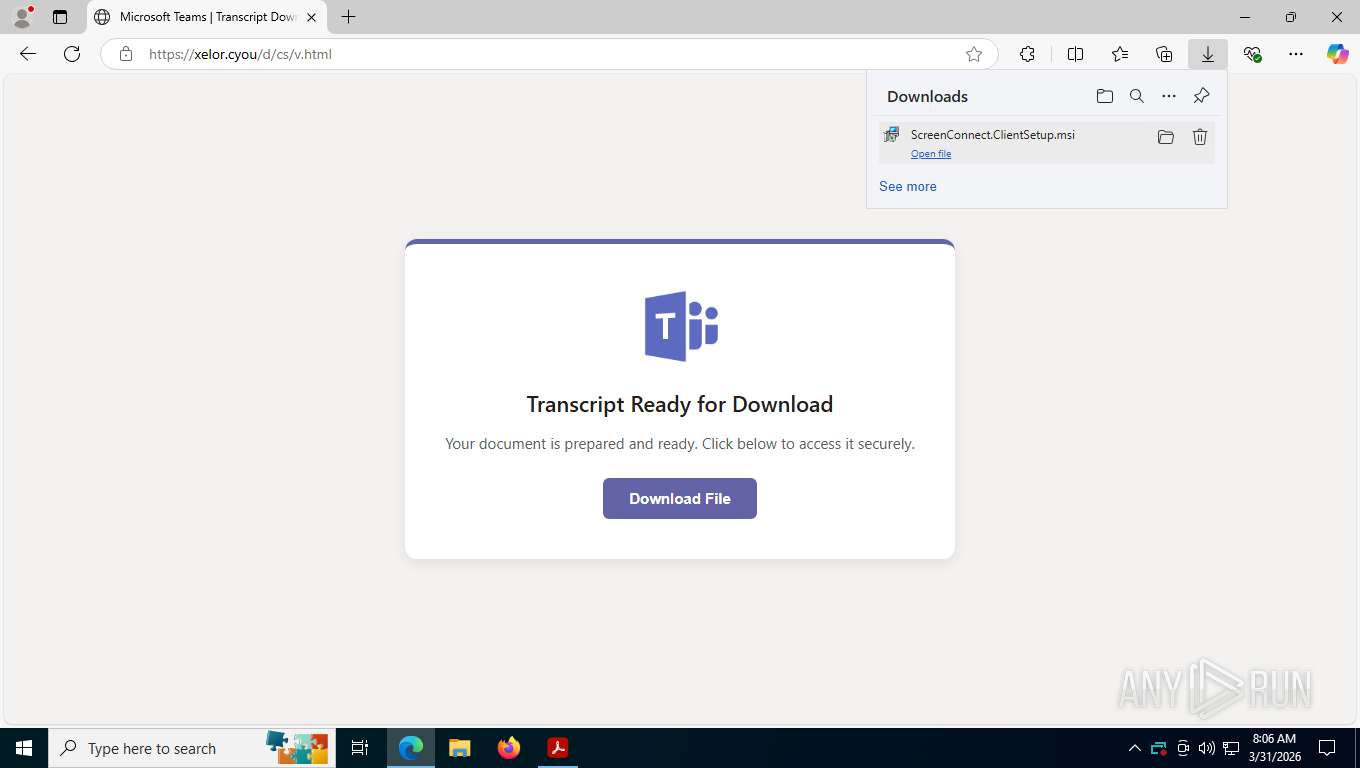
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 1352)
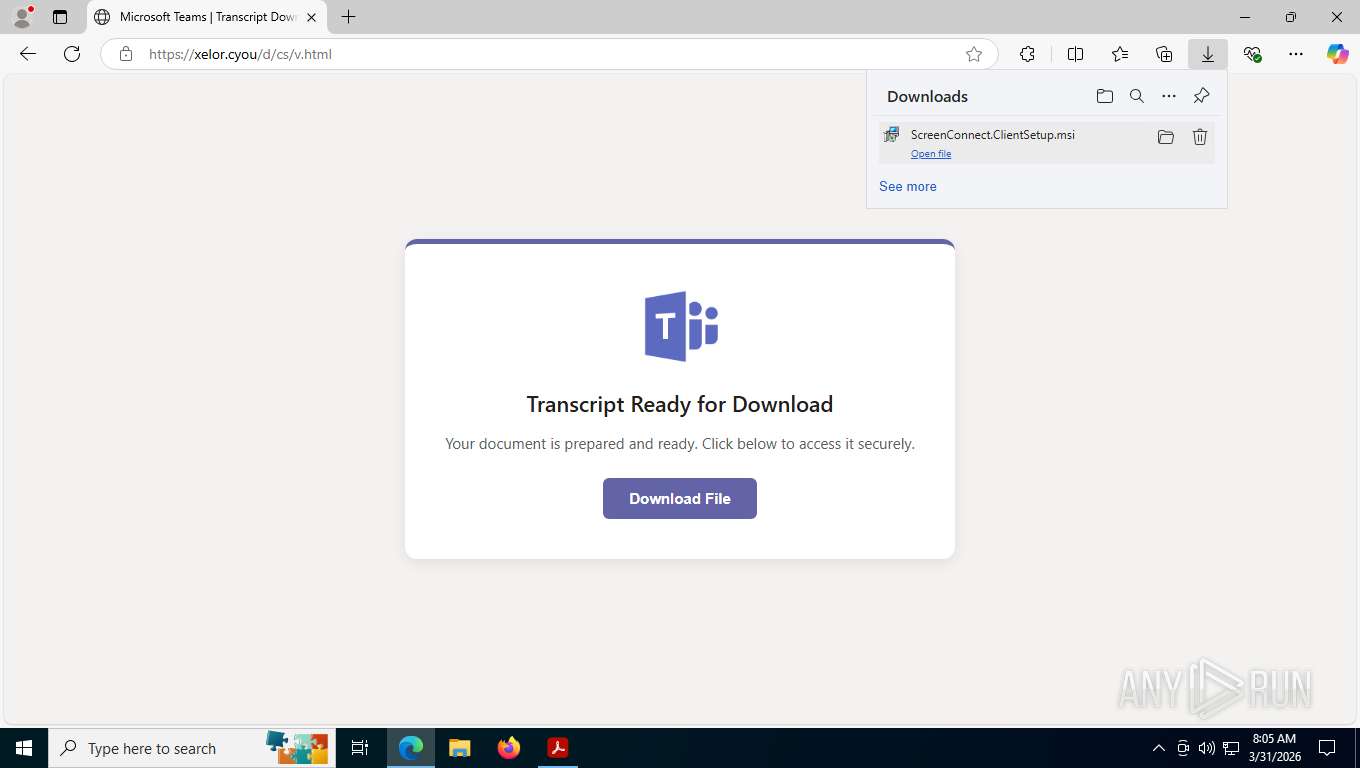
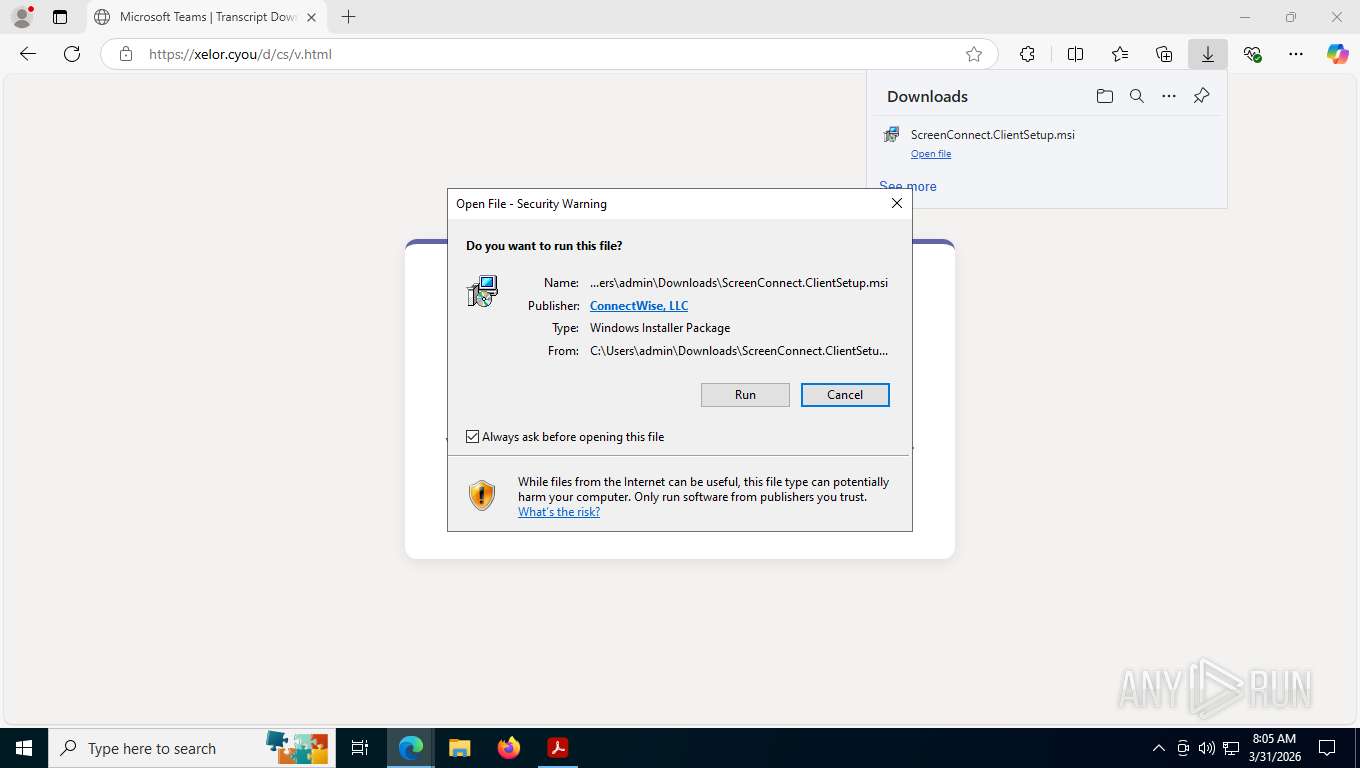
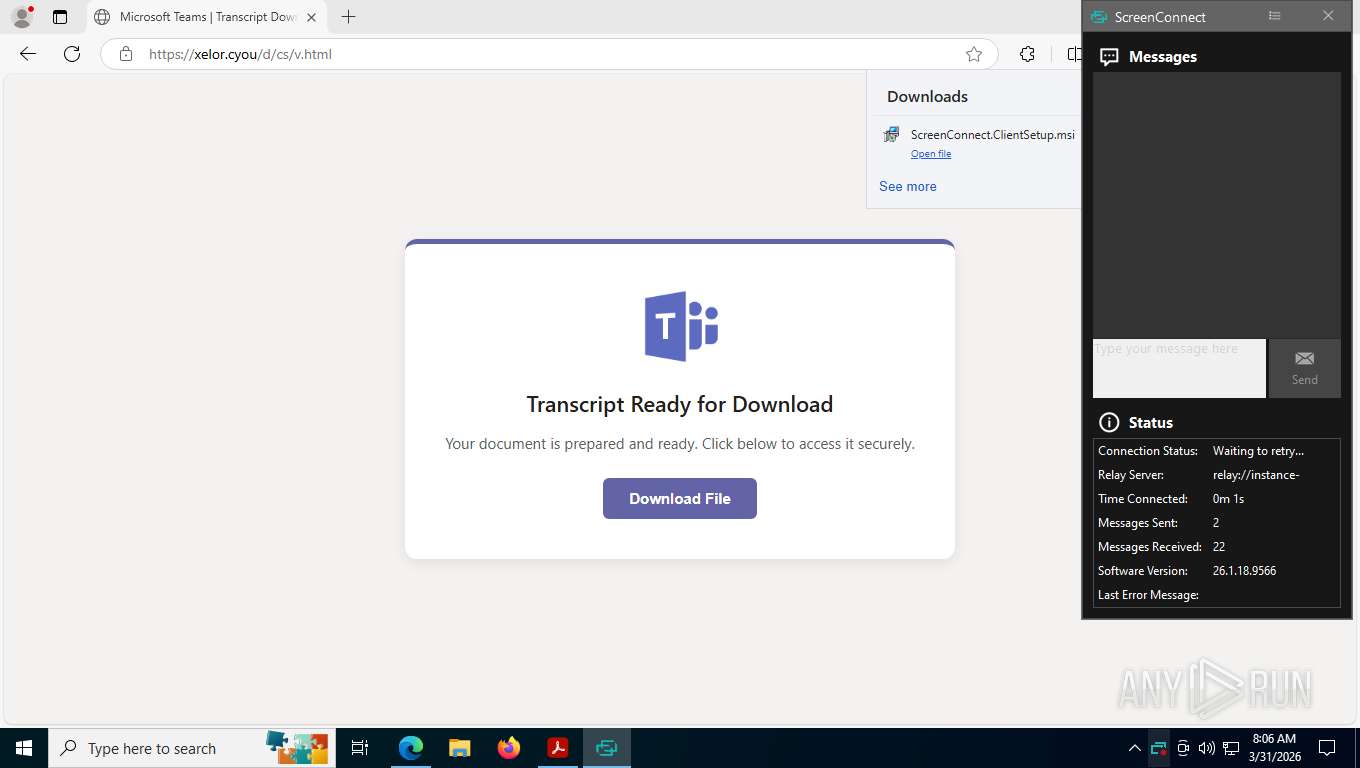
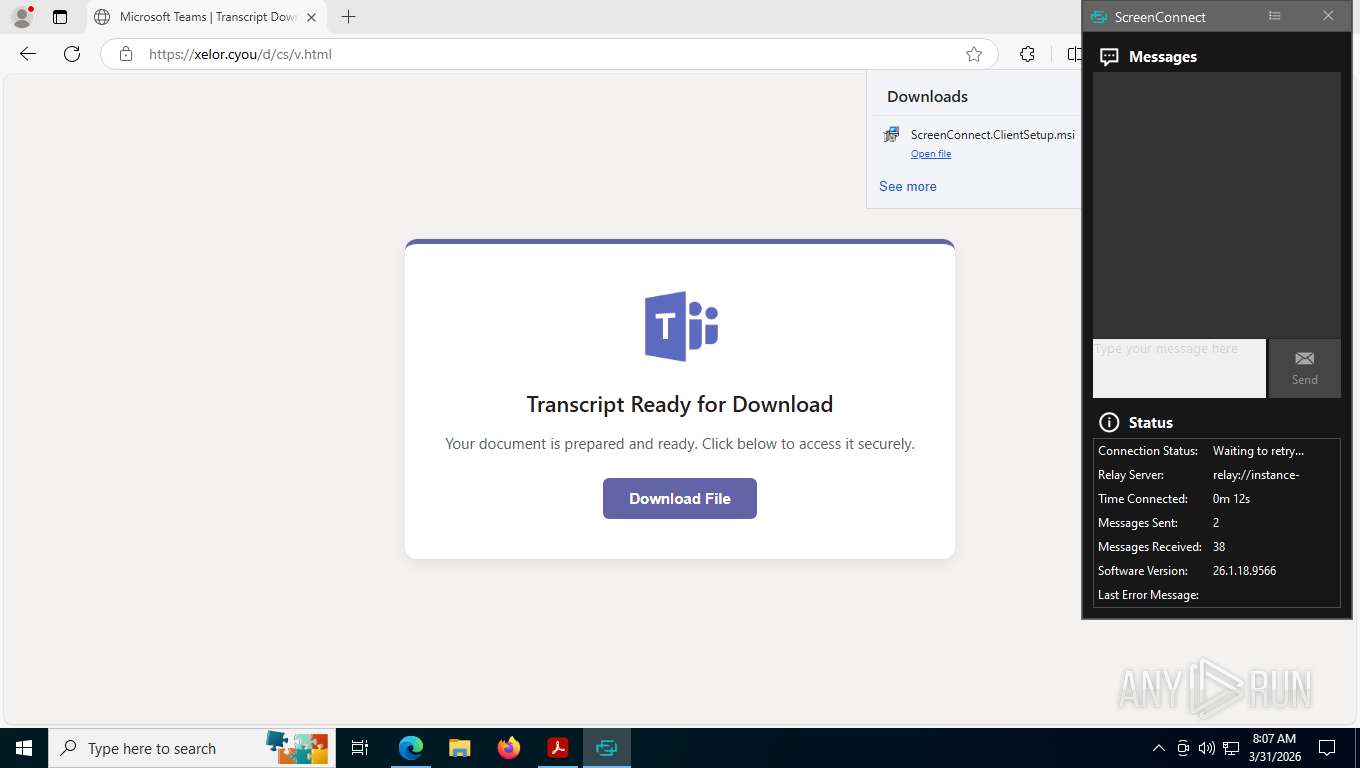
SCREENCONNECT has been detected
- msedge.exe (PID: 8184)
- rundll32.exe (PID: 8676)
- rundll32.exe (PID: 6092)
- rundll32.exe (PID: 5588)
- msiexec.exe (PID: 8244)
SUSPICIOUS
Executable content was dropped or overwritten
- rundll32.exe (PID: 8676)
- rundll32.exe (PID: 5588)
- rundll32.exe (PID: 6092)
Uses RUNDLL32.EXE to run a file without a DLL extension
- rundll32.exe (PID: 8676)
- rundll32.exe (PID: 5588)
Executes as Windows Service
- VSSVC.exe (PID: 8564)
- ScreenConnect.ClientService.exe (PID: 9932)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 9932)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 9932)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 9932)
- ScreenConnect.ClientService.exe (PID: 9932)
INFO
Application launched itself
- msedge.exe (PID: 7324)
- Acrobat.exe (PID: 7664)
- AcroCEF.exe (PID: 7604)
Checks supported languages
- identity_helper.exe (PID: 8672)
- msiexec.exe (PID: 5404)
- msiexec.exe (PID: 9852)
- msiexec.exe (PID: 9900)
- msiexec.exe (PID: 8244)
- ScreenConnect.ClientService.exe (PID: 9932)
- ScreenConnect.WindowsClient.exe (PID: 10000)
Reads Environment values
- identity_helper.exe (PID: 8672)
Reads the computer name
- identity_helper.exe (PID: 8672)
- msiexec.exe (PID: 5404)
- msiexec.exe (PID: 8244)
- msiexec.exe (PID: 9852)
- msiexec.exe (PID: 9900)
- ScreenConnect.ClientService.exe (PID: 9932)
- ScreenConnect.WindowsClient.exe (PID: 10000)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7984)
- ScreenConnect.WindowsClient.exe (PID: 10000)
- ScreenConnect.ClientService.exe (PID: 9932)
Create files in a temporary directory
- rundll32.exe (PID: 6092)
- rundll32.exe (PID: 8676)
- rundll32.exe (PID: 5588)
Disables trace logs
- rundll32.exe (PID: 6092)
- ScreenConnect.ClientService.exe (PID: 9932)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8244)
- msiexec.exe (PID: 7984)
Manages system restore points
- SrTasks.exe (PID: 9692)
CONNECTWISE has been detected
- msiexec.exe (PID: 7984)
- ScreenConnect.ClientService.exe (PID: 9932)
- ScreenConnect.WindowsClient.exe (PID: 10000)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 9932)
Reads the machine GUID from the registry
- ScreenConnect.ClientService.exe (PID: 9932)
- ScreenConnect.WindowsClient.exe (PID: 10000)
There is functionality for taking screenshot (YARA)
- AcroCEF.exe (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.4 |
|---|---|
| Linearized: | No |
| PageCount: | 2 |
| TaggedPDF: | Yes |
| Language: | en-US |
| Title: | about:blank |
| Creator: | Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) HeadlessChrome/146.0.0.0 Safari/537.36 |
| Producer: | Skia/PDF m146 |
| CreateDate: | 2026:03:31 06:31:39+00:00 |
| ModifyDate: | 2026:03:31 06:31:39+00:00 |
Total processes
201
Monitored processes
60
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2260,i,2734194041111846918,13656116609731365562,262144 --variations-seed-version --mojo-platform-channel-handle=2276 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=utility --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2112 --field-trial-handle=1584,i,8043792250417974188,5918364108156783506,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2132 --field-trial-handle=1584,i,8043792250417974188,5918364108156783506,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | AcroCEF.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2332,i,2734194041111846918,13656116609731365562,262144 --variations-seed-version --mojo-platform-channel-handle=2488 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1788 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6896,i,2734194041111846918,13656116609731365562,262144 --variations-seed-version --mojo-platform-channel-handle=6468 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1336 --field-trial-handle=1584,i,8043792250417974188,5918364108156783506,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" --type=renderer /prefetch:1 "C:\Users\admin\AppData\Local\Temp\hrvoje.sitar Vertex b.s. d.o.o. Contract & Payoff Aqreement_928.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | Acrobat.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=renderer --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --touch-events=enabled --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2964 --field-trial-handle=1584,i,8043792250417974188,5918364108156783506,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 3084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7808,i,2734194041111846918,13656116609731365562,262144 --variations-seed-version --mojo-platform-channel-handle=5040 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4240 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2632 --field-trial-handle=1584,i,8043792250417974188,5918364108156783506,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
Total events
28 224
Read events
27 930
Write events
283
Delete events
11
Modification events
| (PID) Process: | (7664) Acrobat.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Mappings\S-1-15-2-2034283098-2252572593-1072577386-2659511007-3245387615-27016815-3920691934 |
| Operation: | write | Name: | DisplayName |
Value: Adobe Acrobat Reader Protected Mode | |||
| (PID) Process: | (2652) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2652) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVEntitlement |
| Operation: | write | Name: | bSynchronizeOPL |
Value: 0 | |||
| (PID) Process: | (2652) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVGeneral |
| Operation: | write | Name: | uLastAppLaunchTimeStamp |
Value: | |||
| (PID) Process: | (2652) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVGeneral |
| Operation: | write | Name: | iNumAcrobatLaunches |
Value: 7 | |||
| (PID) Process: | (2652) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (2652) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\ToolsSearch |
| Operation: | write | Name: | iSearchHintIndex |
Value: 3 | |||
| (PID) Process: | (2652) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVEntitlement |
| Operation: | write | Name: | sProductGUID |
Value: 4143524F4241545F475549445F4E474C5F44554D4D5900 | |||
| (PID) Process: | (2652) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVEntitlement |
| Operation: | write | Name: | sProductGUID |
Value: 4143524F5F5245534944554500 | |||
| (PID) Process: | (7664) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AdobeViewer |
| Operation: | delete value | Name: | ProductInfoCache |
Value: | |||
Executable files
40
Suspicious files
229
Text files
362
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7604 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\72d9f526d2e2e7c8_0 | binary | |
MD5:5894108ECE9FBB338FE651AB2512598A | SHA256:079DAD7AFDF50CD9081302EB4CB93FB3377248F785E6AC7933FF0CE170A63D55 | |||
| 7604 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\0786087c3c360803_0 | binary | |
MD5:ED6278846A4BFD6699178467601089A4 | SHA256:B74423FFF4F618BAABDF7FCF6E5541EAA4B004954D5CB30F3E979445EED8DDB4 | |||
| 7604 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\4a0e94571d979b3c_0 | binary | |
MD5:28BA1FBA662B1BC719C322A7FEE50EFB | SHA256:0B85747D889EB06C4CC71098C0D39E3090C5049219915DAD8E293D545EA1FD11 | |||
| 2652 | Acrobat.exe | C:\Users\admin\AppData\Local\Temp\acrobat_sbx\acroNGLLog.txt | text | |
MD5:052459A28E1C3FB06E9572D67E61CDBF | SHA256:07DAEA368D8D3F391108C3973C20F2F40A5CB8AC3EC437217CC5A3E44F12BB57 | |||
| 2652 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\SOPHIA.json | text | |
MD5:837C1211E392A24D64C670DC10E8DA1B | SHA256:8013AC030684B86D754BBFBAB8A9CEC20CAA4DD9C03022715FF353DC10E14031 | |||
| 7604 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\bba29d2e6197e2f4_0 | binary | |
MD5:0B70BAC88320AB1FC2B12BA47A289E69 | SHA256:3E69C0F9014FE0FBF3189EEA04CDD7609195ED1CE8F2EEC45B3083EC2E8359DF | |||
| 2652 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SharedDataEvents-journal | binary | |
MD5:AA46DFCFCA00BBEC5F90DE0A2A61A6D3 | SHA256:DE35C61249E9827243D844952C4179775B9F0B8531A3D54EFBC5B7D733FD390C | |||
| 7604 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\983b7a3da8f39a46_0 | binary | |
MD5:7284B57B902FBC9C712CDBAFEE82EC08 | SHA256:733FE029ECAE35B7EC8BD84E984A9684E64B187B3C623949916D1472355D1905 | |||
| 7604 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\560e9c8bff5008d8_0 | binary | |
MD5:1AC59ACA4A0682ACE8171545C6F7332C | SHA256:AA5DC3B2748A632497DB670B224CCB4F97584E20F9132E509FD982B00DF7D53A | |||
| 2652 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\TESTING | binary | |
MD5:DC84B0D741E5BEAE8070013ADDCC8C28 | SHA256:81FF65EFC4487853BDB4625559E69AB44F19E0F5EFBD6D5B2AF5E3AB267C8E06 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
117
TCP/UDP connections
102
DNS requests
106
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
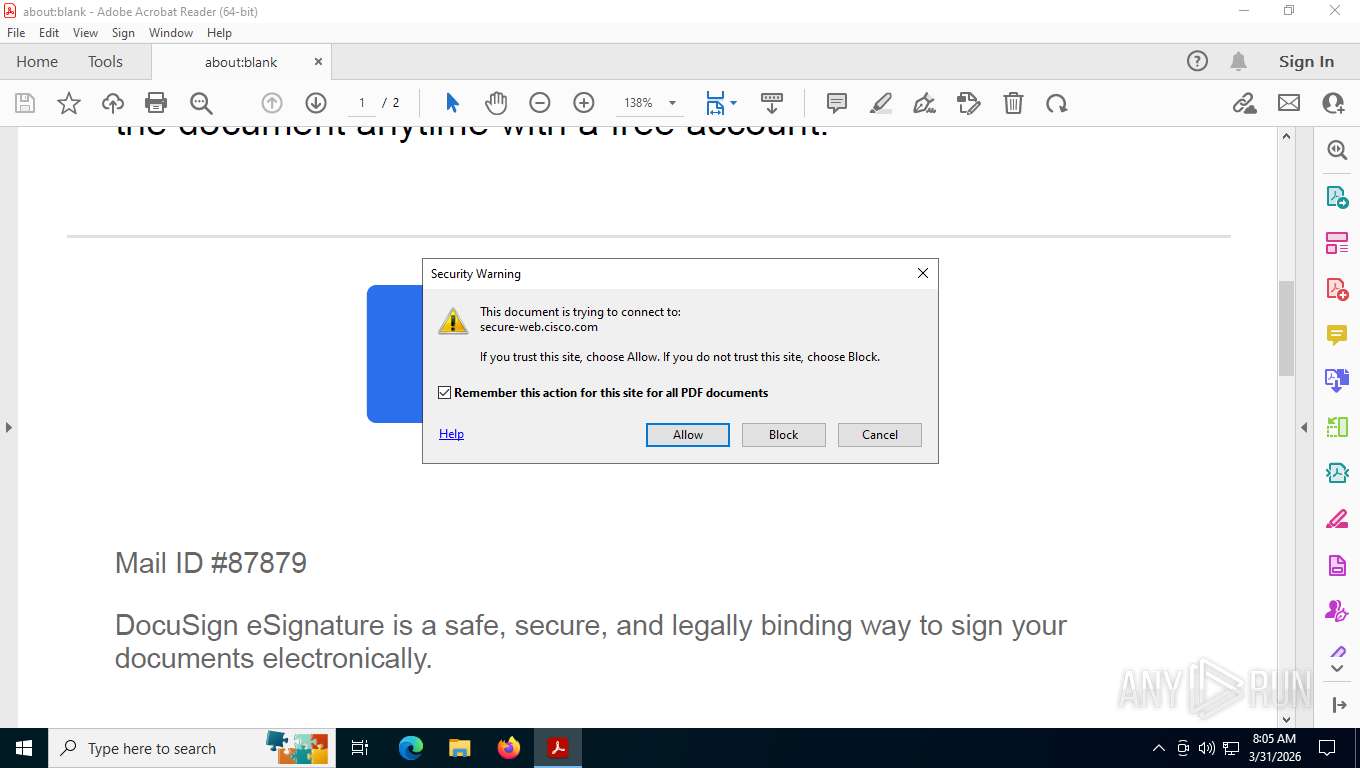
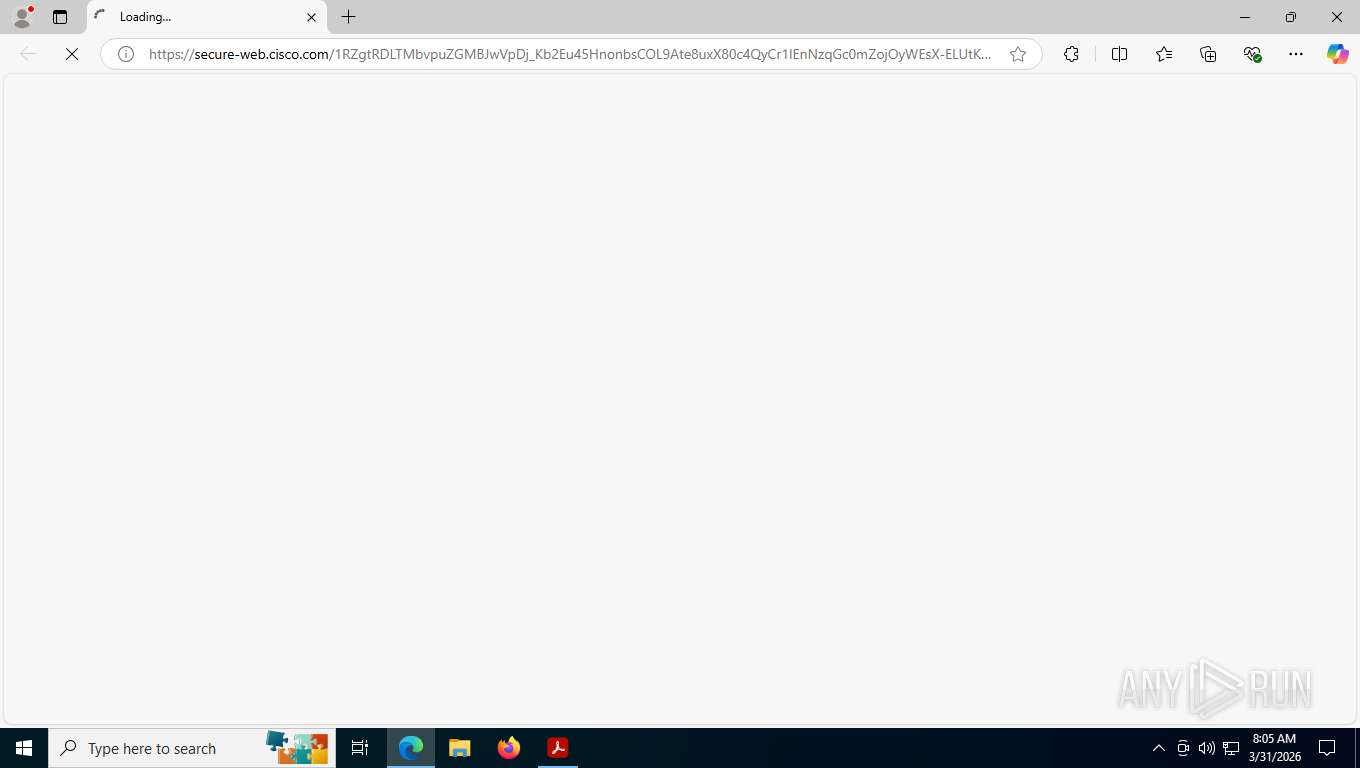
1352 | msedge.exe | GET | 302 | 146.112.255.69:443 | https://secure-web.cisco.com/1RZgtRDLTMbvpuZGMBJwVpDj_Kb2Eu45HnonbsCOL9Ate8uxX80c4QyCr1IEnNzqGc0mZojOyWEsX-ELUtK5B93yFlrPYKUyXrIoDlDnG5PS0oyXSILgFp3junfA1XUlomQk6JXWLWhPWo13UmyGEnPuO1tFFDVYCAhegpKN52QCJPTdvBIhEQCo-hzRPSxDIaYuHNkWW_mQnLMuiFRBqhv15Hiha034s8l9BhfOWObikgaDrrVzrXooj6xBpj6C6OEROwtIhBv-9XtXYKwFQy54AITzu_QSIKj5SDPS51uwewa2E4yFt-DlUx9tpidGNHOdqtzozLe6fsKAxPj8QEt62GIEqDIMC7n_5gOcuoiJWoS148kUUVwREOLu9d27LPgD75d0VHh9MrvFE_9dgSIyfgsprZsh3yF6dmGOAmZEDppO0fSwr7iXkDJ798URxKO27uWswz_3HNfjexem6WA/https%3A%2F%2Fsportspromotion.mx%2Fscr | US | — | — | whitelisted |
1352 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.42 Kb | whitelisted |
— | — | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 313 b | whitelisted |
6076 | svchost.exe | GET | 200 | 20.44.239.154:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.74 Kb | whitelisted |
1352 | msedge.exe | GET | 200 | 13.107.226.45:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
1352 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
1352 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1774958724&lafgdate=0 | US | text | 43.4 Kb | whitelisted |
1352 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:exn1ACHTLipfvL36KqQTInampYuJGRhcYW2RnU6s-yI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 99 b | whitelisted |
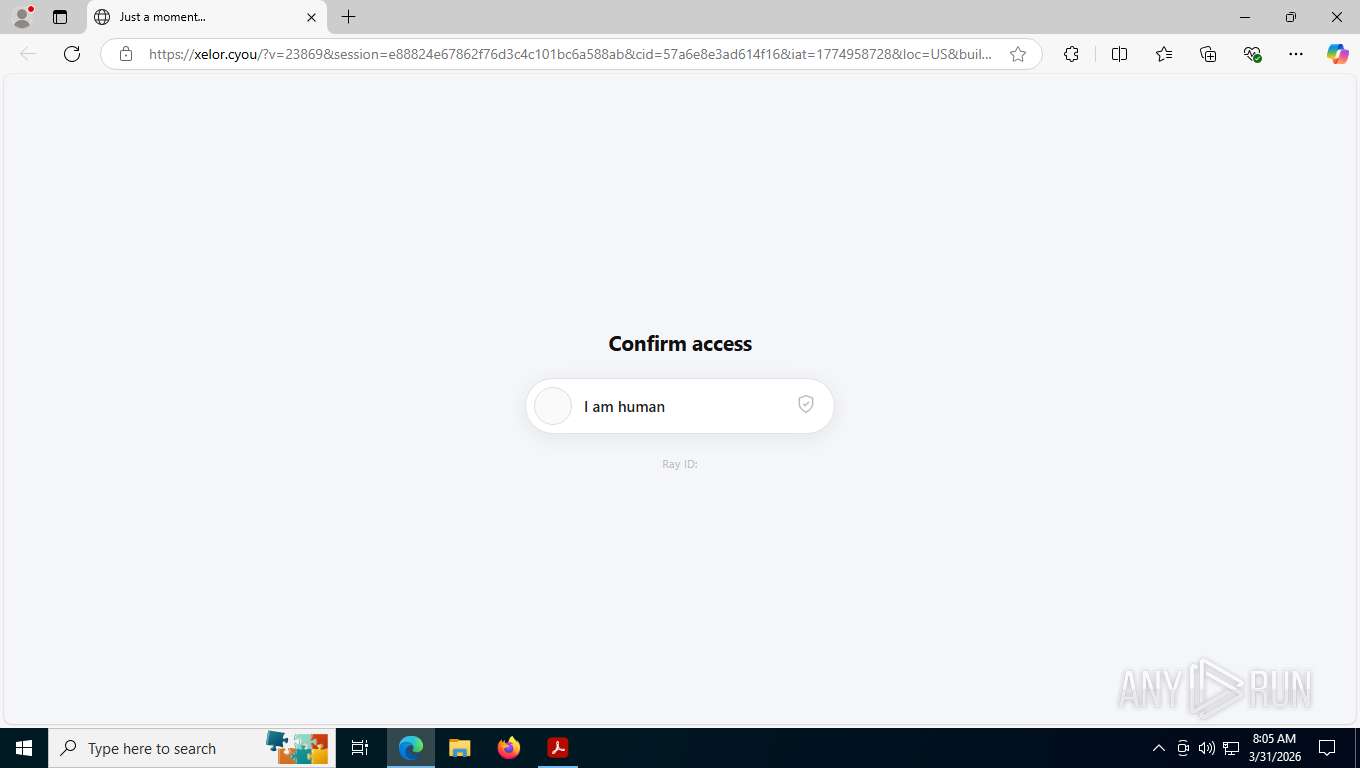
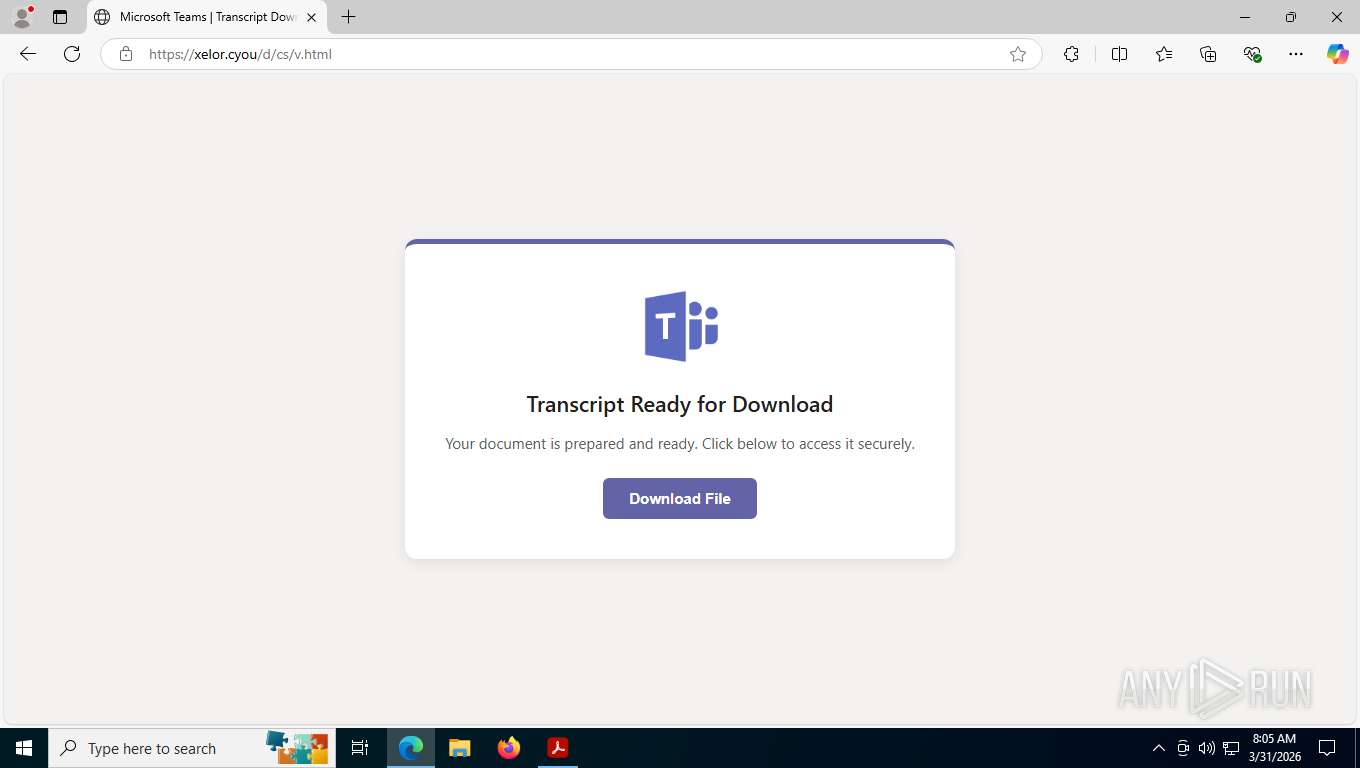
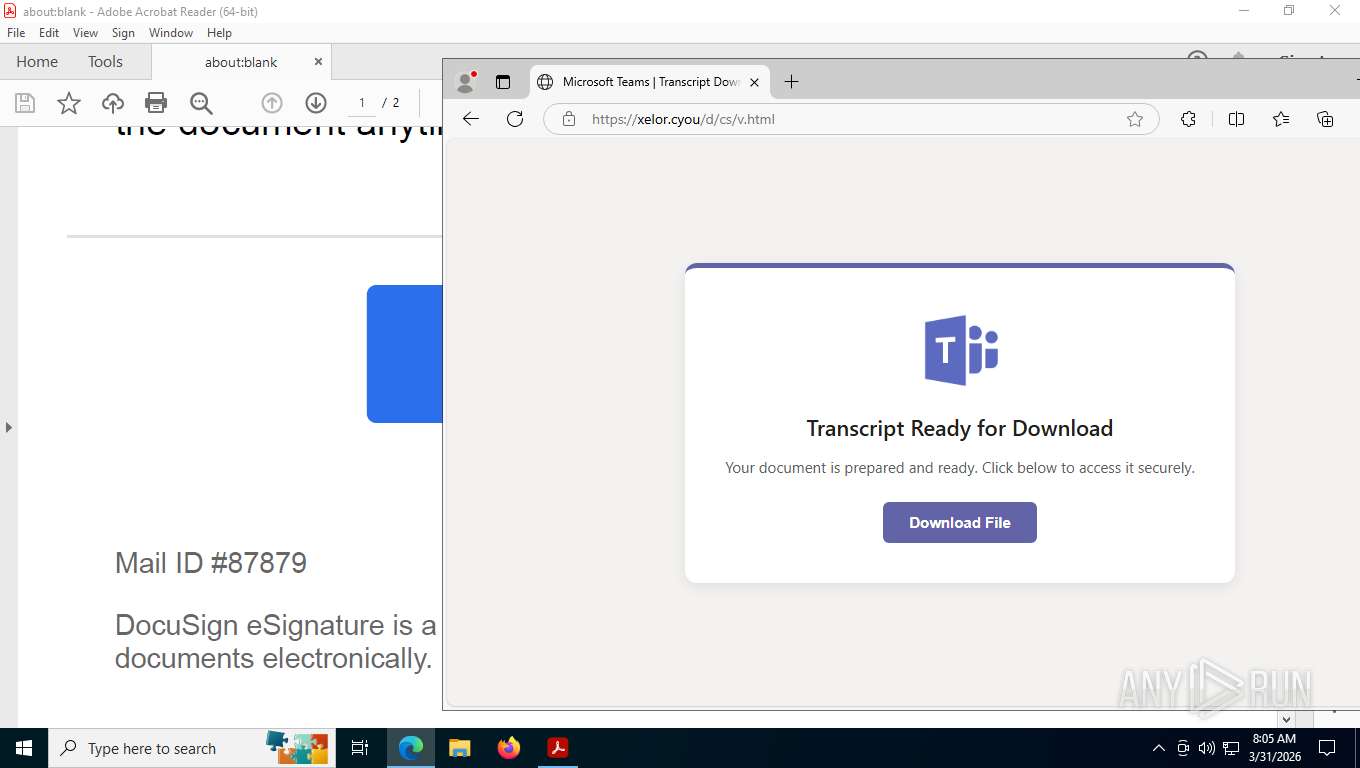
1352 | msedge.exe | GET | 200 | 104.21.94.75:443 | https://xelor.cyou/d/cs/v.html | US | html | 1.24 Kb | malicious |
1352 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6076 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 2.16.241.204:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6076 | svchost.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1176 | AcroCEF.exe | 88.221.168.141:443 | geo2.adobe.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
geo2.adobe.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6076 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1352 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Fake CAPTCHA Redirect Page URL Pattern |
1352 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Fake CAPTCHA Redirect Page URL Pattern |
1352 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
1352 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
1352 | msedge.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
1352 | msedge.exe | A Network Trojan was detected | ET MALWARE RMM Payload Delivery Behvaior Observed in HTTP Cookies |
1352 | msedge.exe | A Network Trojan was detected | ET MALWARE RMM Payload Delivery Behvaior Observed in HTTP Cookies |
1352 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1352 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |