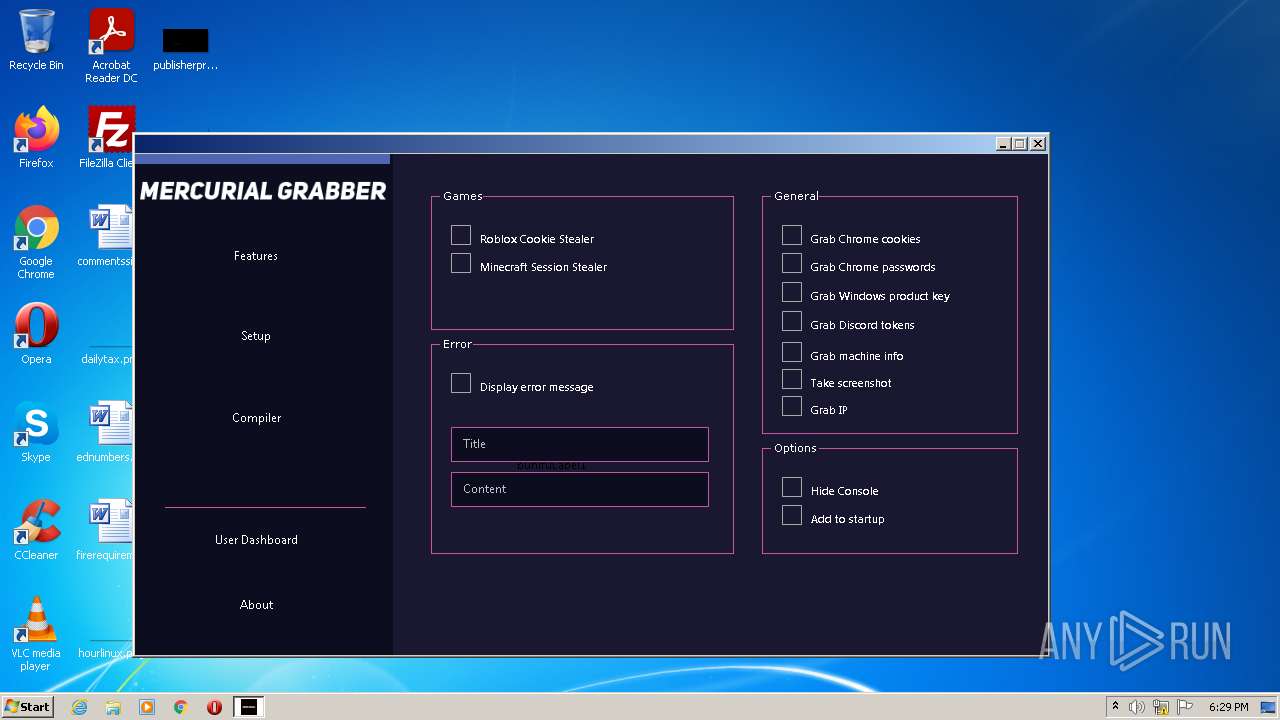
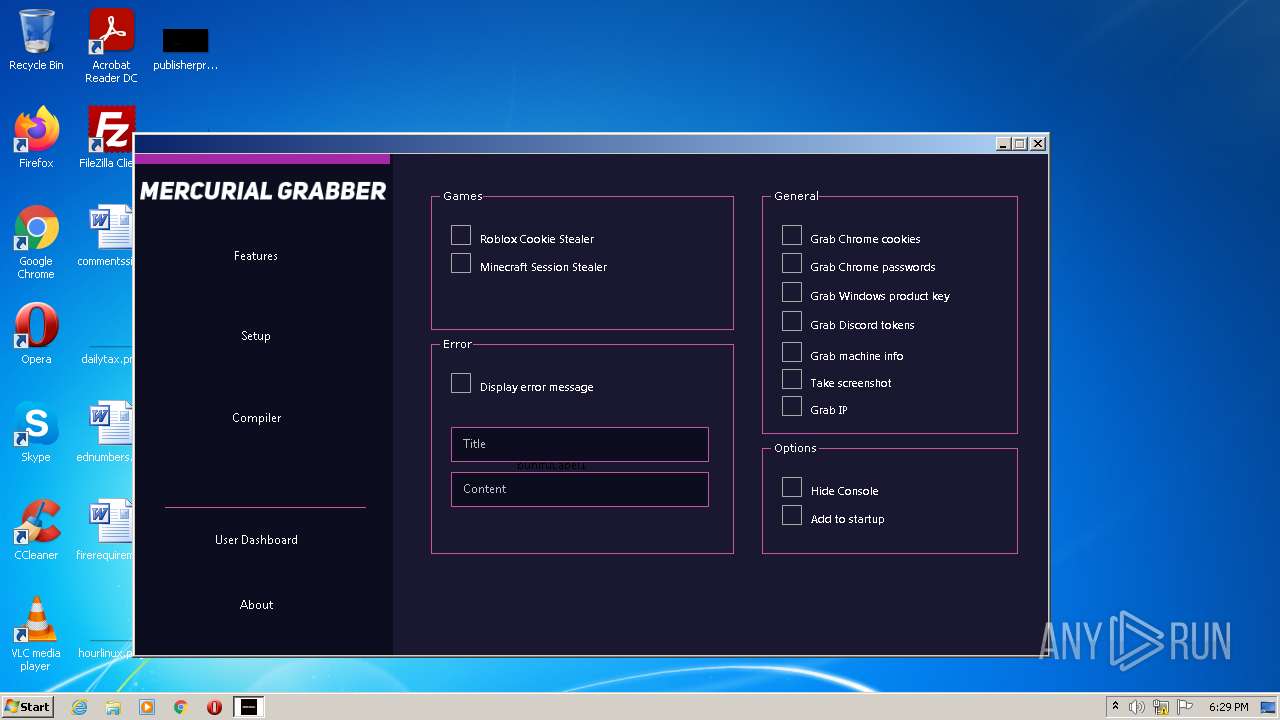
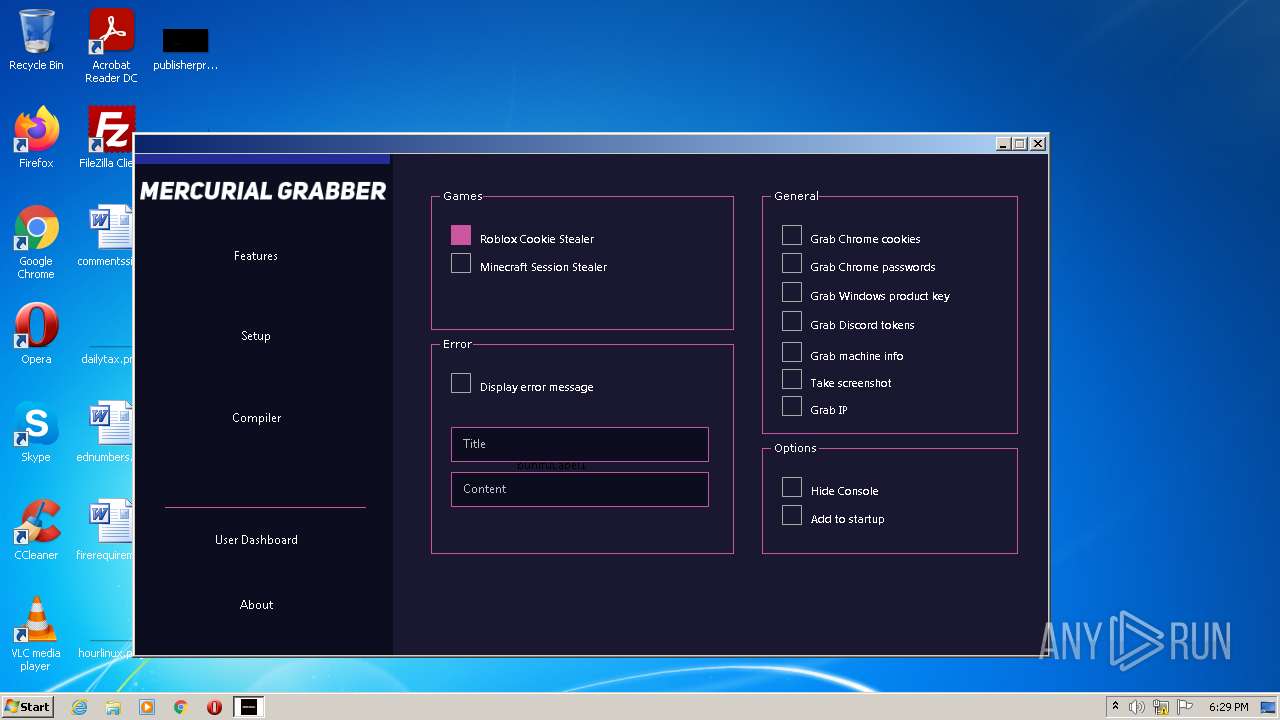
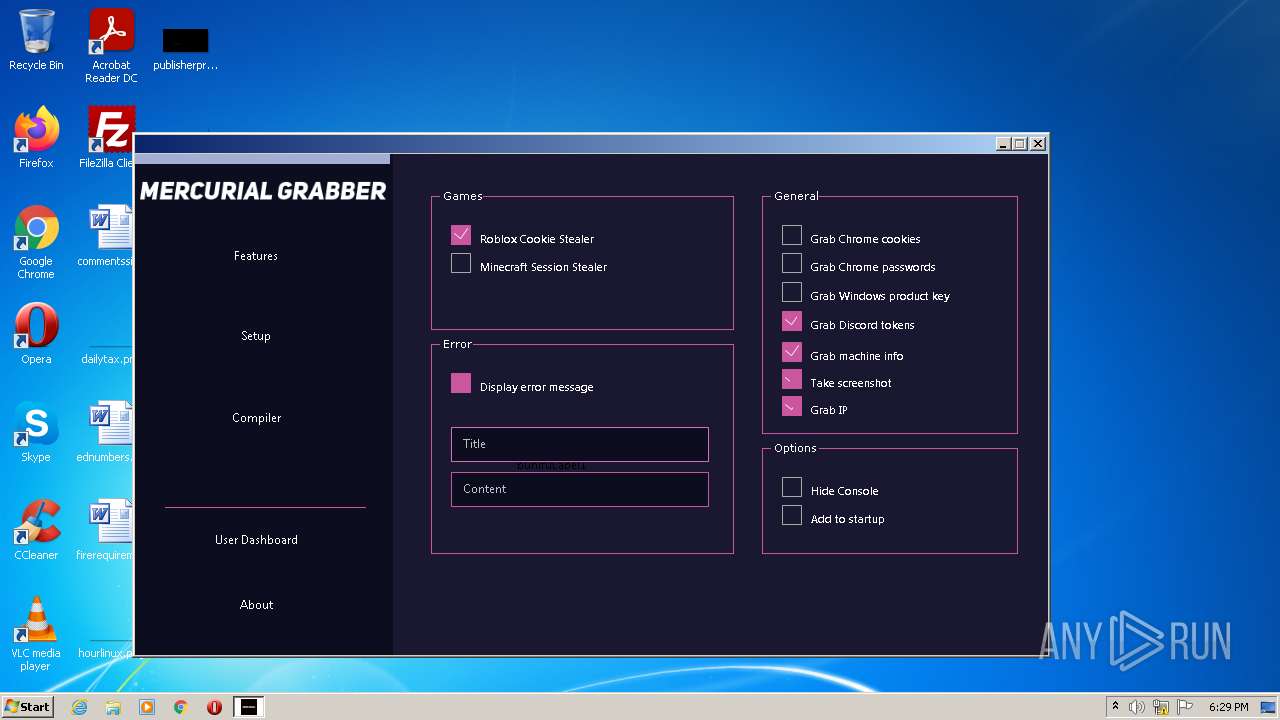
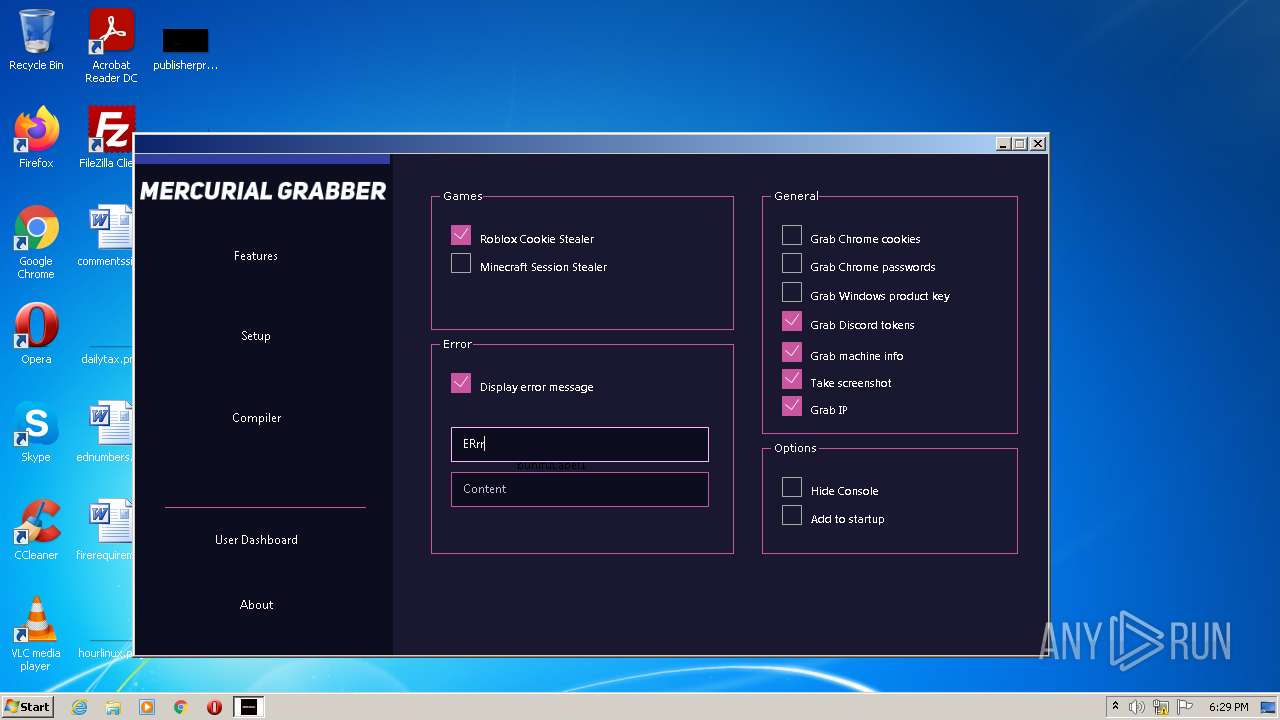
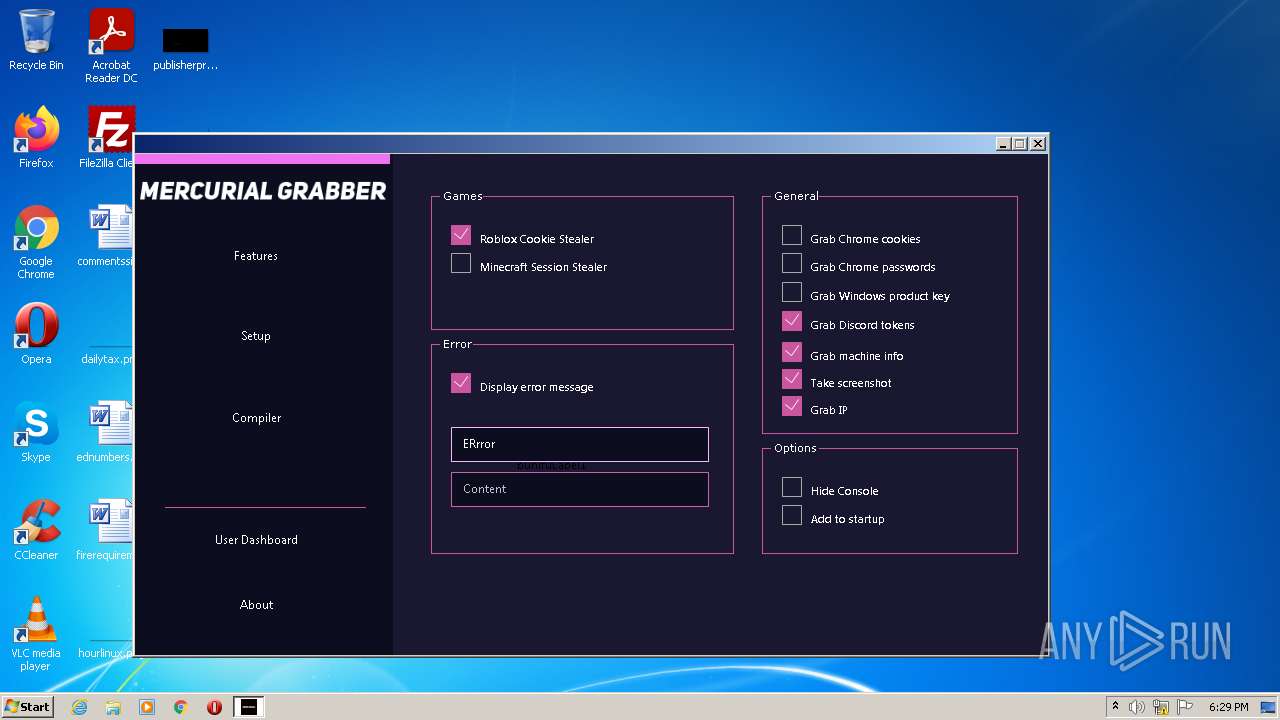
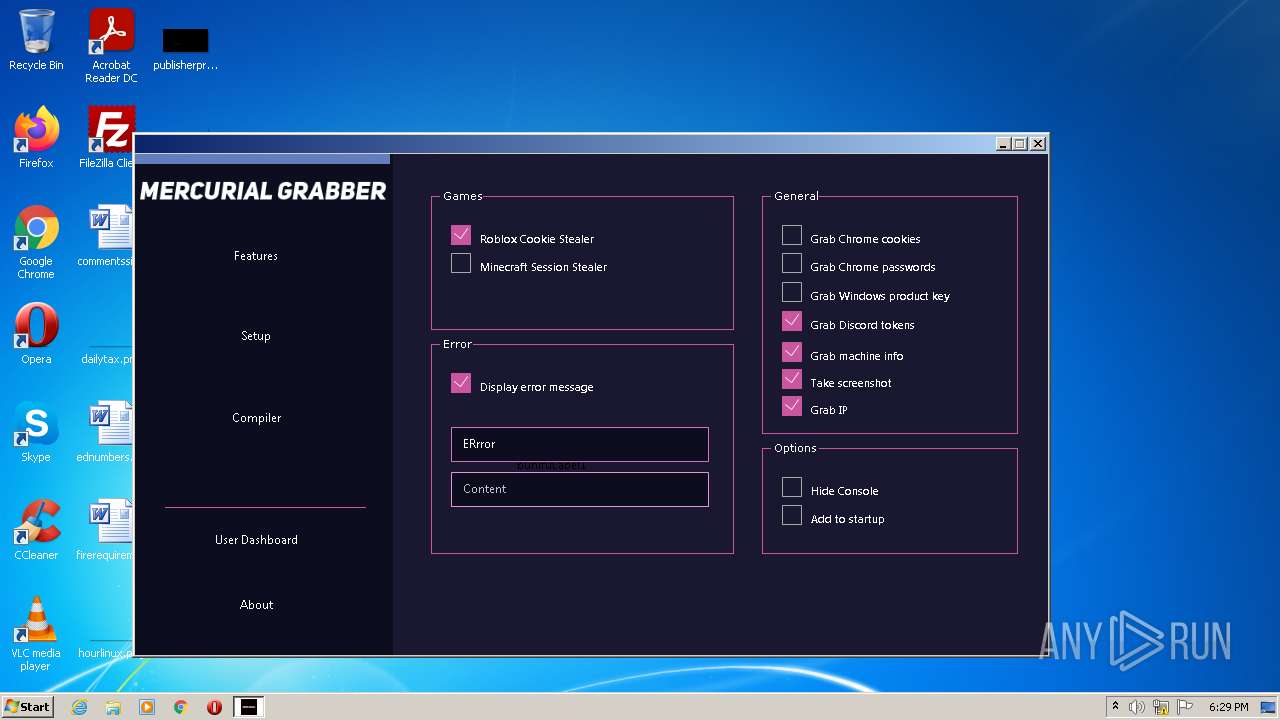
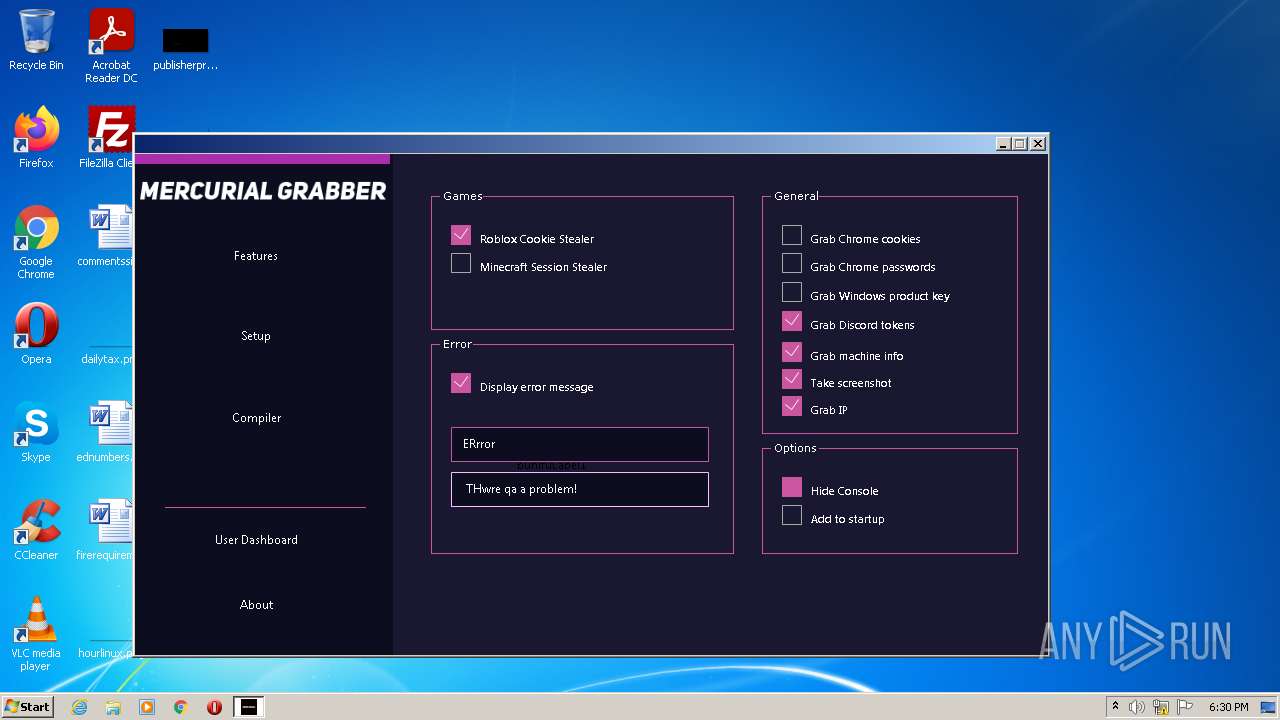
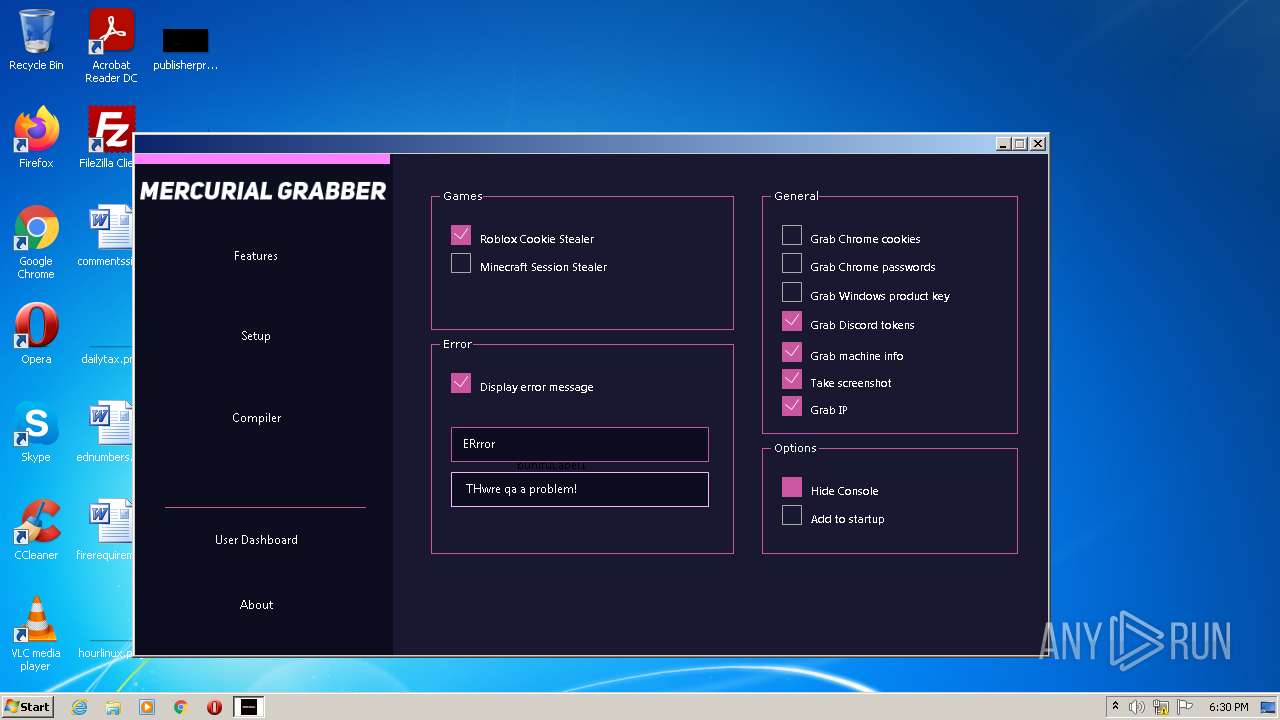
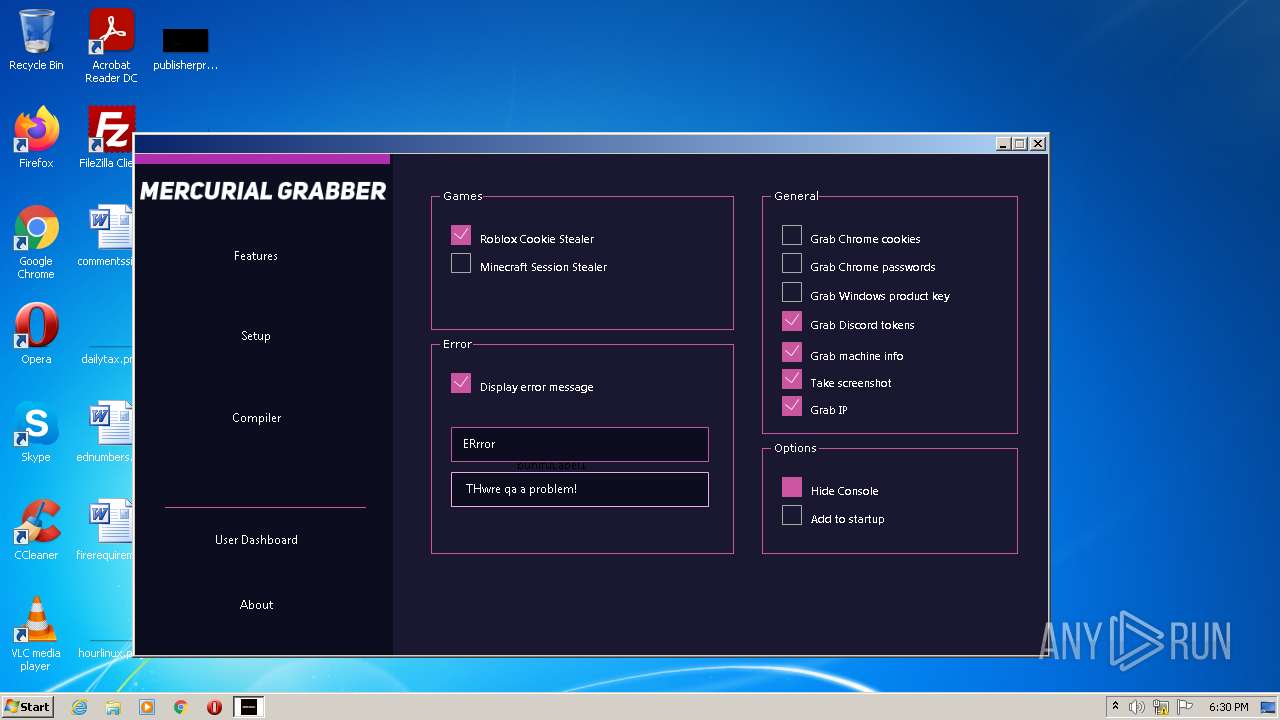
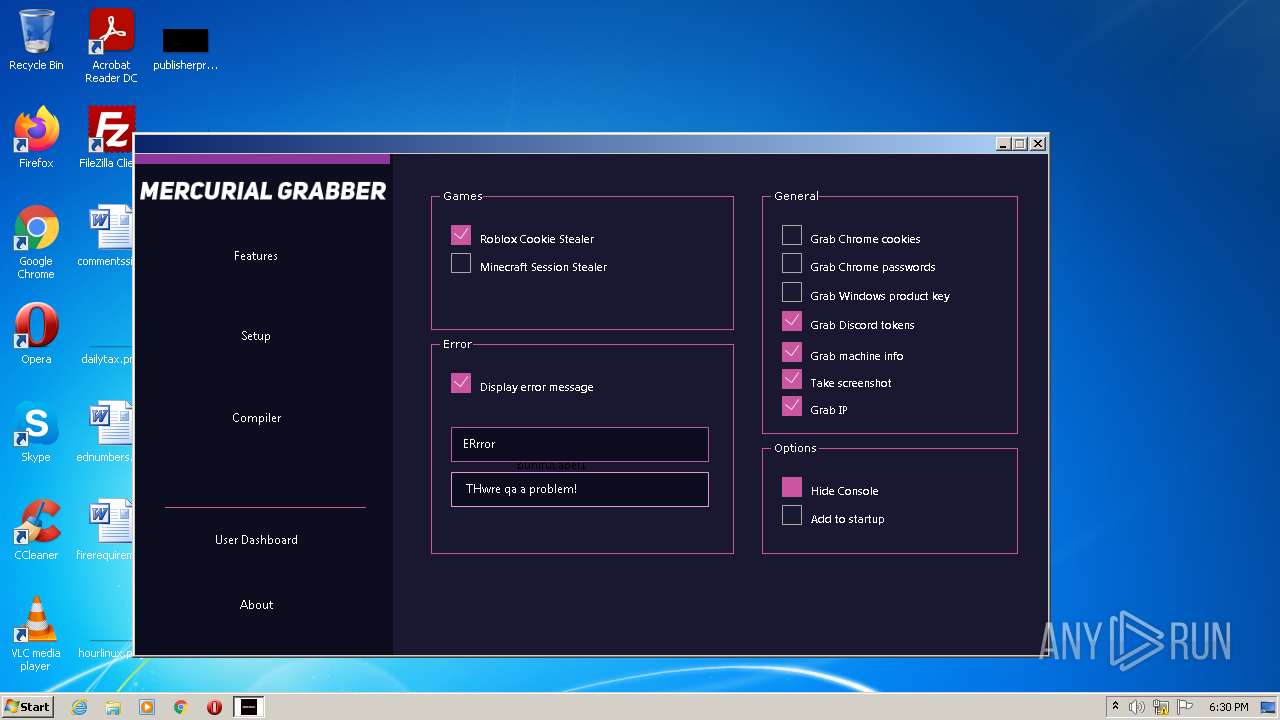
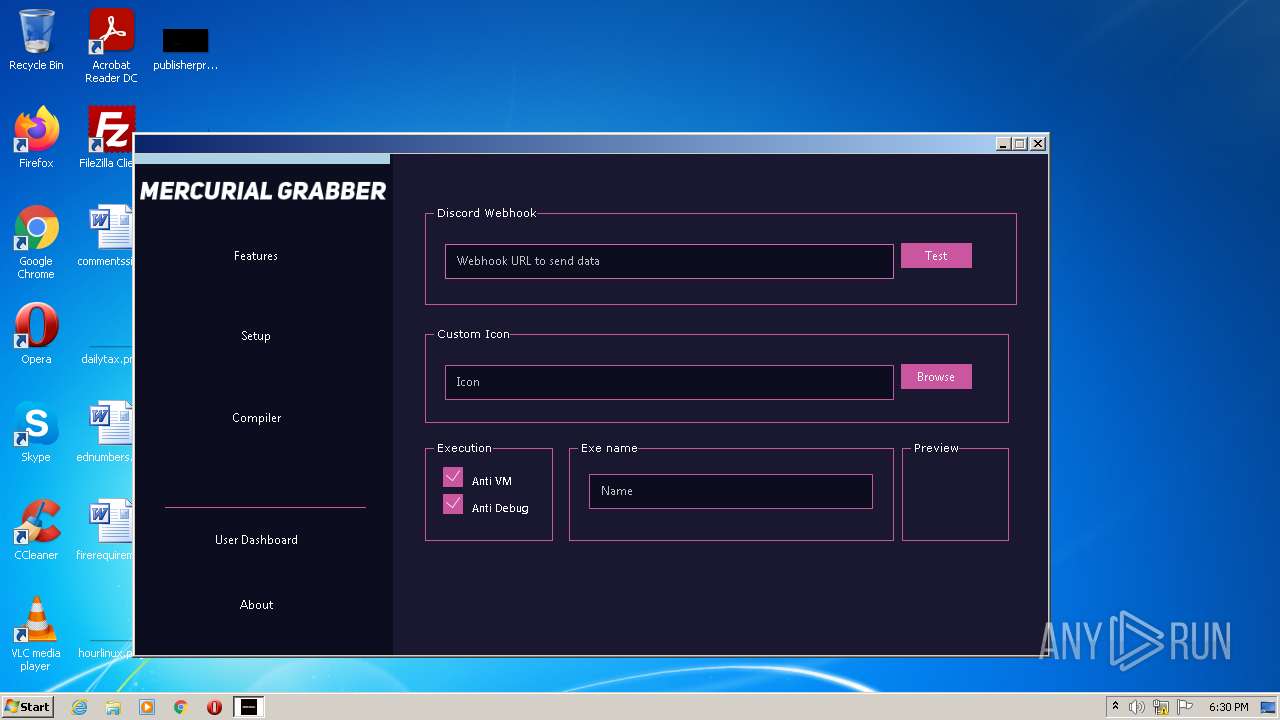
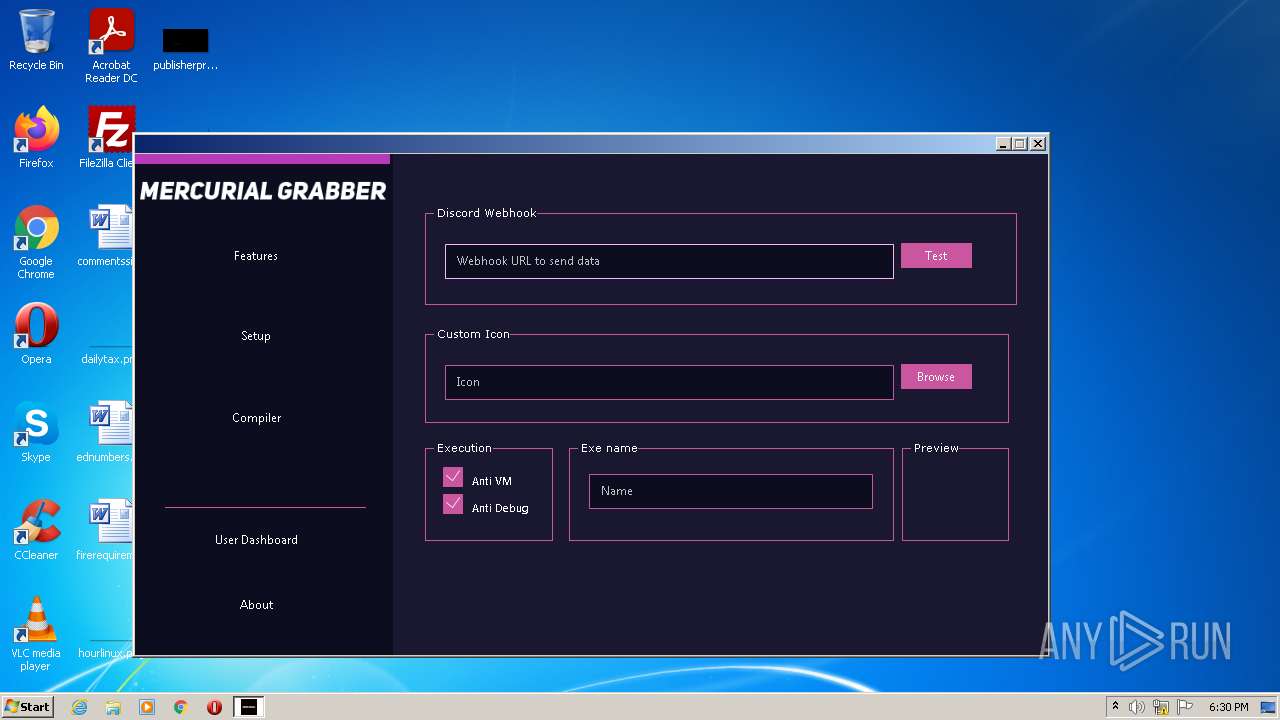
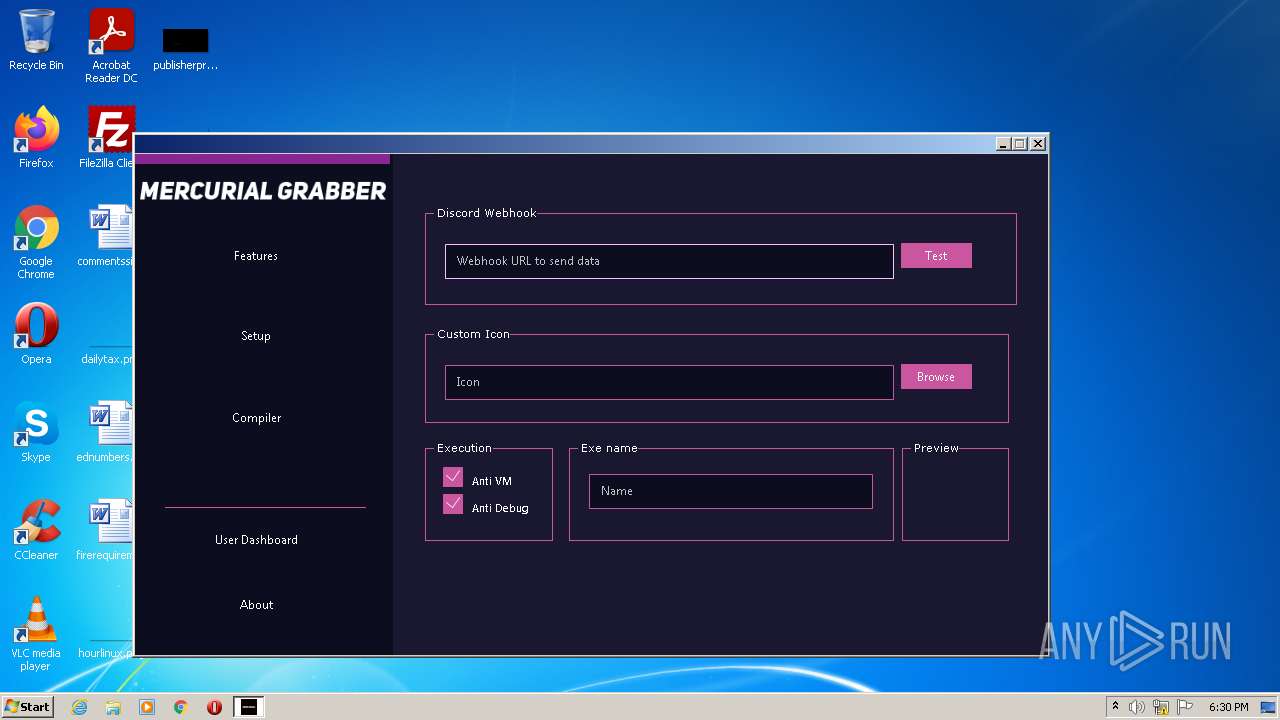
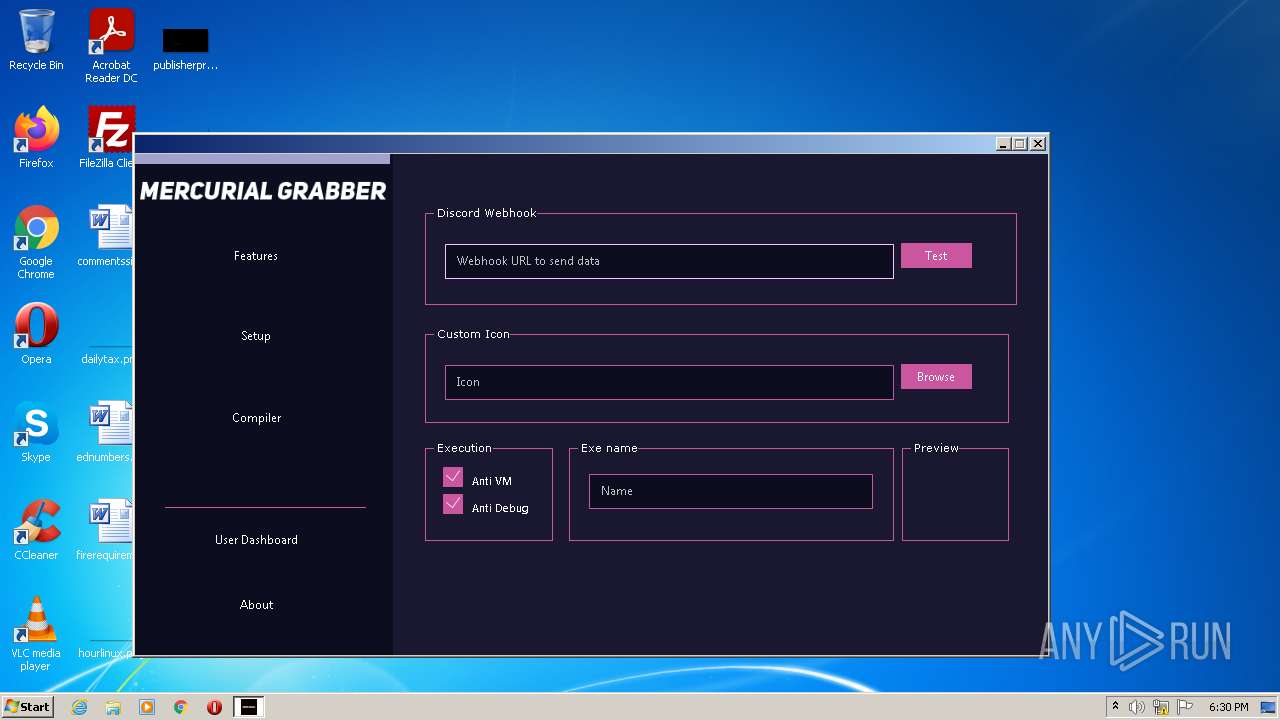
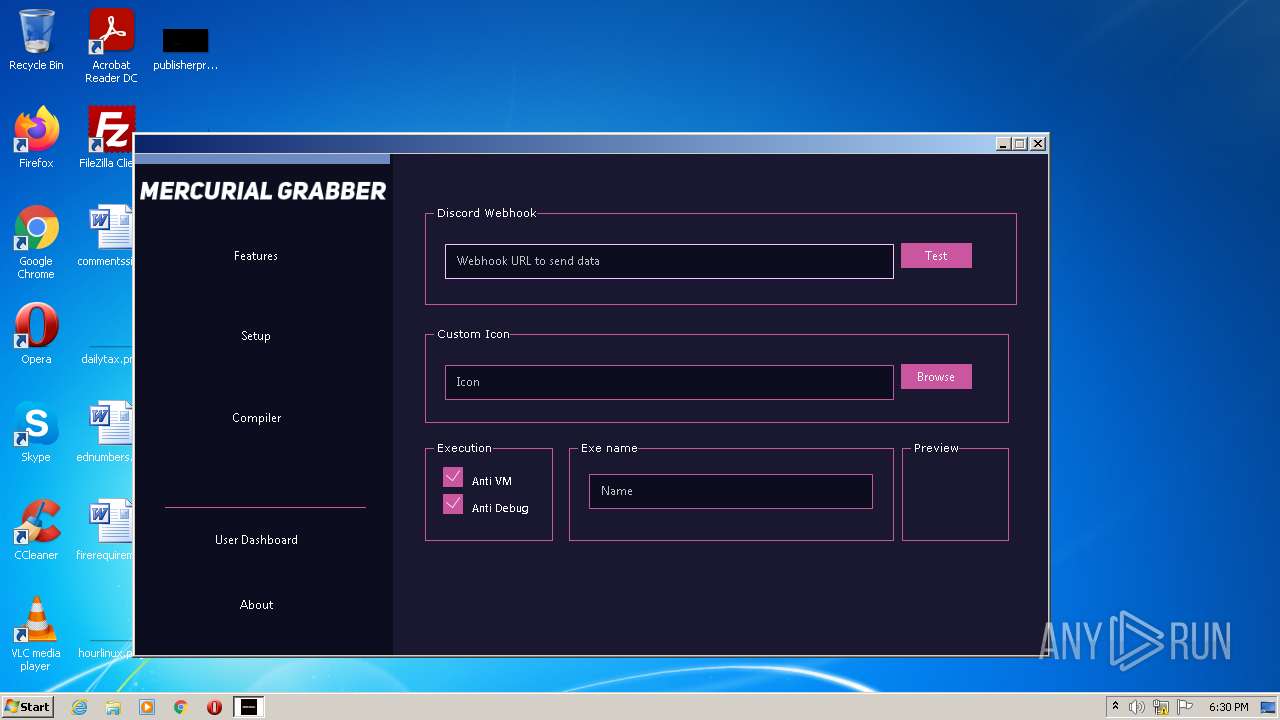
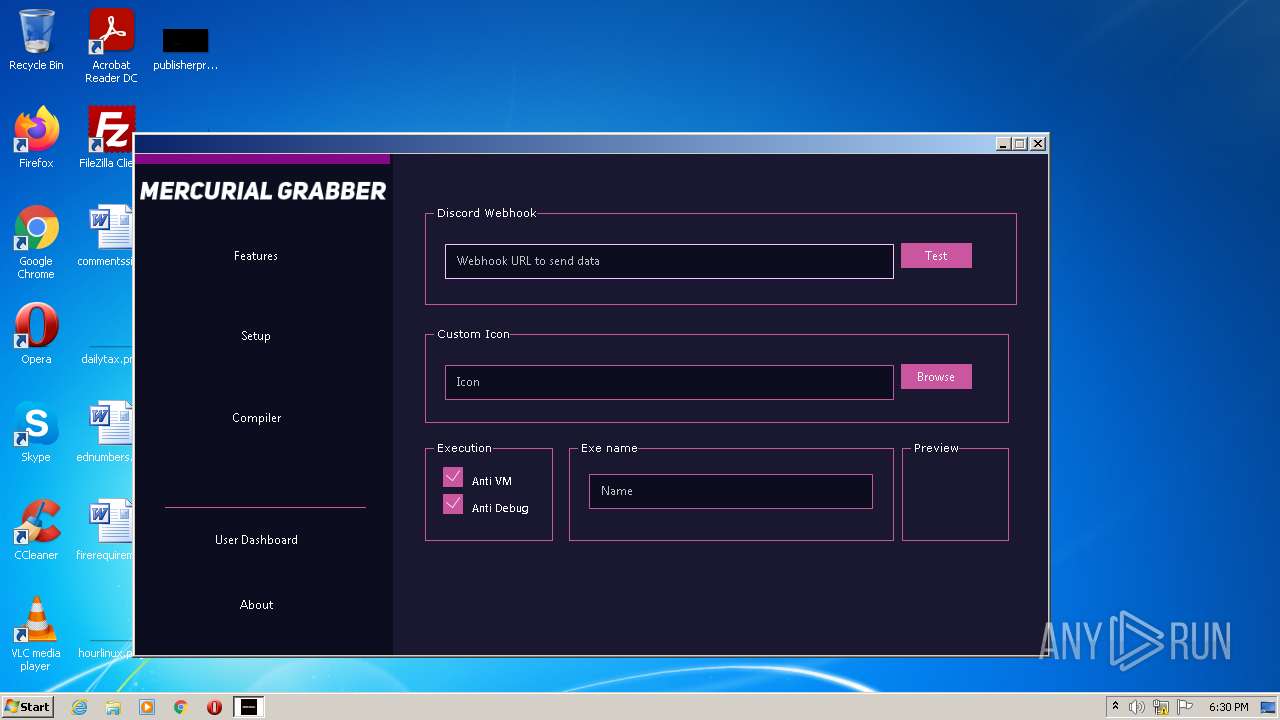
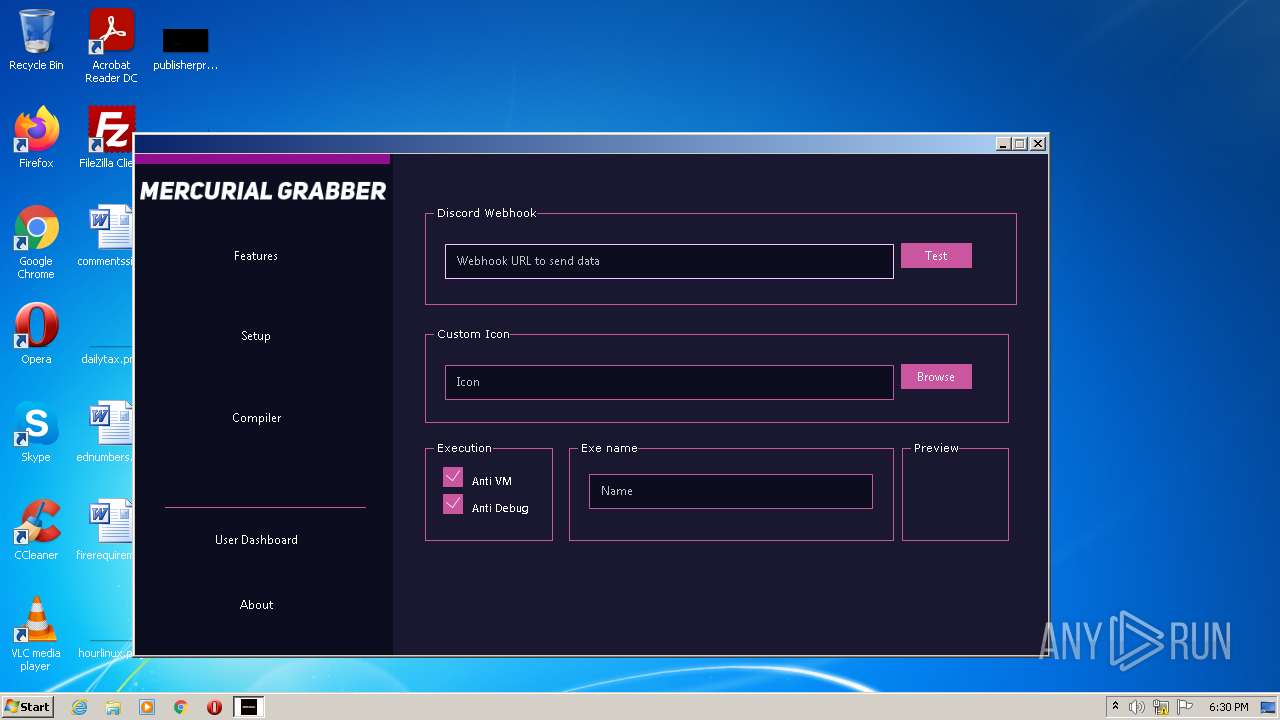
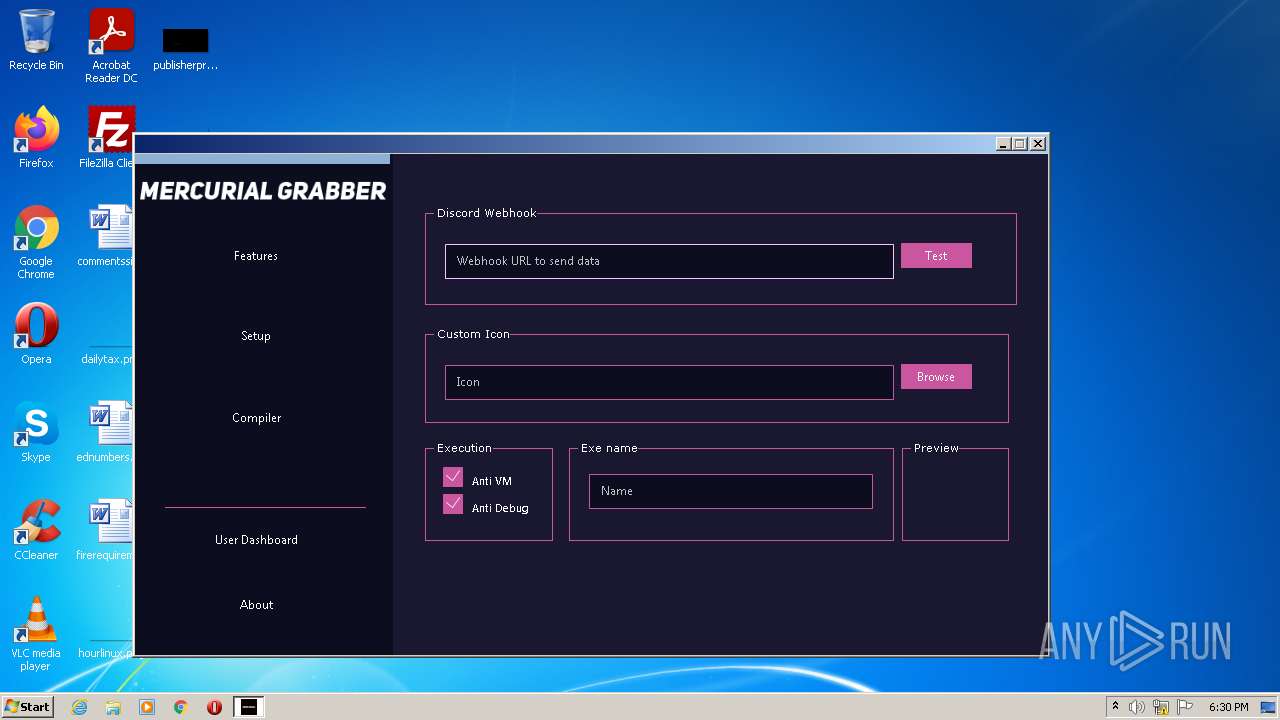
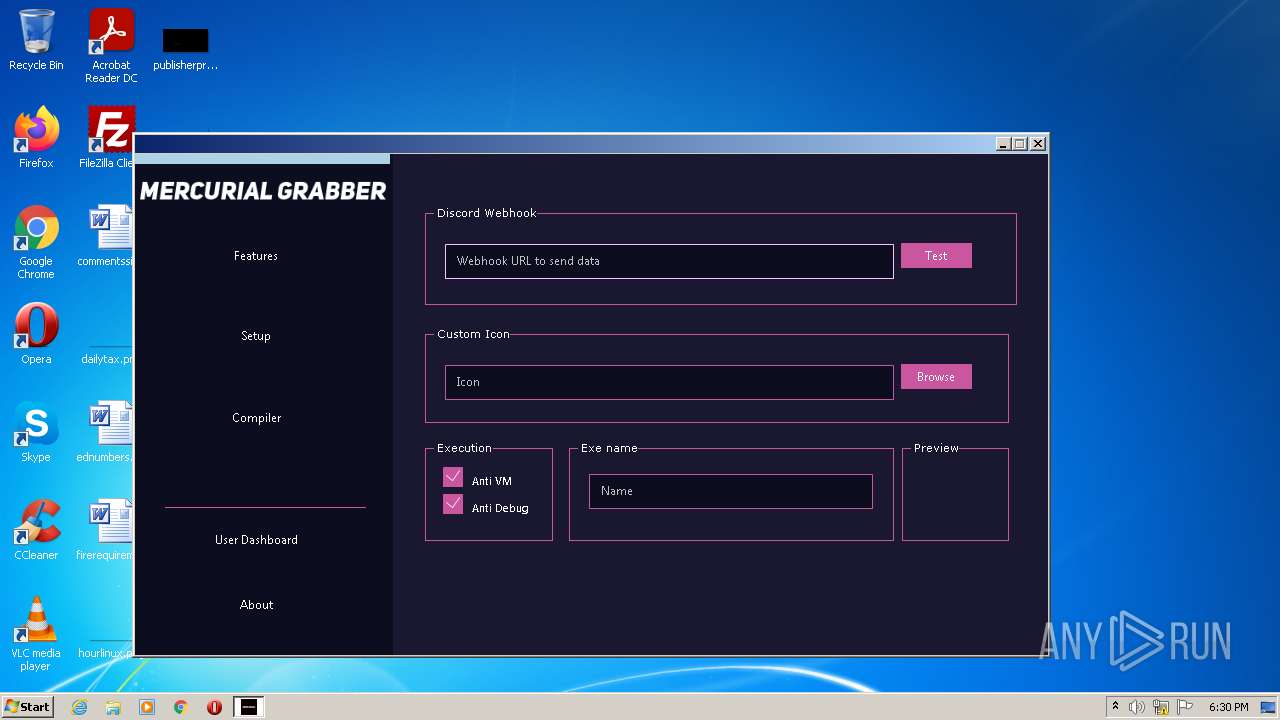
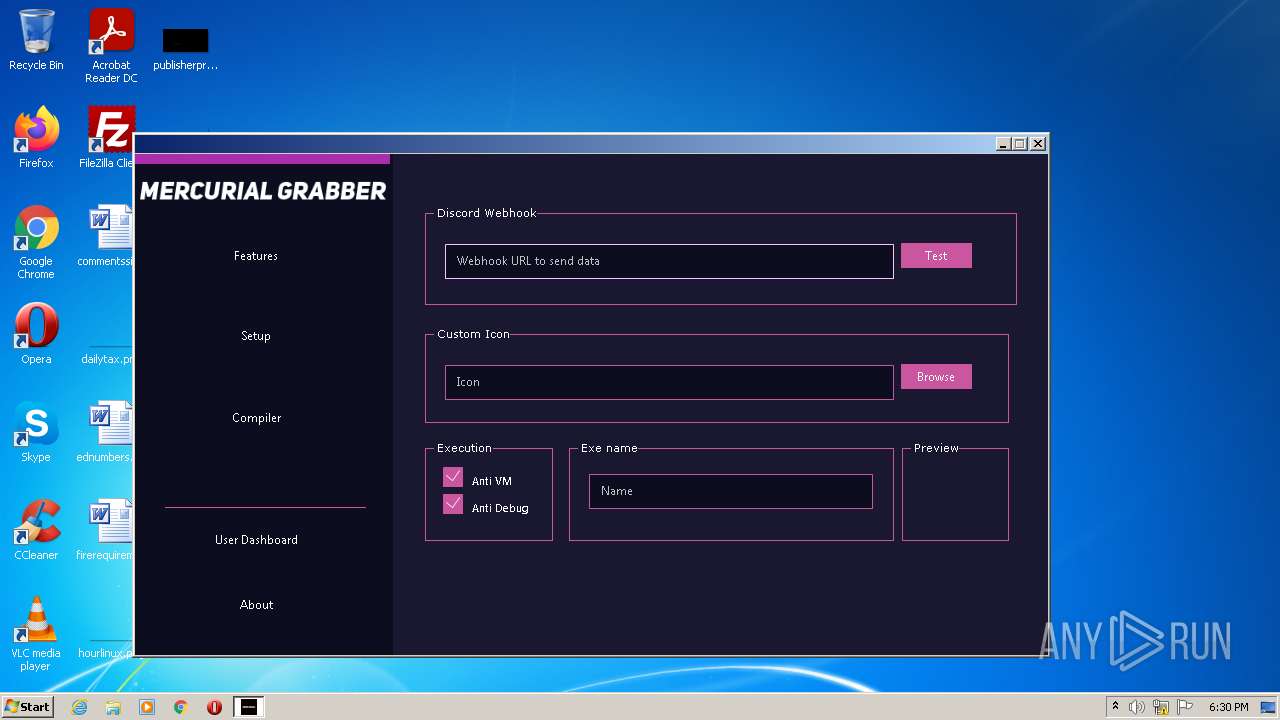
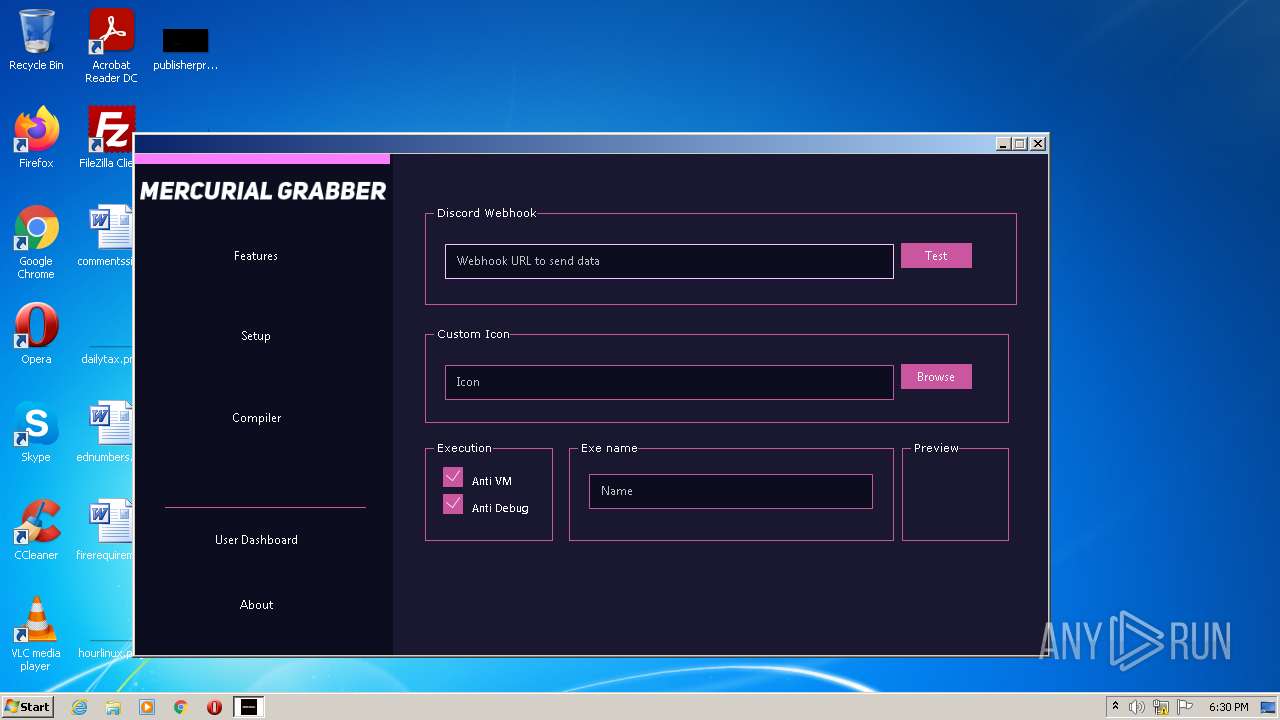
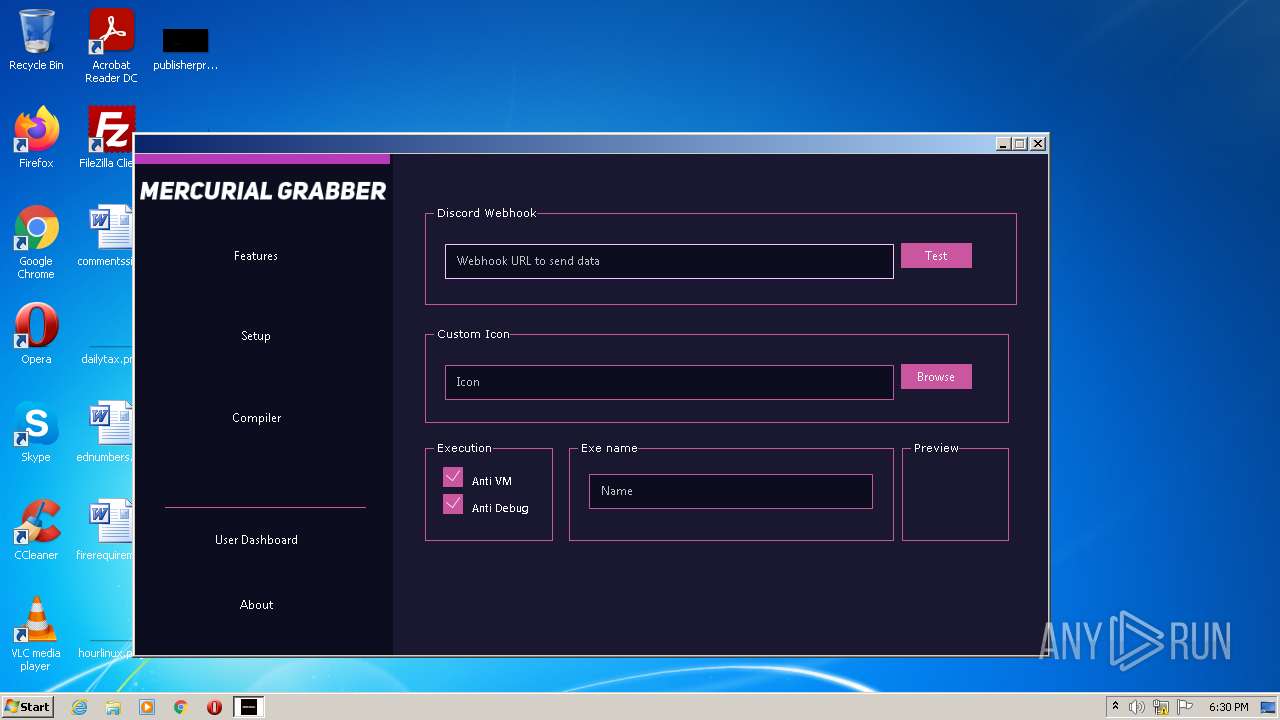
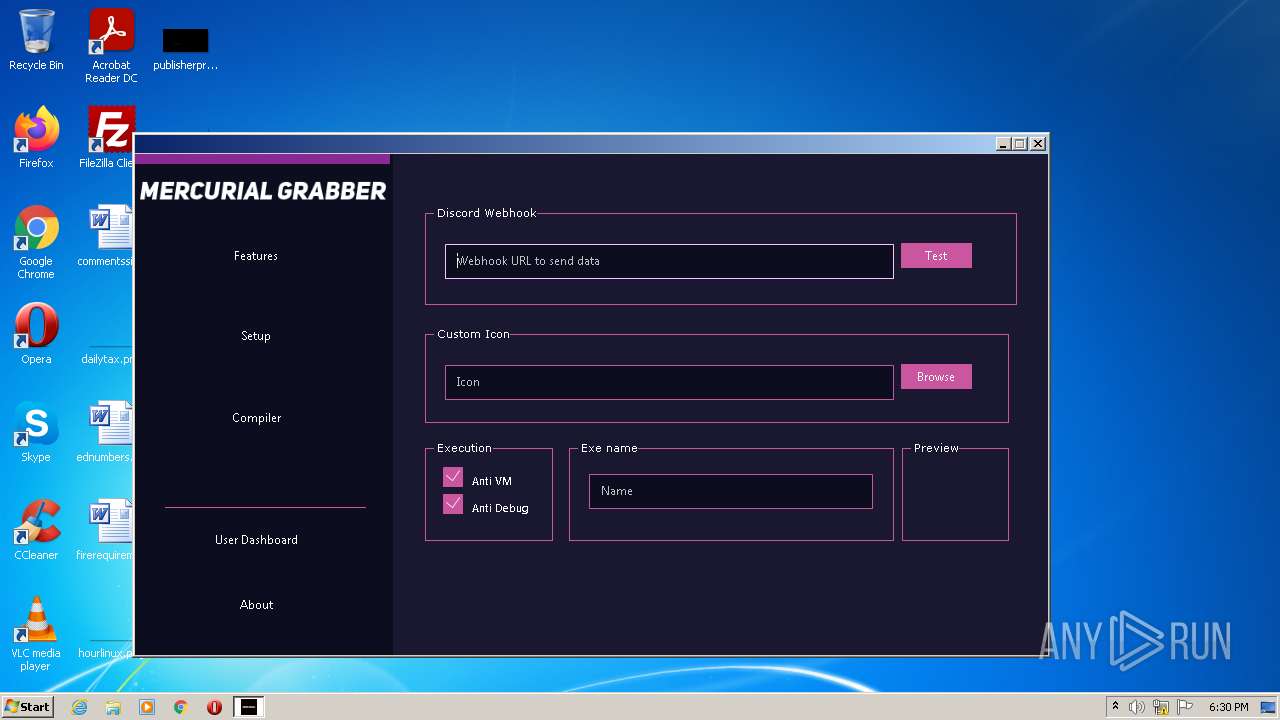
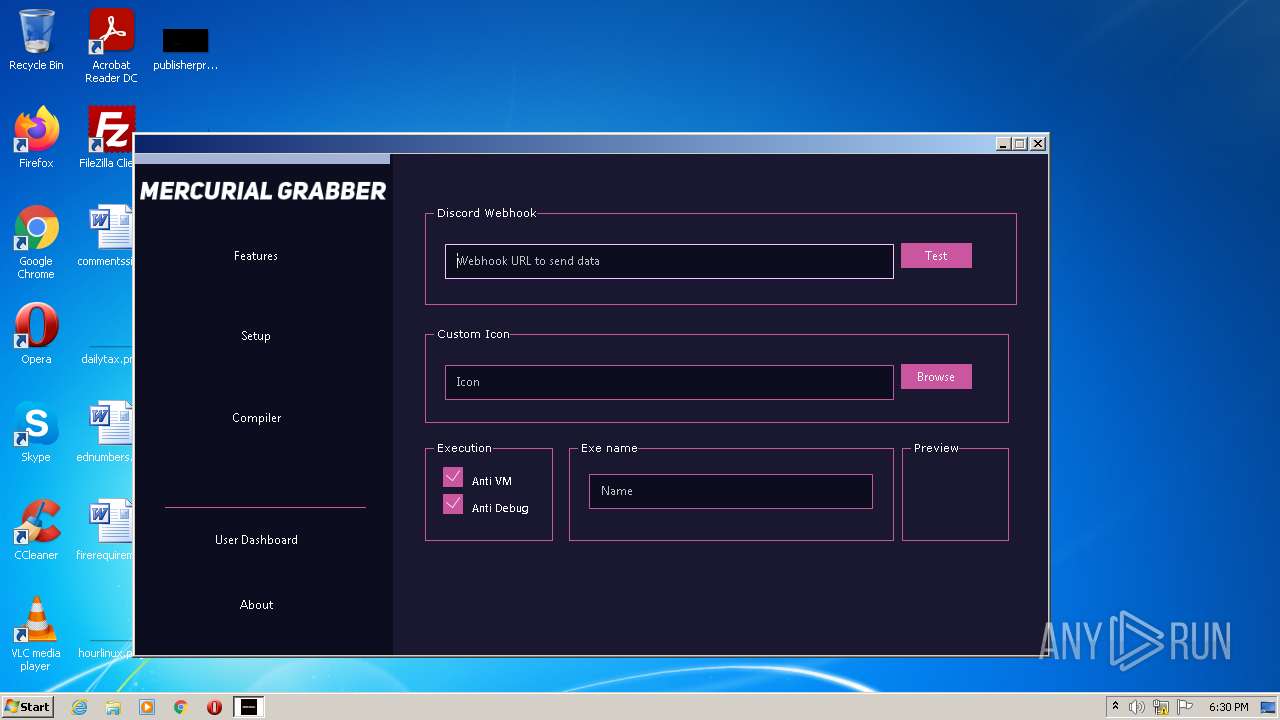
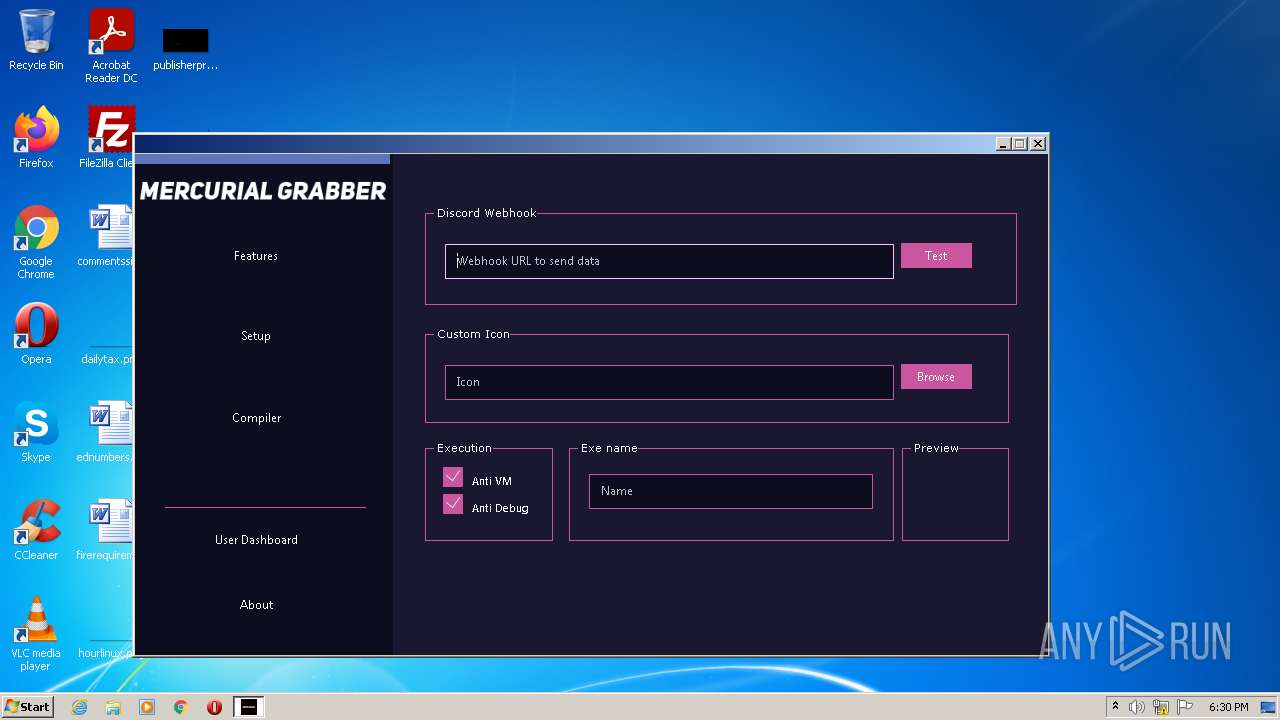
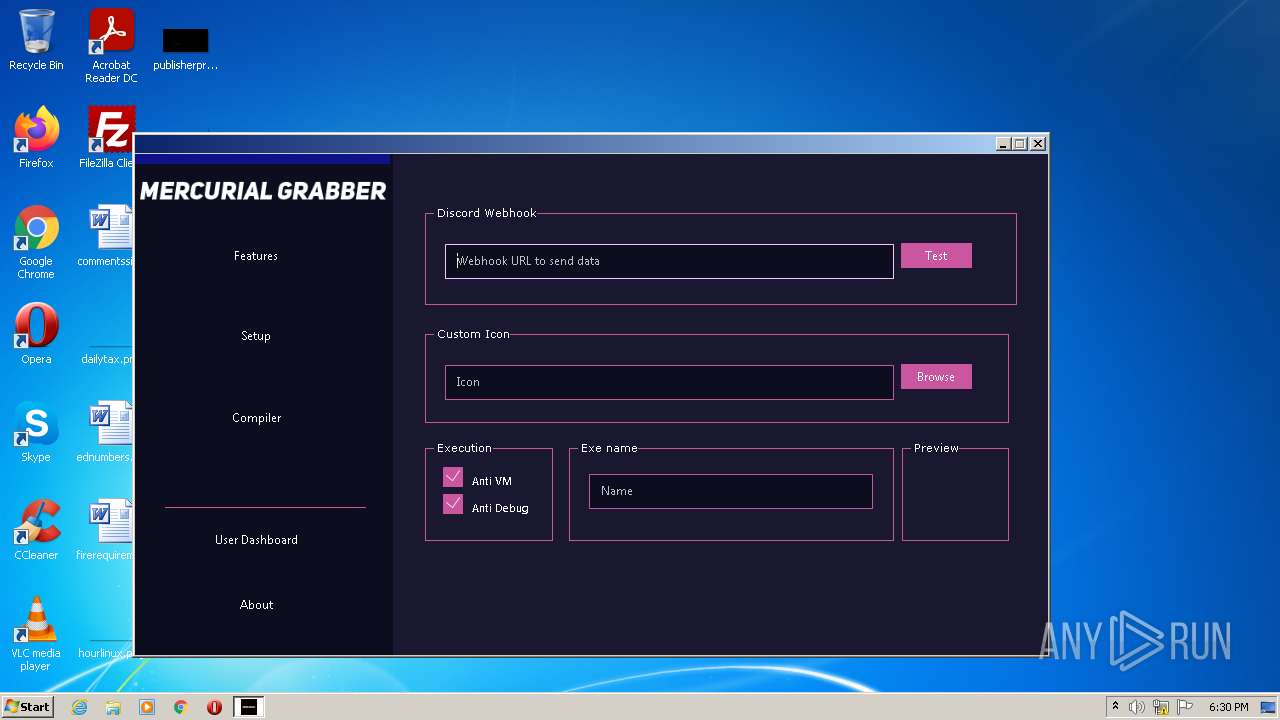
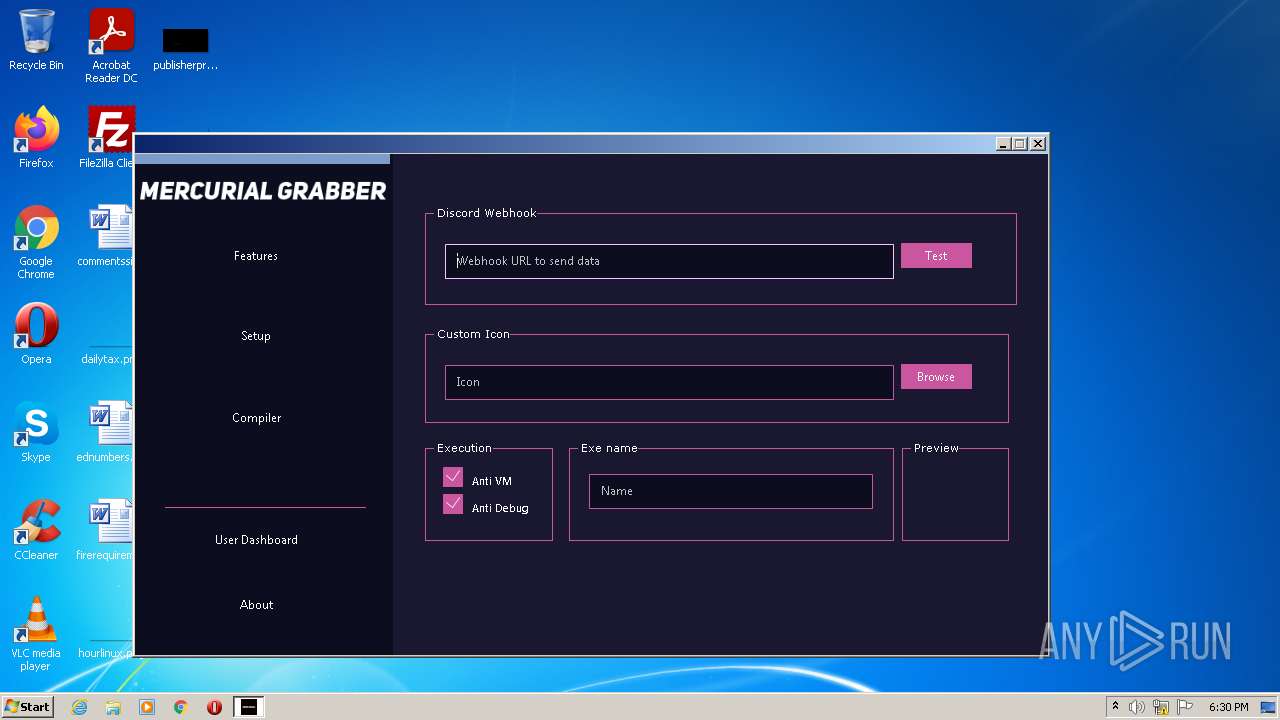
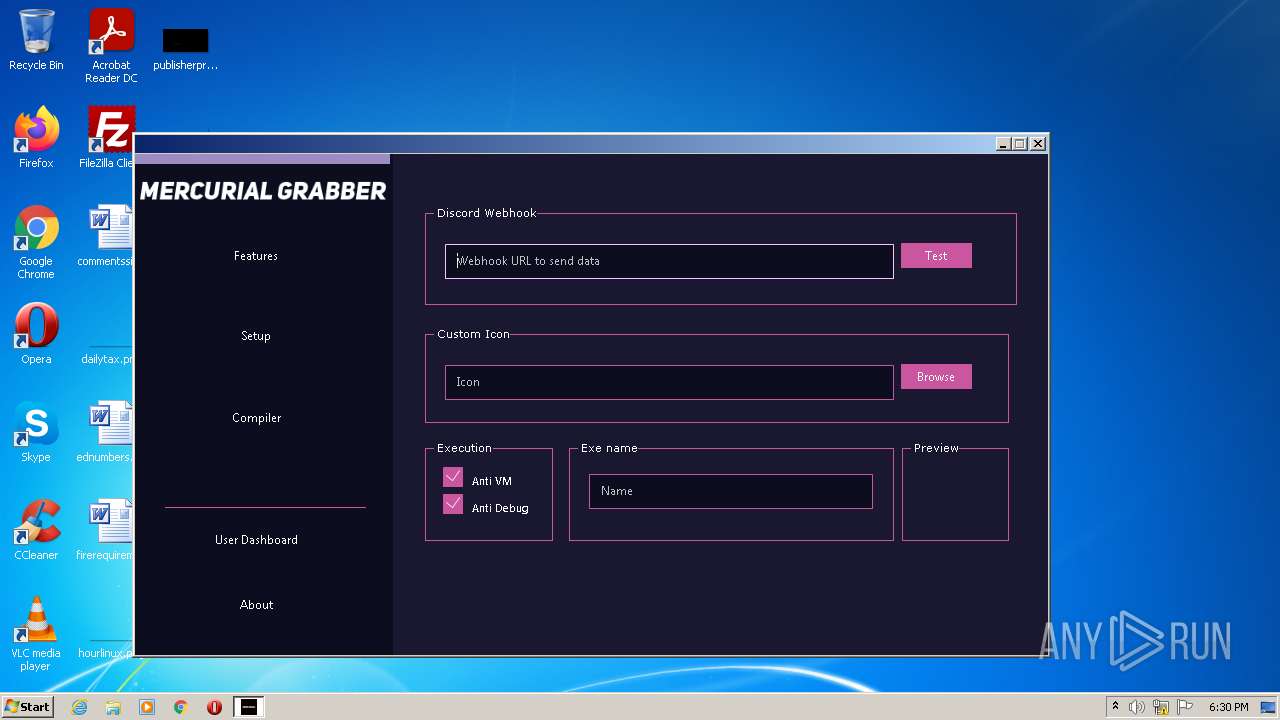
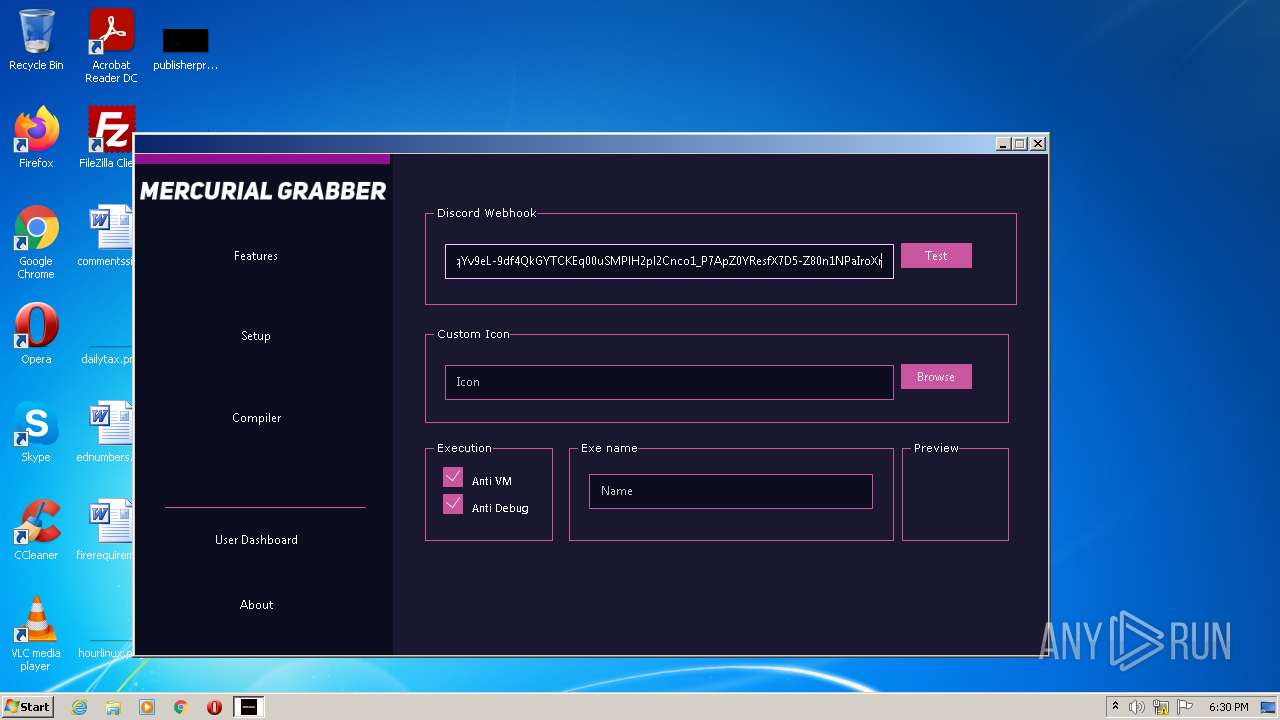
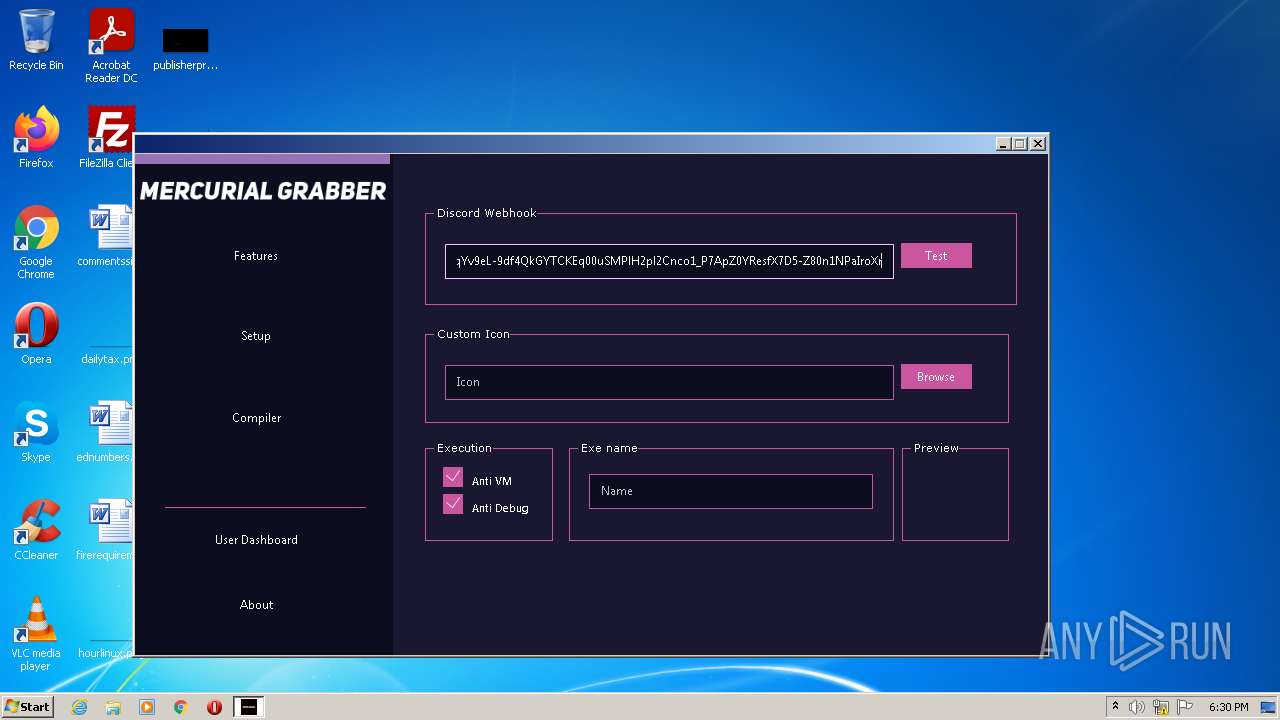
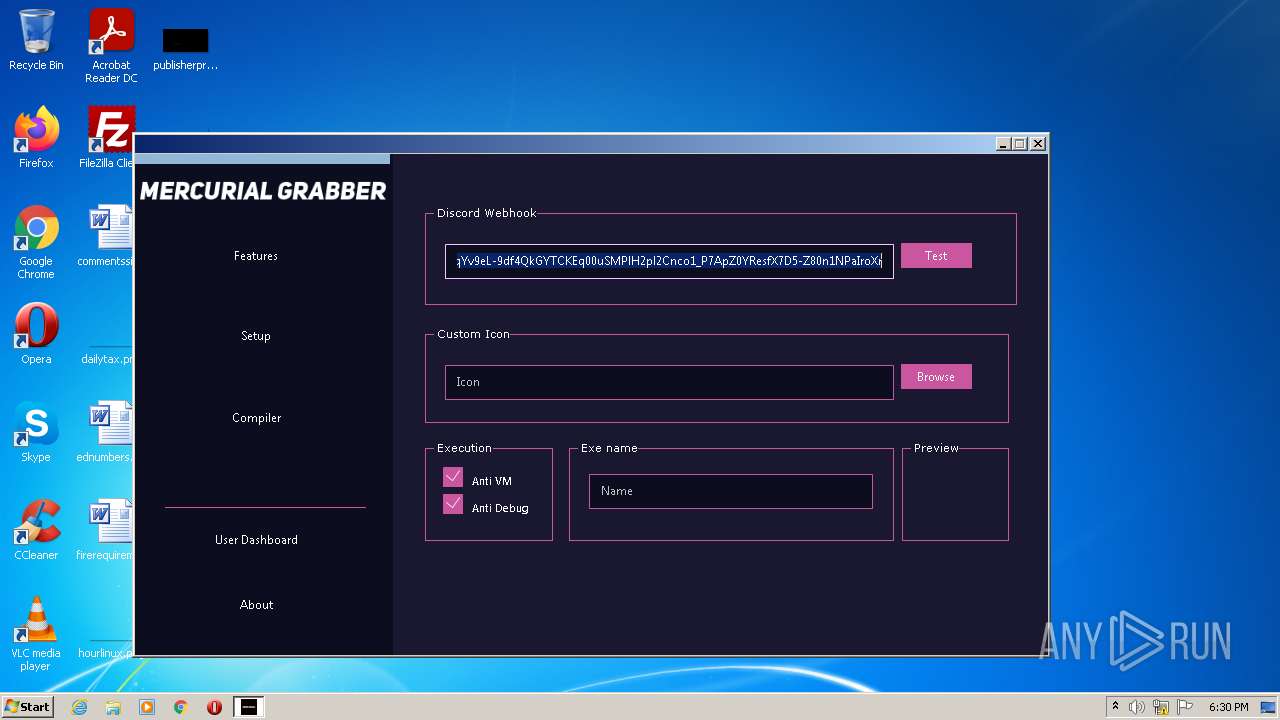
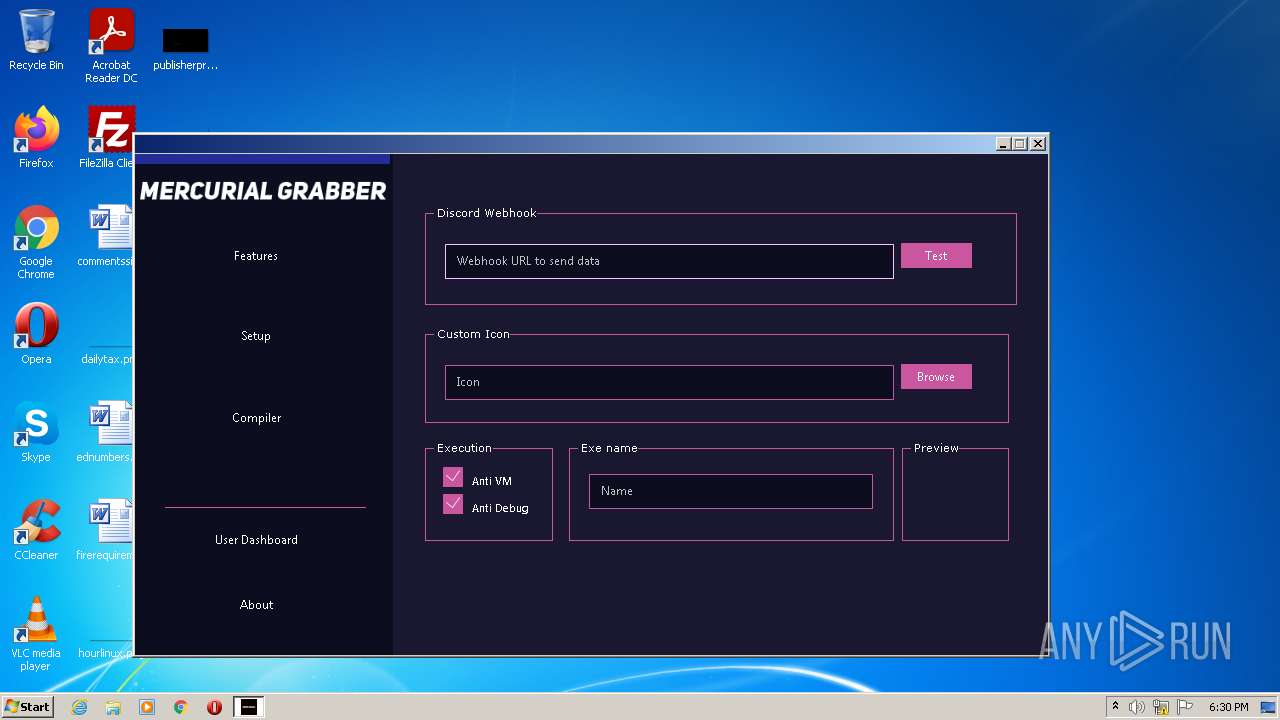
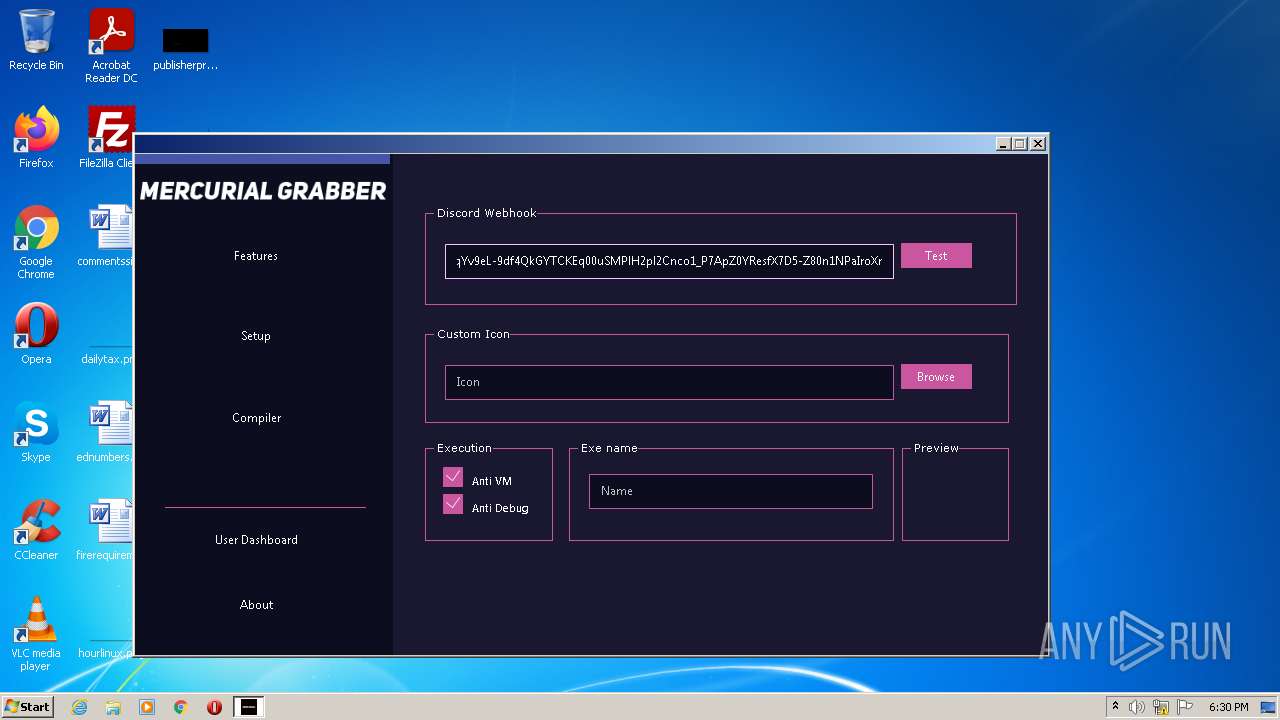
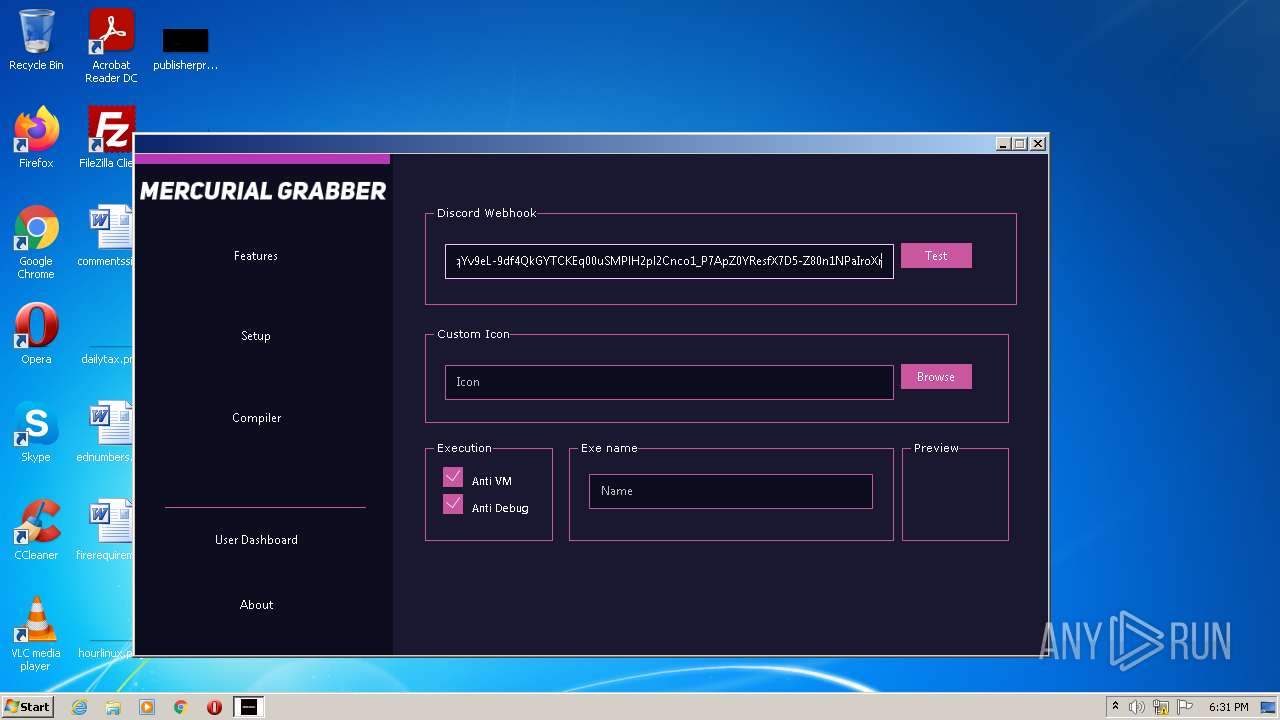
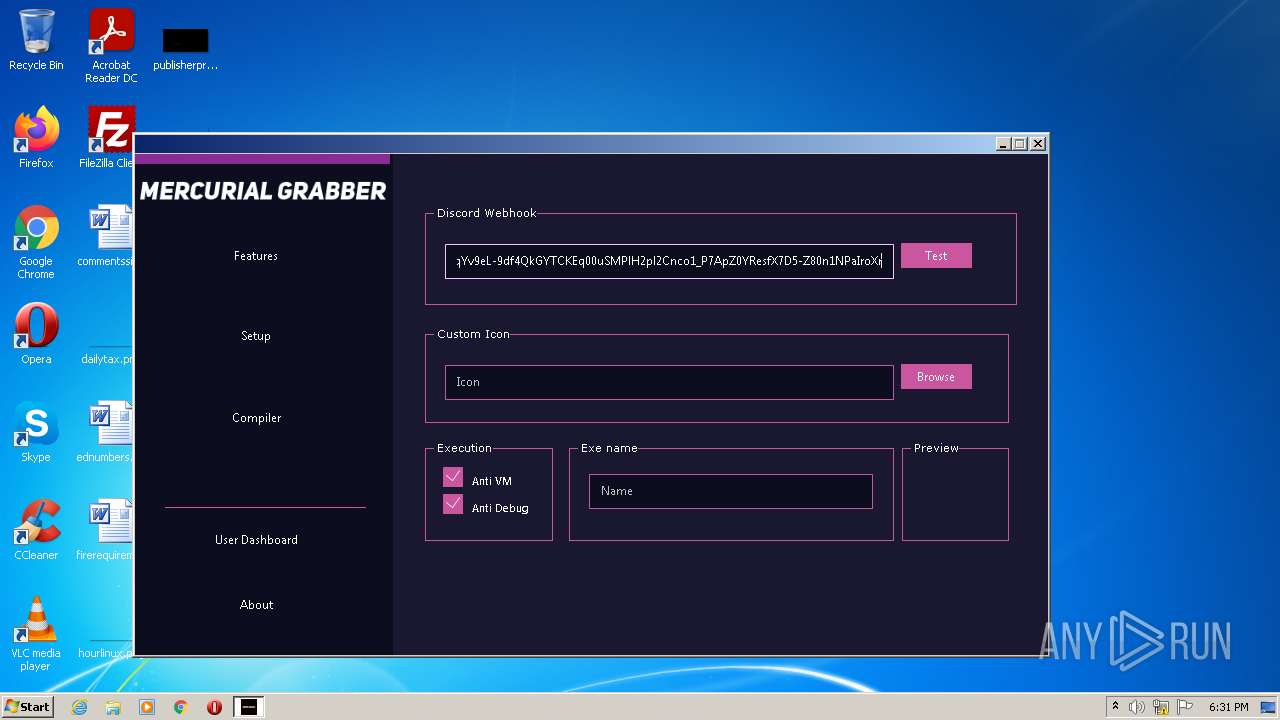
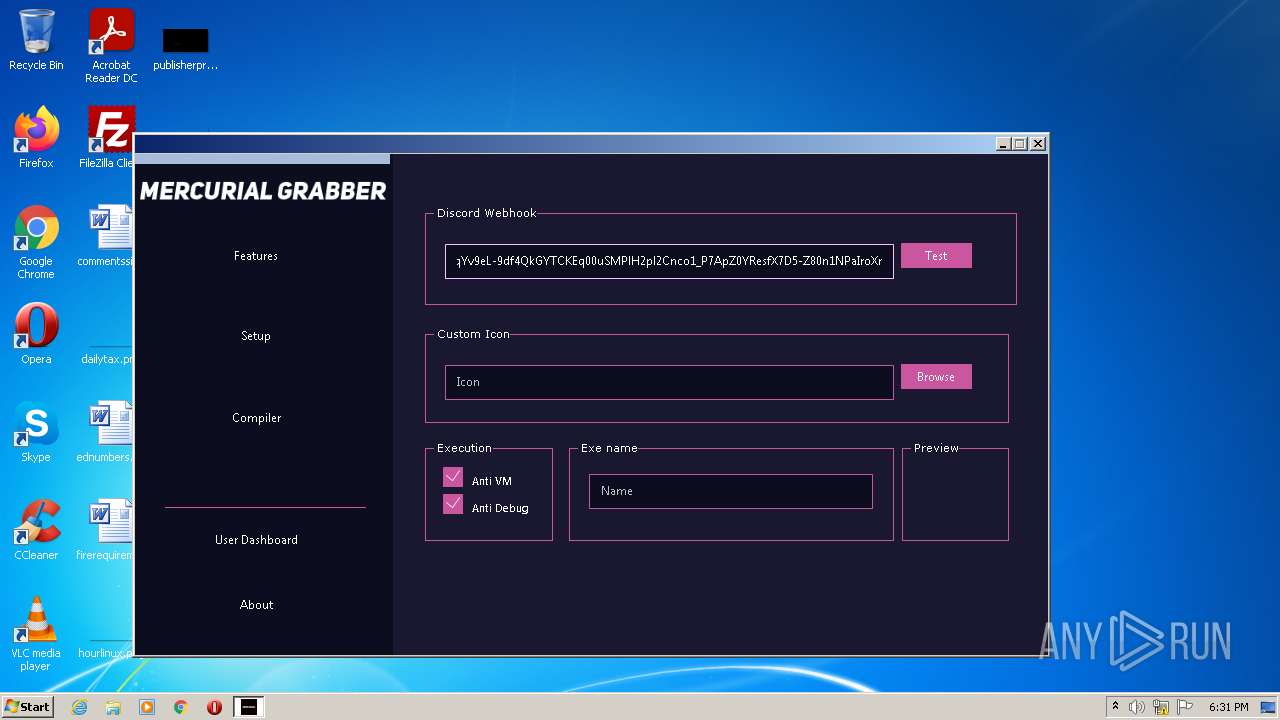
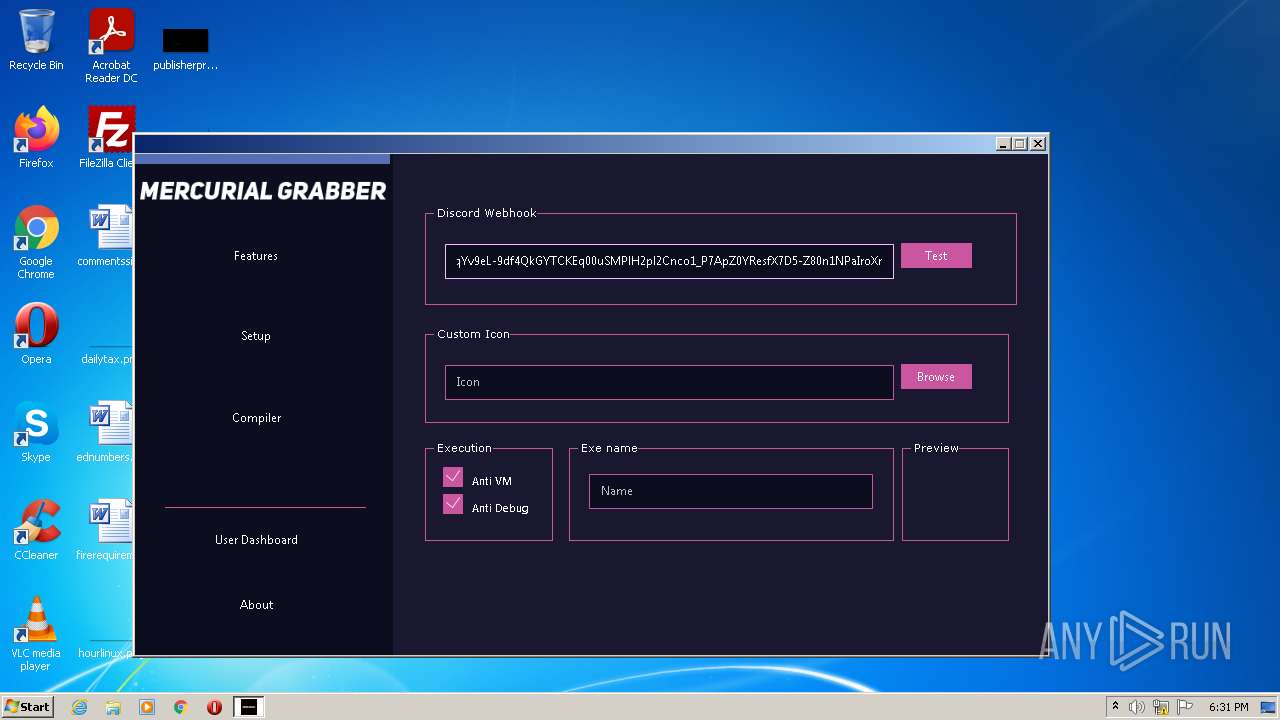
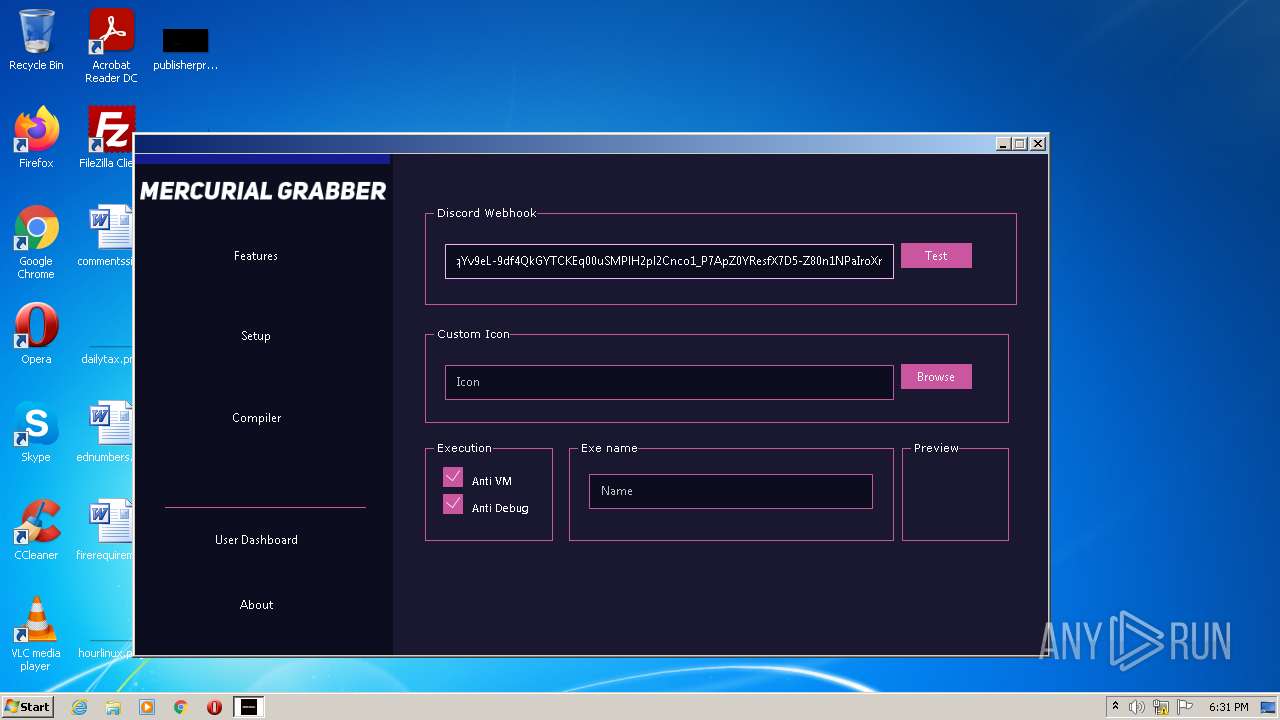
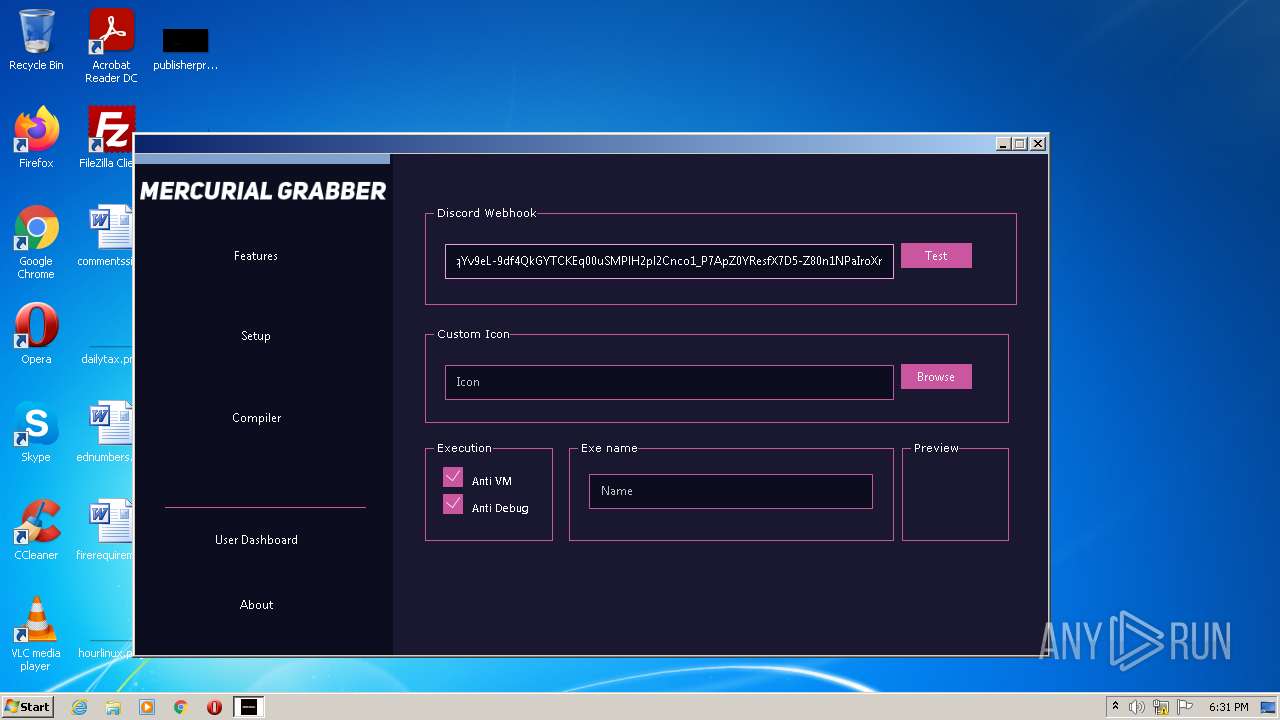
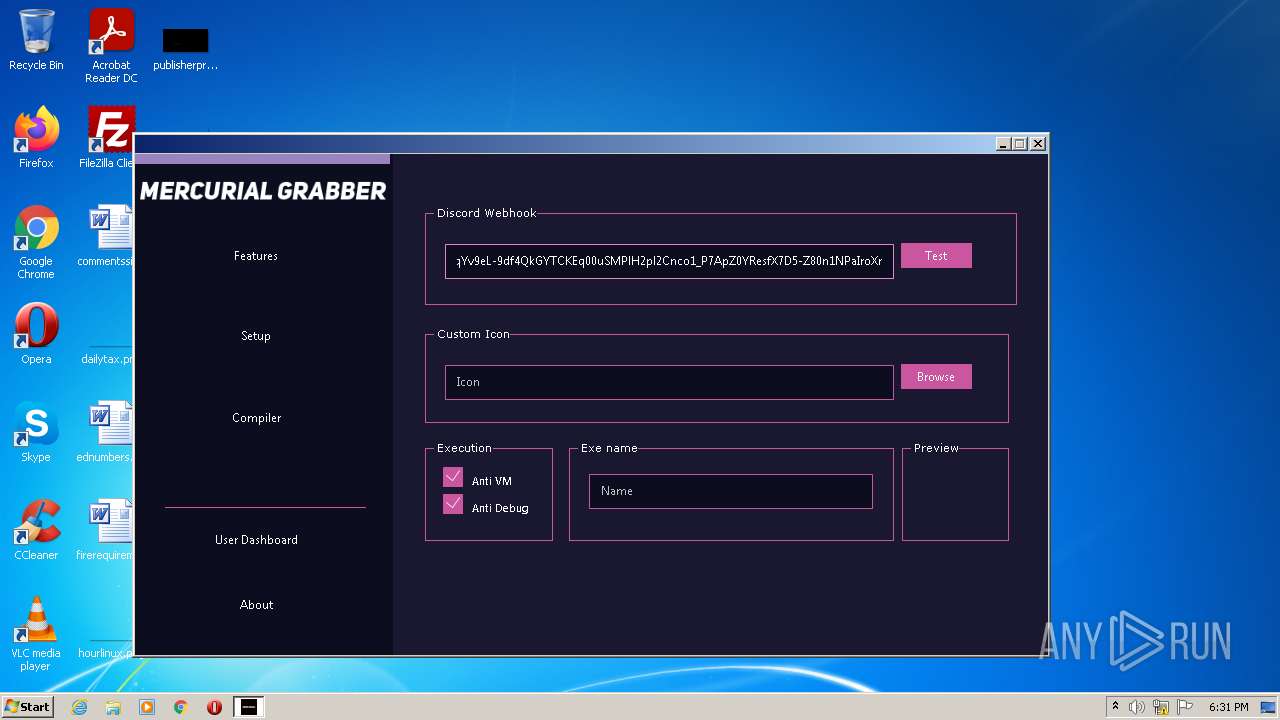
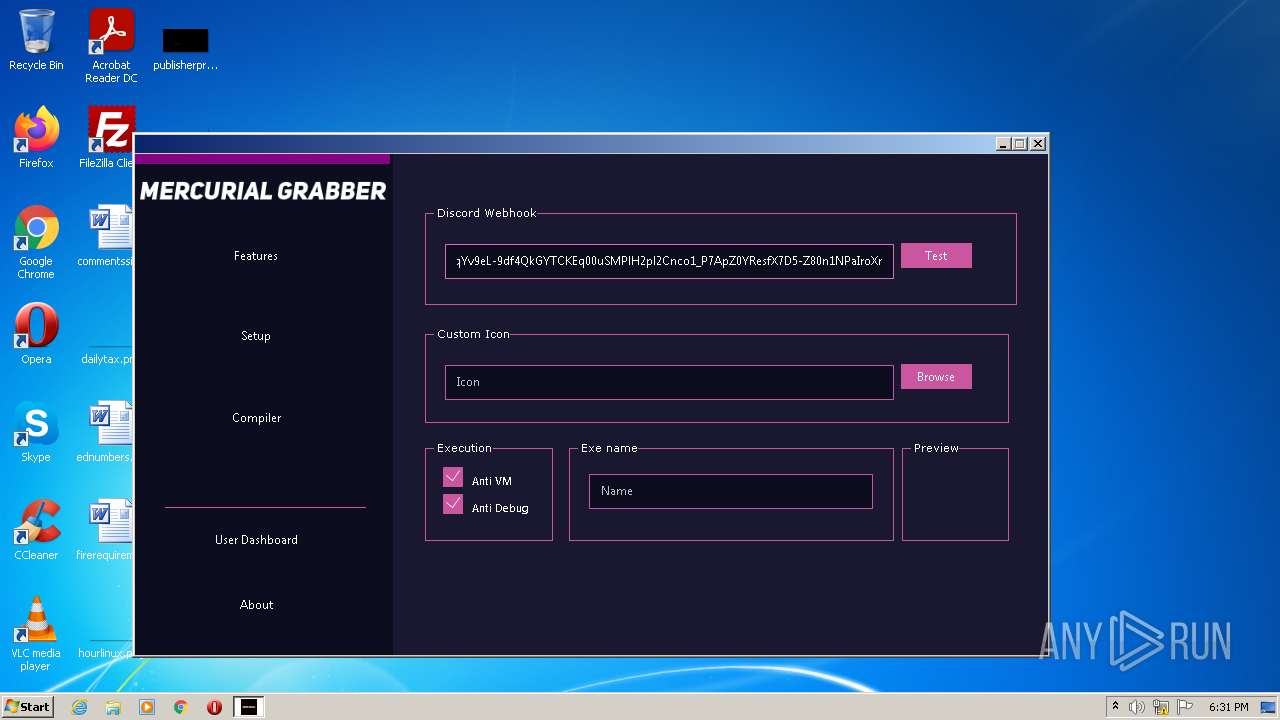
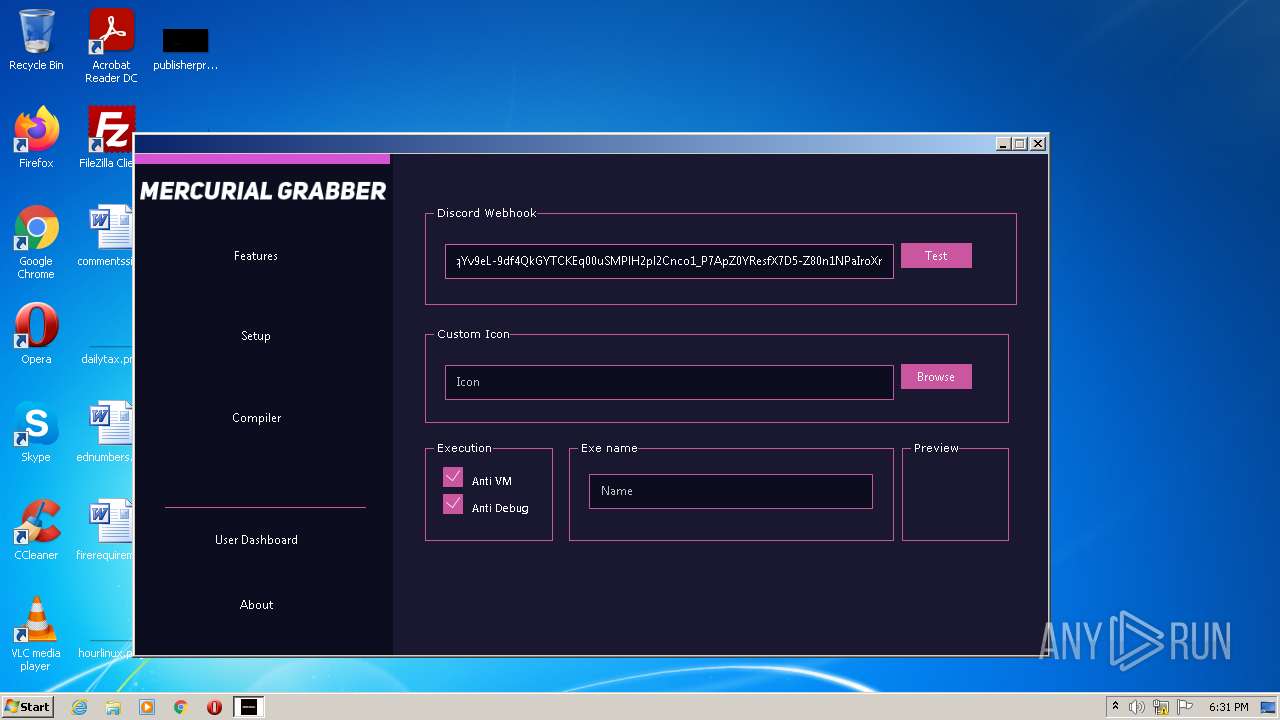
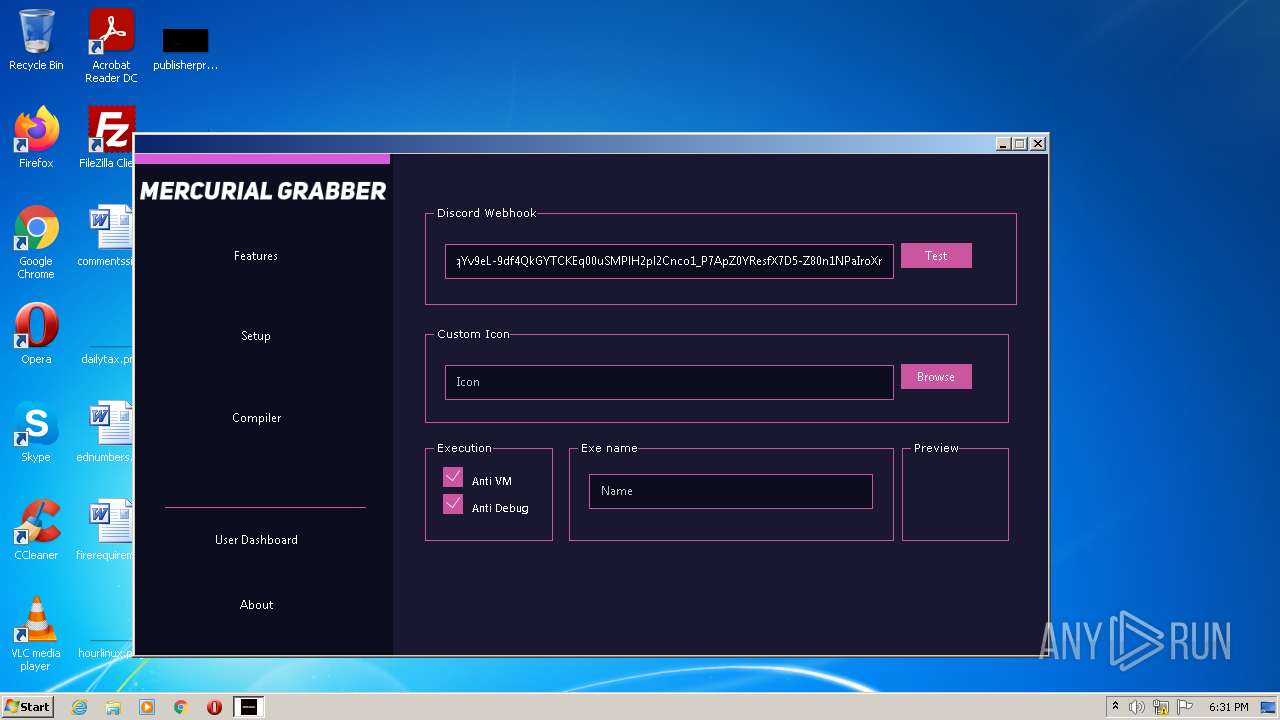
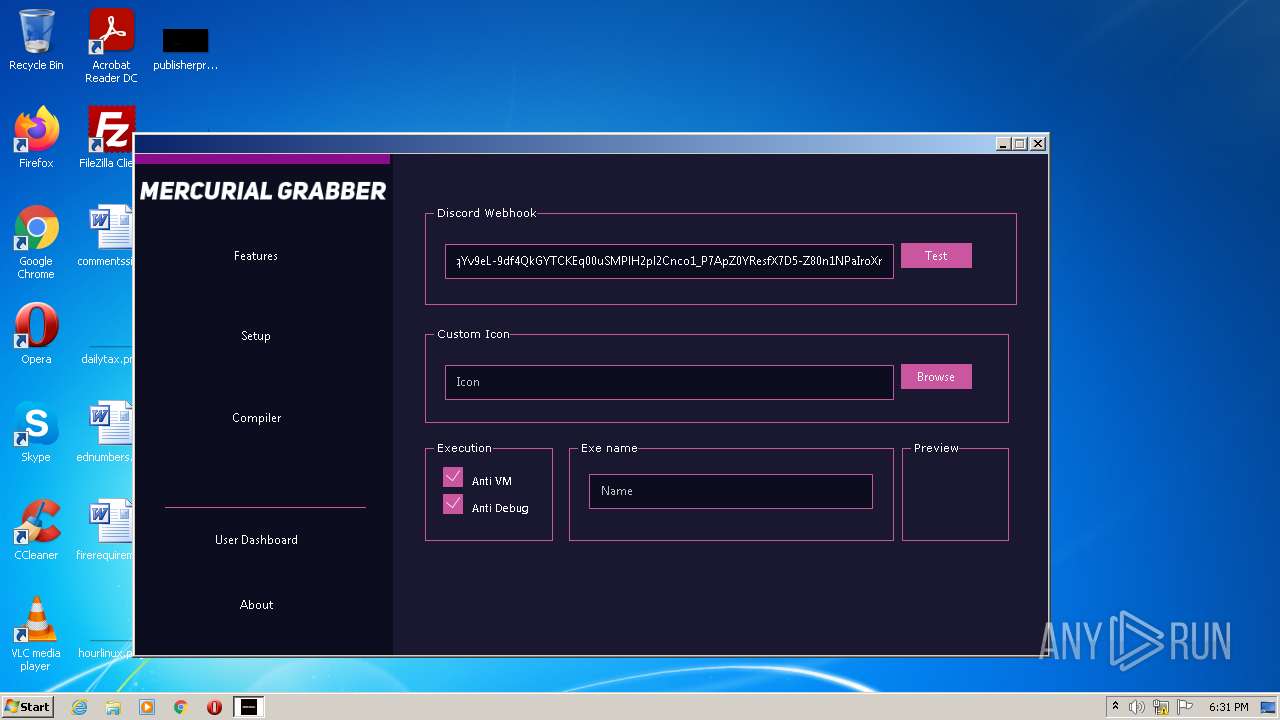
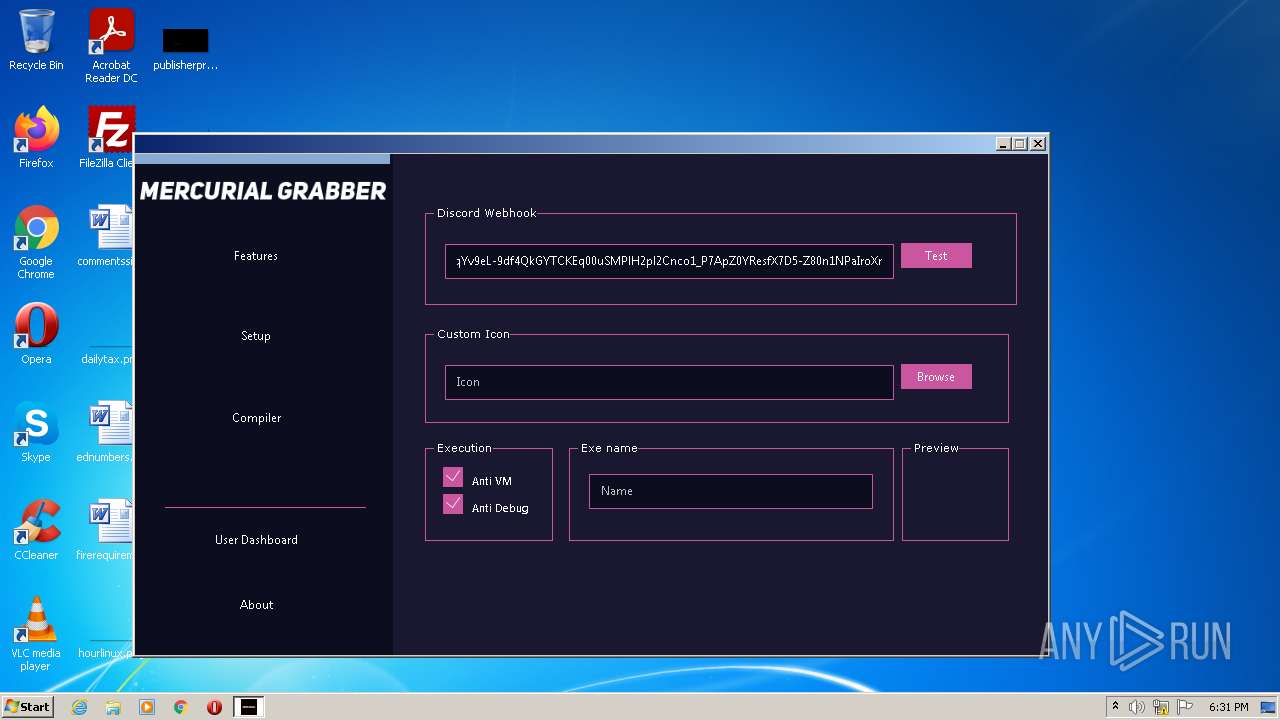
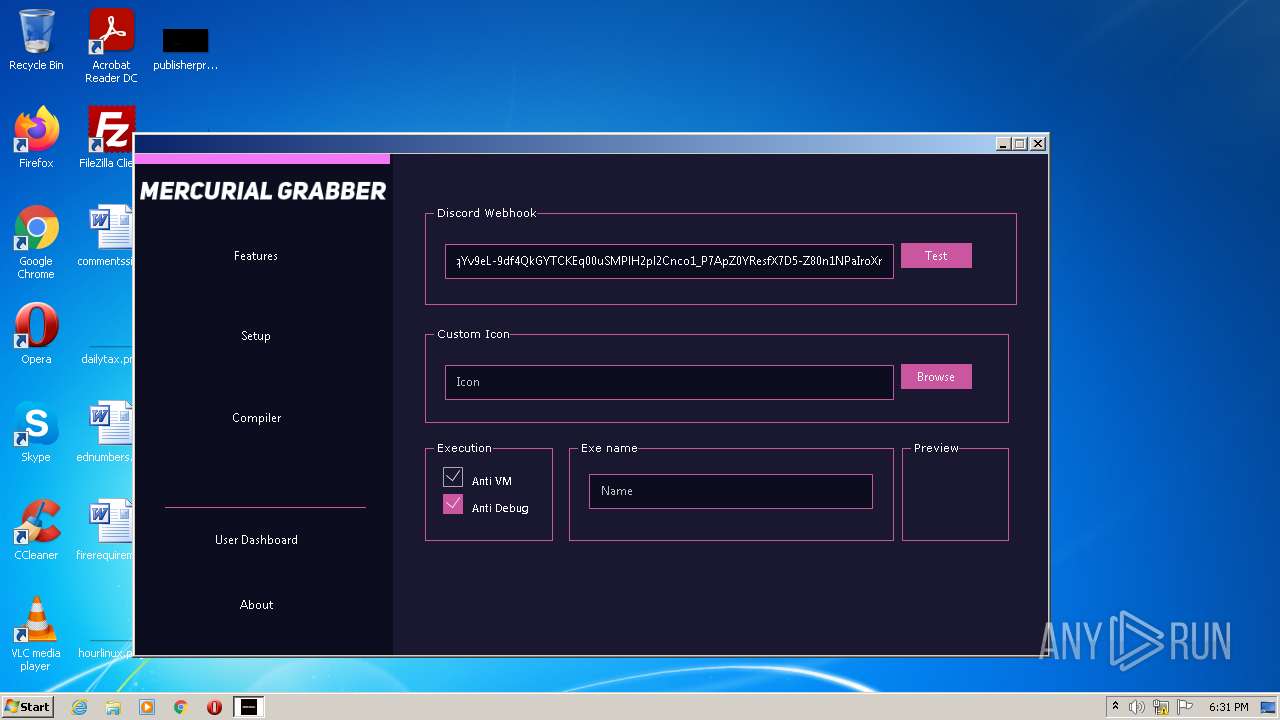
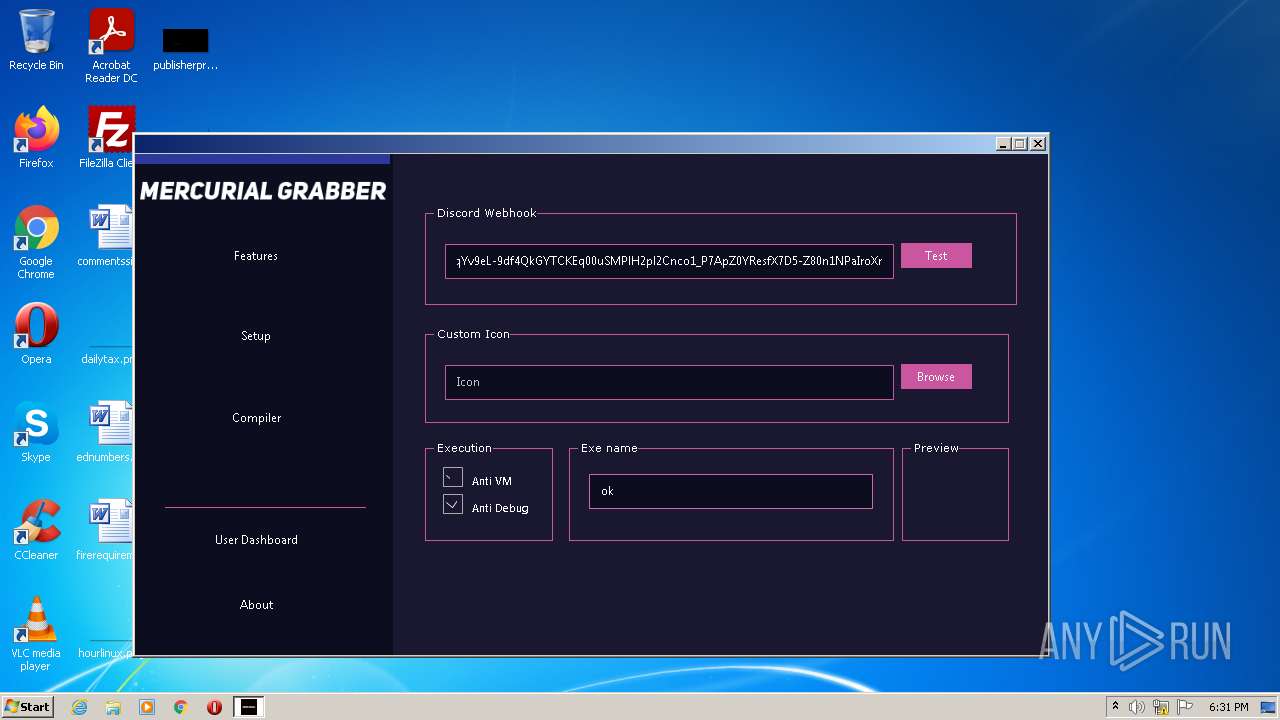
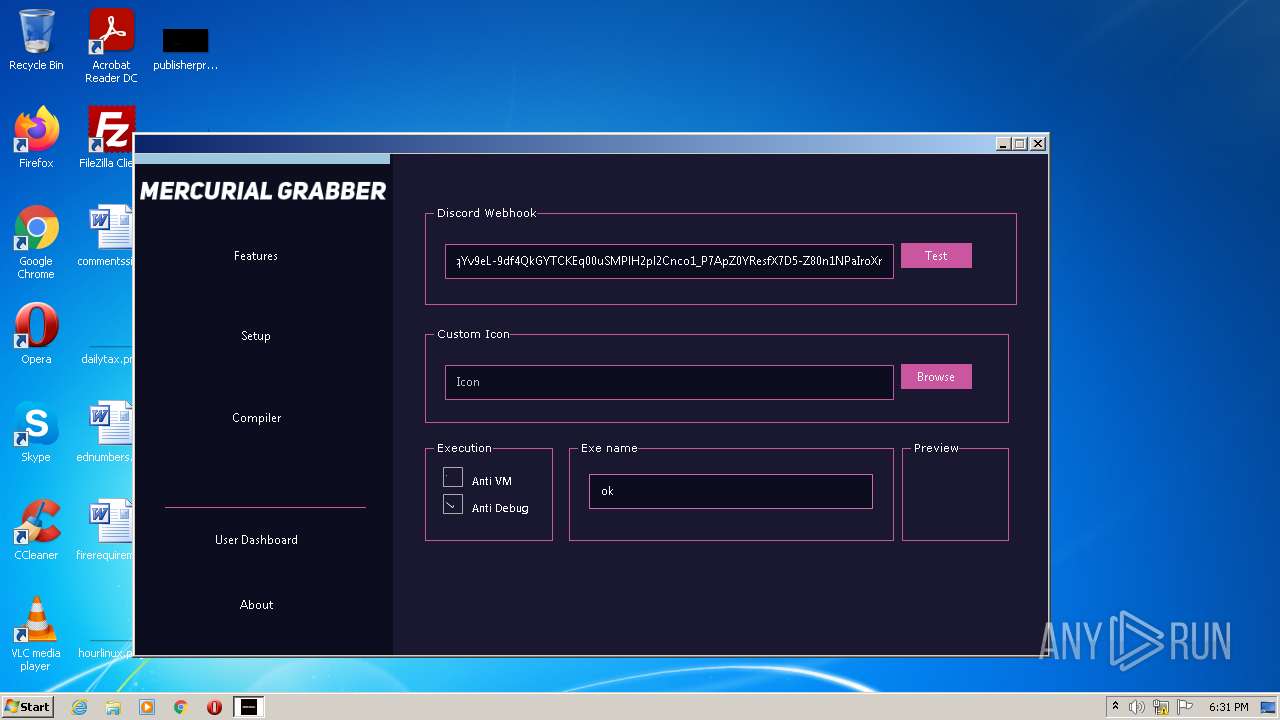
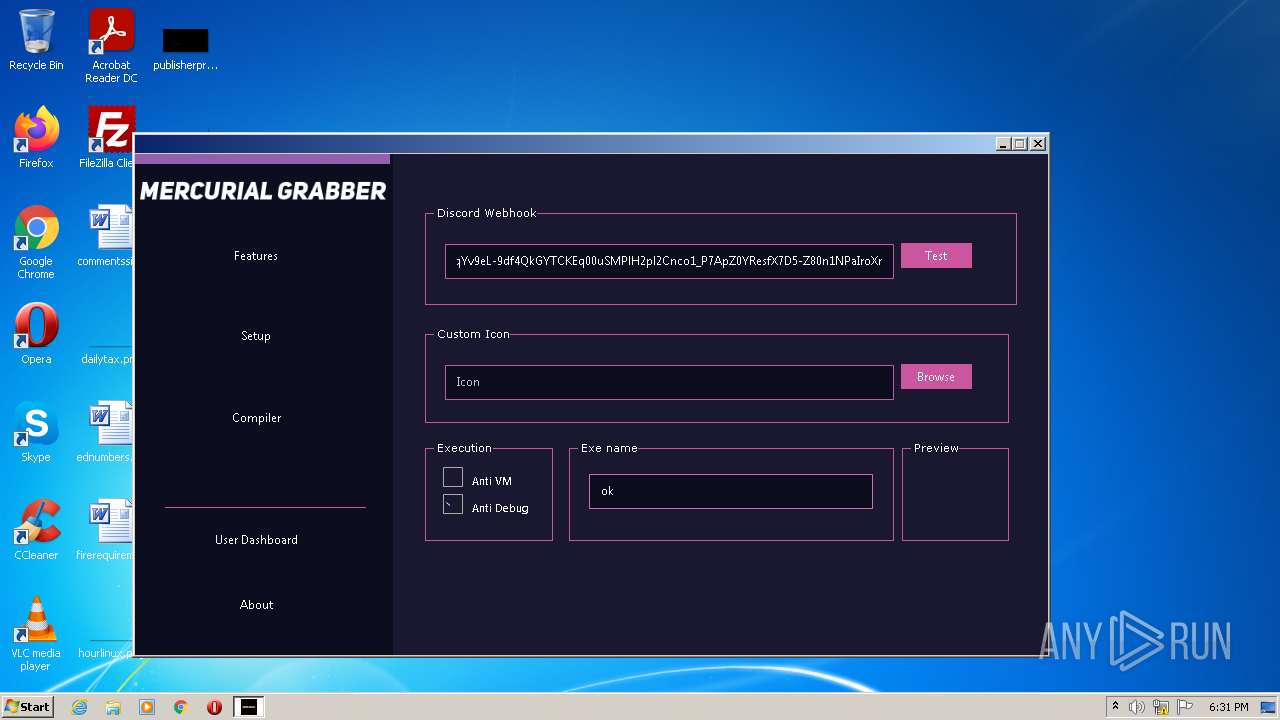
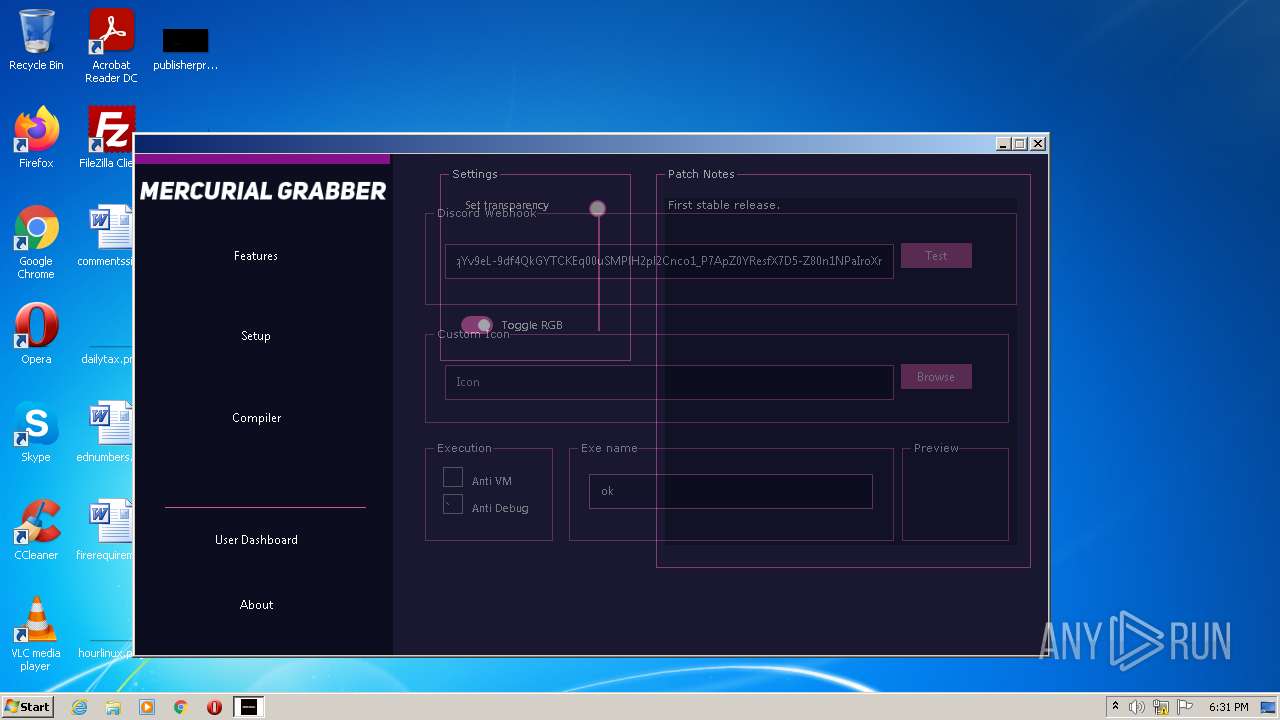
| File name: | Mercurial.exe |
| Full analysis: | https://app.any.run/tasks/ae619368-3e06-490e-b29a-4d12b9370224 |
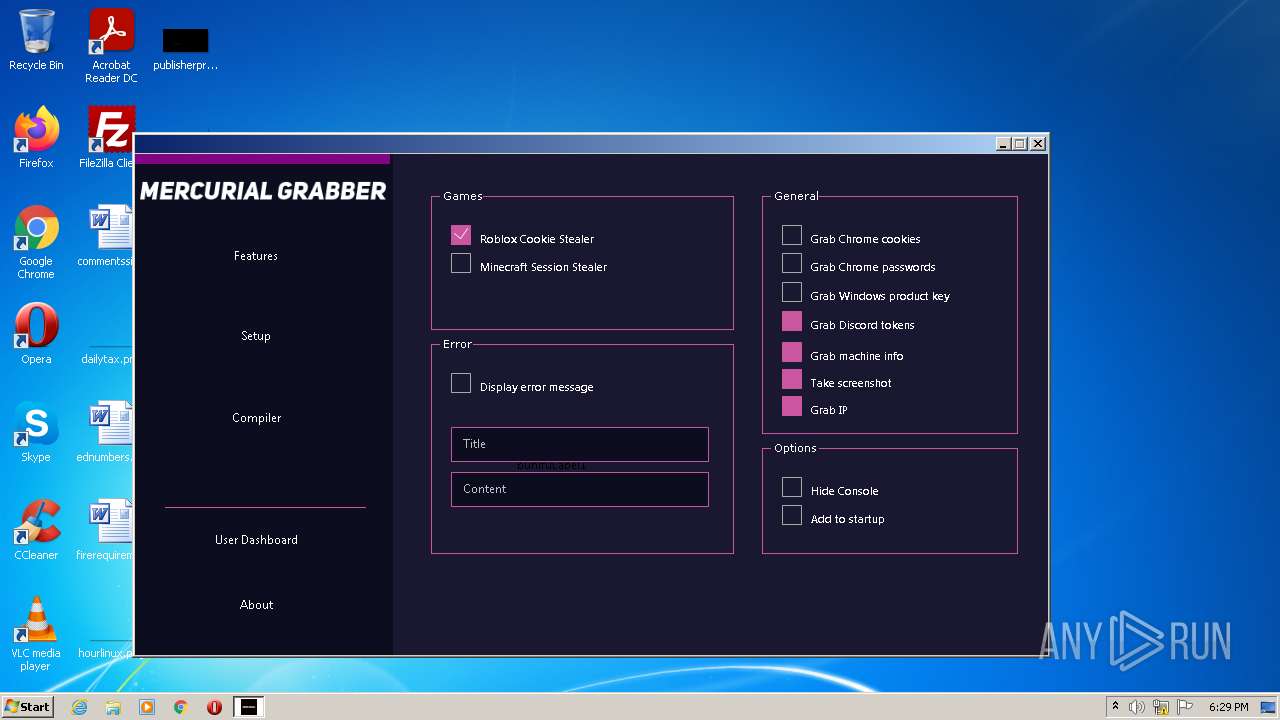
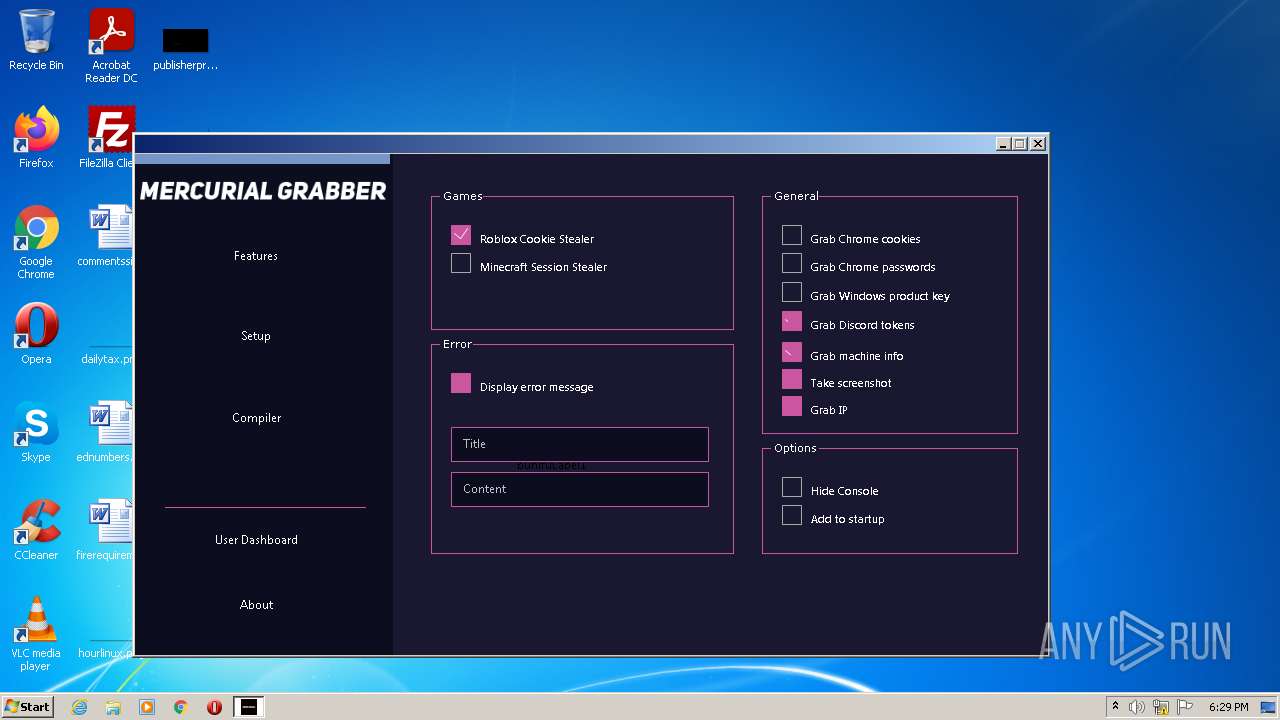
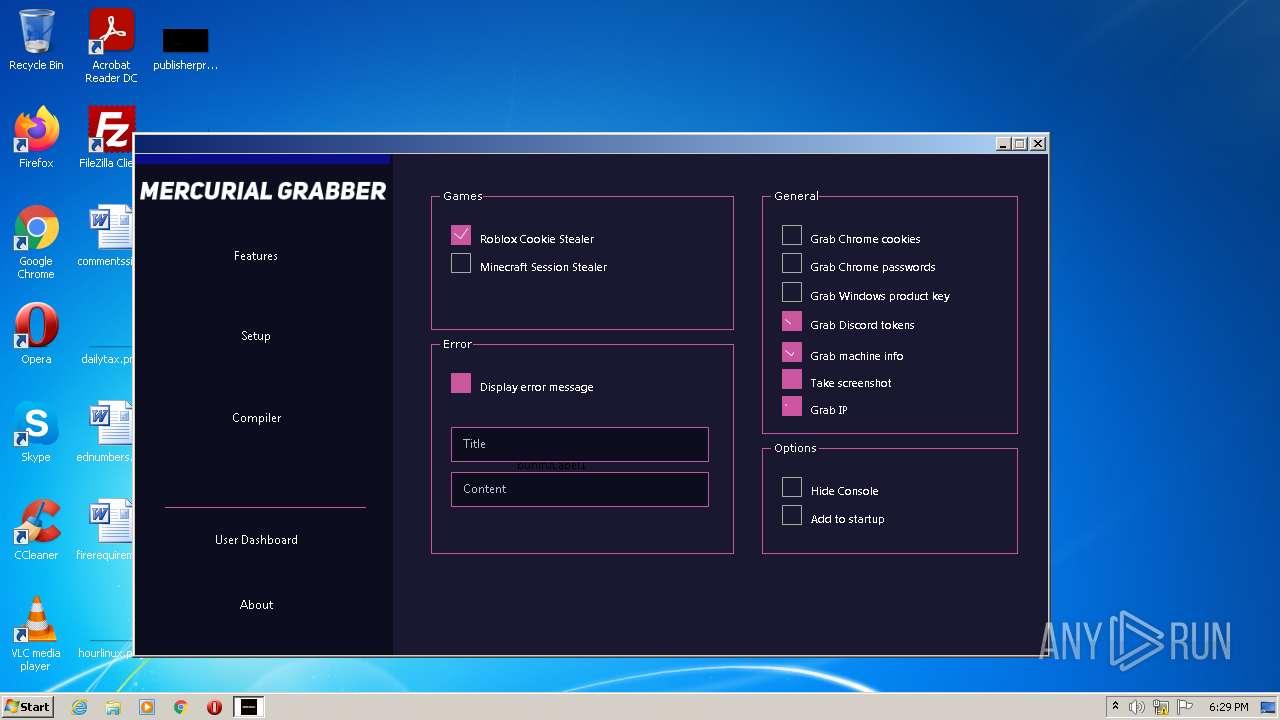
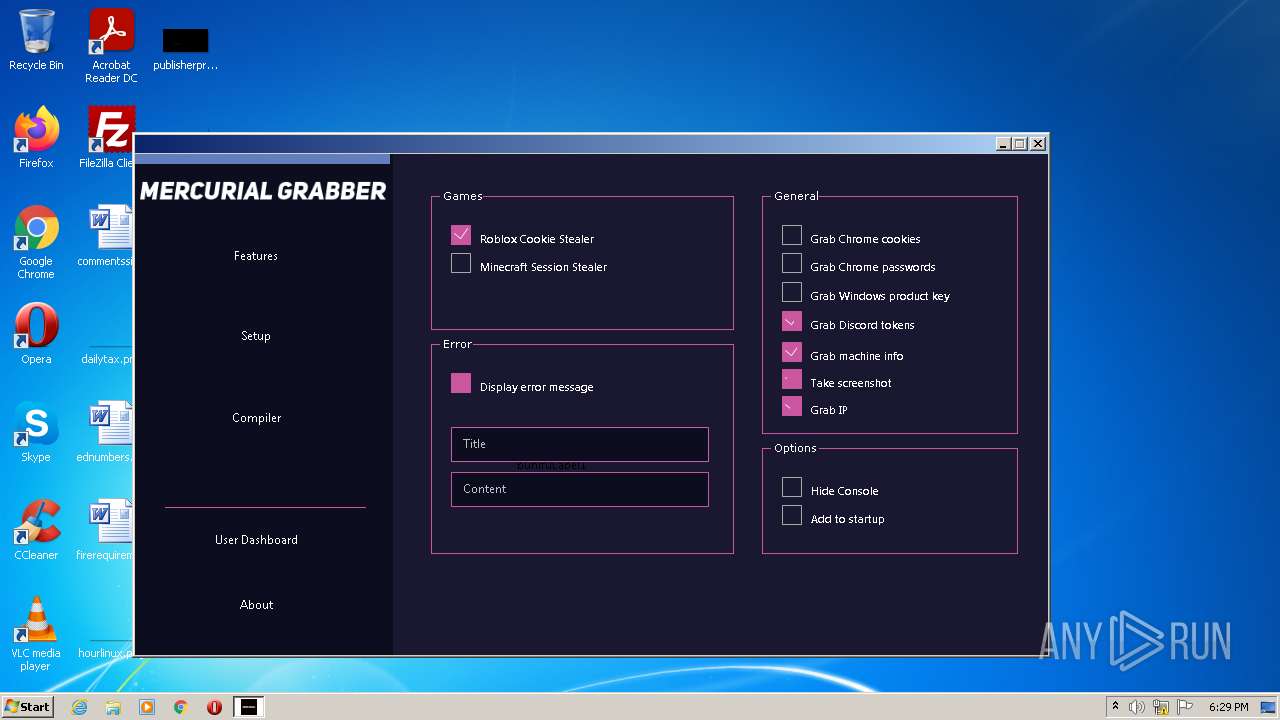
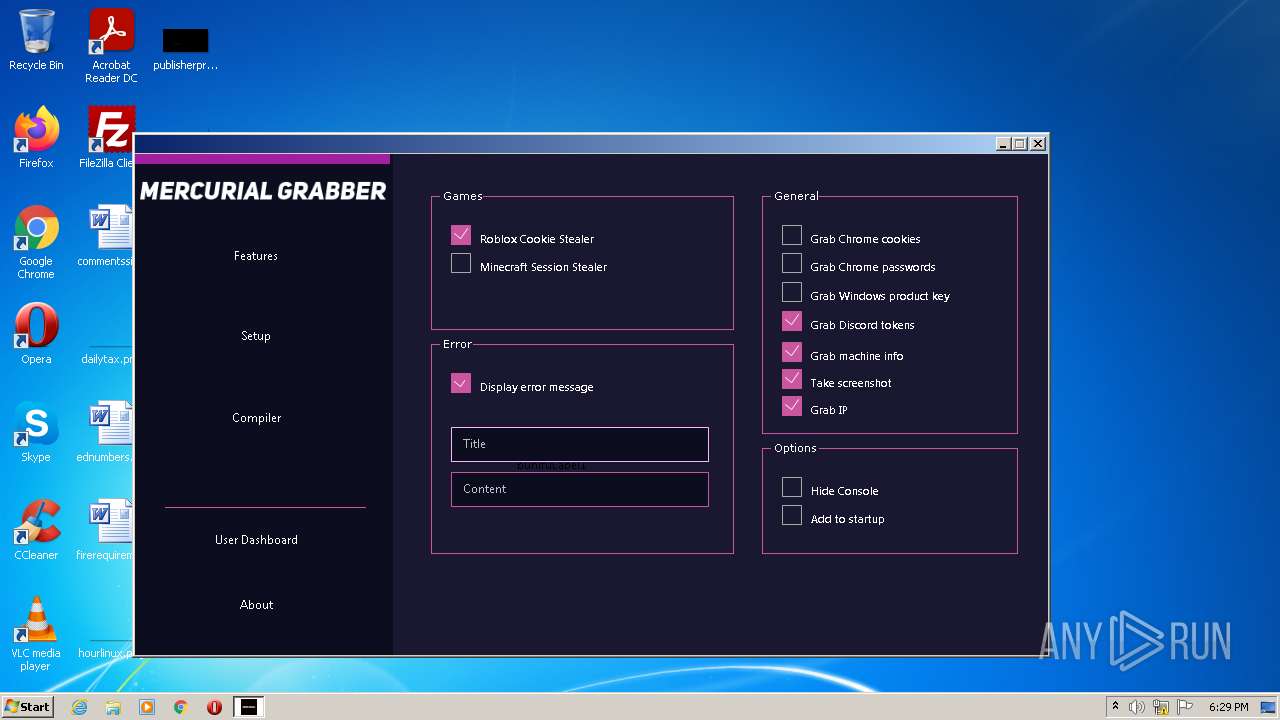
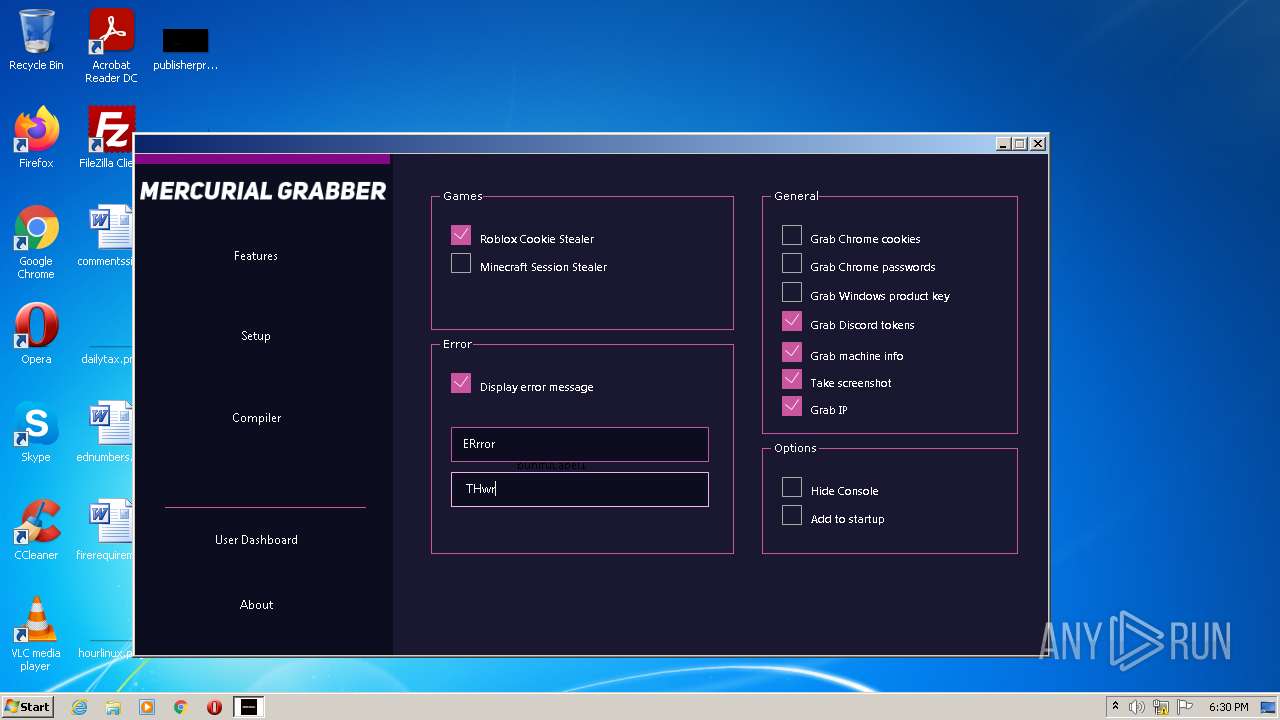
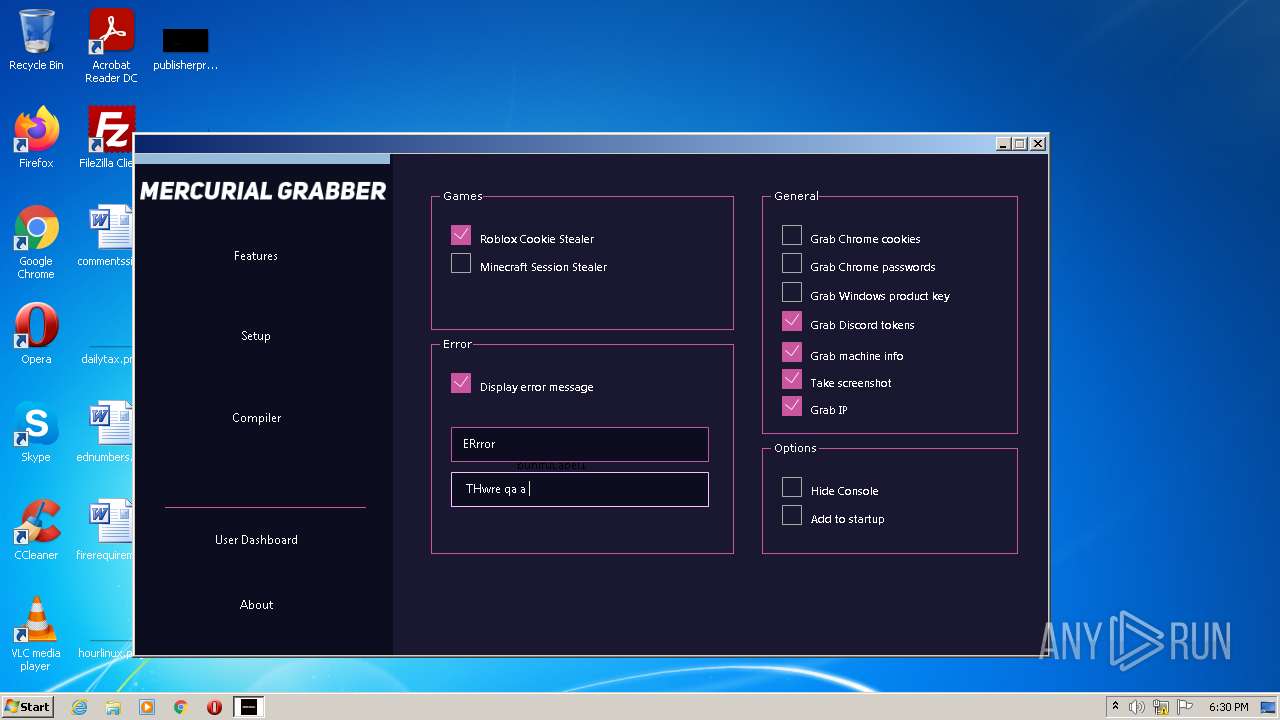
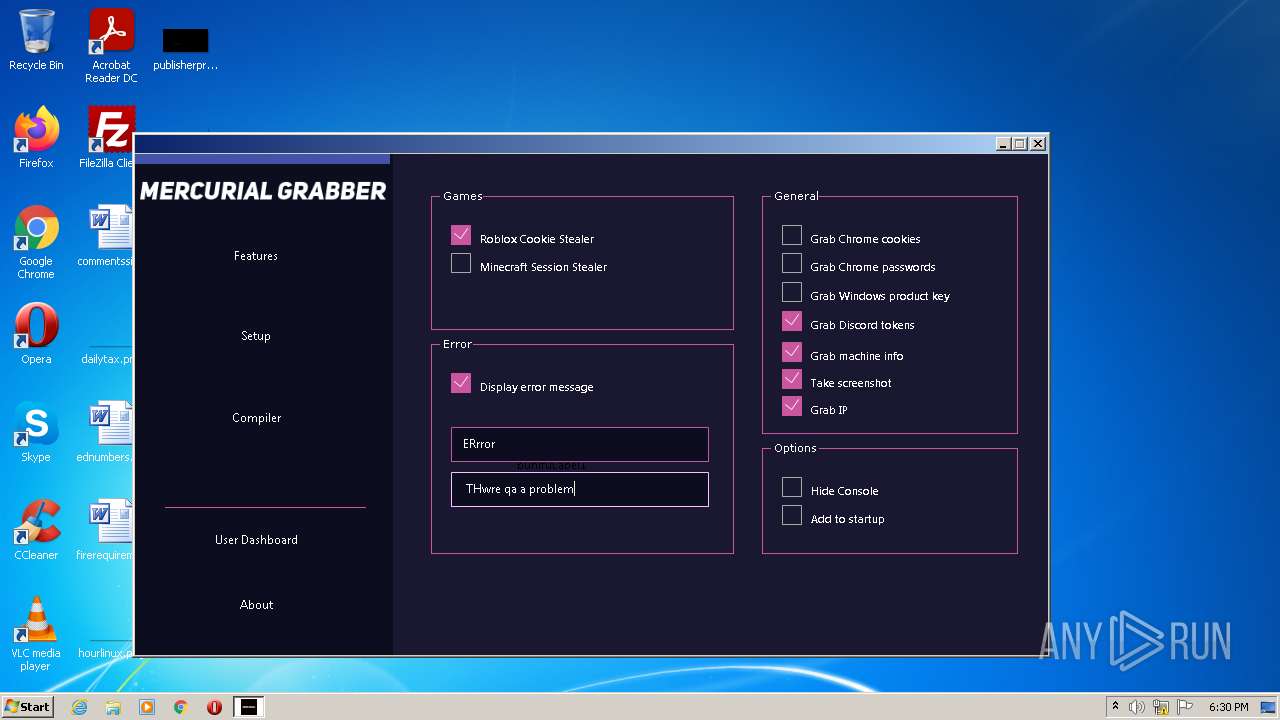
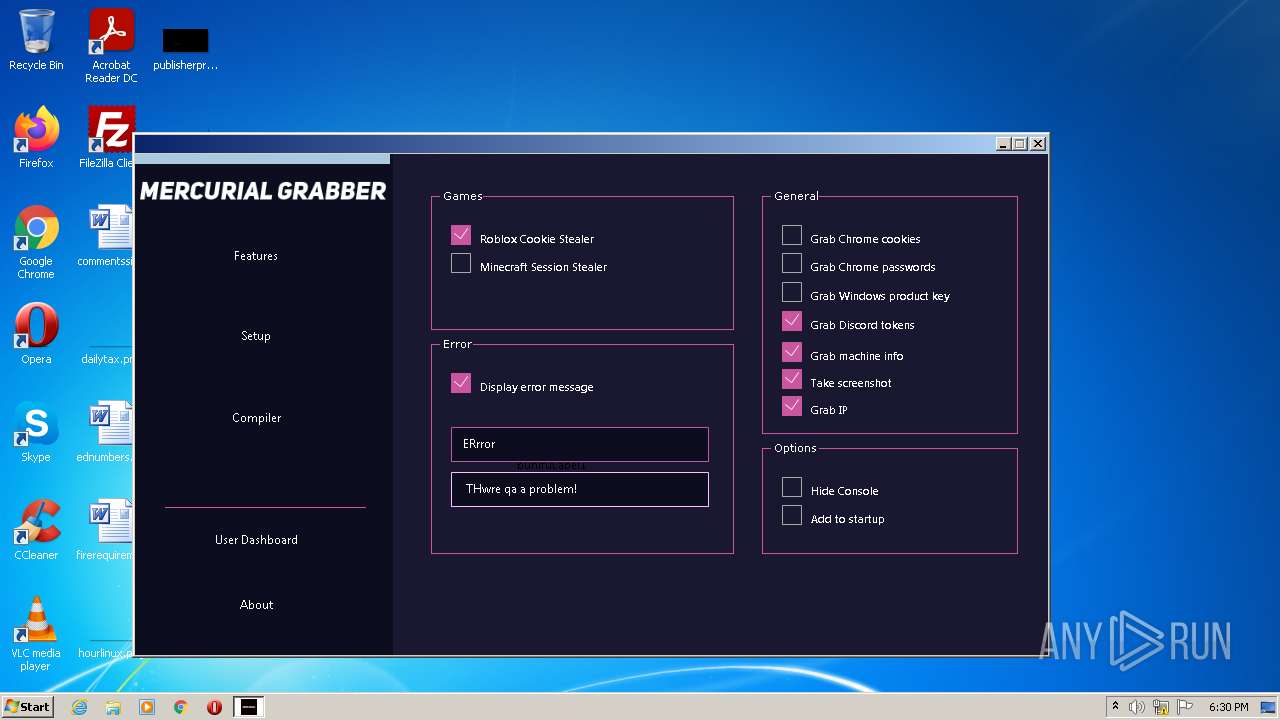
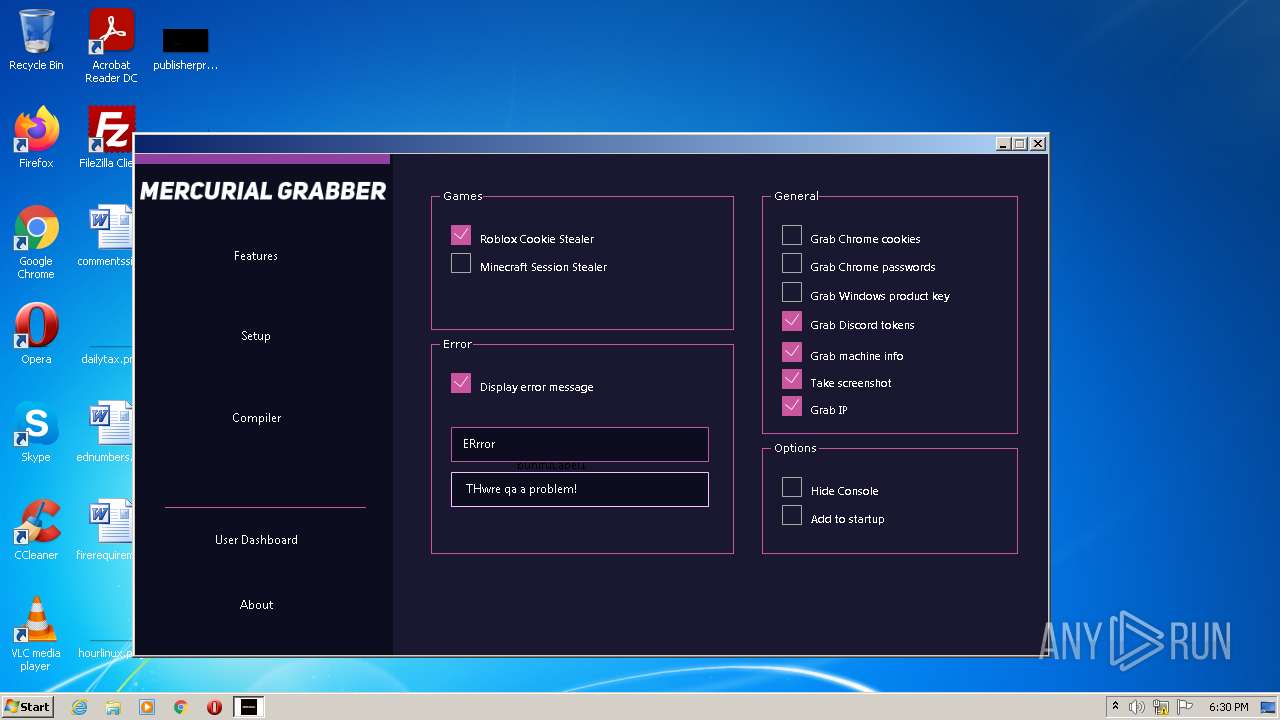
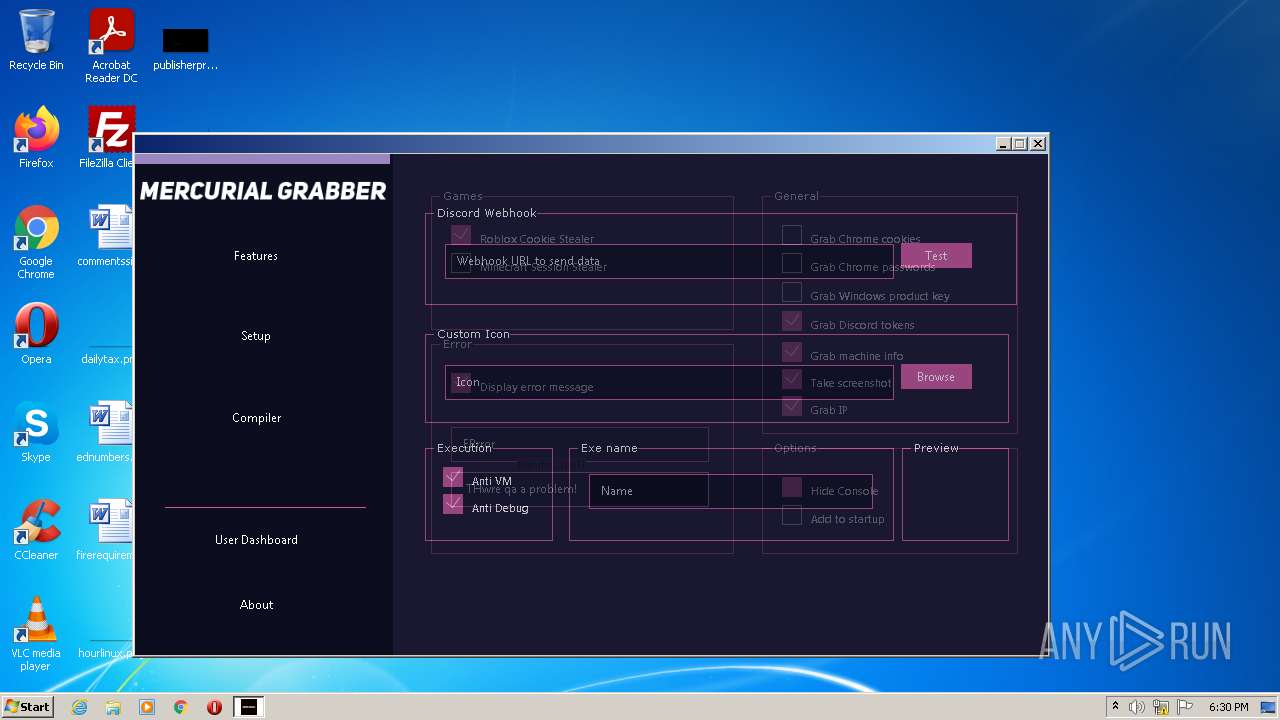
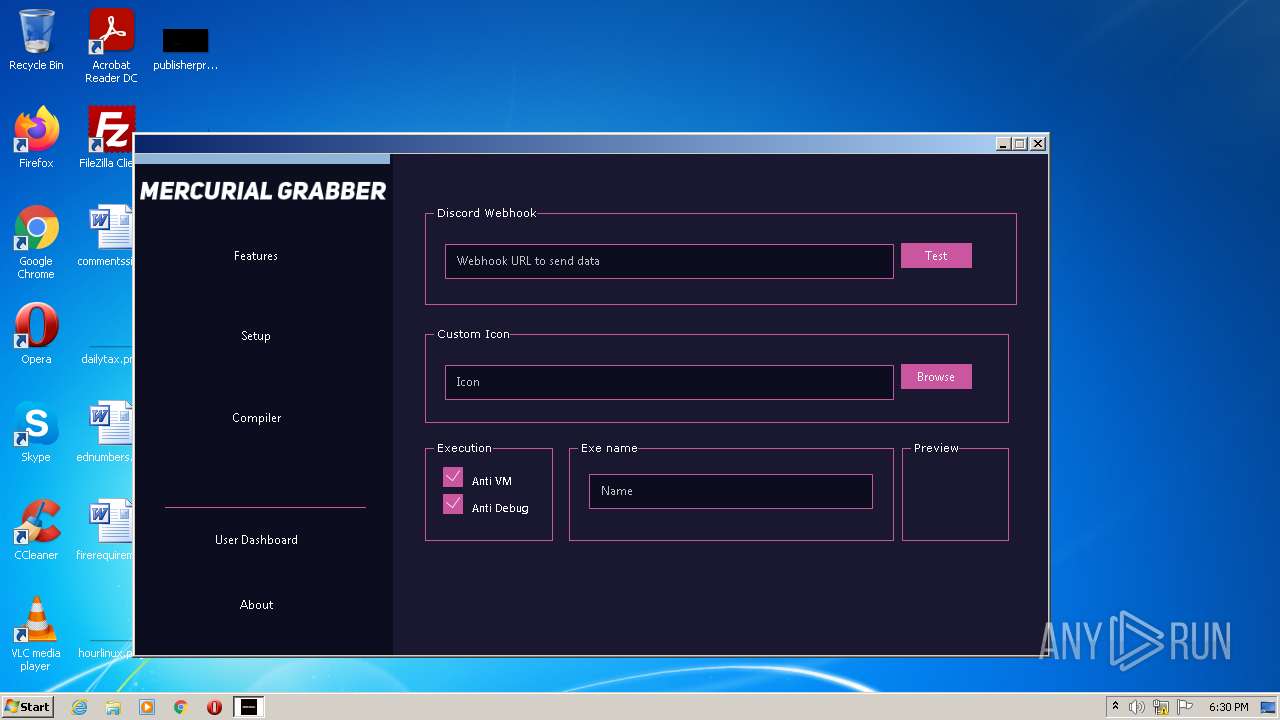
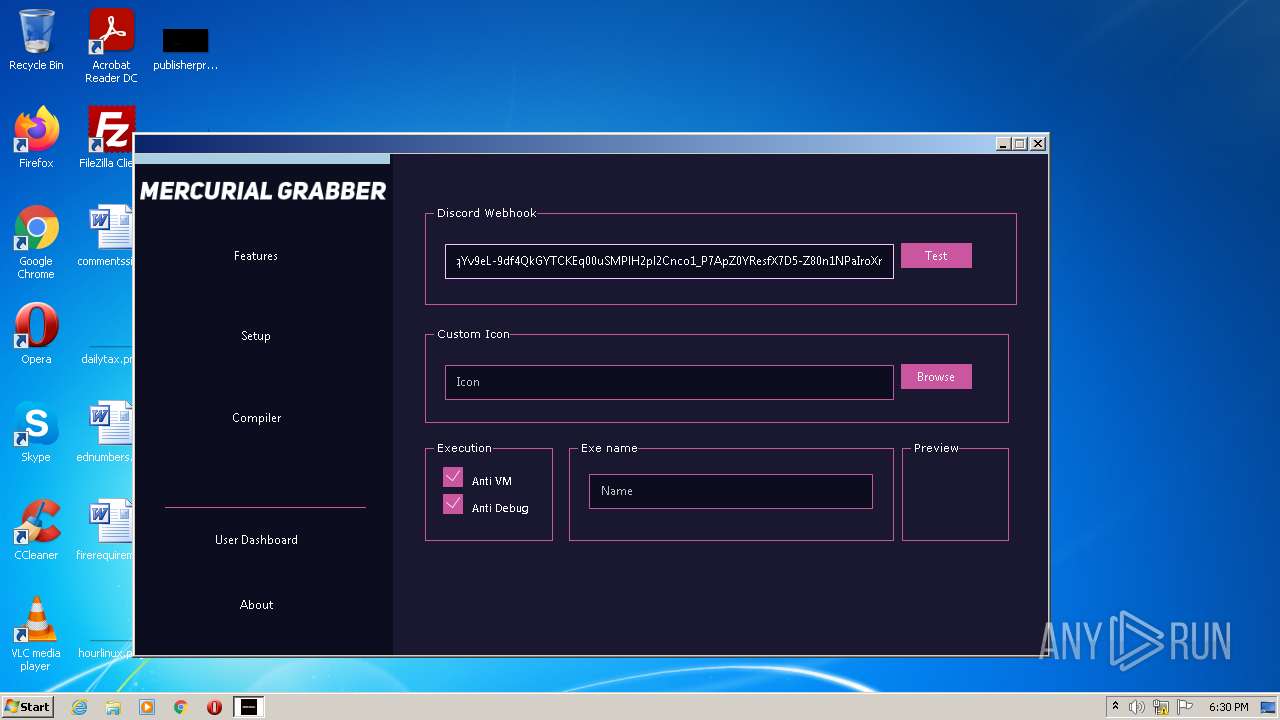
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 18:29:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A9477B3E21018B96FC5D2264D4016E65 |
| SHA1: | 493FA8DA8BF89EA773AEB282215F78219A5401B7 |
| SHA256: | 890FD59AF3370E2CE12E0D11916D1AD4EE9B9C267C434347DBED11E9572E8645 |
| SSDEEP: | 98304:5kjozJ9/im8XVBKl6t1buVfRhq+5tXzgCa/T:lzJpjS346t1bIfuq07 |
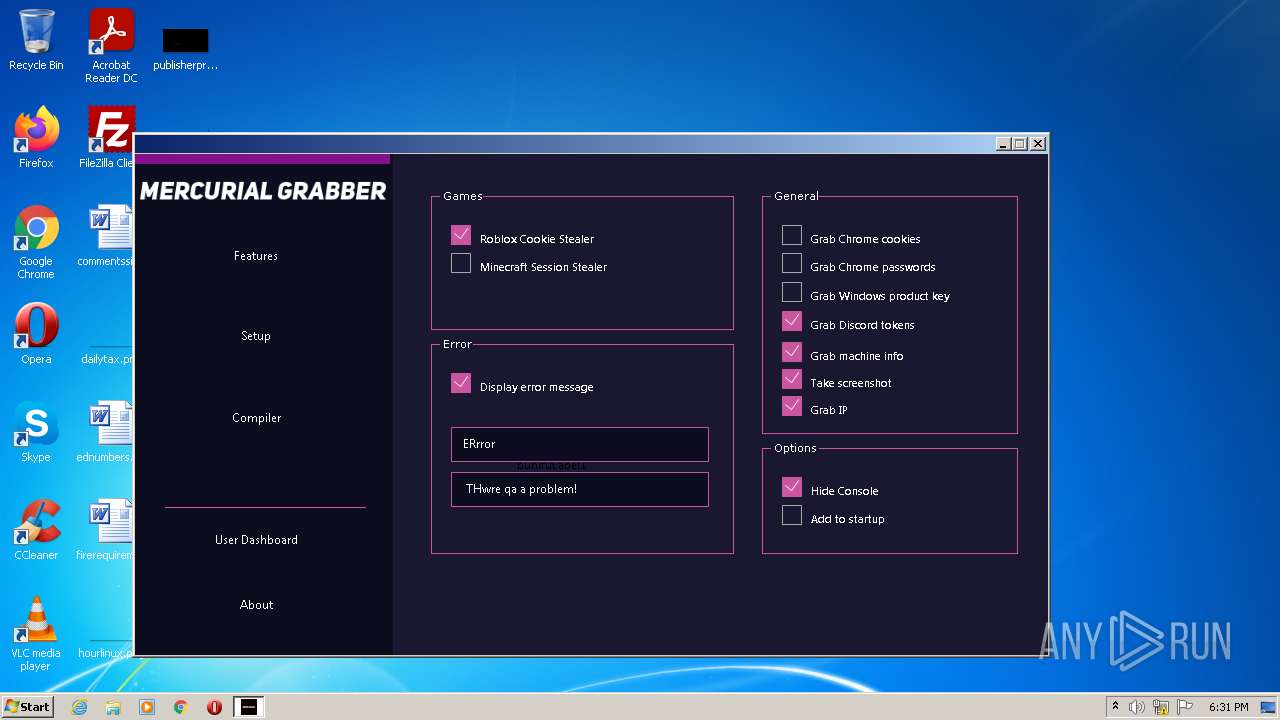
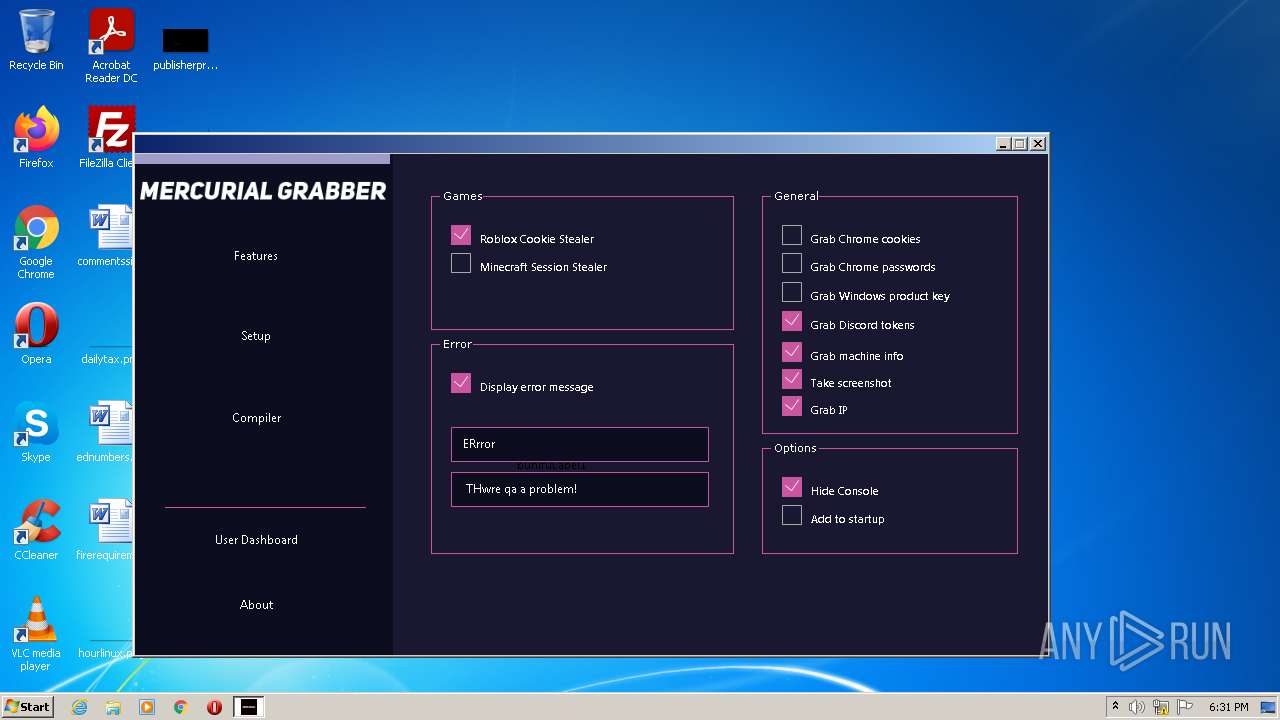
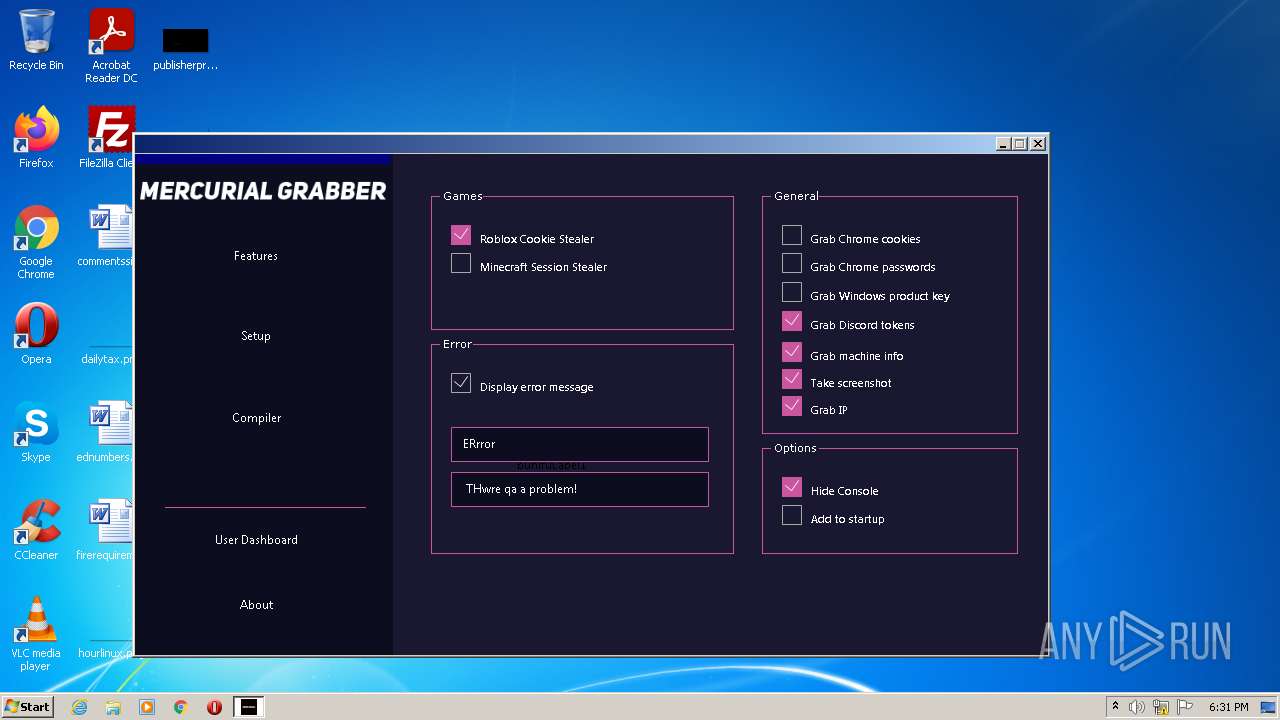
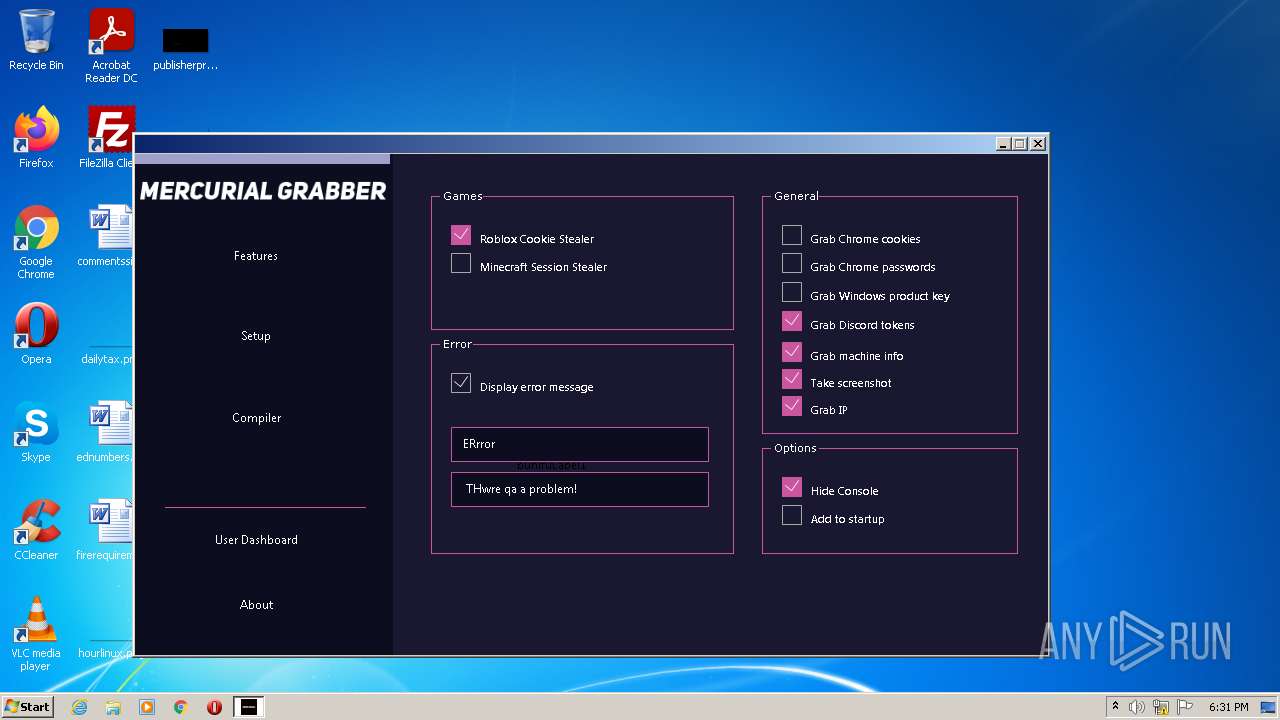
MALICIOUS
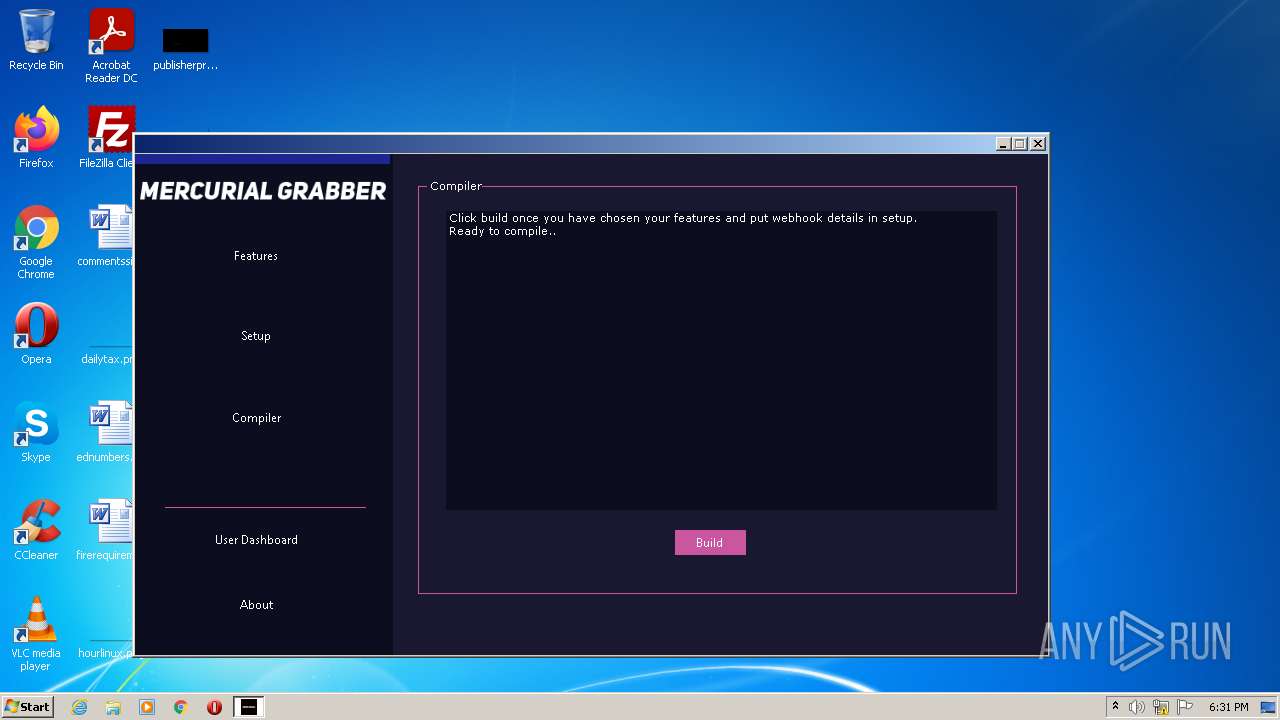
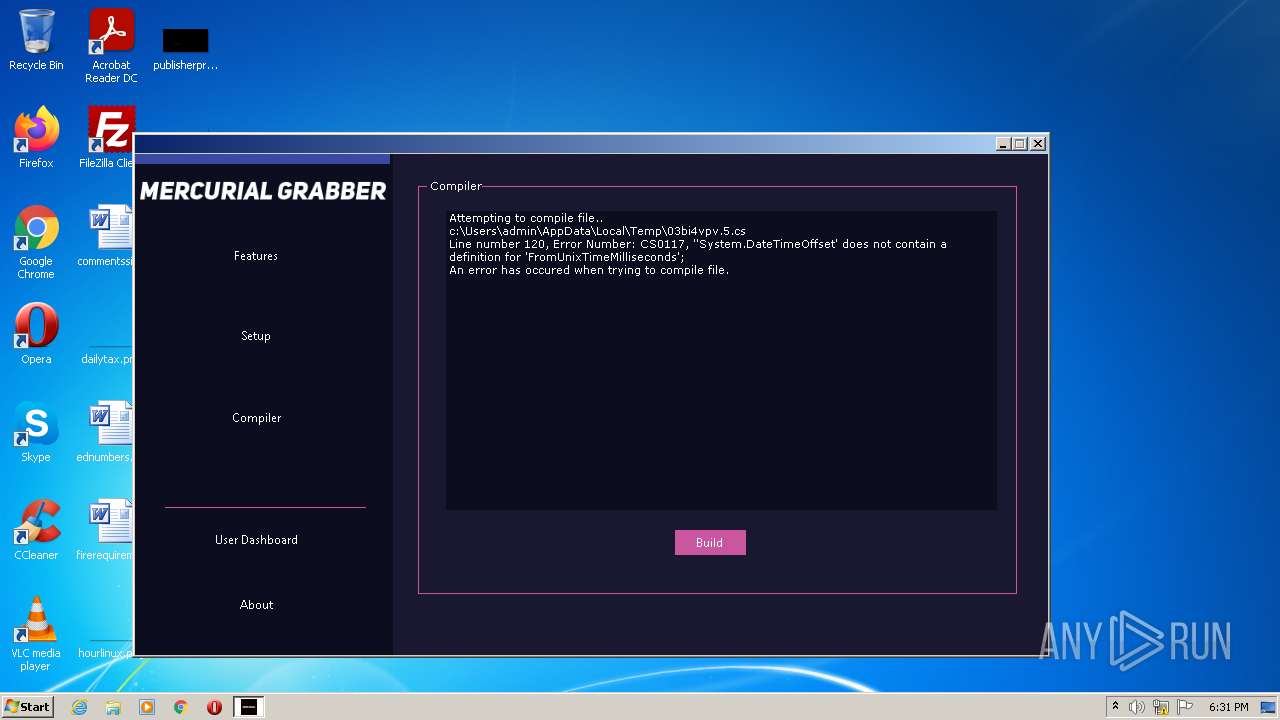
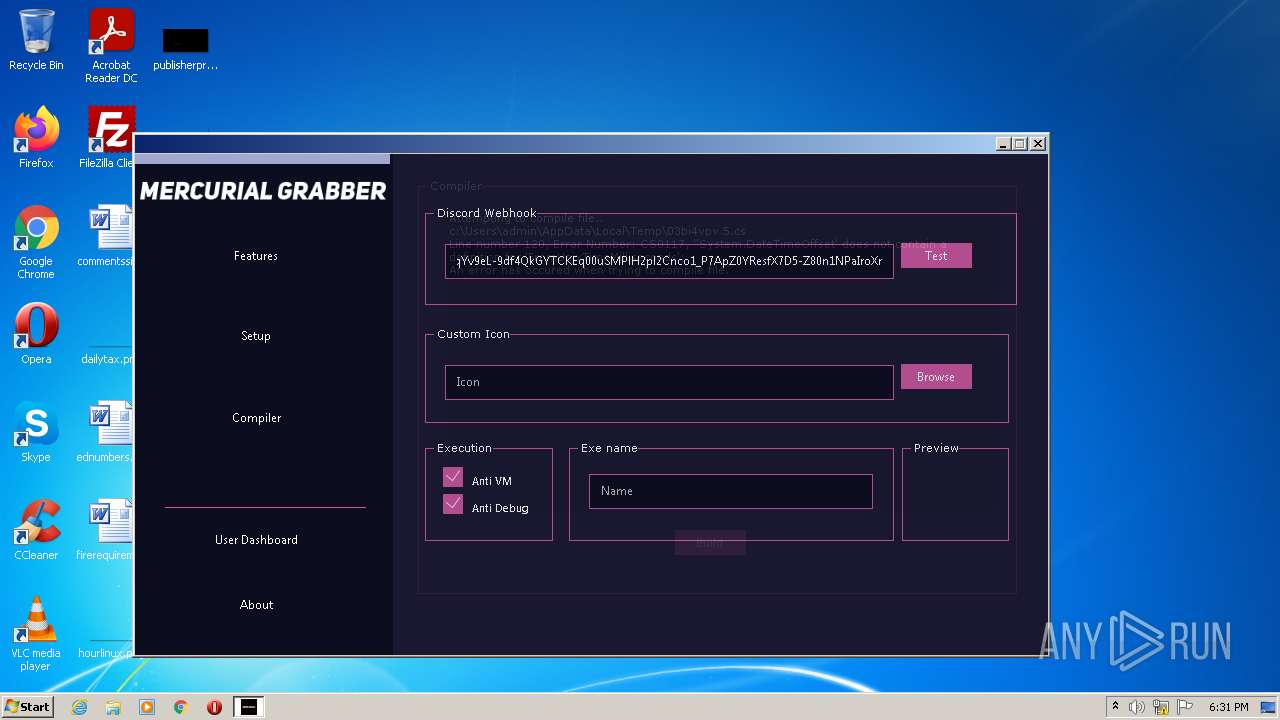
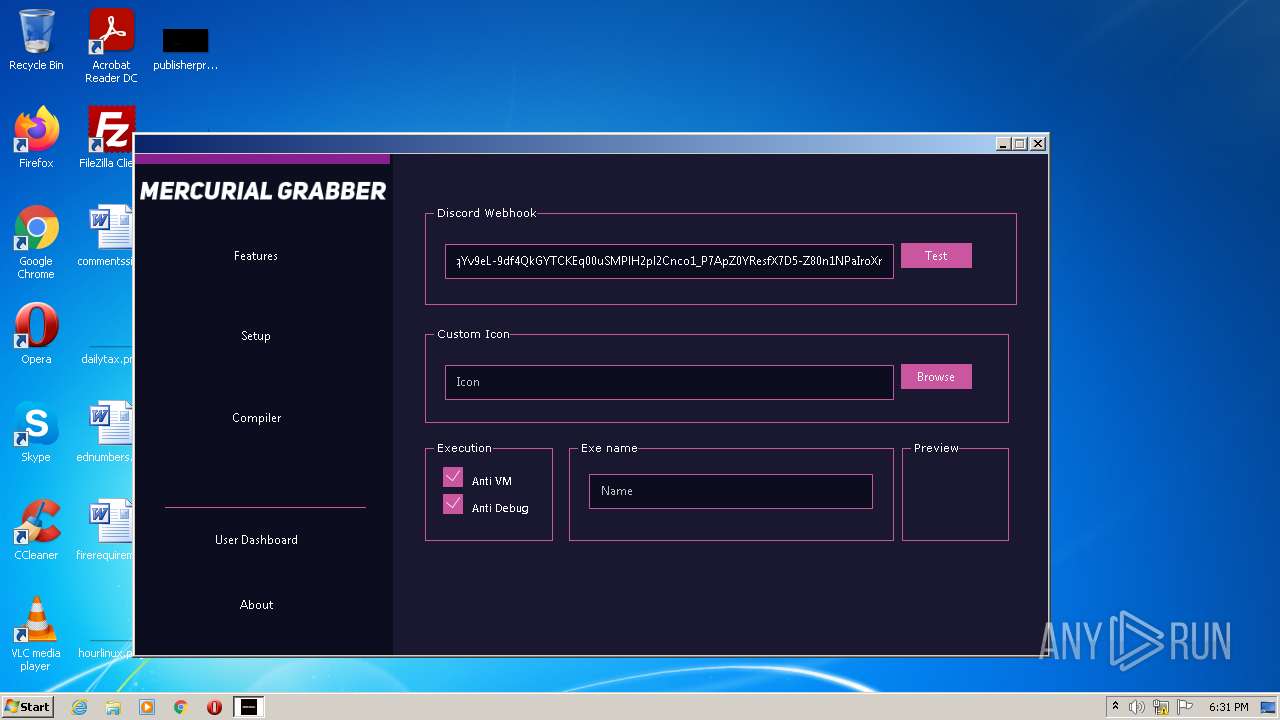
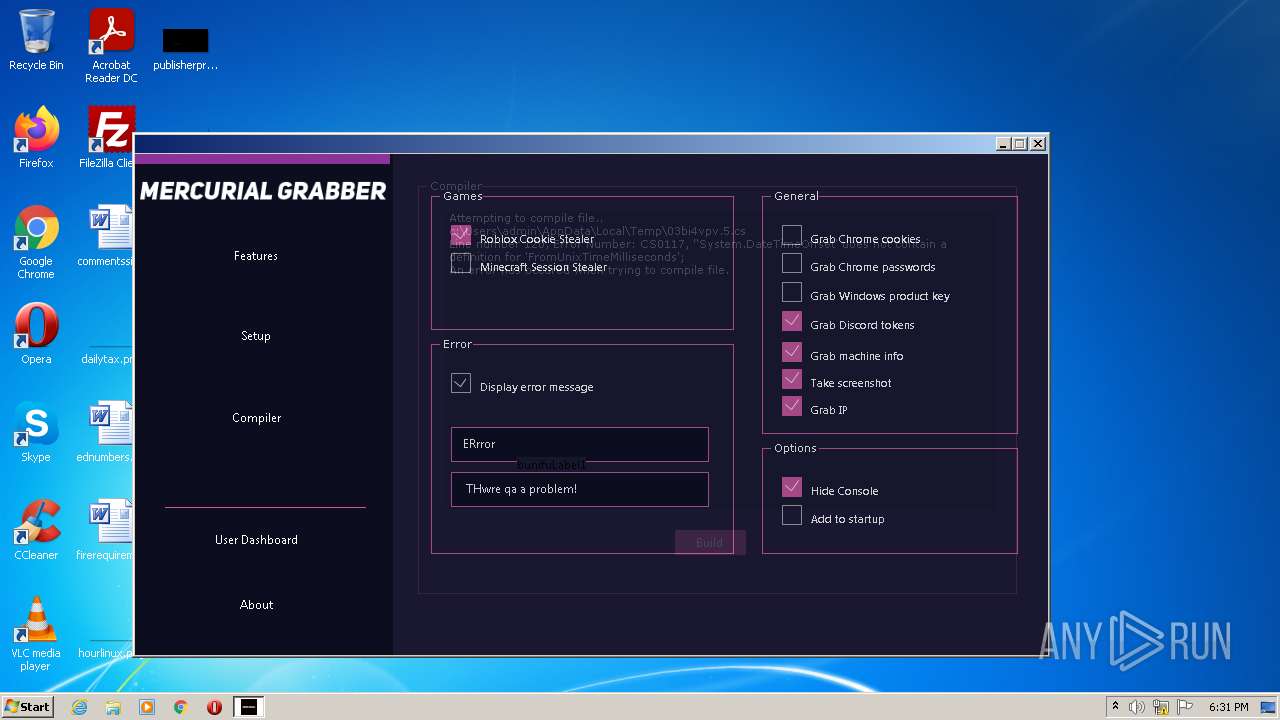
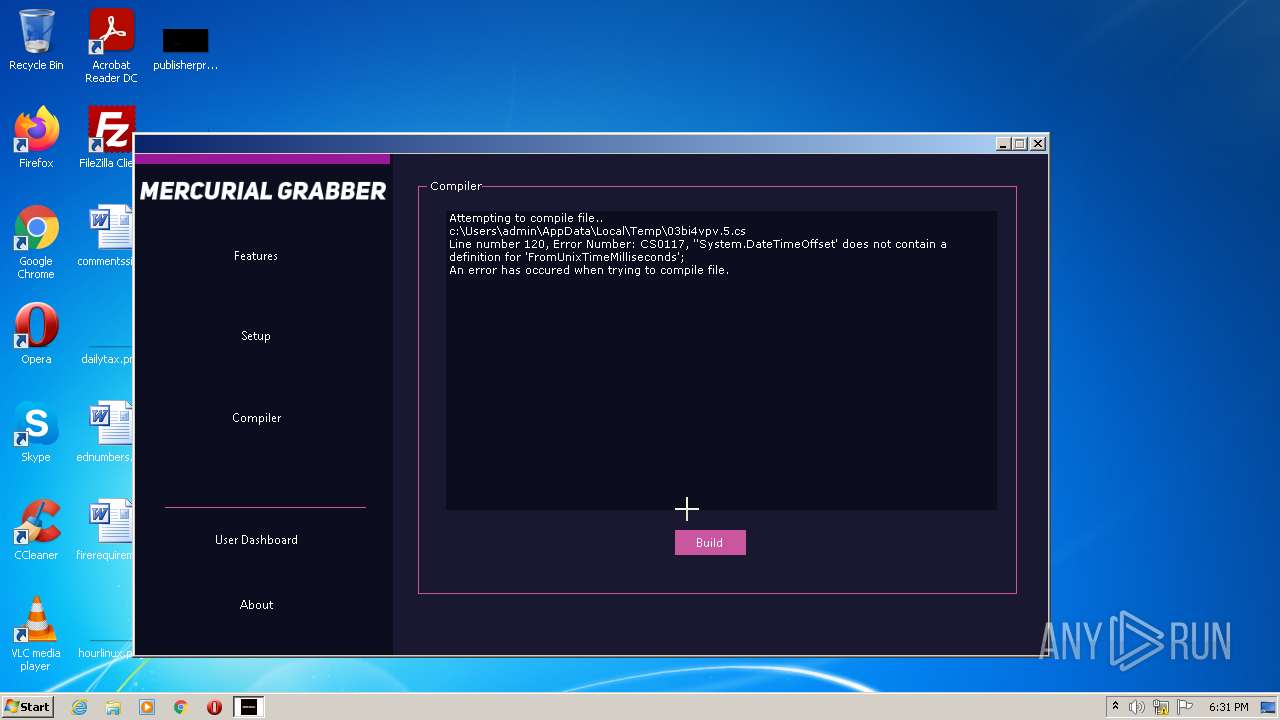
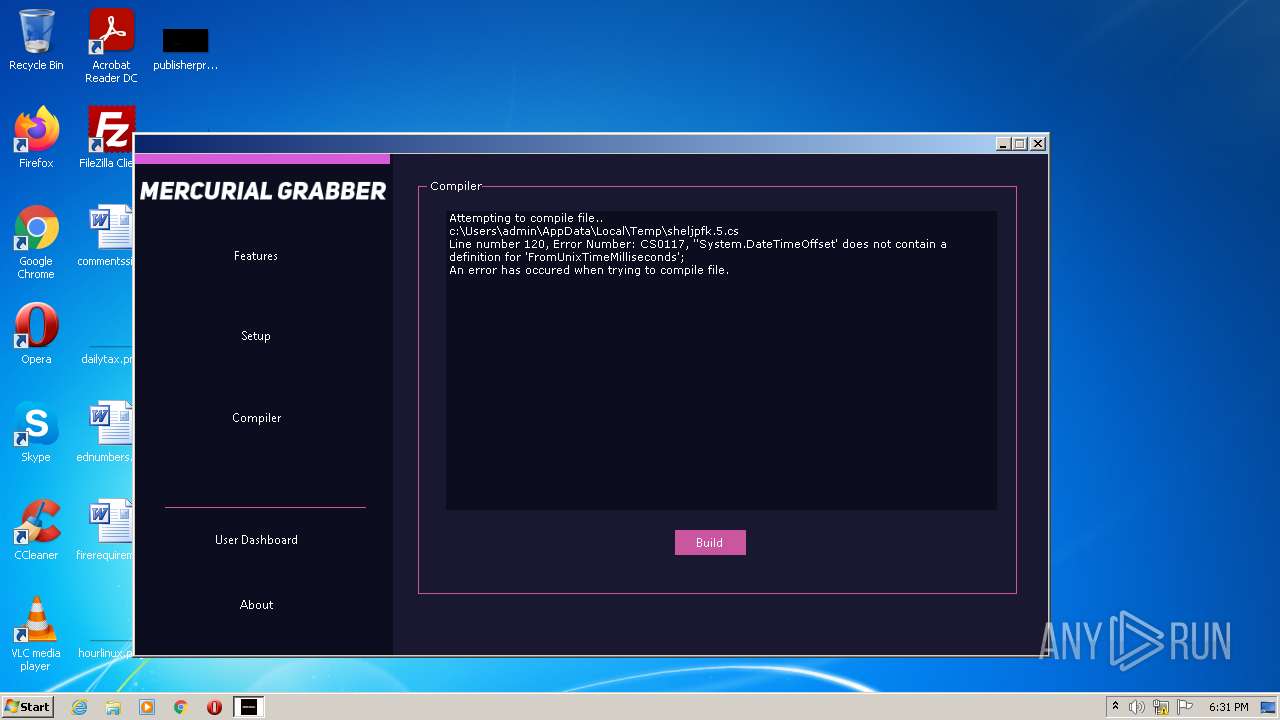
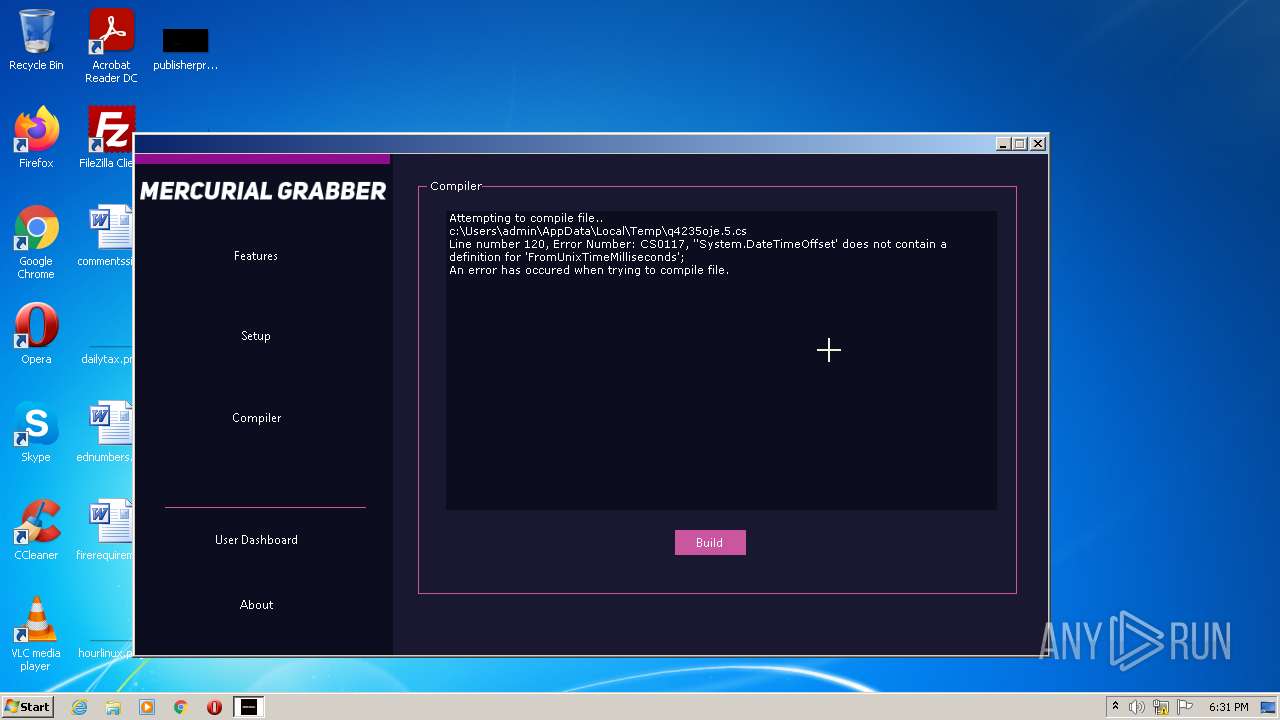
Starts Visual C# compiler
- Mercurial.exe (PID: 3176)
SUSPICIOUS
Reads the computer name
- Mercurial.exe (PID: 3176)
Checks supported languages
- csc.exe (PID: 3920)
- Mercurial.exe (PID: 3176)
- csc.exe (PID: 3052)
- csc.exe (PID: 3400)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
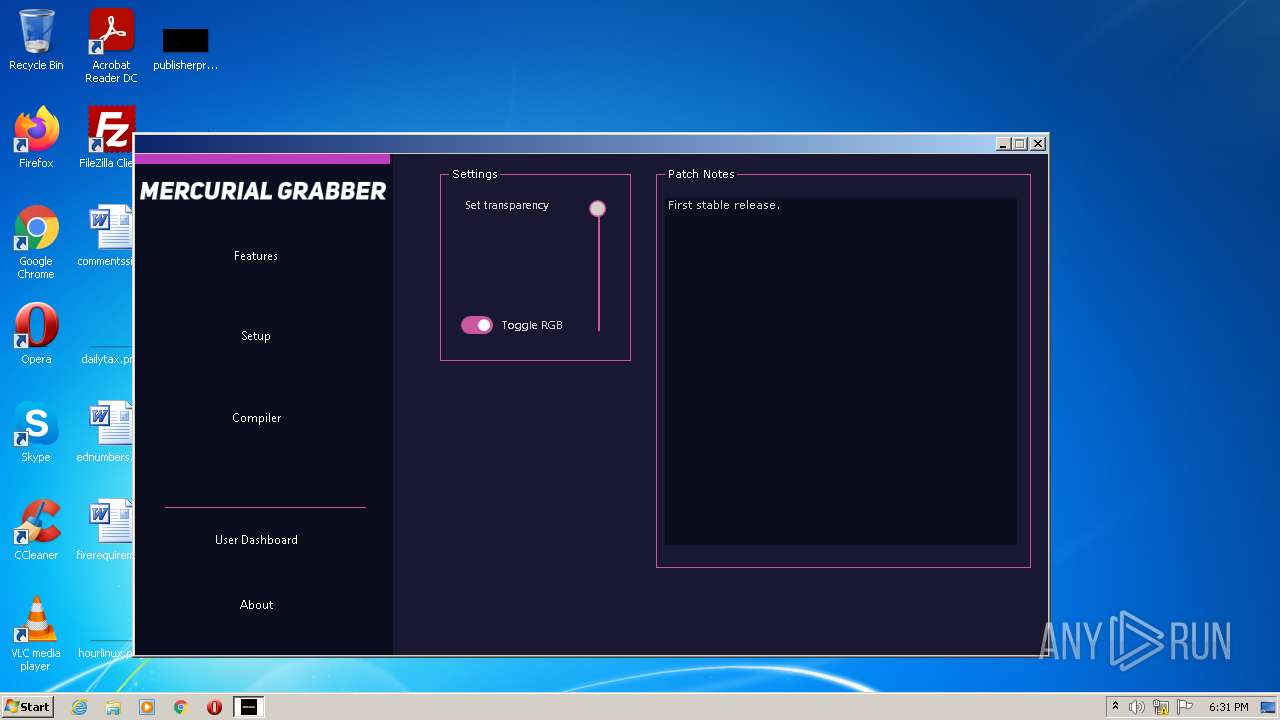
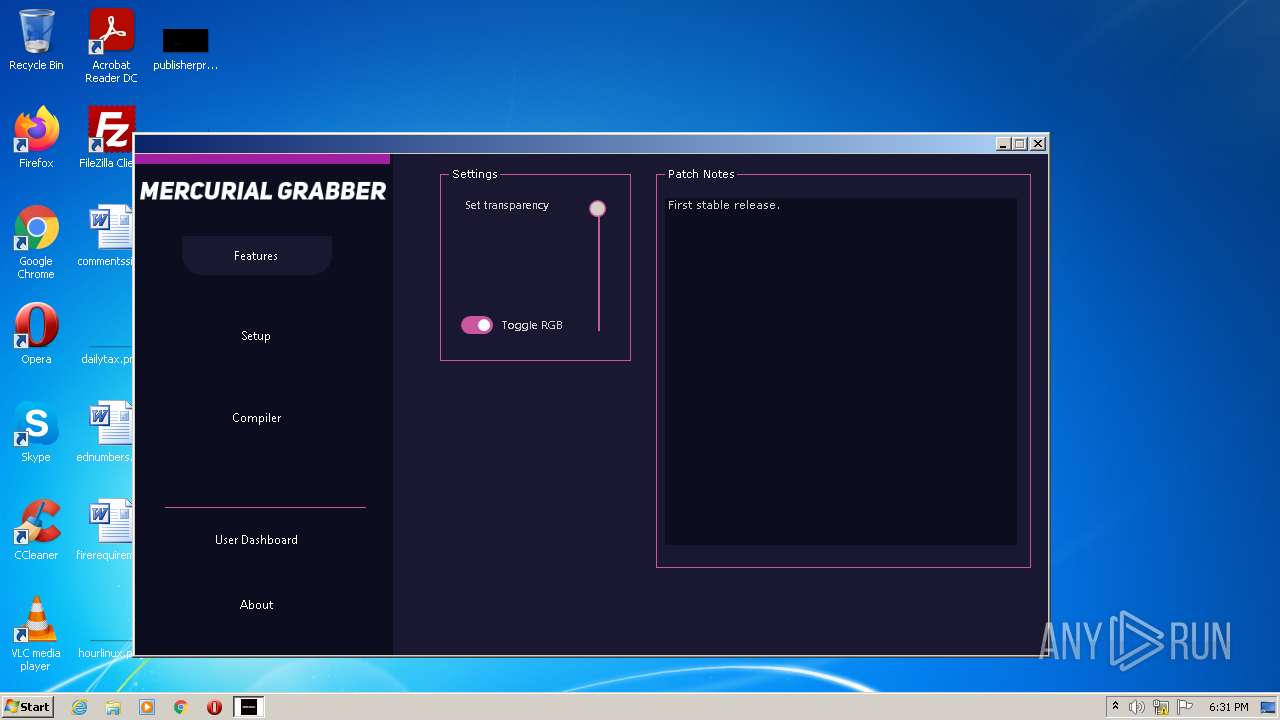
| ProductName: | Mercurial |
| OriginalFileName: | Mercurial.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2021 |
| InternalName: | Mercurial.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Mercurial |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x31bafe |
| UninitializedDataSize: | - |
| InitializedDataSize: | 109568 |
| CodeSize: | 3251200 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2073:01:04 02:50:04+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Nov-1936 19:21:48 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Mercurial |
| FileVersion: | 1.0.0.0 |
| InternalName: | Mercurial.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | Mercurial.exe |
| ProductName: | Mercurial |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 28-Nov-1936 19:21:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00319B04 | 0x00319C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.92929 |
.rsrc | 0x0031C000 | 0x0001A8B4 | 0x0001AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.6757 |
.reloc | 0x00338000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 1.86656 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.10964 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.23942 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.25977 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 2.16519 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
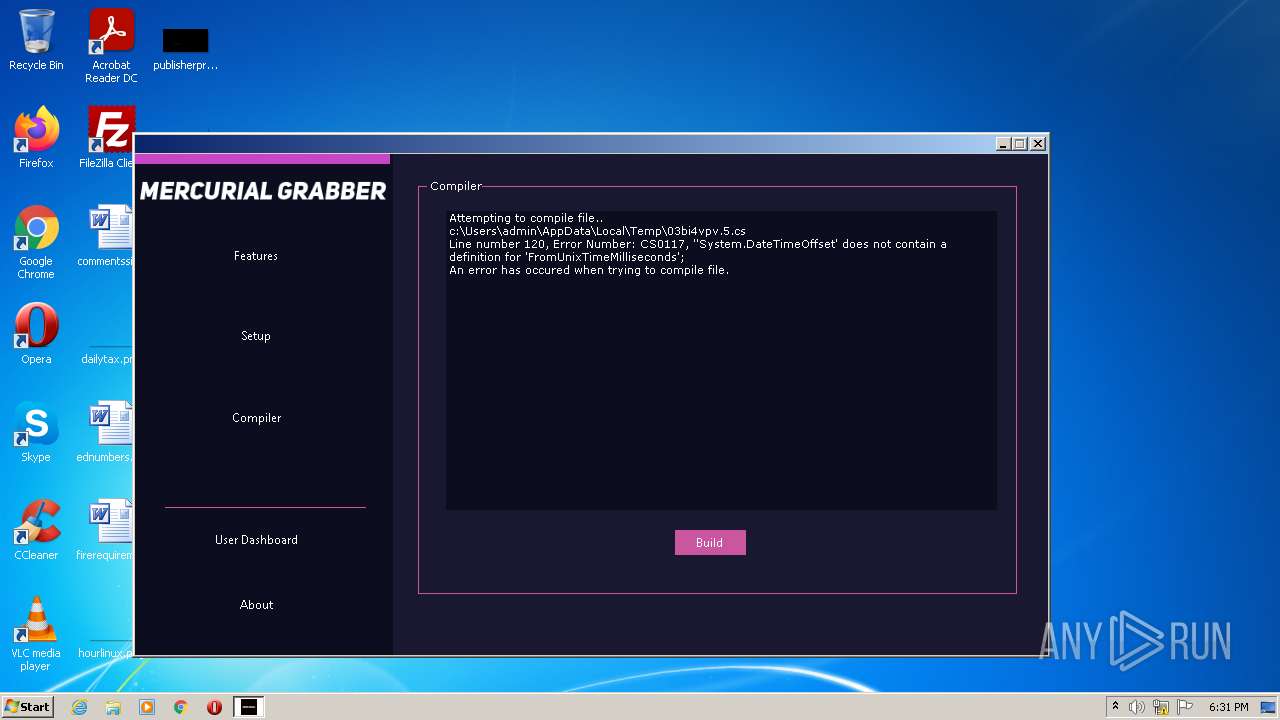
| 3052 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\sheljpfk.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | Mercurial.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 3176 | "C:\Users\admin\Desktop\Mercurial.exe" | C:\Users\admin\Desktop\Mercurial.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Mercurial Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3400 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\q4235oje.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | Mercurial.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 3920 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\03bi4vpv.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | Mercurial.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
Total events
1 048
Read events
1 048
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3176 | Mercurial.exe | C:\Users\admin\AppData\Local\Temp\03bi4vpv.0.cs | text | |
MD5:— | SHA256:— | |||
| 3176 | Mercurial.exe | C:\Users\admin\AppData\Local\Temp\03bi4vpv.1.cs | text | |
MD5:8AAB1997664A604ACA551B20202BFD14 | SHA256:029F57FA483BBCEE0DD5464E0D4D89BD03032161424D0FFD1DA2B3D5DB15977F | |||
| 3920 | csc.exe | C:\Users\admin\AppData\Local\Temp\03bi4vpv.out | text | |
MD5:— | SHA256:— | |||
| 3176 | Mercurial.exe | C:\Users\admin\AppData\Local\Temp\03bi4vpv.2.cs | text | |
MD5:6FDAE9AFC1F8E77E882F1BA6B5859A4E | SHA256:A365264DD2D3388ACC38B2F5C8F3C267BBF83CA463F70FBF6C8459123A7CC33D | |||
| 3176 | Mercurial.exe | C:\Users\admin\AppData\Local\Temp\03bi4vpv.cmdline | text | |
MD5:— | SHA256:— | |||
| 3176 | Mercurial.exe | C:\Users\admin\AppData\Local\Temp\sheljpfk.0.cs | text | |
MD5:— | SHA256:— | |||
| 3176 | Mercurial.exe | C:\Users\admin\AppData\Local\Temp\03bi4vpv.6.cs | text | |
MD5:8EC0F0E49FFE092345673AB4D9F45641 | SHA256:93B9F783B5FAED3ECFAFBE20DFCF1BEE3CE33F66909879CD39AE88C36ACBDFAC | |||
| 3176 | Mercurial.exe | C:\Users\admin\AppData\Local\Temp\03bi4vpv.4.cs | text | |
MD5:FAE5458A5B3CEE952E25D44D6EB9DB85 | SHA256:240478BB9C522341906A0EF376E0188CE6106856A26A3AE0F7B58AF07A377A06 | |||
| 3176 | Mercurial.exe | C:\Users\admin\AppData\Local\Temp\03bi4vpv.3.cs | text | |
MD5:6BA707982EE7E5F0AE55CE3FA5CCAD17 | SHA256:19AF9BEA270F830354AF8250CD82DB32FDCAB6327D139E2720713FB7D43A5797 | |||
| 3176 | Mercurial.exe | C:\Users\admin\AppData\Local\Temp\03bi4vpv.9.cs | text | |
MD5:380D15F61B0E775054EEFDCE7279510D | SHA256:BEF491A61351AD58CDA96B73DBA70027FDBE4966917E33145BA5CFA8C83BC717 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report