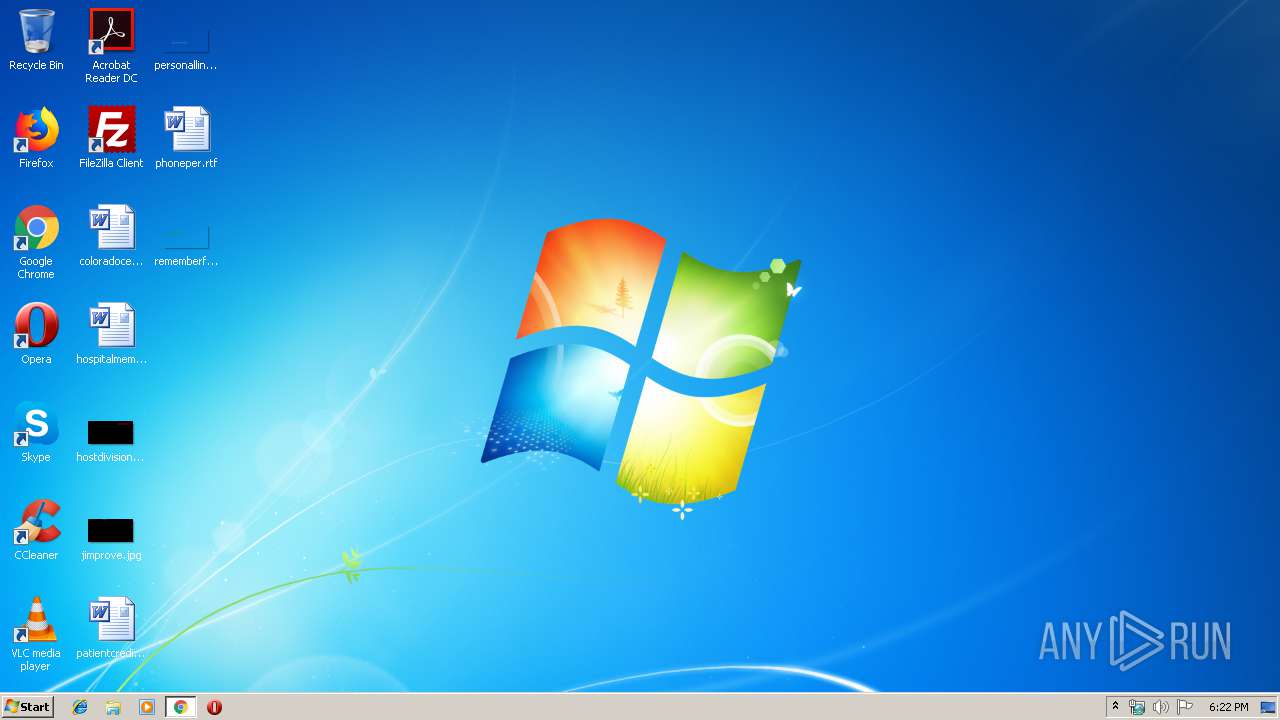
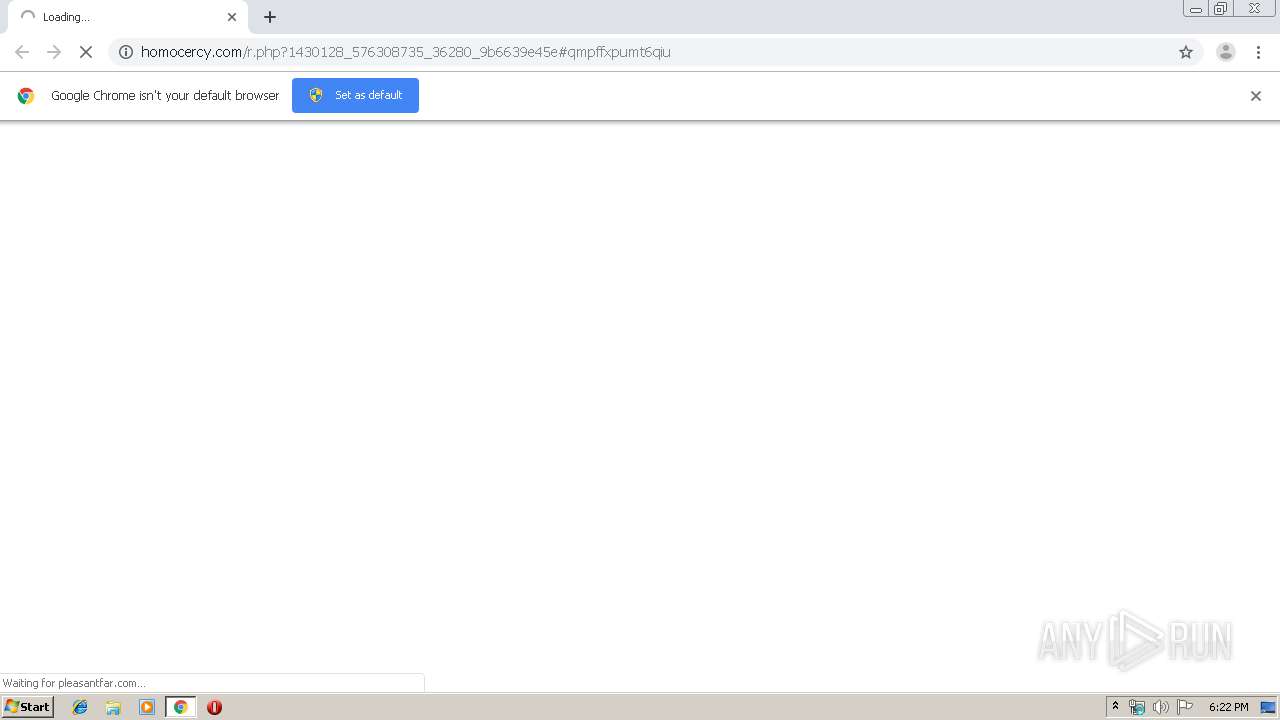
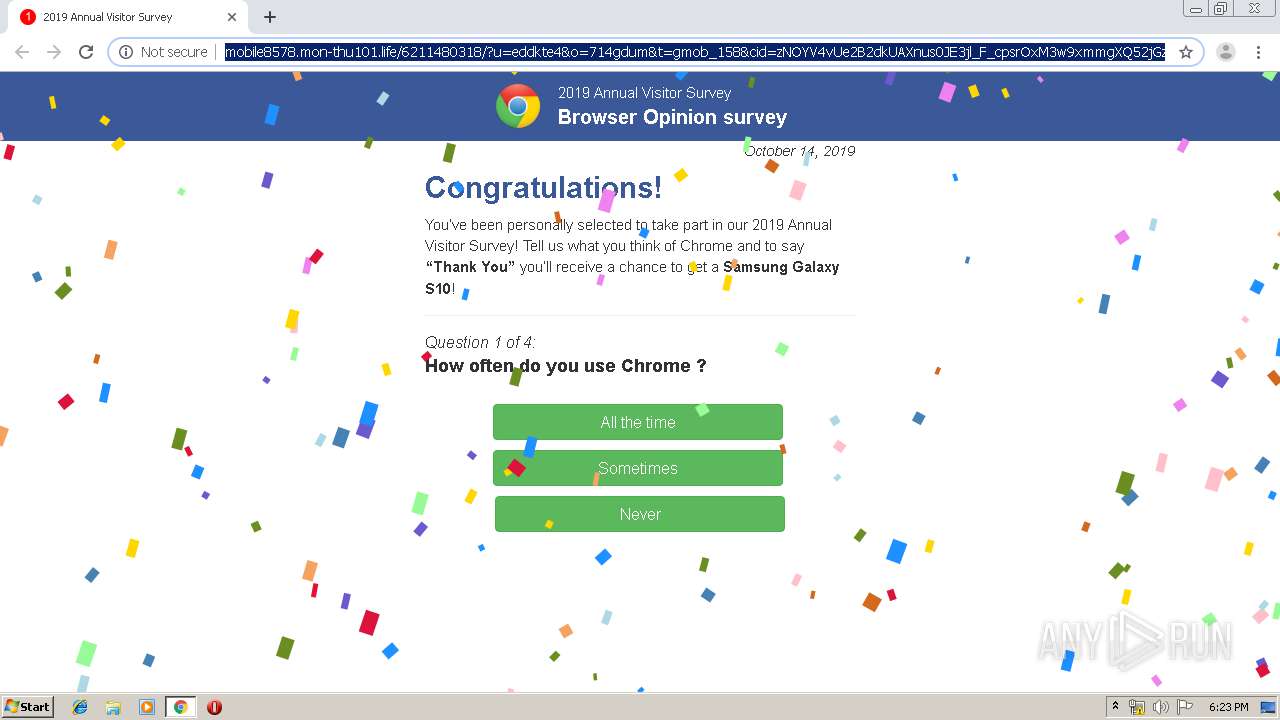
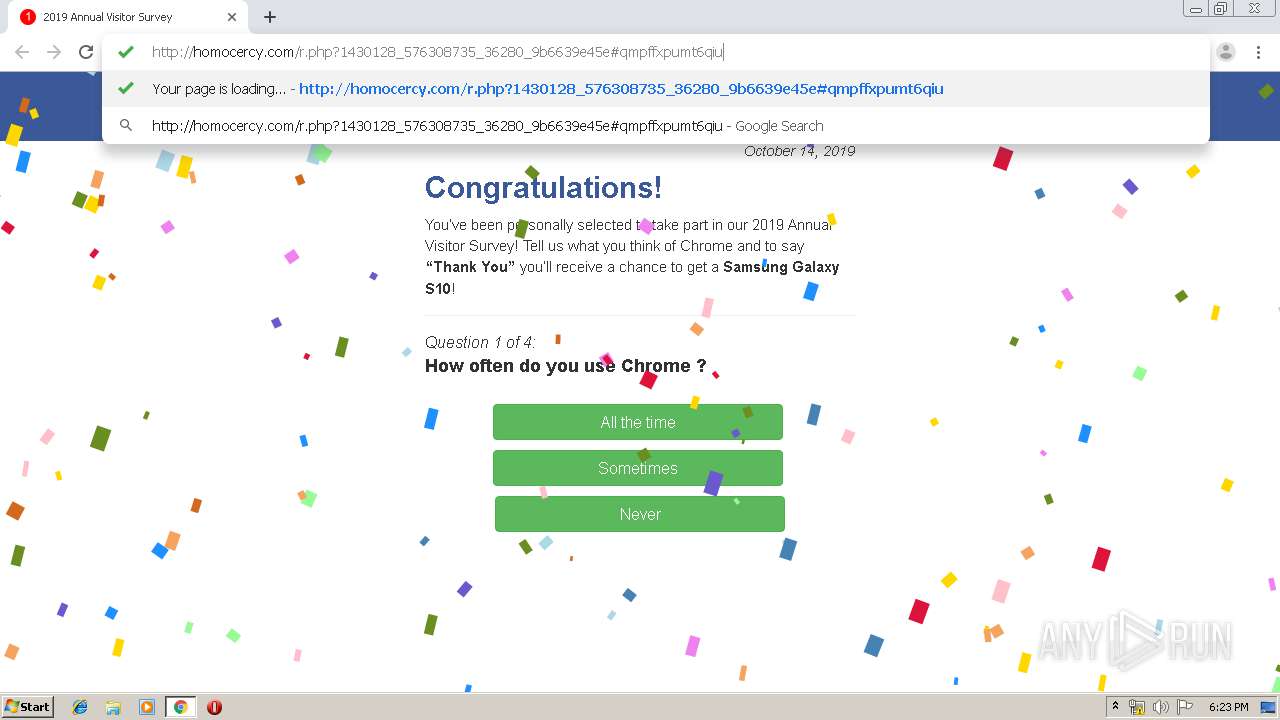
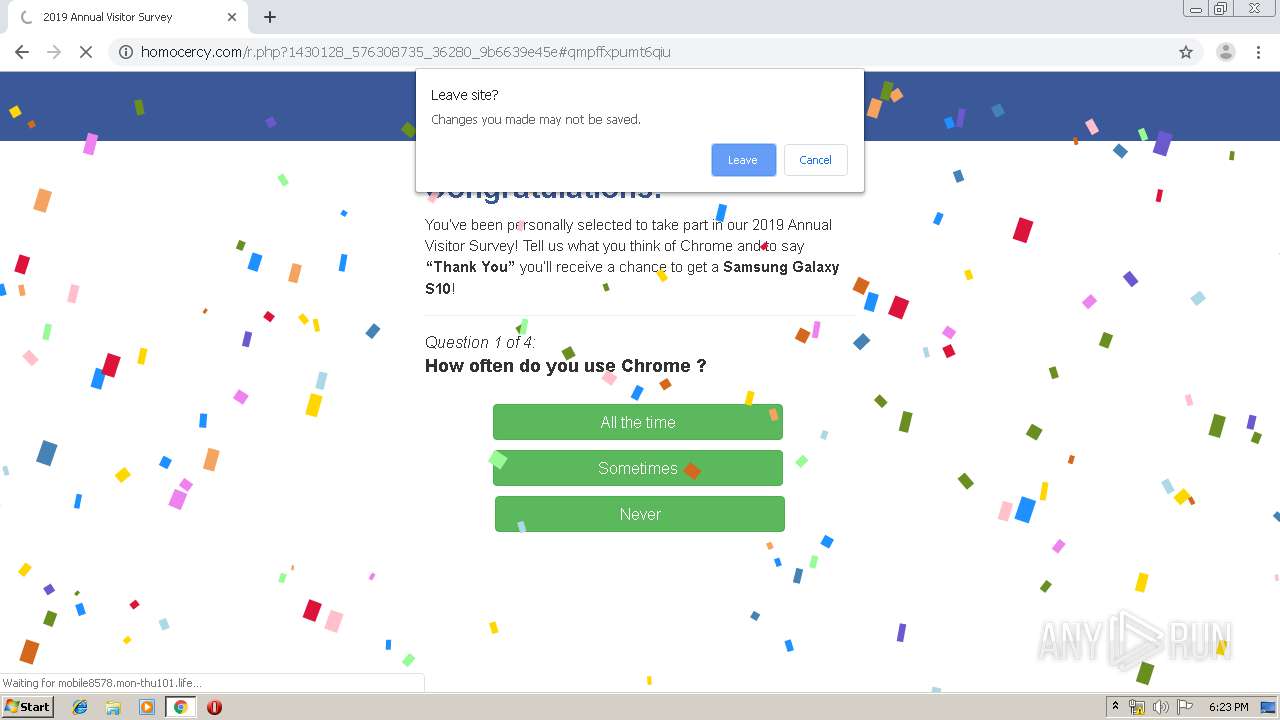
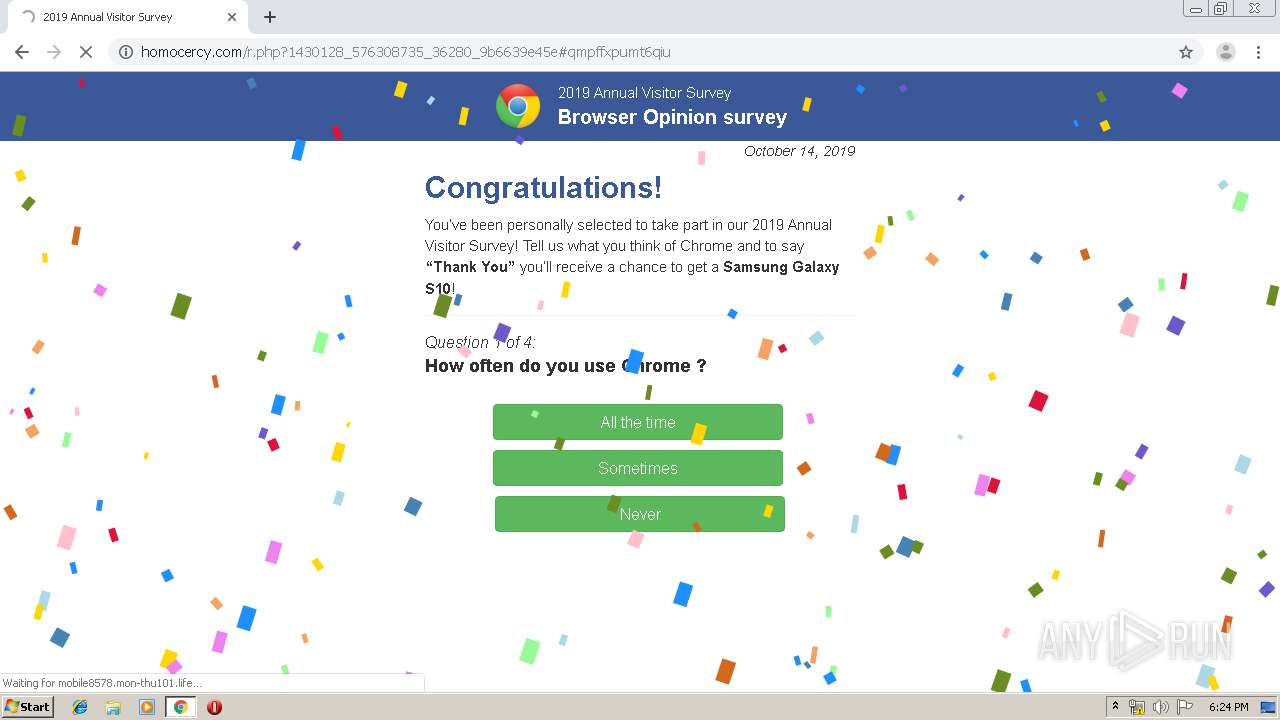
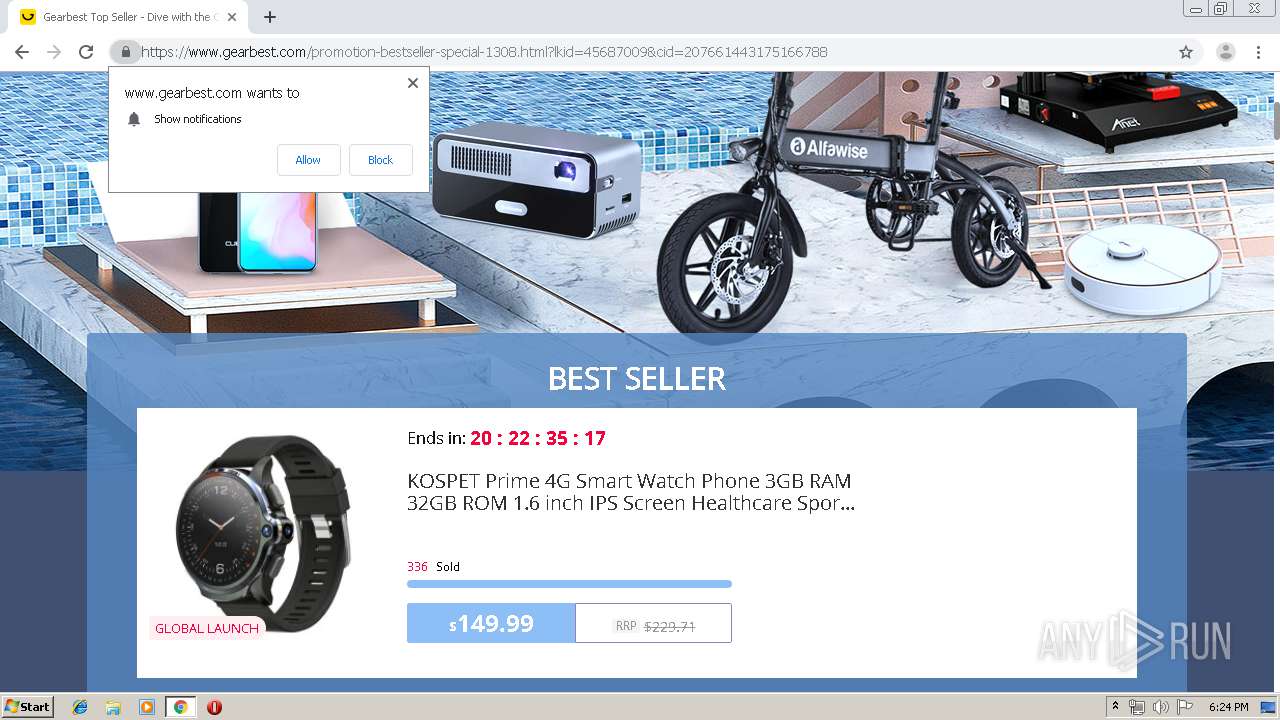
| URL: | http://homocercy.com/r.php?1430128_576308735_36280_9b6639e45e#qmpffxpumt6qiu |
| Full analysis: | https://app.any.run/tasks/f422aa29-3de3-41b4-9819-1b5beff846aa |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 17:22:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 486062F9EA1A1B75A6695180FB643ACA |
| SHA1: | AAA76BEF28261F368A7868922BF83C36BD8C37B0 |
| SHA256: | 890B0F0AC92FB88085122A9DADF778017544D4EDC6710478FABF6B591B6714A7 |
| SSDEEP: | 3:N1KWKnW6GunVa0jDGX6pQjUofdjc:CWmWtGVa0jaNz1o |
MALICIOUS
No malicious indicators.SUSPICIOUS
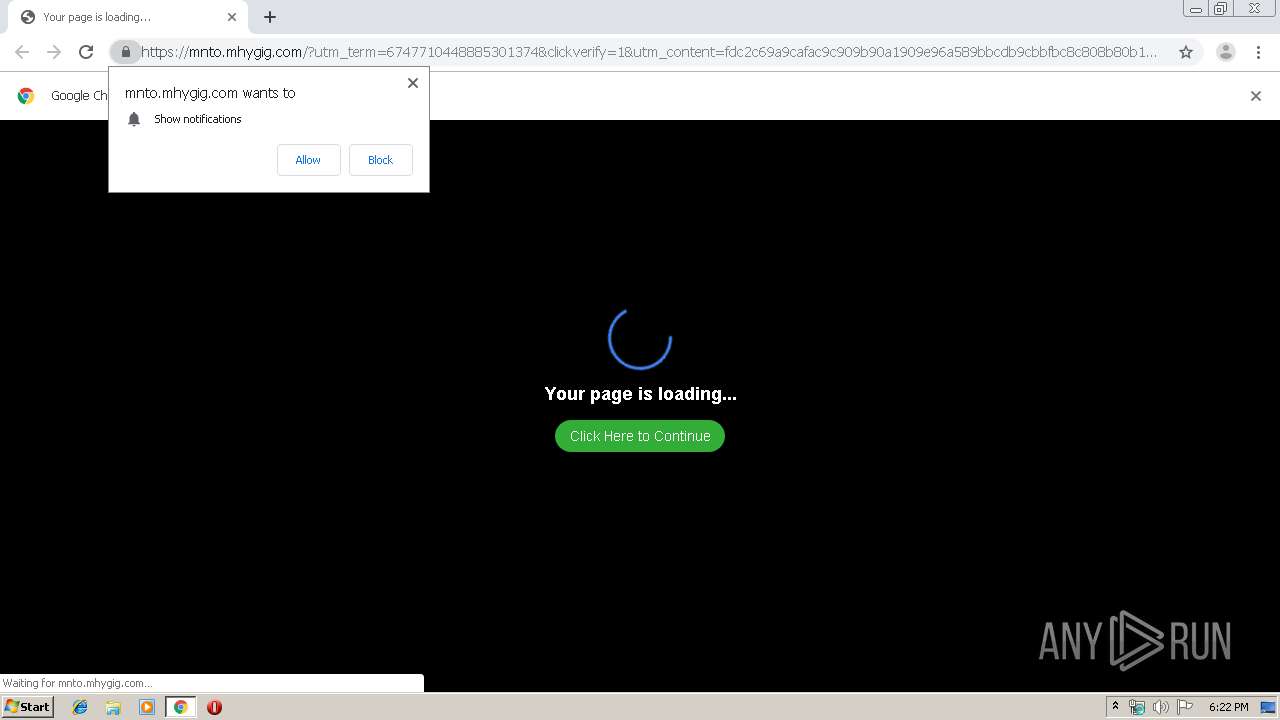
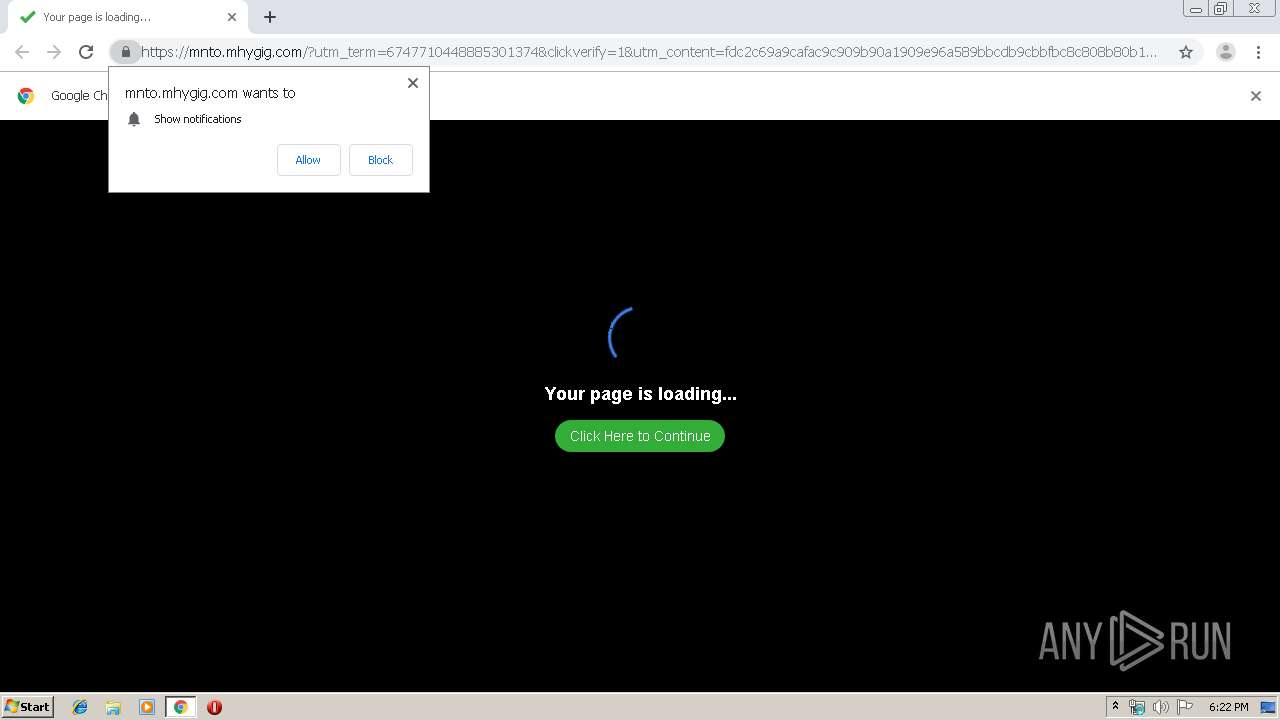
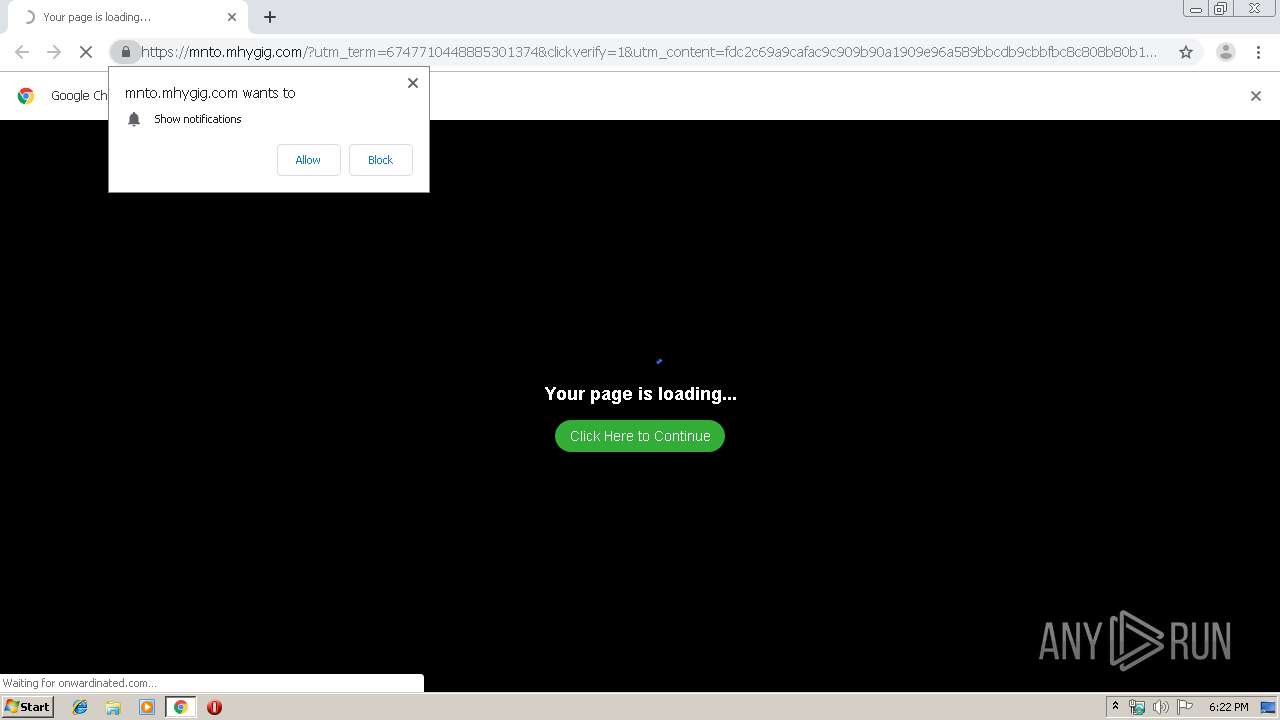
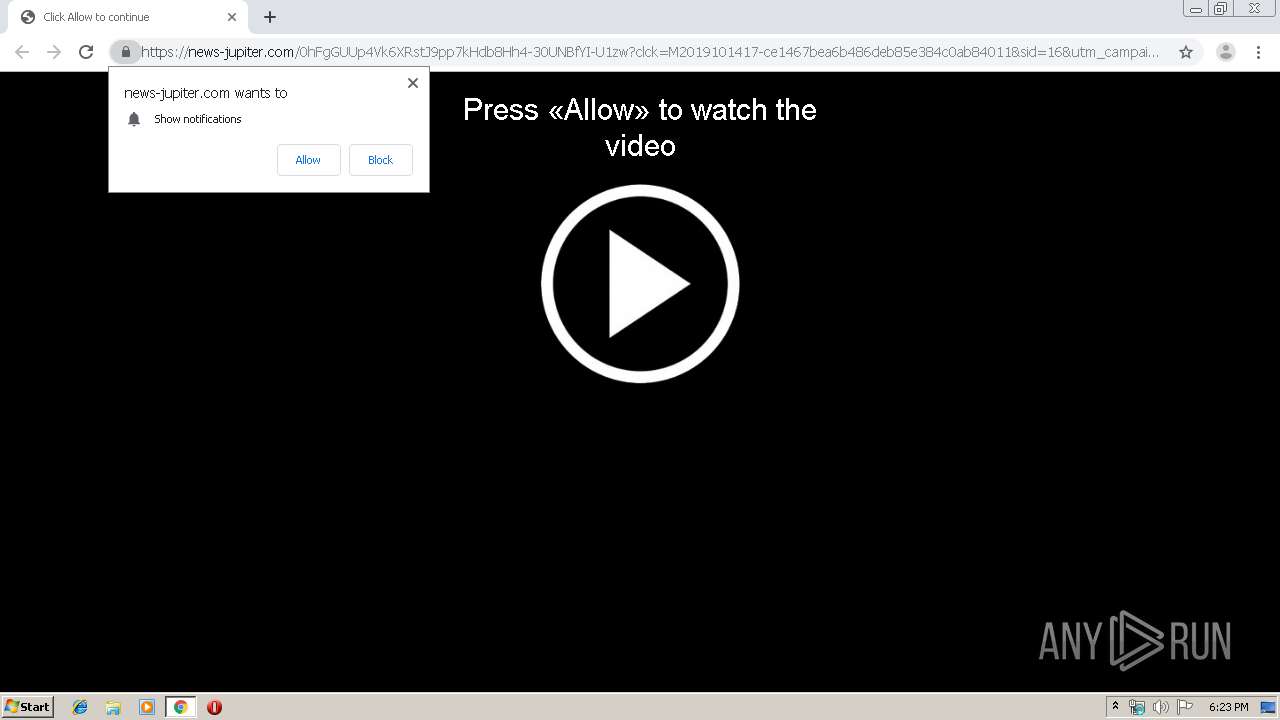
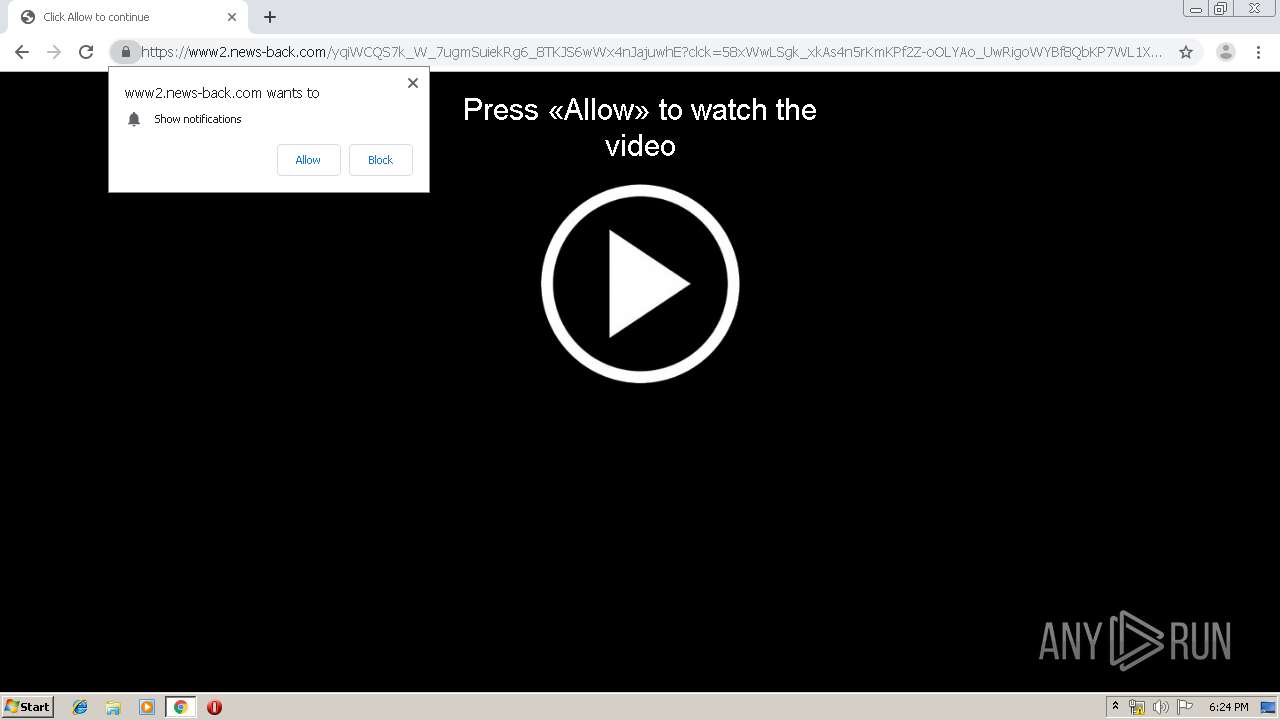
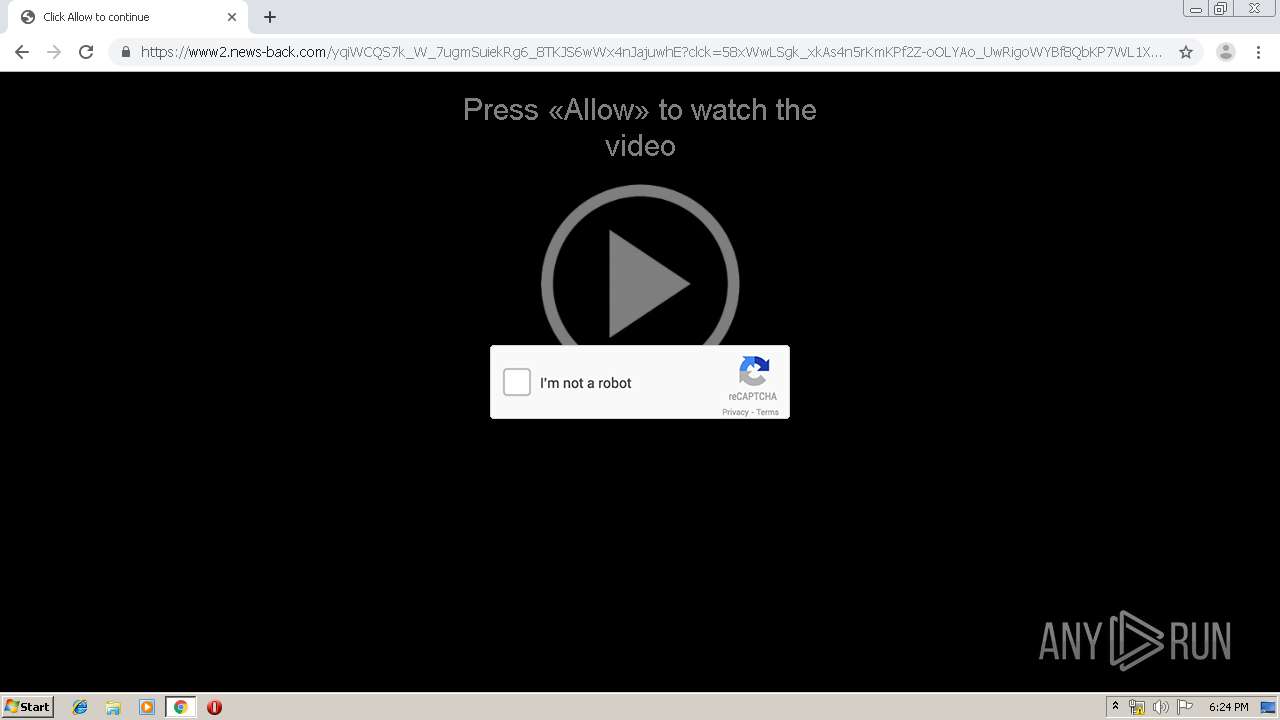
Modifies files in Chrome extension folder
- chrome.exe (PID: 1296)
INFO
Changes settings of System certificates
- chrome.exe (PID: 1504)
Reads the hosts file
- chrome.exe (PID: 1504)
- chrome.exe (PID: 1296)
Application launched itself
- chrome.exe (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
61
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18197810000376370700 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15880064959056813665 --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4335835300193269503 --renderer-client-id=59 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12934474144217333442 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5240653719914184639 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13879534893142192305 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10449635044949503497 --mojo-platform-channel-handle=4596 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4269634091334712298 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9969586613572818575 --renderer-client-id=55 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4656 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,986376271192729891,12520953088493194918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17398781402129097182 --mojo-platform-channel-handle=3756 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
672
Read events
538
Write events
129
Delete events
5
Modification events
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1296-13215547353244500 |
Value: 259 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
160
Text files
267
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7d41a2cb-6a80-45df-9d86-c5f830df880d.tmp | — | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a87f.TMP | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a8dd.TMP | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a87f.TMP | text | |
MD5:— | SHA256:— | |||
| 1296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
129
DNS requests
88
Threats
41
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
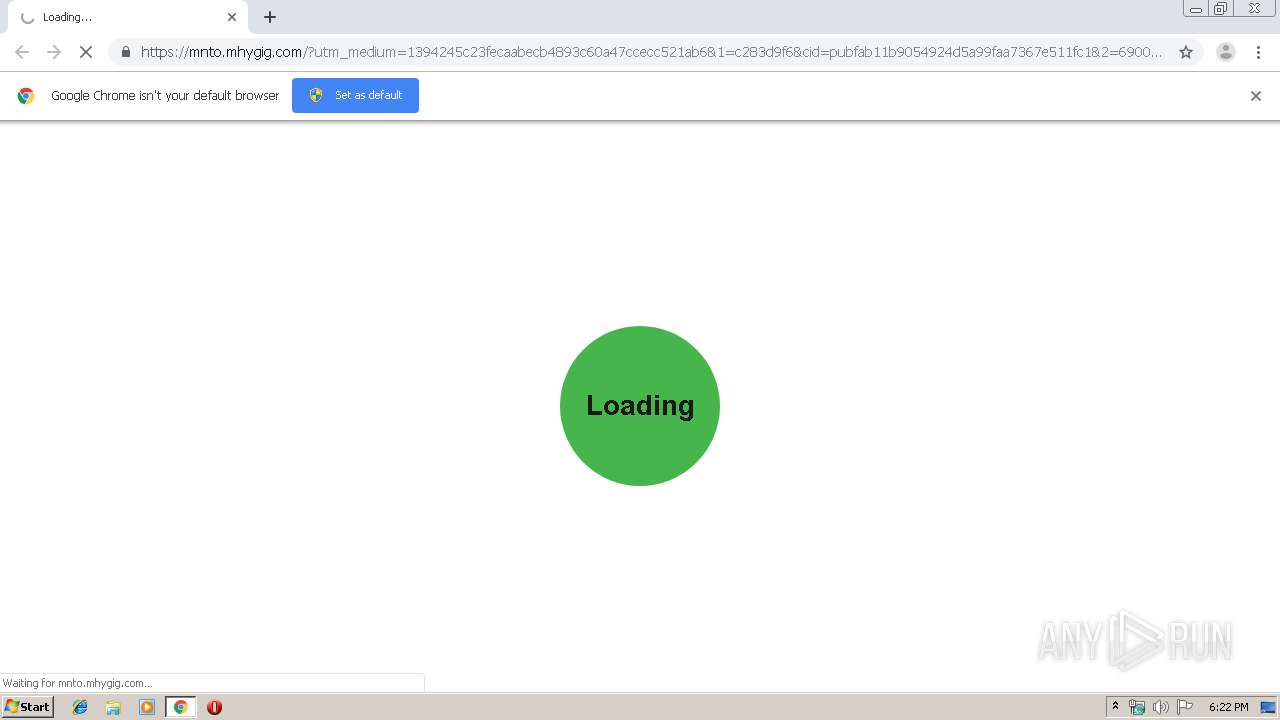
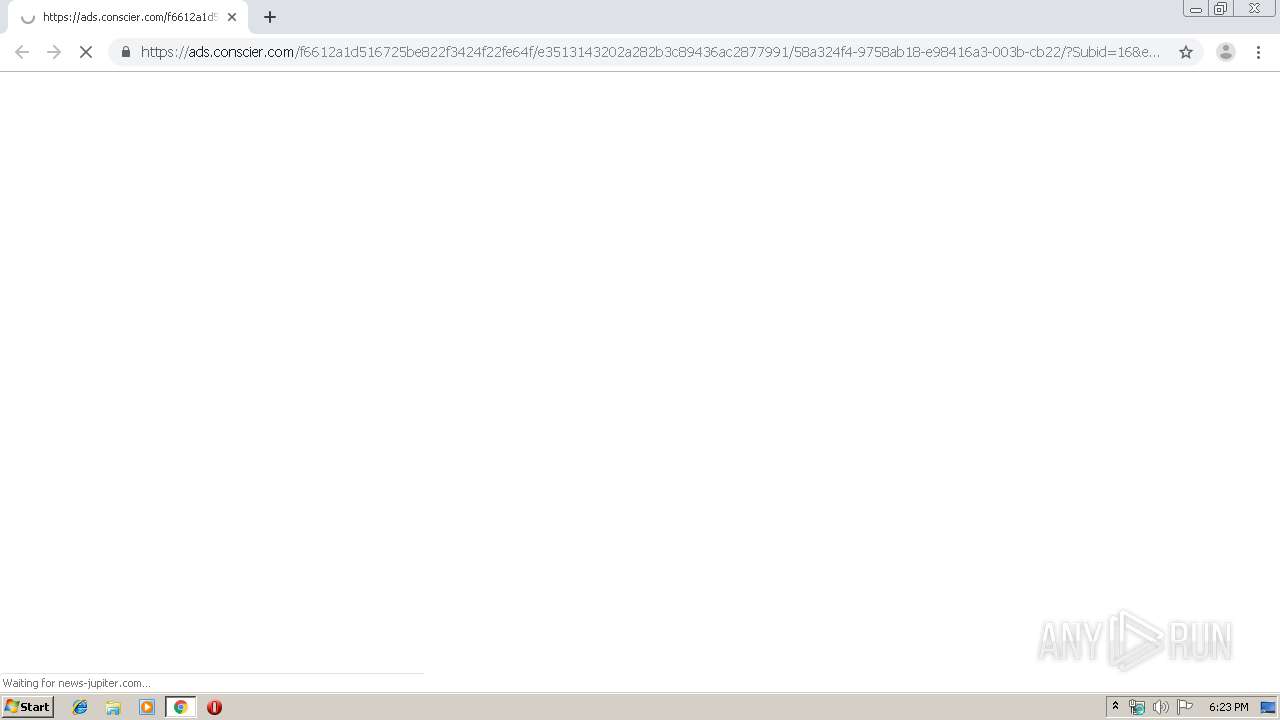
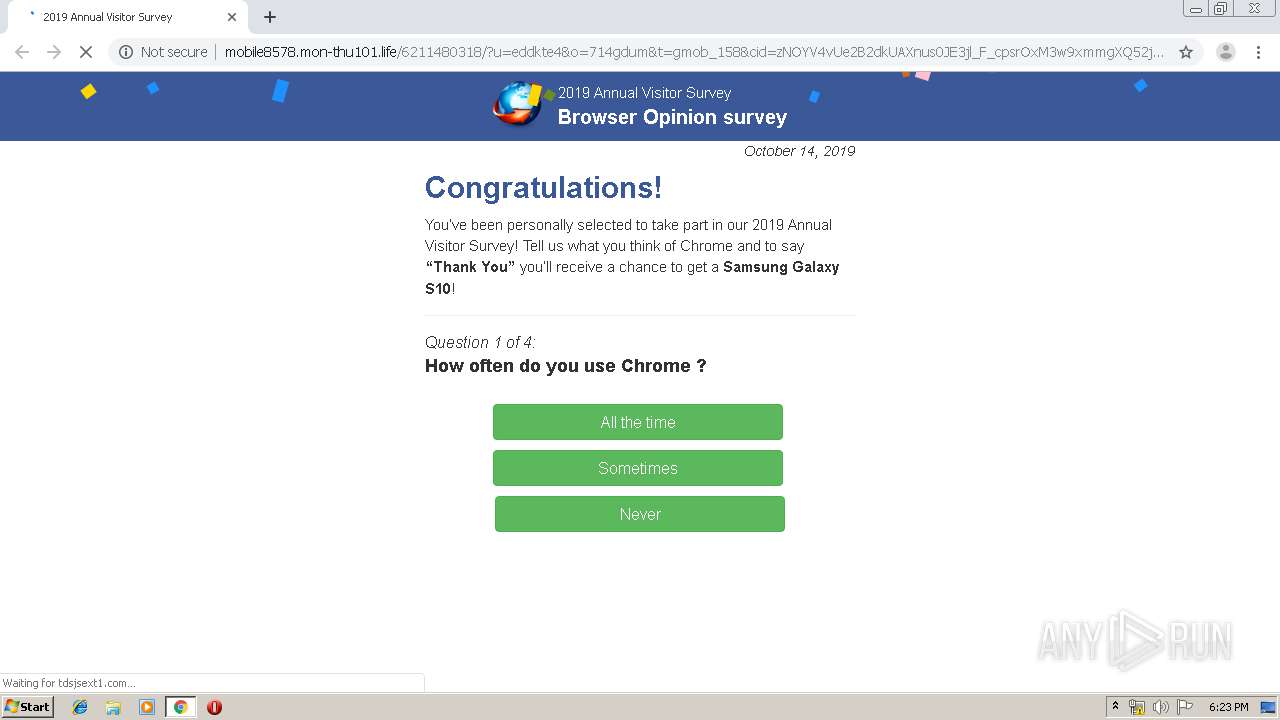
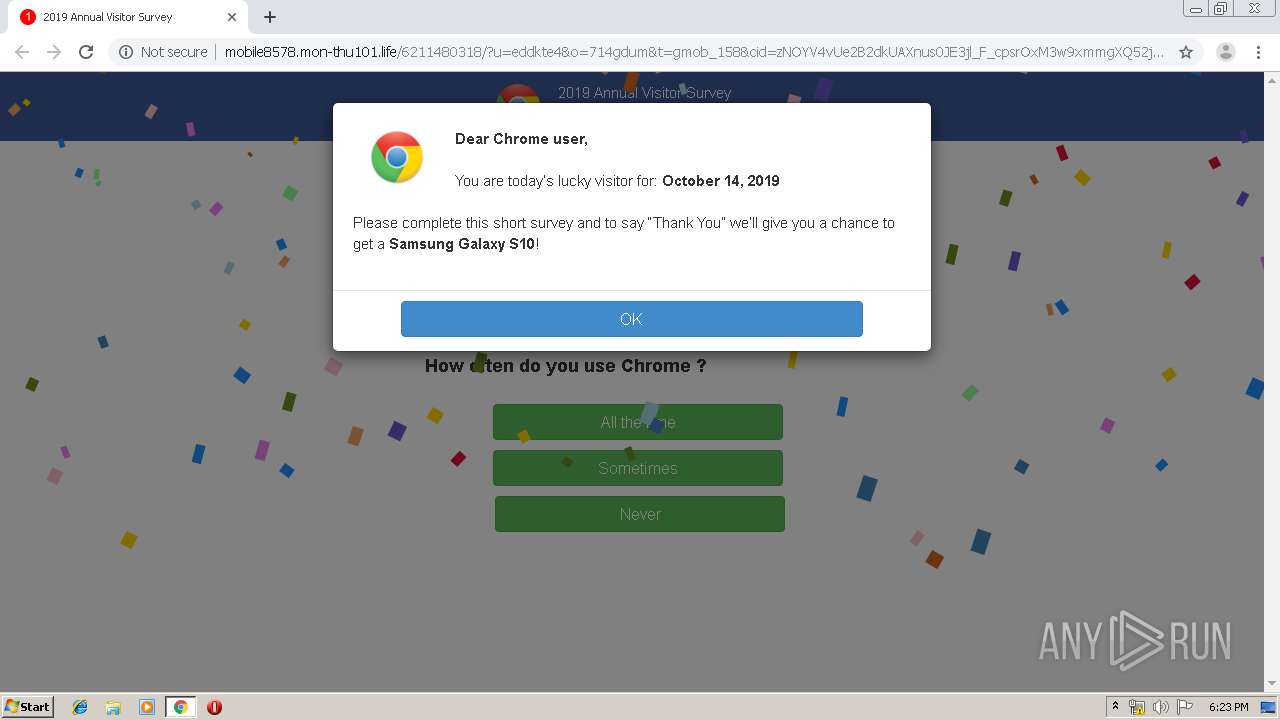
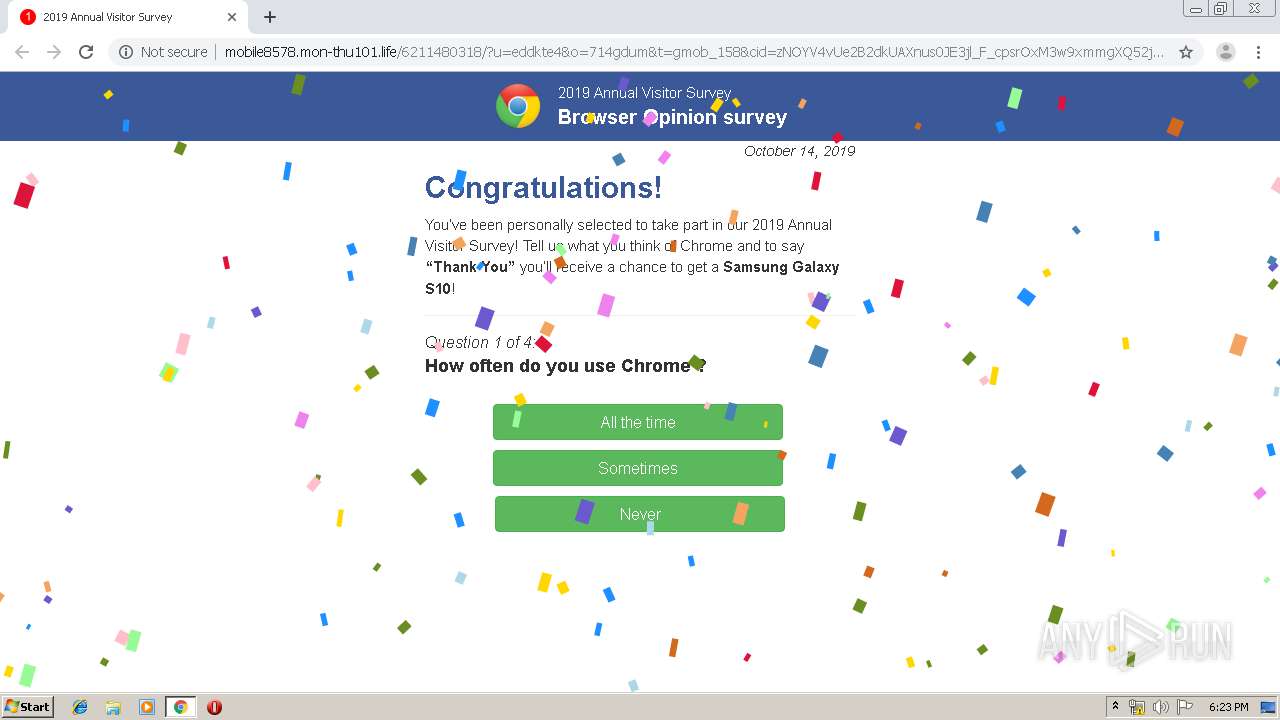
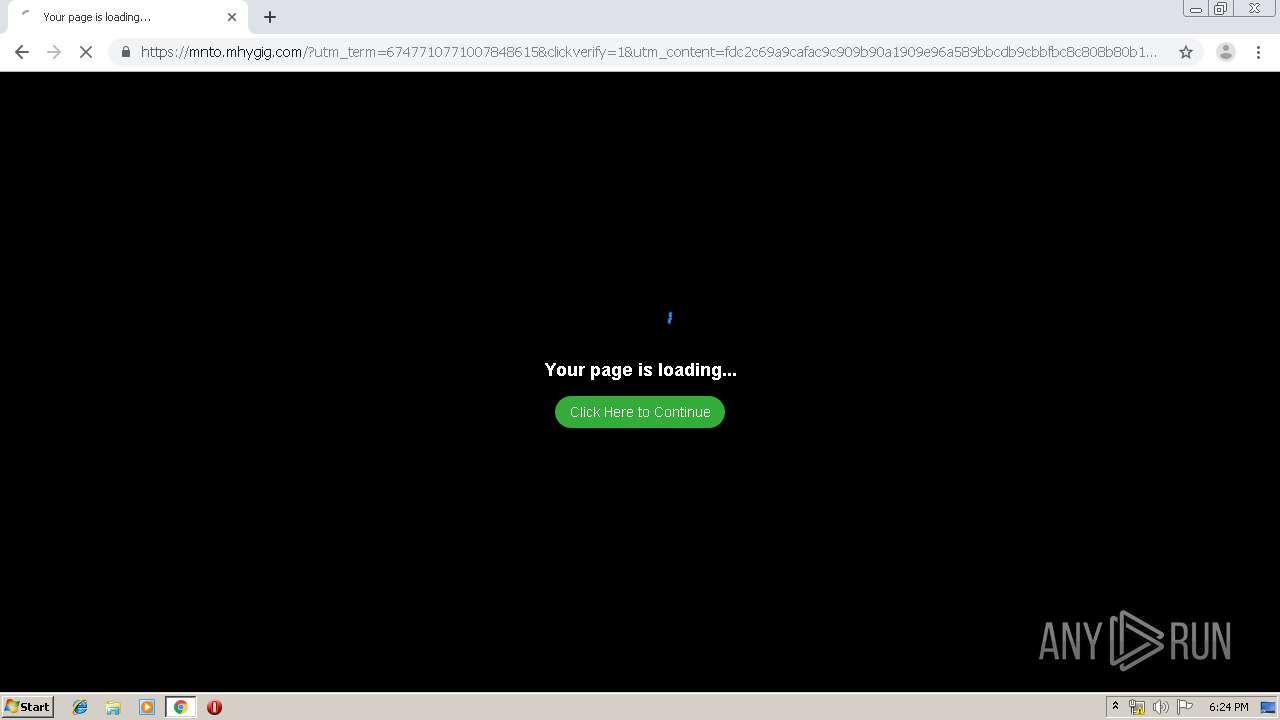
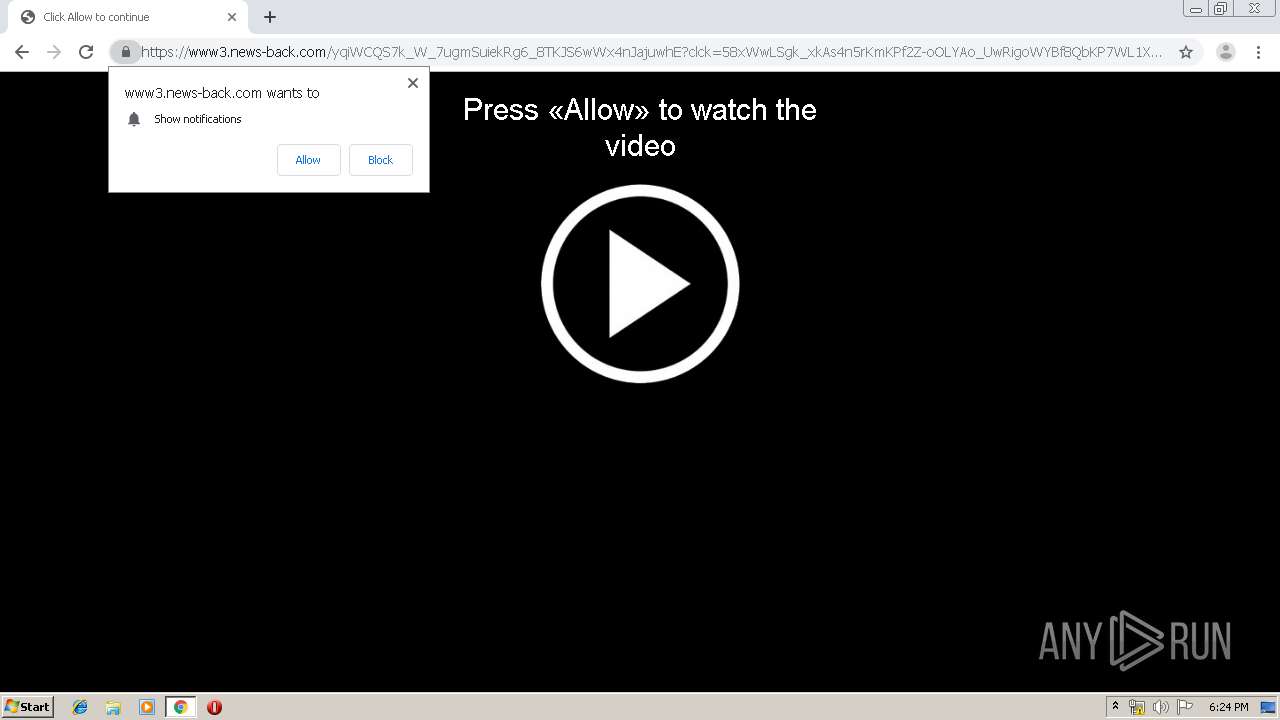
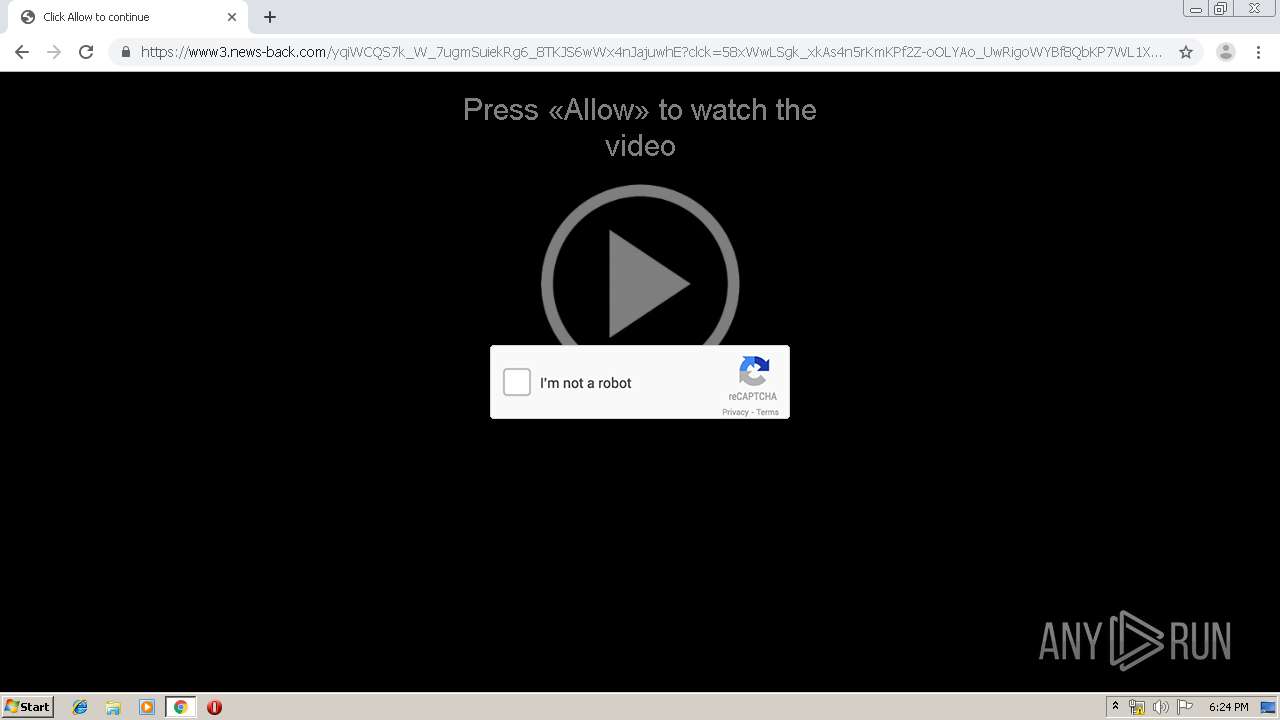
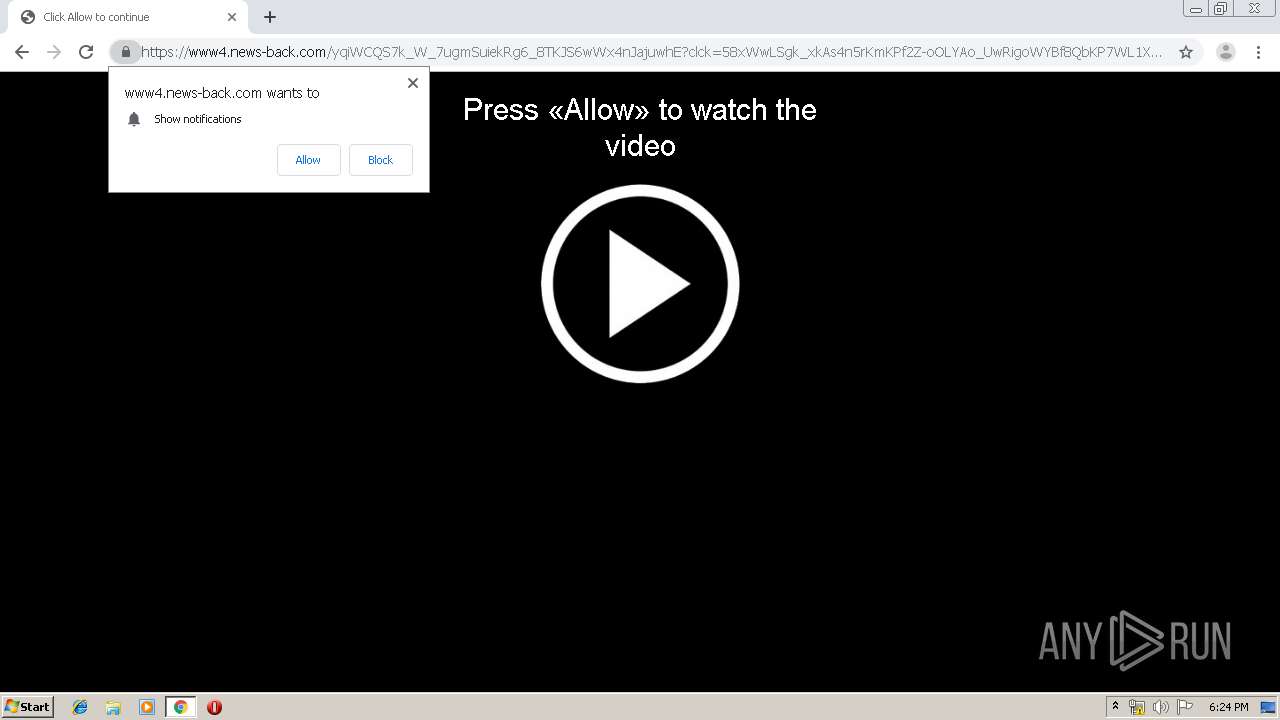
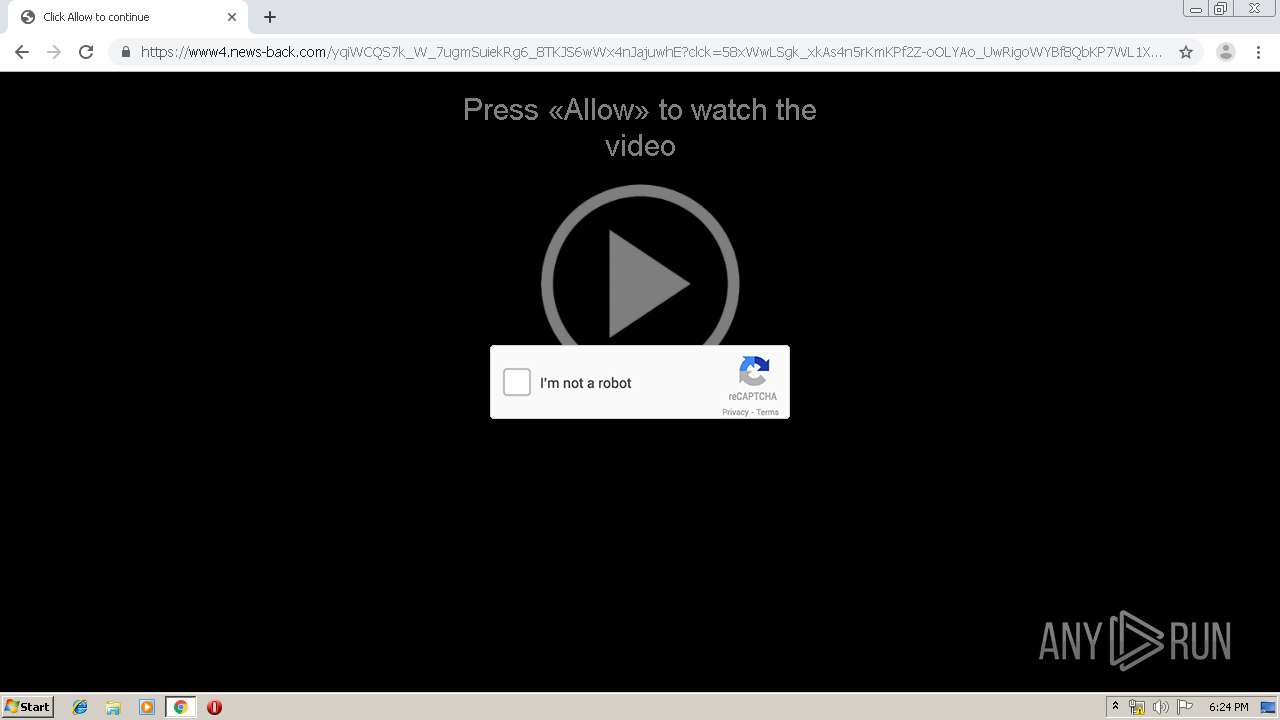
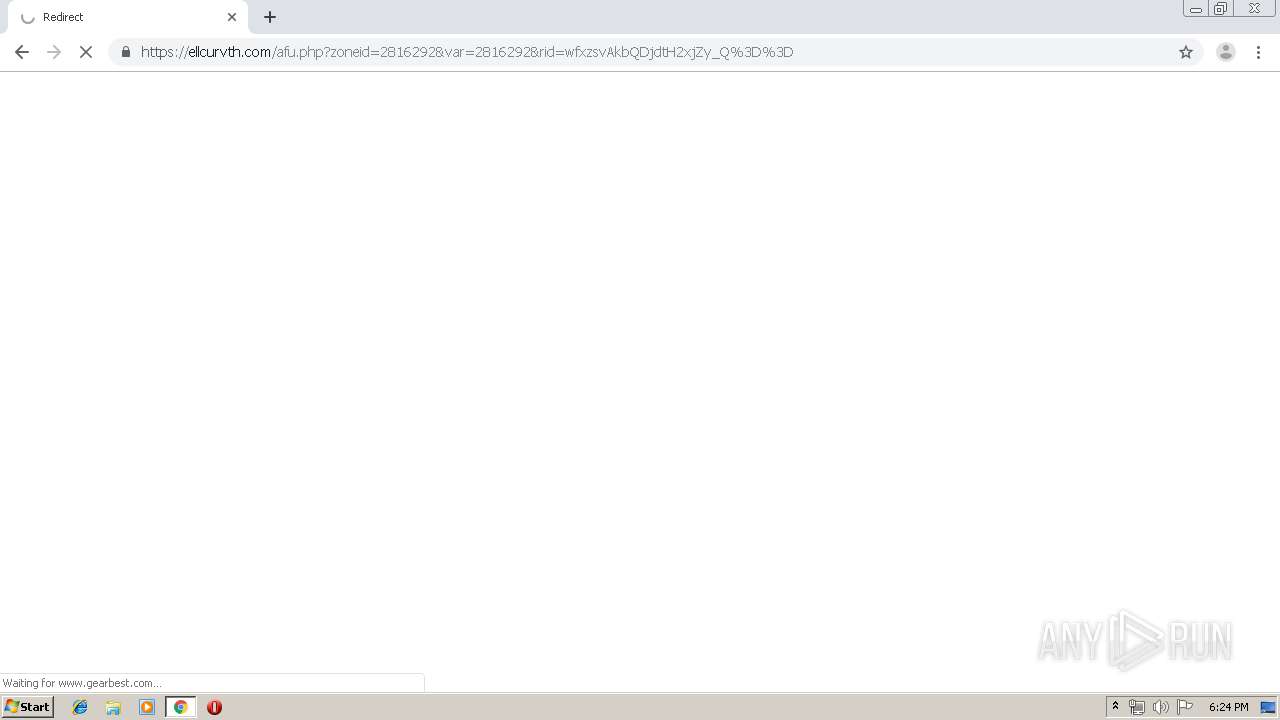
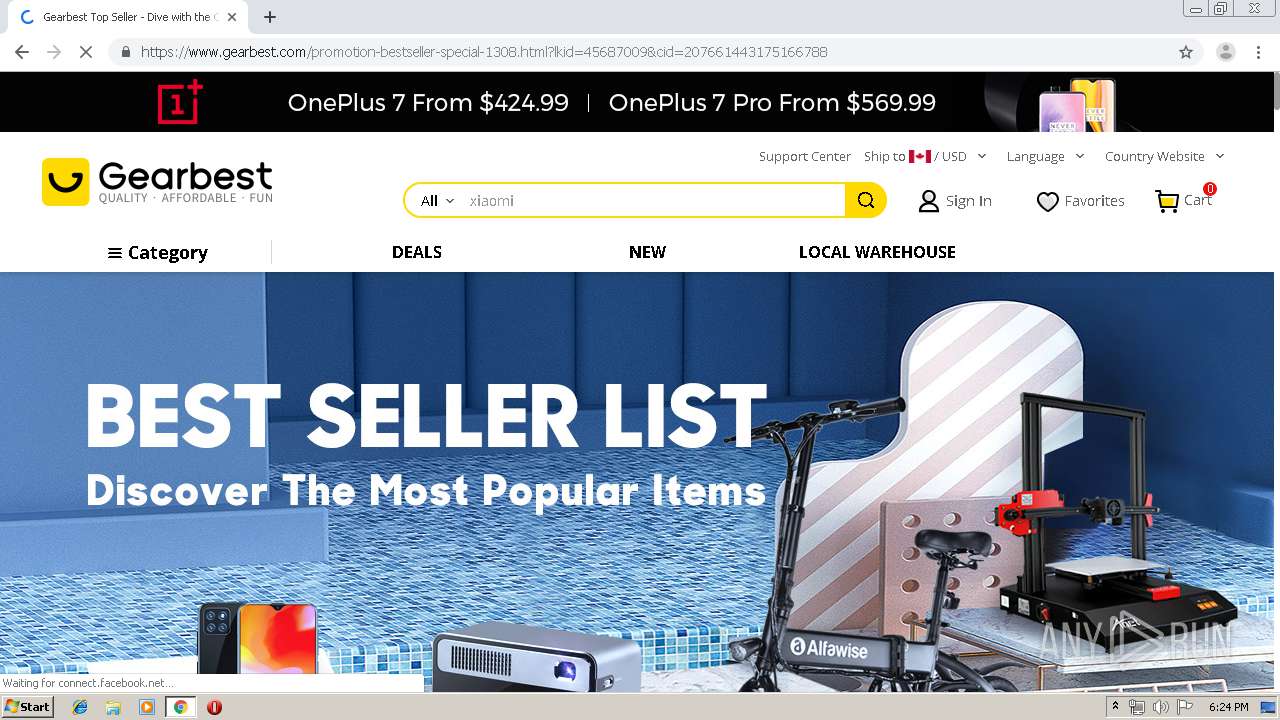
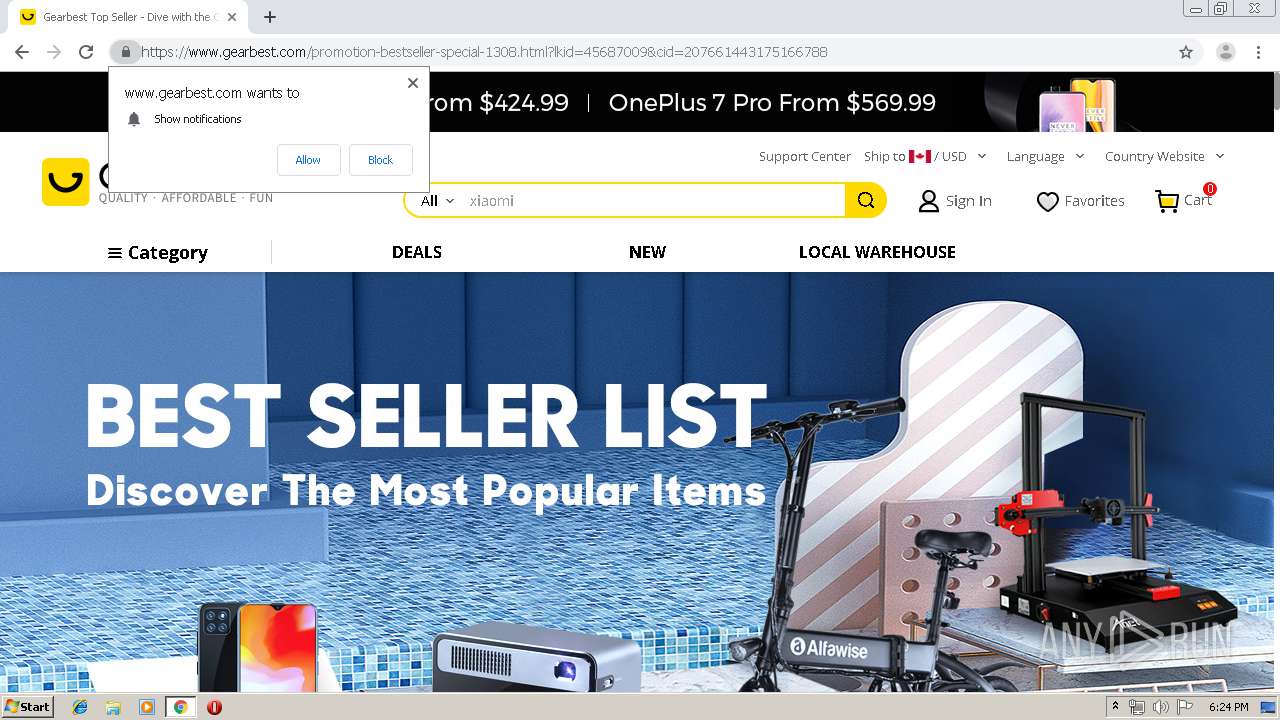
1504 | chrome.exe | GET | 302 | 193.164.4.102:80 | http://homocercy.com/r.php?1430128_576308735_36280_9b6639e45e | unknown | — | — | unknown |
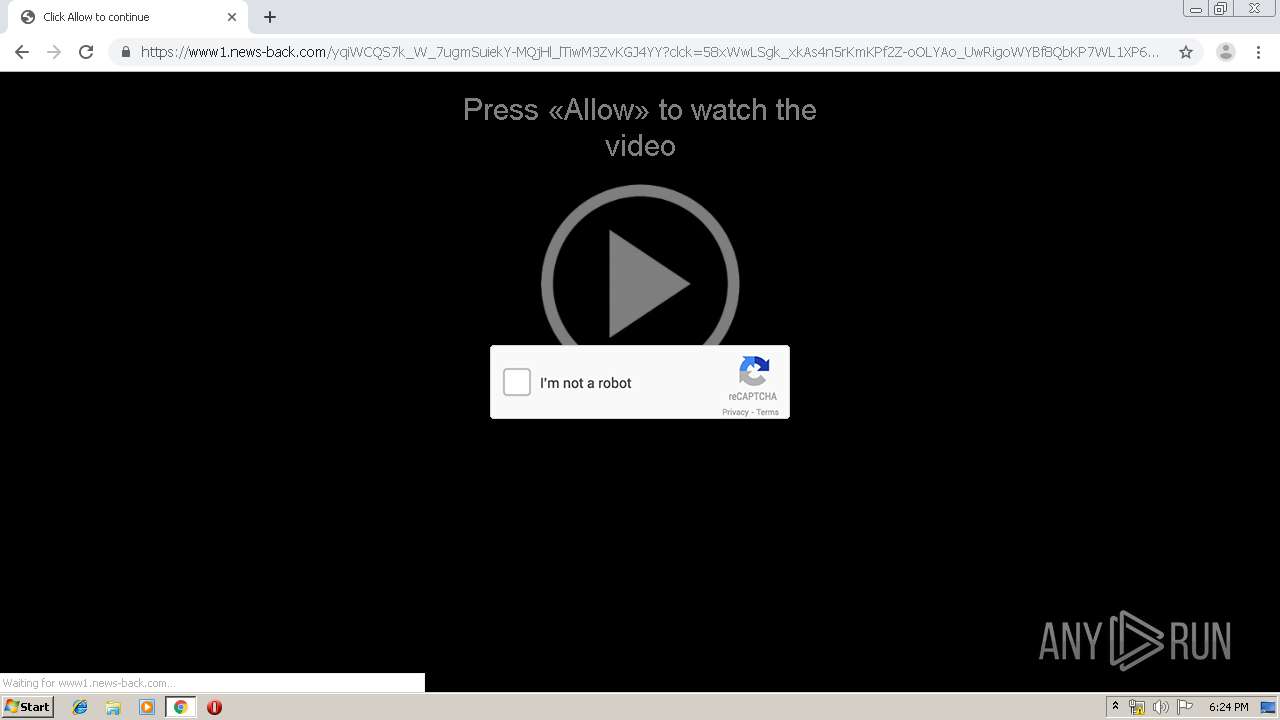
1504 | chrome.exe | GET | 200 | 67.211.37.201:80 | http://pleasantfar.com/1761728ede5abe0c000/131/576308735-36280-9b6639e45e/1430128 | US | html | 135 b | unknown |
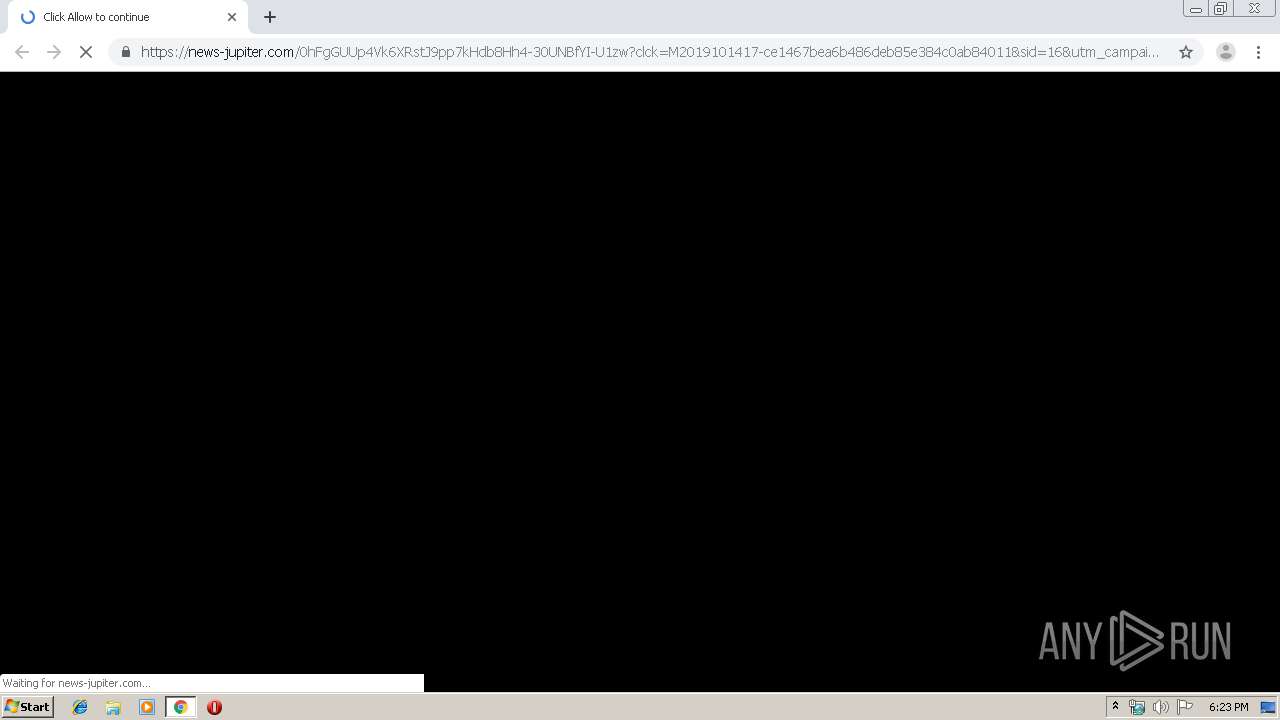
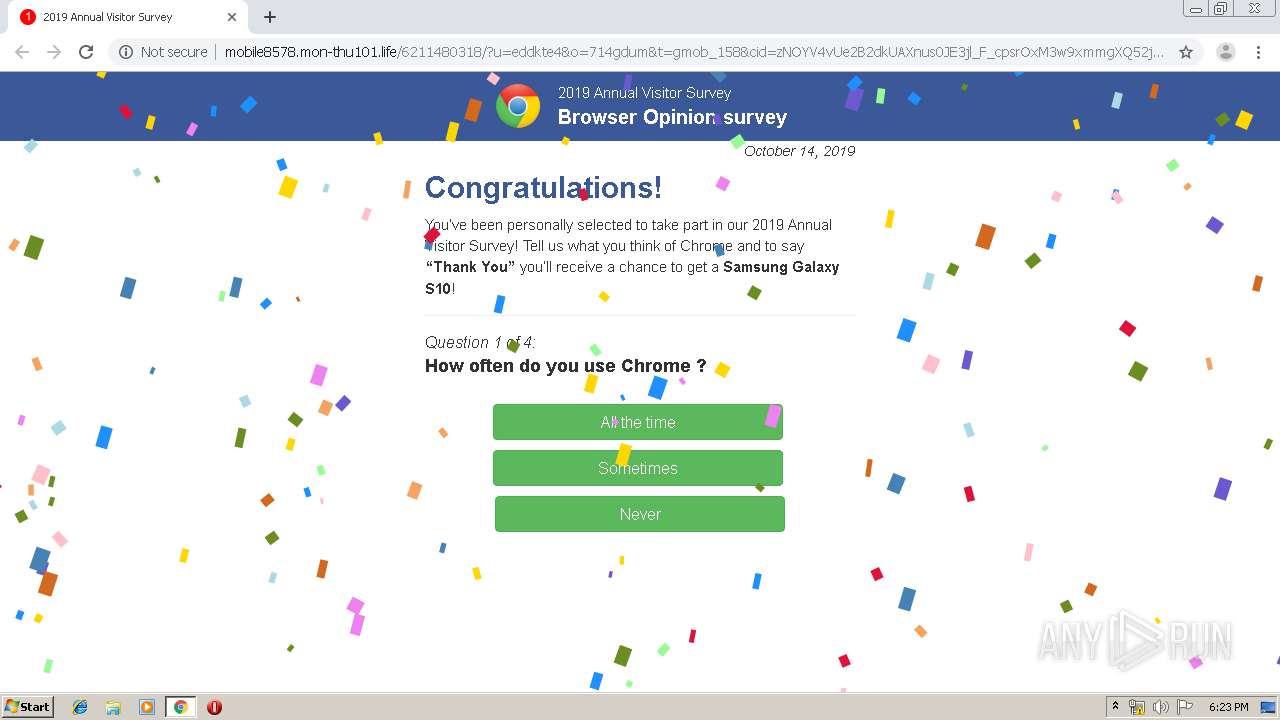
1504 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://mobile8578.mon-thu101.life/media/mainstream/us/wap/mobsurvey/font-awesome.css | UA | text | 17.2 Kb | suspicious |
1504 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://mobile8578.mon-thu101.life/media/mainstream/us/wap/mobsurvey/modernizr-2.6.2-respond-1.1.0.min.js | UA | html | 17.8 Kb | suspicious |
1504 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://mobile8578.mon-thu101.life/media/mainstream/us/wap/mobsurvey/main.css | UA | text | 7.03 Kb | suspicious |
1504 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://mobile8578.mon-thu101.life/media/mainstream/us/wap/mobsurvey/logo1.js | UA | text | 12.7 Kb | suspicious |
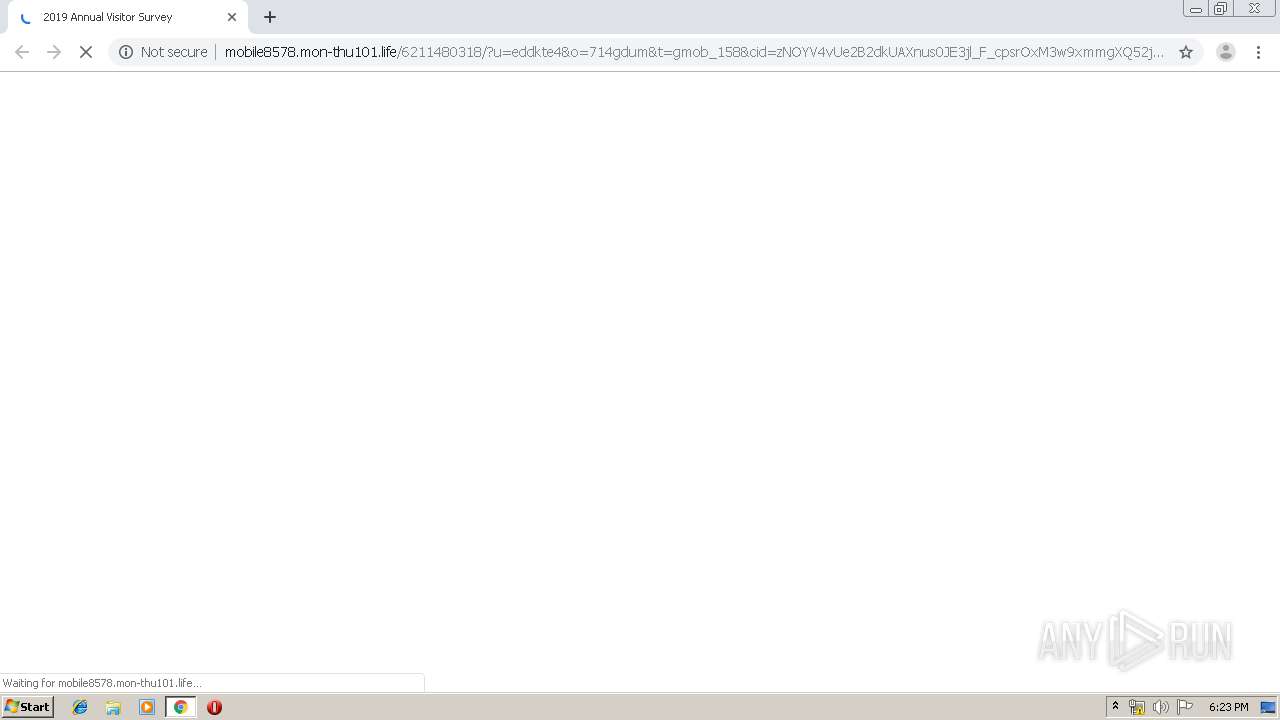
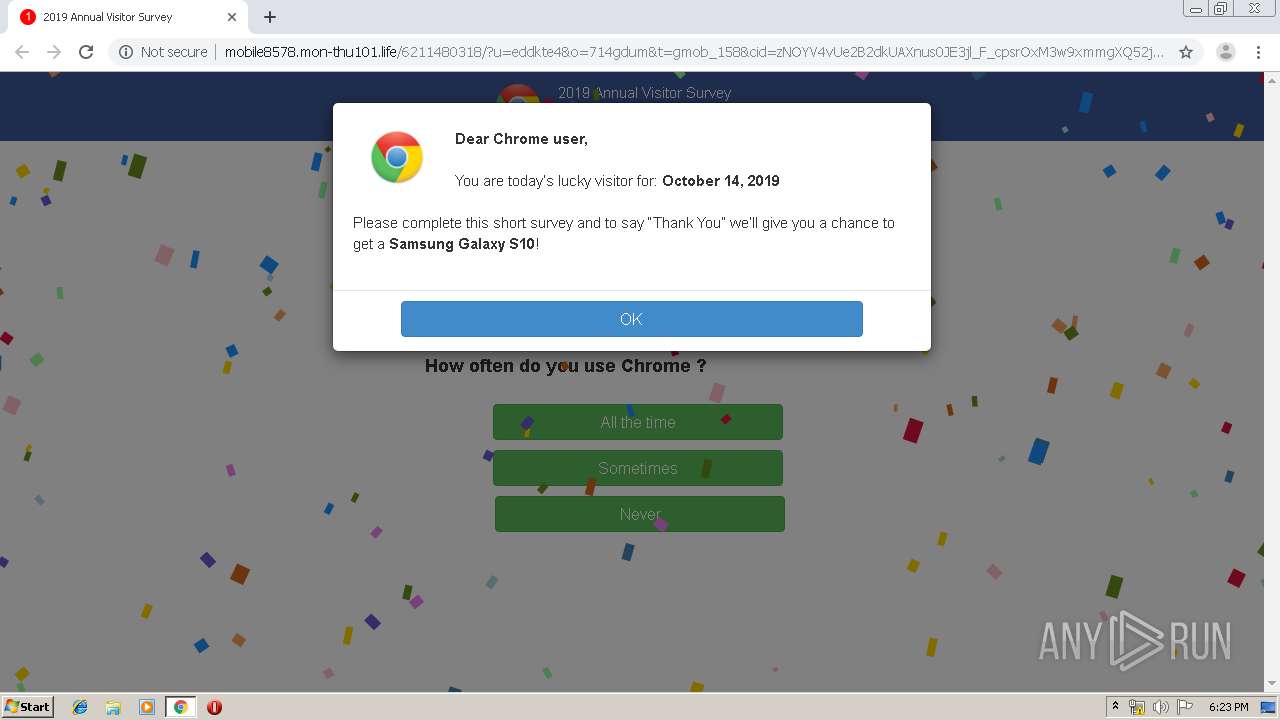
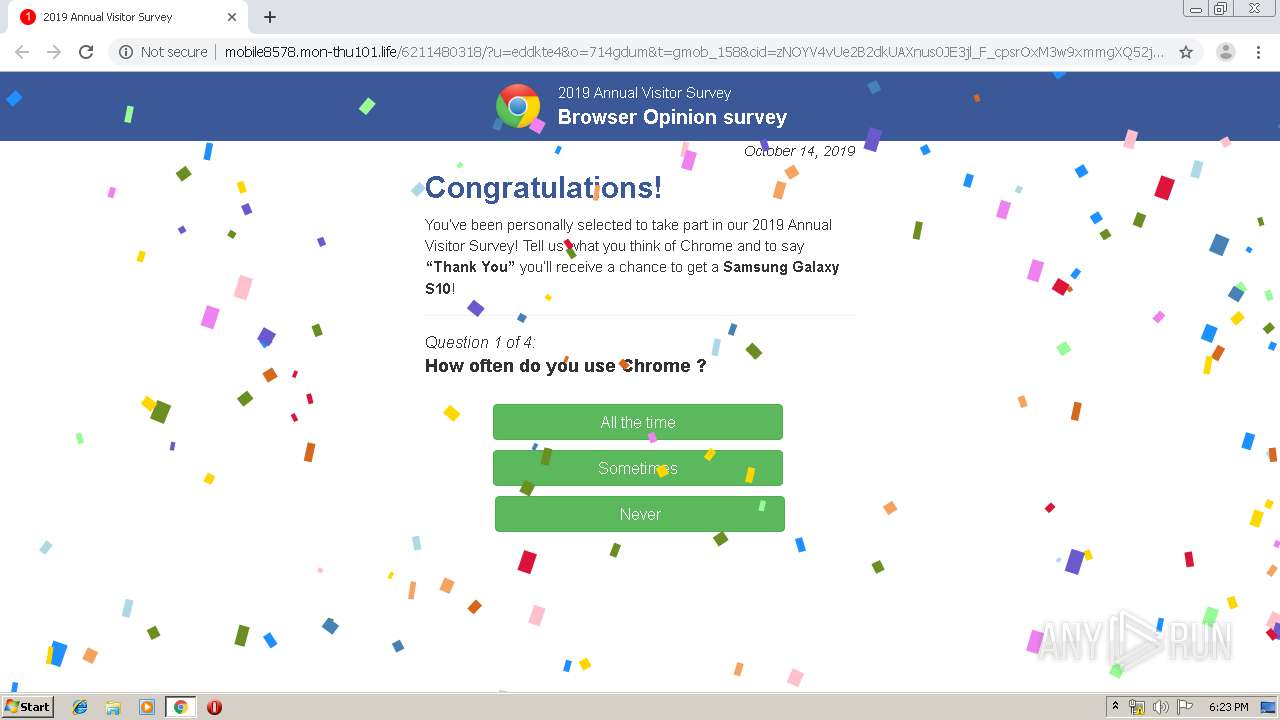
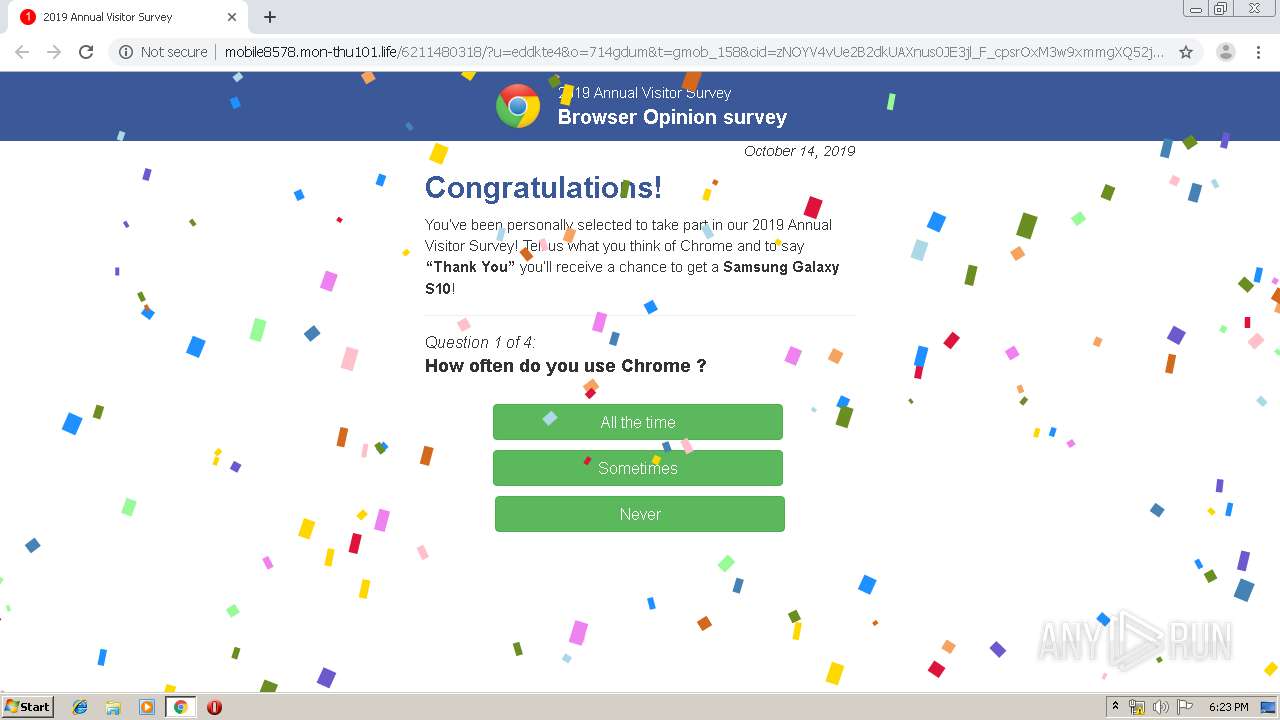
1504 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://mobile8578.mon-thu101.life/6211480318/?u=eddkte4&o=714gdum&t=gmob_158&cid=zNOYV4vUe2B2dkUAXnus0JE3jl_F_cpsrOxM3w9xmmgXQ52jGz3fKk0geCeQaWbt2ej43YFKoIUzlVoumG-v9e-puj7W30J9oS1iBNeqhgbnx4wL8vU4TnC9ciXb5B9x4pPtz5m12eCy4r46mplQIZmSNLnbEcwpZR6mBR12DnwtLaBkv75kkOfdDZa4tV24Qo-BiB-1TVC6oRXNIJ6Bb1jArkX8jIzCRrGxHmx_Hk7X0KwApYjKZYxDmSAbMjXbbinYyl-QSkHqBptLw5vpMDwgszZIxAQ1bAEcLCLDc3zFNMdxfeTP8k7eACY-4E4JhdQT-nA-vYbb5gGZyoiVe9lVEC4zspXx5ef5hHYCZj0yd-ghb-9UYXmJt-mqr5816mp0c-oA3LY-uj1LMT9xvPq0PKwSfF9VyKRNrHb-AbgTONWnLDFjDSW6a0zzRn8M&f=1 | UA | html | 17.1 Kb | suspicious |
1504 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://mobile8578.mon-thu101.life/media/mainstream/us/wap/mobsurvey/en-en.js | UA | text | 5.95 Kb | suspicious |
1504 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://mobile8578.mon-thu101.life/util/utils-ms.js | UA | text | 17.2 Kb | suspicious |
1504 | chrome.exe | GET | 200 | 185.89.102.137:80 | http://mobile8578.mon-thu101.life/media/mainstream/us/wap/mobsurvey/logo2.js | UA | text | 12.8 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1504 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 193.164.4.102:80 | homocercy.com | — | — | unknown |
1504 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 67.211.37.201:80 | pleasantfar.com | EBL Global Networks, Inc. | US | unknown |
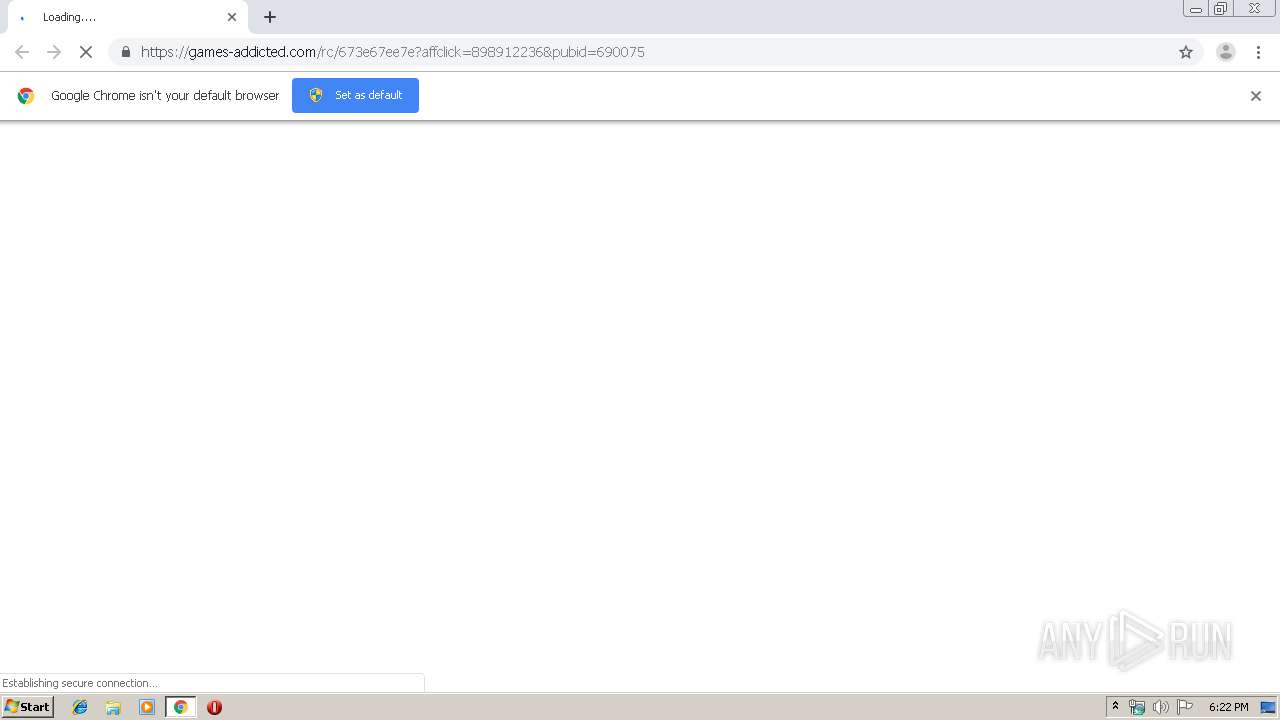
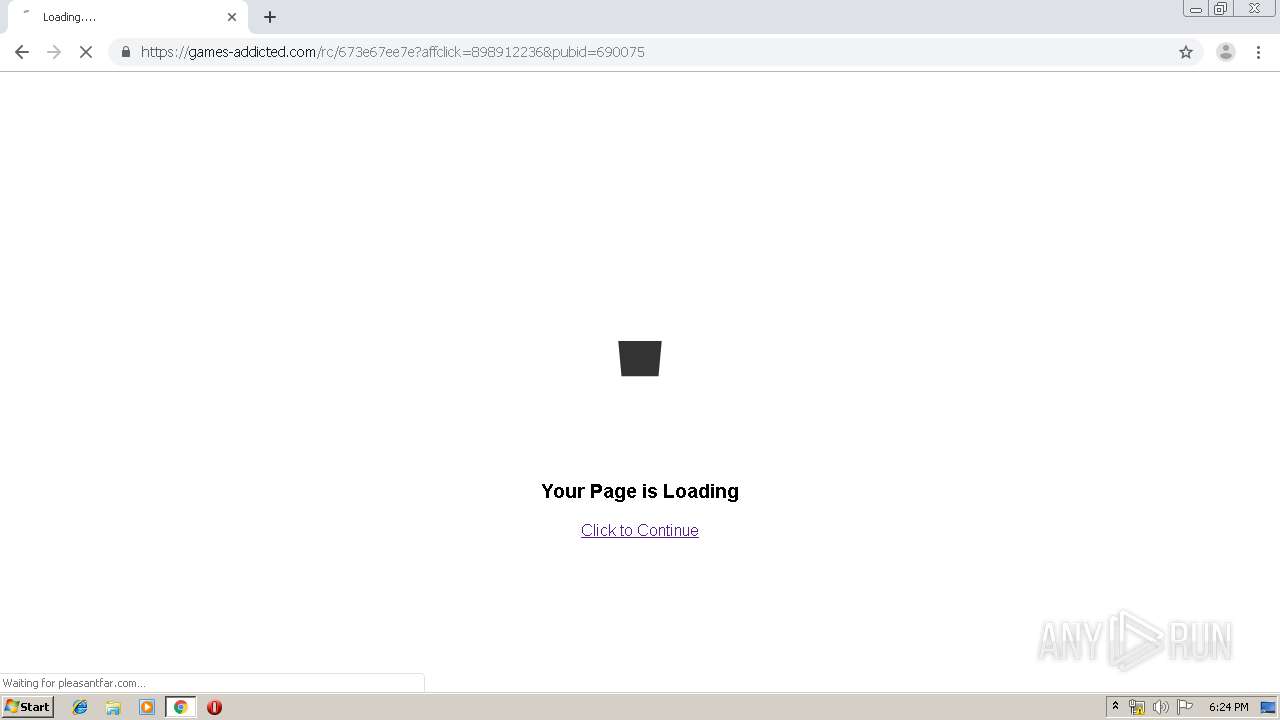
1504 | chrome.exe | 104.28.18.41:443 | games-addicted.com | Cloudflare Inc | US | suspicious |
1504 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 172.64.168.8:443 | cdn.addlnk.com | Cloudflare Inc | US | shared |
1504 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
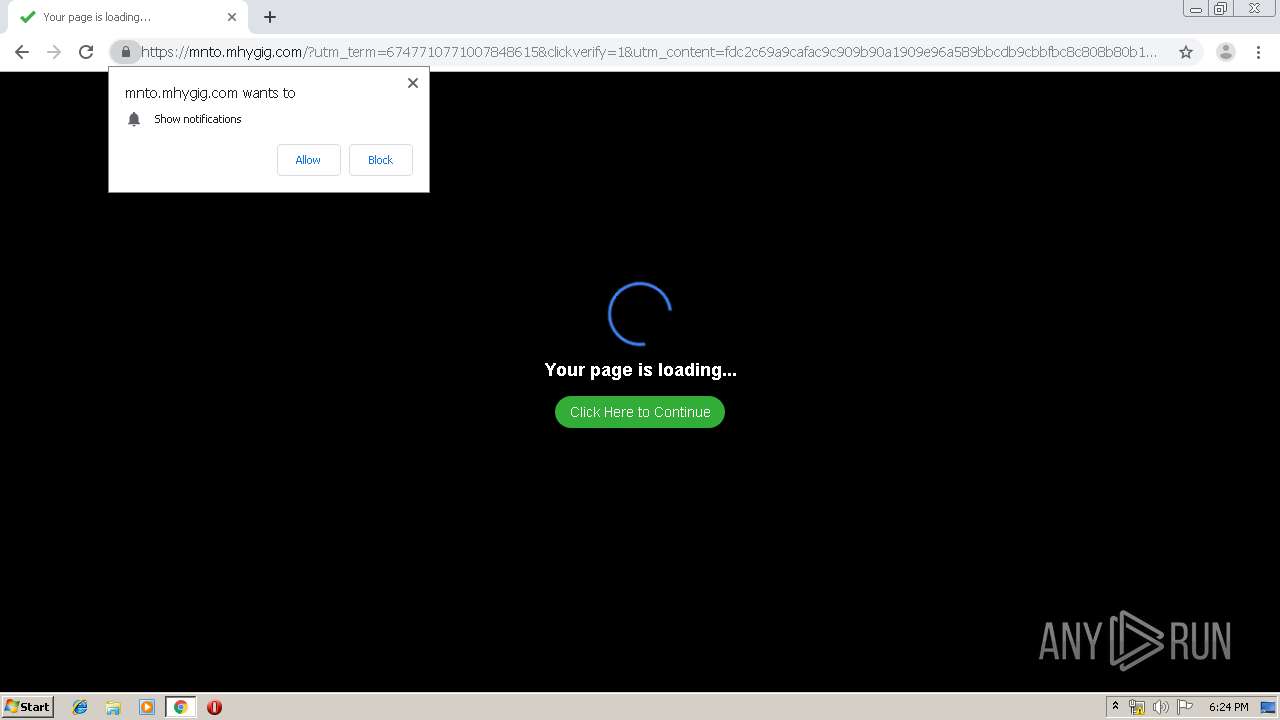
1504 | chrome.exe | 198.143.165.222:443 | mnto.mhygig.com | SingleHop, Inc. | US | suspicious |
1504 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
homocercy.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
pleasantfar.com |
| unknown |
games-addicted.com |
| whitelisted |
cdn.addlnk.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
mnto.mhygig.com |
| suspicious |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1504 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1 ETPRO signatures available at the full report