| File name: | Setup.EXE |
| Full analysis: | https://app.any.run/tasks/50532e5b-dd57-4136-b6db-96ab132f7377 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2024, 11:19:56 |
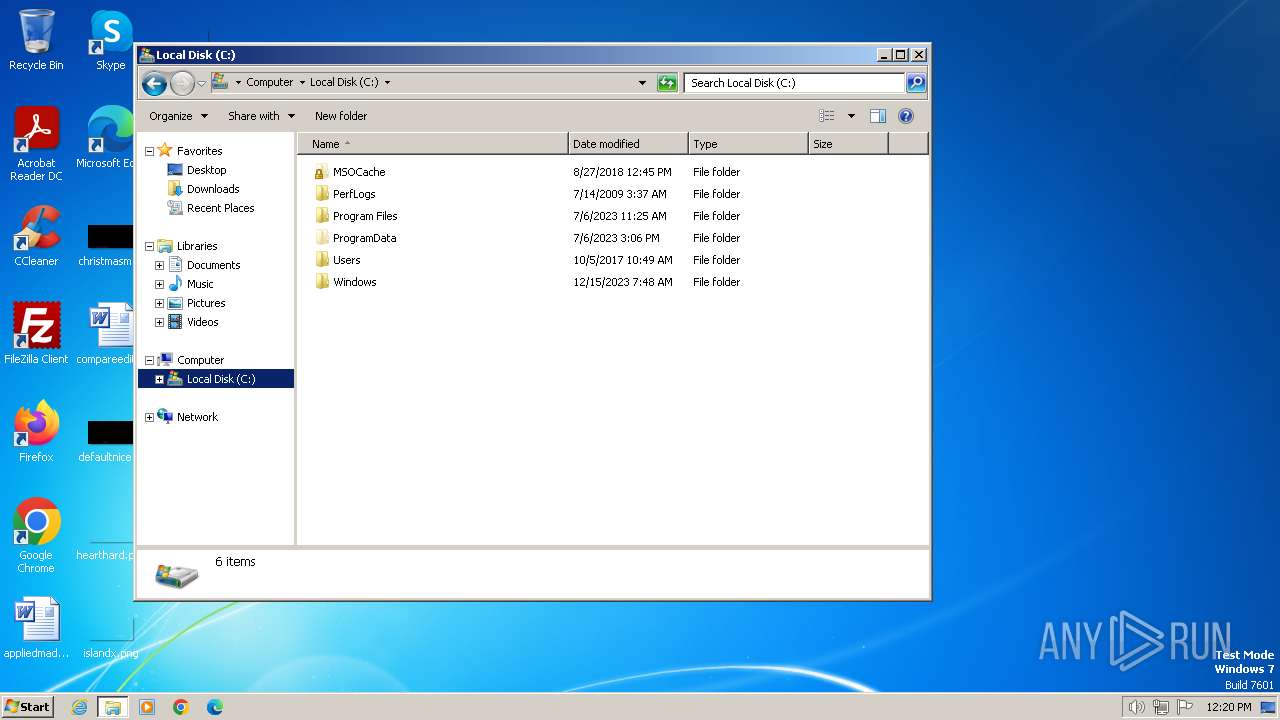
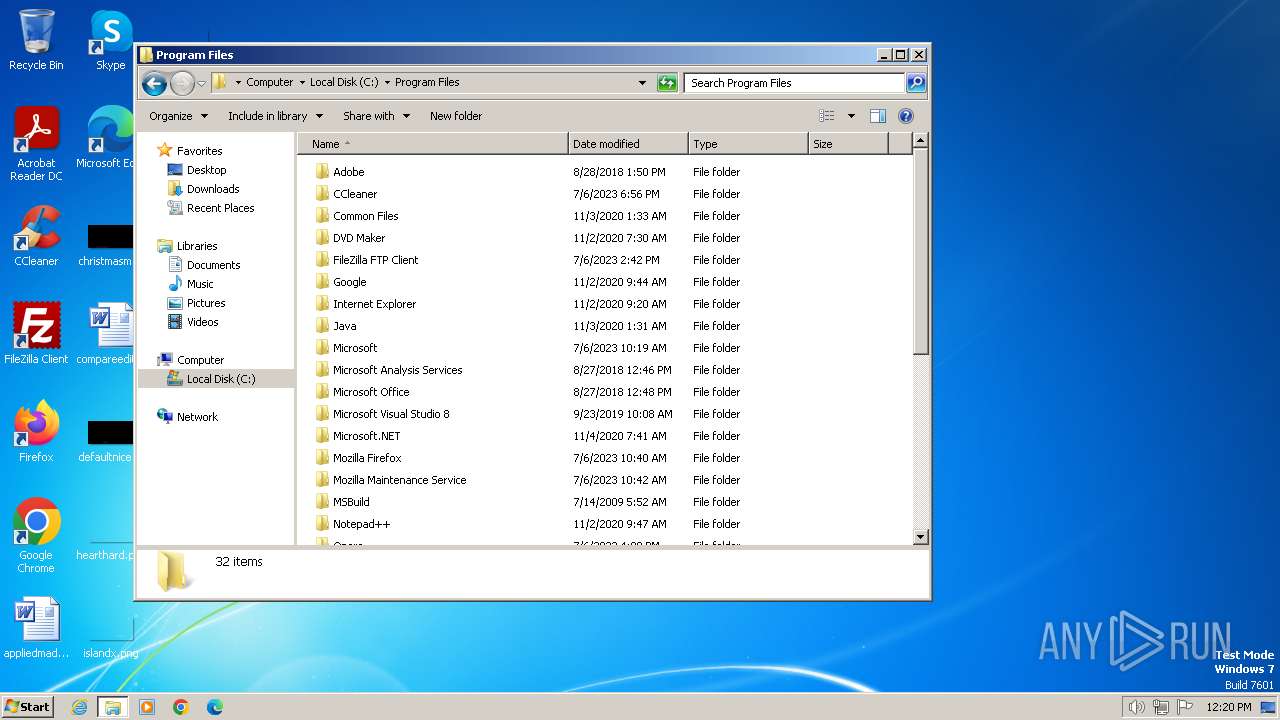
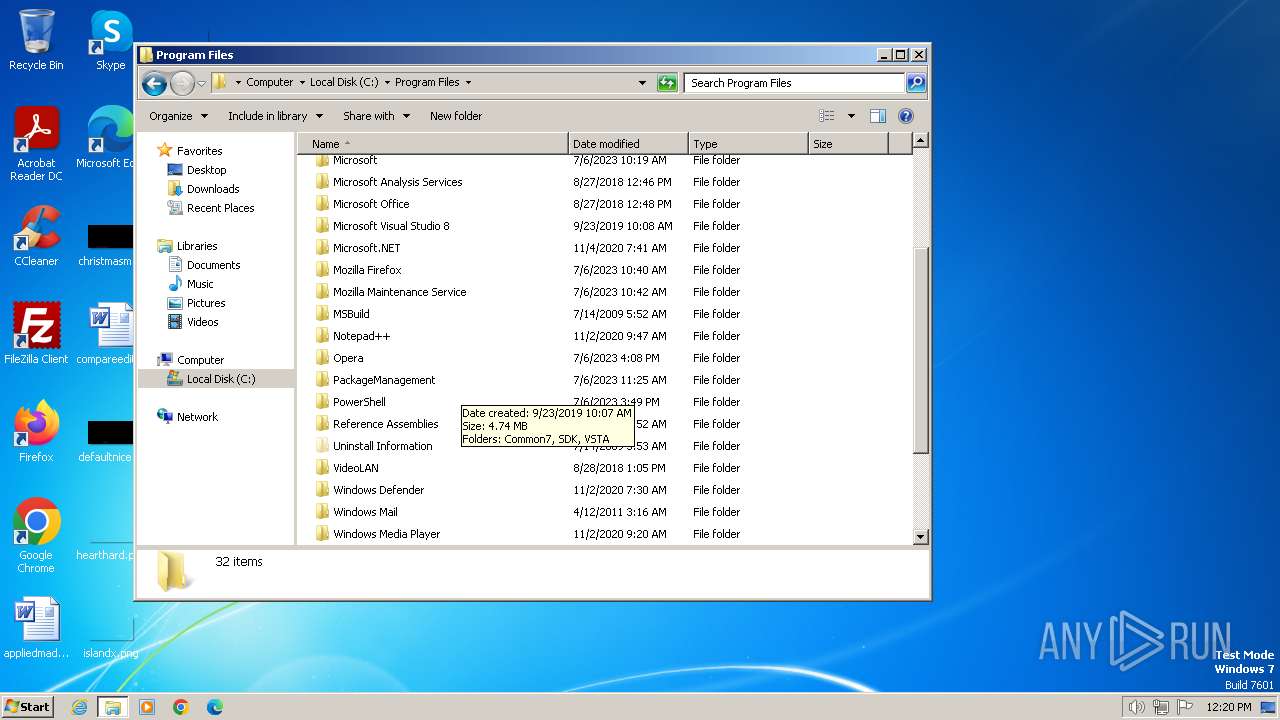
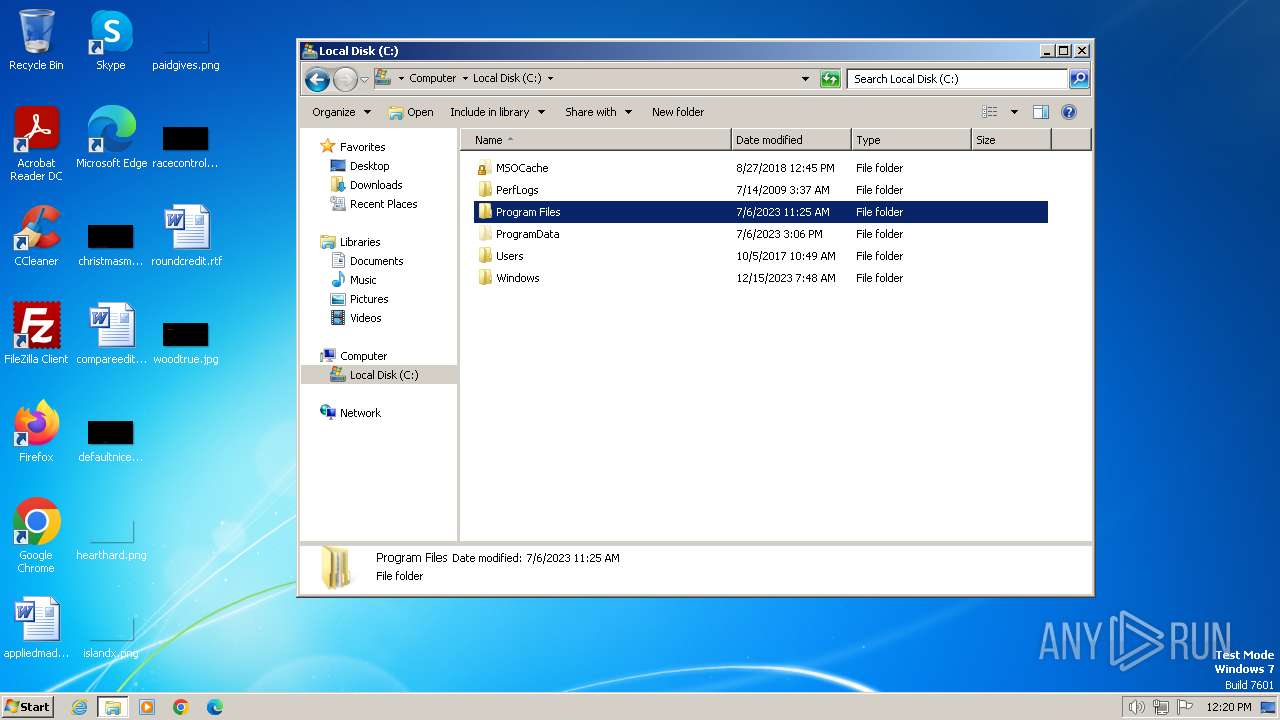
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | D97EBC348587A3364118AA439A1B2A71 |
| SHA1: | 01C0E0FBD61ED828671ABC914F23C0093D38EA2C |
| SHA256: | 89069B132520D5FC69EAC45C1F8B4A774EDC63A997C2788AF8CE9BAB8E5D5226 |
| SSDEEP: | 98304:rn2+14orN/9lKnaouTL0CR20KQIaexccfwgRfjkm9EGEf2ZcxtE97MkaaCBkgSQI:cwfU |
MALICIOUS
Drops the executable file immediately after the start
- Setup.EXE.exe (PID: 1696)
SUSPICIOUS
Process drops legitimate windows executable
- Setup.EXE.exe (PID: 1696)
Starts CMD.EXE for commands execution
- Setup.EXE.exe (PID: 1696)
- cmd.exe (PID: 2860)
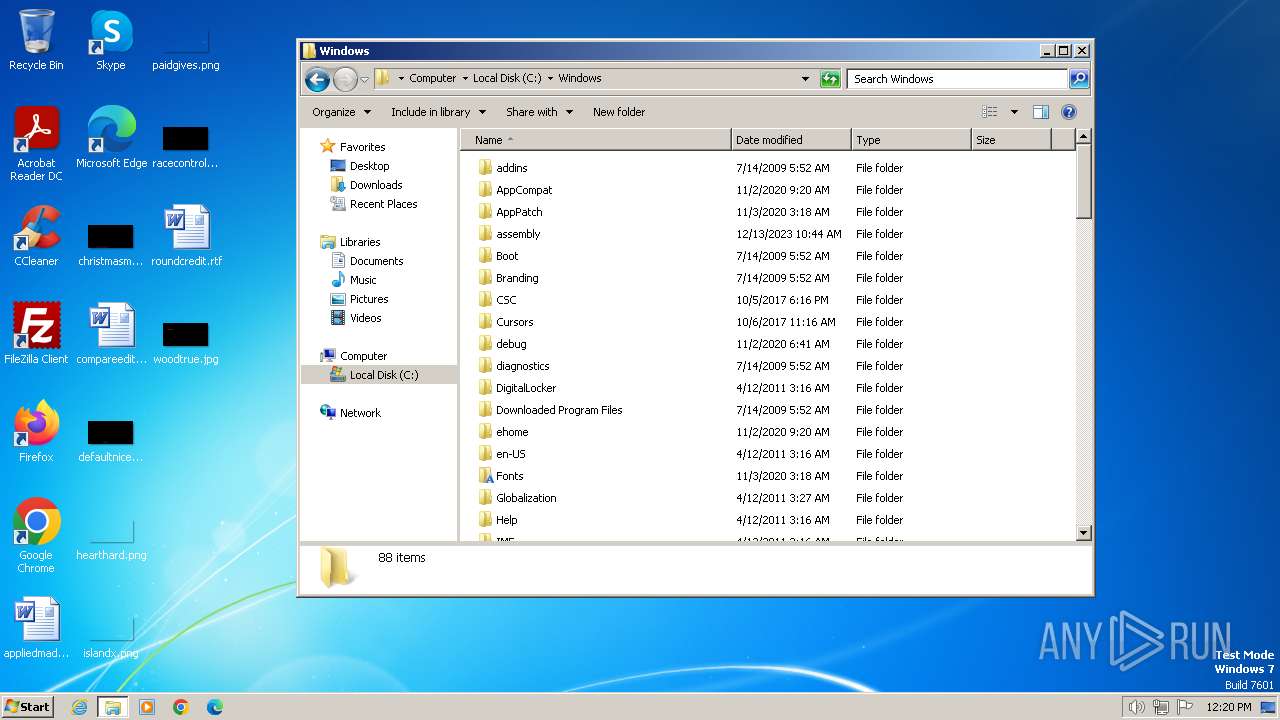
Starts a Microsoft application from unusual location
- Setup.EXE.exe (PID: 1696)
Application launched itself
- cmd.exe (PID: 2860)
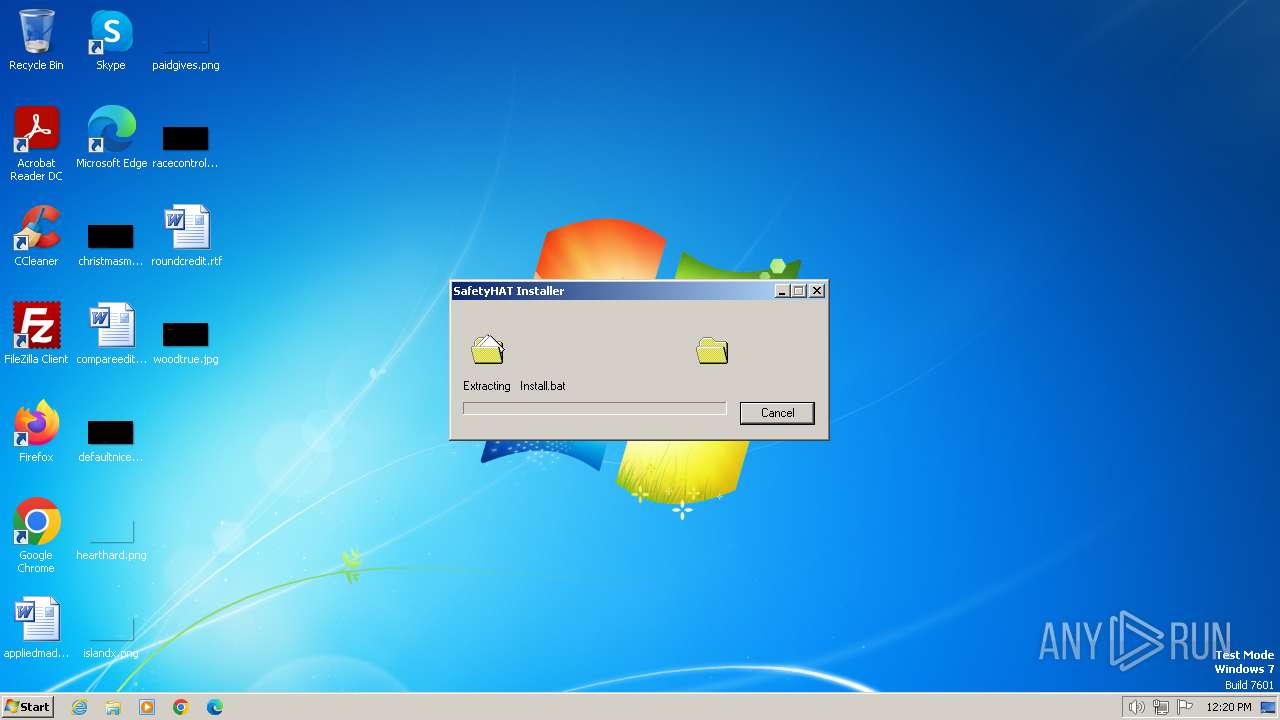
Executing commands from a ".bat" file
- Setup.EXE.exe (PID: 1696)
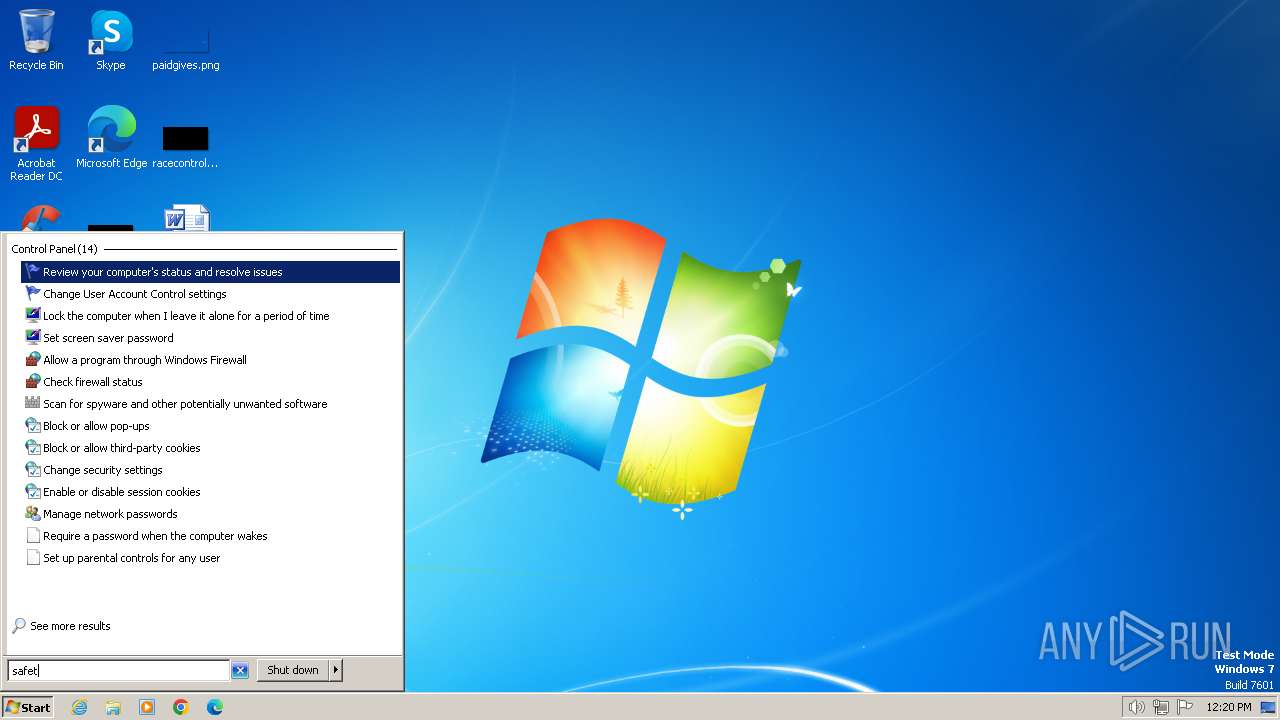
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2860)
INFO
Checks supported languages
- Setup.EXE.exe (PID: 1696)
- Robocopy.exe (PID: 2672)
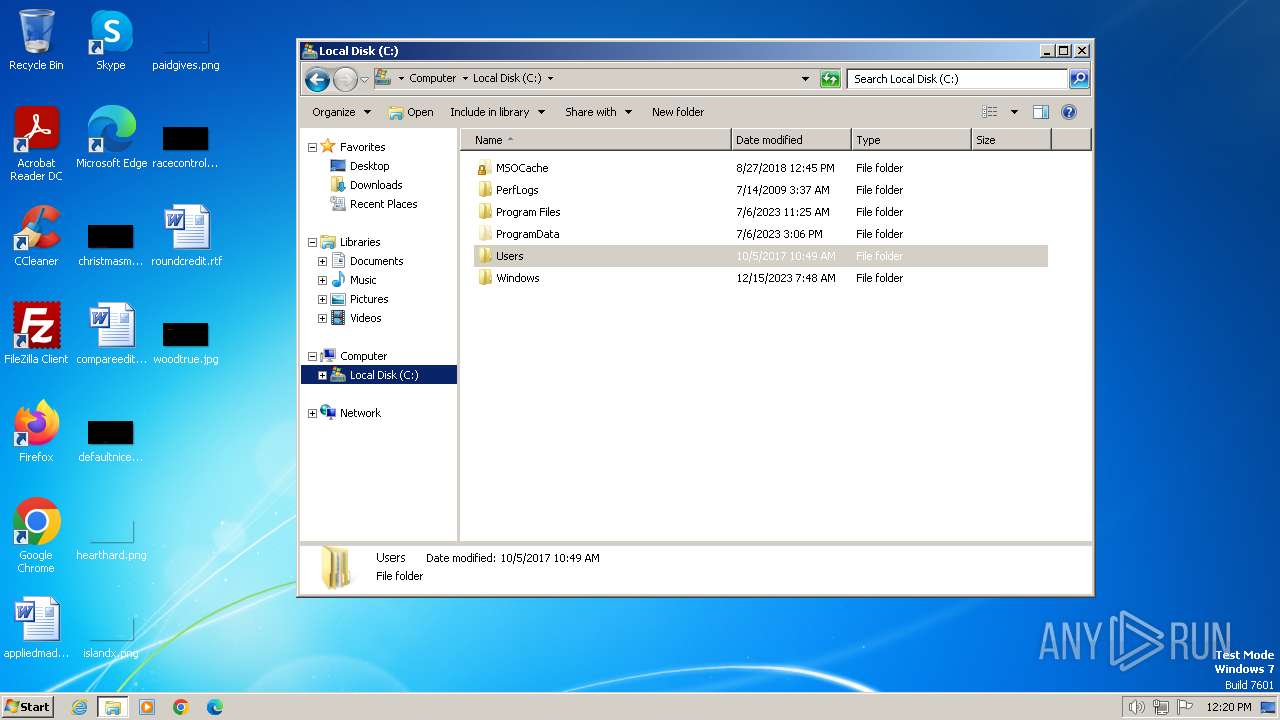
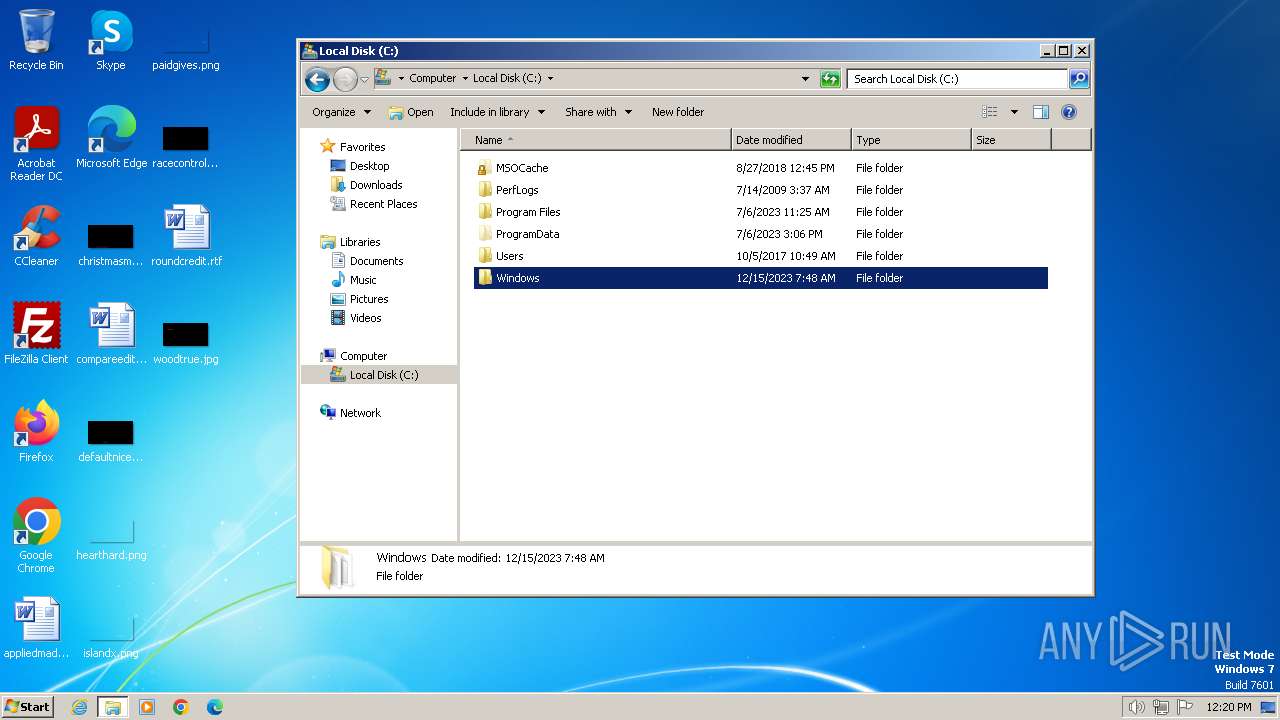
Create files in a temporary directory
- Setup.EXE.exe (PID: 1696)
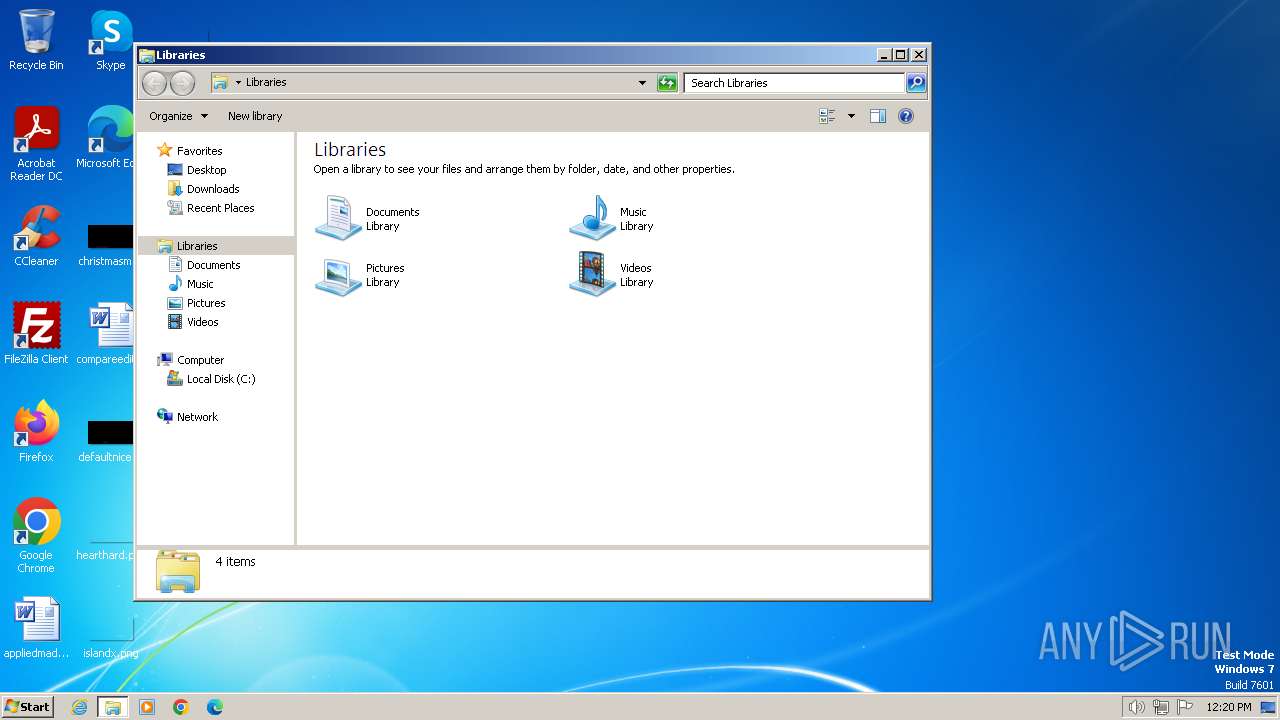
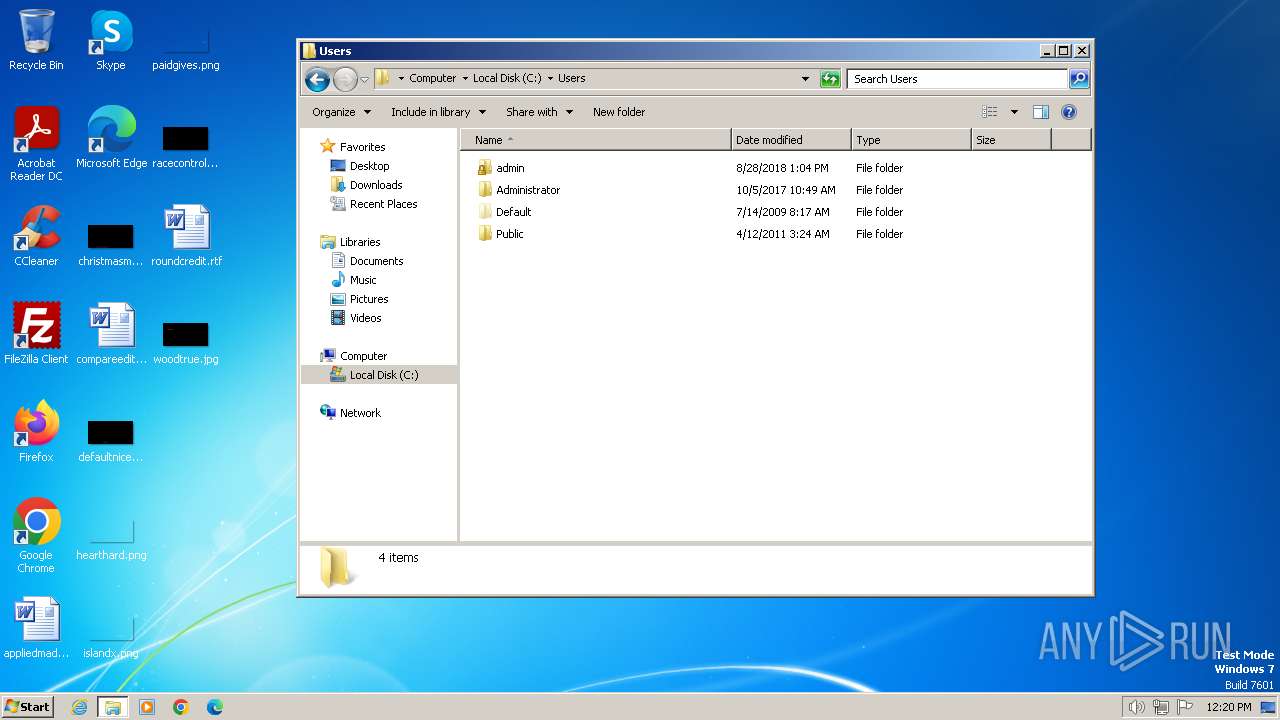
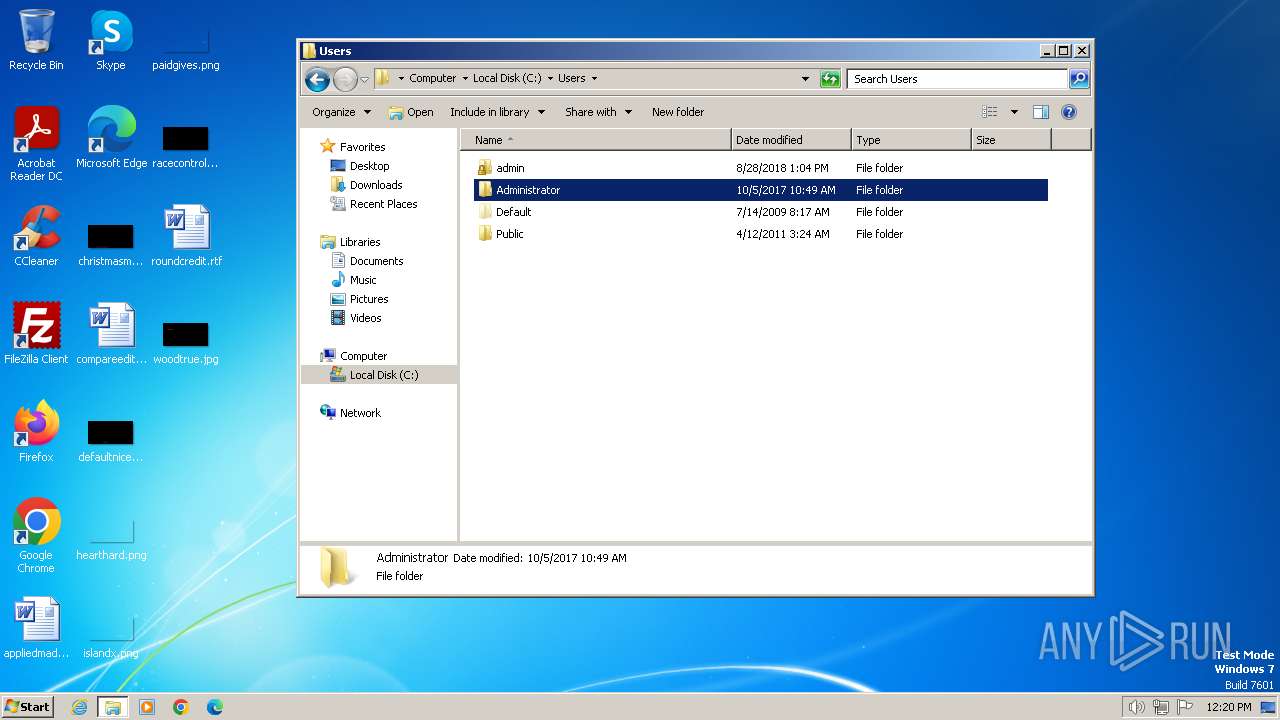
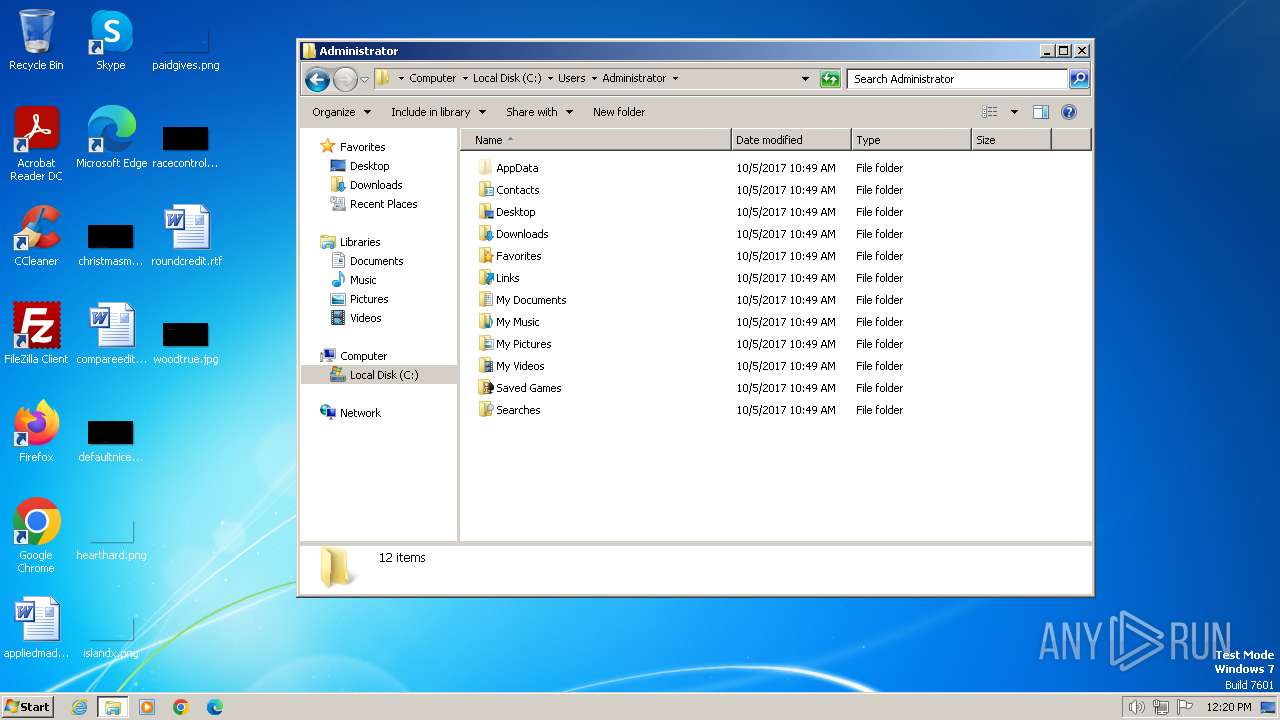
Creates files or folders in the user directory
- Robocopy.exe (PID: 2672)
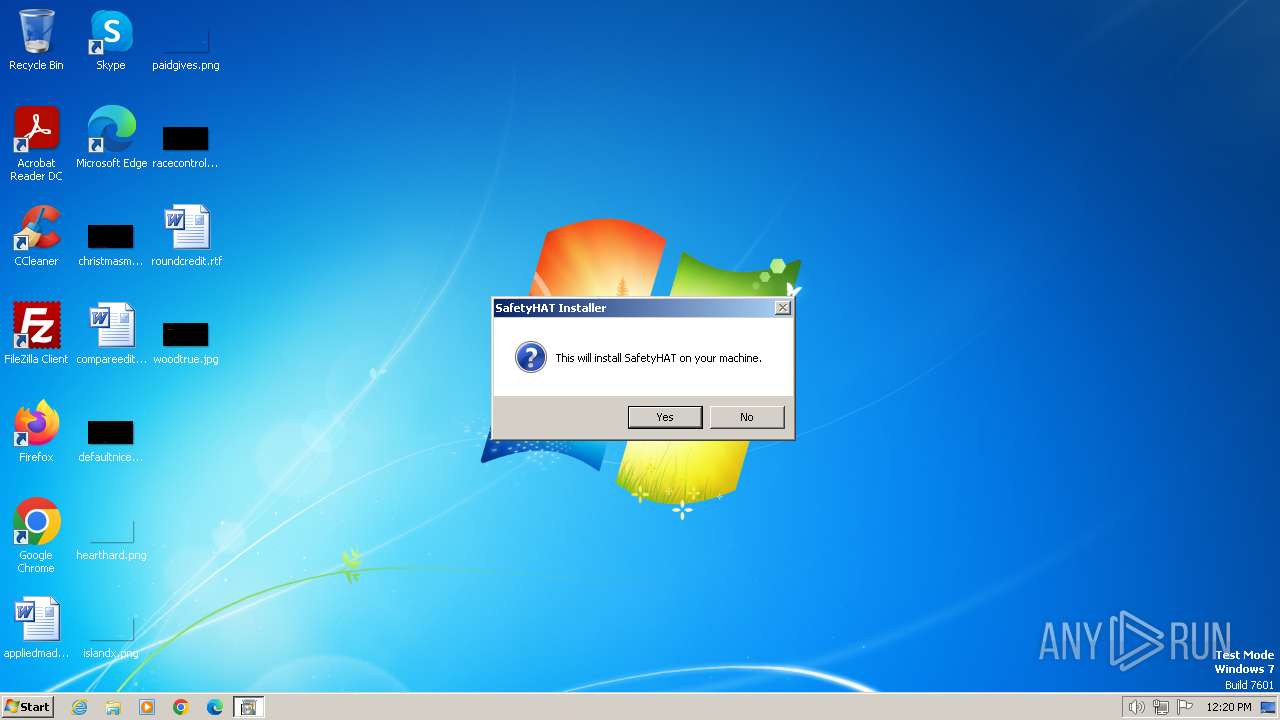
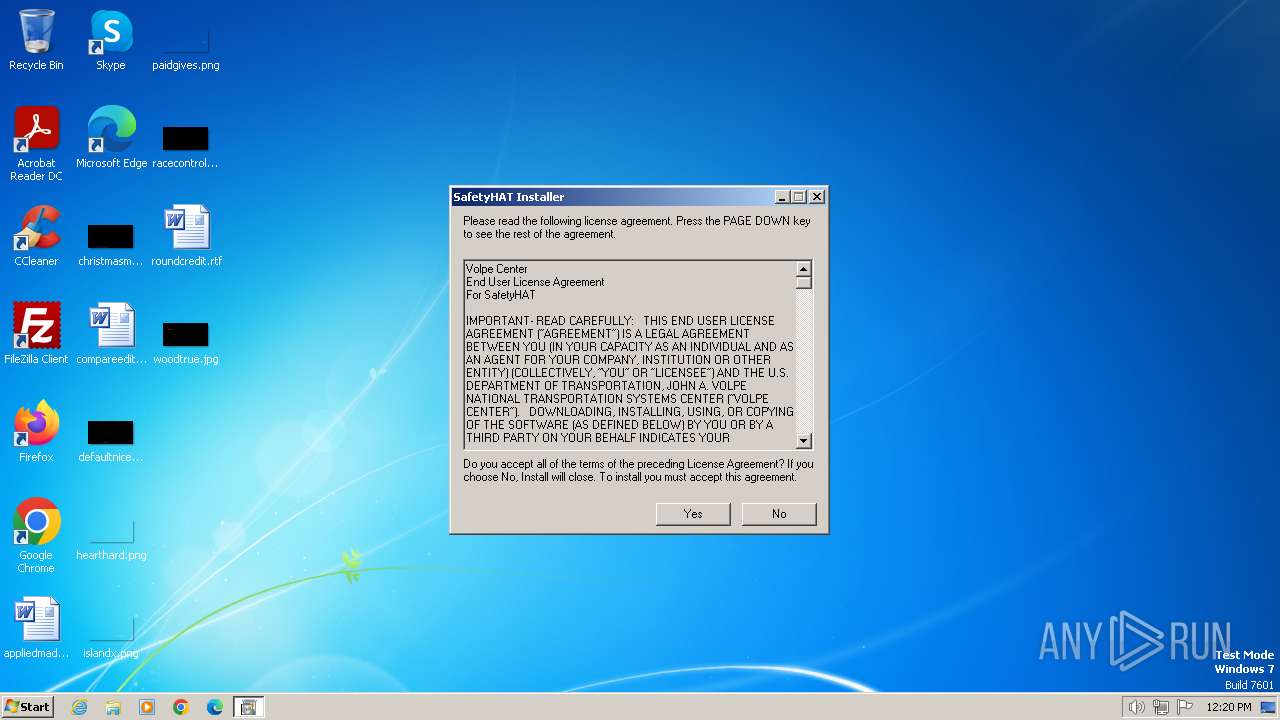
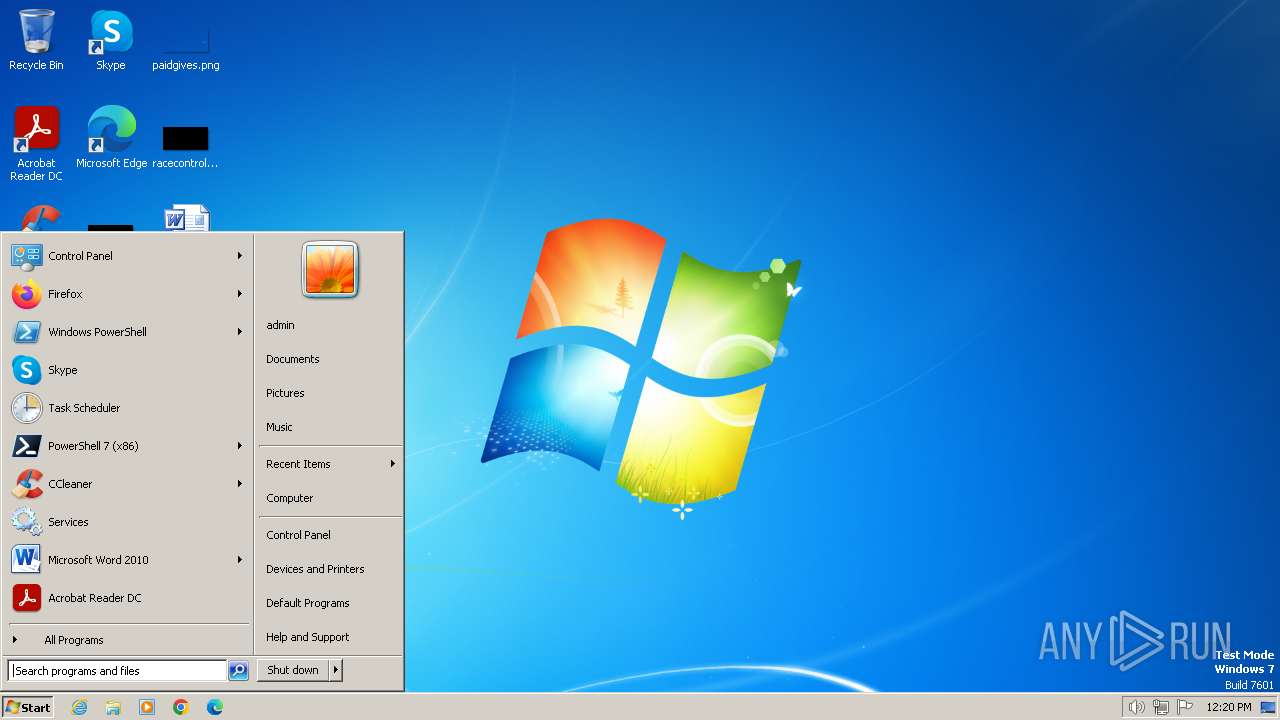
Manual execution by a user
- explorer.exe (PID: 3724)
Checks operating system version
- cmd.exe (PID: 2860)
Reads the computer name
- Robocopy.exe (PID: 2672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (80.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.2) |
| .exe | | | Win64 Executable (generic) (7.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.7) |
| .exe | | | Win32 Executable (generic) (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:07:13 23:42:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 44032 |
| InitializedDataSize: | 2423808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6af8 |
| OSVersion: | 6.1 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.7600.16385 |
| ProductVersionNumber: | 8.0.7600.16385 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 8.00.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Windows® Internet Explorer |
| ProductVersion: | 8.00.7600.16385 |
Total processes
51
Monitored processes
11
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\system32\cmd.exe /S /D /c" ver " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\AppData\Local\Temp\Setup.EXE.exe" | C:\Users\admin\AppData\Local\Temp\Setup.EXE.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | C:\Windows\system32\cmd.exe /S /D /c" ver " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
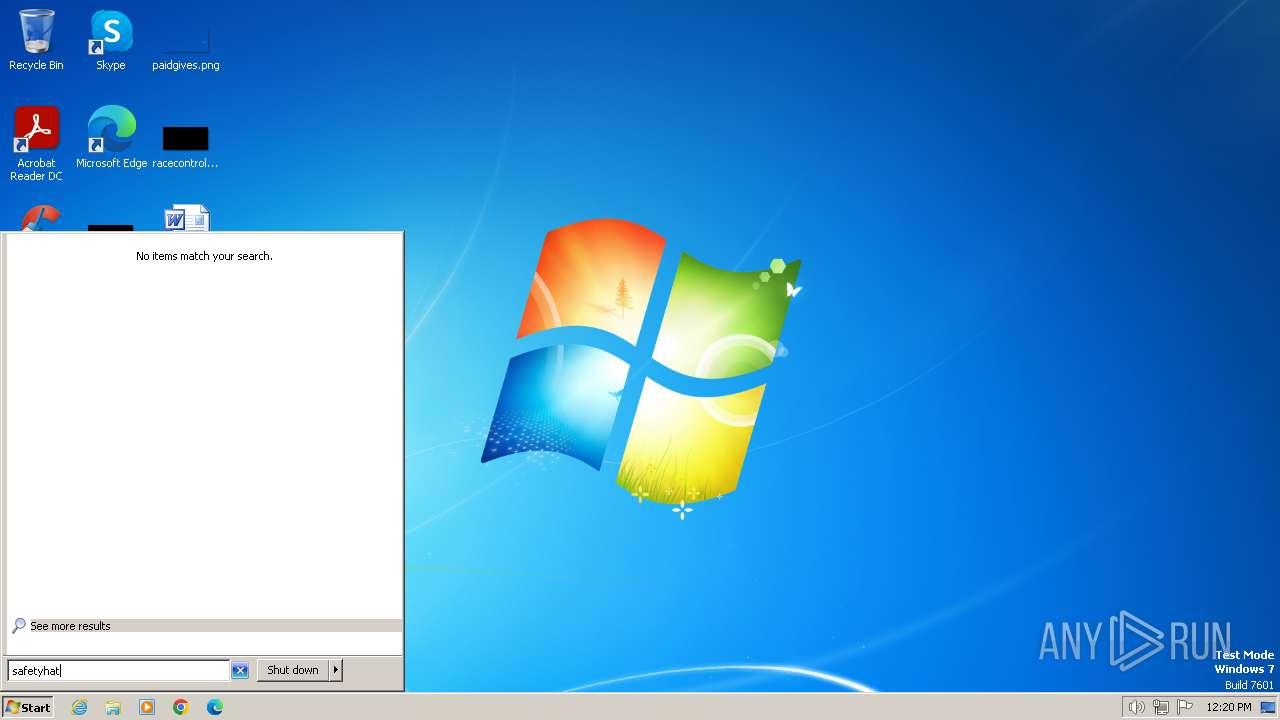
| 2672 | robocopy . "\Users\admin\AppData\Roaming\Microsoft\Templates\Access" SafetyHAT.accdt | C:\Windows\System32\Robocopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: robocopy Exit code: 1 Version: 5, 1, 10, 1027 Modules
| |||||||||||||||
| 2692 | findstr /i "5\.1\." | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | cmd.exe /c Install.bat | C:\Windows\System32\cmd.exe | — | Setup.EXE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2896 | findstr /i "6\.1\." | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
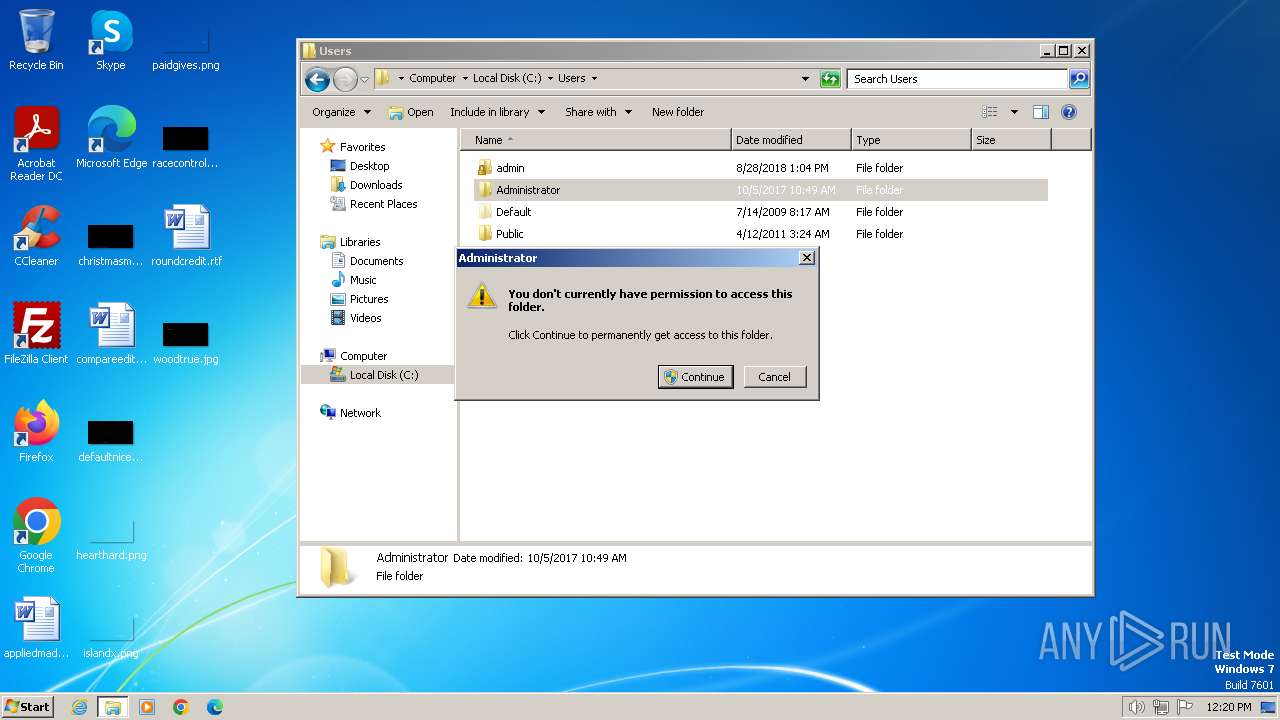
| 3444 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3724 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | C:\Windows\system32\cmd.exe /S /D /c" ver " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
581
Read events
572
Write events
3
Delete events
6
Modification events
| (PID) Process: | (2672) Robocopy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ResKit\Robocopy |
| Operation: | delete value | Name: | WaitTime |
Value: | |||
| (PID) Process: | (2672) Robocopy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ResKit\Robocopy |
| Operation: | write | Name: | WaitTime |
Value: 30000 | |||
| (PID) Process: | (2672) Robocopy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ResKit\Robocopy |
| Operation: | delete value | Name: | RetryMax |
Value: | |||
| (PID) Process: | (2672) Robocopy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ResKit\Robocopy |
| Operation: | write | Name: | RetryMax |
Value: 1000000 | |||
| (PID) Process: | (2672) Robocopy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ResKit\Robocopy |
| Operation: | delete value | Name: | JobDir |
Value: | |||
| (PID) Process: | (2672) Robocopy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ResKit\Robocopy |
| Operation: | write | Name: | JobDir |
Value: :: | |||
Executable files
0
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1696 | Setup.EXE.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Install.bat | text | |
MD5:— | SHA256:— | |||
| 1696 | Setup.EXE.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\SAFETY~1.ACC | compressed | |
MD5:— | SHA256:— | |||
| 2860 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\SafetyHAT.accdt | compressed | |
MD5:— | SHA256:— | |||
| 2672 | Robocopy.exe | C:\Users\admin\AppData\Roaming\Microsoft\Templates\Access\SafetyHAT.accdt | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |