| File name: | Big-Farm.exe |
| Full analysis: | https://app.any.run/tasks/d665dbfe-55ac-493d-88ea-97fea9444d8b |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 16:40:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5D544FE2697E5EA4AE0D472FF0E0ECB2 |
| SHA1: | 62521204572857E756657DAFFF0BCAA56D0AFA37 |
| SHA256: | 8905BA8A29A7BE20A18D5F20549F41D2EAC4A075414ED22669768129AA45ADEF |
| SSDEEP: | 6144:B/2UBG6uKoN3FPDceQzmCunQ+rSxpk+WNvUscxzOWzO5mFGDXKYmpF:Z2UBiFPwDmCunTd+WNNynWD6Yy |
MALICIOUS
Drops executable file immediately after starts
- Big-Farm.tmp (PID: 3792)
- Big-Farm.exe (PID: 2840)
- Big-Farm.exe (PID: 504)
SUSPICIOUS
Checks supported languages
- Big-Farm.exe (PID: 2840)
- Big-Farm.tmp (PID: 3184)
- Big-Farm.exe (PID: 504)
- Big-Farm.tmp (PID: 3792)
Drops a file with a compile date too recent
- Big-Farm.exe (PID: 2840)
- Big-Farm.exe (PID: 504)
- Big-Farm.tmp (PID: 3792)
Reads the computer name
- Big-Farm.tmp (PID: 3792)
- Big-Farm.tmp (PID: 3184)
Executable content was dropped or overwritten
- Big-Farm.exe (PID: 2840)
- Big-Farm.tmp (PID: 3792)
- Big-Farm.exe (PID: 504)
Reads Windows owner or organization settings
- Big-Farm.tmp (PID: 3792)
Reads the Windows organization settings
- Big-Farm.tmp (PID: 3792)
Creates a directory in Program Files
- Big-Farm.tmp (PID: 3792)
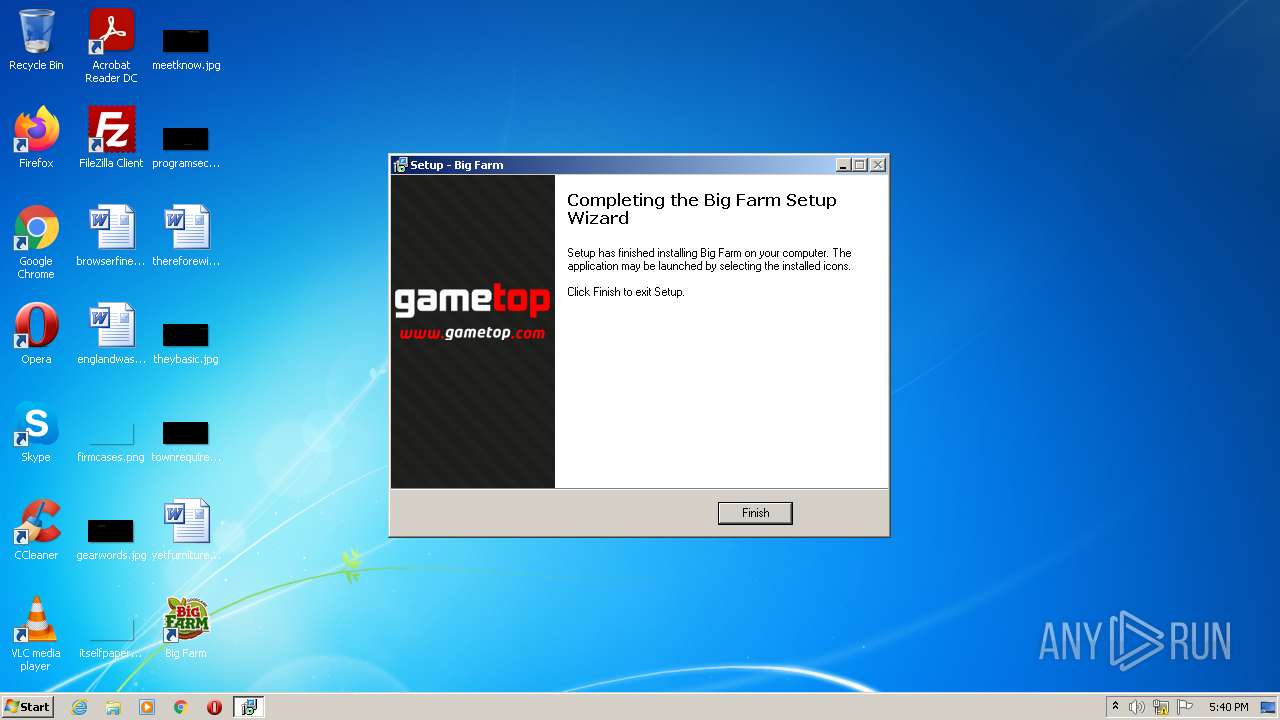
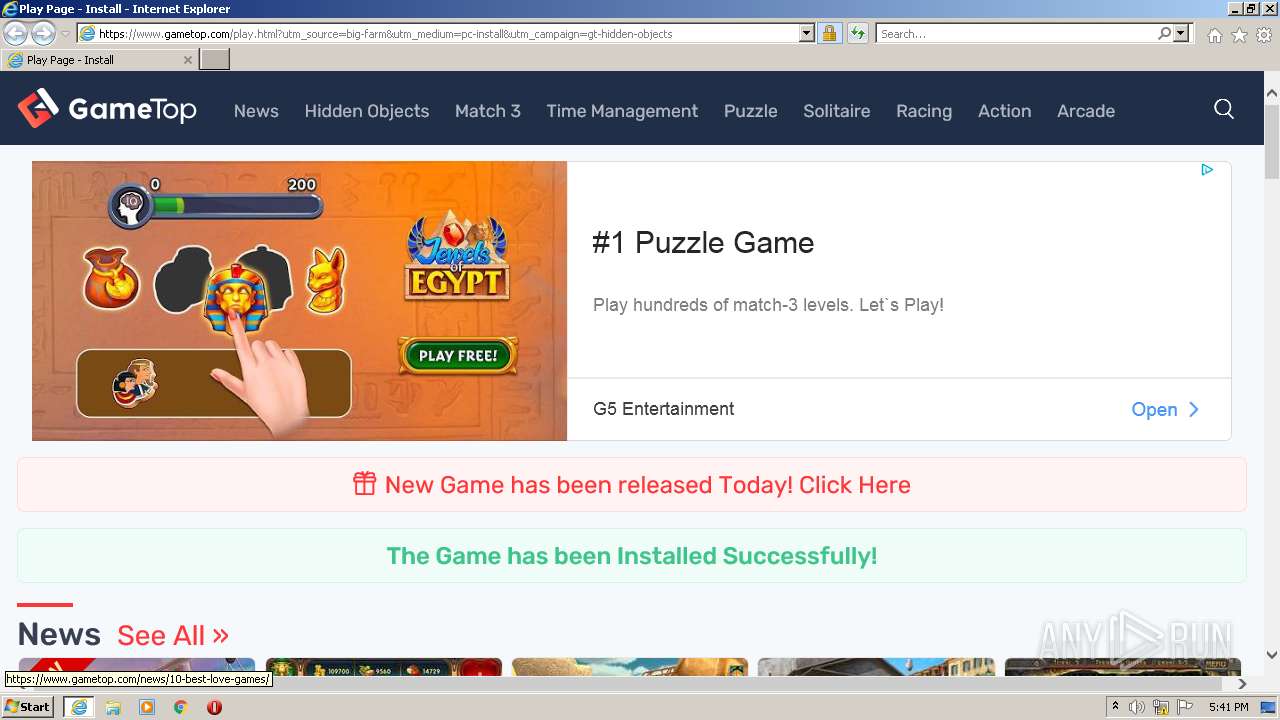
Starts Internet Explorer
- Big-Farm.tmp (PID: 3792)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3916)
INFO
Application was dropped or rewritten from another process
- Big-Farm.tmp (PID: 3184)
- Big-Farm.tmp (PID: 3792)
Loads dropped or rewritten executable
- Big-Farm.tmp (PID: 3792)
Creates files in the program directory
- Big-Farm.tmp (PID: 3792)
Changes internet zones settings
- iexplore.exe (PID: 2140)
Checks supported languages
- iexplore.exe (PID: 3916)
- iexplore.exe (PID: 2140)
Reads the computer name
- iexplore.exe (PID: 2140)
- iexplore.exe (PID: 3916)
Creates a software uninstall entry
- Big-Farm.tmp (PID: 3792)
Application launched itself
- iexplore.exe (PID: 2140)
Checks Windows Trust Settings
- iexplore.exe (PID: 3916)
- iexplore.exe (PID: 2140)
Reads settings of System Certificates
- iexplore.exe (PID: 3916)
- iexplore.exe (PID: 2140)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3916)
Changes settings of System certificates
- iexplore.exe (PID: 3916)
Creates files in the user directory
- iexplore.exe (PID: 3916)
Reads internet explorer settings
- iexplore.exe (PID: 3916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable PowerBASIC/Win 9.x (51.2) |
|---|---|---|
| .exe | | | Inno Setup installer (37.9) |
| .exe | | | Win32 Executable Delphi generic (4.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.2) |
| .exe | | | Win32 Executable (generic) (1.5) |
EXIF
EXE
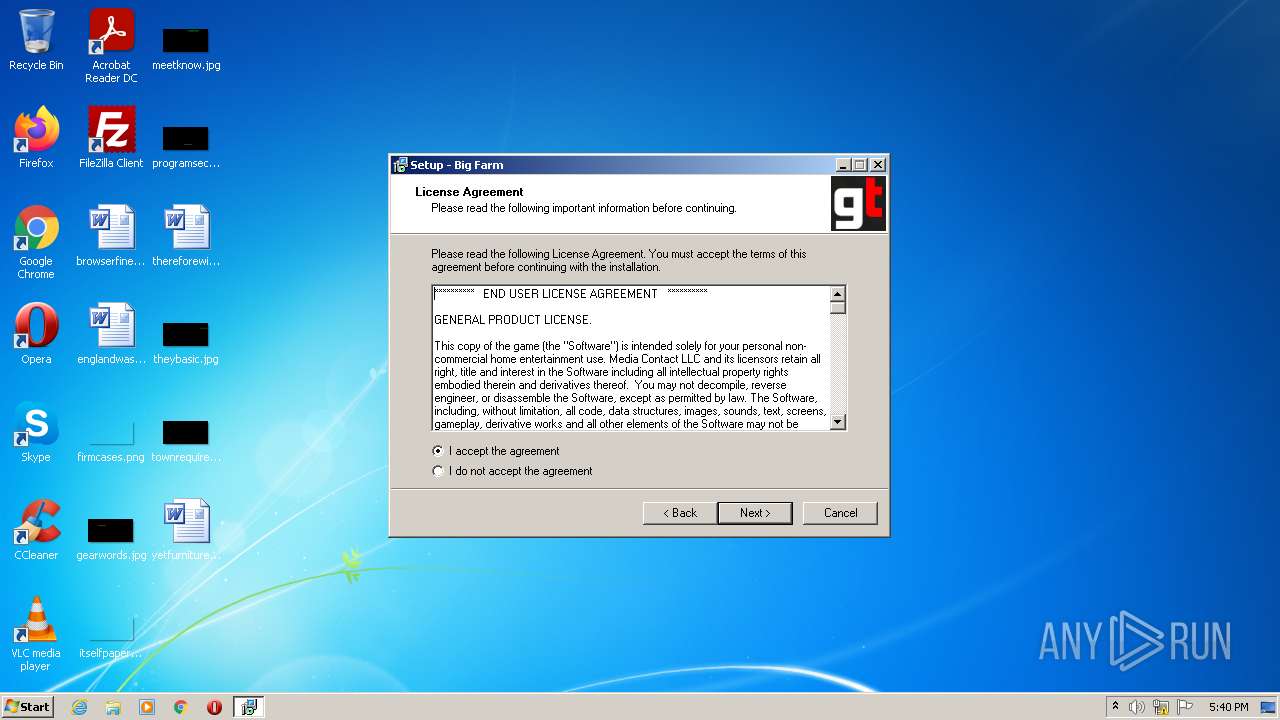
| LegalCopyright: | Copyright (C) Media Contact LLC |
|---|---|
| FileVersion: | |
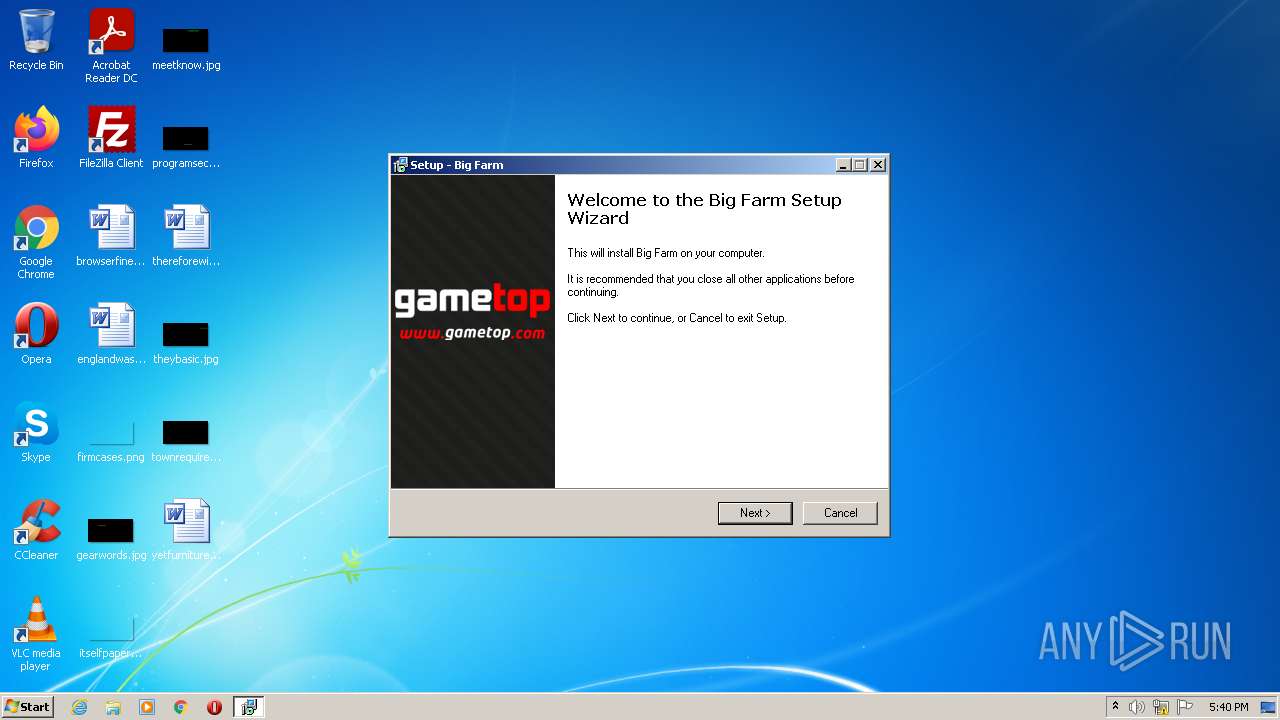
| FileDescription: | Big Farm Setup |
| CompanyName: | Media Contact LLC |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 1 |
| EntryPoint: | 0x9a54 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 17408 |
| CodeSize: | 37376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Media Contact LLC |
| FileDescription: | Big Farm Setup |
| FileVersion: | - |
| LegalCopyright: | Copyright (C) Media Contact LLC |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000916C | 0x00009200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56472 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73351 |
BSS | 0x0000C000 | 0x00000E48 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002A00 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.43241 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94378 | 1150 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
44
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Users\admin\AppData\Local\Temp\Big-Farm.exe" /SPAWNWND=$20130 /NOTIFYWND=$2012C | C:\Users\admin\AppData\Local\Temp\Big-Farm.exe | Big-Farm.tmp | ||||||||||||
User: admin Company: Media Contact LLC Integrity Level: HIGH Description: Big Farm Setup Exit code: 0 Version: Modules
| |||||||||||||||
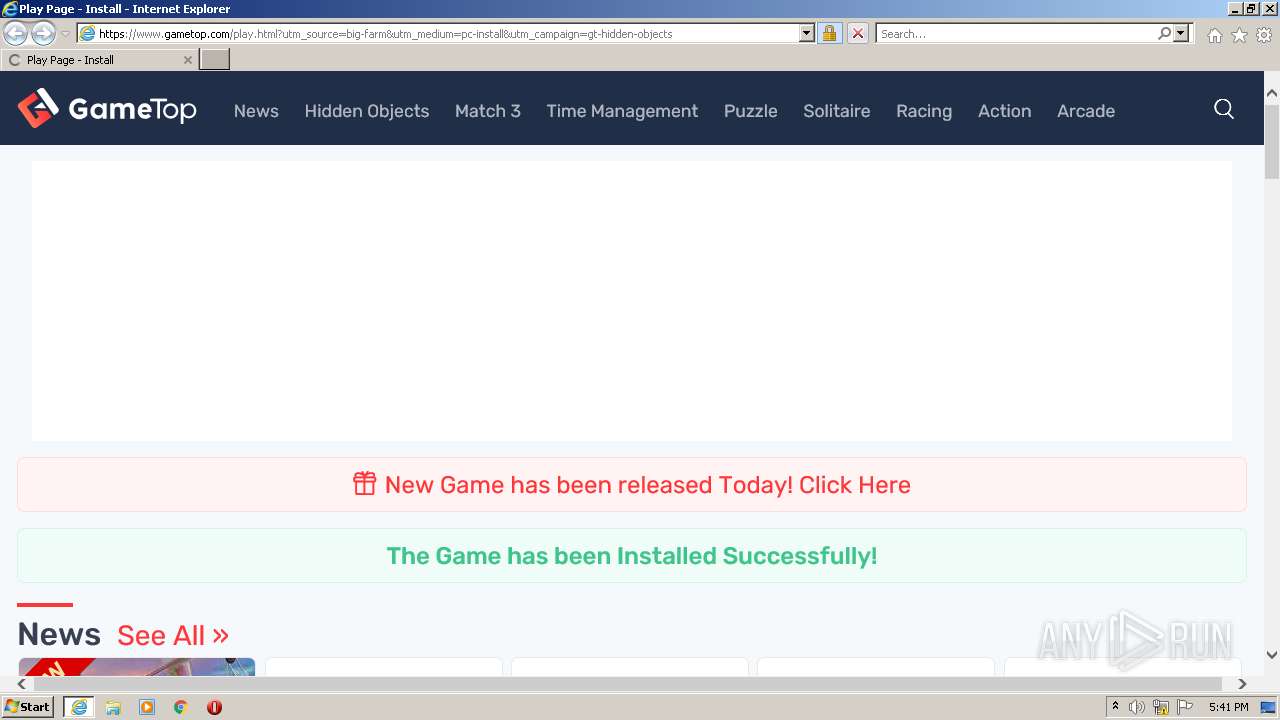
| 2140 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.gametop.com/stats/big-farm_install.html | C:\Program Files\Internet Explorer\iexplore.exe | Big-Farm.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2840 | "C:\Users\admin\AppData\Local\Temp\Big-Farm.exe" | C:\Users\admin\AppData\Local\Temp\Big-Farm.exe | Explorer.EXE | ||||||||||||
User: admin Company: Media Contact LLC Integrity Level: MEDIUM Description: Big Farm Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3184 | "C:\Users\admin\AppData\Local\Temp\is-3F9OH.tmp\Big-Farm.tmp" /SL5="$2012C,172556,53248,C:\Users\admin\AppData\Local\Temp\Big-Farm.exe" | C:\Users\admin\AppData\Local\Temp\is-3F9OH.tmp\Big-Farm.tmp | — | Big-Farm.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 3792 | "C:\Users\admin\AppData\Local\Temp\is-31NGJ.tmp\Big-Farm.tmp" /SL5="$30138,172556,53248,C:\Users\admin\AppData\Local\Temp\Big-Farm.exe" /SPAWNWND=$20130 /NOTIFYWND=$2012C | C:\Users\admin\AppData\Local\Temp\is-31NGJ.tmp\Big-Farm.tmp | Big-Farm.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 3916 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2140 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
30 743
Read events
30 509
Write events
234
Delete events
0
Modification events
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.2.2 | |||
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
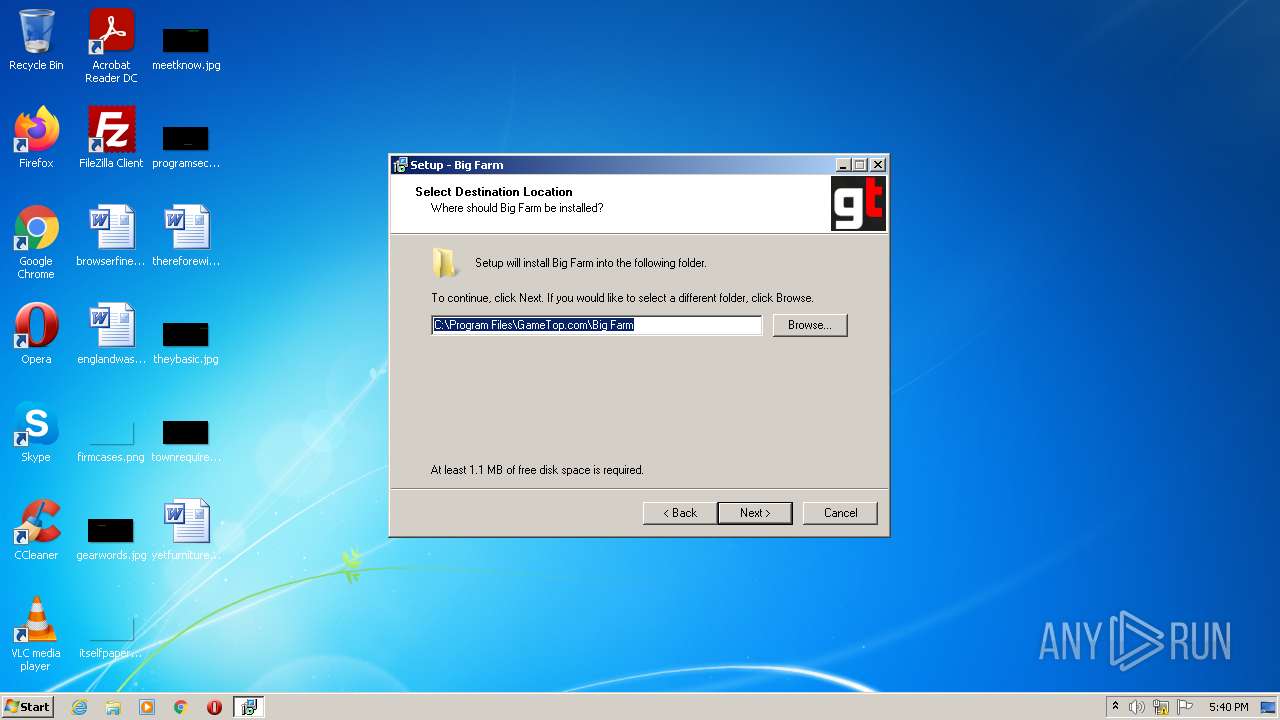
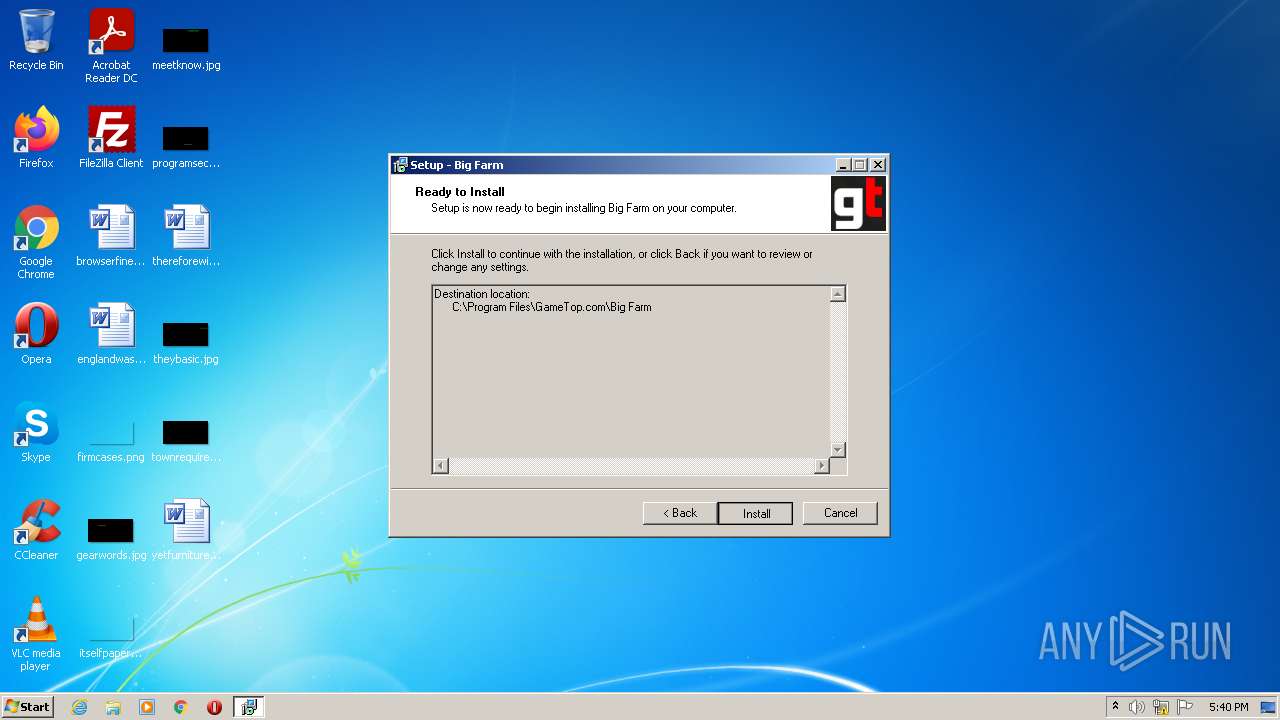
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\GameTop.com\Big Farm | |||
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\GameTop.com\Big Farm\ | |||
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: GameTop.com\Big Farm | |||
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
| Operation: | write | Name: | DisplayName |
Value: Big Farm | |||
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\GameTop.com\Big Farm\BigFarm.exe | |||
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\GameTop.com\Big Farm\unins000.exe" | |||
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\GameTop.com\Big Farm\unins000.exe" /SILENT | |||
| (PID) Process: | (3792) Big-Farm.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Big Farm_is1 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0 | |||
Executable files
8
Suspicious files
27
Text files
65
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3792 | Big-Farm.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\GameTop.com\Big Farm\Uninstall Big Farm.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\big-farm_install[1].htm | html | |
MD5:— | SHA256:— | |||
| 3792 | Big-Farm.tmp | C:\Users\admin\Desktop\Big Farm.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80A16DAF421EE6AB95634E54F4251FD8_113C44991CE1B24FF636ABAF644FE1E0 | der | |
MD5:— | SHA256:— | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:— | SHA256:— | |||
| 3792 | Big-Farm.tmp | C:\Program Files\GameTop.com\Big Farm\is-FJQ6E.tmp | executable | |
MD5:95A9E551911ADF742D5BBF98C4E782DA | SHA256:87E221866CB57C1039EB48CF7CBAED89730EB07AA9C9A47AABAD398B6B20CE0A | |||
| 2840 | Big-Farm.exe | C:\Users\admin\AppData\Local\Temp\is-3F9OH.tmp\Big-Farm.tmp | executable | |
MD5:9E30AB5E3F6B43F69F928E6B4FCFD604 | SHA256:AFFBE7F0320F9602D8C51468ECB7BC7960DF4F62AB1A36C05AC2FE2816D175BA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
92
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3916 | iexplore.exe | GET | — | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCdUrA%2FwvrytArhIvu6cF3d | US | — | — | whitelisted |
3916 | iexplore.exe | GET | — | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDwQ9JNOs3IcArkp%2FBu7NbU | US | — | — | whitelisted |
3916 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3916 | iexplore.exe | GET | 301 | 142.251.36.147:80 | http://www.gametop.com/stats/big-farm_install.html | US | html | 434 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3916 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | US | der | 724 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCHXS%2FWwGsOSRJbmAIB8NC3 | US | der | 472 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 8.248.139.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0da4cce14b203f0f | US | compressed | 60.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3916 | iexplore.exe | 142.251.36.147:80 | www.gametop.com | Google Inc. | US | unknown |
3916 | iexplore.exe | 142.251.36.147:443 | www.gametop.com | Google Inc. | US | unknown |
3916 | iexplore.exe | 142.250.185.168:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3916 | iexplore.exe | 142.250.184.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3916 | iexplore.exe | 142.250.185.162:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3916 | iexplore.exe | 69.16.175.10:443 | cdn.gametop.com | Highwinds Network Group, Inc. | US | malicious |
3916 | iexplore.exe | 142.250.186.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3916 | iexplore.exe | 104.18.11.207:443 | stackpath.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
3916 | iexplore.exe | 142.250.186.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3916 | iexplore.exe | 142.250.184.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gametop.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cdn.gametop.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |