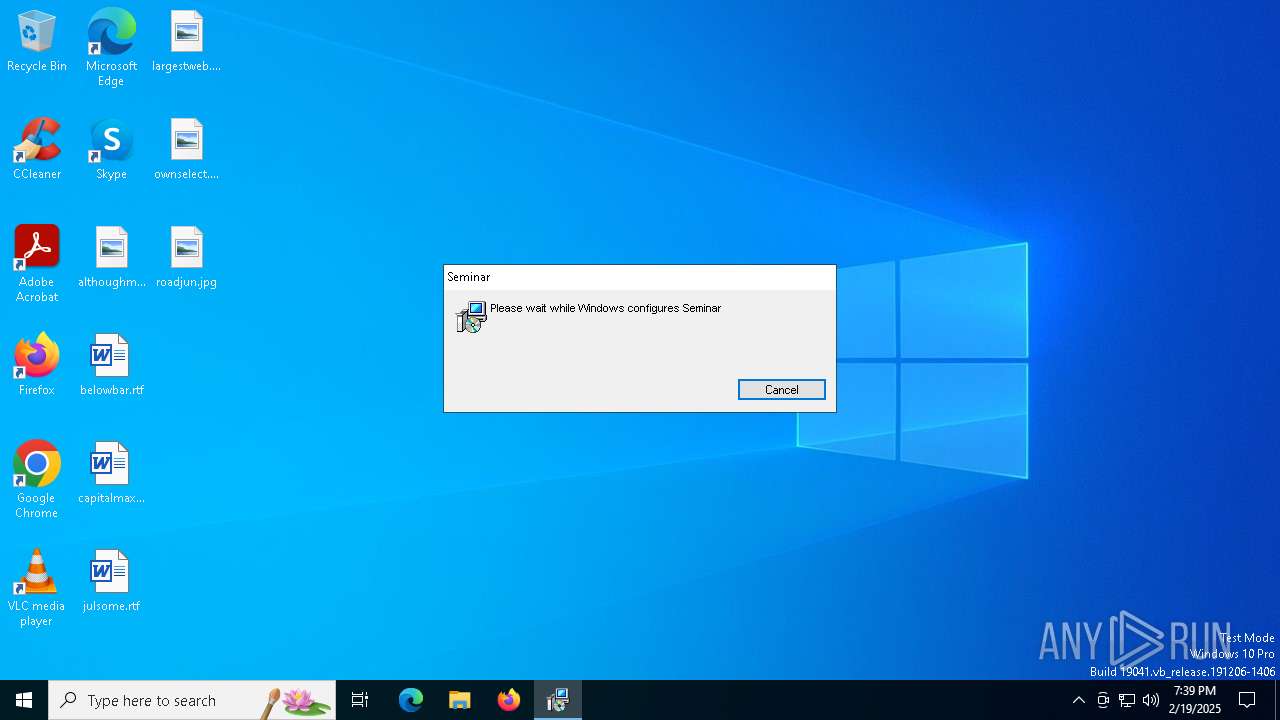
| File name: | 3aw.msi |
| Full analysis: | https://app.any.run/tasks/f3df23b2-a132-489e-8e48-485b70cb6e69 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2025, 19:39:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Seminar, Author: Ptisan Proconsul, Keywords: Installer, Comments: This installer database contains the logic and data required to install Seminar., Template: Intel;1033, Revision Number: {FDB1E7FE-EB59-441C-8DB7-AD97C5136106}, Create Time/Date: Mon Feb 17 18:29:28 2025, Last Saved Time/Date: Mon Feb 17 18:29:28 2025, Number of Pages: 500, Number of Words: 10, Name of Creating Application: WiX Toolset (4.0.0.0), Security: 2 |
| MD5: | 2352FD75DD319CAEAAD478E52902E7B9 |
| SHA1: | C6D6F871CB42F50CB700A3509321AB4546CCA092 |
| SHA256: | 88FAF43E563ACF0628487F6A36E9AB4EE2B9B470DD70461CE34CACECC005CB43 |
| SSDEEP: | 98304:fjfEXzK1ouNsgGVWCvUDYYgzXIjr4koWkSL3YMR0+hBCeuX9DrhEqpX0jMs9H+W7:mWLnktZZgZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 4932)
- msiexec.exe (PID: 6160)
- AppCheck.exe (PID: 2232)
Executes as Windows Service
- VSSVC.exe (PID: 6248)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6160)
The process drops C-runtime libraries
- msiexec.exe (PID: 6160)
- AppCheck.exe (PID: 2232)
Executable content was dropped or overwritten
- AppCheck.exe (PID: 2232)
Starts itself from another location
- AppCheck.exe (PID: 2232)
Starts CMD.EXE for commands execution
- AppCheck.exe (PID: 1412)
INFO
Manages system restore points
- SrTasks.exe (PID: 1020)
Reads the computer name
- msiexec.exe (PID: 6160)
- AppCheck.exe (PID: 1412)
The sample compiled with english language support
- msiexec.exe (PID: 4932)
- msiexec.exe (PID: 6160)
- AppCheck.exe (PID: 2232)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6160)
Checks supported languages
- msiexec.exe (PID: 6160)
Creates a software uninstall entry
- msiexec.exe (PID: 6160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Seminar |
| Author: | Ptisan Proconsul |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Seminar. |
| Template: | Intel;1033 |
| RevisionNumber: | {FDB1E7FE-EB59-441C-8DB7-AD97C5136106} |
| CreateDate: | 2025:02:17 18:29:28 |
| ModifyDate: | 2025:02:17 18:29:28 |
| Pages: | 500 |
| Words: | 10 |
| Software: | WiX Toolset (4.0.0.0) |
| Security: | Read-only recommended |
Total processes
135
Monitored processes
9
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | C:\Users\admin\AppData\Roaming\NFY_Reader_v4\AppCheck.exe | C:\Users\admin\AppData\Roaming\NFY_Reader_v4\AppCheck.exe | — | AppCheck.exe | |||||||||||
User: admin Company: CheckMAL Inc. Integrity Level: MEDIUM Description: AppCheck Anti-Ransomware Exit code: 1 Version: 3.1.39.3 Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\AppData\Local\Temp\Axinite\AppCheck.exe" | C:\Users\admin\AppData\Local\Temp\Axinite\AppCheck.exe | msiexec.exe | ||||||||||||
User: admin Company: CheckMAL Inc. Integrity Level: MEDIUM Description: AppCheck Anti-Ransomware Exit code: 0 Version: 3.1.39.3 Modules
| |||||||||||||||
| 3420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4244 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | AppCheck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4932 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\3aw.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5748 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6160 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6248 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 025
Read events
2 760
Write events
247
Delete events
18
Modification events
| (PID) Process: | (6160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000386D94F80583DB01101800004C180000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000386D94F80583DB01101800004C180000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000056604EF90583DB01101800004C180000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000056604EF90583DB01101800004C180000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000003AE757F90583DB01101800004C180000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000024145FF90583DB01101800004C180000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000430157FA0583DB01101800004C180000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000009C95BFA0583DB011018000078190000E8030000010000000000000000000000F62E77BB2088D6438FDBF8673F7C92F700000000000000000000000000000000 | |||
| (PID) Process: | (6248) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000130C6AFA0583DB0168180000B4190000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
8
Suspicious files
21
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6160 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6160 | msiexec.exe | C:\Windows\Installer\13fa80.msi | — | |
MD5:— | SHA256:— | |||
| 6160 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Axinite\baddie.ai | — | |
MD5:— | SHA256:— | |||
| 6160 | msiexec.exe | C:\Windows\Installer\13fa82.msi | — | |
MD5:— | SHA256:— | |||
| 6160 | msiexec.exe | C:\Windows\Installer\MSI5C.tmp | binary | |
MD5:FBFAAE4BB7468F26EDF9BEA613DC504C | SHA256:7F2E80F9A6386CB2BC95550511CA5A493EE63978672B6B6C6D3D17F5AFAF1644 | |||
| 6160 | msiexec.exe | C:\Windows\Temp\~DFC4FC9A5C5F2C9BA8.TMP | binary | |
MD5:FE0D43A7F9B920506E32058751CA312E | SHA256:4C57A925A0326C2CF86C80CE94D1CC671EF46F80D8DFEDF86B4DAB6B0A5B67BF | |||
| 6160 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Axinite\msvcp140.dll | executable | |
MD5:9FF712C25312821B8AEC84C4F8782A34 | SHA256:517CD3AAC2177A357CCA6032F07AD7360EE8CA212A02DD6E1301BF6CFADE2094 | |||
| 6160 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Axinite\north.ogg | binary | |
MD5:369C4C70D6F6C154C2506E899694E682 | SHA256:1DD2A18D514634D2DEE5A9F7DDEEB5C9BDBAD5F0A1A31EC76EF1B5DA7E43E426 | |||
| 6160 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:CC90FF29424B25B12FF81FEB51C2D863 | SHA256:47320FE59EDAAB7968630D360068F37472441B0DE75E621443356C9721FA77CC | |||
| 6160 | msiexec.exe | C:\Windows\Temp\~DF13A8F4C1A991B34B.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
36
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.41.82:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2164 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
2164 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6472 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4144 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4144 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4328 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.41.82:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3976 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 92.123.104.28:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 23.213.170.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |