| File name: | 88faf43e563acf0628487f6a36e9ab4ee2b9b470dd70461ce34cacecc005cb43 |
| Full analysis: | https://app.any.run/tasks/6301c3fb-05a4-40a3-bcfb-b896730b2feb |
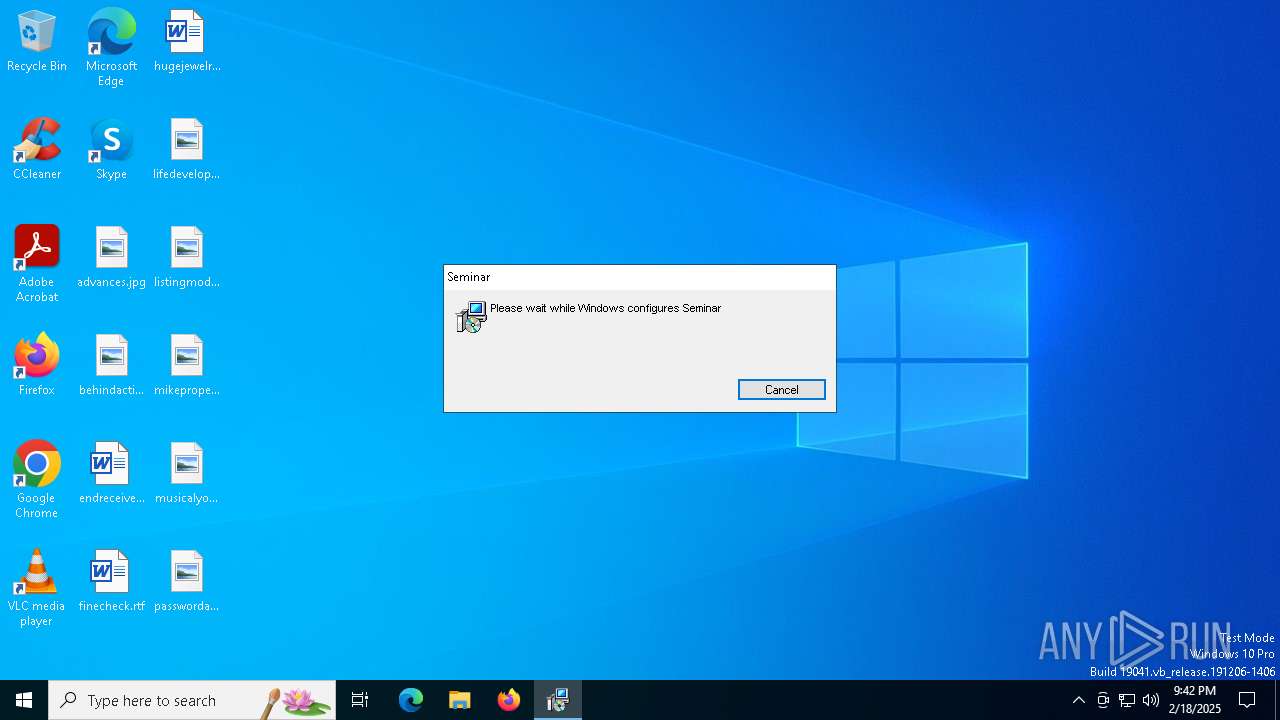
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2025, 21:41:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Seminar, Author: Ptisan Proconsul, Keywords: Installer, Comments: This installer database contains the logic and data required to install Seminar., Template: Intel;1033, Revision Number: {FDB1E7FE-EB59-441C-8DB7-AD97C5136106}, Create Time/Date: Mon Feb 17 18:29:28 2025, Last Saved Time/Date: Mon Feb 17 18:29:28 2025, Number of Pages: 500, Number of Words: 10, Name of Creating Application: WiX Toolset (4.0.0.0), Security: 2 |
| MD5: | 2352FD75DD319CAEAAD478E52902E7B9 |
| SHA1: | C6D6F871CB42F50CB700A3509321AB4546CCA092 |
| SHA256: | 88FAF43E563ACF0628487F6A36E9AB4EE2B9B470DD70461CE34CACECC005CB43 |
| SSDEEP: | 98304:fjfEXzK1ouNsgGVWCvUDYYgzXIjr4koWkSL3YMR0+hBCeuX9DrhEqpX0jMs9H+W7:mWLnktZZgZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6452)
Process drops legitimate windows executable
- msiexec.exe (PID: 6260)
- msiexec.exe (PID: 6404)
- AppCheck.exe (PID: 2084)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6404)
The process drops C-runtime libraries
- msiexec.exe (PID: 6404)
- AppCheck.exe (PID: 2084)
Starts itself from another location
- AppCheck.exe (PID: 2084)
Starts CMD.EXE for commands execution
- AppCheck.exe (PID: 2672)
Executable content was dropped or overwritten
- cmd.exe (PID: 2096)
- AppCheck.exe (PID: 2084)
The executable file from the user directory is run by the CMD process
- Ec_Oracle.exe (PID: 7076)
Reads the date of Windows installation
- Ec_Oracle.exe (PID: 7076)
INFO
The sample compiled with english language support
- msiexec.exe (PID: 6260)
- msiexec.exe (PID: 6404)
- AppCheck.exe (PID: 2084)
Reads the computer name
- msiexec.exe (PID: 6404)
- AppCheck.exe (PID: 2672)
- Ec_Oracle.exe (PID: 7076)
- AppCheck.exe (PID: 2084)
Checks supported languages
- msiexec.exe (PID: 6404)
- AppCheck.exe (PID: 2084)
- AppCheck.exe (PID: 2672)
- Ec_Oracle.exe (PID: 7076)
Manages system restore points
- SrTasks.exe (PID: 4716)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6404)
Creates a software uninstall entry
- msiexec.exe (PID: 6404)
Create files in a temporary directory
- msiexec.exe (PID: 6404)
- AppCheck.exe (PID: 2672)
Creates files or folders in the user directory
- AppCheck.exe (PID: 2084)
Reads the machine GUID from the registry
- Ec_Oracle.exe (PID: 7076)
Checks proxy server information
- Ec_Oracle.exe (PID: 7076)
Reads the software policy settings
- Ec_Oracle.exe (PID: 7076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Seminar |
| Author: | Ptisan Proconsul |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Seminar. |
| Template: | Intel;1033 |
| RevisionNumber: | {FDB1E7FE-EB59-441C-8DB7-AD97C5136106} |
| CreateDate: | 2025:02:17 18:29:28 |
| ModifyDate: | 2025:02:17 18:29:28 |
| Pages: | 500 |
| Words: | 10 |
| Software: | WiX Toolset (4.0.0.0) |
| Security: | Read-only recommended |
Total processes
140
Monitored processes
10
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2084 | "C:\Users\admin\AppData\Local\Temp\Axinite\AppCheck.exe" | C:\Users\admin\AppData\Local\Temp\Axinite\AppCheck.exe | msiexec.exe | ||||||||||||
User: admin Company: CheckMAL Inc. Integrity Level: MEDIUM Description: AppCheck Anti-Ransomware Exit code: 0 Version: 3.1.39.3 Modules
| |||||||||||||||
| 2096 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | AppCheck.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2672 | C:\Users\admin\AppData\Roaming\NFY_Reader_v4\AppCheck.exe | C:\Users\admin\AppData\Roaming\NFY_Reader_v4\AppCheck.exe | — | AppCheck.exe | |||||||||||
User: admin Company: CheckMAL Inc. Integrity Level: MEDIUM Description: AppCheck Anti-Ransomware Exit code: 1 Version: 3.1.39.3 Modules
| |||||||||||||||
| 3608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4716 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6260 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\88faf43e563acf0628487f6a36e9ab4ee2b9b470dd70461ce34cacecc005cb43.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6404 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6452 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7076 | C:\Users\admin\AppData\Local\Temp\Ec_Oracle.exe | C:\Users\admin\AppData\Local\Temp\Ec_Oracle.exe | cmd.exe | ||||||||||||
User: admin Company: Nenad Hrg (SoftwareOK.com) Integrity Level: MEDIUM Description: Q-Dir Version: 11,4,4,0 Modules
| |||||||||||||||
Total events
3 405
Read events
3 140
Write events
247
Delete events
18
Modification events
| (PID) Process: | (6404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000007EB6A8F24D82DB010419000024190000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000007EB6A8F24D82DB010419000024190000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000003E03F5F24D82DB010419000024190000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000003E03F5F24D82DB010419000024190000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000008D30FCF24D82DB010419000024190000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000003A94FEF24D82DB010419000024190000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000298391F44D82DB010419000024190000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000298391F44D82DB01041900006C1A0000E8030000010000000000000000000000029D0AC5F2E5234B9AC81D00E253E7E100000000000000000000000000000000 | |||
| (PID) Process: | (6452) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000CBFD9AF44D82DB0134190000901A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
9
Suspicious files
21
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6404 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6404 | msiexec.exe | C:\Windows\Installer\13a7bd.msi | — | |
MD5:— | SHA256:— | |||
| 6404 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Axinite\baddie.ai | — | |
MD5:— | SHA256:— | |||
| 6404 | msiexec.exe | C:\Windows\Installer\13a7bf.msi | — | |
MD5:— | SHA256:— | |||
| 6404 | msiexec.exe | C:\Windows\Installer\SourceHash{B0E8CB82-48EB-41B8-B7E1-BE66DFE5BF67} | binary | |
MD5:1FE7F7EE7C2D489623A6E6076469E60C | SHA256:3A89FAB4289CB0E1E087272EF17F66929F4ADC2FDDEA0F428D15CC581B0EDF36 | |||
| 6404 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Axinite\vcruntime140.dll | executable | |
MD5:EDF9D5C18111D82CF10EC99F6AFA6B47 | SHA256:D89C7B863FC1AC3A179D45D5FE1B9FD35FB6FBD45171CA68D0D68AB1C1AD04FB | |||
| 6404 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:4B988849B168D2242E203A9F9BA81F1E | SHA256:0FA7720FDD02B36352080A7E00688FA695A9F18AC2AFC0DDFC897FE0DC27FD29 | |||
| 6404 | msiexec.exe | C:\Windows\Temp\~DF51CB25FB19F26346.TMP | binary | |
MD5:4B988849B168D2242E203A9F9BA81F1E | SHA256:0FA7720FDD02B36352080A7E00688FA695A9F18AC2AFC0DDFC897FE0DC27FD29 | |||
| 6404 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:81ED158DD8D5FFA7AF068FF57722E071 | SHA256:8180CC594EFDF224659FDBEF958D2A2CCD63176764C1F199CACFAB87CD438AE8 | |||
| 6404 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{c50a9d02-e5f2-4b23-9ac8-1d00e253e7e1}_OnDiskSnapshotProp | binary | |
MD5:81ED158DD8D5FFA7AF068FF57722E071 | SHA256:8180CC594EFDF224659FDBEF958D2A2CCD63176764C1F199CACFAB87CD438AE8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
36
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6596 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2624 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6060 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 184.86.251.22:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 2.19.246.123:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |