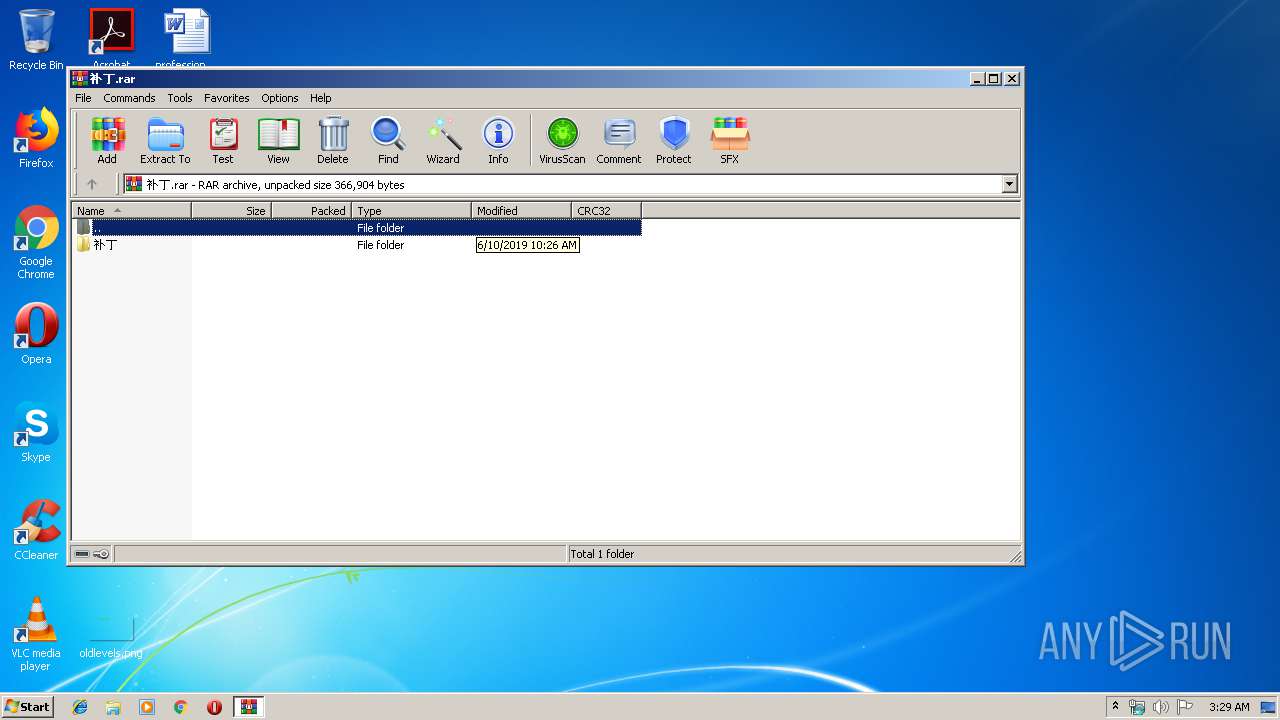
| File name: | 补丁.rar |
| Full analysis: | https://app.any.run/tasks/922d3ad7-d5b4-423d-bb8c-9c201112f1e8 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 02:28:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | D738780FA1E33459AE32164ECAF8EB39 |
| SHA1: | AB2D32FD28859264A7C14CAF9B5CA1EAF88F3D15 |
| SHA256: | 88F9B5C5F688818D51E2F7429B2594FD87326381C9BDC61C2685B1E061BA23C3 |
| SSDEEP: | 3072:nh1rnVM1ioDOJoeuYwT3r1YtFaaeftRNyRFidJWAmYW8gxwpQelldd:hunBYq3saFtRNIYLnmYKxwNlt |
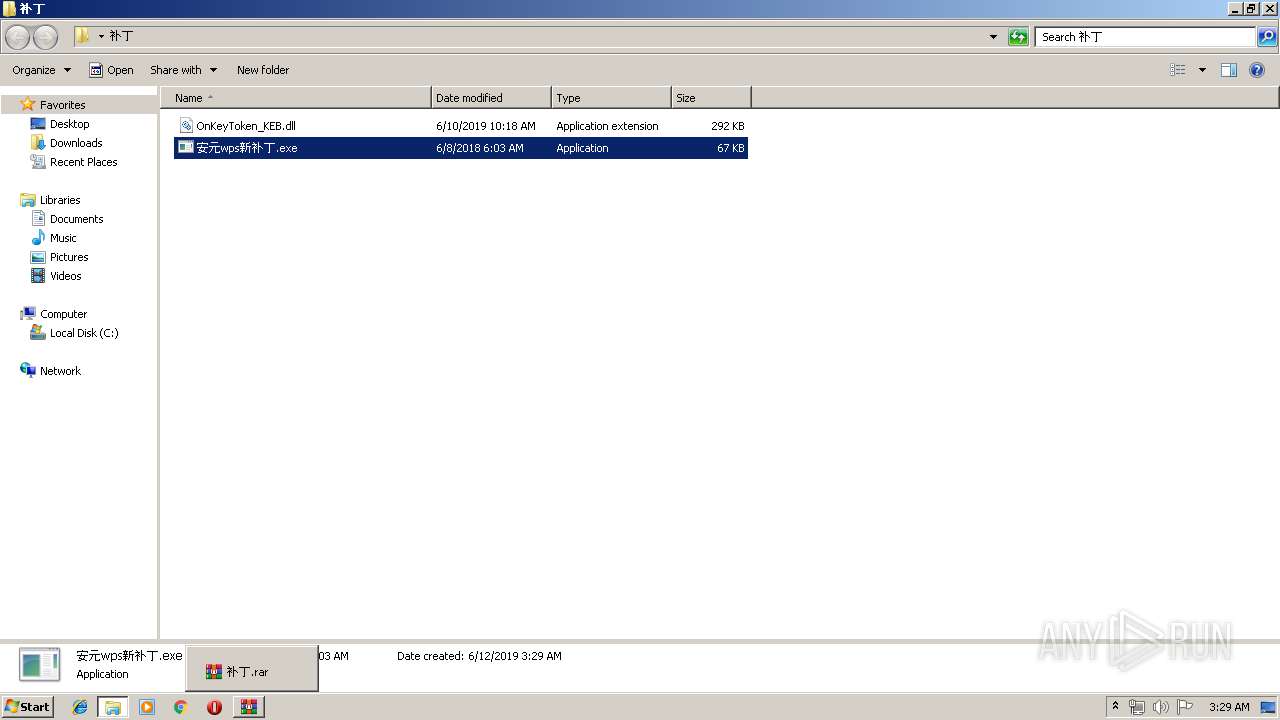
MALICIOUS
Changes the autorun value in the registry
- 安元wps新补丁.exe (PID: 3616)
- 安元wps新补丁.exe (PID: 2116)
- 安元wps新补丁.exe (PID: 3432)
SUSPICIOUS
Starts Internet Explorer
- 安元wps新补丁.exe (PID: 3616)
- 安元wps新补丁.exe (PID: 2116)
- 安元wps新补丁.exe (PID: 3432)
INFO
Manual execution by user
- 安元wps新补丁.exe (PID: 2116)
- 安元wps新补丁.exe (PID: 3616)
- 安元wps新补丁.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
40
Monitored processes
7
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2116 | "C:\Users\admin\Desktop\补丁\安元wps新补丁.exe" | C:\Users\admin\Desktop\补丁\安元wps新补丁.exe | explorer.exe | ||||||||||||
User: admin Company: Tendyron Corporation Integrity Level: MEDIUM Description: OnKeySvr Exit code: 0 Version: 2, 5, 1, 9 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | 安元wps新补丁.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | 安元wps新补丁.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\补丁.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3432 | "C:\Users\admin\Desktop\补丁\安元wps新补丁.exe" | C:\Users\admin\Desktop\补丁\安元wps新补丁.exe | explorer.exe | ||||||||||||
User: admin Company: Tendyron Corporation Integrity Level: MEDIUM Description: OnKeySvr Exit code: 0 Version: 2, 5, 1, 9 Modules
| |||||||||||||||
| 3488 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | 安元wps新补丁.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3616 | "C:\Users\admin\Desktop\补丁\安元wps新补丁.exe" | C:\Users\admin\Desktop\补丁\安元wps新补丁.exe | explorer.exe | ||||||||||||
User: admin Company: Tendyron Corporation Integrity Level: MEDIUM Description: OnKeySvr Exit code: 0 Version: 2, 5, 1, 9 Modules
| |||||||||||||||
Total events
434
Read events
423
Write events
11
Delete events
0
Modification events
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\补丁.rar | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2116) 安元wps新补丁.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Tendyron |
Value: C:\Users\admin\Desktop\??\??wps???.exe | |||
| (PID) Process: | (3616) 安元wps新补丁.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Tendyron |
Value: C:\Users\admin\Desktop\??\??wps???.exe | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
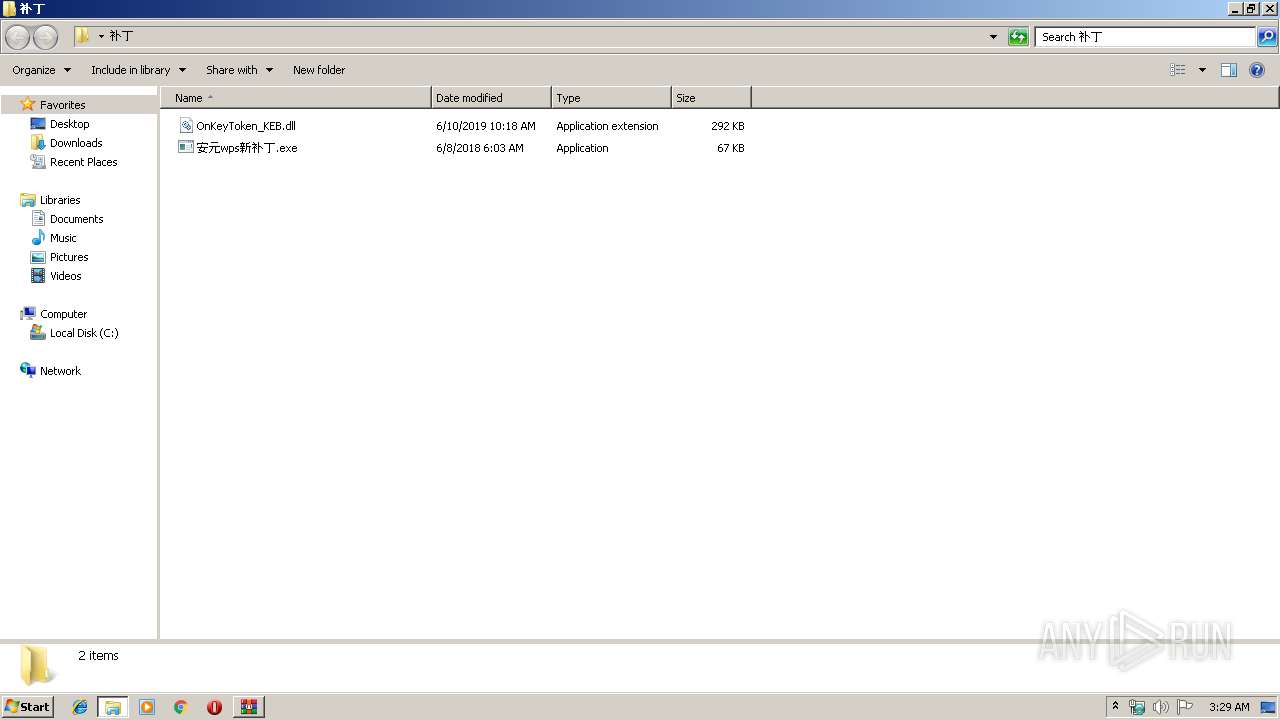
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2984.6534\补丁\OnKeyToken_KEB.dll | — | |
MD5:— | SHA256:— | |||
| 2984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2984.6534\补丁\安元wps新补丁.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3488 | iexplore.exe | 114.118.83.141:53 | — | IDC, China Telecommunications Corporation | CN | malicious |
2184 | iexplore.exe | 114.118.83.141:53 | — | IDC, China Telecommunications Corporation | CN | malicious |
2296 | iexplore.exe | 114.118.83.141:53 | — | IDC, China Telecommunications Corporation | CN | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3488 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32.Backdoor.Zegost.Auto connection |
2296 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32.Backdoor.Zegost.Auto connection |
2184 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32.Backdoor.Zegost.Auto connection |