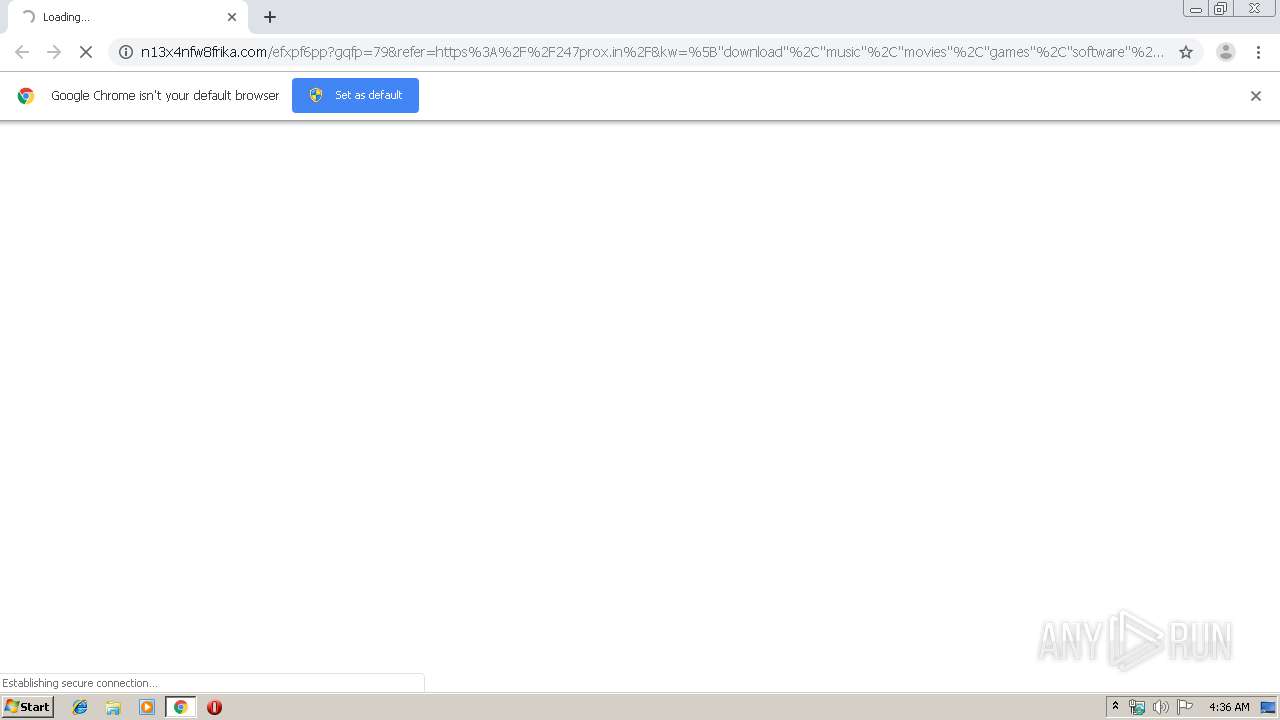
| URL: | http://n13x4nfw8frika.com/efxpf6pp?gqfp=79&refer=https%3A%2F%2F247prox.in%2F&kw=%5B%22download%22%2C%22music%22%2C%22movies%22%2C%22games%22%2C%22software%22%2C%22the%22%2C%22pirate%22%2C%22bay%22%2C%22-%22%2C%22the%22%2C%22galaxy%22%2C%22s%22%2C%22most%22%2C%22resilient%22%2C%22bittorrent%22%2C%22site%22%5D&key=b1f57639c83dbef948eefa8b64183e1e&scrWidth=1920&scrHeight=1080&tz=7&ship=&pst=&v=19.12.v.10&res=7.31&dev=r&adb=y;not-a-virus:HEUR:AdWare.Script.Pusher.gen;http://n13x4nfw8frika.com/efxpf6pp?gqfp=79&refer=https%3A%2F%2F247prox.in%2F&kw=%5B%22download%22%2C%22music%22%2C%22movies%22%2C%22games%22%2C%22software%22%2C%22the%22%2C%22pirate%22%2C%22bay%22%2C%22-%22%2C%22the%22%2C%22galaxy%22%2C%22s%22%2C%22most%22%2C%22resilient%22%2C%22bittorrent%22%2C%22site%22%5D&key=b1f57639c83dbef948eefa8b64183e1e&scrWidth=1920&scrHeight=1080&tz=7&ship=&pst=&v=19.12.v.10&res=7.31&dev=r&adb=y |
| Full analysis: | https://app.any.run/tasks/4abcf7ab-2452-4529-94af-a1adddd96f53 |
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2019, 04:36:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4AE530F7AF78F4BA0894563C0E56C795 |
| SHA1: | 22704D8713C46CA713D18F6A147DA39757EC66CB |
| SHA256: | 88F1EE3BA948CDCB8353480C9C91024382424CF364FCA4D261C7C0AD4CE5B0F4 |
| SSDEEP: | 24:F6Mb19wWEFiOyH6OB8AXGIG+MP6Mb19wWEFiOyH6OB8AXGIG+D:AMB9wWOiOyH6OB8MGI9MSMB9wWOiOyHR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 1944)
- chrome.exe (PID: 2644)
Application launched itself
- chrome.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18221804053872320171 --mojo-platform-channel-handle=3728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6026809178109638016 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14475649962416293546 --mojo-platform-channel-handle=3896 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5470765567912645277 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8928580258688441367 --mojo-platform-channel-handle=3880 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4145746234771660876 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14697920340110142243 --mojo-platform-channel-handle=4684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16973284147742605948 --mojo-platform-channel-handle=1544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12483896056123980272 --mojo-platform-channel-handle=4436 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10301067063328607494,3396839800461332667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12696795399358161907 --mojo-platform-channel-handle=4368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
229
Read events
161
Write events
64
Delete events
4
Modification events
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2644-13221808600809500 |
Value: 259 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
41
Text files
235
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a27f2d00-626c-4a0a-8161-f120ec669b4c.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF39a8ec.TMP | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a850.TMP | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
49
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1944 | chrome.exe | GET | 302 | 198.134.112.242:80 | http://n13x4nfw8frika.com/efxpf6pp?gqfp=79&refer=https%3A%2F%2F247prox.in%2F&kw=%5B%22download%22%2C%22music%22%2C%22movies%22%2C%22games%22%2C%22software%22%2C%22the%22%2C%22pirate%22%2C%22bay%22%2C%22-%22%2C%22the%22%2C%22galaxy%22%2C%22s%22%2C%22most%22%2C%22resilient%22%2C%22bittorrent%22%2C%22site%22%5D&key=b1f57639c83dbef948eefa8b64183e1e&scrWidth=1920&scrHeight=1080&tz=7&ship=&pst=&v=19.12.v.10&res=7.31&dev=r&adb=y;not-a-virus:HEUR:AdWare.Script.Pusher.gen;http://n13x4nfw8frika.com/efxpf6pp?gqfp=79&refer=https%3A%2F%2F247prox.in%2F&kw=%5B%22download%22%2C%22music%22%2C%22movies%22%2C%22games%22%2C%22software%22%2C%22the%22%2C%22pirate%22%2C%22bay%22%2C%22-%22%2C%22the%22%2C%22galaxy%22%2C%22s%22%2C%22most%22%2C%22resilient%22%2C%22bittorrent%22%2C%22site%22%5D&key=b1f57639c83dbef948eefa8b64183e1e&scrWidth=1920&scrHeight=1080&tz=7&ship=&pst=&v=19.12.v.10&res=7.31&dev=r&adb=y | US | — | — | suspicious |
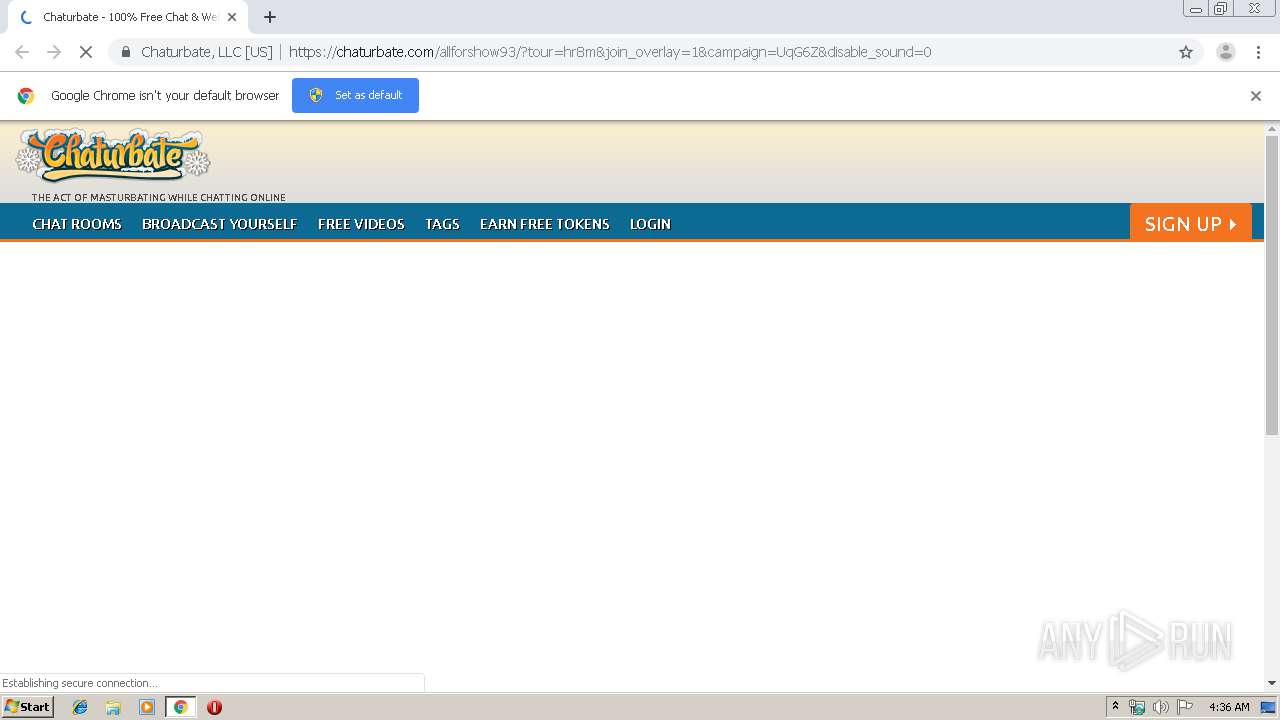
1944 | chrome.exe | GET | 301 | 104.18.91.31:80 | http://chaturbate.com/toproom/?join_overlay=1&tour=hr8m&disable_sound=0&campaign=UqG6Z | US | — | — | suspicious |
1944 | chrome.exe | GET | 302 | 104.18.91.31:80 | http://chaturbate.com/affiliates/in/?track=p8323_153660&tour=hr8m&campaign=UqG6Z | US | — | — | suspicious |
1944 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 512 b | whitelisted |
1944 | chrome.exe | GET | 200 | 185.48.9.17:80 | http://r6---sn-x2pm-3uf6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=31.204.154.118&mm=28&mn=sn-x2pm-3uf6&ms=nvh&mt=1577334914&mv=m&mvi=5&pl=21&shardbypass=yes | PL | crx | 862 Kb | whitelisted |
1944 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 517 b | whitelisted |
1944 | chrome.exe | GET | 302 | 151.139.128.10:80 | http://redir.jads.co/pu_uu.php?cb=1577335004&uu=1C451643-E411-6280-5CAE-C34234D91FF2 | US | binary | 20 b | suspicious |
1944 | chrome.exe | GET | 200 | 176.126.58.204:80 | http://r1---sn-x2pm-3ufk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=31.204.154.118&mm=28&mn=sn-x2pm-3ufk&ms=nvh&mt=1577334914&mv=m&mvi=0&pl=21&shardbypass=yes | PL | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1944 | chrome.exe | 198.134.112.242:80 | n13x4nfw8frika.com | Webair Internet Development Company Inc. | US | suspicious |
1944 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 104.18.91.31:443 | chaturbate.com | Cloudflare Inc | US | unknown |
1944 | chrome.exe | 104.16.93.42:443 | ssl-ccstatic.highwebmedia.com | Cloudflare Inc | US | unknown |
1944 | chrome.exe | 213.196.2.1:443 | r.remarketingpixel.com | Servers.com, Inc. | NL | suspicious |
1944 | chrome.exe | 151.139.128.10:80 | xapi.juicyads.com | Highwinds Network Group, Inc. | US | malicious |
1944 | chrome.exe | 198.134.112.242:443 | n13x4nfw8frika.com | Webair Internet Development Company Inc. | US | suspicious |
1944 | chrome.exe | 216.58.205.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 172.217.22.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
n13x4nfw8frika.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
newoctads.com |
| malicious |
r.remarketingpixel.com |
| whitelisted |
xapi.juicyads.com |
| whitelisted |
redir.jads.co |
| suspicious |
chaturbate.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| malicious |