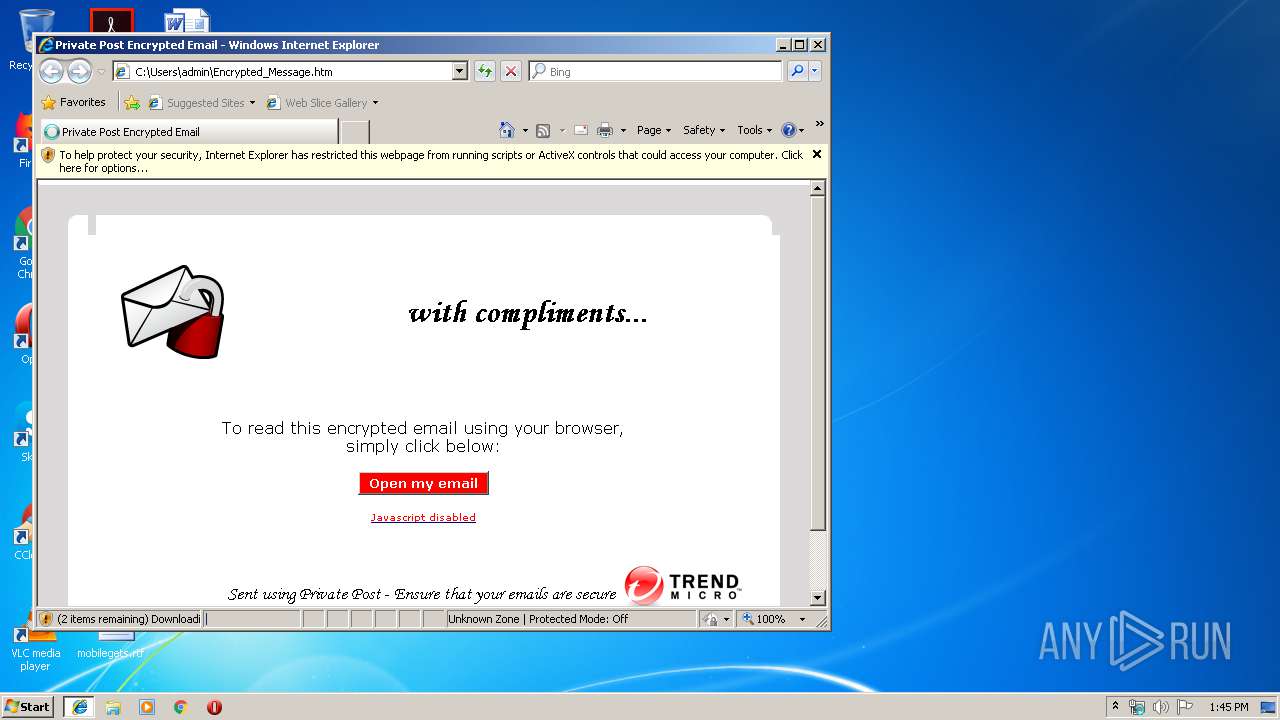
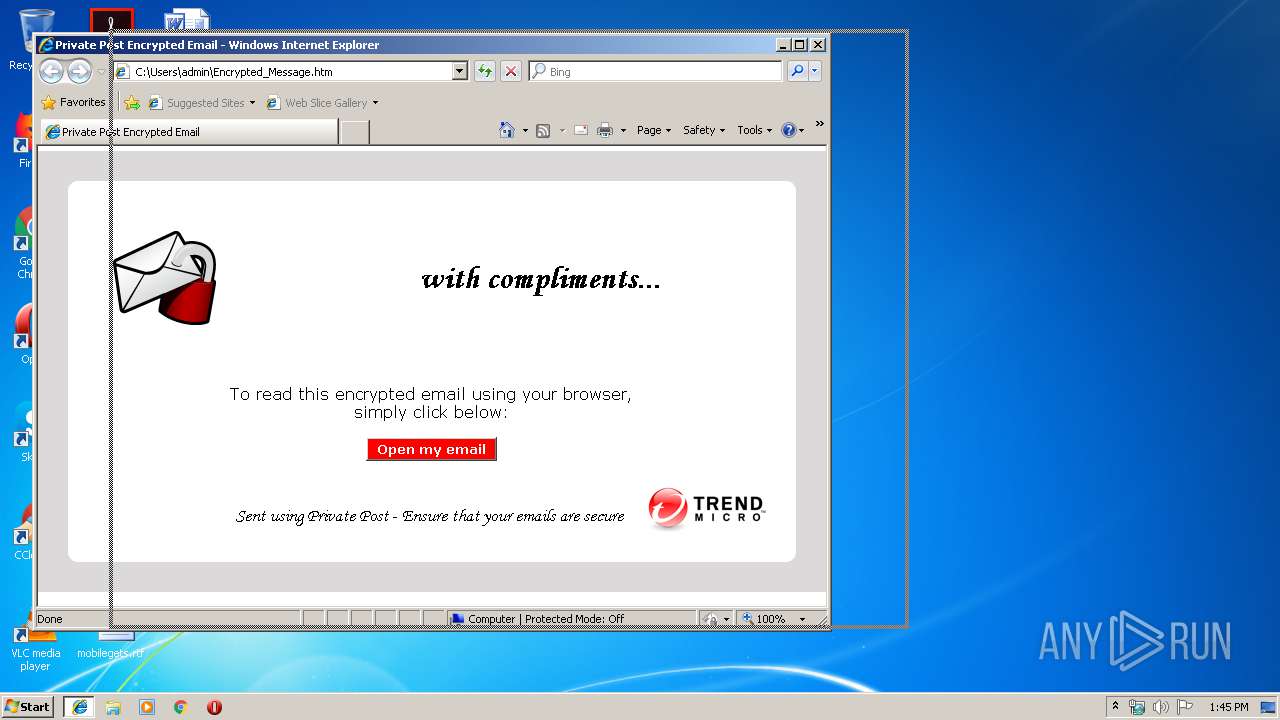
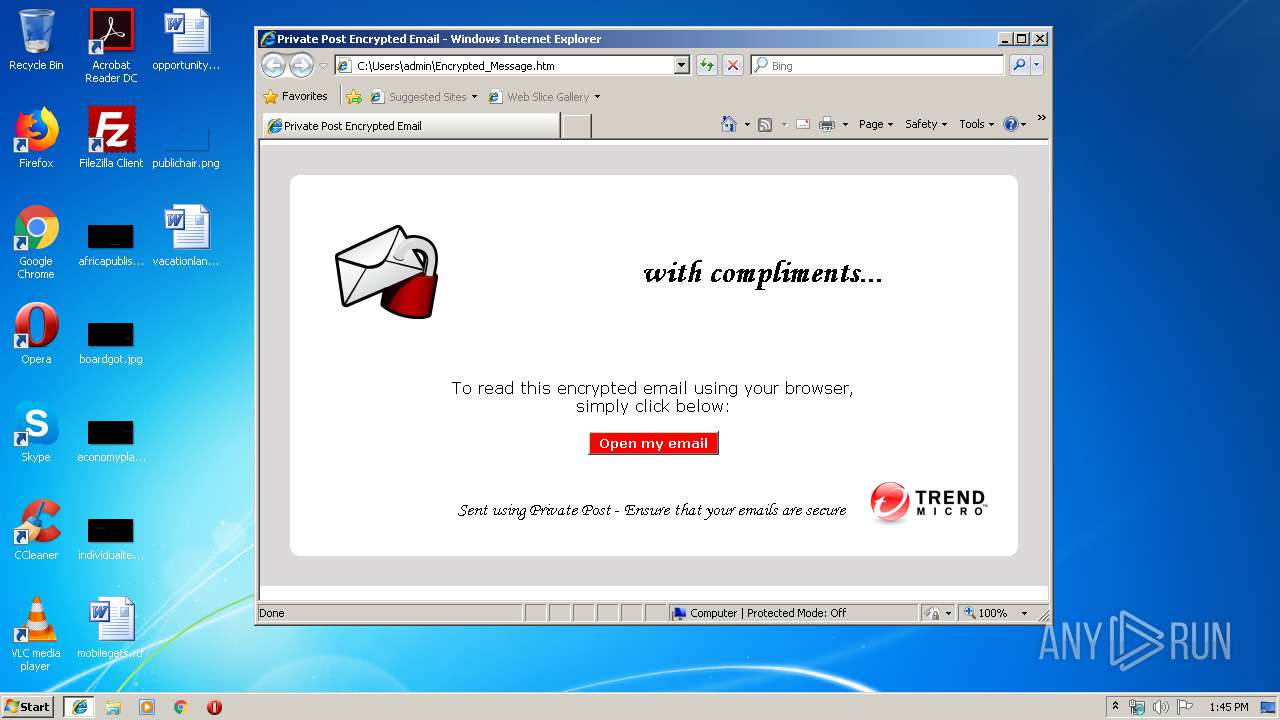
| File name: | Encrypted_Message.htm |
| Full analysis: | https://app.any.run/tasks/a075b45e-7e50-4d2d-af97-8fb15dc1eeea |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 12:44:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode (with BOM) text, with CRLF line terminators |
| MD5: | 955B6FCE3211CE25D6C564EB2555D97F |
| SHA1: | 1E92C2A8B21A4CB10DF63CC247D332B8B04169F8 |
| SHA256: | 88F0F6F1AF6091123DD83F089E8A87C9403255BA9421816F6158A89B80A6383F |
| SSDEEP: | 1536:pb+AeAK+RDRdktghDUI7Slqc0R+AbWf+MgJ0R:pb+AeAhFRdigh0lXA76fkY |
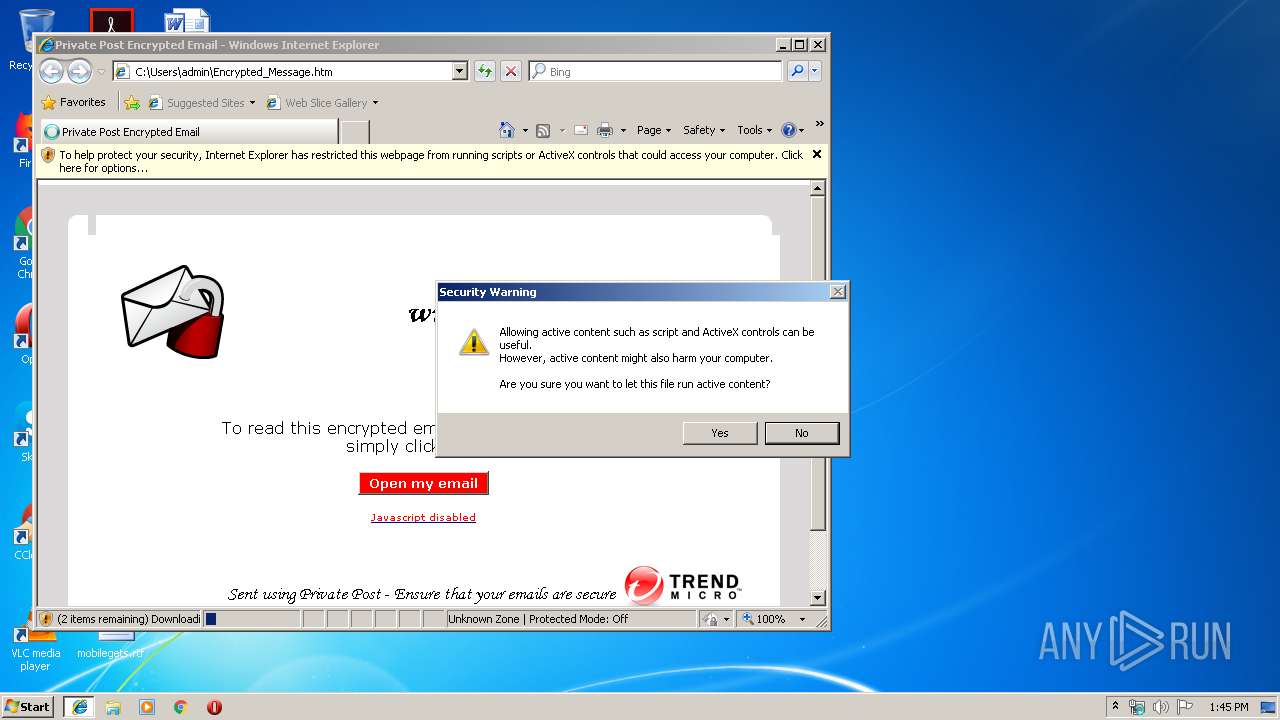
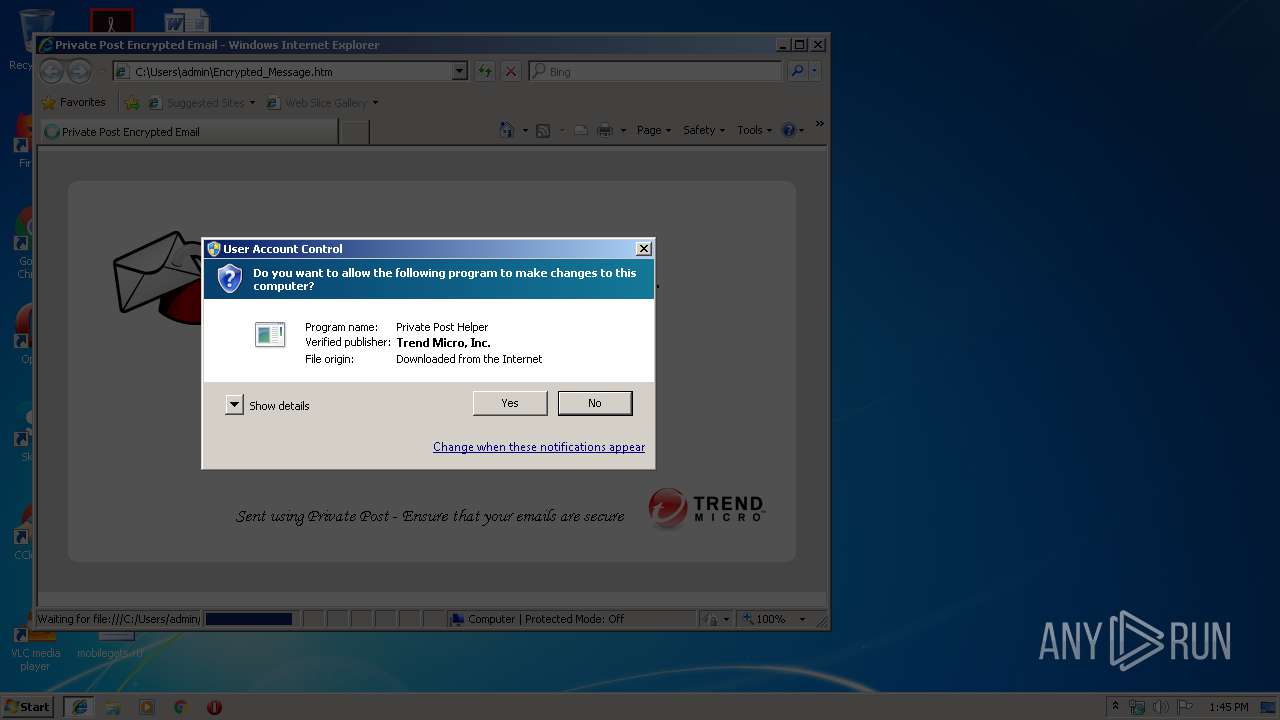
MALICIOUS
Changes settings of System certificates
- IEInstal.exe (PID: 3272)
Loads dropped or rewritten executable
- iexplore.exe (PID: 3476)
- IEInstal.exe (PID: 3272)
SUSPICIOUS
Creates COM task schedule object
- IEInstal.exe (PID: 3272)
Removes files from Windows directory
- IEInstal.exe (PID: 3272)
Creates files in the Windows directory
- IEInstal.exe (PID: 3272)
Executable content was dropped or overwritten
- IEInstal.exe (PID: 3272)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2992)
Reads internet explorer settings
- iexplore.exe (PID: 3476)
- iexplore.exe (PID: 2440)
Application launched itself
- iexplore.exe (PID: 2992)
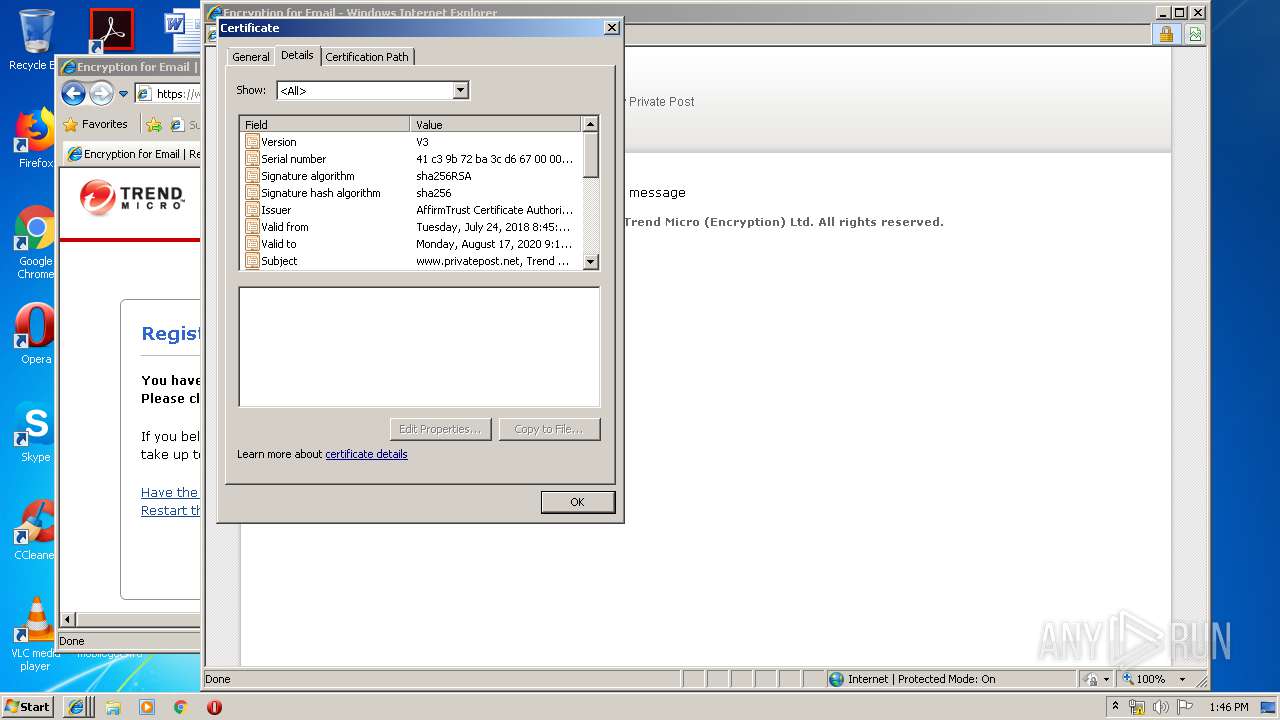
Reads settings of System Certificates
- iexplore.exe (PID: 3476)
- iexplore.exe (PID: 2992)
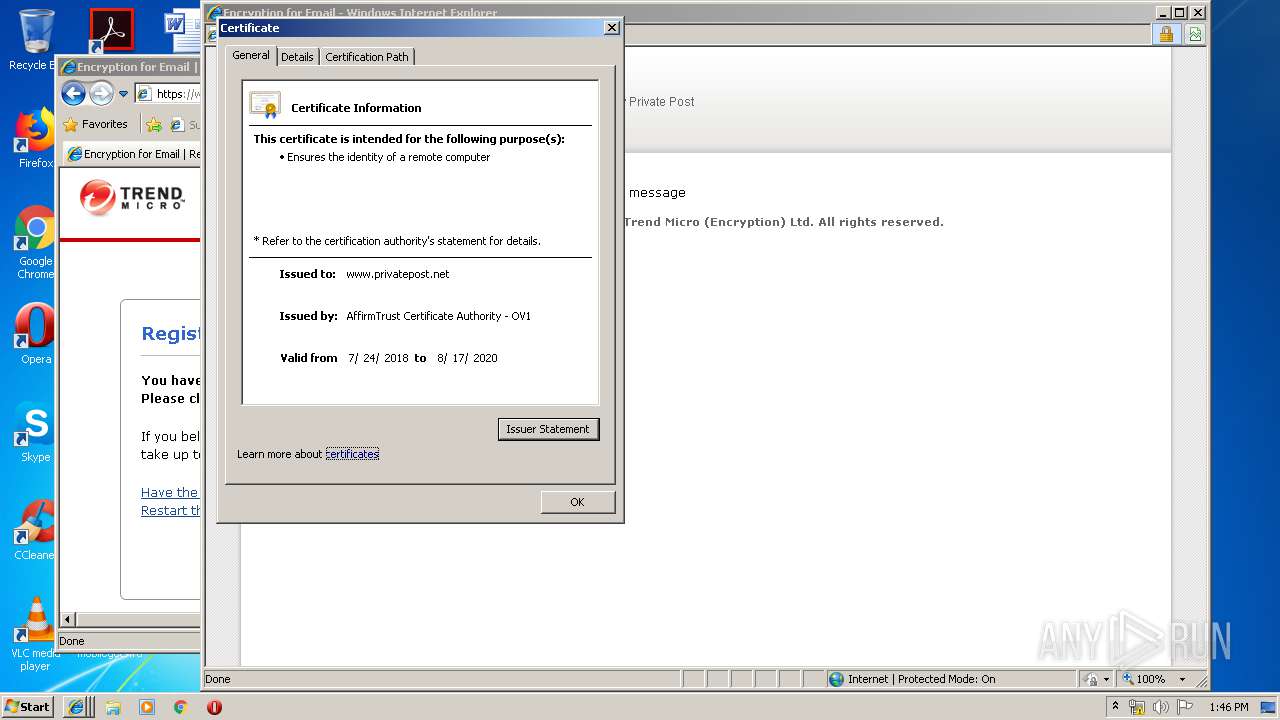
Adds / modifies Windows certificates
- iexplore.exe (PID: 3476)
- iexplore.exe (PID: 2992)
Reads Internet Cache Settings
- iexplore.exe (PID: 2992)
- iexplore.exe (PID: 3476)
- iexplore.exe (PID: 2440)
Creates files in the user directory
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 2992)
Changes settings of System certificates
- iexplore.exe (PID: 2992)
- iexplore.exe (PID: 3476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|---|
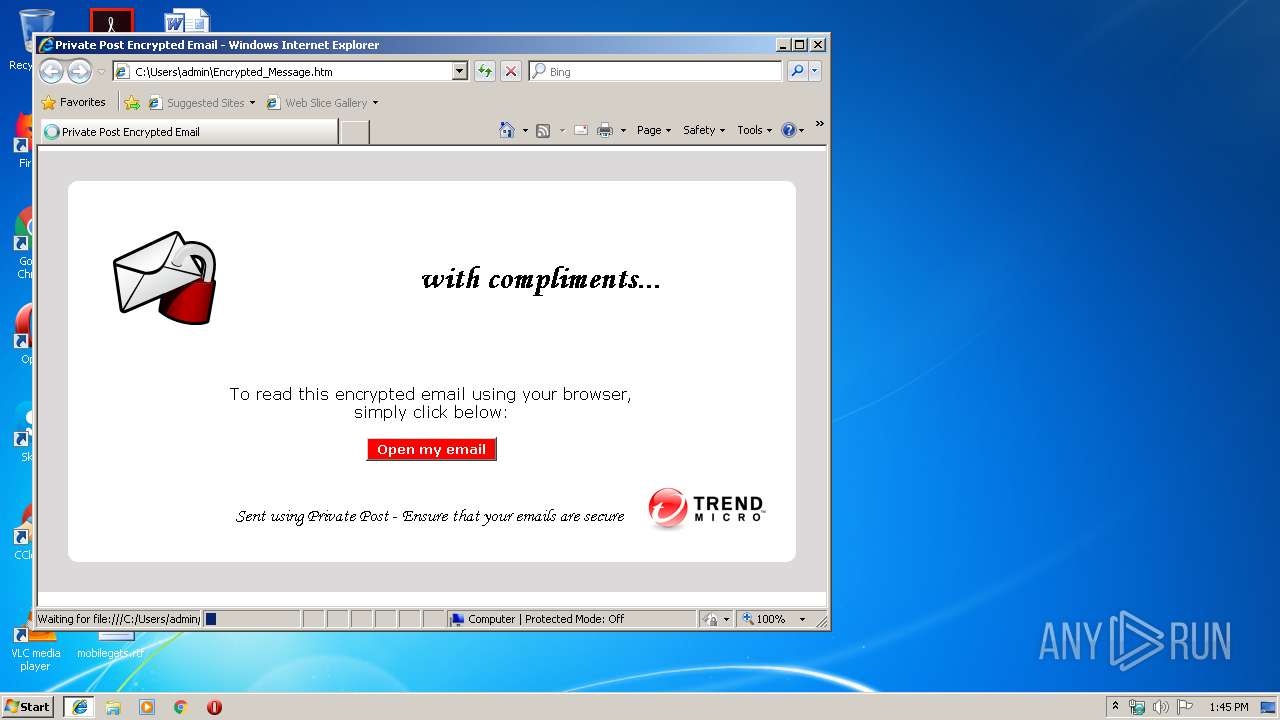
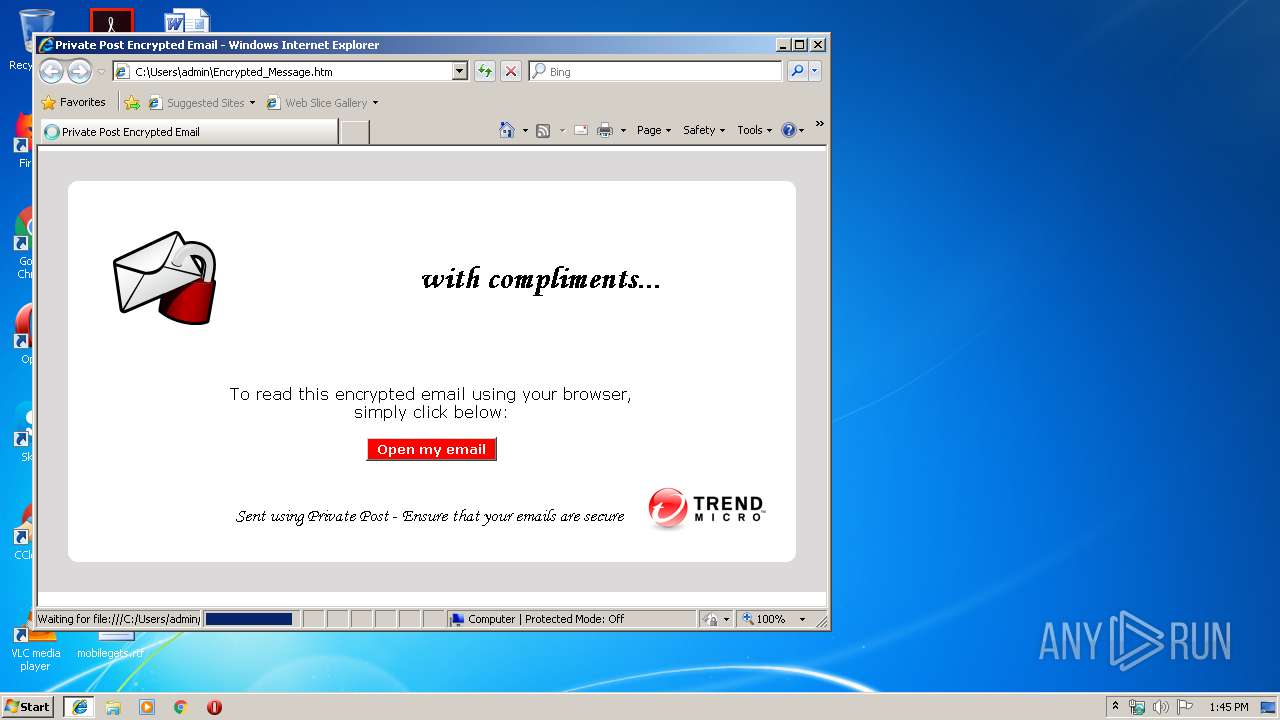
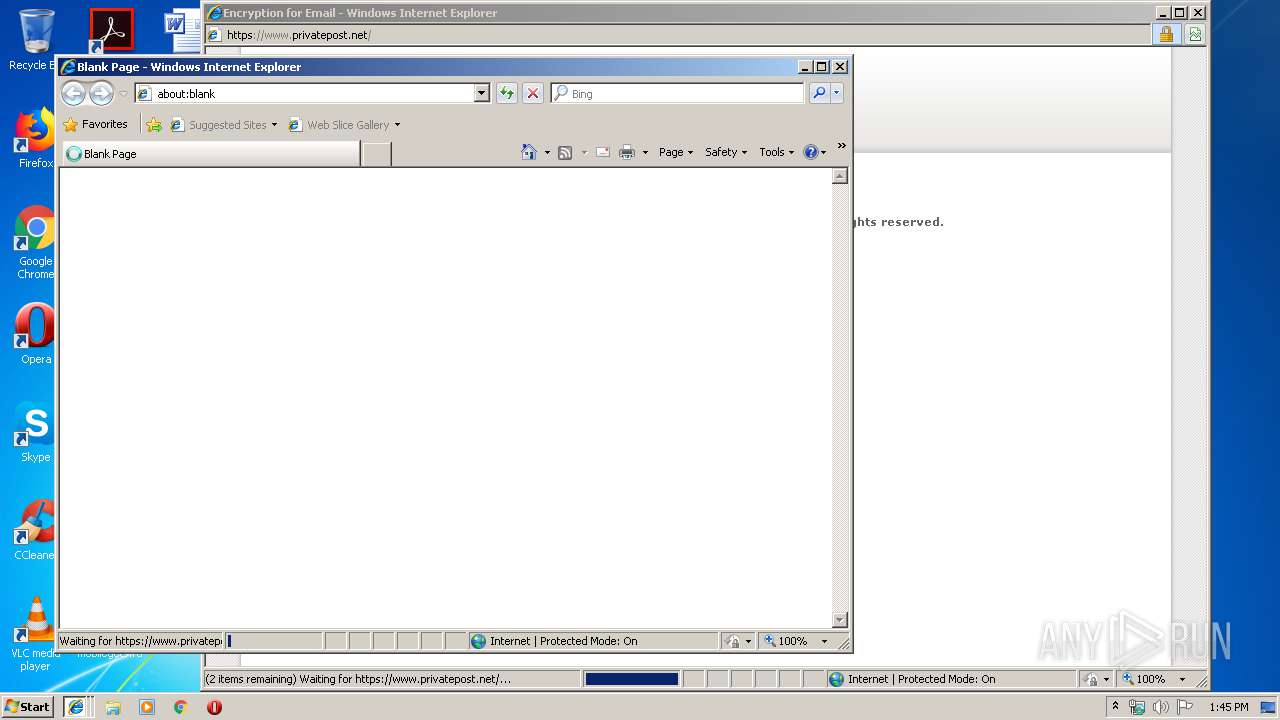
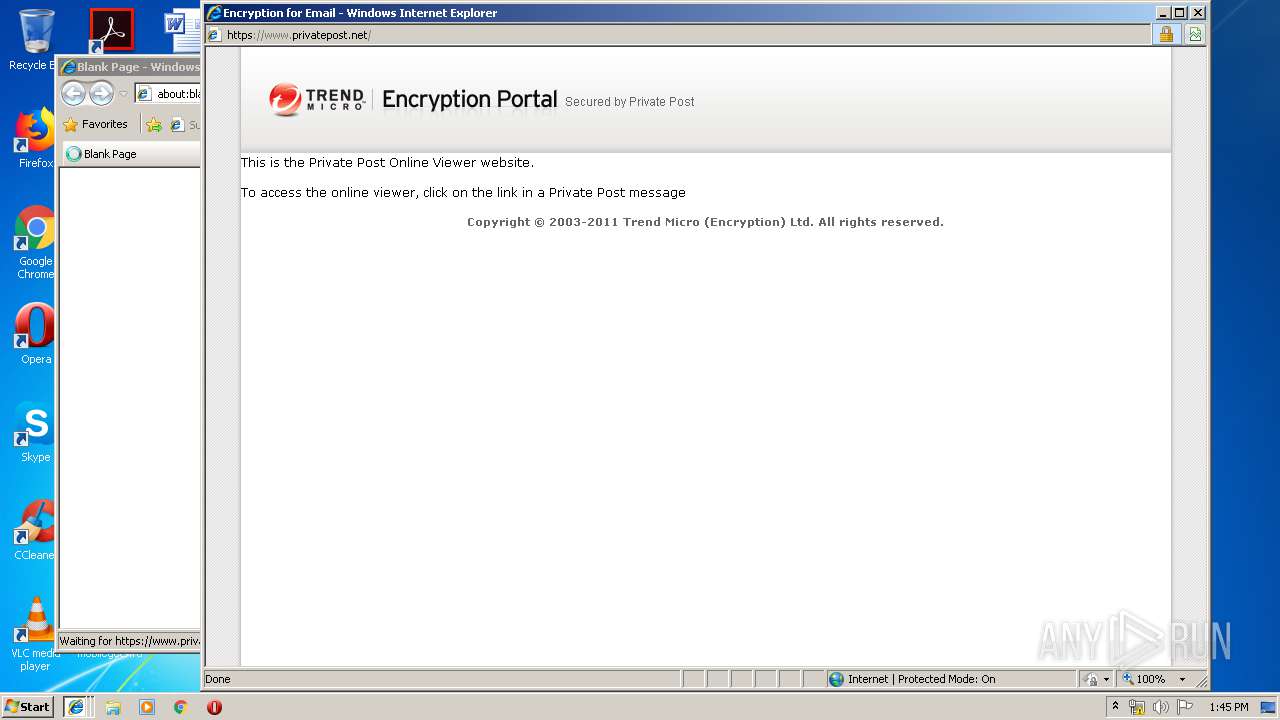
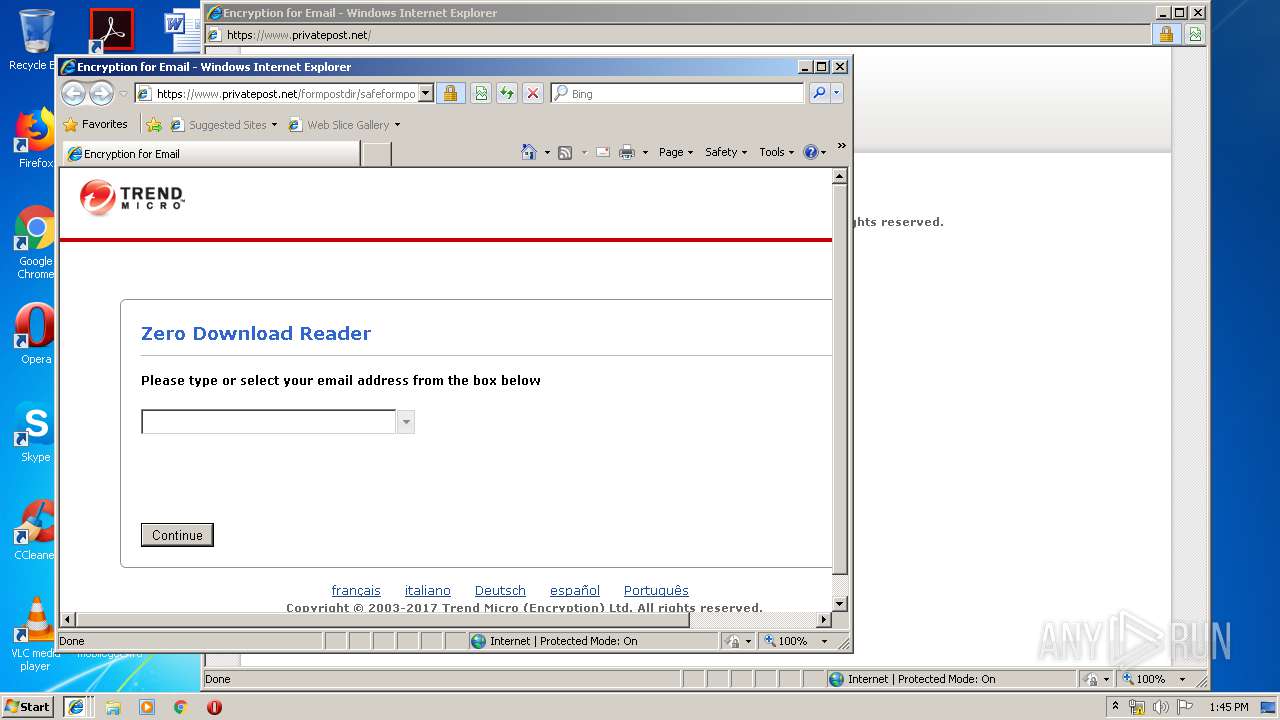
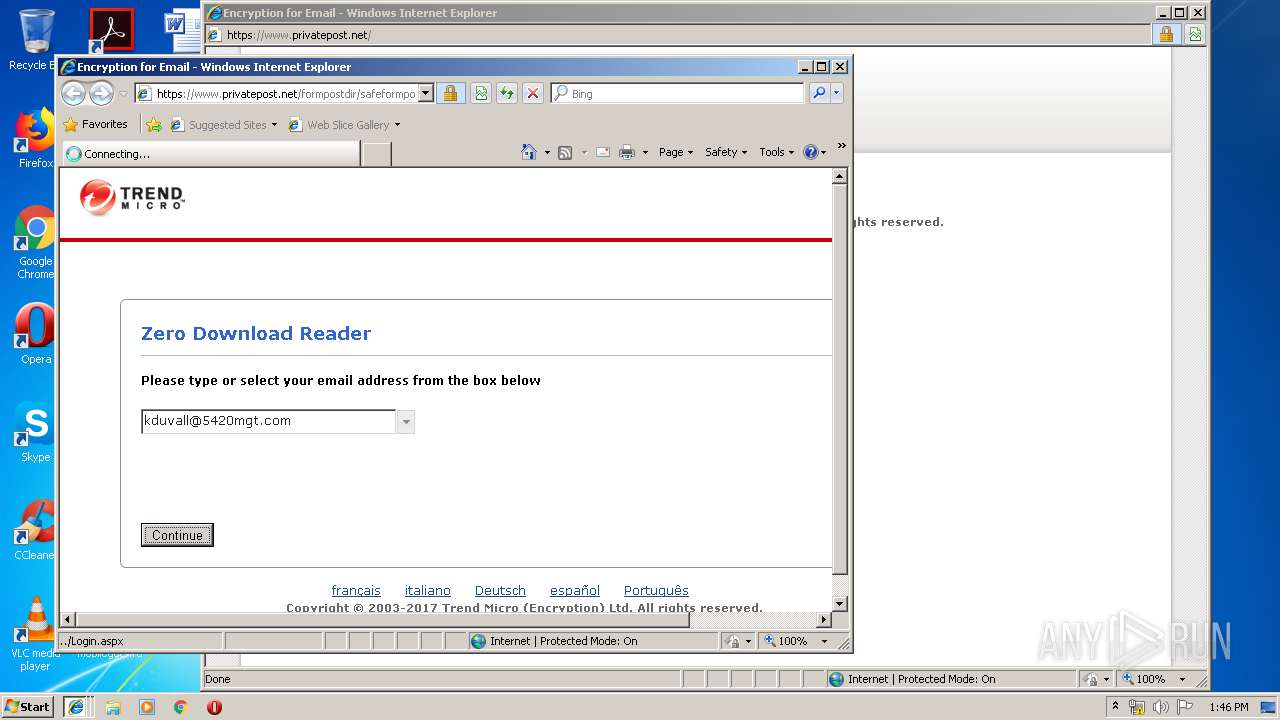
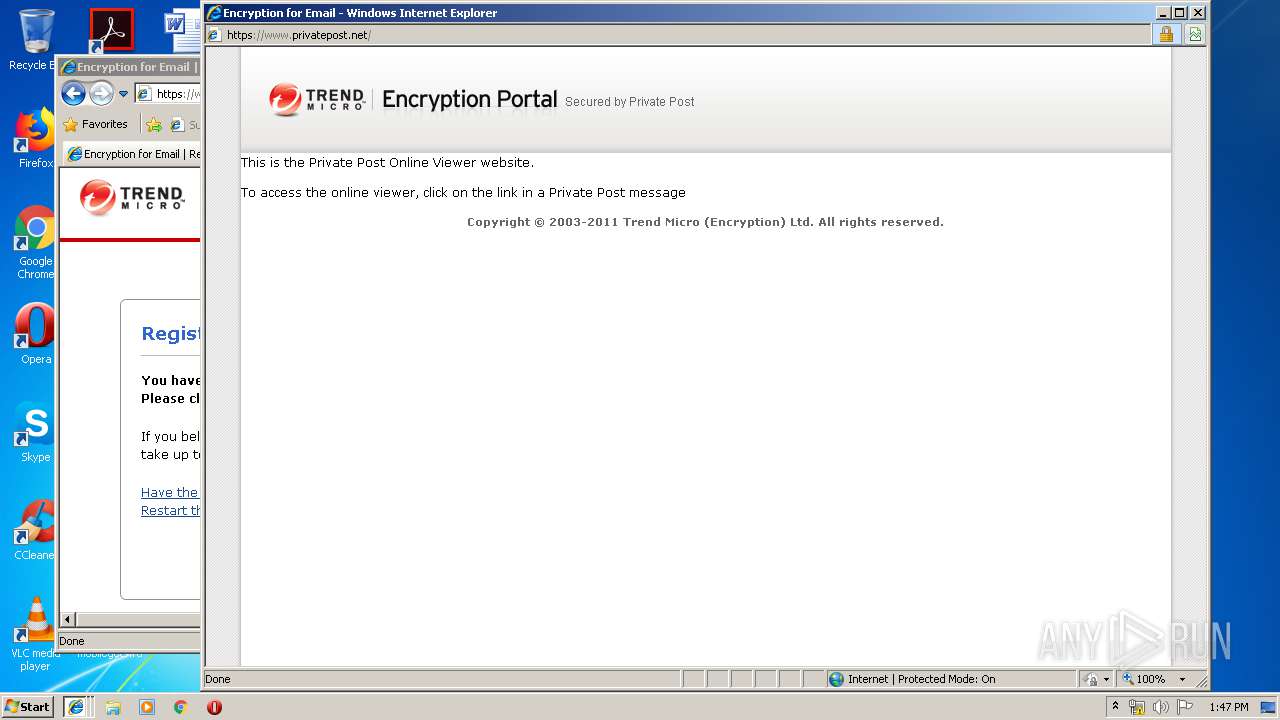
| Title: | Private Post Encrypted Email |
| ibeZDVersion: | 3 |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2992 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Encrypted_Message.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Internet Explorer\IEInstal.exe" -Embedding | C:\Program Files\Internet Explorer\IEInstal.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Add-on Installer Exit code: 2147942402 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3476 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2992 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 089
Read events
817
Write events
262
Delete events
10
Modification events
| (PID) Process: | (2992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2992) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {9C42C9FD-65C5-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070400020017000C002D000300EA00 | |||
Executable files
8
Suspicious files
20
Text files
144
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2992 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab840.tmp | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab842.tmp | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab843.tmp | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab844.tmp | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab845.tmp | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab846.tmp | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar847.tmp | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar848.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
36
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
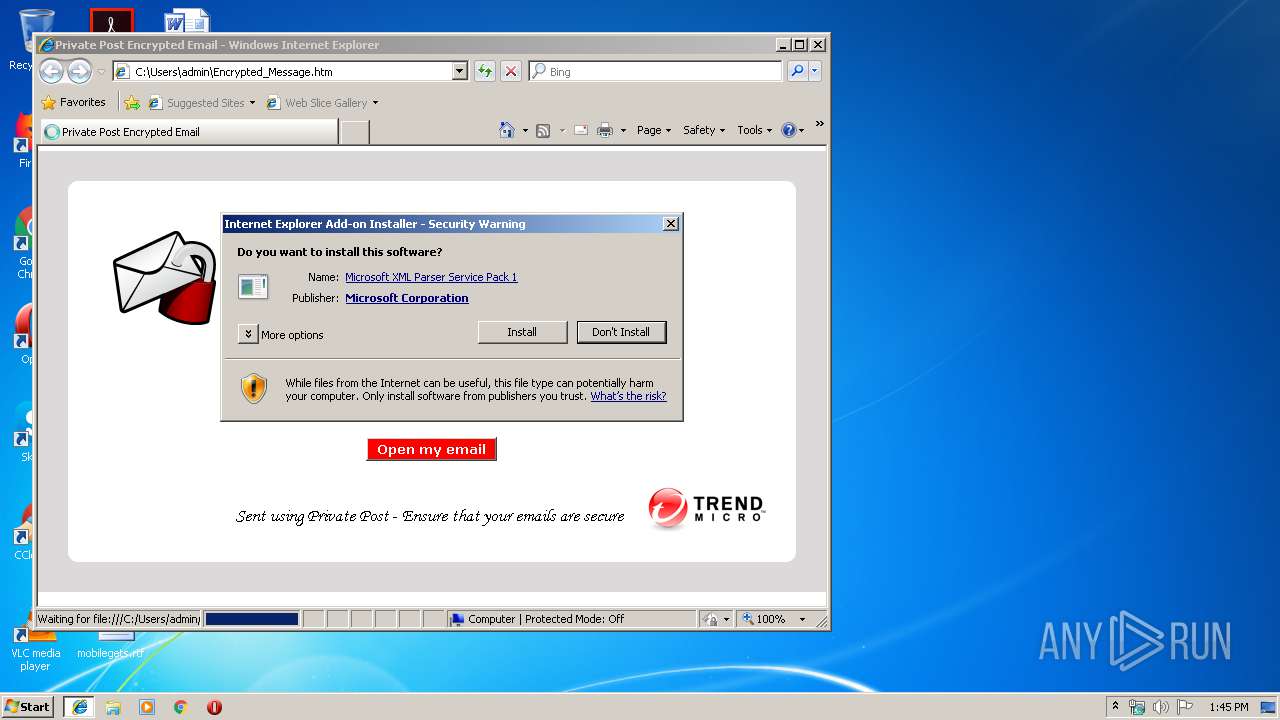
3476 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
3476 | iexplore.exe | GET | 200 | 213.129.92.227:80 | http://downloads.privatepost.com/files/ppZDHelper/ppZDHelper.cab | GB | compressed | 389 Kb | suspicious |
3476 | iexplore.exe | GET | 200 | 213.129.92.227:80 | http://downloads.privatepost.com/files/ppZDHelper/msxml3.cab | GB | compressed | 550 Kb | suspicious |
3476 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/F9B5B632455F9CBEEC575F80DCE96E2CC7B278B7.crt | US | der | 848 b | whitelisted |
3476 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/F9B5B632455F9CBEEC575F80DCE96E2CC7B278B7.crt | US | der | 848 b | whitelisted |
2992 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3476 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
3476 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
3476 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/F9B5B632455F9CBEEC575F80DCE96E2CC7B278B7.crt | US | der | 848 b | whitelisted |
3476 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/F9B5B632455F9CBEEC575F80DCE96E2CC7B278B7.crt | US | der | 848 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
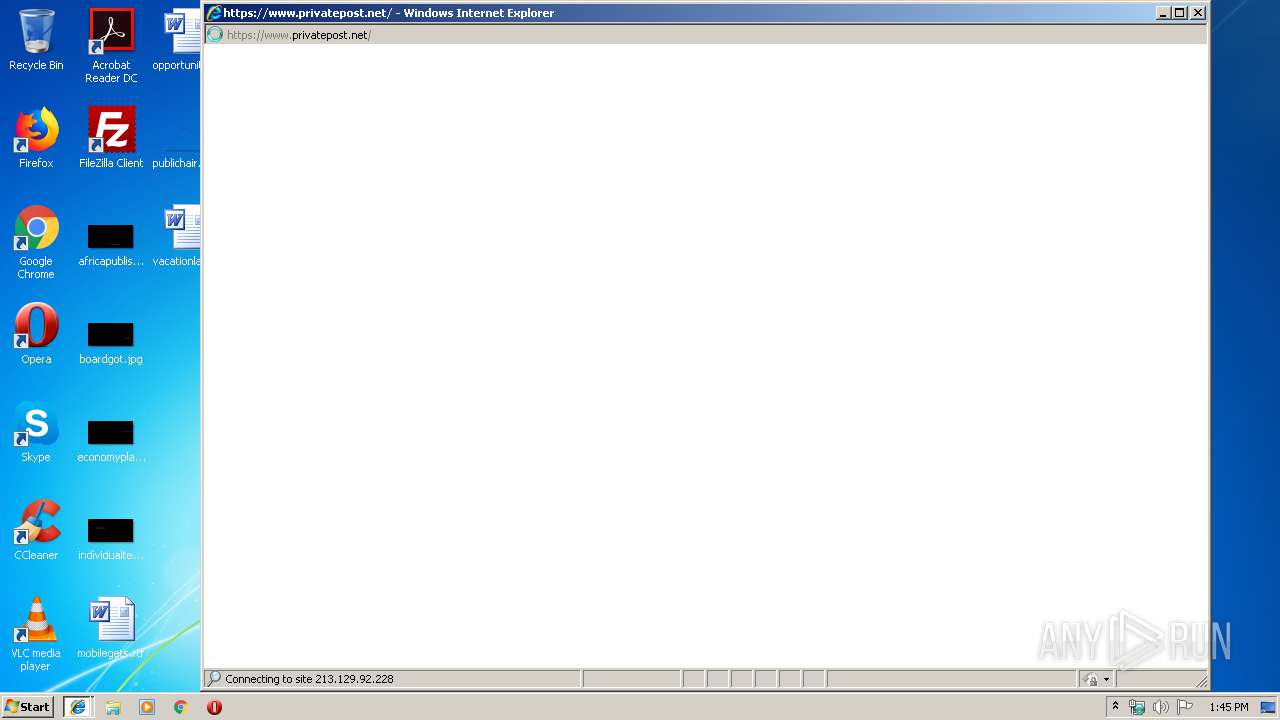
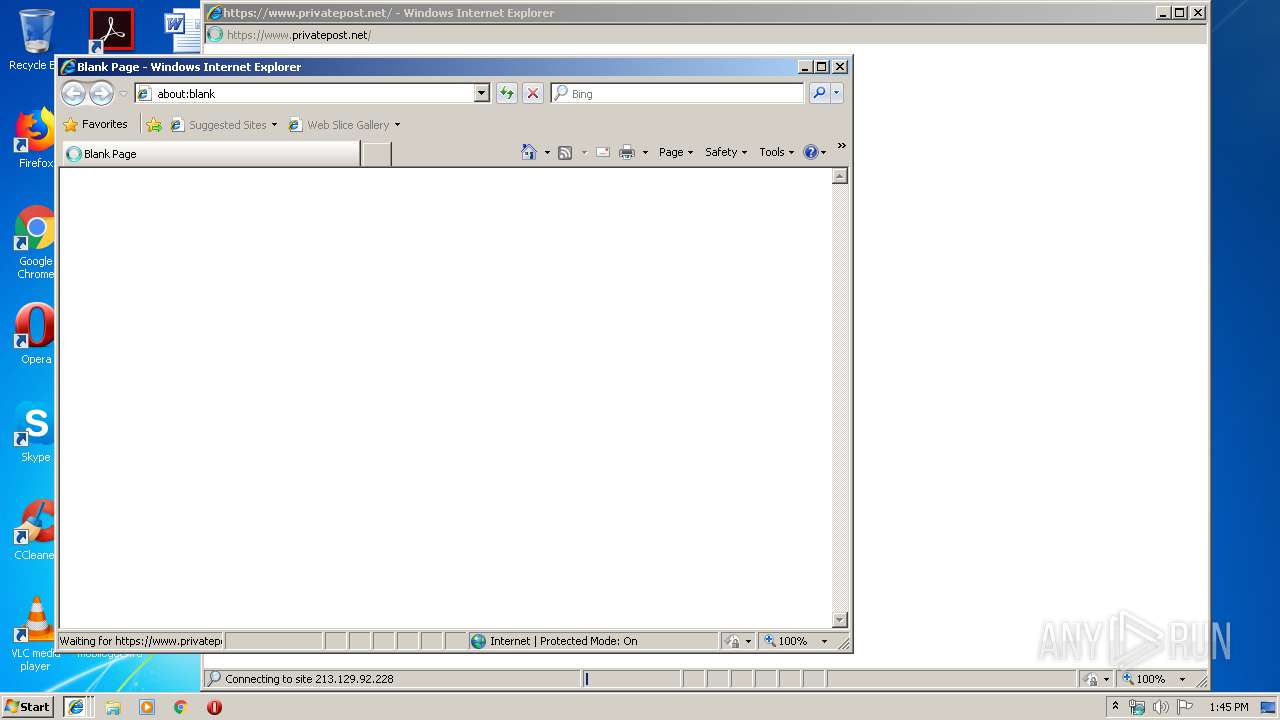
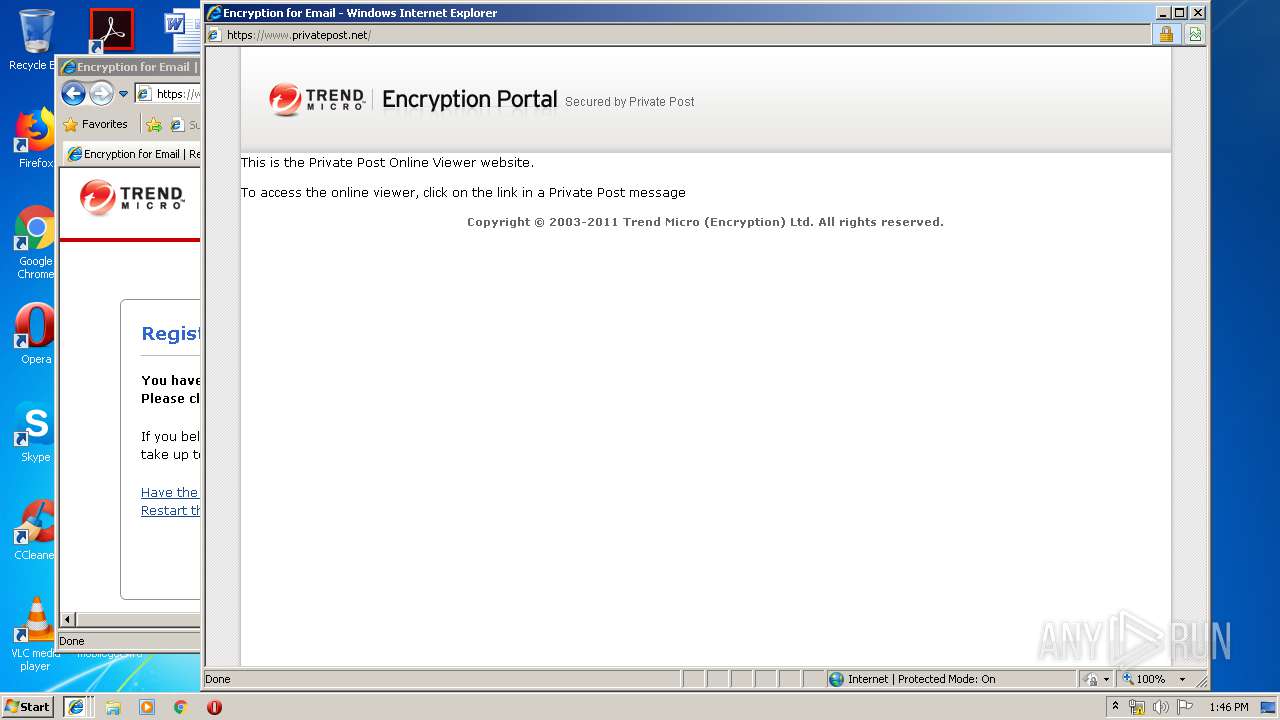
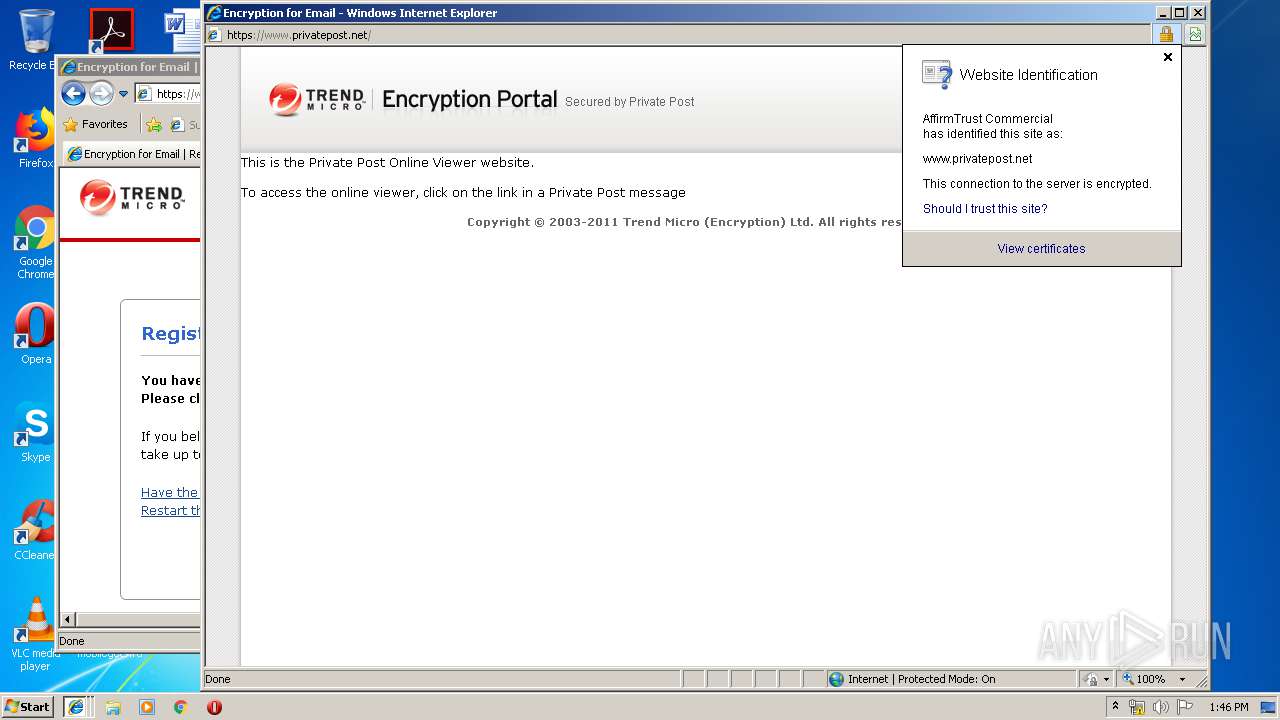
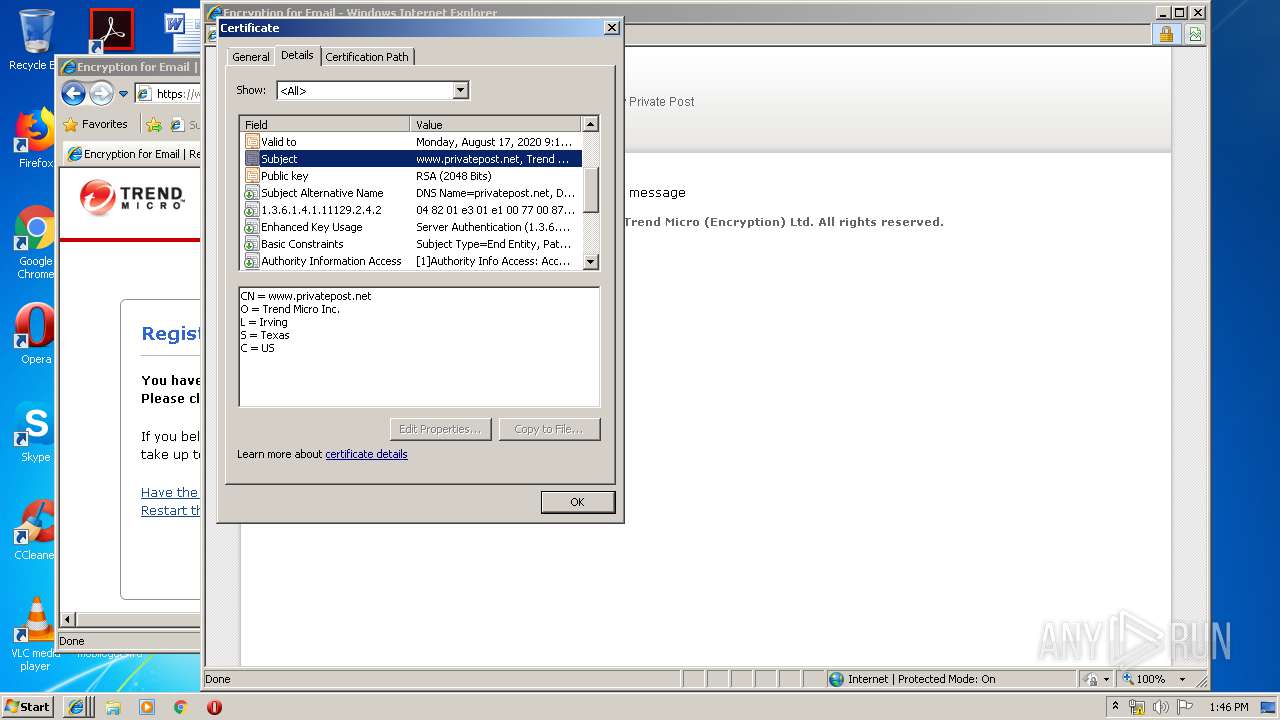
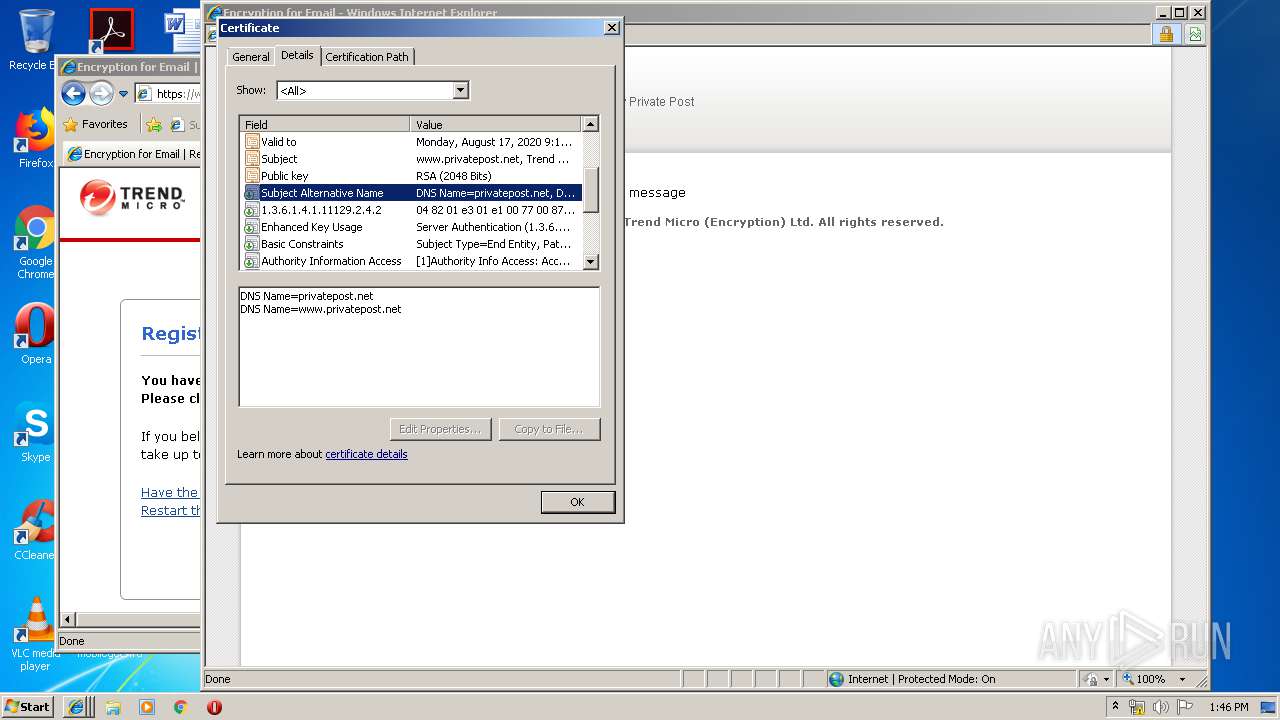
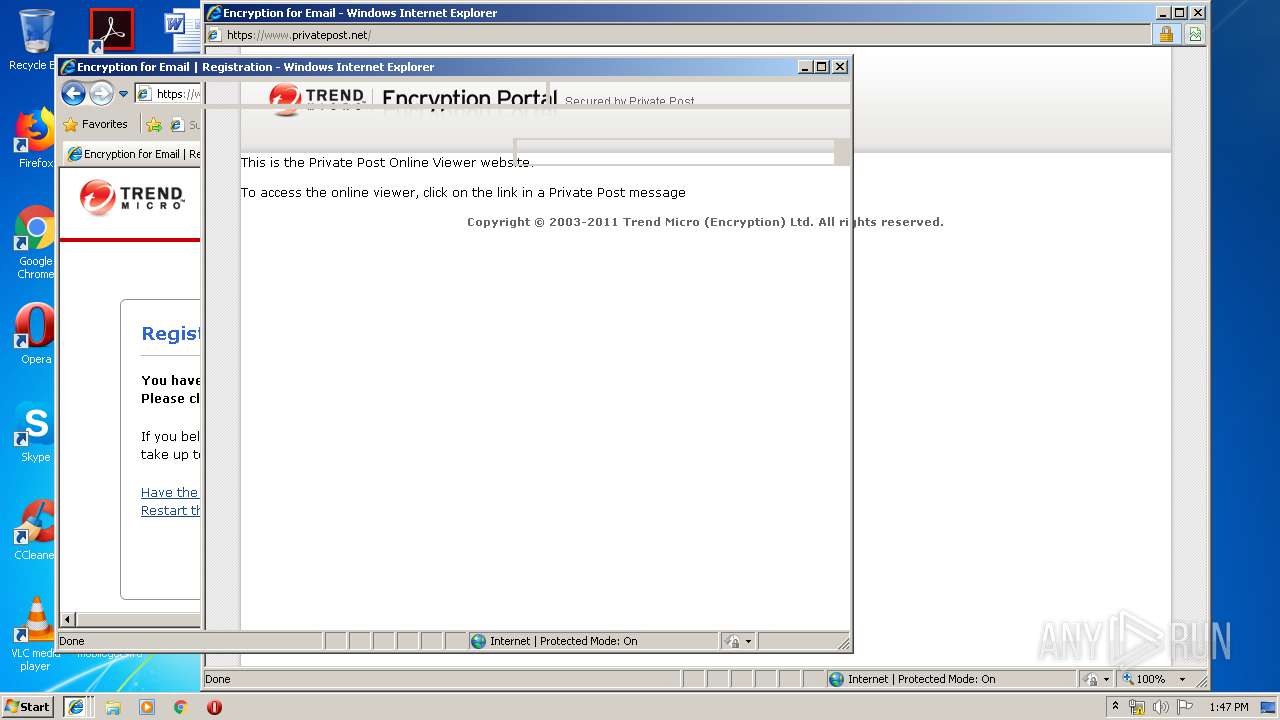
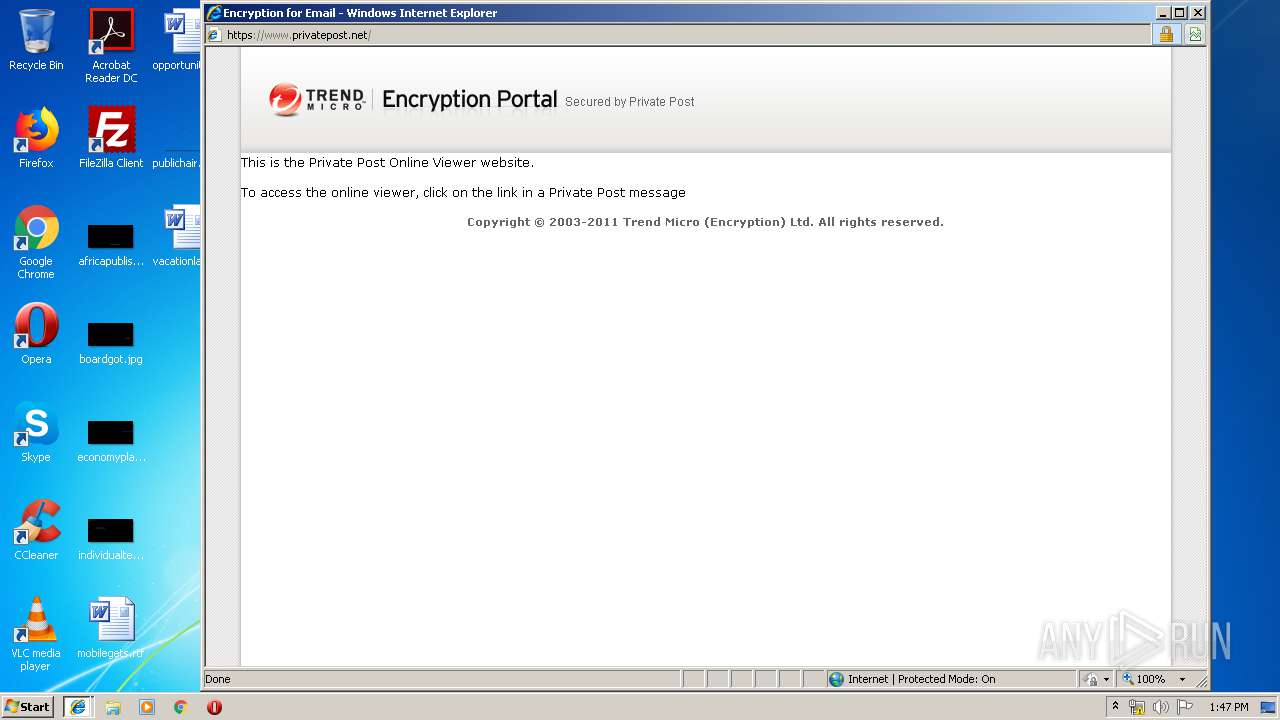
2992 | iexplore.exe | 213.129.92.228:443 | www.privatepost.net | The Bunker Secure Hosting Ltd | GB | unknown |
3476 | iexplore.exe | 213.129.92.228:443 | www.privatepost.net | The Bunker Secure Hosting Ltd | GB | unknown |
2992 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
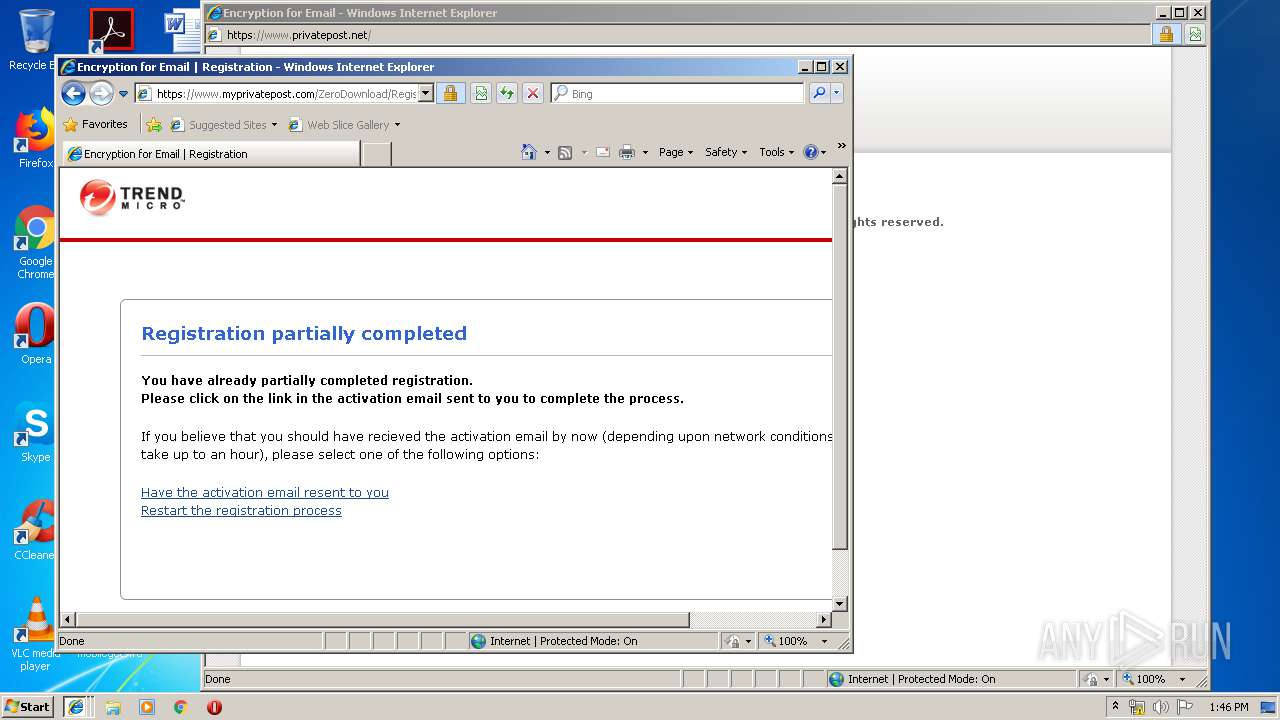
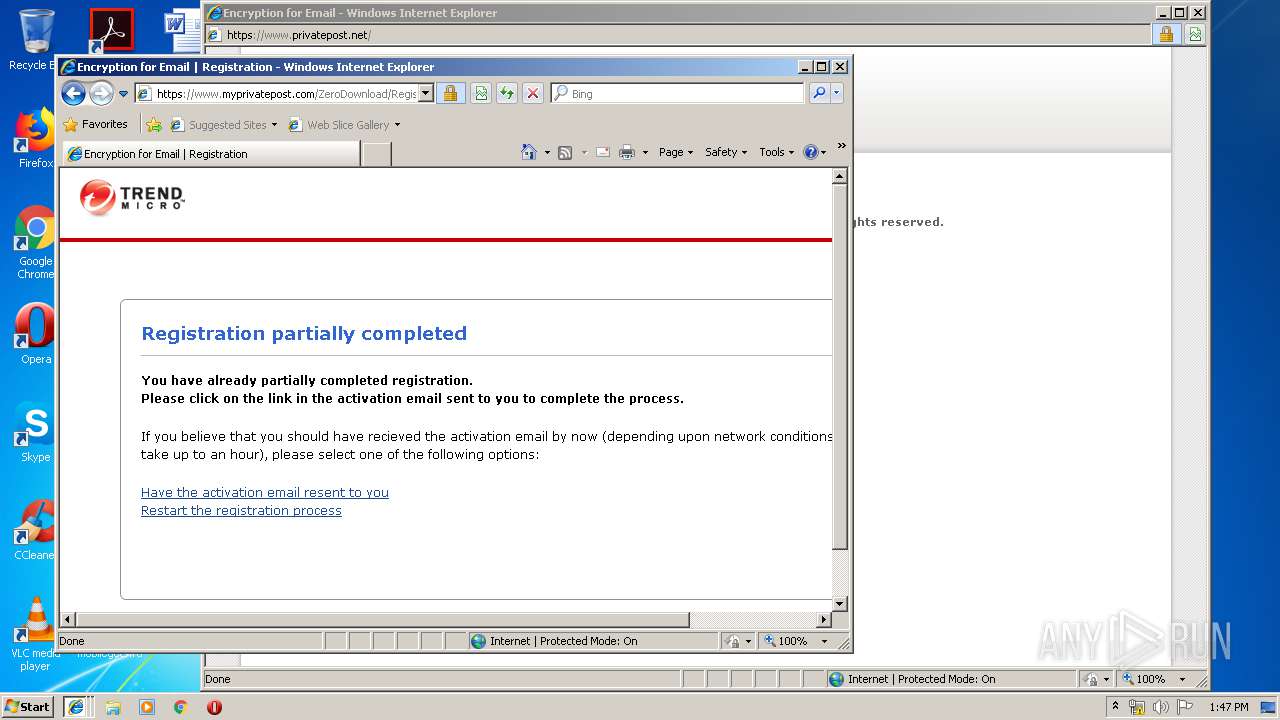
2992 | iexplore.exe | 150.70.226.87:443 | www.myprivatepost.com | TREND MICRO INCORPORATED | JP | unknown |
3476 | iexplore.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
2440 | iexplore.exe | 150.70.226.87:443 | www.myprivatepost.com | TREND MICRO INCORPORATED | JP | unknown |
— | — | 213.129.92.228:443 | www.privatepost.net | The Bunker Secure Hosting Ltd | GB | unknown |
3476 | iexplore.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3476 | iexplore.exe | 213.129.92.227:80 | downloads.privatepost.com | The Bunker Secure Hosting Ltd | GB | unknown |
2440 | iexplore.exe | 213.129.92.228:443 | www.privatepost.net | The Bunker Secure Hosting Ltd | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.privatepost.net |
| suspicious |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
downloads.privatepost.com |
| unknown |
www.myprivatepost.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3476 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |