| File name: | Silverlight.exe |
| Full analysis: | https://app.any.run/tasks/2959a85e-d65e-4ff5-b90f-9bcab3583055 |
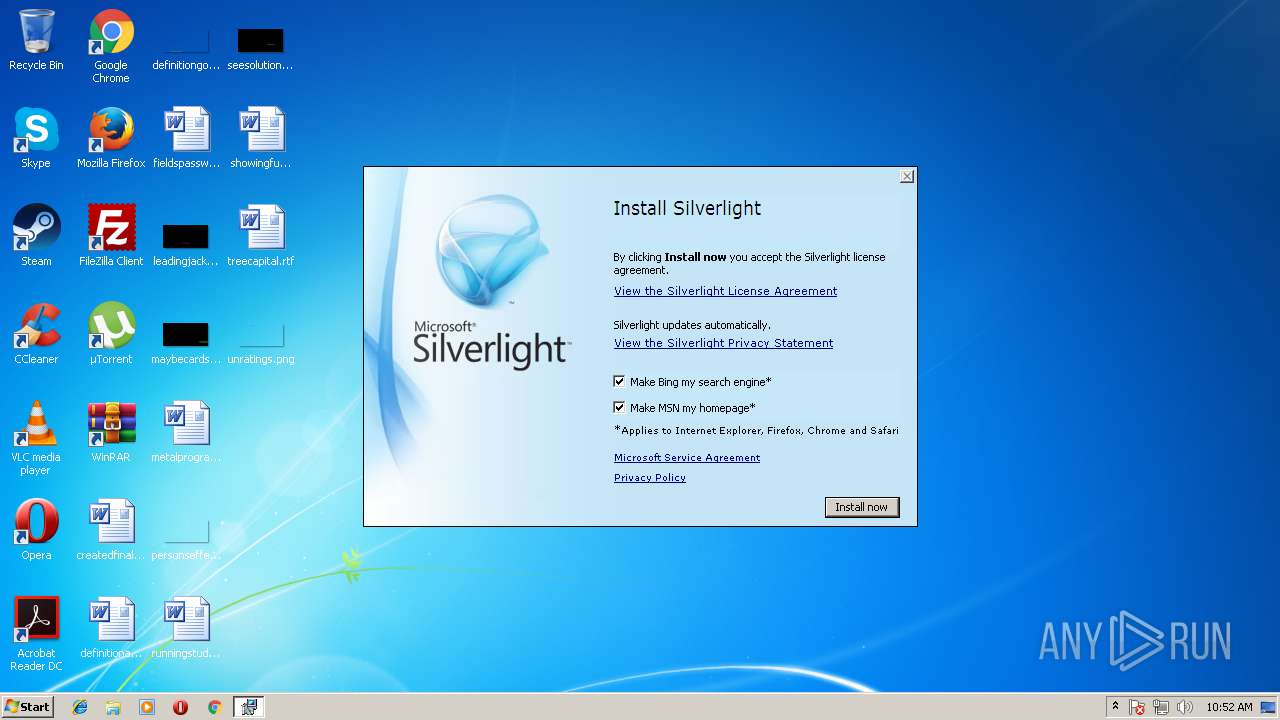
| Verdict: | Suspicious activity |
| Analysis date: | August 10, 2018, 09:52:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D83B8AE32EB0D6C8DF1D5BD9A2953702 |
| SHA1: | E7478F9995AC6F9309034A85D78E1C61ABA5A29F |
| SHA256: | 88E1B76BDF799478A72FA27DB0BFE7BC5D02CC7E53675967399300448F0E266F |
| SSDEEP: | 196608:Ohg7Fxdtk3wntS+kBDQwIlvJg46oI5Z5T38aRGn4pimiAvr:Oh8x7kAt8QLzCzhT38agndAT |
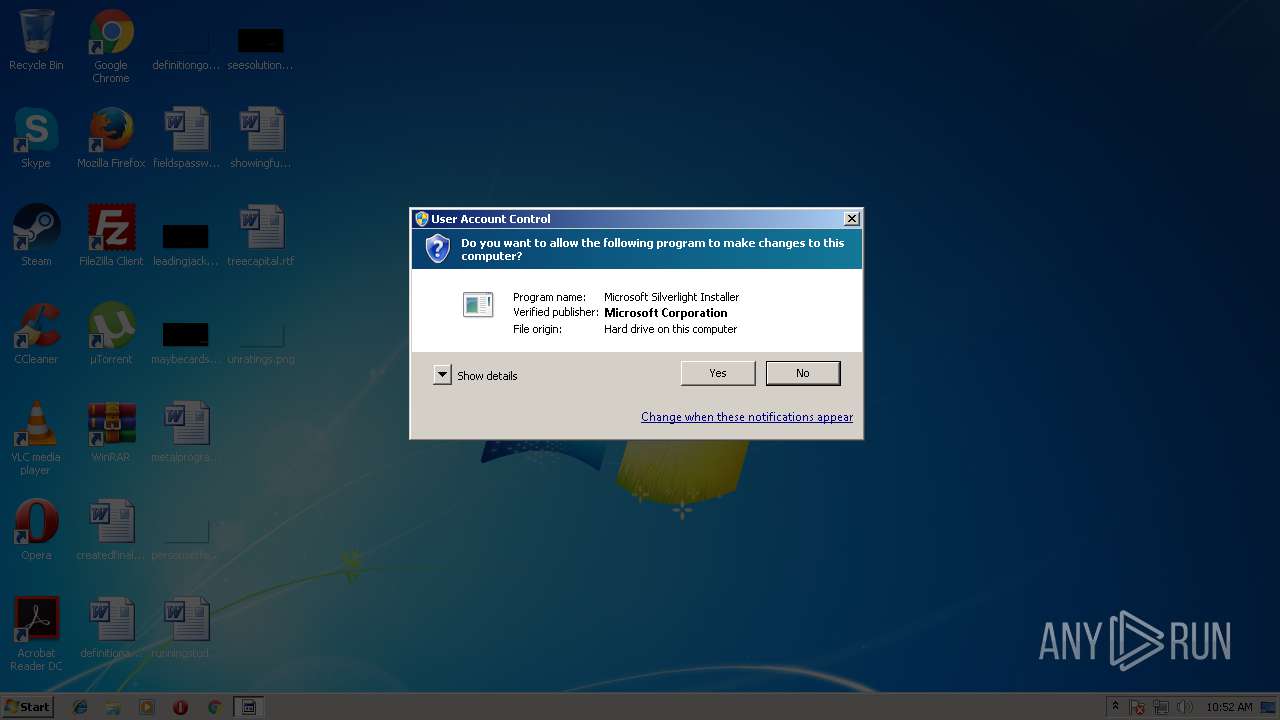
MALICIOUS
Application was dropped or rewritten from another process
- install.exe (PID: 3872)
- install.exe (PID: 340)
Loads dropped or rewritten executable
- install.exe (PID: 340)
SUSPICIOUS
Executable content was dropped or overwritten
- Silverlight.exe (PID: 3236)
INFO
Dropped object may contain URL's
- Silverlight.exe (PID: 3236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:06:25 02:14:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 30720 |
| InitializedDataSize: | 3072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5892 |
| OSVersion: | 5.2 |
| ImageVersion: | 5.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.50907.0 |
| ProductVersionNumber: | 5.5.31.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Self-Extracting Cabinet |
| FileVersion: | 5.1.50907.0 |
| InternalName: | SFXCAB.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | SFXCAB.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 5.5.0031.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jun-2004 00:14:00 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Self-Extracting Cabinet |
| FileVersion: | 5.1.50907.0 |
| InternalName: | SFXCAB.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | SFXCAB.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 5.5.0031.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Jun-2004 00:14:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00007760 | 0x00007800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60212 |
.data | 0x0000A000 | 0x000110D4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.513491 |
.rsrc | 0x0001C000 | 0x000009B0 | 0x006A8000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99994 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.20123 | 960 | Latin 1 / Western European | English - United States | RT_VERSION |
100 | 3.0946 | 282 | Latin 1 / Western European | English - United States | RT_DIALOG |
107 | 2.9591 | 224 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
ntdll.dll |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
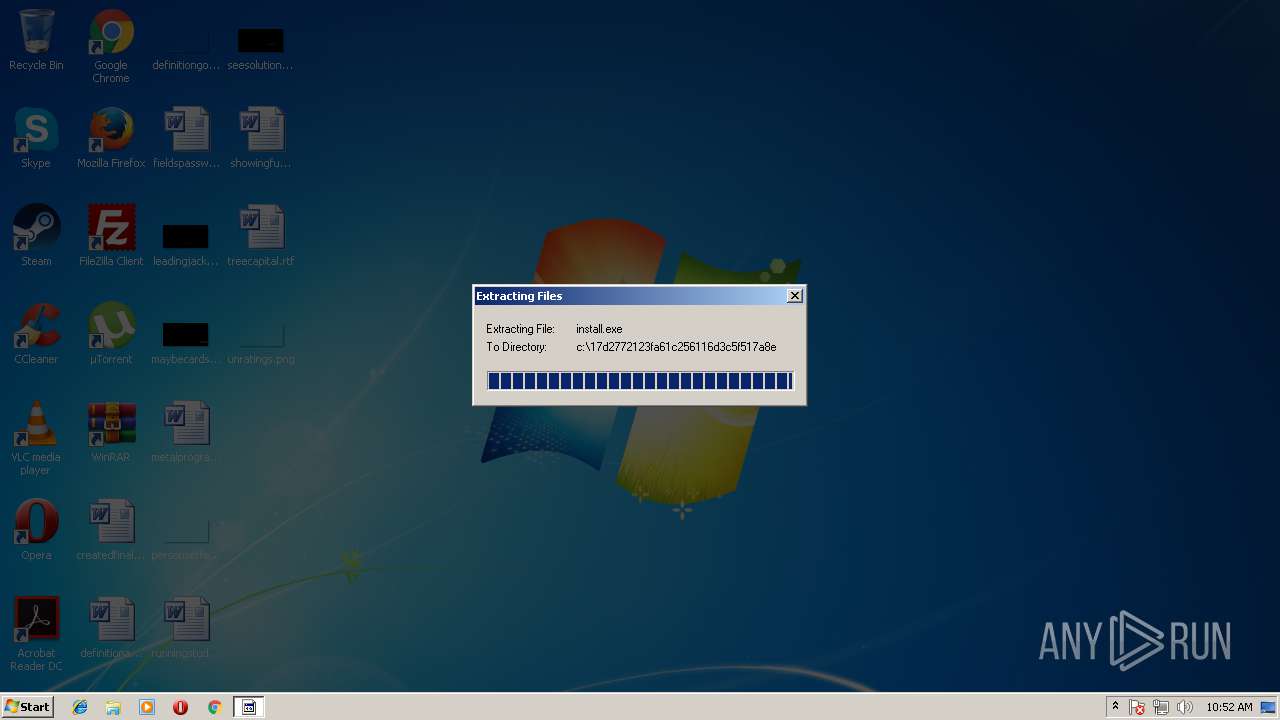
| 340 | c:\17d2772123fa61c256116d3c5f517a8e\install.exe | c:\17d2772123fa61c256116d3c5f517a8e\install.exe | Silverlight.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: External Installer Exit code: 0 Version: VER_DOTPRODUCTVERSION Modules
| |||||||||||||||
| 3236 | "C:\Users\admin\AppData\Local\Temp\Silverlight.exe" | C:\Users\admin\AppData\Local\Temp\Silverlight.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Self-Extracting Cabinet Exit code: 0 Version: 5.1.50907.0 Modules
| |||||||||||||||
| 3872 | c:\17d2772123fa61c256116d3c5f517a8e\install.exe | c:\17d2772123fa61c256116d3c5f517a8e\install.exe | — | Silverlight.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: External Installer Exit code: 3221226540 Version: VER_DOTPRODUCTVERSION Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
4
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3236 | Silverlight.exe | C:\17d2772123fa61c256116d3c5f517a8e\silverlight.7z | — | |
MD5:— | SHA256:— | |||
| 3236 | Silverlight.exe | C:\17d2772123fa61c256116d3c5f517a8e\$shtdwn$.req | — | |
MD5:— | SHA256:— | |||
| 340 | install.exe | C:\Users\admin\AppData\Local\Temp\Silverlight0.log | txt | |
MD5:— | SHA256:— | |||
| 3236 | Silverlight.exe | C:\17d2772123fa61c256116d3c5f517a8e\install.res.dll | executable | |
MD5:21E387428342410E09EDA281ED8028EB | SHA256:405FAA3BD84FCA09F21DBD854A0EE75493DEDDD5BF56421FE6B05B2285352201 | |||
| 3236 | Silverlight.exe | C:\17d2772123fa61c256116d3c5f517a8e\silverlight.msi | executable | |
MD5:A65CB3800519735631408256E7B4DE9B | SHA256:A022D0447F13546827B47AFF83D246A52438D46C72B28A38E37DEED5D85BC8BE | |||
| 3236 | Silverlight.exe | C:\17d2772123fa61c256116d3c5f517a8e\microsoft_defaults.exe | executable | |
MD5:64CADAEF6DCF7B6A6171FC1A2BEE94A1 | SHA256:5720BD8E18456D0B96CD4BDBB715C2217A1EE30609DD05C195895874105A557C | |||
| 3236 | Silverlight.exe | C:\17d2772123fa61c256116d3c5f517a8e\install.exe | executable | |
MD5:6D09793299832D9BFE4458E4A4B8BA0A | SHA256:6DBDF0F7E9377CE3D89EC865442A2E5C1261DECAE4A2196E55235BB3FD5D3D35 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report