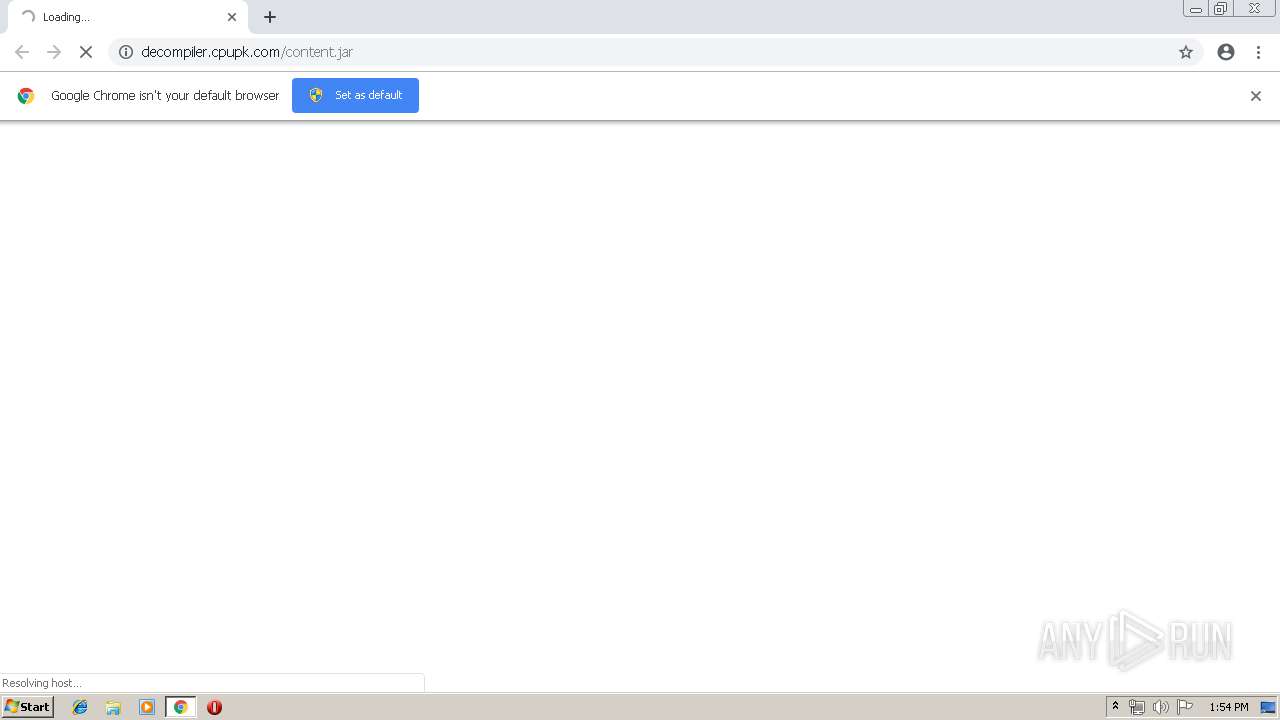
| URL: | http://decompiler.cpupk.com/content.jar |
| Full analysis: | https://app.any.run/tasks/a21a8749-4762-4901-80cc-6dce244dd439 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 12:53:52 |
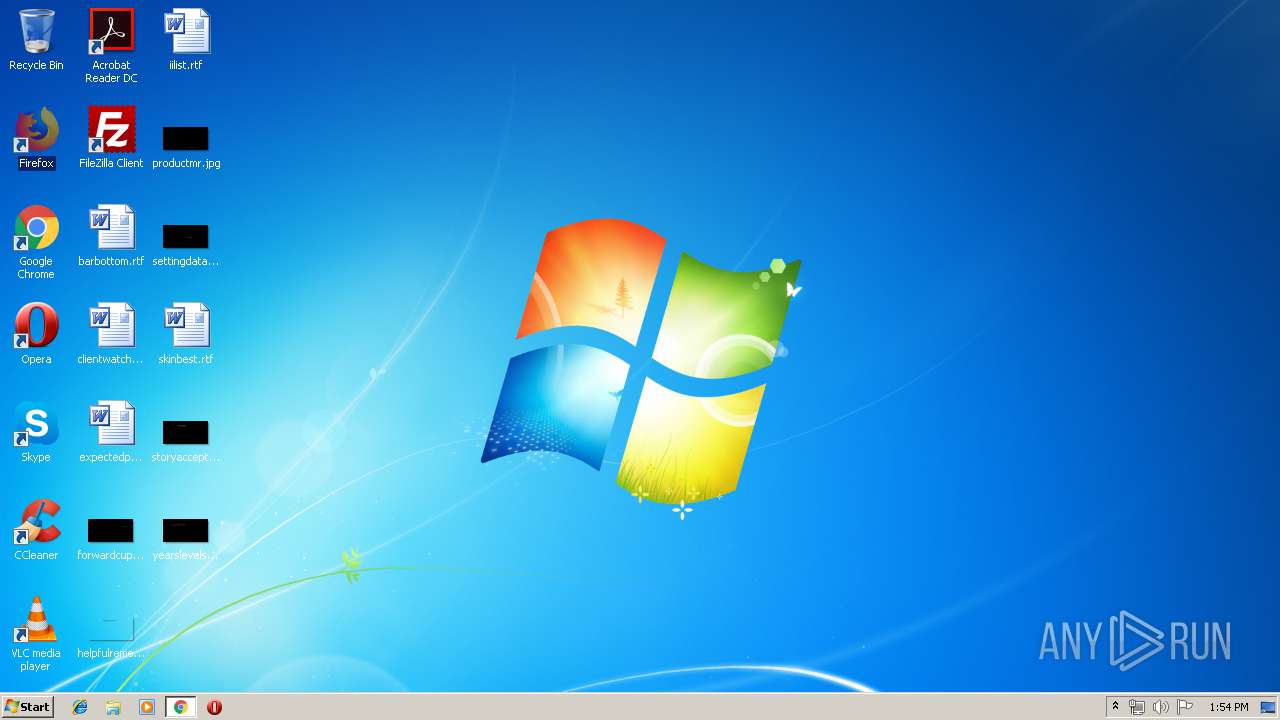
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DAD1A2D20EEF3EC9F1AA90113329C54D |
| SHA1: | 88E3D545ADE9362D311BEC60302BEB469C8F1550 |
| SHA256: | 88DCAB9828A0968536BB11392036CD23C2AF752C09803EE8F942088C654B840F |
| SSDEEP: | 3:N1KaAGL3FTKdL8tP+:CajJquG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3044)
INFO
Application launched itself
- chrome.exe (PID: 3044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa60f18,0x6fa60f28,0x6fa60f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10814552814063981347 --mojo-platform-channel-handle=3220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18093374258155831192 --mojo-platform-channel-handle=3472 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=243488669087036809 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=243488669087036809 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5886352957994645551 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5886352957994645551 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10404833976663561836 --mojo-platform-channel-handle=3328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14585021511065589160 --mojo-platform-channel-handle=1516 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --service-pipe-token=4658536170051861043 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4658536170051861043 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10529791781094596685 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10529791781094596685 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8264601097220516804 --mojo-platform-channel-handle=3104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
580
Read events
476
Write events
99
Delete events
5
Modification events
| (PID) Process: | (3300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3044-13199806446782375 |
Value: 259 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
86
Text files
148
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f8d65f94-9459-4954-b1dc-1e2e90f627da.tmp | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
53
DNS requests
39
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
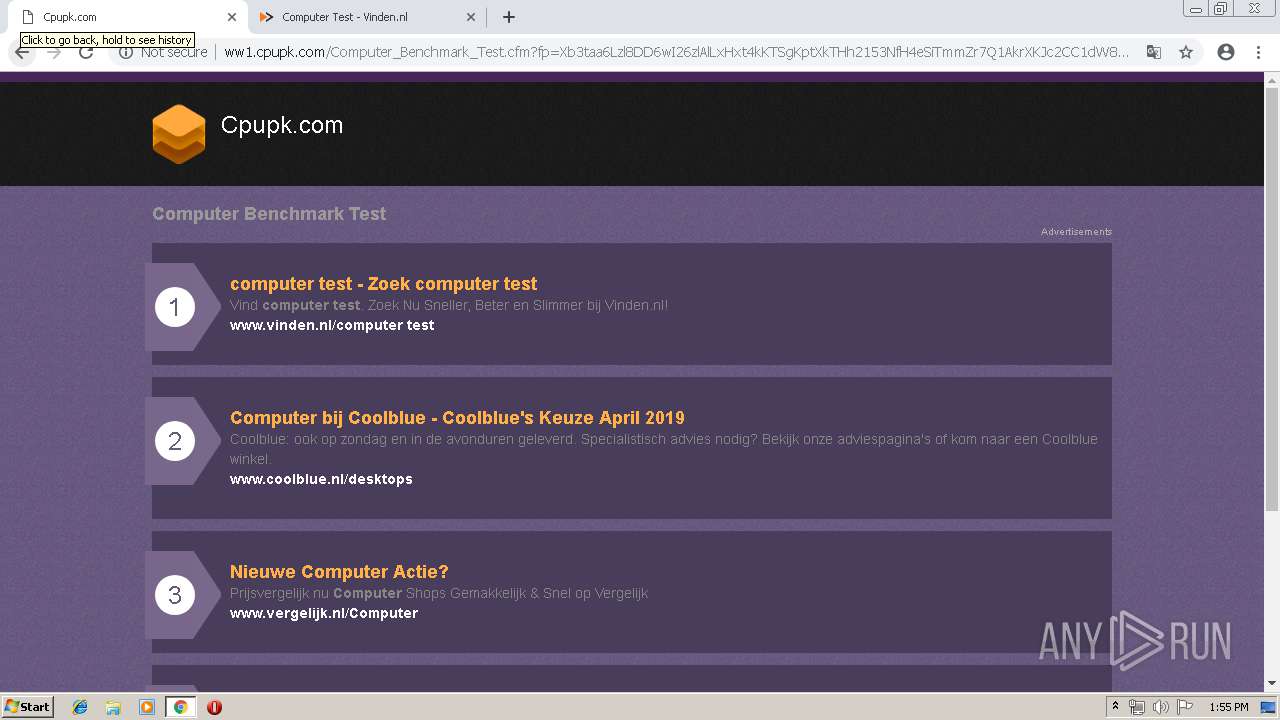
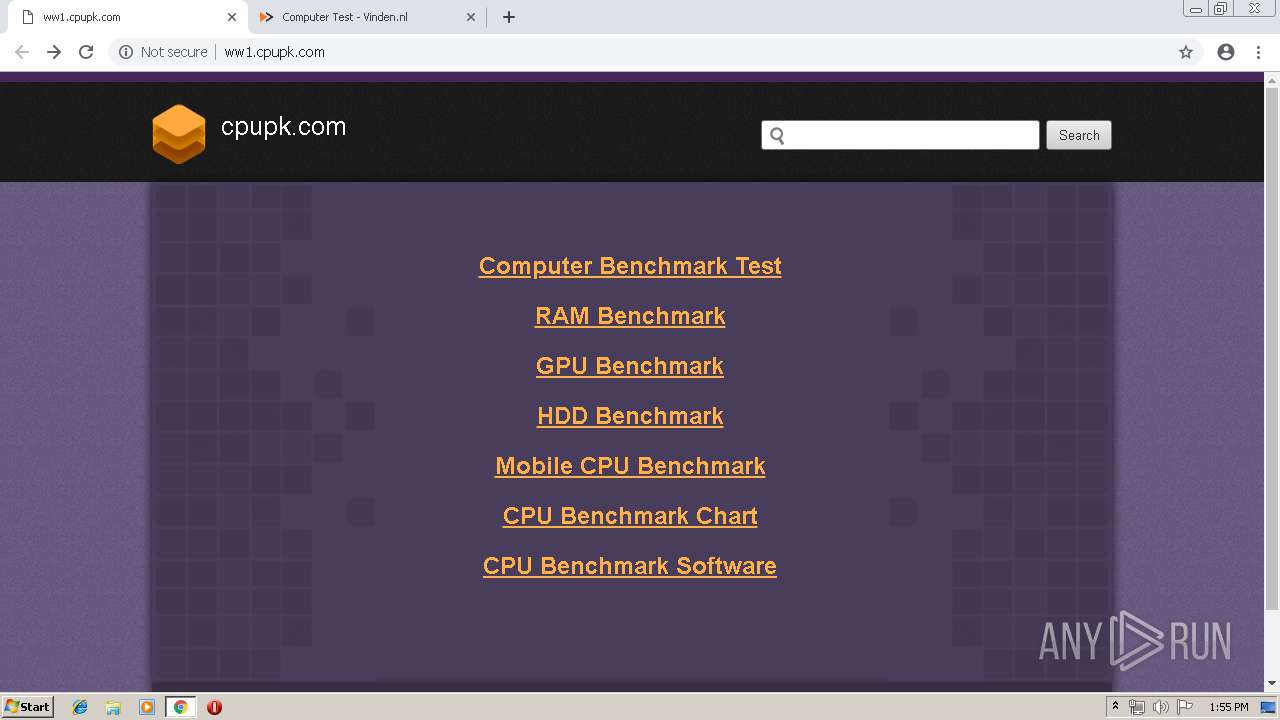
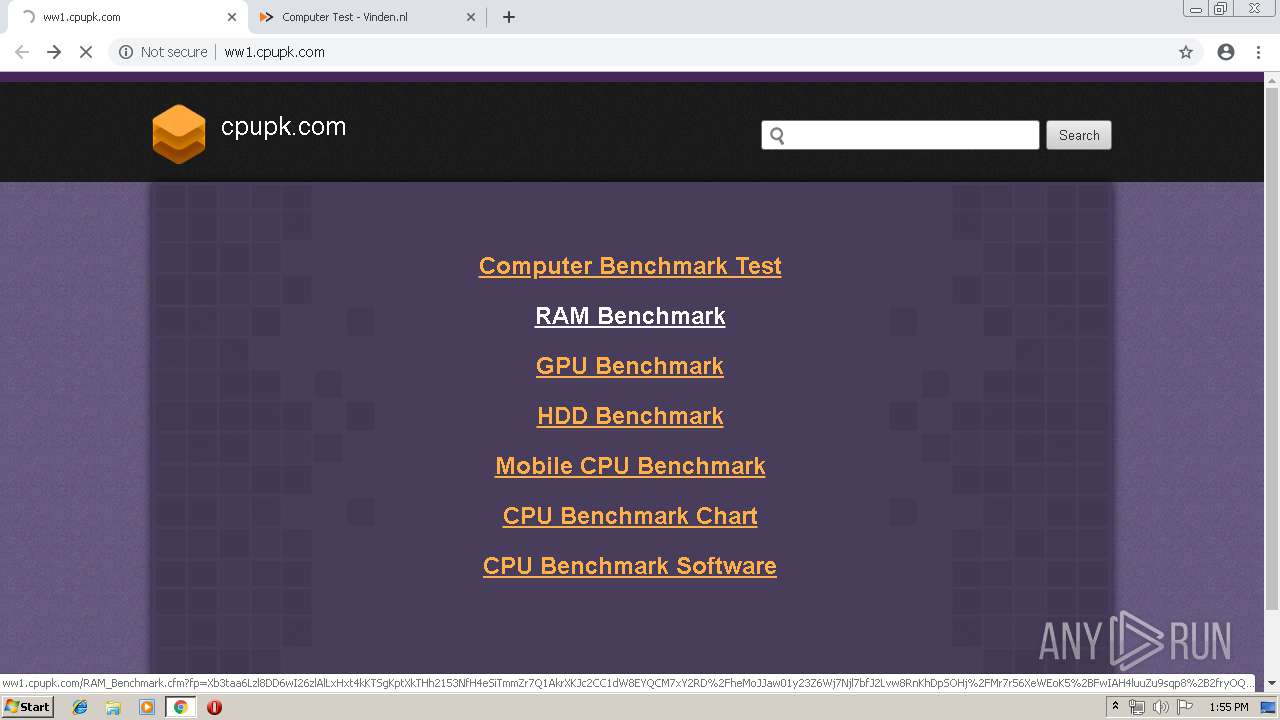
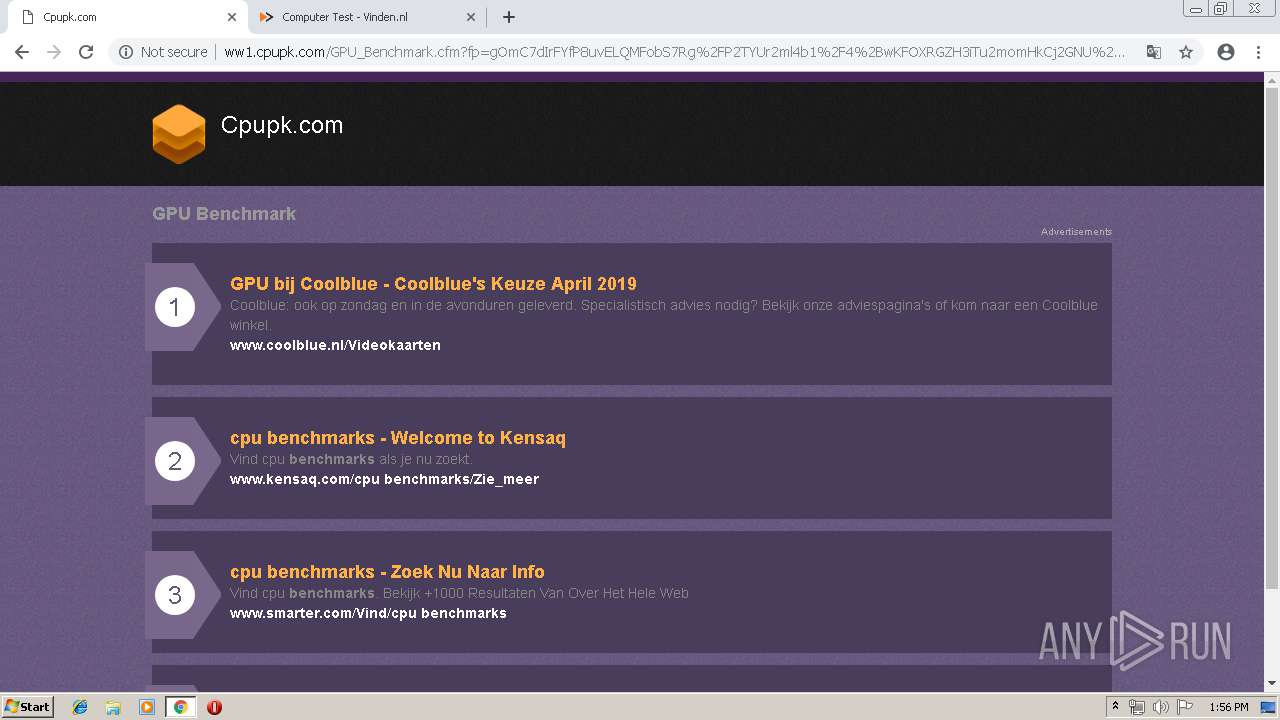
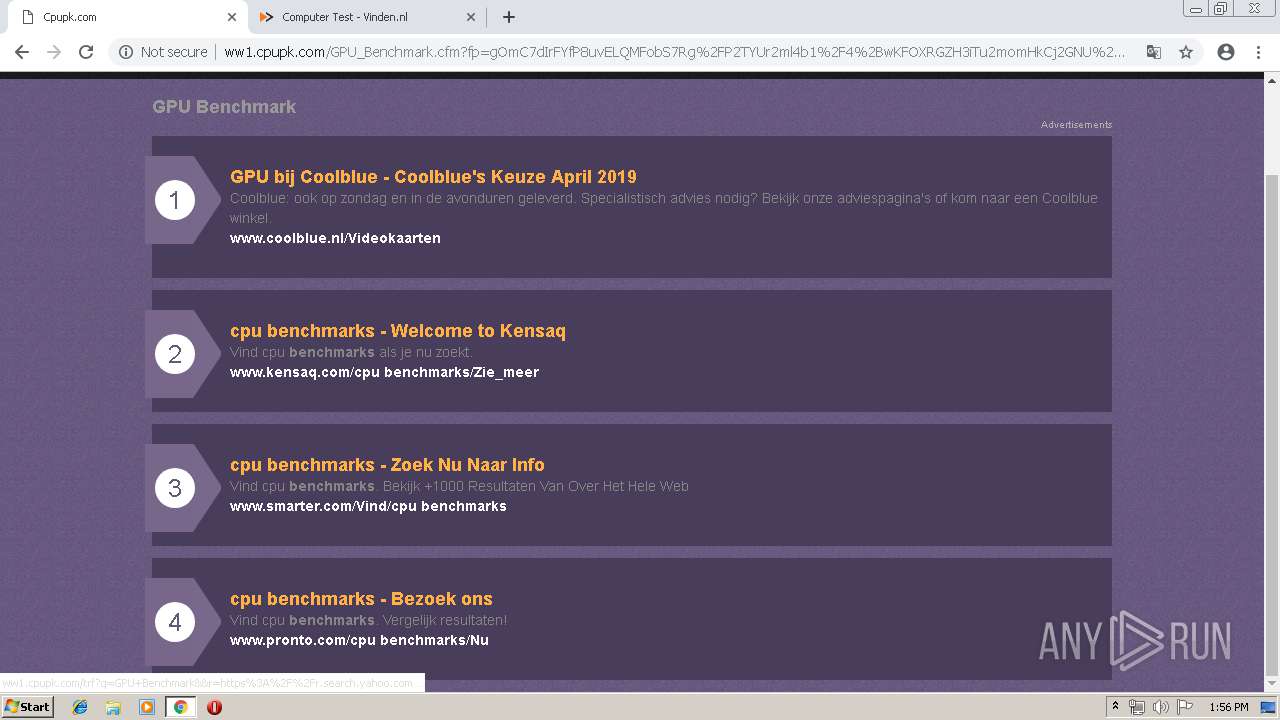
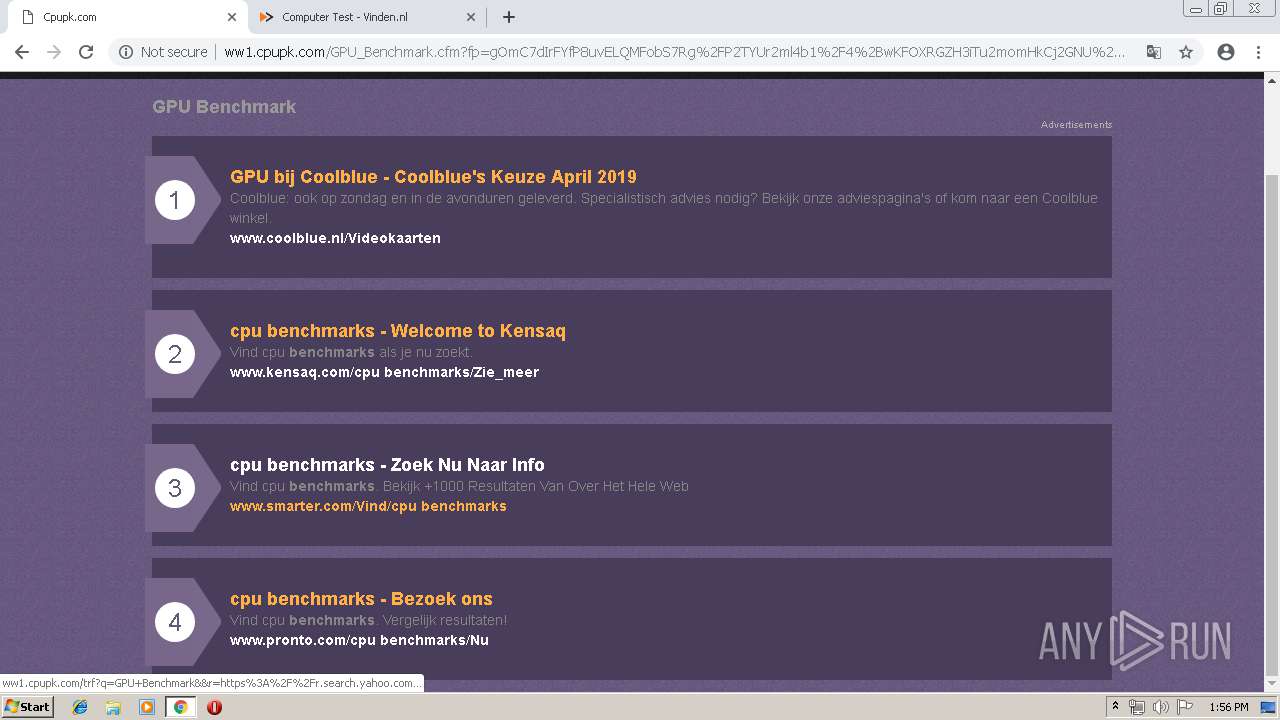
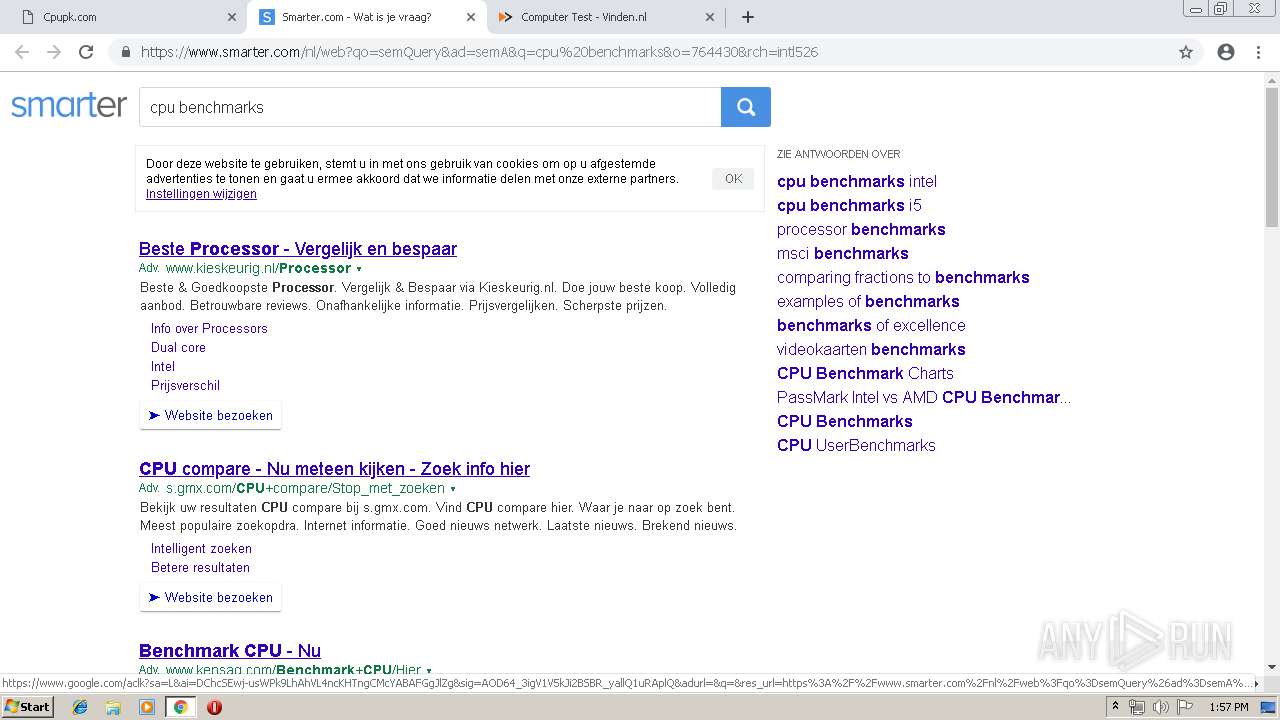
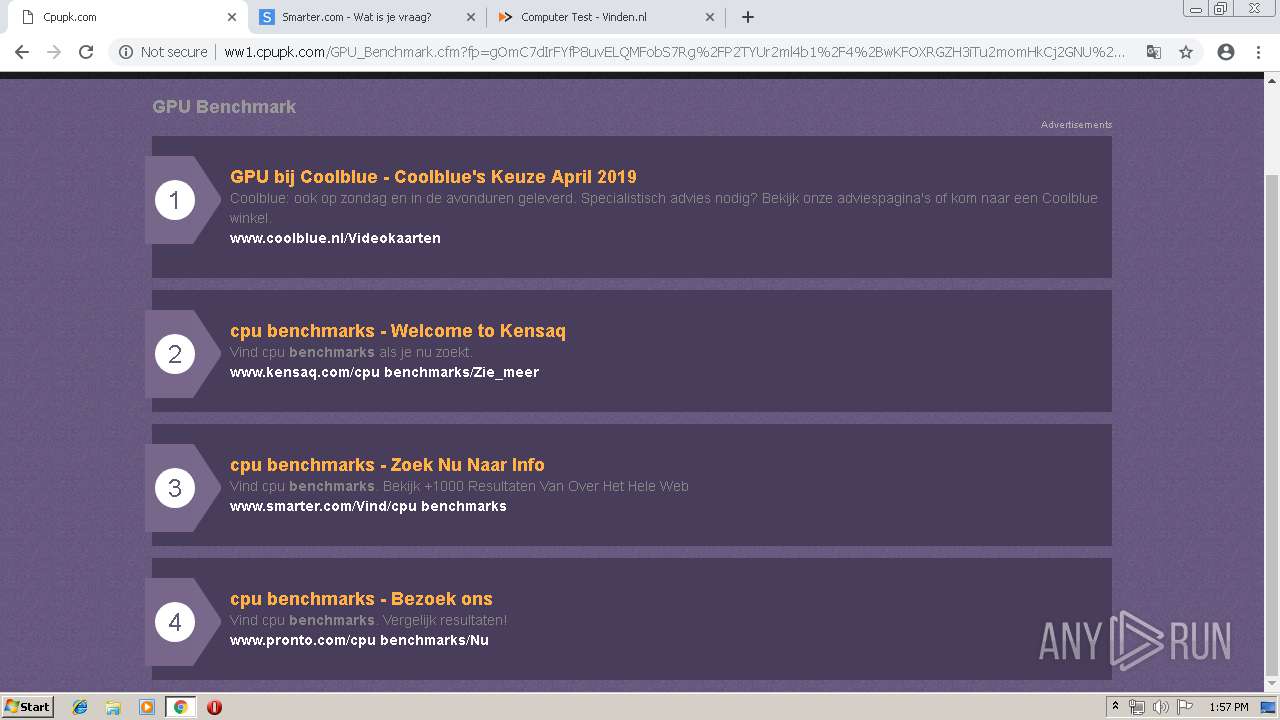
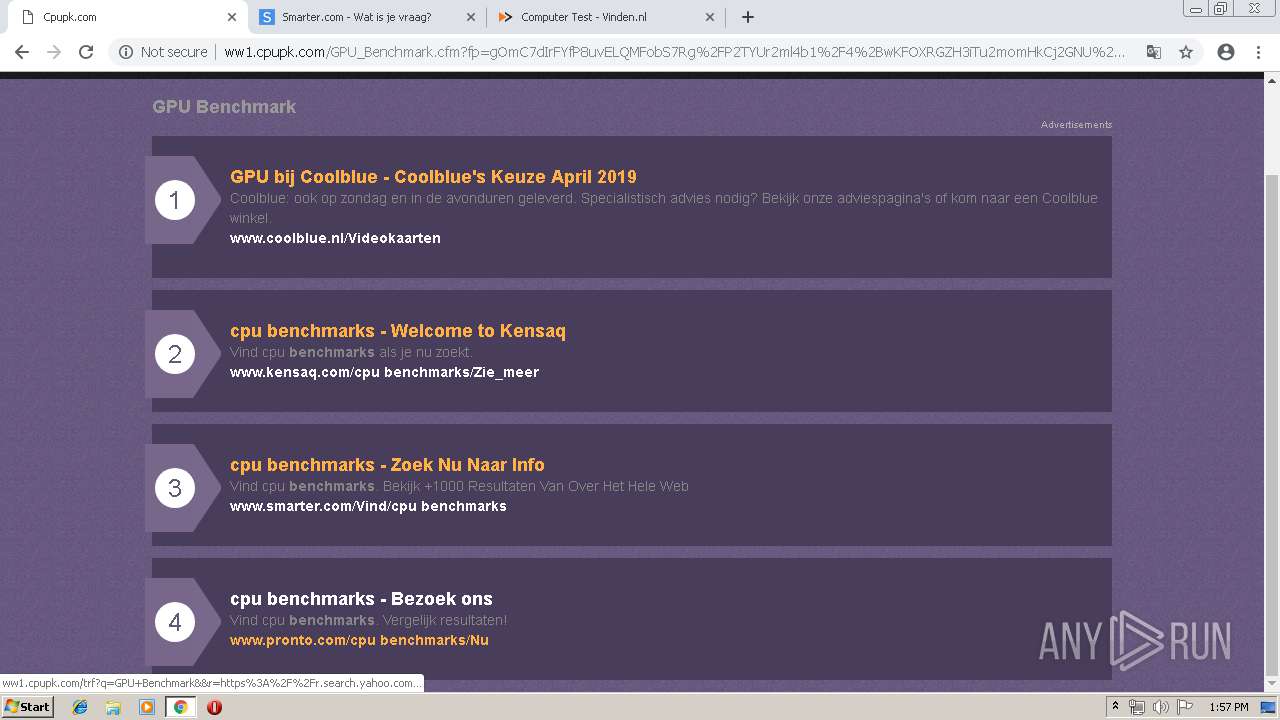
2172 | chrome.exe | GET | — | 208.91.196.145:80 | http://ww1.cpupk.com/Computer_Benchmark_Test.cfm?fp=Xb3taa6Lzl8DD6wI26zlAlLxHxt4kKTSgKptXkTHh2153NfH4eSiTmmZr7Q1AkrXKJc2CC1dW8EYQCM7xY2RD%2FheMoJJaw01y23Z6Wj7Njl7bfJ2Lvw8RnKhDpSOHj%2FMr7r56XeWEoK5%2BFwIAH4luuZu9sqp8%2B2fryOQn1z3cSP3Zx5JXvqUyLbpzNpo66d1Z0ZvOQMrBhF%2FK26CycQxfg%3D%3D&yep=Ym2OX2reog9A5w62E1NFAueY01YPGHuhHFBodBG9I2xeBy0hnjdv8wL0HgHoAp%2FOCYkLsooXYuCWuYen5kmo%2F9eIbCc0wzqYLg6D%2F%2BpJCylw%2F0HsJj3xsnmKLZu2wdok59QhLe7iAErN%2F85pEW0z8Pfs00uVLUol1mqI2%2F18OS9jHBPUoMuz0gscMu7bHdh6Q7OWzaQCogInzEjpjqL3xr8qYgqlwN4MdtP%2BCtkdQNkT46BllXNYfF4ej%2BKbjZc0SxuiuYMoZNZjCK7k1Y13iaA3hSw5D7j1imwHoOvXGVRD3%2BKrFiAoGP4d5Zsu7TObk%2FrzvxPUtIUBIUkPgDIbVEUEOKxrzGicuenL6Zq1Qkg2t1UZaWxaZ9mYGnSSMmRTjtEdlH6m24Ucyw3YIyrdci8irBTDVKtLLNjwkQ%2FZZx7eFAuxd%2FEMipxScQdsl%2FHPVeAUMisxy7%2FhktY4mrw6klRncK7mixFeaeav7GB0WTh31PKpfIv3lPaUGnAp5I4tsgSKjsMTql6nfVQf%2F6R6NO2ILgHvaYfpPOzQnGLsSrSwCjULPpvKzH0GEIRiDMOxm8QjkI36hFt4I6Kbd85vPA%3D%3D>np=0>pp=0&maxads=0&kld=1040&yprpnd=%2FeWU%2B4fWDR4ogE7HfT4adMthbPqvdlwNN7gBisjgchk%3D&prvtof=K%2BvlbC43UX0Hgr89qr7%2BnXklpmcoJ48WVV5w%2BYoHiGs%3D&>np=0>pp=0&kt=210&&kbc=3997&ki=6654596&ktd=0&kld=1040&kp=1&bd=1%23720%231280%231%230%23598%23197 | VG | — | — | malicious |
2172 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i3.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
2172 | chrome.exe | GET | 200 | 208.91.196.145:80 | http://ww1.cpupk.com/?fp=942Rbd1cpp02WSjb5lbnVV8%2F3gPUi%2BGnCAkhkIbdCNMGSm5YaH4YAHyFYAH445Pd21eZ5ZM2OEZoi5IMNcEfo9O%2FZGWZIx7Mq93vBR2YG0e%2FIPma0HmI4dUXvb%2F1qaxQIS5Gql6Fxn3J7OkLDhizfBEX3vo%2FI0LyTNUIRzIuMBY%3D&prvtof=K%2BvlbC43UX0Hgr89qr7%2BnXklpmcoJ48WVV5w%2BYoHiGs%3D&poru=RllqxREEA%2FovUsQ58yGvvnTjGx7vhfX0nsfMYWj50WTAivL9LUvh%2B8PQkRV0Sfti& | VG | html | 6.41 Kb | malicious |
2172 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
2172 | chrome.exe | GET | 200 | 208.91.196.145:80 | http://ww1.cpupk.com/ | VG | html | 1.05 Kb | malicious |
2172 | chrome.exe | GET | 200 | 172.217.133.70:80 | http://r1---sn-f5f7lne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=62.212.86.130&mm=28&mn=sn-f5f7lne6&ms=nvh&mt=1555332552&mv=u&pl=27&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2172 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i1.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
2172 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i4.cdn-image.com/__media__/pics/8243/logo.png | unknown | image | 4.32 Kb | whitelisted |
2172 | chrome.exe | GET | 302 | 5.79.68.108:80 | http://decompiler.cpupk.com/content.jar | NL | text | 11 b | malicious |
2172 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i3.cdn-image.com/__media__/pics/8243/bg.gif | unknown | image | 4.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2172 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2172 | chrome.exe | 5.79.68.108:80 | decompiler.cpupk.com | LeaseWeb Netherlands B.V. | NL | malicious |
2172 | chrome.exe | 2.16.186.106:80 | i3.cdn-image.com | Akamai International B.V. | — | whitelisted |
2172 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2172 | chrome.exe | 2.16.186.64:80 | i3.cdn-image.com | Akamai International B.V. | — | whitelisted |
— | — | 172.217.21.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2172 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2172 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2172 | chrome.exe | 172.217.16.202:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
2172 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
decompiler.cpupk.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ww1.cpupk.com |
| malicious |
i3.cdn-image.com |
| whitelisted |
i4.cdn-image.com |
| whitelisted |
i2.cdn-image.com |
| whitelisted |
i1.cdn-image.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |