| File name: | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66 |
| Full analysis: | https://app.any.run/tasks/234cb648-f996-4fd2-9be3-5b5f0cd53945 |
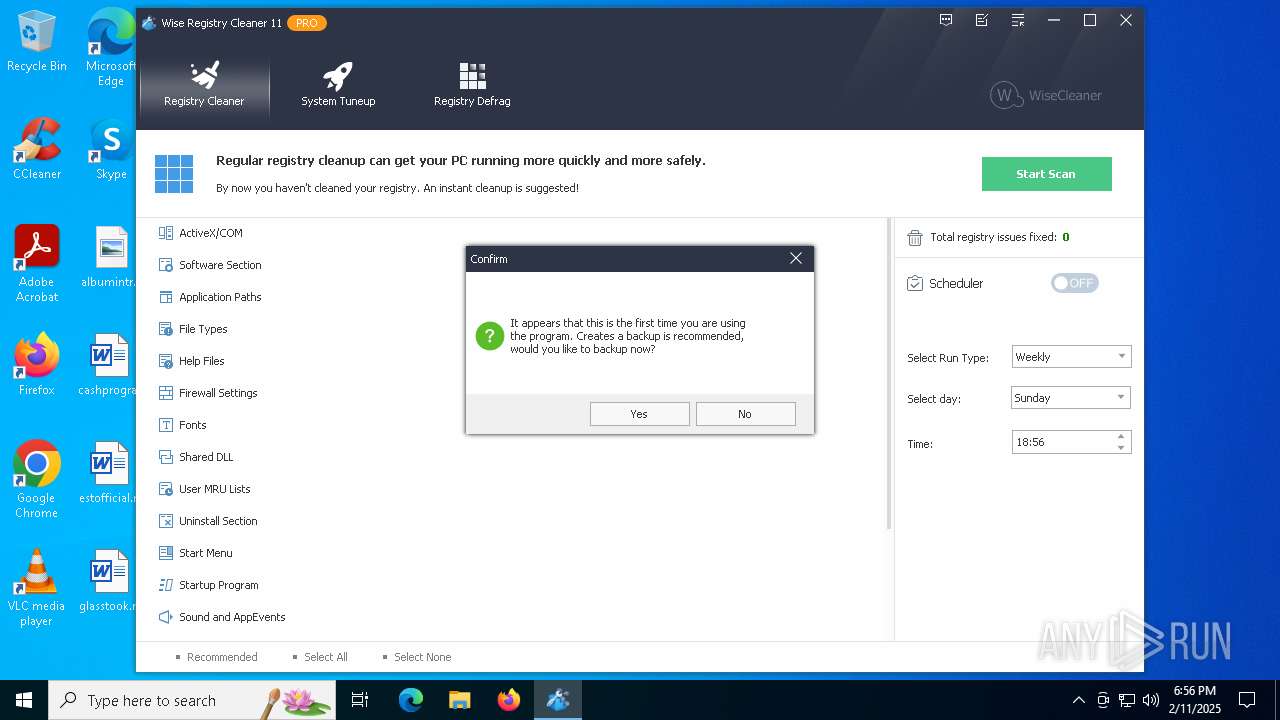
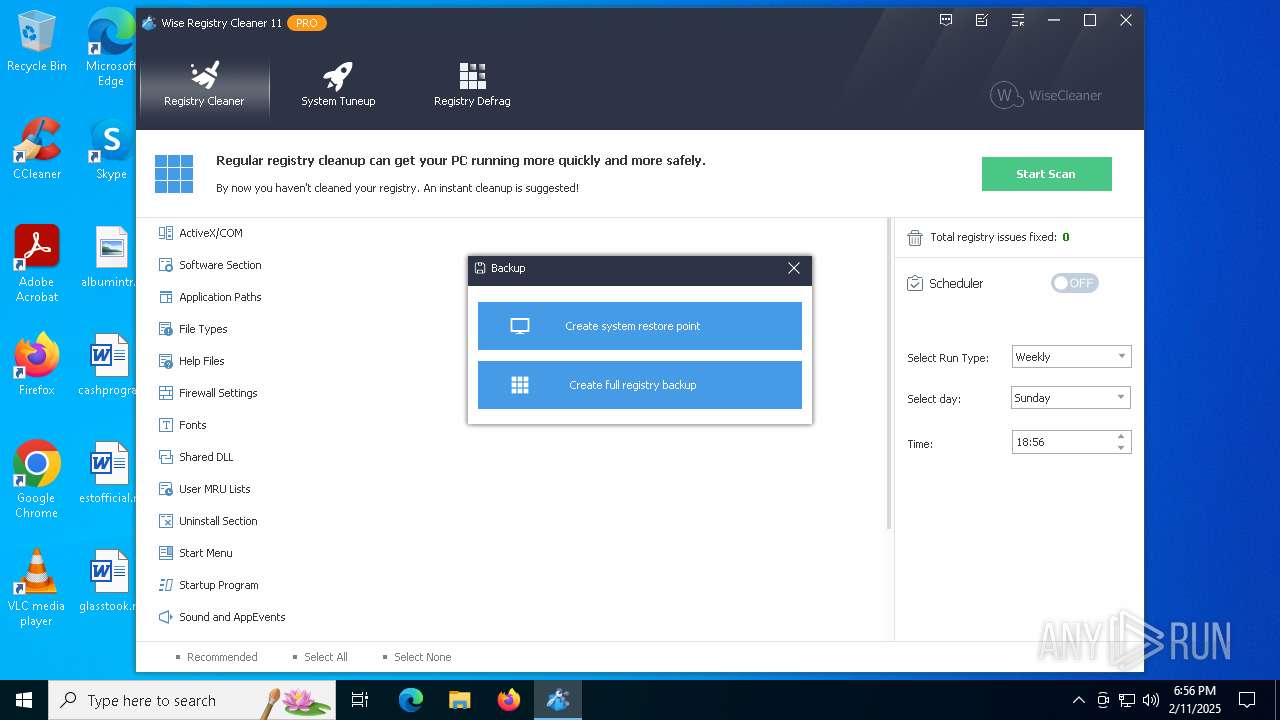
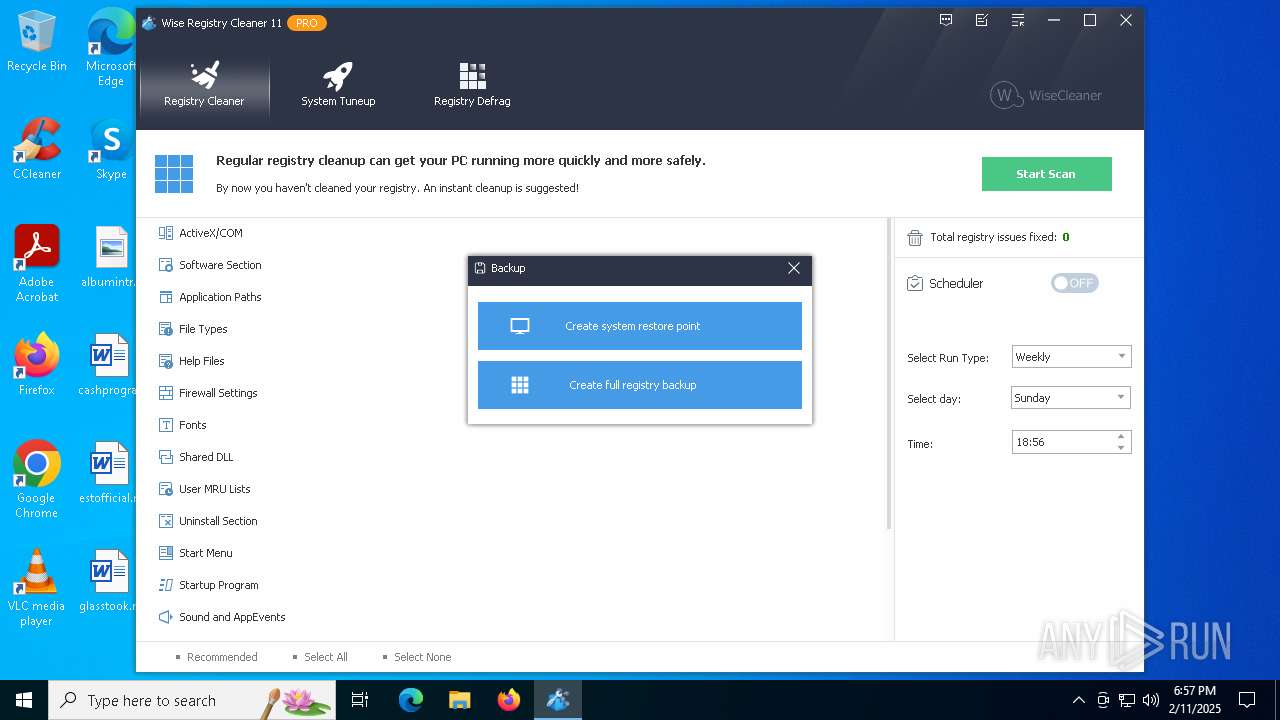
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2025, 18:56:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | F3144EC2A4540E57A2A6017EAE04B250 |
| SHA1: | 224F3C95C22B37EE640CE0E5CBB3F53C1238EBDB |
| SHA256: | 88D29143537D4400DA2D6F84537635FD8359DE078BAE7F73F7D64D793746FC66 |
| SSDEEP: | 98304:cjDHgVKkmrr6NazRsUJc6FlqLqqIkz4eSBYPPlUcjgwG5ben3PK3PsRqF6mM+T4o:crrTAH6 |
MALICIOUS
Executing a file with an untrusted certificate
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
Connects to the CnC server
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
SUSPICIOUS
Reads security settings of Internet Explorer
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Executable content was dropped or overwritten
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Process drops legitimate windows executable
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Application launched itself
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
Contacting a server suspected of hosting an CnC
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
INFO
Failed to create an executable file in Windows directory
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
Create files in a temporary directory
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
The sample compiled with english language support
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Reads the computer name
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Process checks computer location settings
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
Checks supported languages
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Checks proxy server information
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 5536)
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Reads the software policy settings
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Reads the machine GUID from the registry
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Compiled with Borland Delphi (YARA)
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Creates files in the program directory
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
UPX packer has been detected
- 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe (PID: 4076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (62.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (23.7) |
| .scr | | | Windows screen saver (7.4) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:09:01 05:27:22+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 7936000 |
| InitializedDataSize: | 2828800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x79245c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.1.1.716 |
| ProductVersionNumber: | 11.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
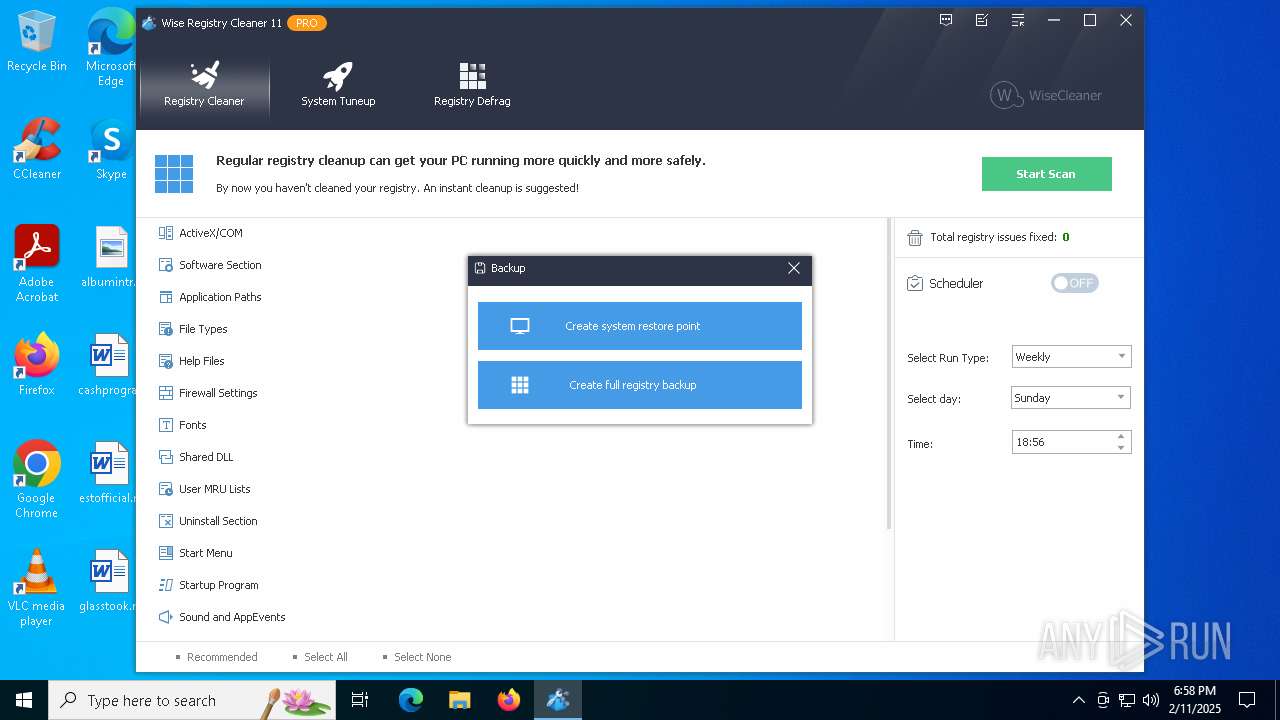
| CompanyName: | WiseCleaner.com |
| FileDescription: | Wise Registry Cleaner |
| FileVersion: | 11.1.1.716 |
| InternalName: | Wise Registry Cleaner |
| LegalCopyright: | WiseCleaner.com |
| LegalTrademarks: | WiseCleaner.com |
| OriginalFileName: | Wise Registry Cleaner |
| ProductName: | Wise Registry Cleaner |
| ProductVersion: | 11.1 |
| Comments: | Clean Registry |
| ProgramID: | com.embarcadero.WiseRegCleaner |
Total processes
119
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4076 | "C:\Users\admin\Desktop\88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe" $UAC | C:\Users\admin\Desktop\88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | ||||||||||||
User: admin Company: WiseCleaner.com Integrity Level: HIGH Description: Wise Registry Cleaner Version: 11.1.1.716 Modules
| |||||||||||||||
| 5536 | "C:\Users\admin\Desktop\88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe" | C:\Users\admin\Desktop\88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | explorer.exe | ||||||||||||
User: admin Company: WiseCleaner.com Integrity Level: MEDIUM Description: Wise Registry Cleaner Exit code: 0 Version: 11.1.1.716 Modules
| |||||||||||||||
Total events
4 464
Read events
4 460
Write events
4
Delete events
0
Modification events
| (PID) Process: | (4076) 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4076) 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4076) 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4076) 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WiseCleaner\WRC |
| Operation: | write | Name: | guid |
Value: {B1C61424-62FC-49C1-950A-659B3989077C} | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5536 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | C:\Users\admin\AppData\Local\Temp\conres.dll | executable | |
MD5:7574CF2C64F35161AB1292E2F532AABF | SHA256:DE055A89DE246E629A8694BDE18AF2B1605E4B9B493C7E4AEF669DD67ACF5085 | |||
| 4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | C:\Program Files\Common Files\System\symsrv.dll.000 | text | |
MD5:1130C911BF5DB4B8F7CF9B6F4B457623 | SHA256:EBA08CC8182F379392A97F542B350EA0DBBE5E4009472F35AF20E3D857EAFDF1 | |||
| 4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | C:\Program Files\Common Files\System\symsrv.dll | executable | |
MD5:7574CF2C64F35161AB1292E2F532AABF | SHA256:DE055A89DE246E629A8694BDE18AF2B1605E4B9B493C7E4AEF669DD67ACF5085 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
30
DNS requests
16
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 104.124.11.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
436 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
— | — | GET | 200 | 172.67.68.11:443 | https://info.wisecleaner.com/messages/index.php?to=checknews&pid=2 | unknown | binary | 248 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
436 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.19.96.82:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 104.124.11.17:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
436 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | 45.56.79.23:80 | www.aieov.com | Linode, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
5isohu.com |
| whitelisted |
www.aieov.com |
| malicious |
info.wisecleaner.com |
| whitelisted |
static.wisecleaner.net |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
— | — | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |
— | — | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Embarcadero URI Client/1.0) |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
4076 | 88d29143537d4400da2d6f84537635fd8359de078bae7f73f7d64d793746fc66.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |