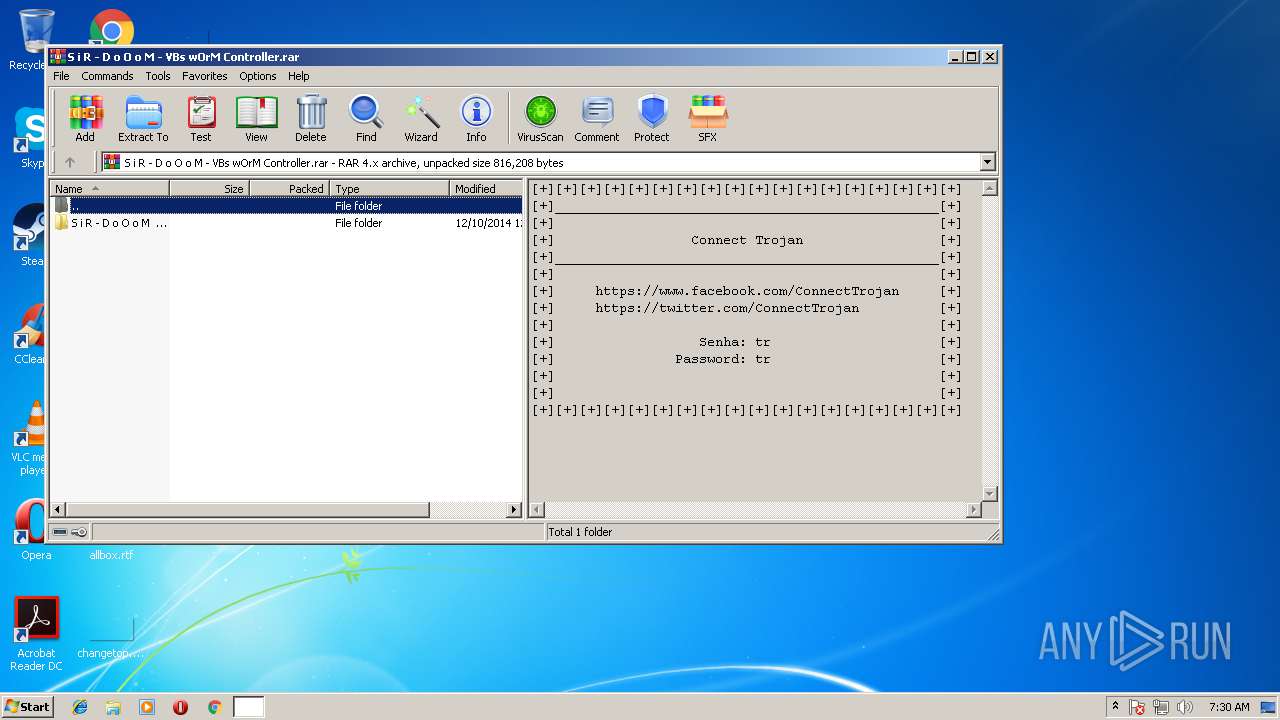
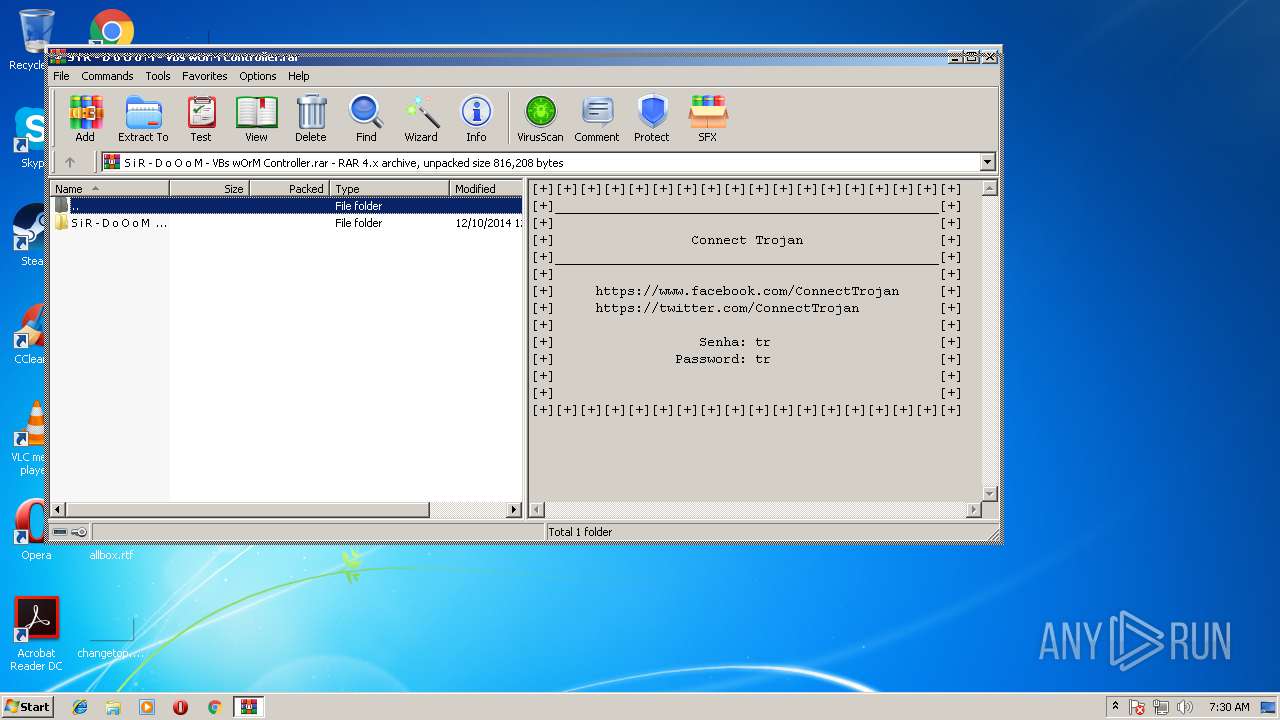
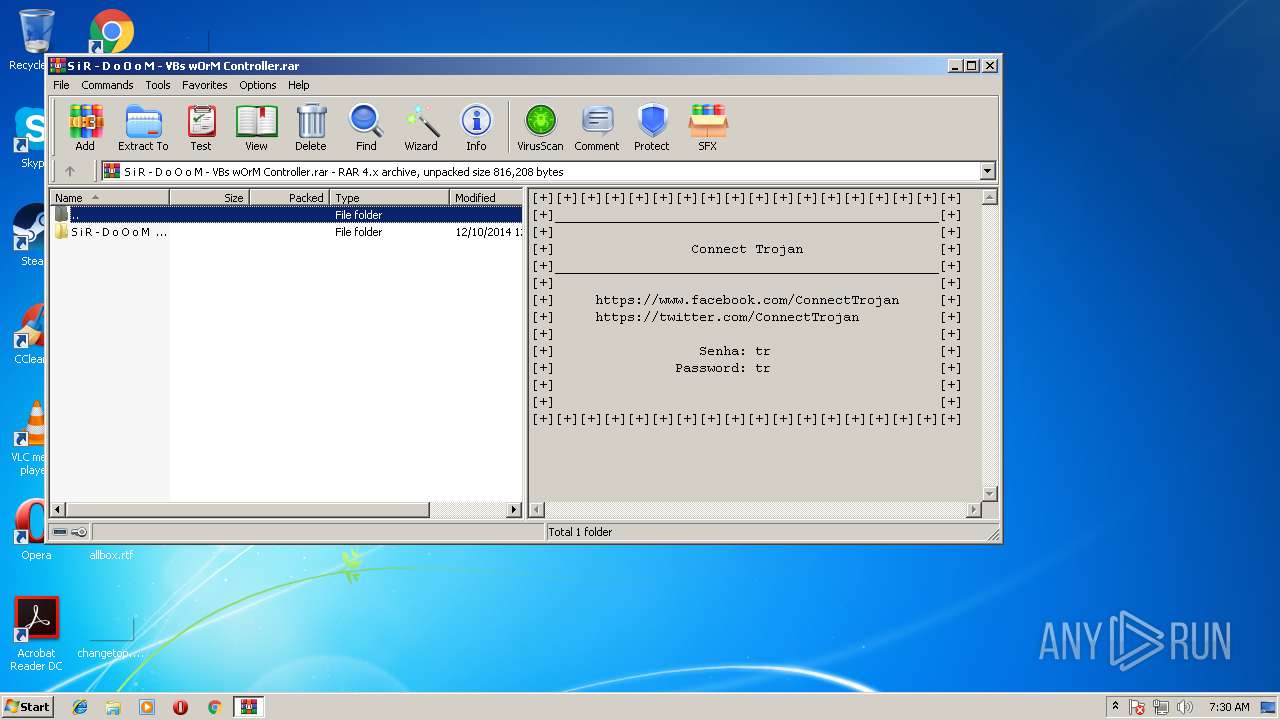
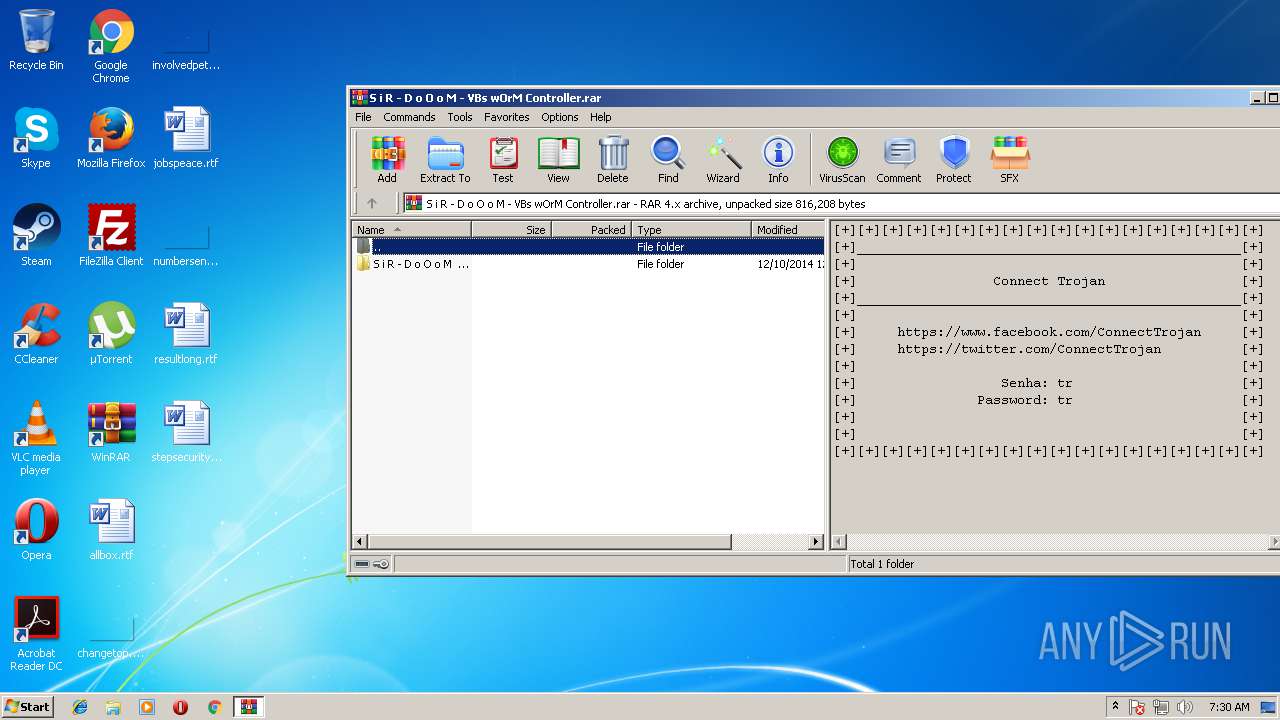
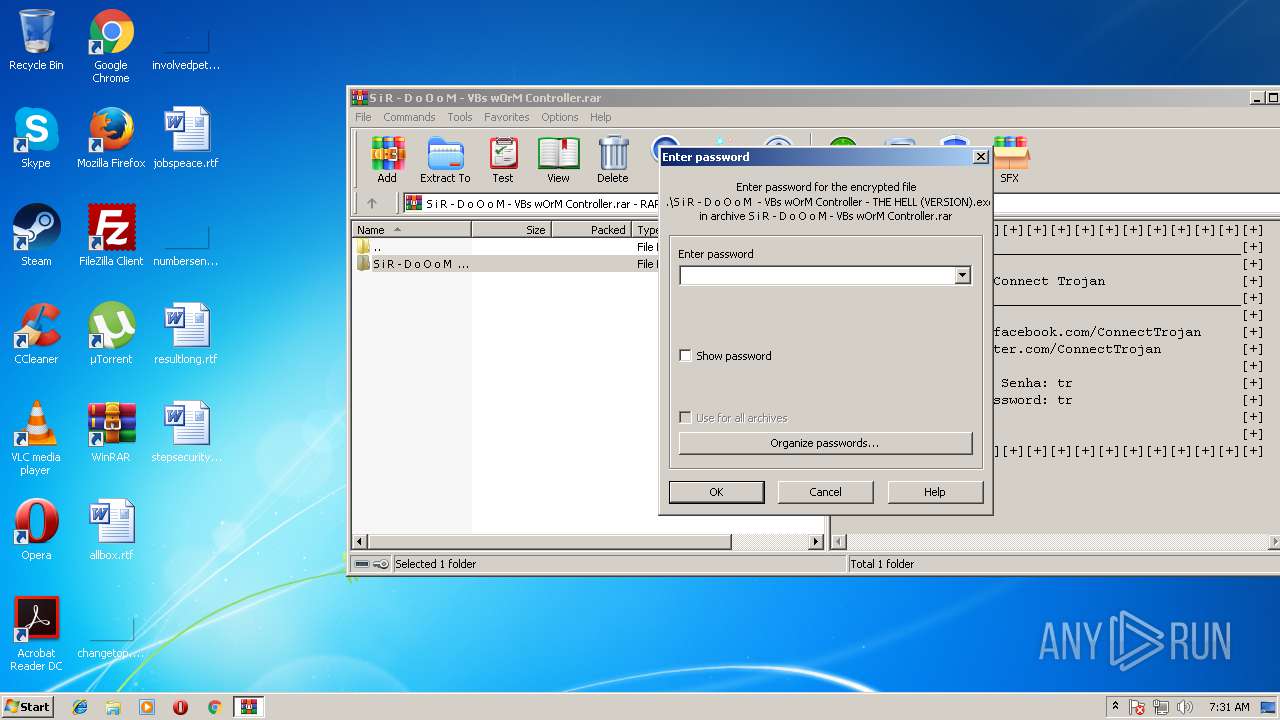
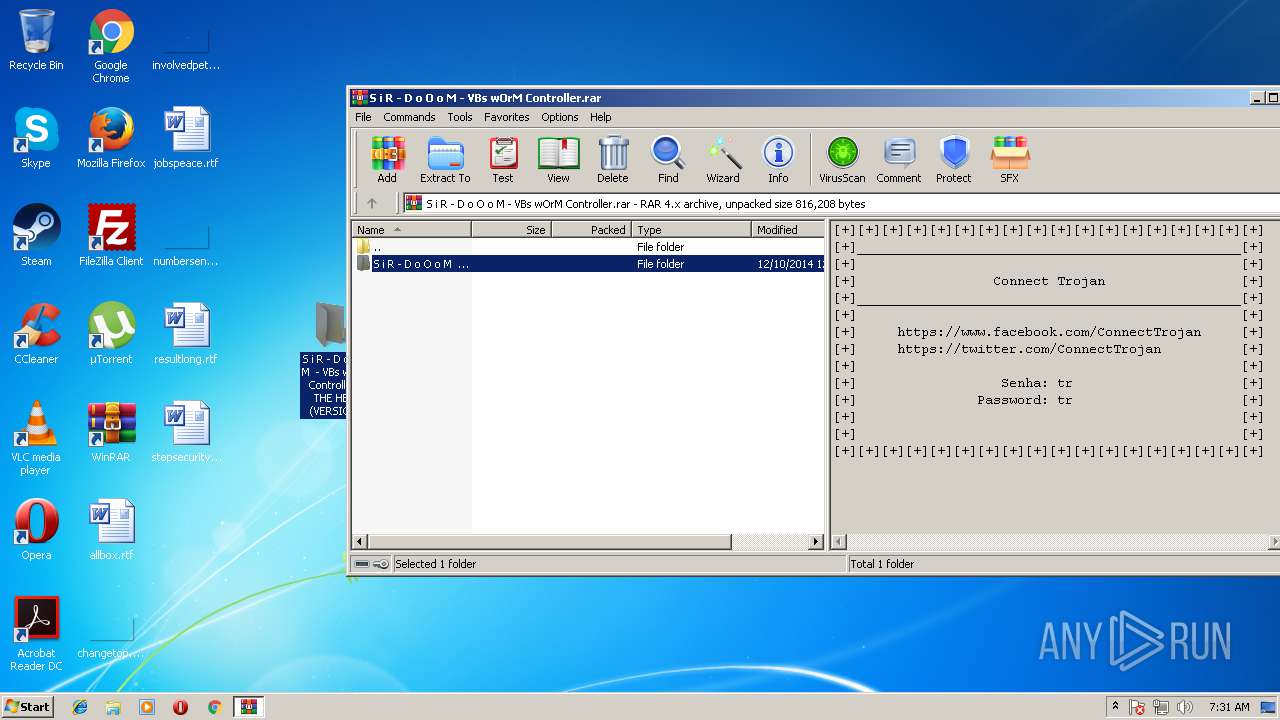
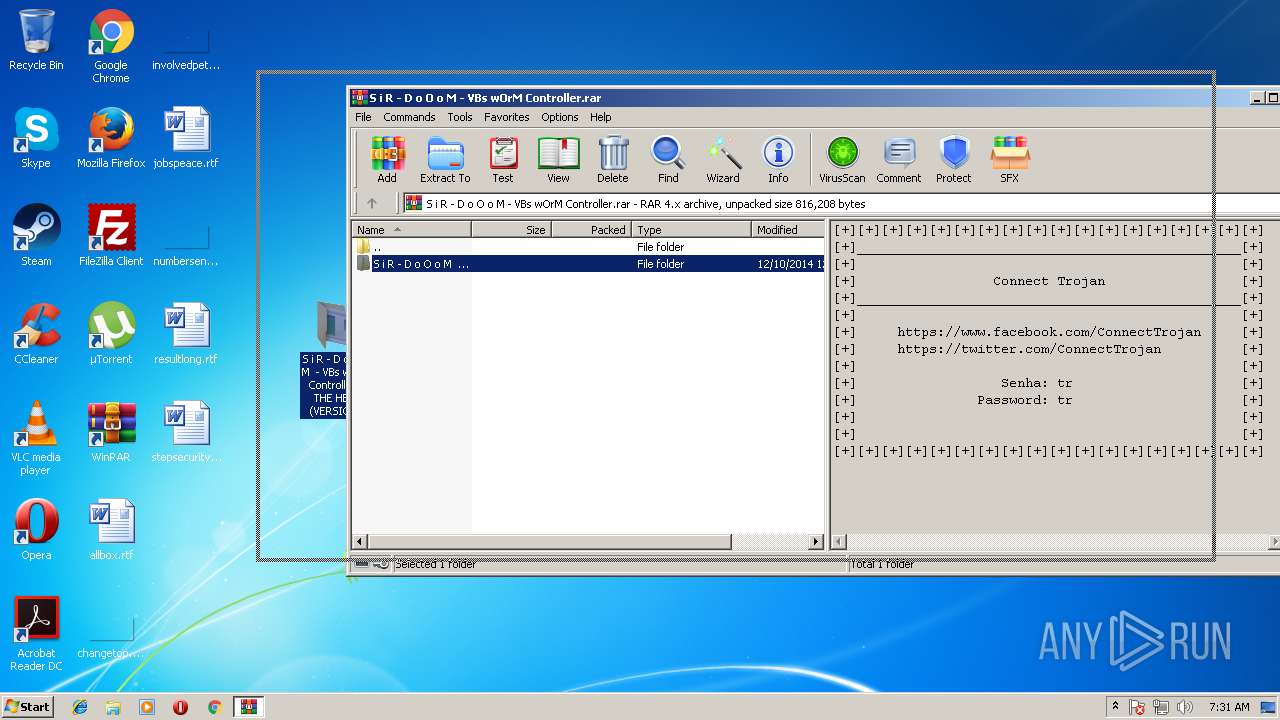
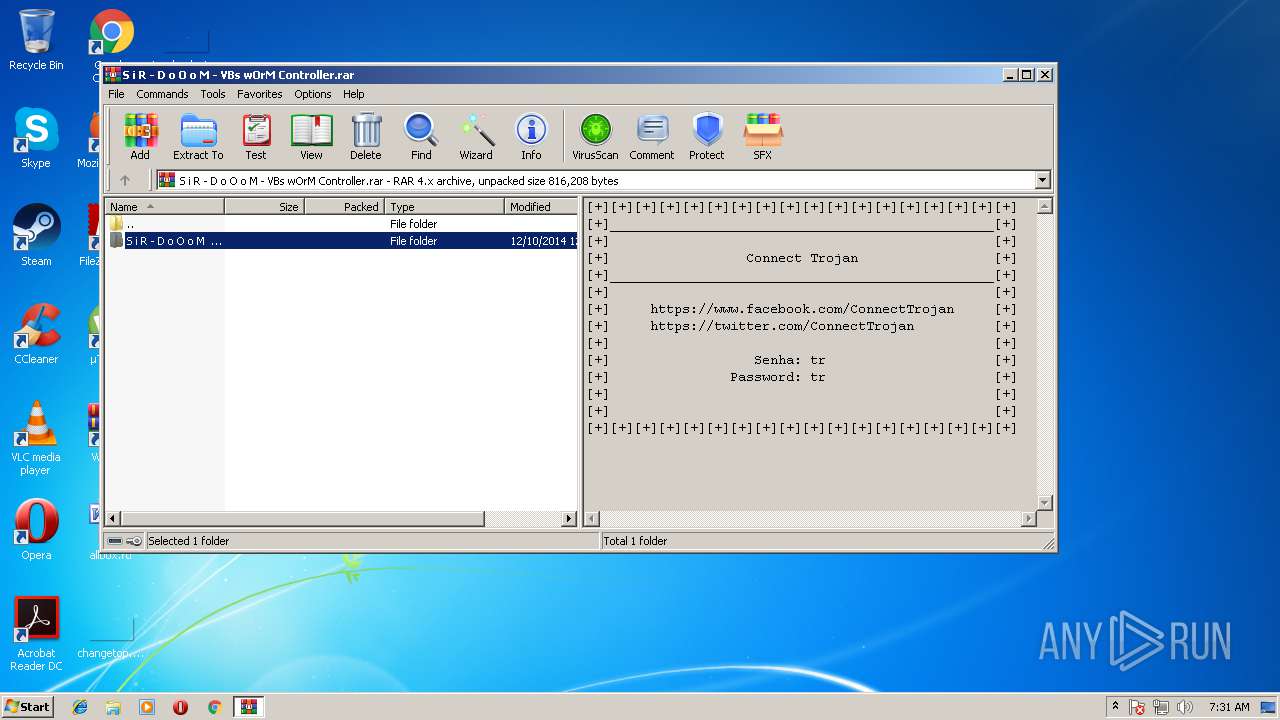
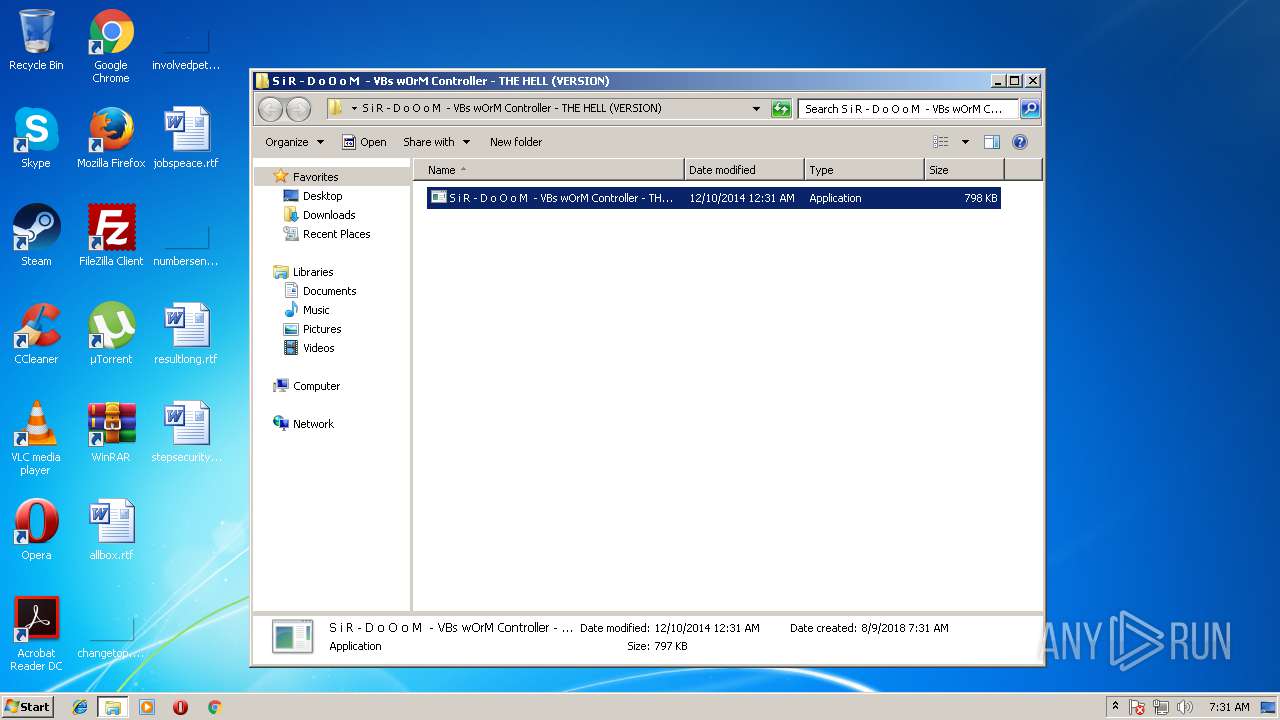
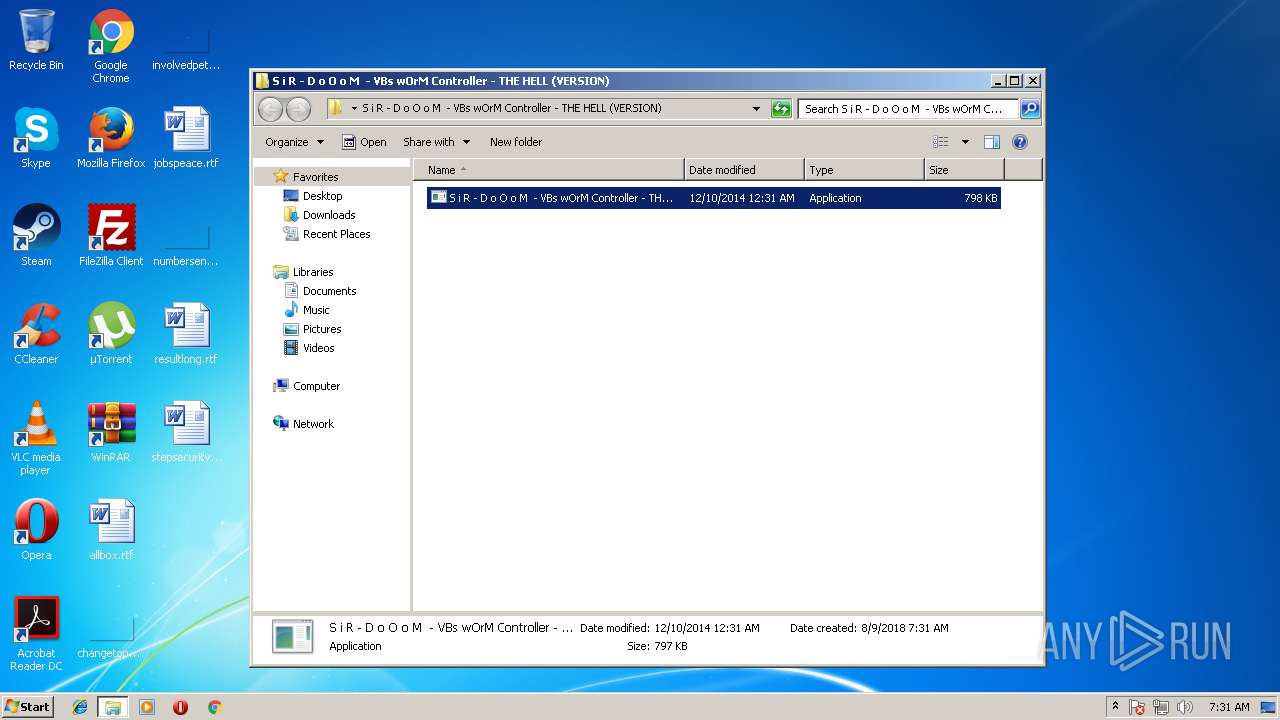
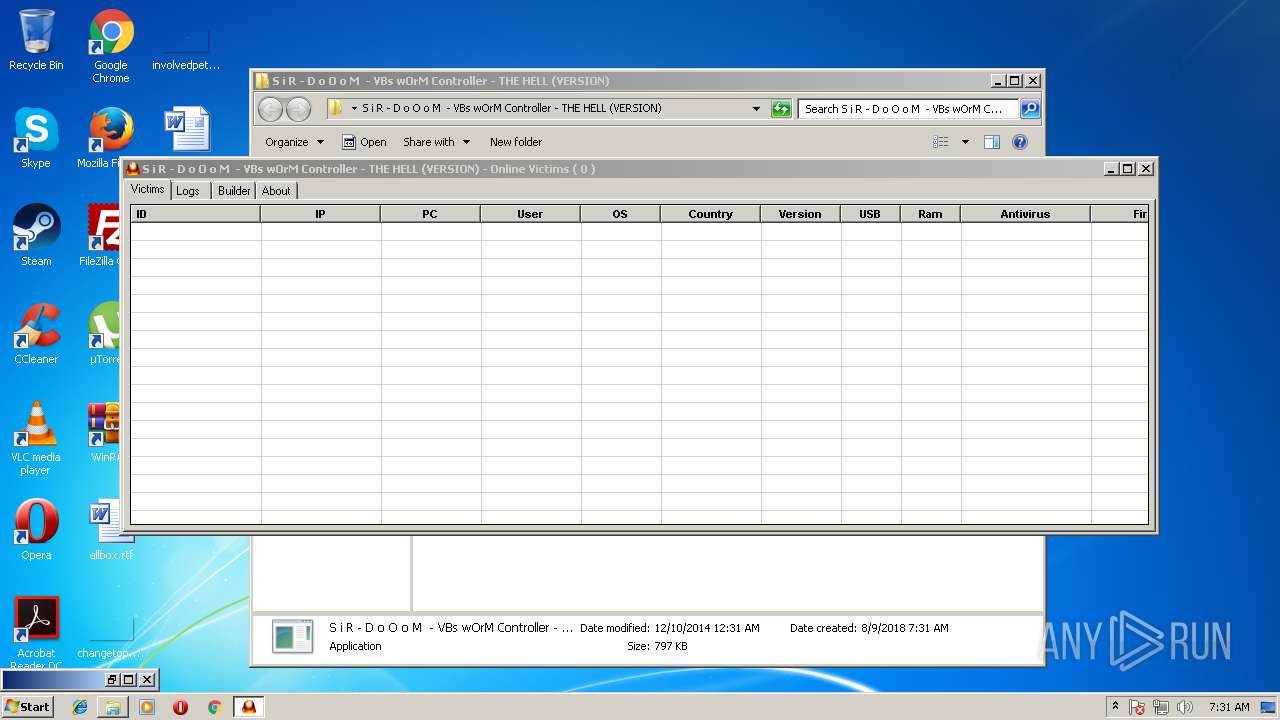
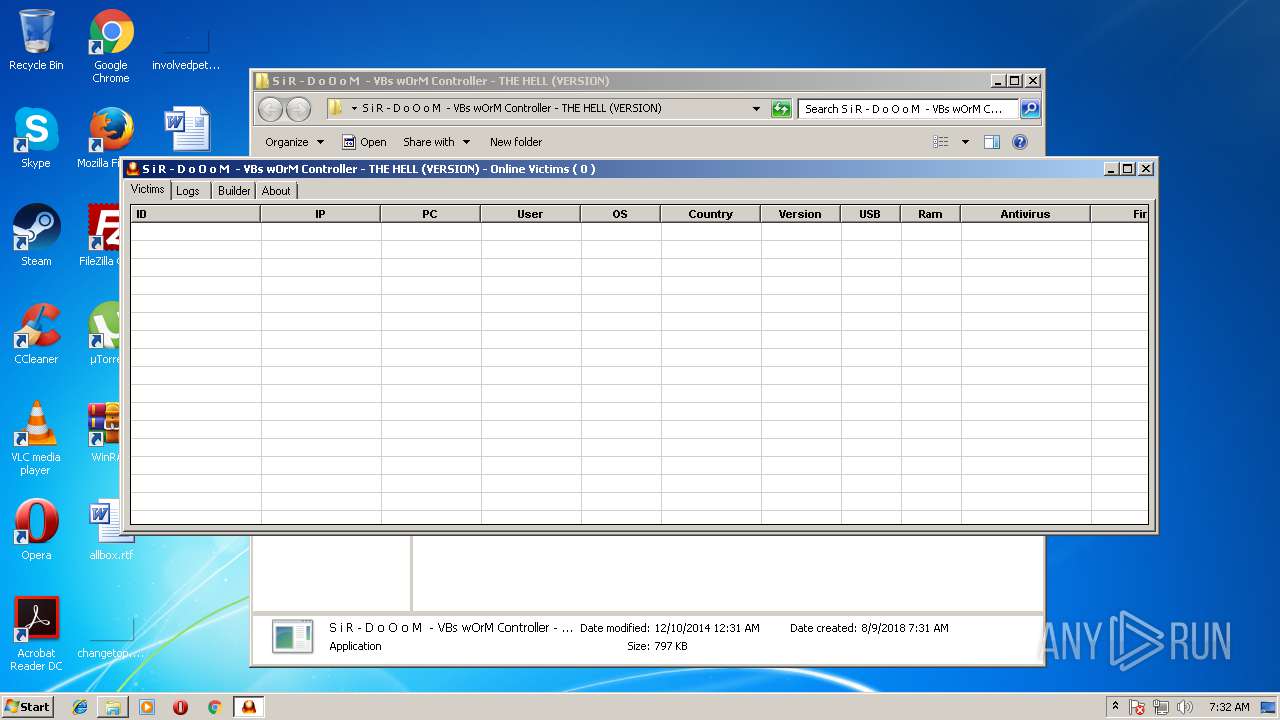
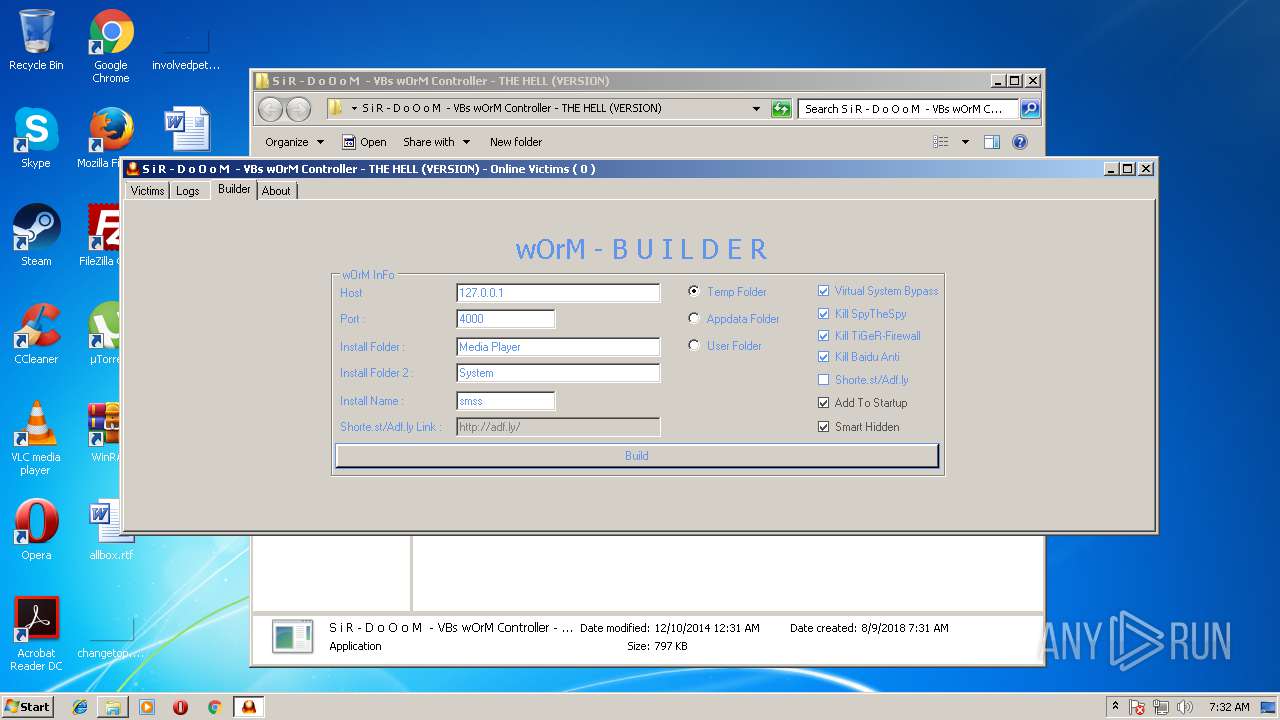
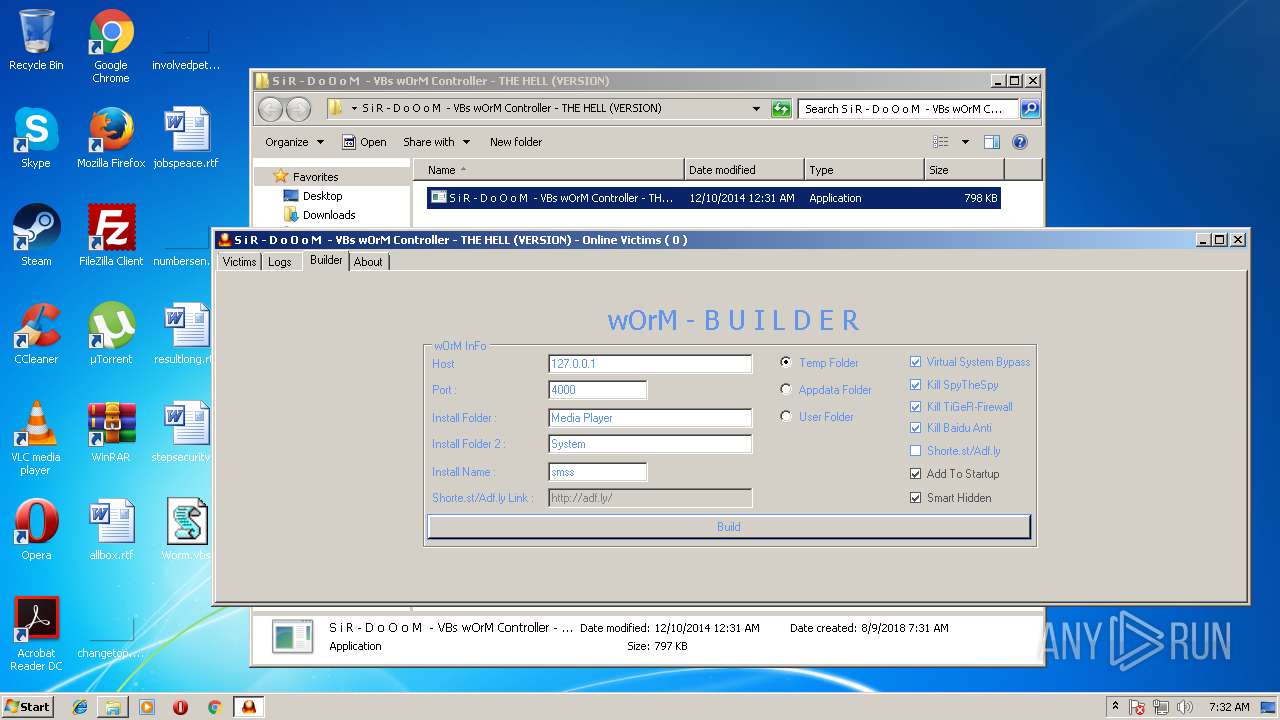
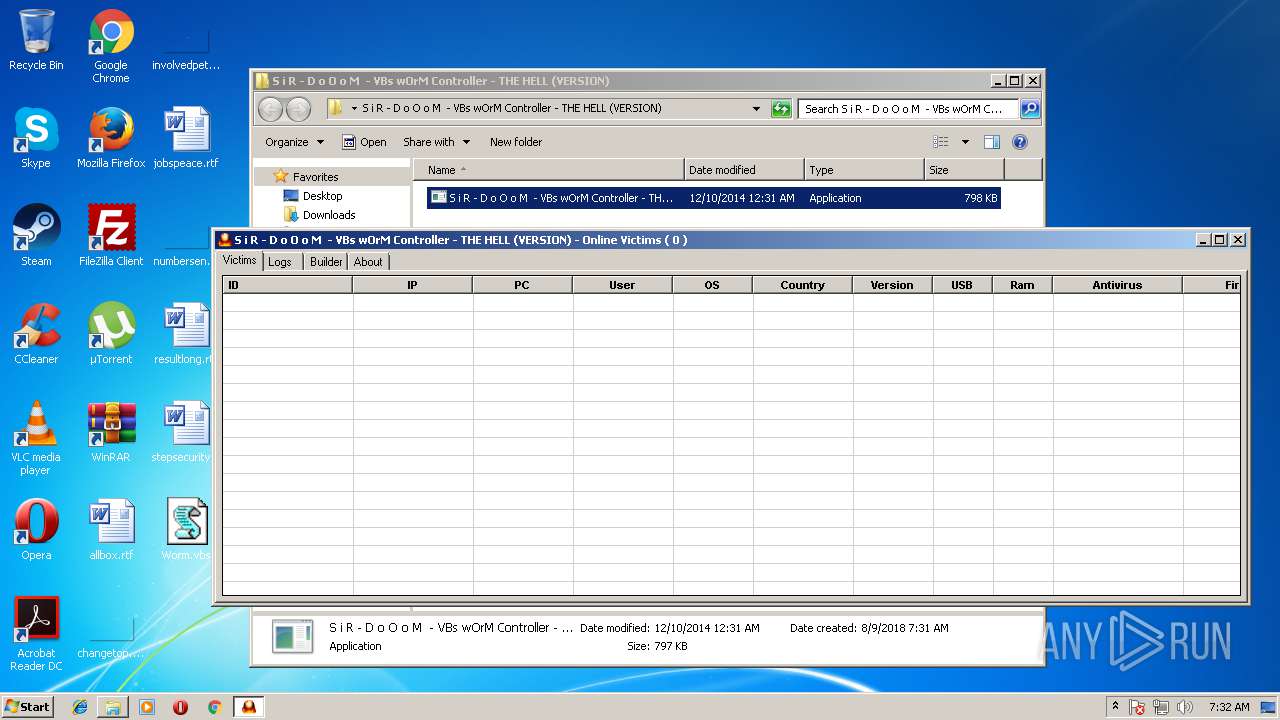
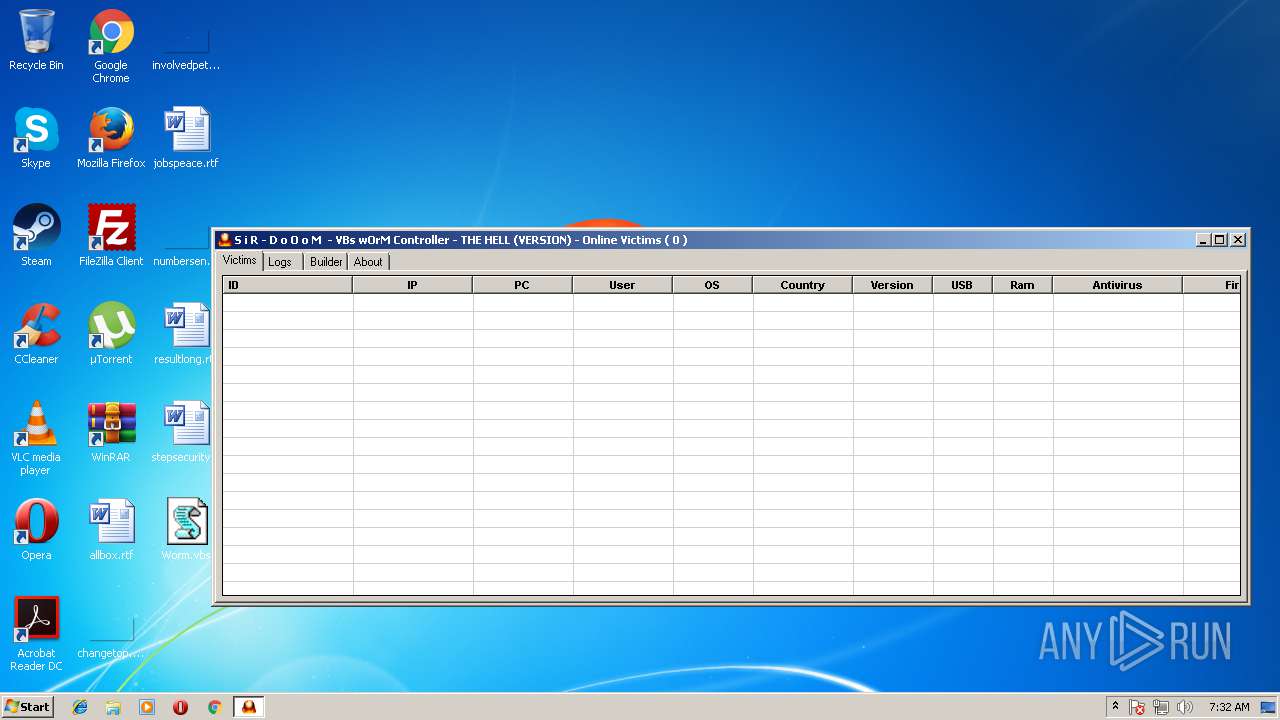
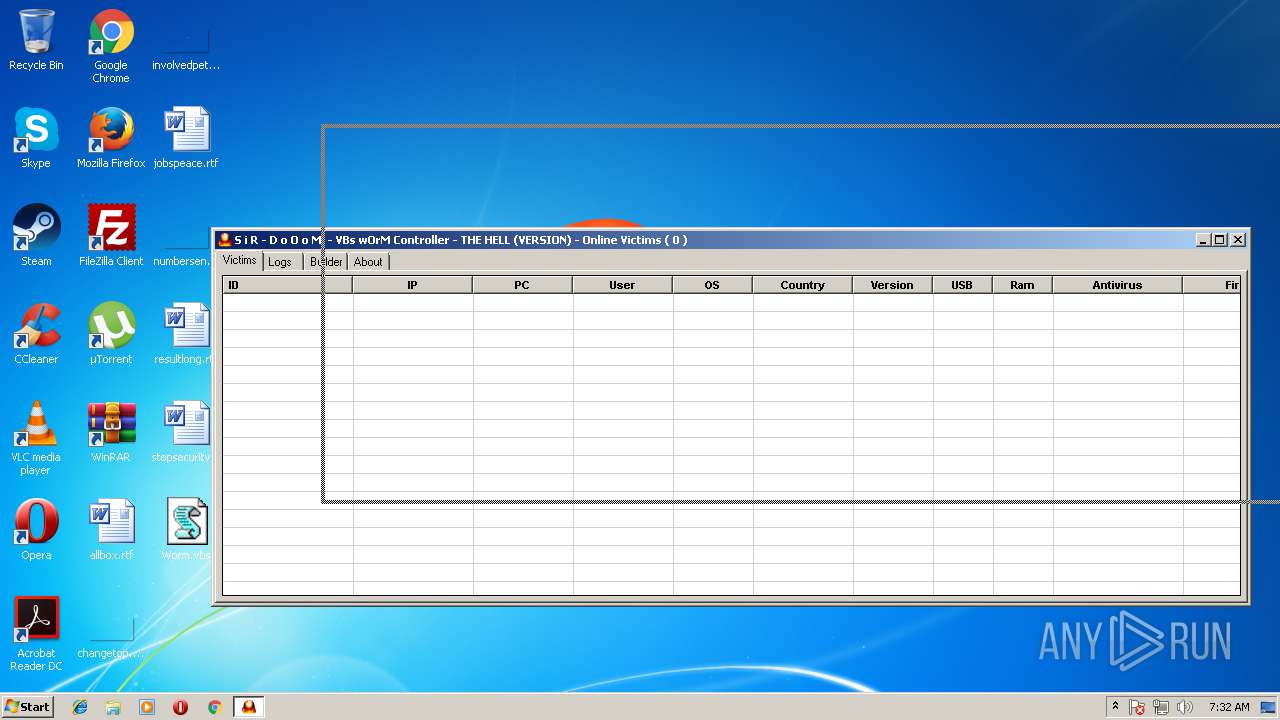
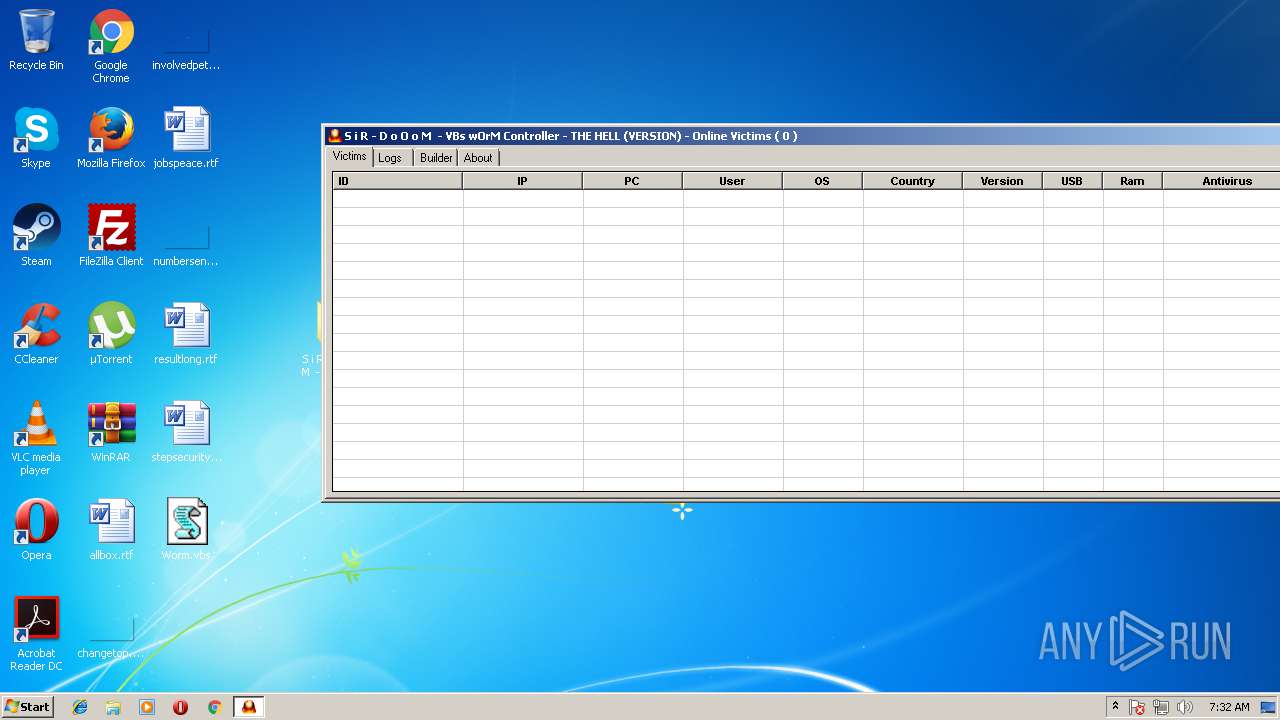
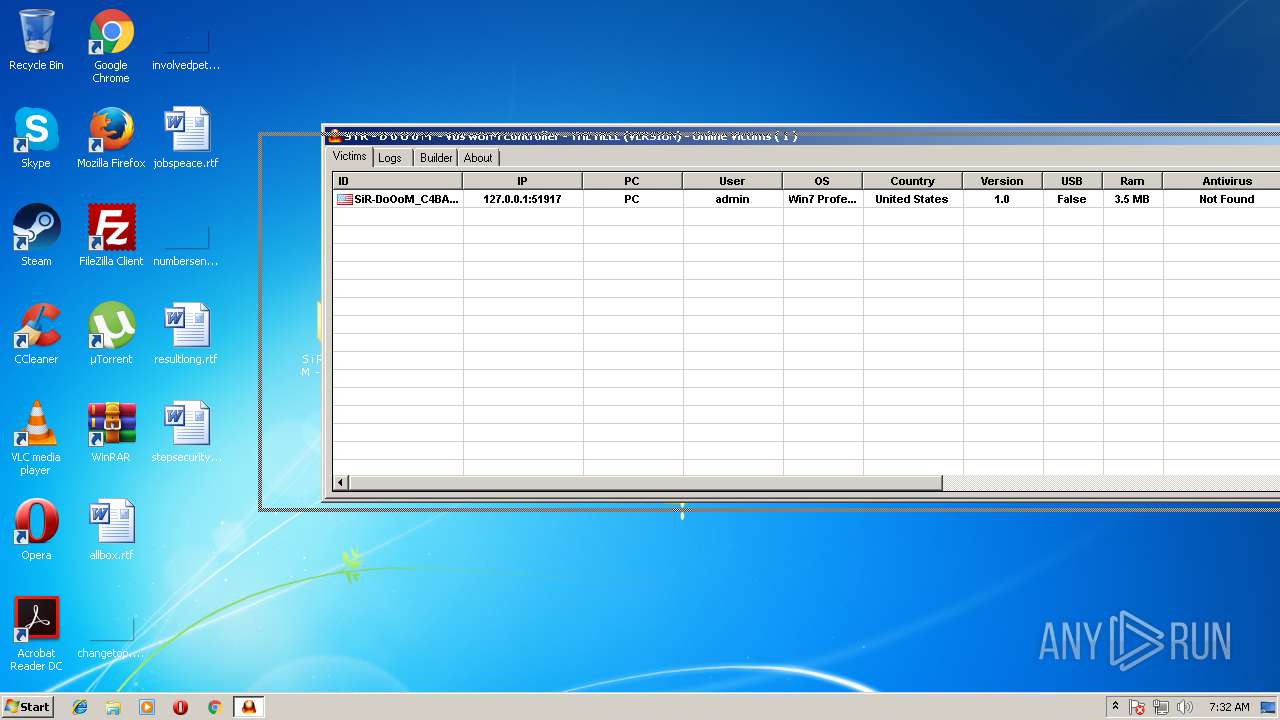
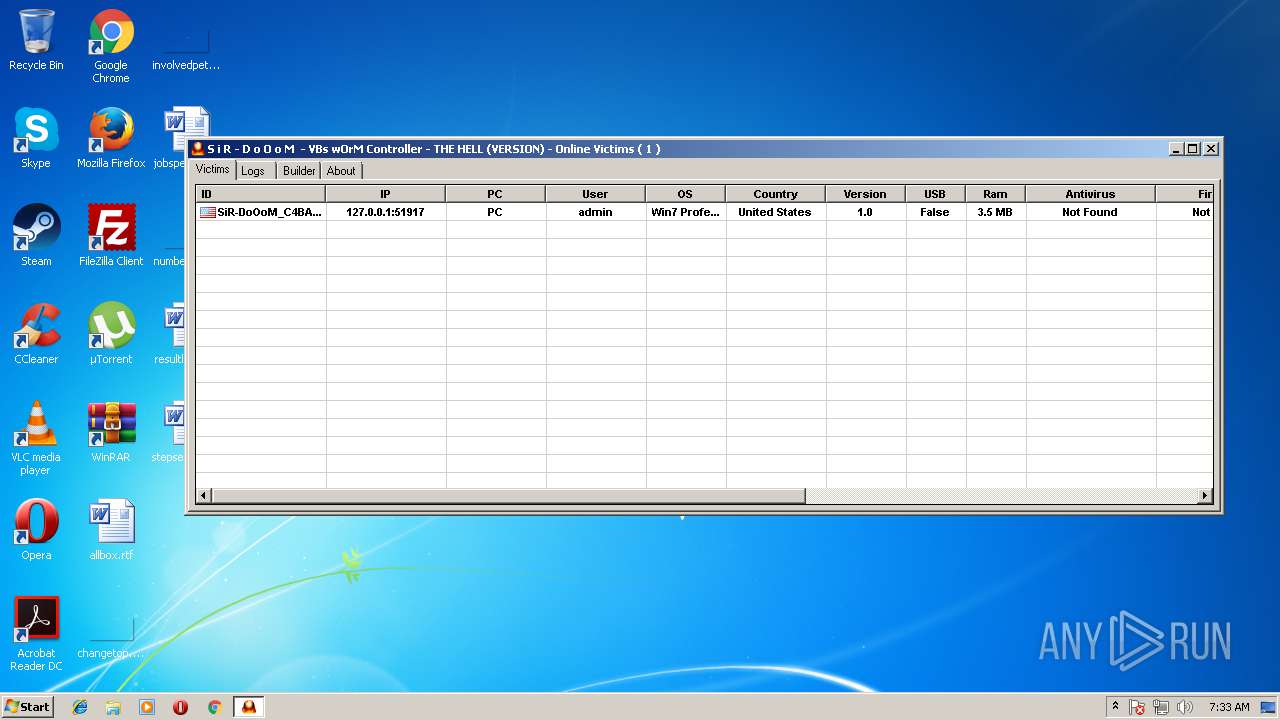
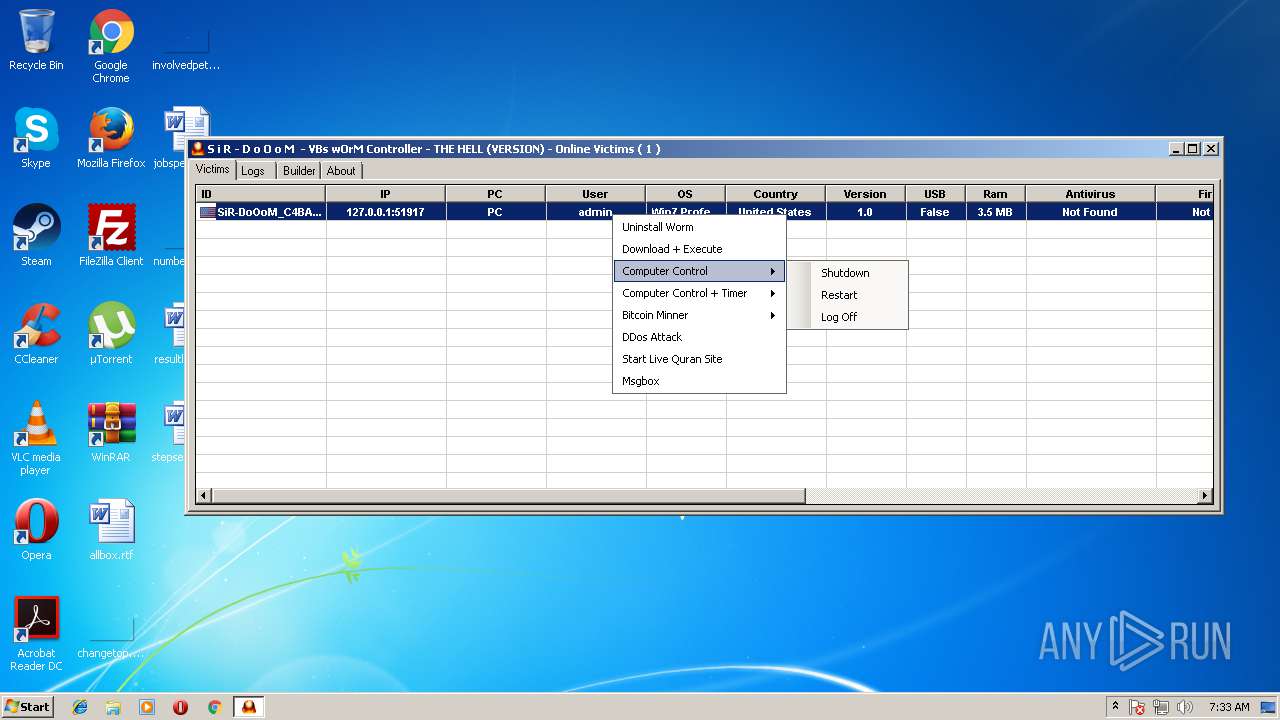
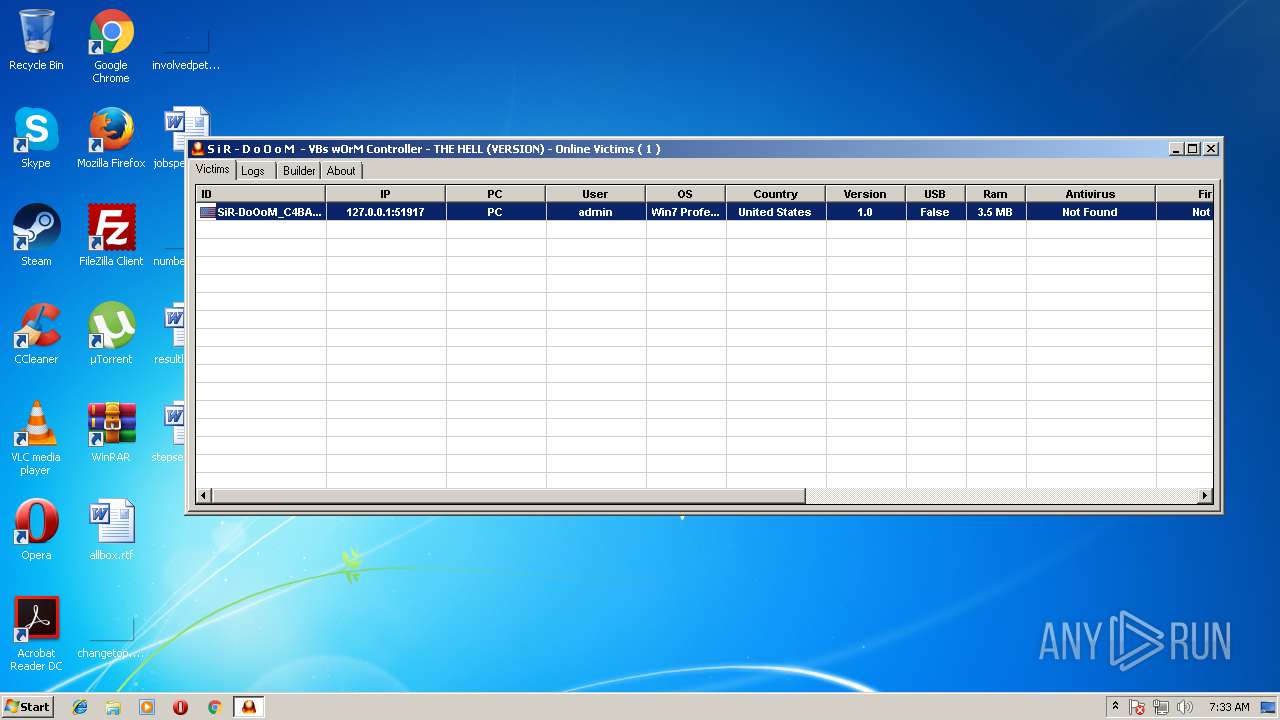
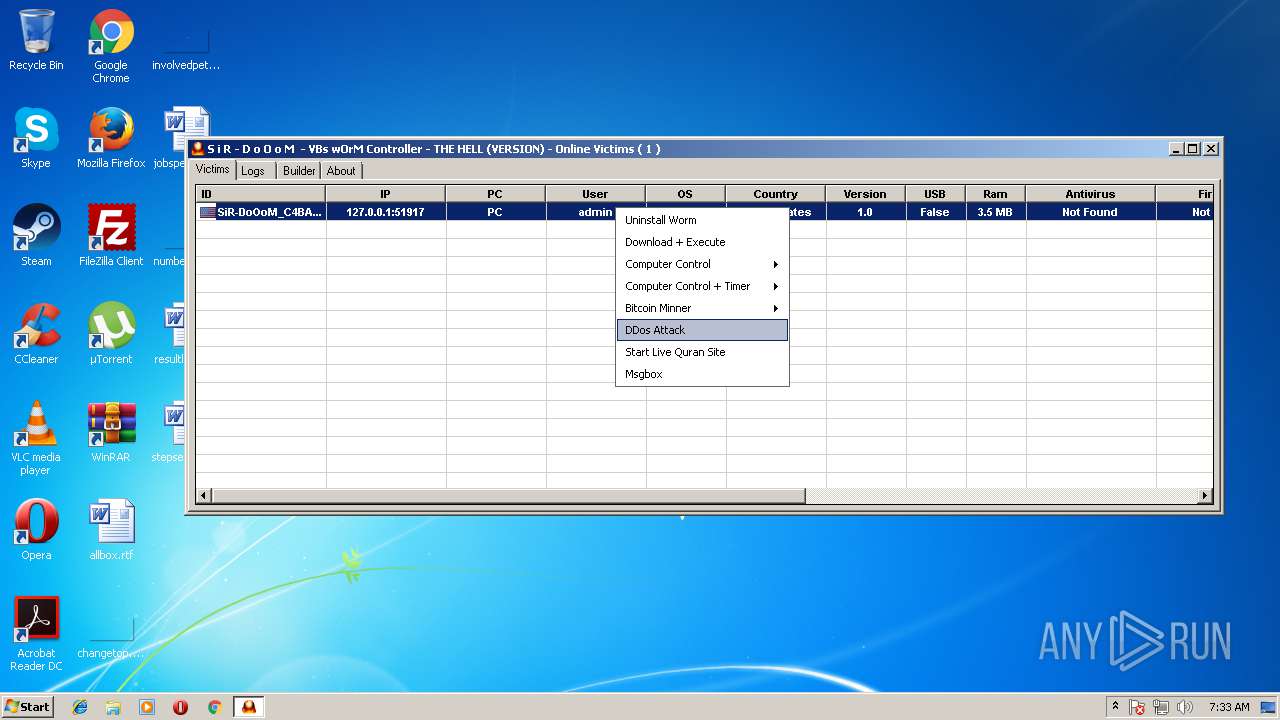
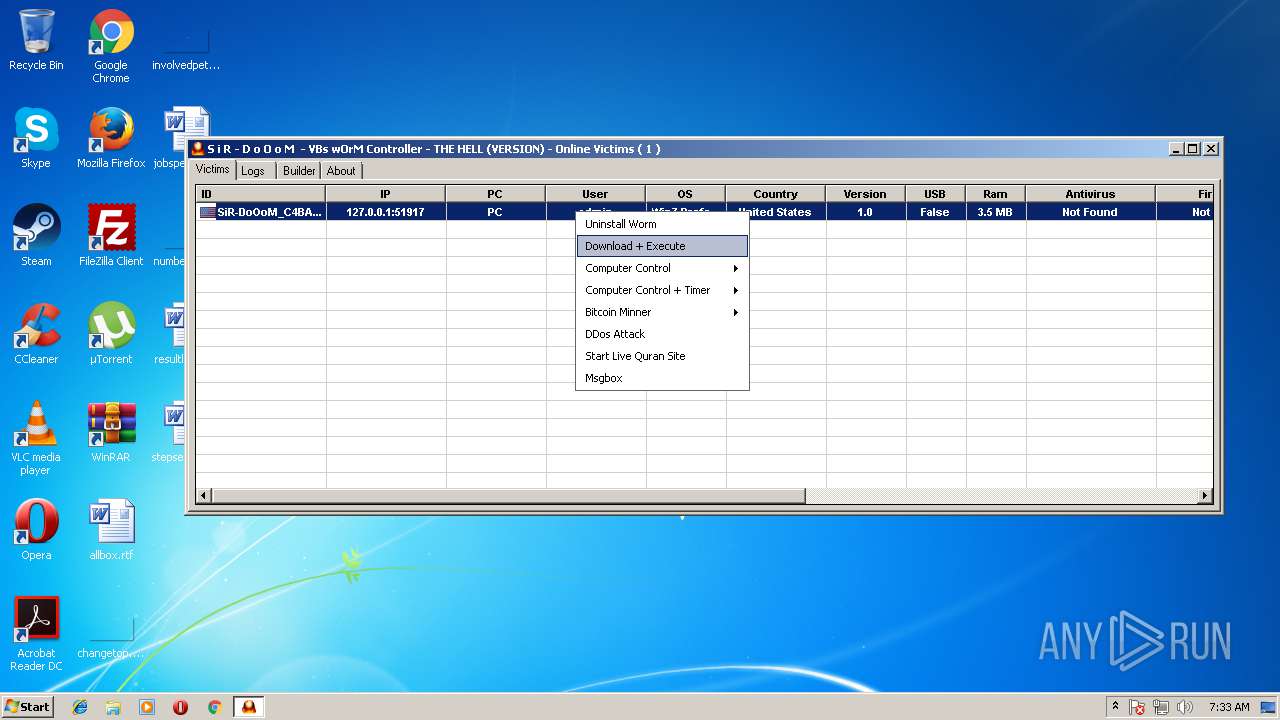
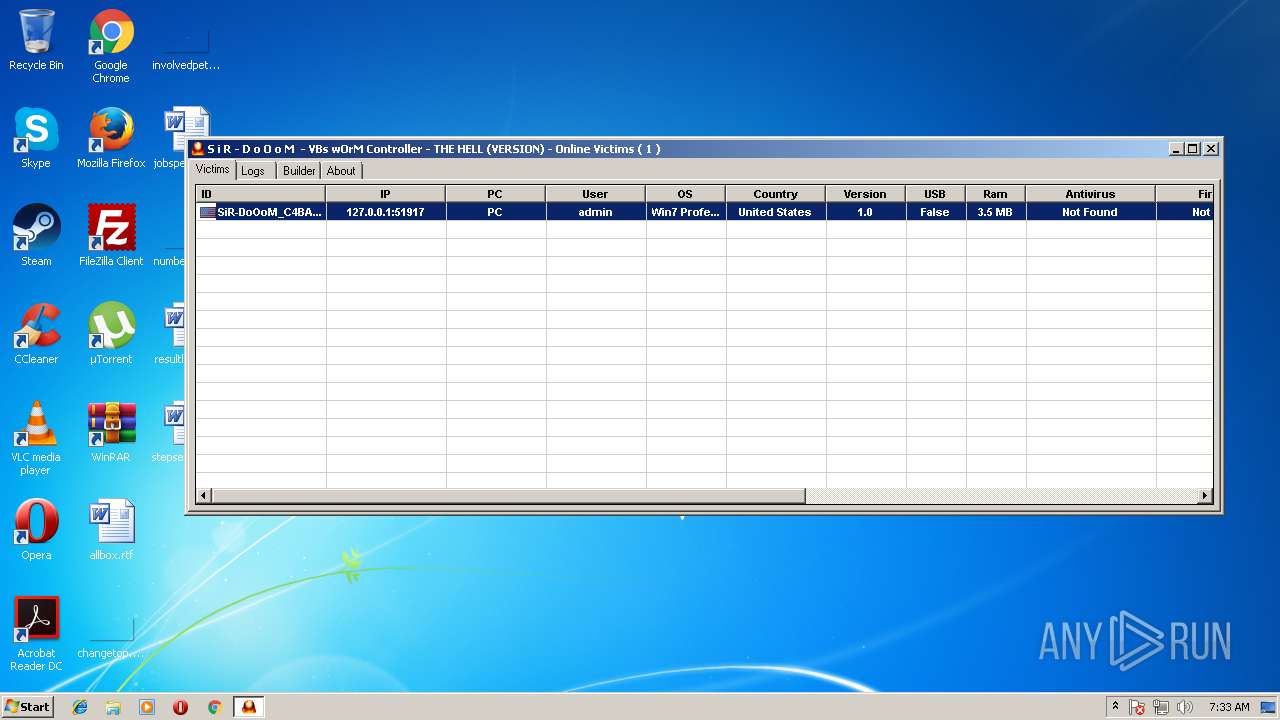
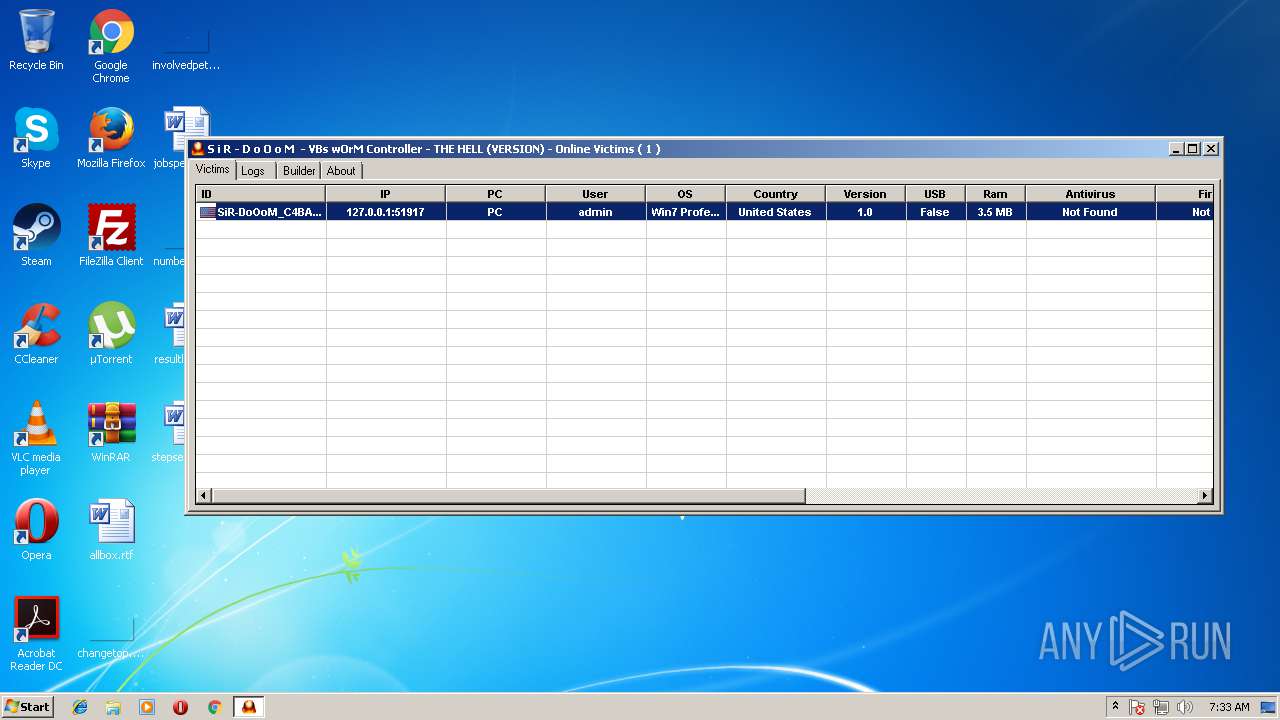
| File name: | S i R - D o O o M - VBs wOrM Controller.rar |
| Full analysis: | https://app.any.run/tasks/1d1e8182-ecb0-4e09-9c86-1e6f94caab20 |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2018, 06:30:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 00EC014444375C67C72142C66A5EF02F |
| SHA1: | 09E0DEDE6162FE81272934D383A201436AC8FA88 |
| SHA256: | 88D06393DDF5BCCFDF265E3F96ACA87187D576D8CCB4F024BB43CEDD20CC6EDF |
| SSDEEP: | 12288:vU67+zTo7CGosVFkUxLuCmdcVRpiDHnKM7iIQigZnlFF:vL7+TECnyFkUxYc8Hnd7iI2nlL |
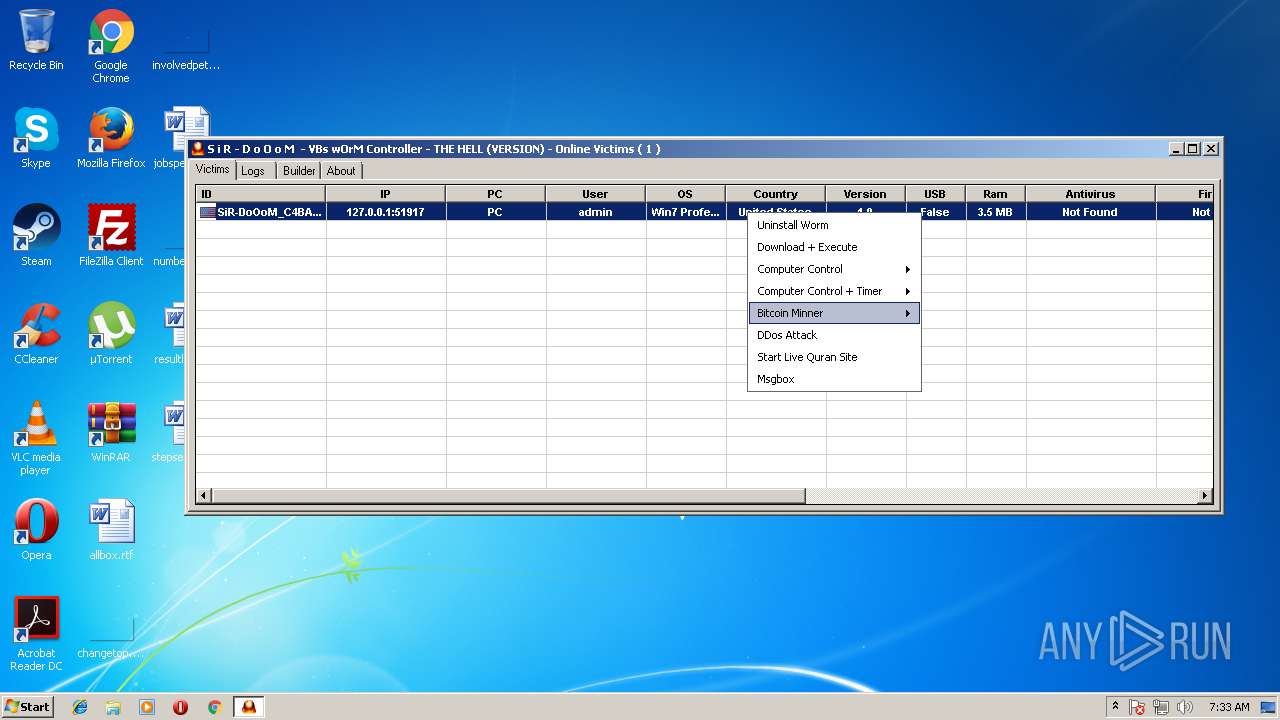
MALICIOUS
Changes the autorun value in the registry
- WScript.exe (PID: 3704)
Writes to a start menu file
- WScript.exe (PID: 3704)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3196)
- schtasks.exe (PID: 996)
- schtasks.exe (PID: 3220)
- schtasks.exe (PID: 344)
Uses Task Scheduler to run other applications
- WScript.exe (PID: 3704)
SUSPICIOUS
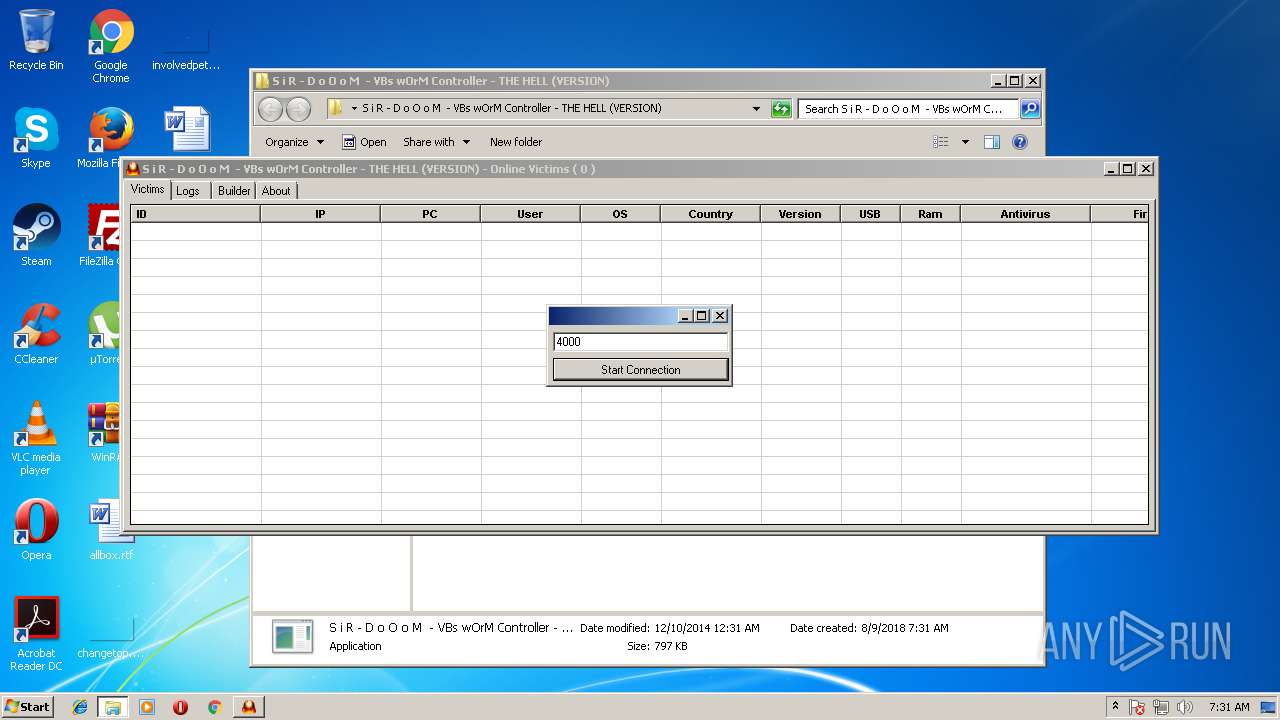
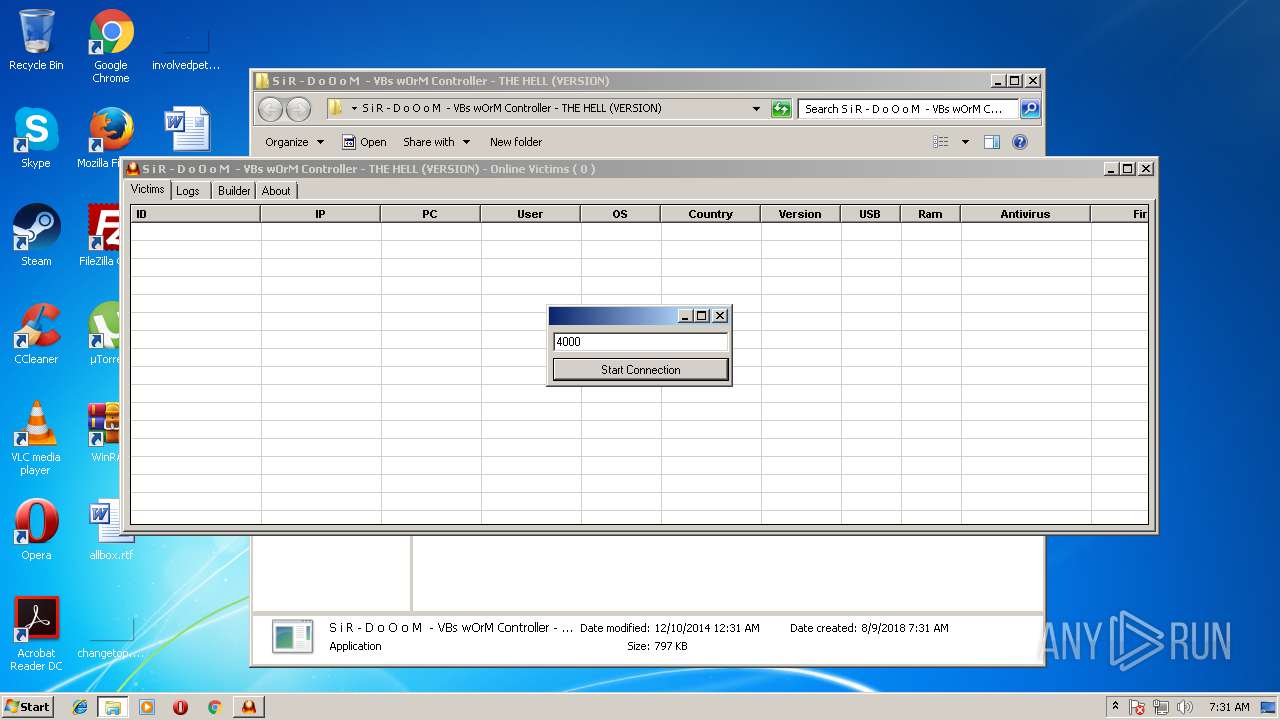
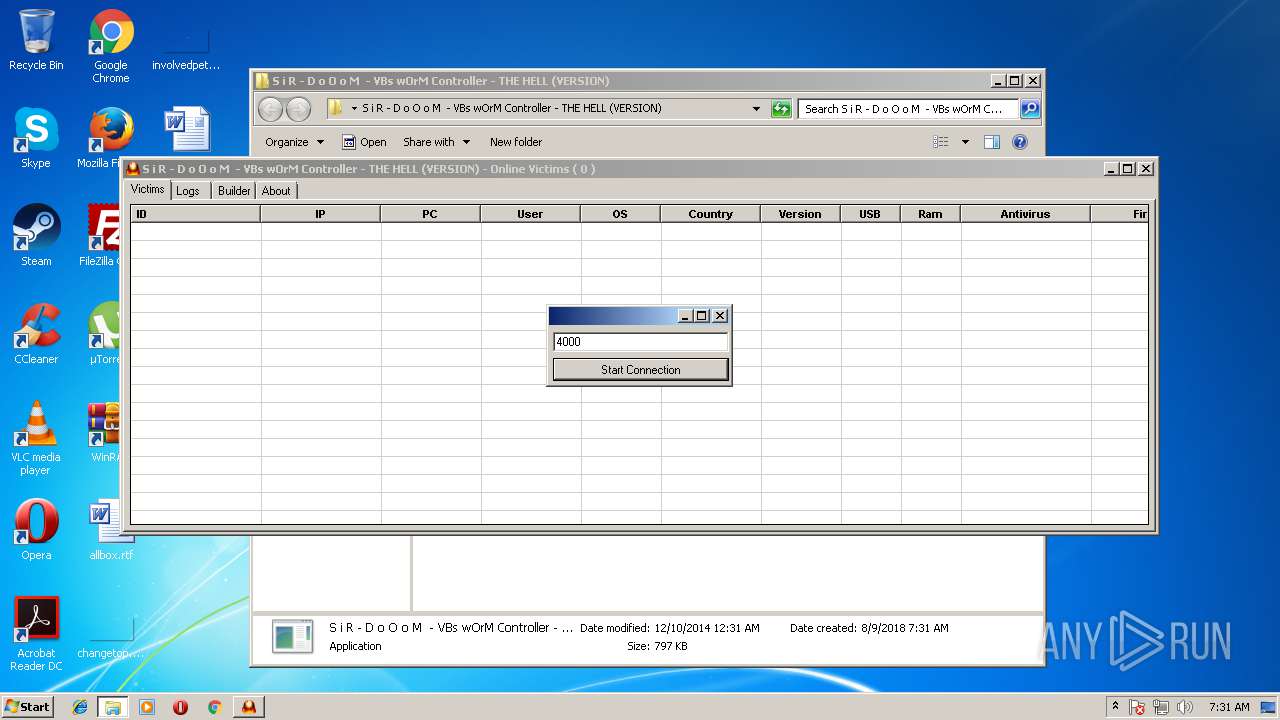
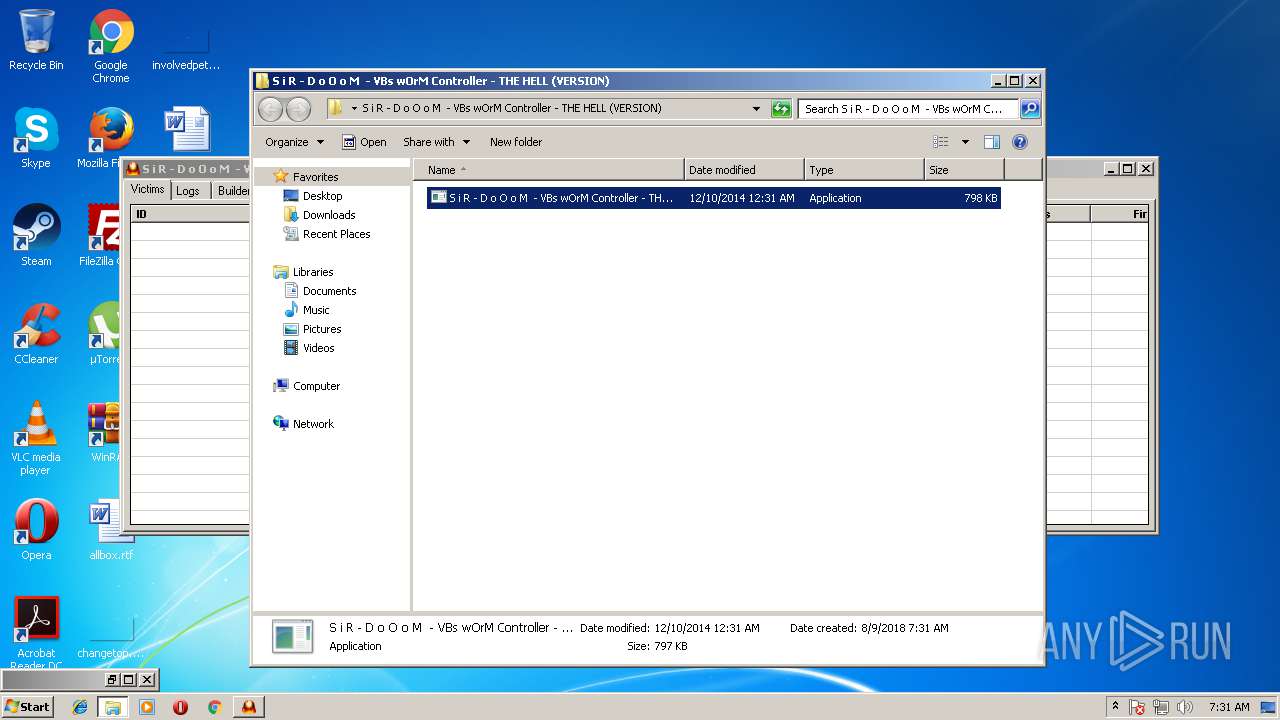
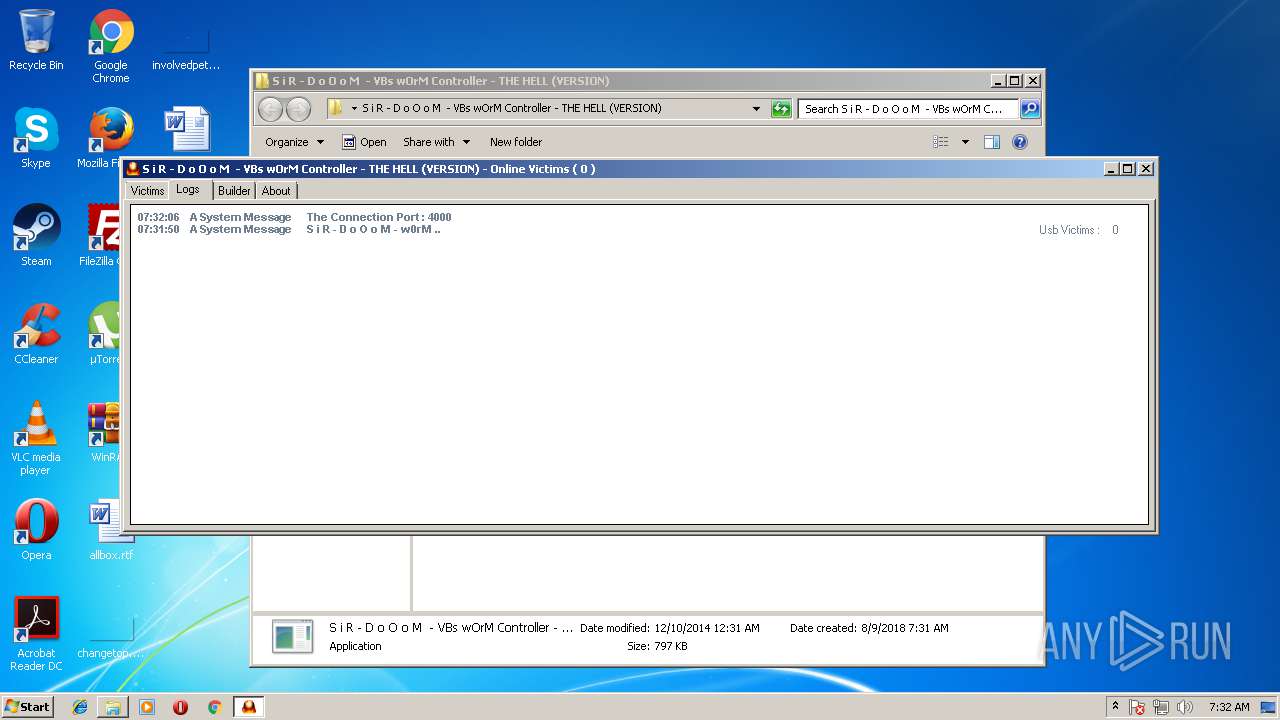
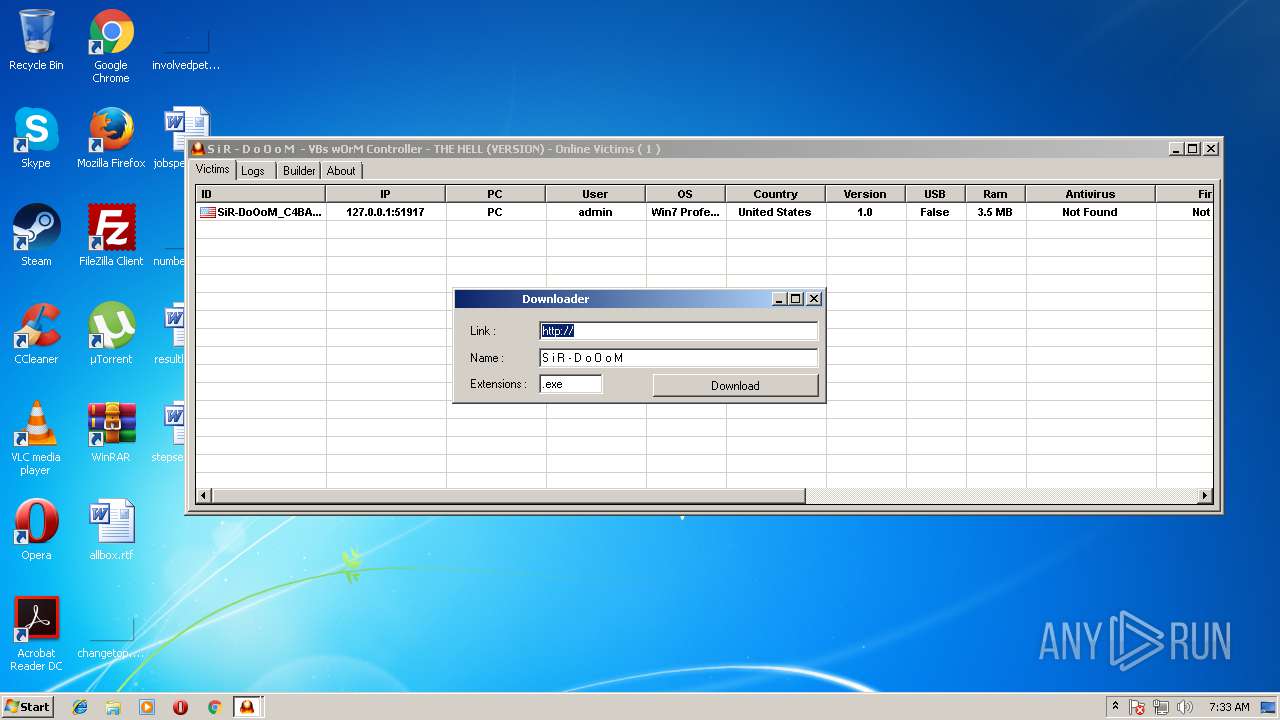
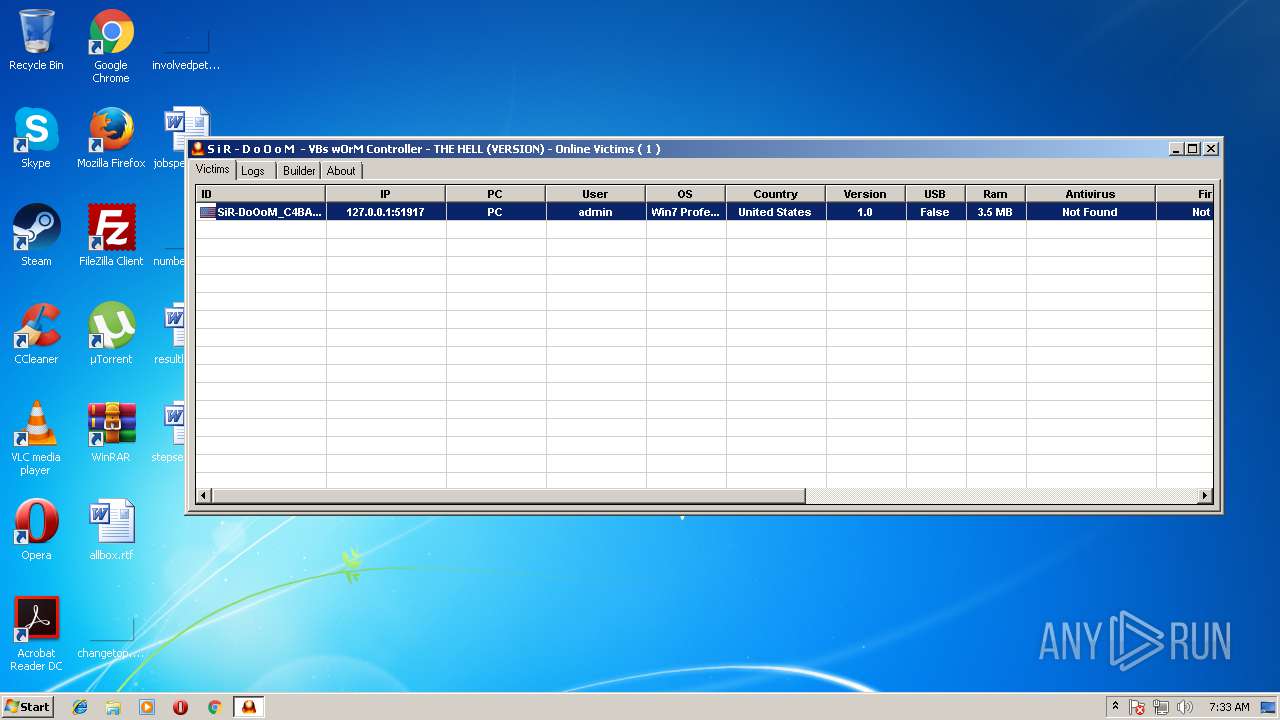
Application launched itself
- S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe (PID: 3972)
Reads Internet Cache Settings
- S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe (PID: 2548)
Starts Internet Explorer
- WScript.exe (PID: 3704)
Uses TASKKILL.EXE to kill process
- WScript.exe (PID: 3704)
Creates files in the user directory
- WScript.exe (PID: 3704)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3704)
INFO
Dropped object may contain URL's
- S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe (PID: 2548)
- iexplore.exe (PID: 1872)
- iexplore.exe (PID: 3980)
- WScript.exe (PID: 3704)
Reads Internet Cache Settings
- iexplore.exe (PID: 3980)
Reads internet explorer settings
- iexplore.exe (PID: 3980)
Changes internet zones settings
- iexplore.exe (PID: 1872)
Application launched itself
- iexplore.exe (PID: 1872)
Creates files in the user directory
- iexplore.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 661617 |
|---|---|
| UncompressedSize: | 816208 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2014:12:10 00:31:13 |
| PackingMethod: | Normal |
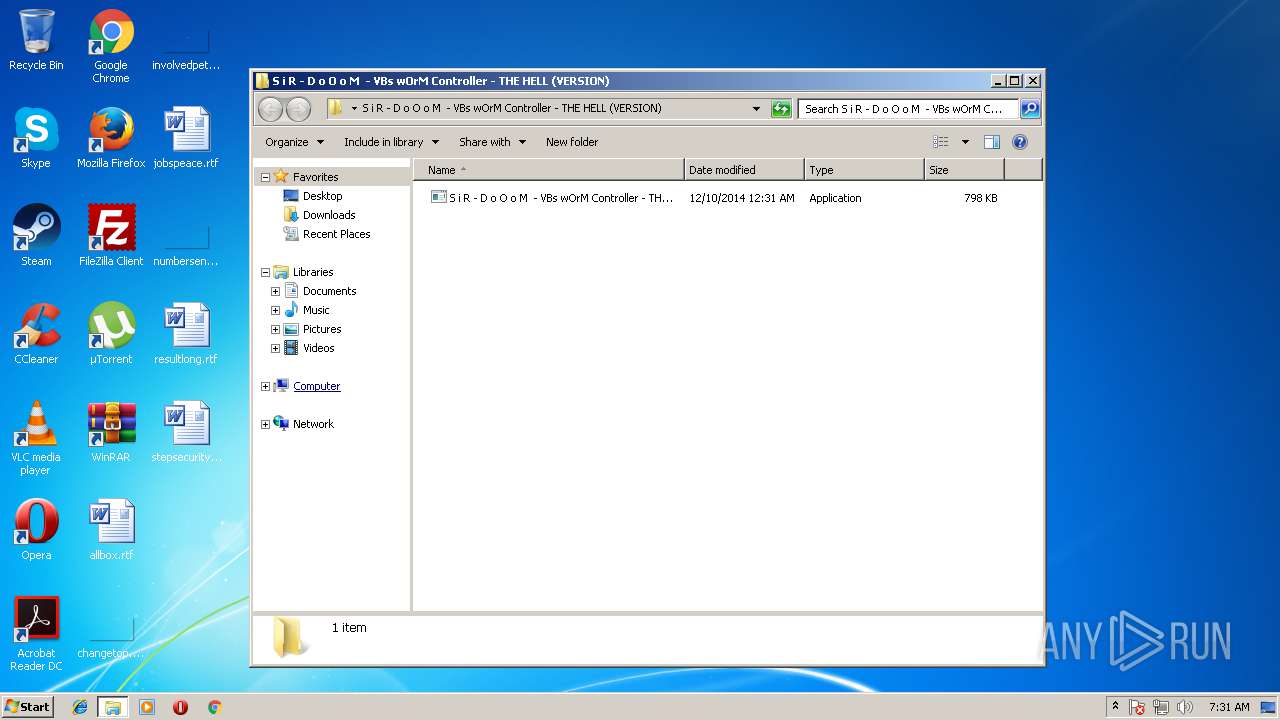
| ArchivedFileName: | S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION)\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe |
Total processes
68
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Windows\System32\schtasks.exe" /create /sc ONLOGON /RL HIGHEST /tn smss-DoOoM.vbe /tr "C:\Users\admin\AppData\Local\Temp\System\smss-DoOoMs.vbs" | C:\Windows\System32\schtasks.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | "C:\Windows\System32\schtasks.exe" /create /sc ONLOGON /RL HIGHEST /tn smss-DoOoM.vbe /tr "C:\Users\admin\AppData\Local\Temp\System\smss-DoOoMs.vbs" | C:\Windows\System32\schtasks.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | "C:\Windows\System32\taskkill.exe" /F /IM bavtray.exe | C:\Windows\System32\taskkill.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1892 | "C:\Users\admin\Desktop\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION)\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe" | C:\Users\admin\Desktop\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION)\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe | — | S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2136 | "C:\Windows\System32\taskkill.exe" /F /IM TiGeR-Firewall.exe | C:\Windows\System32\taskkill.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | "C:\Users\admin\Desktop\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION)\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe" | C:\Users\admin\Desktop\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION)\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\Desktop\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION)\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe" | C:\Users\admin\Desktop\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION)\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe | — | S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2712 | "C:\Windows\System32\taskkill.exe" /F /IM SpyTheSpy.exe | C:\Windows\System32\taskkill.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
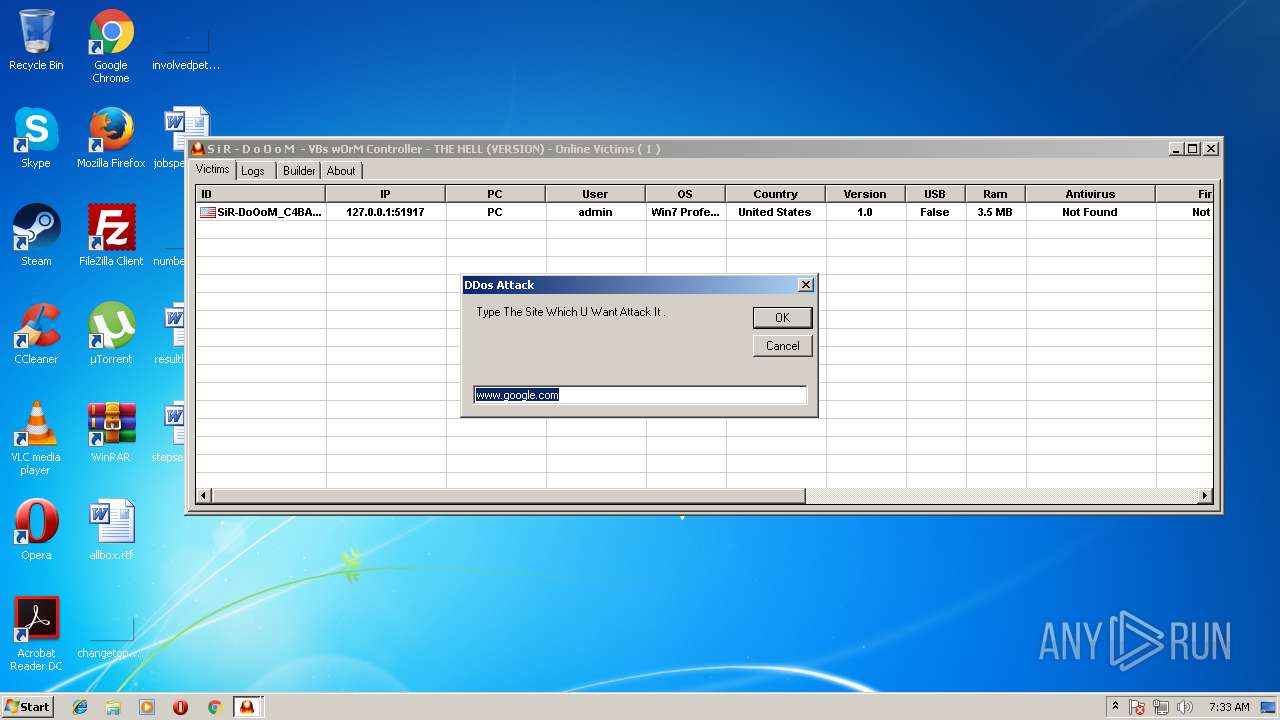
| 3164 | ping www.google.com -l 2000 -t | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 765
Read events
1 582
Write events
178
Delete events
5
Modification events
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\S i R - D o O o M - VBs wOrM Controller.rar | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF630000003E000000230400002A020000 | |||
Executable files
0
Suspicious files
2
Text files
12
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3872.43455\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION)\S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe | — | |
MD5:— | SHA256:— | |||
| 1872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3980 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MJG226QK\ww1_livequran_org[1].txt | — | |
MD5:— | SHA256:— | |||
| 1872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9D9F245CEAD69CA2.TMP | — | |
MD5:— | SHA256:— | |||
| 1872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4666B4069F1F657E.TMP | — | |
MD5:— | SHA256:— | |||
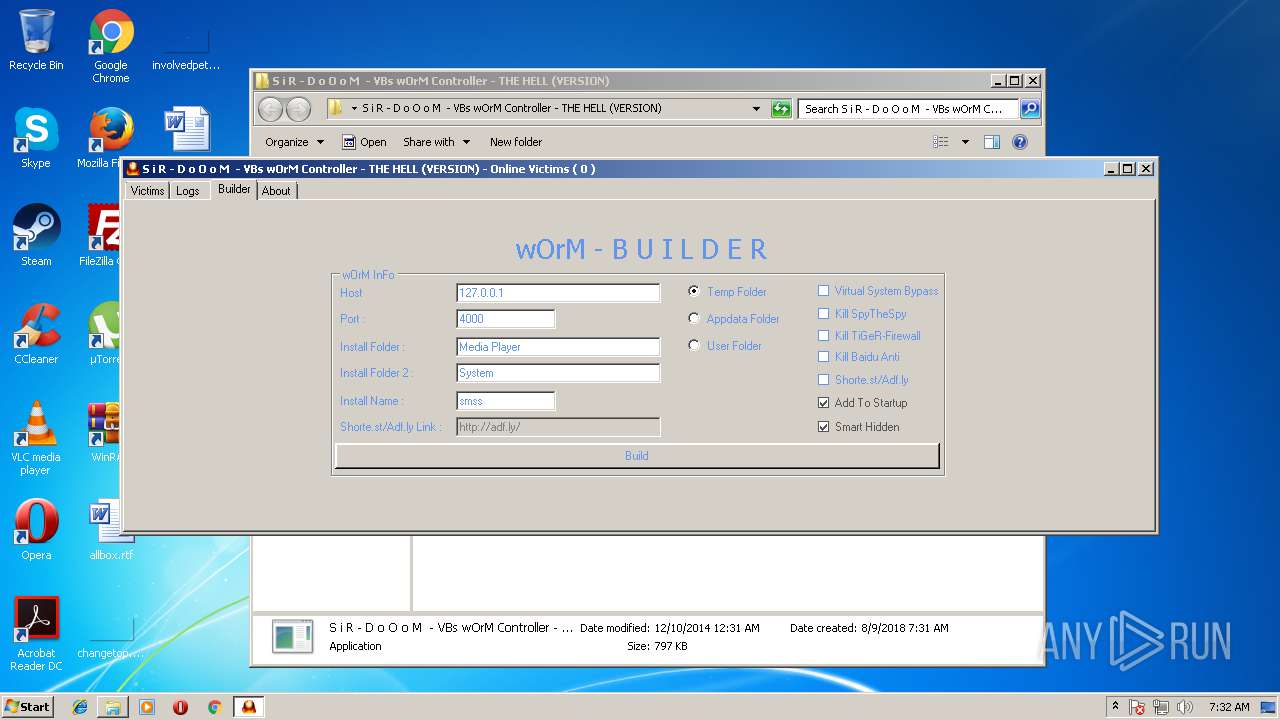
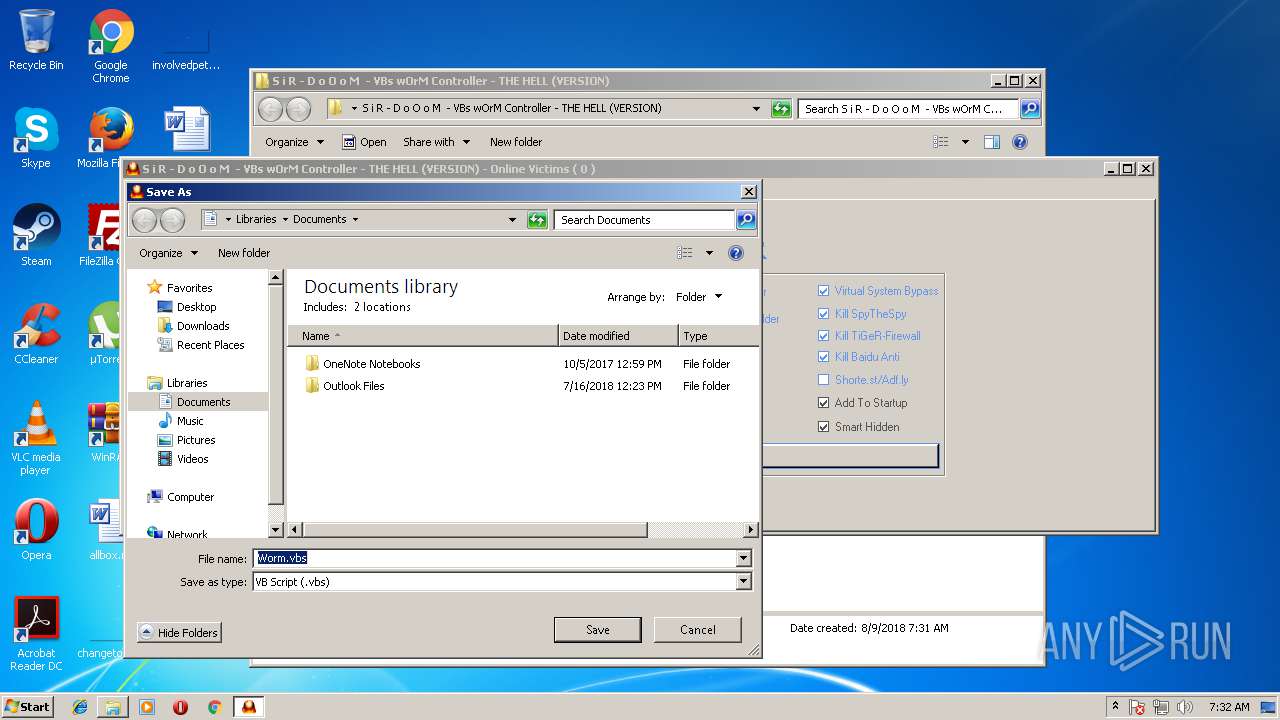
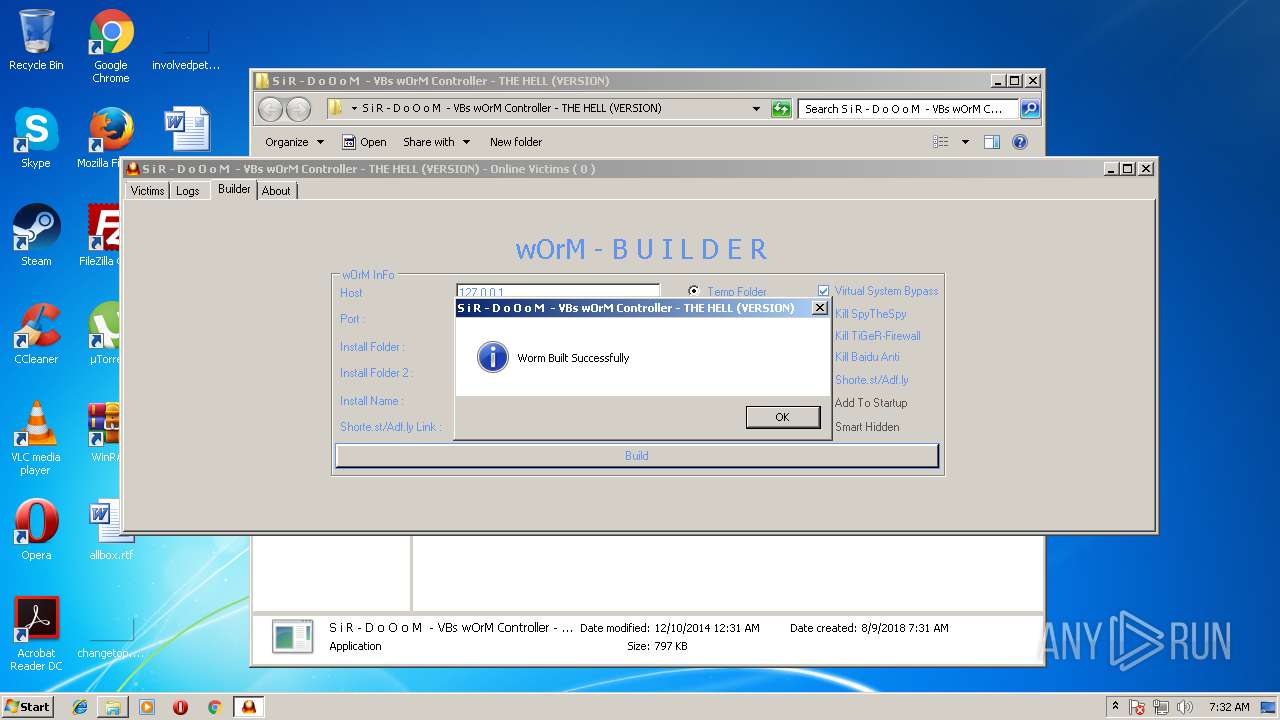
| 2548 | S i R - D o O o M - VBs wOrM Controller - THE HELL (VERSION).exe | C:\Users\admin\Desktop\Worm.vbs | text | |
MD5:— | SHA256:— | |||
| 1872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1619799143D3AA43.TMP | — | |
MD5:— | SHA256:— | |||
| 1872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{1F992A8A-9B9E-11E8-ACE5-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3704 | WScript.exe | C:\Users\admin\AppData\Local\Temp\smss-DoOoM-service\smss-DoOoMs.vbe | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
7
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
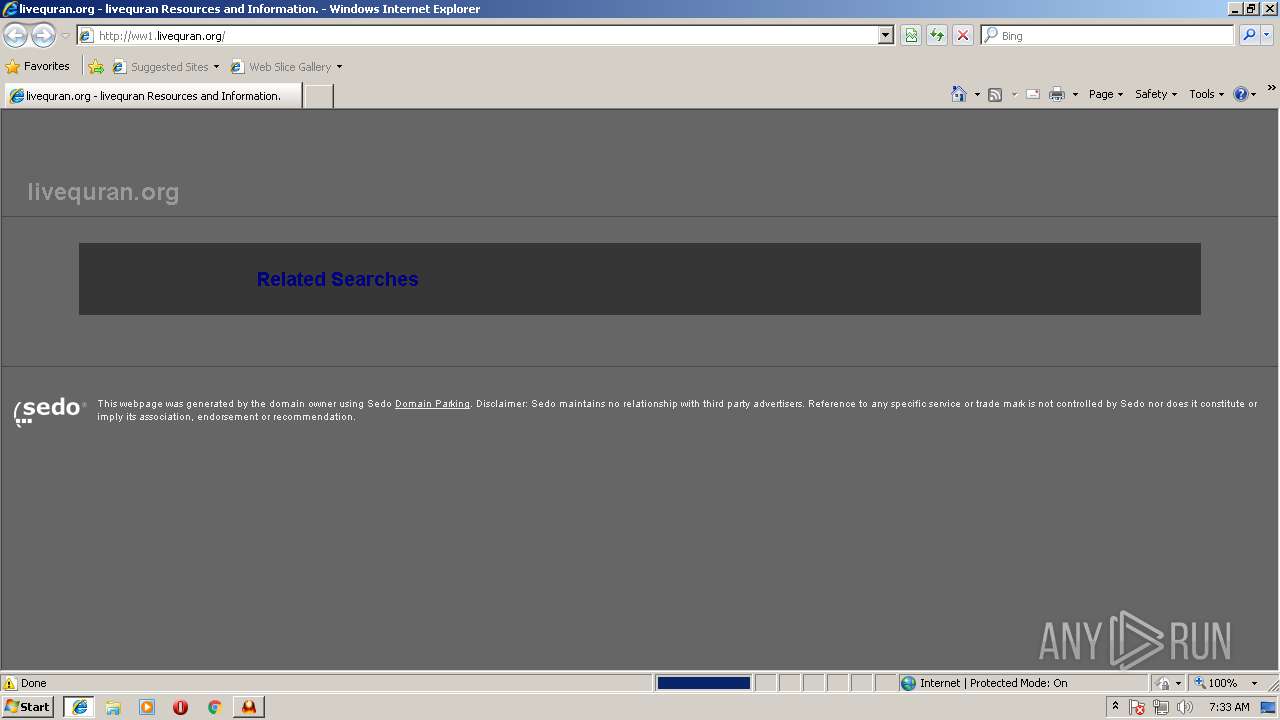
3980 | iexplore.exe | GET | 302 | 67.227.226.240:80 | http://www.livequran.org/ | US | — | — | malicious |
3980 | iexplore.exe | GET | 200 | 72.52.4.90:80 | http://ww1.livequran.org/log/jserr.php?msg=Object+doesn't+support+this+property+or+method&file=http%3A%2F%2Fwww.google.com%2Fadsense%2Fdomains%2Fcaf.js&line=362 | US | compressed | 7.90 Kb | malicious |
3980 | iexplore.exe | GET | 200 | 72.52.4.90:80 | http://ww1.livequran.org/ | US | html | 7.90 Kb | malicious |
3980 | iexplore.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/templates/brick_gfx/common/logo_white.png | US | image | 2.18 Kb | whitelisted |
3980 | iexplore.exe | GET | 200 | 72.52.4.90:80 | http://ww1.livequran.org/search/tsc.php?200=Mjg4MzEwODQx&21=ODIuMTAyLjIyLjExMQ==&681=MTUzMzc5NjQxMDc2NDdiOWVkZmNkZmIyMGY3MmY0YWRiNWI4NDZhNTc2&crc=79305fddbb884f813219cef72c7bfe090334bbe8&cv=1 | US | compressed | 7.90 Kb | malicious |
3980 | iexplore.exe | GET | 200 | 172.217.168.4:80 | http://www.google.com/adsense/domains/caf.js | US | text | 73.0 Kb | malicious |
3980 | iexplore.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/js/jquery-1.4.2.min.js | US | text | 26.1 Kb | whitelisted |
3980 | iexplore.exe | GET | 200 | 72.52.4.90:80 | http://ww1.livequran.org/log/jserr.php?msg='google'+is+undefined&file=%5Brendered+html%5D&line=100 | US | — | — | malicious |
3980 | iexplore.exe | GET | 200 | 67.225.218.50:80 | http://parking.parklogic.com/page/enhance.js?pcId=2&domain=livequran.org | US | html | 2.17 Kb | suspicious |
3980 | iexplore.exe | GET | 200 | 72.52.4.90:80 | http://ww1.livequran.org/log/jserr.php?msg=Object+doesn't+support+this+property+or+method&file=http%3A%2F%2Fwww.google.com%2Fadsense%2Fdomains%2Fcaf.js&line=362 | US | compressed | 7.90 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3980 | iexplore.exe | 67.227.226.240:80 | www.livequran.org | Liquid Web, L.L.C | US | malicious |
3980 | iexplore.exe | 72.52.4.90:80 | ww1.livequran.org | Akamai Technologies, Inc. | US | whitelisted |
3980 | iexplore.exe | 172.217.168.4:80 | www.google.com | Google Inc. | US | whitelisted |
3980 | iexplore.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
1872 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3980 | iexplore.exe | 67.225.218.50:80 | parking.parklogic.com | Liquid Web, L.L.C | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dc304.gulfup.com |
| unknown |
www.bing.com |
| whitelisted |
www.livequran.org |
| malicious |
ww1.livequran.org |
| malicious |
img.sedoparking.com |
| whitelisted |
www.google.com |
| malicious |
parking.parklogic.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3980 | iexplore.exe | Web Application Attack | SC Microsoft Edge Uint8Array - Remote Code Execution |