| File name: | 88cd063af950f0ac2b1085f148a75e9f9654f634e7262c8a22813258471dfd70 |
| Full analysis: | https://app.any.run/tasks/9aa2e839-c913-4cb0-a71b-065937ef08d0 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2024, 20:32:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {4EC82513-0279-4313-850F-996E4FDD9AFE}, Number of Words: 10, Subject: Oovi Appc, Author: Yuwei Qusi, Name of Creating Application: Oovi Appc, Template: x64;1033, Comments: This installer database contains the logic and data required to install Oovi Appc., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Sun Nov 24 19:56:54 2024, Last Saved Time/Date: Sun Nov 24 19:56:54 2024, Last Printed: Sun Nov 24 19:56:54 2024, Number of Pages: 450 |
| MD5: | DCE26534527D10B00359837951A4F672 |
| SHA1: | 35F2BF722F71AC7D356ACA4D097099A8CC3FEC23 |
| SHA256: | 88CD063AF950F0AC2B1085F148A75E9F9654F634E7262C8A22813258471DFD70 |
| SSDEEP: | 393216:1tCV/lfl4WYP56O+X0lFe/pIrr/VjW47CYSBhJWSEl:Lutfh05Y08p85jW4shW |
MALICIOUS
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 4008)
Bypass execution policy to execute commands
- powershell.exe (PID: 3984)
SUSPICIOUS
The process executes Powershell scripts
- msiexec.exe (PID: 4008)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 4008)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 4008)
The process drops C-runtime libraries
- msiexec.exe (PID: 6096)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 4008)
Process drops legitimate windows executable
- msiexec.exe (PID: 6096)
INFO
Reads the computer name
- msiexec.exe (PID: 6096)
Checks supported languages
- msiexec.exe (PID: 6096)
An automatically generated document
- msiexec.exe (PID: 3688)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {4EC82513-0279-4313-850F-996E4FDD9AFE} |
| Words: | 10 |
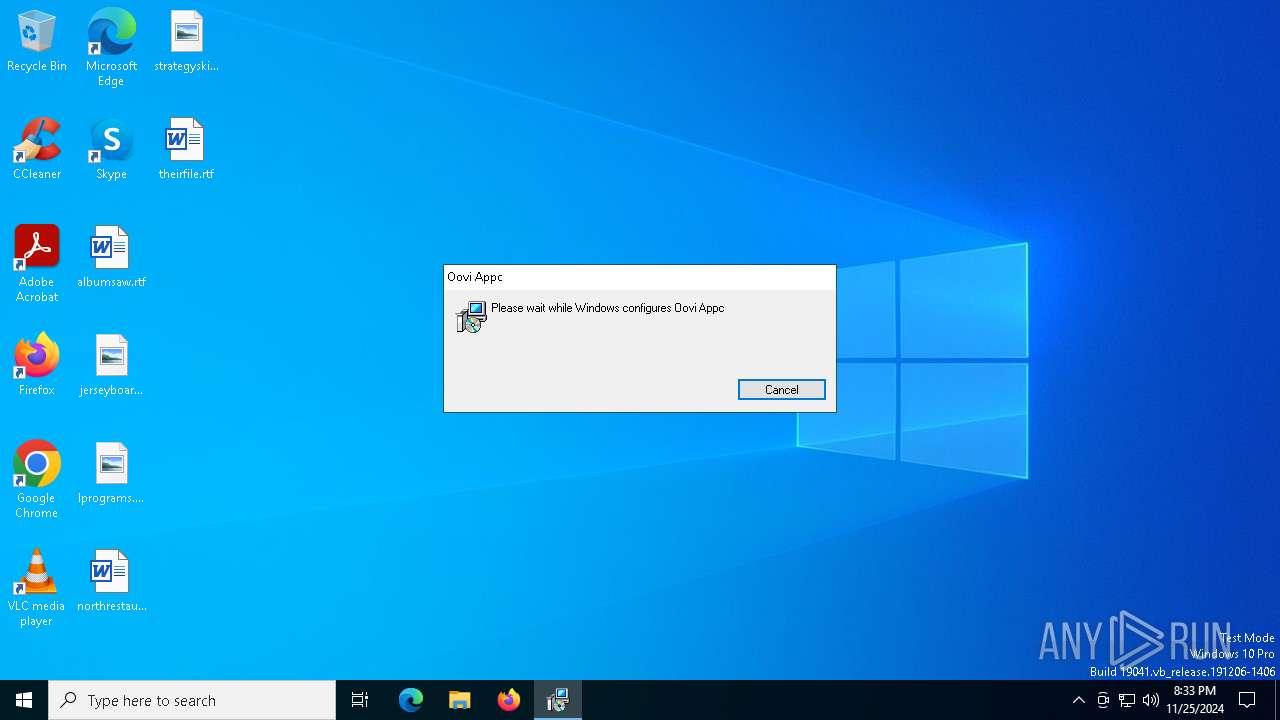
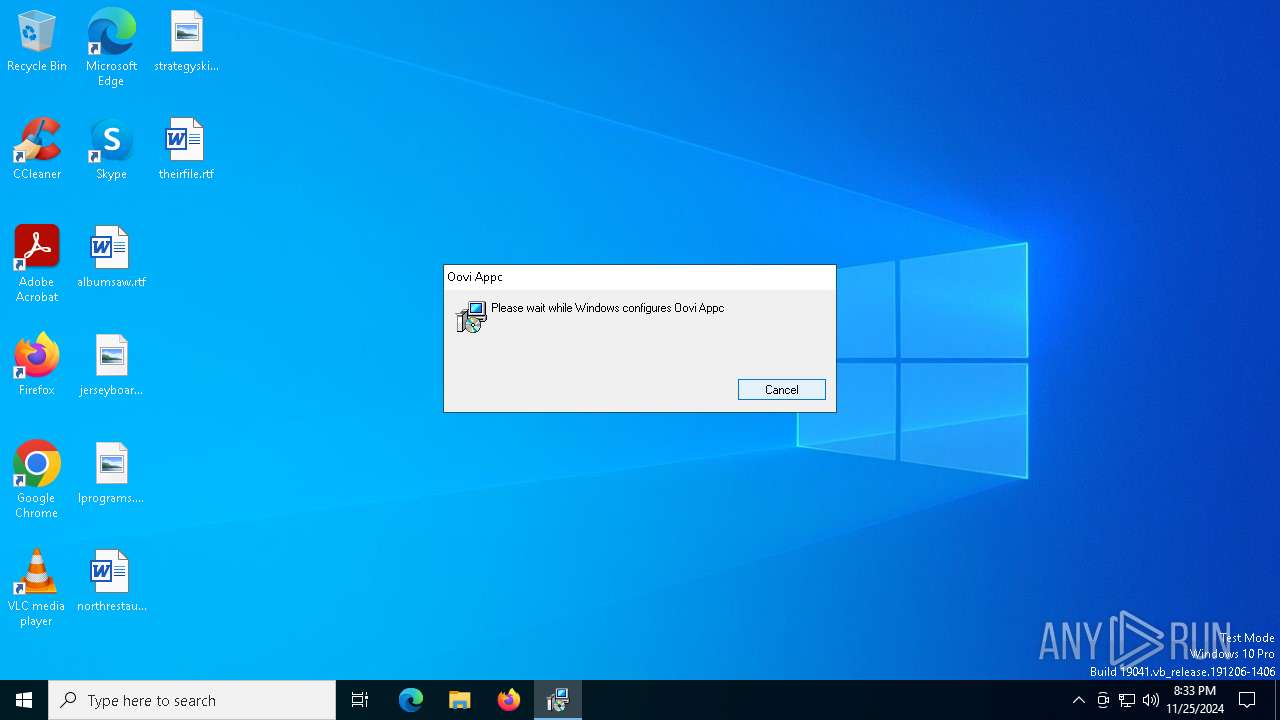
| Subject: | Oovi Appc |
| Author: | Yuwei Qusi |
| LastModifiedBy: | - |
| Software: | Oovi Appc |
| Template: | x64;1033 |
| Comments: | This installer database contains the logic and data required to install Oovi Appc. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:11:24 19:56:54 |
| ModifyDate: | 2024:11:24 19:56:54 |
| LastPrinted: | 2024:11:24 19:56:54 |
| Pages: | 450 |
Total processes
129
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3688 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\88cd063af950f0ac2b1085f148a75e9f9654f634e7262c8a22813258471dfd70.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3984 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss8EE8.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi8EE5.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr8EE6.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr8EE7.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4008 | C:\Windows\syswow64\MsiExec.exe -Embedding 551B58225ED67FCB79D64FAD2E25E36C | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6096 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6252 | "C:\Users\admin\AppData\Roaming\Yuwei Qusi\Oovi Appc\openvpn.exe" | C:\Users\admin\AppData\Roaming\Yuwei Qusi\Oovi Appc\openvpn.exe | — | msiexec.exe | |||||||||||
User: admin Company: The OpenVPN Project Integrity Level: MEDIUM Description: OpenVPN Daemon Exit code: 0 Version: 2.6.12.0 Modules
| |||||||||||||||
| 6264 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | openvpn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 314
Read events
9 175
Write events
130
Delete events
9
Modification events
| (PID) Process: | (6096) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: D01700001B657338793FDB01 | |||
| (PID) Process: | (6096) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 1109F5C75DA639F82A9CD0151A4D637E998CC82DC29835F1CC4ABA62CBD50D1C | |||
| (PID) Process: | (6096) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (4008) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4008) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4008) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6096) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (6096) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\13718c.rbs |
Value: 31145849 | |||
| (PID) Process: | (6096) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\13718c.rbsLow |
Value: | |||
| (PID) Process: | (6096) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Users\admin\AppData\Roaming\Microsoft\Installer\ |
Value: | |||
Executable files
43
Suspicious files
86
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6096 | msiexec.exe | C:\Windows\Installer\13718a.msi | — | |
MD5:— | SHA256:— | |||
| 4008 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi8EE5.txt | — | |
MD5:— | SHA256:— | |||
| 4008 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr8EE6.ps1 | — | |
MD5:— | SHA256:— | |||
| 4008 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr8EE7.txt | — | |
MD5:— | SHA256:— | |||
| 4008 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss8EE8.ps1 | — | |
MD5:— | SHA256:— | |||
| 6096 | msiexec.exe | C:\Windows\Installer\MSI741C.tmp | executable | |
MD5:EE09D6A1BB908B42C05FD0BEEB67DFD2 | SHA256:7BBF611F5E2A16439DC8CD11936F6364F6D5CC0044545C92775DA5646AFC7752 | |||
| 6096 | msiexec.exe | C:\Windows\Installer\MSI746B.tmp | executable | |
MD5:EE09D6A1BB908B42C05FD0BEEB67DFD2 | SHA256:7BBF611F5E2A16439DC8CD11936F6364F6D5CC0044545C92775DA5646AFC7752 | |||
| 6096 | msiexec.exe | C:\Windows\Installer\MSI73AD.tmp | executable | |
MD5:EE09D6A1BB908B42C05FD0BEEB67DFD2 | SHA256:7BBF611F5E2A16439DC8CD11936F6364F6D5CC0044545C92775DA5646AFC7752 | |||
| 6096 | msiexec.exe | C:\Windows\Installer\MSI72C2.tmp | executable | |
MD5:EE09D6A1BB908B42C05FD0BEEB67DFD2 | SHA256:7BBF611F5E2A16439DC8CD11936F6364F6D5CC0044545C92775DA5646AFC7752 | |||
| 6096 | msiexec.exe | C:\Windows\Installer\MSI9F88.tmp | executable | |
MD5:E0BFA64EEFA440859C8525DFEC1962D0 | SHA256:8E1B93631C730C9ECDADF15477CCA540A45A8935EF200A435BA84E15D4B1C80F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
34
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.41.248:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.25.170:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4008 | msiexec.exe | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
4008 | msiexec.exe | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
6408 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6408 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5972 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.41.248:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.25.170:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.161:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 23.52.181.141:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
key-keys.com |
| unknown |
c.pki.goog |
| whitelisted |