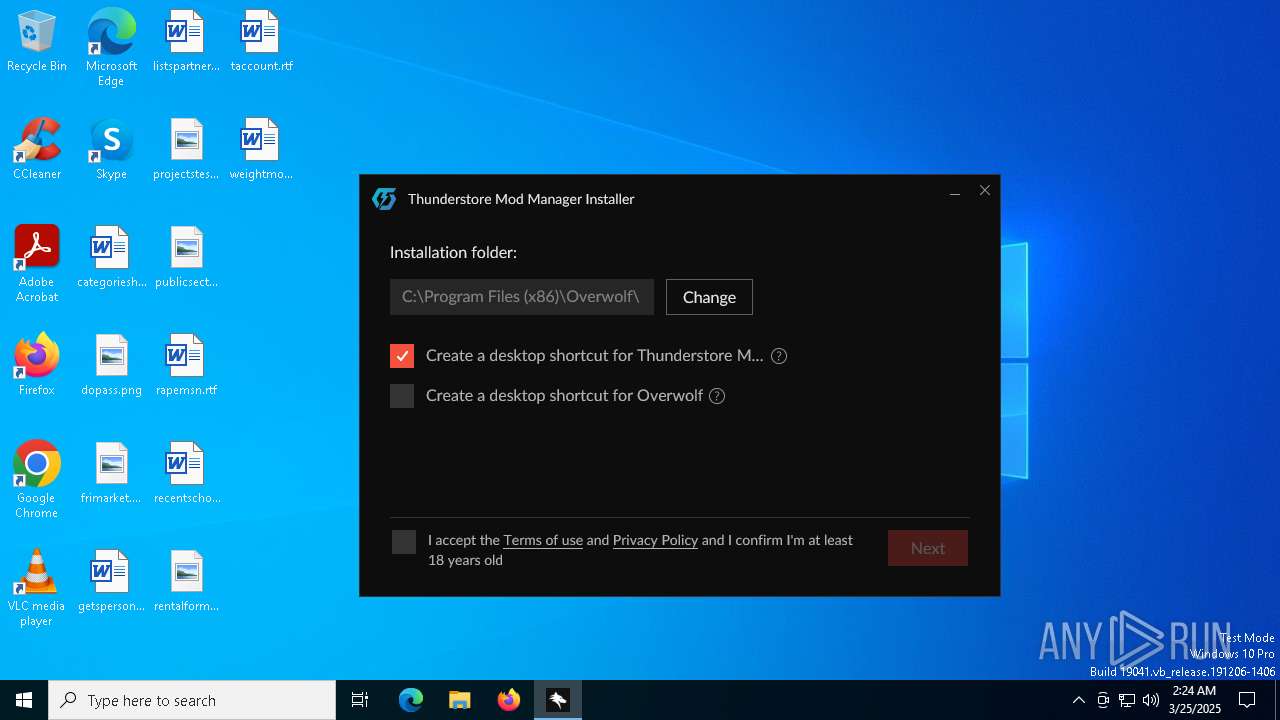
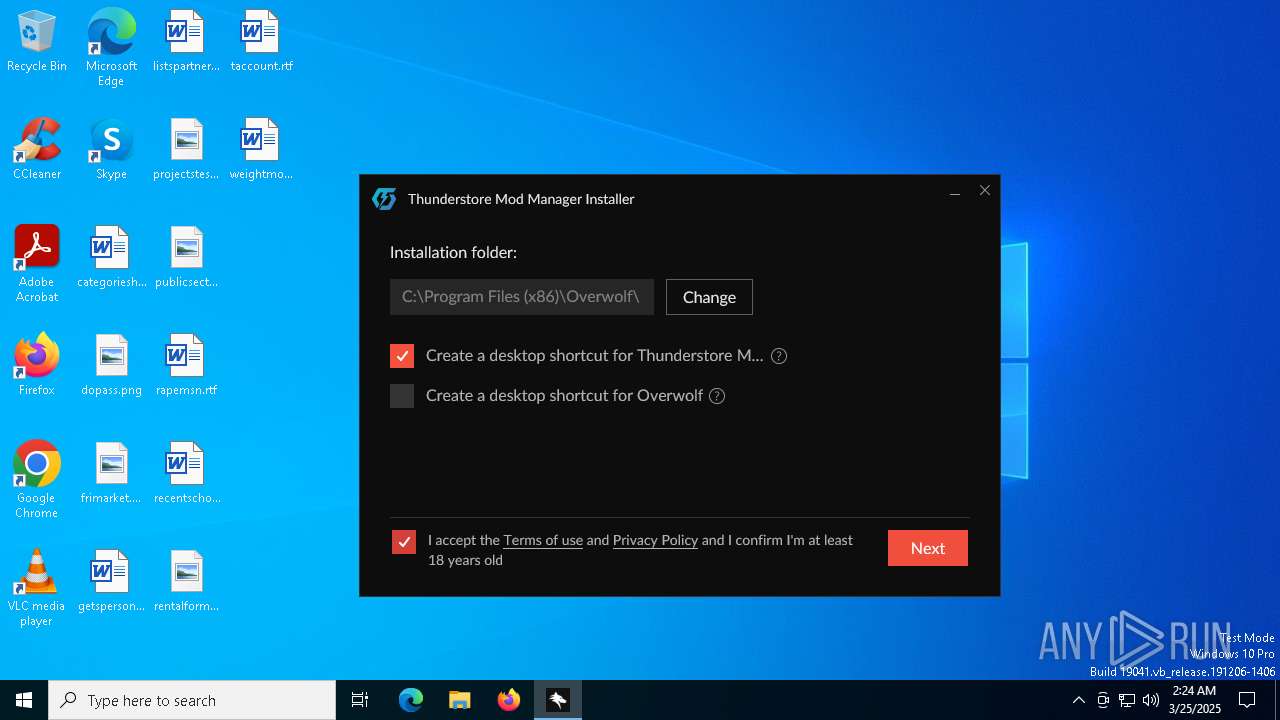
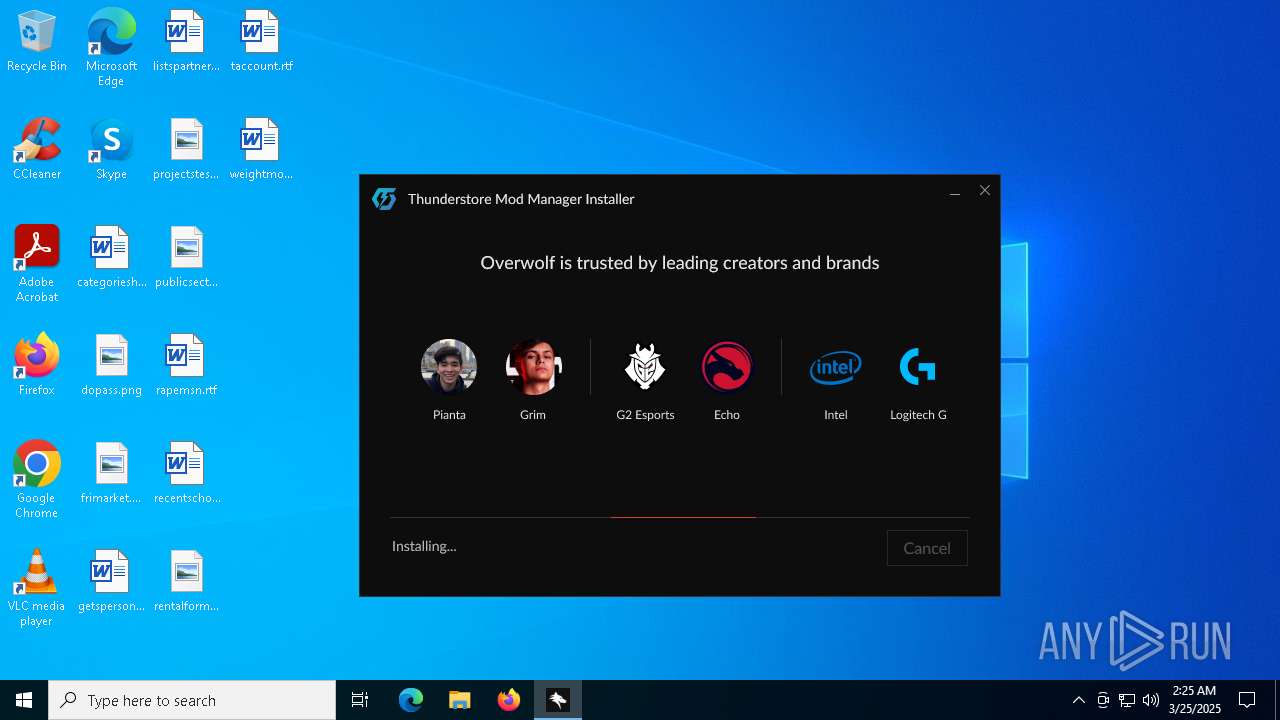
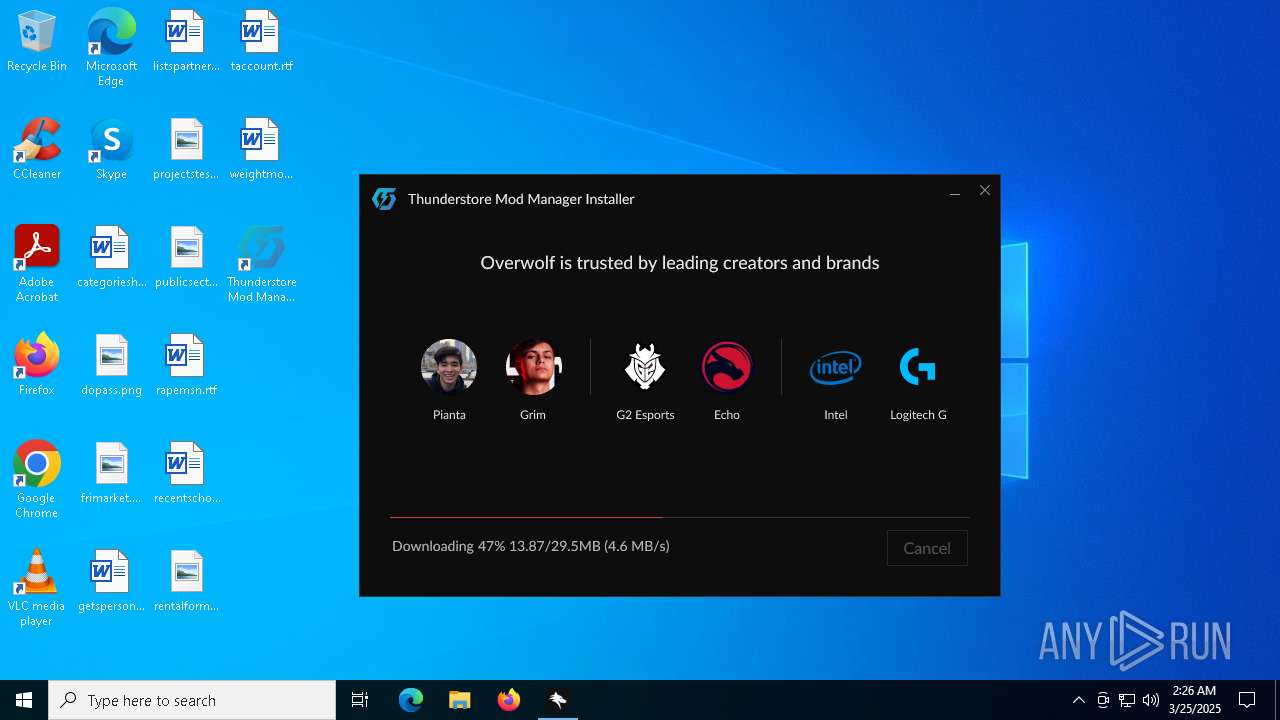
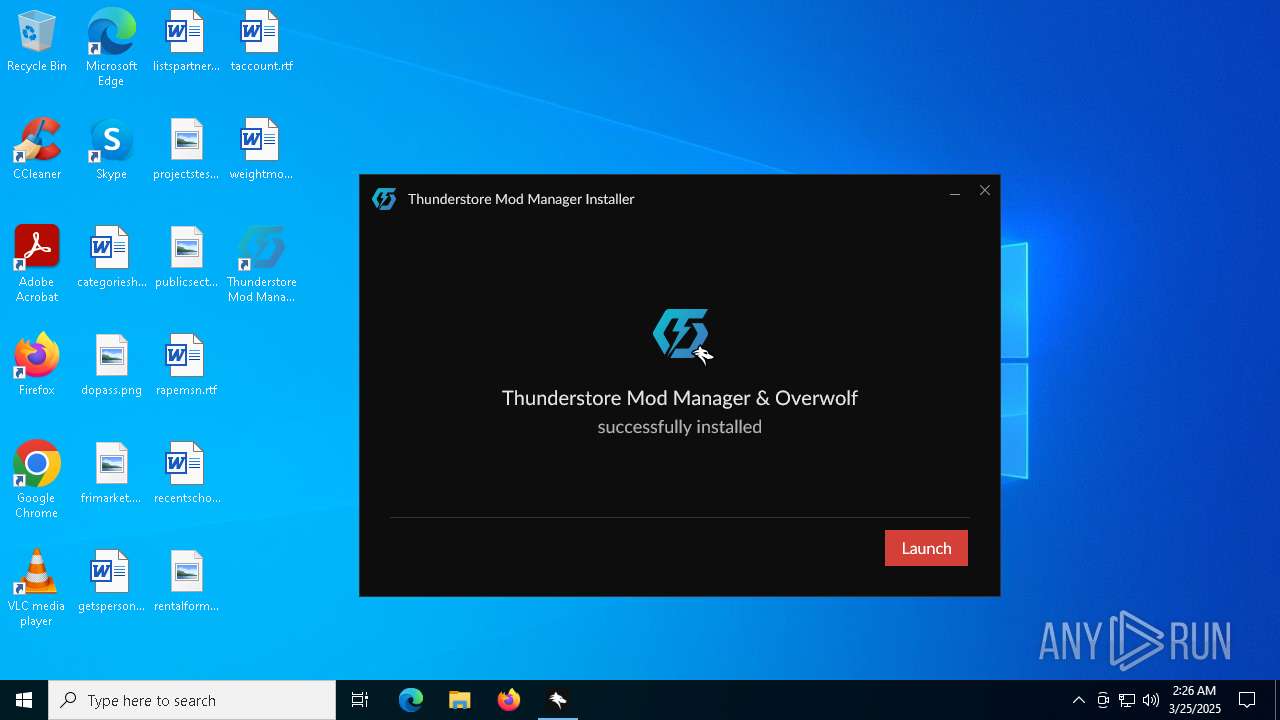
| File name: | Thunderstore Mod Manager - Installer.exe |
| Full analysis: | https://app.any.run/tasks/f0bb6289-175d-4d37-8c40-c6f32c6b7ad4 |
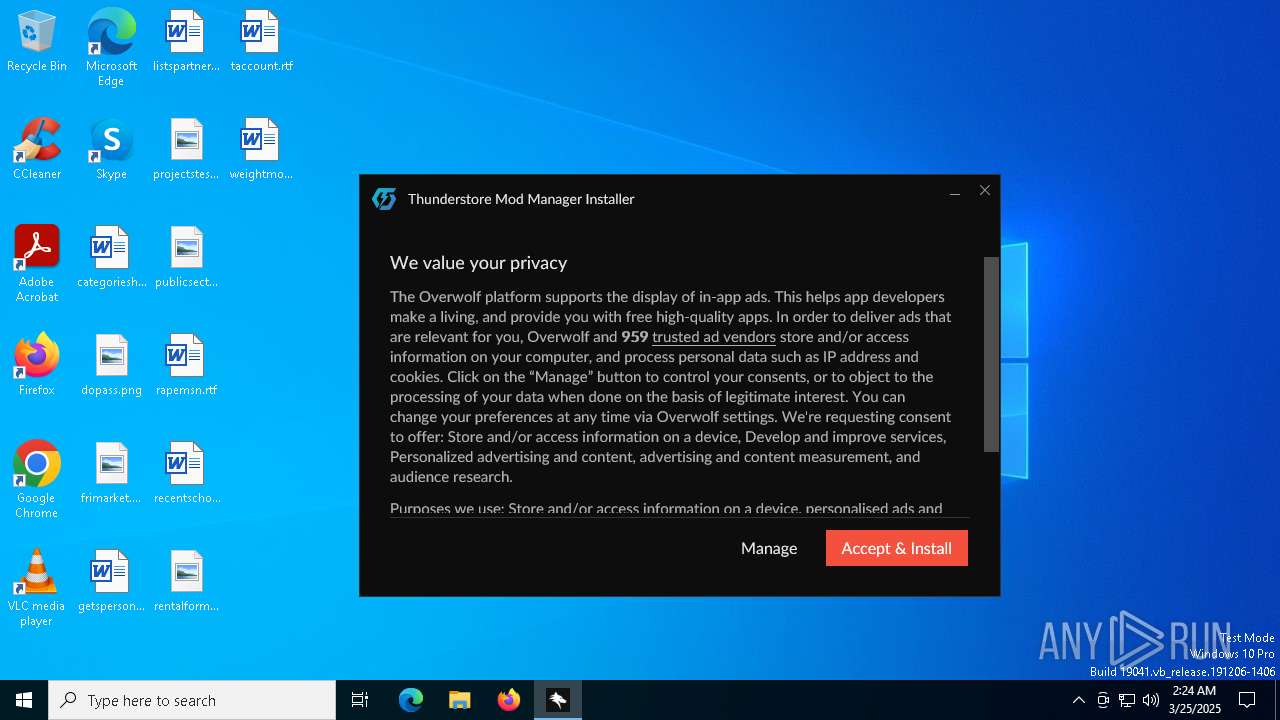
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 02:23:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | E5B5234BC4627F4D627210873F1482EF |
| SHA1: | 77C3A89C68FF831DE8F25660CE4FC8DB08ECE30E |
| SHA256: | 88C996AFFD1B459B1F4462CADBF4FD854D25761BDA02CE7E7FA2AFF48A0516ED |
| SSDEEP: | 98304:R//rhEGJ/A9nGcRa1xXcVsy3RxeLLCIJgap176MVhBIHtugzPFMNxs3JPAWQPIap:ZIYaROW |
MALICIOUS
Changes the autorun value in the registry
- OWInstaller.exe (PID: 7596)
- VC_redist.x64.exe (PID: 2776)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- OverwolfSetup.exe (PID: 6300)
Reads security settings of Internet Explorer
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- OWInstaller.exe (PID: 7596)
- OverwolfSetup.exe (PID: 6300)
- OverwolfUpdater.exe (PID: 6644)
- vcredist.exe (PID: 7100)
- OverwolfLauncher.exe (PID: 2088)
- OverwolfLauncher.exe (PID: 5968)
- Overwolf.exe (PID: 7520)
- VC_redist.x64.exe (PID: 7372)
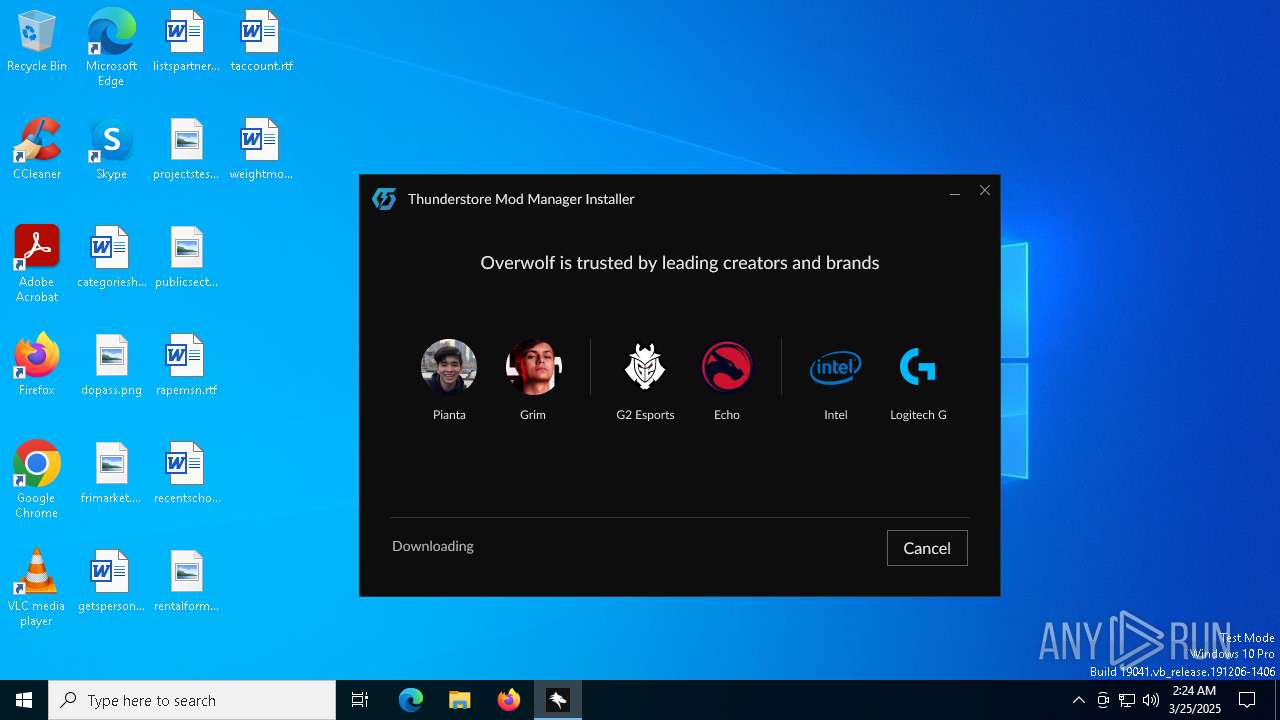
Application launched itself
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- OverwolfLauncher.exe (PID: 2088)
- VC_redist.x64.exe (PID: 6572)
- VC_redist.x64.exe (PID: 7372)
The process creates files with name similar to system file names
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- OverwolfSetup.exe (PID: 6300)
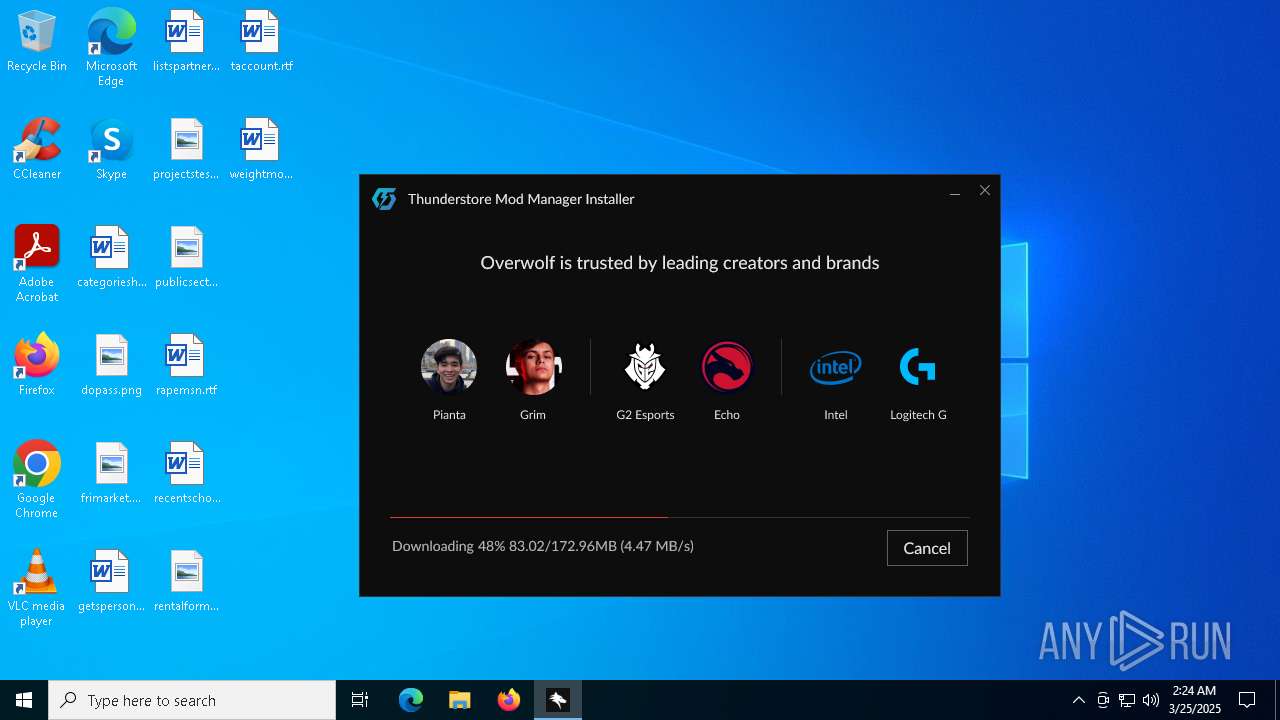
Executable content was dropped or overwritten
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- OverwolfSetup.exe (PID: 6300)
- OverwolfUpdater.exe (PID: 8164)
- vcredist.exe (PID: 3768)
- vcredist.exe (PID: 7100)
- OWInstaller.exe (PID: 7596)
- VC_redist.x64.exe (PID: 2776)
- VC_redist.x64.exe (PID: 7372)
- VC_redist.x64.exe (PID: 5740)
- Overwolf.exe (PID: 7520)
Drops 7-zip archiver for unpacking
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- OverwolfSetup.exe (PID: 6300)
- OverwolfUpdater.exe (PID: 8164)
Reads the date of Windows installation
- OWInstaller.exe (PID: 7596)
- Overwolf.exe (PID: 7520)
Creates/Modifies COM task schedule object
- dxdiag.exe (PID: 8028)
Reads Microsoft Outlook installation path
- OWInstaller.exe (PID: 7596)
Reads Internet Explorer settings
- OWInstaller.exe (PID: 7596)
There is functionality for taking screenshot (YARA)
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
Process drops legitimate windows executable
- OverwolfSetup.exe (PID: 6300)
- vcredist.exe (PID: 3768)
- vcredist.exe (PID: 7100)
- VC_redist.x64.exe (PID: 2776)
- msiexec.exe (PID: 7800)
- VC_redist.x64.exe (PID: 5740)
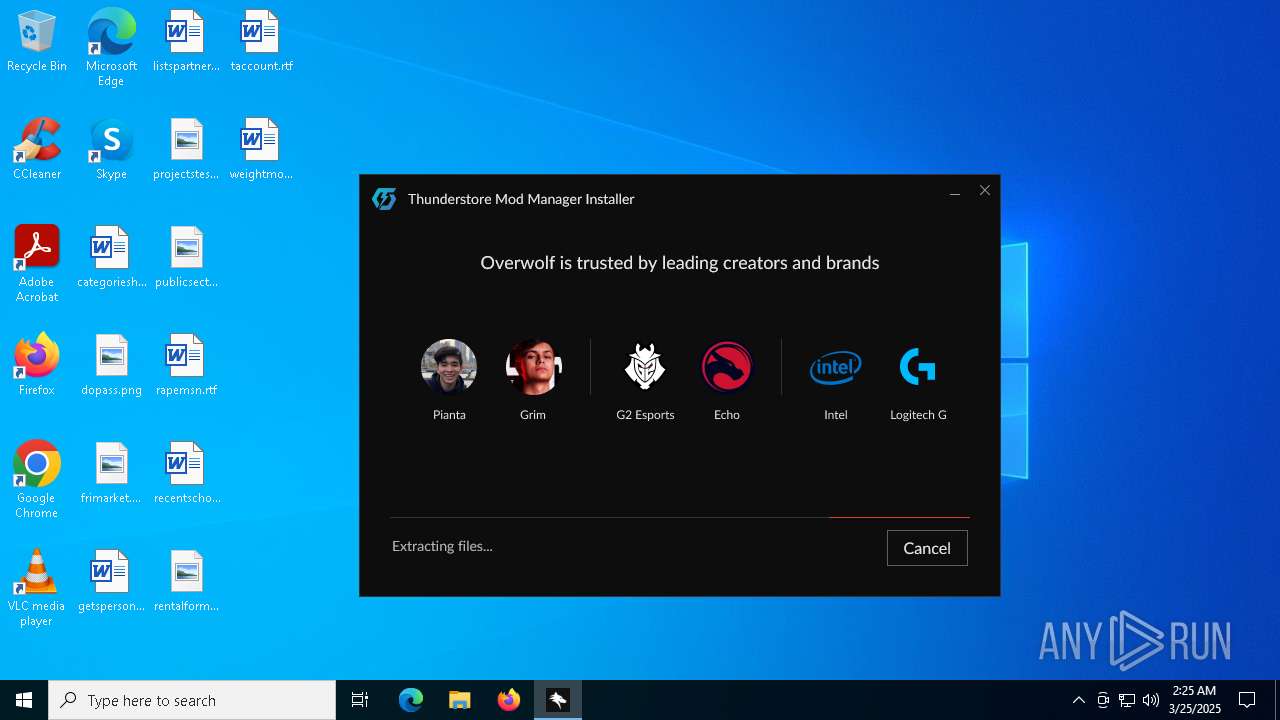
The process drops C-runtime libraries
- OverwolfSetup.exe (PID: 6300)
- msiexec.exe (PID: 7800)
Creates a software uninstall entry
- OverwolfSetup.exe (PID: 6300)
- VC_redist.x64.exe (PID: 2776)
- Overwolf.exe (PID: 7520)
Windows service management via SC.EXE
- sc.exe (PID: 7560)
- sc.exe (PID: 7684)
- sc.exe (PID: 8004)
- sc.exe (PID: 8100)
- sc.exe (PID: 3024)
- sc.exe (PID: 7220)
- sc.exe (PID: 4932)
- sc.exe (PID: 6744)
- sc.exe (PID: 5776)
- sc.exe (PID: 6660)
- sc.exe (PID: 3156)
- sc.exe (PID: 5960)
Starts SC.EXE for service management
- OverwolfUpdater.exe (PID: 6644)
Adds/modifies Windows certificates
- OverwolfUpdater.exe (PID: 6644)
Executes application which crashes
- checkRedist.exe (PID: 2644)
Starts a Microsoft application from unusual location
- vcredist.exe (PID: 7100)
- VC_redist.x64.exe (PID: 2776)
Searches for installed software
- vcredist.exe (PID: 7100)
- VC_redist.x64.exe (PID: 2776)
- dllhost.exe (PID: 7828)
- VC_redist.x64.exe (PID: 7372)
- VC_redist.x64.exe (PID: 5740)
- Overwolf.exe (PID: 7520)
Starts itself from another location
- vcredist.exe (PID: 7100)
Executes as Windows Service
- VSSVC.exe (PID: 6476)
The process executes via Task Scheduler
- OverwolfLauncher.exe (PID: 2088)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7800)
The process checks if it is being run in the virtual environment
- msiexec.exe (PID: 7800)
INFO
The sample compiled with english language support
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- OverwolfSetup.exe (PID: 6300)
- OverwolfUpdater.exe (PID: 8164)
- vcredist.exe (PID: 3768)
- vcredist.exe (PID: 7100)
- VC_redist.x64.exe (PID: 2776)
- msiexec.exe (PID: 7800)
- VC_redist.x64.exe (PID: 7372)
- VC_redist.x64.exe (PID: 5740)
- Overwolf.exe (PID: 7520)
Process checks computer location settings
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- OWInstaller.exe (PID: 7596)
- vcredist.exe (PID: 7100)
- Overwolf.exe (PID: 7520)
- VC_redist.x64.exe (PID: 7372)
- OverwolfBrowser.exe (PID: 7612)
Checks supported languages
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- OWInstaller.exe (PID: 7596)
- OverwolfSetup.exe (PID: 6300)
- OverwolfTSHelper.exe (PID: 5056)
- OverwolfUpdater.exe (PID: 6644)
- OverwolfUpdater.exe (PID: 8164)
- checkRedist.exe (PID: 2644)
- vcredist.exe (PID: 3768)
- vcredist.exe (PID: 7100)
- VC_redist.x64.exe (PID: 2776)
- OverwolfLauncher.exe (PID: 2088)
- OverwolfLauncher.exe (PID: 5968)
- msiexec.exe (PID: 7800)
- VC_redist.x64.exe (PID: 6572)
- Overwolf.exe (PID: 7520)
- VC_redist.x64.exe (PID: 7372)
- OverwolfTSHelper.exe (PID: 4572)
- OverwolfBrowser.exe (PID: 2904)
- VC_redist.x64.exe (PID: 5740)
- OverwolfBrowser.exe (PID: 632)
- OverwolfBrowser.exe (PID: 7180)
- OverwolfBrowser.exe (PID: 7612)
Reads the computer name
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- OWInstaller.exe (PID: 7596)
- OverwolfSetup.exe (PID: 6300)
- OverwolfUpdater.exe (PID: 8164)
- OverwolfUpdater.exe (PID: 6644)
- OverwolfTSHelper.exe (PID: 5056)
- vcredist.exe (PID: 3768)
- vcredist.exe (PID: 7100)
- VC_redist.x64.exe (PID: 2776)
- OverwolfLauncher.exe (PID: 2088)
- OverwolfLauncher.exe (PID: 5968)
- msiexec.exe (PID: 7800)
- Overwolf.exe (PID: 7520)
- VC_redist.x64.exe (PID: 7372)
- OverwolfTSHelper.exe (PID: 4572)
- VC_redist.x64.exe (PID: 5740)
- OverwolfBrowser.exe (PID: 632)
- OverwolfBrowser.exe (PID: 7612)
- OverwolfBrowser.exe (PID: 7180)
- OverwolfBrowser.exe (PID: 2904)
Create files in a temporary directory
- Thunderstore Mod Manager - Installer.exe (PID: 7320)
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- OverwolfSetup.exe (PID: 6300)
- OWInstaller.exe (PID: 7596)
- vcredist.exe (PID: 7100)
- VC_redist.x64.exe (PID: 2776)
- VC_redist.x64.exe (PID: 7372)
Checks proxy server information
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- dxdiag.exe (PID: 8028)
- OWInstaller.exe (PID: 7596)
- OverwolfSetup.exe (PID: 6300)
- OverwolfUpdater.exe (PID: 6644)
- slui.exe (PID: 7172)
- Overwolf.exe (PID: 7520)
Creates files or folders in the user directory
- Thunderstore Mod Manager - Installer.exe (PID: 7436)
- dxdiag.exe (PID: 8028)
- OWInstaller.exe (PID: 7596)
- OverwolfSetup.exe (PID: 6300)
- WerFault.exe (PID: 4920)
- OverwolfUpdater.exe (PID: 6644)
- msiexec.exe (PID: 7800)
- Overwolf.exe (PID: 7520)
- OverwolfBrowser.exe (PID: 2904)
- OverwolfBrowser.exe (PID: 7180)
- dxdiag.exe (PID: 2560)
Reads the machine GUID from the registry
- OWInstaller.exe (PID: 7596)
- OverwolfSetup.exe (PID: 6300)
- OverwolfUpdater.exe (PID: 6644)
- VC_redist.x64.exe (PID: 2776)
- msiexec.exe (PID: 7800)
- Overwolf.exe (PID: 7520)
- OverwolfBrowser.exe (PID: 2904)
- OverwolfBrowser.exe (PID: 7180)
- OverwolfBrowser.exe (PID: 7612)
- OverwolfBrowser.exe (PID: 632)
Reads product name
- OWInstaller.exe (PID: 7596)
- Overwolf.exe (PID: 7520)
Reads Environment values
- OWInstaller.exe (PID: 7596)
- Overwolf.exe (PID: 7520)
- OverwolfBrowser.exe (PID: 2904)
Disables trace logs
- OWInstaller.exe (PID: 7596)
- Overwolf.exe (PID: 7520)
Reads the software policy settings
- OWInstaller.exe (PID: 7596)
- dxdiag.exe (PID: 8028)
- OverwolfSetup.exe (PID: 6300)
- slui.exe (PID: 7548)
- OverwolfUpdater.exe (PID: 6644)
- slui.exe (PID: 7172)
- OverwolfLauncher.exe (PID: 5968)
- msiexec.exe (PID: 7800)
- Overwolf.exe (PID: 7520)
- dxdiag.exe (PID: 2560)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 8028)
- dxdiag.exe (PID: 2560)
Creates files in the program directory
- OverwolfSetup.exe (PID: 6300)
- OWInstaller.exe (PID: 7596)
- OverwolfUpdater.exe (PID: 8164)
- OverwolfUpdater.exe (PID: 6644)
- VC_redist.x64.exe (PID: 2776)
- Overwolf.exe (PID: 7520)
Manages system restore points
- SrTasks.exe (PID: 7708)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7800)
Creates a software uninstall entry
- msiexec.exe (PID: 7800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.266.0.11 |
| ProductVersionNumber: | 2.266.0.11 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Overwolf Ltd. |
| FileDescription: | Overwolf |
| FileVersion: | 2.266.0.11 |
| LegalCopyright: | Copyright (C) 2021 Overwolf Ltd. All Rights Reserved. |
| LegalTrademarks: | - |
| ProductName: | Overwolf |
| ProductVersion: | 2.266.0.11 |
Total processes
205
Monitored processes
58
Malicious processes
14
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files (x86)\Overwolf\0.270.0.12\OverwolfBrowser.exe" --type=gpu-process --no-sandbox --string-annotations=is-enterprise-managed=no --user-agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36" --start-stack-profiler --user-data-dir="C:\Users\admin\AppData\Local\Overwolf\CefBrowserCache" --locales-dir-path="C:\Program Files (x86)\Overwolf\0.270.0.12\Locales" --log-severity=disable --ignore-certificate-errors --remote-allow-origins=* --ow-domain=www.overwolf.com --ow-process-id=7520 --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=4792,i,5713762024229925206,6570844645575360848,262144 --enable-features=AudioVideoTracks --disable-features=HeavyAdIntervention,HeavyAdPrivacyMitigations,PictureInPicture,ProcessSharingWithDefaultSiteInstances,SpareRendererForSitePerProcess,UseModernMediaControls,WinUseBrowserSpellChecker --variations-seed-version --enable-logging=handle --log-file=4796 --mojo-platform-channel-handle=4788 /prefetch:2 | C:\Program Files (x86)\Overwolf\0.270.0.12\OverwolfBrowser.exe | — | Overwolf.exe | |||||||||||
User: admin Company: Overwolf LTD Integrity Level: MEDIUM Description: OverwolfBrowser Version: 0.270.0.12 Modules
| |||||||||||||||
| 812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | checkRedist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Overwolf\OverwolfLauncher.exe" | C:\Program Files (x86)\Overwolf\OverwolfLauncher.exe | — | svchost.exe | |||||||||||
User: admin Company: Overwolf Ltd. Integrity Level: MEDIUM Description: Overwolf Launcher Exit code: 0 Version: 1.131.271.8 Modules
| |||||||||||||||
| 2560 | "C:\WINDOWS\System32\DxDiag.exe" /tC:\Users\admin\AppData\Local\Overwolf\Temp\DxDiagOutput.txt | C:\Windows\System32\dxdiag.exe | — | Overwolf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft DirectX Diagnostic Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | "C:\ProgramData\Overwolf\Setup\checkRedist.exe" | C:\ProgramData\Overwolf\Setup\checkRedist.exe | OverwolfSetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 2776 | "C:\WINDOWS\Temp\{0BC78F42-A4A4-414F-8DDA-22E879E2DD7F}\.be\VC_redist.x64.exe" -q -burn.elevated BurnPipe.{64F0FF17-B576-40AF-809D-FC49ABA21C94} {765E9D70-E73B-447E-92F5-C73ABF614EA4} 7100 | C:\Windows\Temp\{0BC78F42-A4A4-414F-8DDA-22E879E2DD7F}\.be\VC_redist.x64.exe | vcredist.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.42.34438 Exit code: 3010 Version: 14.42.34438.0 Modules
| |||||||||||||||
| 2904 | "C:\Program Files (x86)\Overwolf\0.270.0.12\OverwolfBrowser.exe" --type=crashpad-handler --no-rate-limit --max-db-size=10 --max-db-age=5 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Overwolf\User Data\Crashpad" --url=http://localhost:54288/ --annotation=platform=win64 --annotation=product=Overwolf --annotation=version=0.270.0.12 --initial-client-data=0xe9c,0xe6c,0xea0,0xe98,0xea4,0x7ffc82038fc8,0x7ffc82038fd4,0x7ffc82038fe0 | C:\Program Files (x86)\Overwolf\0.270.0.12\OverwolfBrowser.exe | — | Overwolf.exe | |||||||||||
User: admin Company: Overwolf LTD Integrity Level: MEDIUM Description: OverwolfBrowser Version: 0.270.0.12 Modules
| |||||||||||||||
Total events
49 336
Read events
47 972
Write events
939
Delete events
425
Modification events
| (PID) Process: | (7436) Thunderstore Mod Manager - Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7436) Thunderstore Mod Manager - Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7436) Thunderstore Mod Manager - Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7596) OWInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\OverwolfPersist |
| Operation: | write | Name: | MUIDV2 |
Value: 8aff4141-58b1-4350-85cd-d71b74b5cebb | |||
| (PID) Process: | (7596) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\OverwolfPersist |
| Operation: | write | Name: | MUIDV2 |
Value: 8aff4141-58b1-4350-85cd-d71b74b5cebb | |||
| (PID) Process: | (7596) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Overwolf |
| Operation: | write | Name: | MUID |
Value: bb926e54-e3ca-40fd-ae90-2764341e7792 | |||
| (PID) Process: | (8028) dxdiag.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\DirectX Diagnostic Tool |
| Operation: | write | Name: | DxDiag In SystemInfo |
Value: 1 | |||
| (PID) Process: | (8028) dxdiag.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{EEB1CAE3-D0B2-446E-AEDE-727AA9089A1B}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (7596) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7596) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
408
Suspicious files
1 079
Text files
1 491
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\UserInfo.dll | executable | |
MD5:1DD4CA0F4A94155F8D46EC95A20ADA4A | SHA256:A27DC3069793535CB64123C27DCA8748983D133C8FA5AADDEE8CDBC83F16986D | |||
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\utils.dll | executable | |
MD5:C6B46A5FCDCCBF3AEFF930B1E5B383D4 | SHA256:251AB3E2690562DCFCD510642607F206E6DCF626D06D94B74E1FA8297B1050A0 | |||
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\uac.dll | executable | |
MD5:861F7E800BB28F68927E65719869409C | SHA256:10A0E8CF46038AB3B2C3CF5DCE407B9A043A631CBDE9A5C8BCF0A54B2566C010 | |||
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\nsProcess.dll | executable | |
MD5:10E47E822B85D2A12FA4727001612182 | SHA256:D530589A90918334B8E08D7355630892DD62F41333D948A860735D5BECFCB391 | |||
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\System.dll | executable | |
MD5:51BD16A2EA23AE1E7A92CEDC6785C82E | SHA256:4DBC79D2B1C7987CC64BB5D014DB81BB5108BDD6D8BF3A5F820FAC1DED62BE33 | |||
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\log4net.dll | executable | |
MD5:F15C8A9E2876568B3910189B2D493706 | SHA256:AE9C8073C3357C490F5D1C64101362918357C568F6B9380A60B09A4A4C1FF309 | |||
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\OWInstaller.exe | executable | |
MD5:D58D2772011C07E51FDDCB8D592F61FE | SHA256:9A737F35E38ABCB7E264DB5DEE7BE9E558492060B59BFB305D967F3960DD4D9F | |||
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\Newtonsoft.Json.dll | executable | |
MD5:98CBB64F074DC600B23A2EE1A0F46448 | SHA256:7B44639CBFBC8DDAC8C7A3DE8FFA97A7460BEBB0D54E9FF2E1CCDC3A742C2B13 | |||
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\websocket-sharp.dll | executable | |
MD5:1B4FCDE3554ED9CA14E8E7C3A1706FB3 | SHA256:B152284FD1EF5CEBEE56802F13B46DEF7C136F0C50FB173AE29CF0648BB4CB1F | |||
| 7320 | Thunderstore Mod Manager - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsmBA3B.tmp\DotNetZip.dll | executable | |
MD5:190E712F2E3B065BA3D5F63CB9B7725E | SHA256:6C512D9943A225D686B26FC832589E4C8BEF7C4DD0A8BDFD557D5D27FE5BBA0F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
80
DNS requests
58
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7436 | Thunderstore Mod Manager - Installer.exe | GET | 200 | 54.230.228.60:80 | http://analyticsnew.overwolf.com/analytics/Counter?Name=installer_uac_action&Value=1&&Extra=%5b%7b%22Name%22%3a%22installer_version%22%2c%22Value%22%3a%222.266.0.11%22%7d%5d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | — | 18.173.189.168:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7596 | OWInstaller.exe | GET | 200 | 18.173.189.168:80 | http://ocsp.rootca3.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRkNawYMzz%2BjKSfYbTyFR0AXuhs6QQUq7bb1waeN6wwhgeRcMecxBmxeMACEwdzEnA9eVH9TrLXPKuCavuqCA0%3D | unknown | — | — | whitelisted |
7596 | OWInstaller.exe | GET | 200 | 142.250.186.78:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.7.2&utmn=533682917&utmhn=&utmcs=UTF-8&utmsr=-&utmsc=-&utmul=-&utmje=0&utmfl=-&utmdt=&utmhid=892635392&utmr=/&utmp=/&utmac=UA-18298709-8&utmcc=__utma%3D0.1528496324.1742869442.1742869442.1742869442.2%3B%2B__utmz%3D0.1742869442.1.1.utmcsr%3D%28direct%29%7Cutmccn%3D%7Cutmcmd%3D%3B&utme=5%28Funnel2%2AInstaller%20Launched%2A2.0.50727%20SP2%2C%203.0%20SP2%2C%203.5%20SP1%2C%204%20Client%2C%204%20Full%2C%204.0%20Client%29%28%29&gaq=1&utmt=event | unknown | — | — | whitelisted |
7596 | OWInstaller.exe | GET | 200 | 142.250.186.78:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.7.2&utmn=14559576&utmhn=&utmcs=UTF-8&utmsr=-&utmsc=-&utmul=-&utmje=0&utmfl=-&utmdt=&utmhid=52608086&utmr=/&utmp=/&utmac=UA-80584726-1&utmcc=__utma%3D0.1528496324.1742869442.1742869442.1742869442.2%3B%2B__utmz%3D0.1742869442.1.1.utmcsr%3D%28direct%29%7Cutmccn%3D%7Cutmcmd%3D%3B&utme=5%28Funnel2%2AInstaller%20Launched%2A2.0.50727%20SP2%2C%203.0%20SP2%2C%203.5%20SP1%2C%204%20Client%2C%204%20Full%2C%204.0%20Client%29%28%29&gaq=1&utmt=event | unknown | — | — | whitelisted |
— | — | GET | 200 | 18.173.189.168:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkzUBtJnwJkc3SmanzgxeYU%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7436 | Thunderstore Mod Manager - Installer.exe | 54.230.228.60:80 | analyticsnew.overwolf.com | AMAZON-02 | US | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
analyticsnew.overwolf.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
content.overwolf.com |
| whitelisted |
storeapi.overwolf.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7436 | Thunderstore Mod Manager - Installer.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|