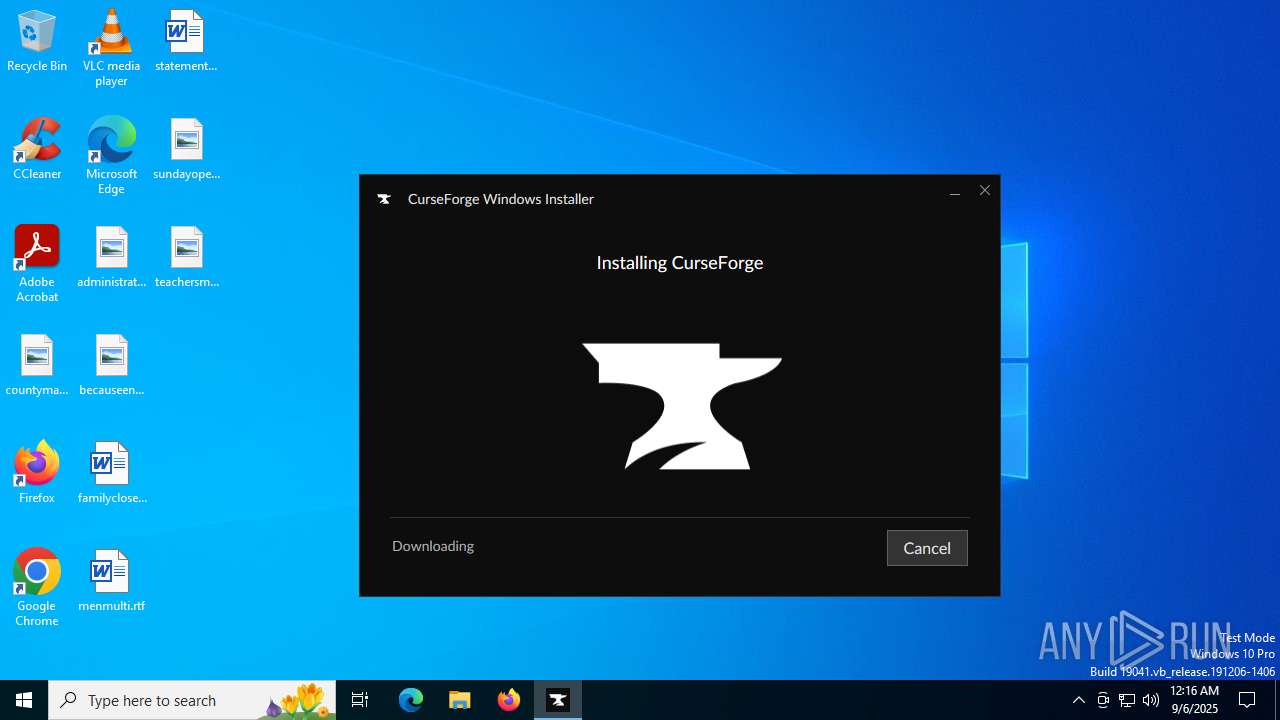
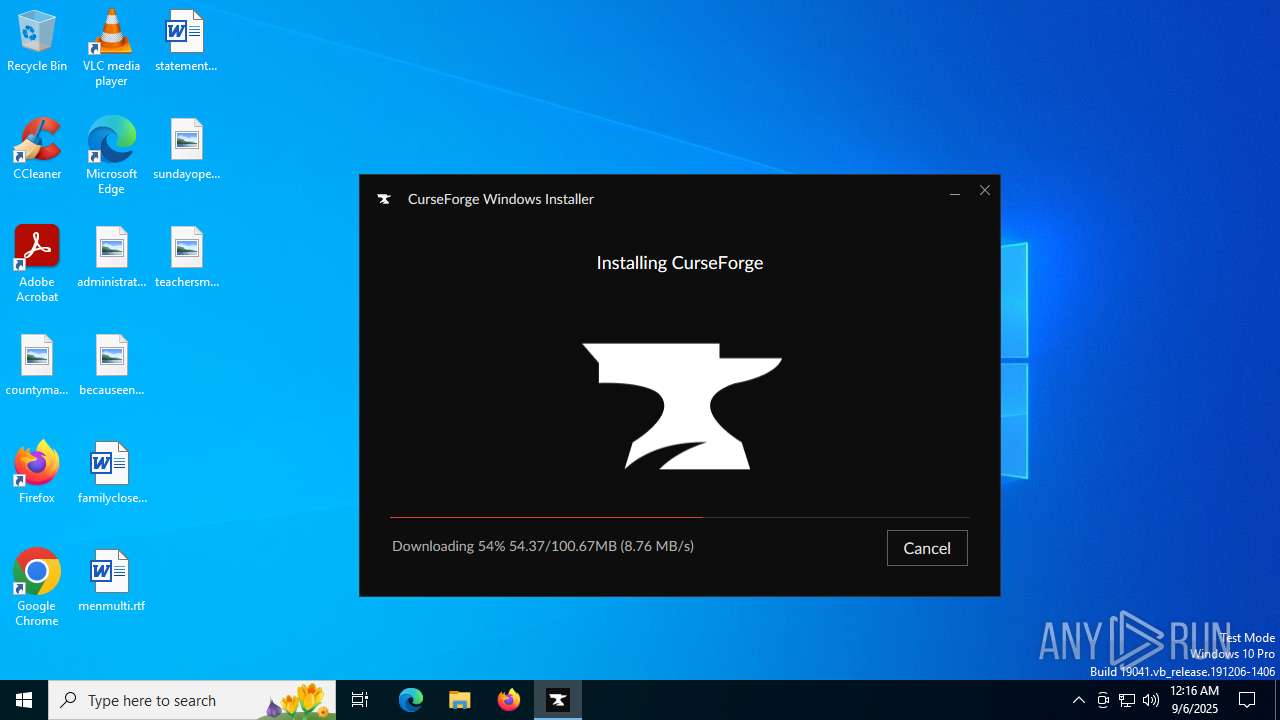
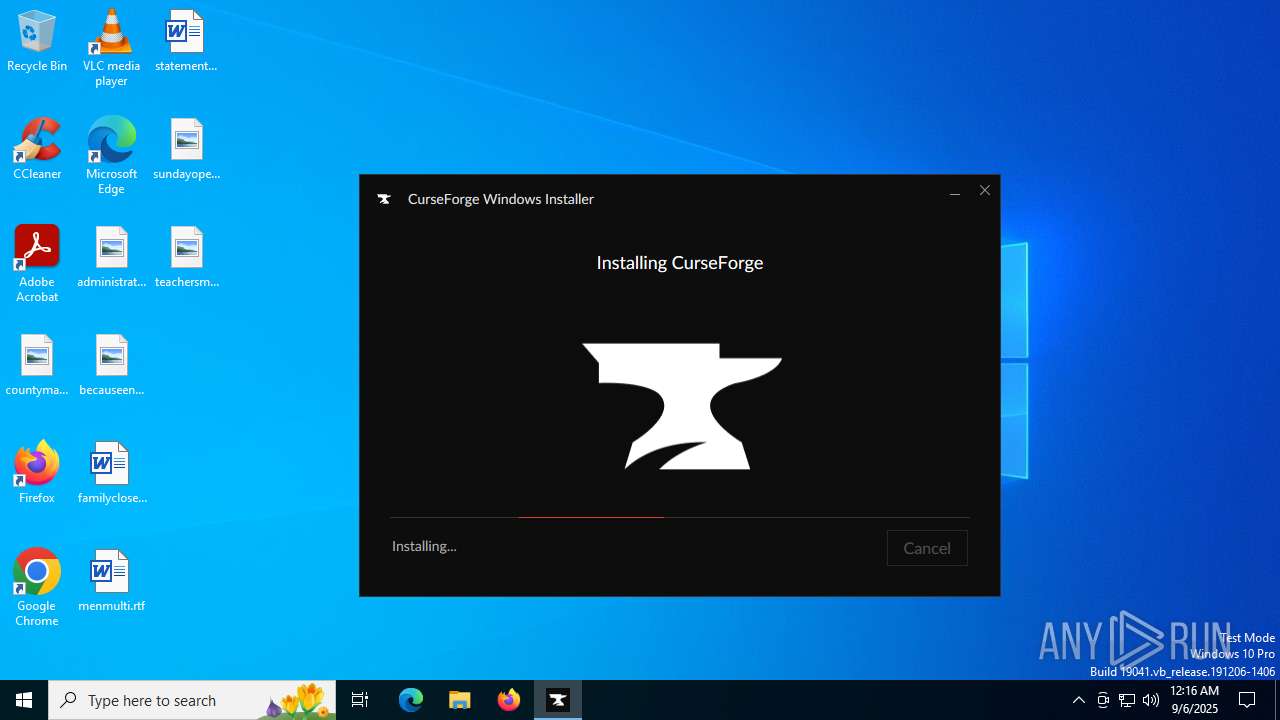
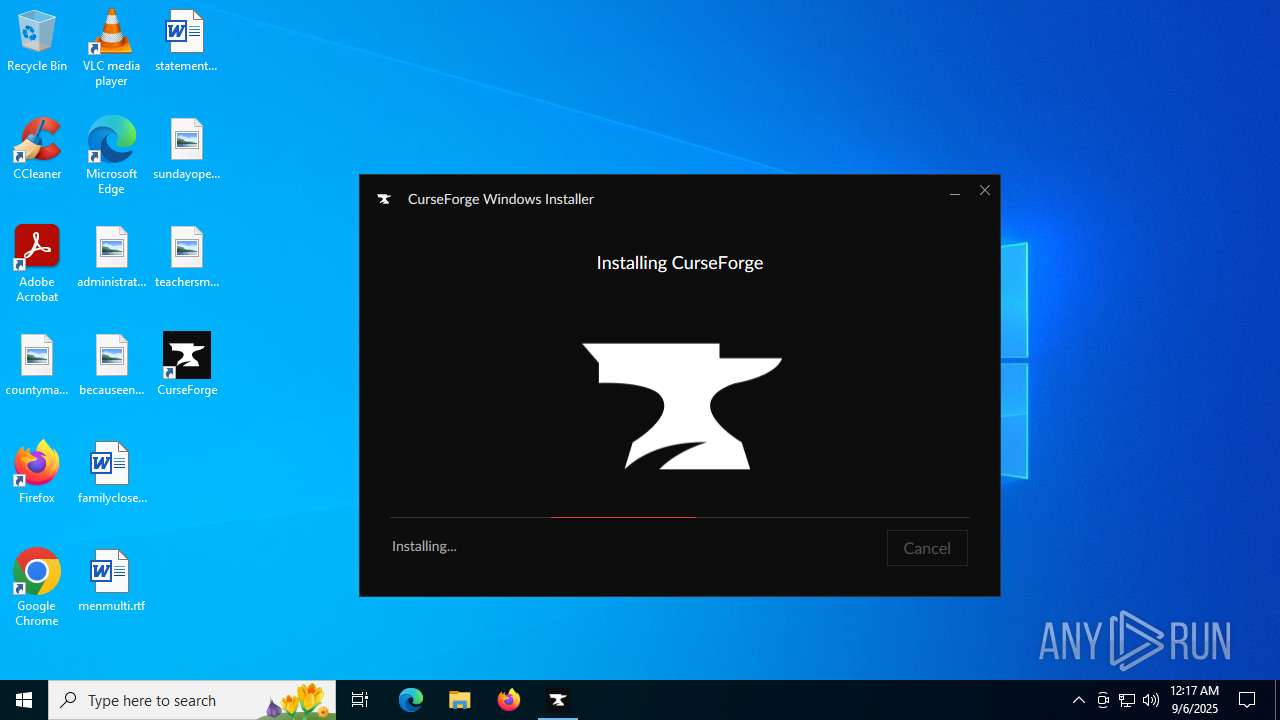
| File name: | CurseForge Windows - Installer.exe |
| Full analysis: | https://app.any.run/tasks/4a0b92e6-44ab-4386-ad86-dcaf1fa6b3bd |
| Verdict: | Malicious activity |
| Analysis date: | September 06, 2025, 00:16:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | B14F85AFA6E8584BBF8C376F08DD1344 |
| SHA1: | 4DB186912083937CFD981A377F4DB5AEC3711E0C |
| SHA256: | 889DA00684AAE2536FDFDFF746C61C6F727CADF75A140DB1F9FCBB53B31CFBE1 |
| SSDEEP: | 98304:A/DiTyNJ/A9nGcRa1xXcVsy3RxeLLCIJgap176MVhBIHsCE+1mcMRwSMRwgF9RPi:dYARi |
MALICIOUS
Changes powershell execution policy (Unrestricted)
- CurseForge.exe (PID: 6360)
Changes the autorun value in the registry
- CurseForge.exe (PID: 6360)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- CurseForge Windows - Installer.exe (PID: 6340)
- ow-electron-setup.exe (PID: 6180)
The process creates files with name similar to system file names
- CurseForge Windows - Installer.exe (PID: 6340)
- ow-electron-setup.exe (PID: 6180)
Executable content was dropped or overwritten
- CurseForge Windows - Installer.exe (PID: 6340)
- ow-electron-setup.exe (PID: 6180)
- CurseForge.exe (PID: 7268)
- Curse.Agent.Host.exe (PID: 7236)
Drops 7-zip archiver for unpacking
- CurseForge Windows - Installer.exe (PID: 6340)
- ow-electron-setup.exe (PID: 6180)
Reads Microsoft Outlook installation path
- OWInstaller.exe (PID: 4724)
Reads Internet Explorer settings
- OWInstaller.exe (PID: 4724)
Reads security settings of Internet Explorer
- OWInstaller.exe (PID: 4724)
- ow-electron-setup.exe (PID: 6180)
There is functionality for taking screenshot (YARA)
- CurseForge Windows - Installer.exe (PID: 6340)
Starts CMD.EXE for commands execution
- ow-electron-setup.exe (PID: 6180)
- CurseForge.exe (PID: 7268)
Get information on the list of running processes
- ow-electron-setup.exe (PID: 6180)
- cmd.exe (PID: 4088)
Process drops legitimate windows executable
- ow-electron-setup.exe (PID: 6180)
Creates a software uninstall entry
- ow-electron-setup.exe (PID: 6180)
Application launched itself
- CurseForge.exe (PID: 6360)
The process bypasses the loading of PowerShell profile settings
- CurseForge.exe (PID: 6360)
The process hides Powershell's copyright startup banner
- CurseForge.exe (PID: 6360)
Starts POWERSHELL.EXE for commands execution
- CurseForge.exe (PID: 6360)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7824)
Reads the date of Windows installation
- OWInstaller.exe (PID: 4724)
INFO
Creates files or folders in the user directory
- CurseForge Windows - Installer.exe (PID: 6340)
- OWInstaller.exe (PID: 4724)
- dxdiag.exe (PID: 3768)
- ow-electron-setup.exe (PID: 6180)
- CurseForge.exe (PID: 6360)
- CurseForge.exe (PID: 1712)
- CurseForge.exe (PID: 7268)
- CurseForge.exe (PID: 7436)
- Curse.Agent.Host.exe (PID: 7236)
Checks supported languages
- CurseForge Windows - Installer.exe (PID: 6340)
- OWInstaller.exe (PID: 4724)
- ow-electron-setup.exe (PID: 6180)
- CurseForge.exe (PID: 6172)
- CurseForge.exe (PID: 6360)
- CurseForge.exe (PID: 1712)
- CurseForge.exe (PID: 5684)
- CurseForge.exe (PID: 4084)
- CurseForge.exe (PID: 1204)
- CurseForge.exe (PID: 7268)
- Curse.Agent.Host.exe (PID: 7236)
- CurseForge.exe (PID: 7436)
The sample compiled with english language support
- CurseForge Windows - Installer.exe (PID: 6340)
- ow-electron-setup.exe (PID: 6180)
- CurseForge.exe (PID: 7268)
- Curse.Agent.Host.exe (PID: 7236)
Reads the computer name
- OWInstaller.exe (PID: 4724)
- ow-electron-setup.exe (PID: 6180)
- CurseForge.exe (PID: 6360)
- CurseForge.exe (PID: 1712)
- CurseForge.exe (PID: 6172)
- CurseForge.exe (PID: 5684)
- CurseForge.exe (PID: 7268)
- Curse.Agent.Host.exe (PID: 7236)
- CurseForge.exe (PID: 7436)
Create files in a temporary directory
- CurseForge Windows - Installer.exe (PID: 6340)
- OWInstaller.exe (PID: 4724)
- ow-electron-setup.exe (PID: 6180)
- CurseForge.exe (PID: 6360)
Reads the machine GUID from the registry
- OWInstaller.exe (PID: 4724)
- CurseForge.exe (PID: 6360)
- CurseForge.exe (PID: 6172)
- CurseForge.exe (PID: 7436)
Reads Environment values
- OWInstaller.exe (PID: 4724)
- CurseForge.exe (PID: 6360)
- CurseForge.exe (PID: 7268)
- CurseForge.exe (PID: 6172)
Disables trace logs
- OWInstaller.exe (PID: 4724)
Reads product name
- OWInstaller.exe (PID: 4724)
- CurseForge.exe (PID: 6360)
- CurseForge.exe (PID: 7268)
Reads the software policy settings
- OWInstaller.exe (PID: 4724)
- dxdiag.exe (PID: 3768)
- CurseForge.exe (PID: 5684)
- Curse.Agent.Host.exe (PID: 7236)
Process checks computer location settings
- OWInstaller.exe (PID: 4724)
- CurseForge.exe (PID: 6360)
- CurseForge.exe (PID: 1204)
- CurseForge.exe (PID: 4084)
- CurseForge.exe (PID: 7268)
Checks proxy server information
- OWInstaller.exe (PID: 4724)
- dxdiag.exe (PID: 3768)
- CurseForge.exe (PID: 6360)
- Curse.Agent.Host.exe (PID: 7236)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 3768)
Manual execution by a user
- CurseForge.exe (PID: 6360)
Reads CPU info
- CurseForge.exe (PID: 6360)
Creates files in the program directory
- Curse.Agent.Host.exe (PID: 7236)
Launching a file from a Registry key
- CurseForge.exe (PID: 6360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.282.0.1 |
| ProductVersionNumber: | 2.282.0.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Overwolf Ltd. |
| FileDescription: | Curseforge |
| FileVersion: | 2.282.0.1 |
| LegalCopyright: | Copyright (C) 2021 Overwolf Ltd. All Rights Reserved. |
| LegalTrademarks: | - |
| ProductName: | Curseforge |
| ProductVersion: | 2.282.0.1 |
Total processes
167
Monitored processes
32
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CurseForge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 828 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | "C:\Users\admin\AppData\Local\Programs\CurseForge Windows\CurseForge.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\CurseForge" --standard-schemes=owepm --secure-schemes=owepm --bypasscsp-schemes=owepm --fetch-schemes=owepm --streaming-schemes=owepm --app-path="C:\Users\admin\AppData\Local\Programs\CurseForge Windows\resources\app.asar" --enable-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --time-ticks-at-unix-epoch=-1757116150744892 --launch-time-ticks=1681394742 --field-trial-handle=1812,i,15678328909215686320,15627309996040637967,262144 --enable-features=EnableTransparentHwndEnlargement,PdfUseShowSaveFilePicker --disable-features=ScreenAIOCREnabled,SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit --variations-seed-version --mojo-platform-channel-handle=3776 disableSentry=false /prefetch:1 | C:\Users\admin\AppData\Local\Programs\CurseForge Windows\CurseForge.exe | — | CurseForge.exe | |||||||||||
User: admin Company: Overwolf Integrity Level: LOW Description: CurseForge Version: 1.287.0-28081.28081 Modules
| |||||||||||||||
| 1712 | "C:\Users\admin\AppData\Local\Programs\CurseForge Windows\CurseForge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\CurseForge" --standard-schemes=owepm --secure-schemes=owepm --bypasscsp-schemes=owepm --fetch-schemes=owepm --streaming-schemes=owepm --field-trial-handle=1812,i,15678328909215686320,15627309996040637967,262144 --enable-features=EnableTransparentHwndEnlargement,PdfUseShowSaveFilePicker --disable-features=ScreenAIOCREnabled,SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit --variations-seed-version --mojo-platform-channel-handle=1420 /prefetch:3 | C:\Users\admin\AppData\Local\Programs\CurseForge Windows\CurseForge.exe | CurseForge.exe | ||||||||||||
User: admin Company: Overwolf Integrity Level: MEDIUM Description: CurseForge Version: 1.287.0-28081.28081 Modules
| |||||||||||||||
| 3768 | "C:\WINDOWS\System32\DxDiag.exe" /xC:\Users\admin\AppData\Local\Overwolf\Temp\DxDiagOutput.xml | C:\Windows\System32\dxdiag.exe | OWInstaller.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft DirectX Diagnostic Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4084 | "C:\Users\admin\AppData\Local\Programs\CurseForge Windows\CurseForge.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\CurseForge" --standard-schemes=owepm --secure-schemes=owepm --bypasscsp-schemes=owepm --fetch-schemes=owepm --streaming-schemes=owepm --app-path="C:\Users\admin\AppData\Local\Programs\CurseForge Windows\resources\app.asar" --enable-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --time-ticks-at-unix-epoch=-1757116150744892 --launch-time-ticks=1681290562 --field-trial-handle=1812,i,15678328909215686320,15627309996040637967,262144 --enable-features=EnableTransparentHwndEnlargement,PdfUseShowSaveFilePicker --disable-features=ScreenAIOCREnabled,SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit --variations-seed-version --mojo-platform-channel-handle=3364 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\CurseForge Windows\CurseForge.exe | — | CurseForge.exe | |||||||||||
User: admin Company: Overwolf Integrity Level: LOW Description: CurseForge Exit code: 0 Version: 1.287.0-28081.28081 Modules
| |||||||||||||||
| 4088 | "C:\WINDOWS\system32\cmd.exe" /c tasklist /FI "USERNAME eq %USERNAME%" /FI "IMAGENAME eq CurseForge.exe" /FO csv | "C:\WINDOWS\system32\find.exe" "CurseForge.exe" | C:\Windows\SysWOW64\cmd.exe | — | ow-electron-setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4648 | powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CurseForge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4724 | "C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\OWinstaller.exe" Sel=0&Extension=cfiahnpaolfnlgaihhmobmnjdafknjnjdpdabpcm&Name=CurseForge%20Windows&UtmTerm=eyJkb21haW4iOiJjZi13ZWIifQ%3D%3D&Referer=www.curseforge.com&Browser=firefox -partnerCustomizationLevel 1 -customPromoPages --owelectronUrl=https://download.overwolf.com/setup/electron/cfiahnpaolfnlgaihhmobmnjdafknjnjdpdabpcm -AllowWindowsInsider --disable-change-location --disable-ow-shortcut-ui --disable-app-shortcut-ui --enable-app-shortcut --silent-setup --app-name="Curseforge" --auto-close -exepath C:\Users\admin\AppData\Local\Temp\CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\OWInstaller.exe | CurseForge Windows - Installer.exe | ||||||||||||
User: admin Company: Overwolf Integrity Level: MEDIUM Description: Curseforge Installer Exit code: 0 Version: 2.282.0.1 Modules
| |||||||||||||||
| 4932 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 854
Read events
26 678
Write events
134
Delete events
42
Modification events
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\OverwolfPersist |
| Operation: | write | Name: | MUIDV2 |
Value: 696eafc2-8be5-466c-8ad9-ea8fe4cf967c | |||
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\OverwolfElectron |
| Operation: | write | Name: | MUID |
Value: bb926e54-e3ca-40fd-ae90-2764341e7792 | |||
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4724) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OWinstaller_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
56
Suspicious files
300
Text files
95
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Overwolf\OWInstall.log | text | |
MD5:07E605D2D7609CF336EA1708E86B5A0C | SHA256:C69AD6C6A1D6D89336E18DB86A6C852AB60C0CEB367C79922807E55DE7BE49DD | |||
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\OWInstaller.exe.config | xml | |
MD5:82D22E4E19E27E306317513B9BFA70FF | SHA256:272E4C5364193E73633CAA3793E07509A349B79314EA01808B24FDB12C51B827 | |||
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\utils.dll | executable | |
MD5:C6B46A5FCDCCBF3AEFF930B1E5B383D4 | SHA256:251AB3E2690562DCFCD510642607F206E6DCF626D06D94B74E1FA8297B1050A0 | |||
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\nsProcess.dll | executable | |
MD5:10E47E822B85D2A12FA4727001612182 | SHA256:D530589A90918334B8E08D7355630892DD62F41333D948A860735D5BECFCB391 | |||
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\System.dll | executable | |
MD5:51BD16A2EA23AE1E7A92CEDC6785C82E | SHA256:4DBC79D2B1C7987CC64BB5D014DB81BB5108BDD6D8BF3A5F820FAC1DED62BE33 | |||
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\OWInstaller.exe | executable | |
MD5:3227EF39A4227820E3FDAA92B7880738 | SHA256:C26748BD25C4100D2031BB0D2E868CBD6347F65D5B840ADAC4FFCE8CE09C23D5 | |||
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\DotNetZip.dll | executable | |
MD5:190E712F2E3B065BA3D5F63CB9B7725E | SHA256:6C512D9943A225D686B26FC832589E4C8BEF7C4DD0A8BDFD557D5D27FE5BBA0F | |||
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\Newtonsoft.Json.dll | executable | |
MD5:98CBB64F074DC600B23A2EE1A0F46448 | SHA256:7B44639CBFBC8DDAC8C7A3DE8FFA97A7460BEBB0D54E9FF2E1CCDC3A742C2B13 | |||
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\uac.dll | executable | |
MD5:861F7E800BB28F68927E65719869409C | SHA256:10A0E8CF46038AB3B2C3CF5DCE407B9A043A631CBDE9A5C8BCF0A54B2566C010 | |||
| 6340 | CurseForge Windows - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsfD82C.tmp\Microsoft.Win32.TaskScheduler.dll | executable | |
MD5:198949A4C3E67B9EB916140DFF75C114 | SHA256:0BDAD6DEB1B651E0A52BAB4DB2C7883C9332884AA37300B3439C69D85B054C7C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
83
DNS requests
65
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4724 | OWInstaller.exe | GET | 200 | 142.250.186.174:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.7.2&utmn=775714462&utmhn=&utmcs=UTF-8&utmsr=-&utmsc=-&utmul=-&utmje=0&utmfl=-&utmdt=&utmhid=454688362&utmr=/&utmp=/&utmac=UA-80584726-1&utmcc=__utma%3D0.1766214910.1757117780.1757117780.1757117780.2%3B%2B__utmz%3D0.1757117780.1.1.utmcsr%3D%28direct%29%7Cutmccn%3D%7Cutmcmd%3D%3B&utme=5%28Funnel2%2AInstaller%20Launched%2A%29%28%29&gaq=1&utmt=event | US | image | 35 b | whitelisted |
4724 | OWInstaller.exe | GET | 200 | 142.250.186.174:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.7.2&utmn=469248215&utmhn=&utmcs=UTF-8&utmsr=-&utmsc=-&utmul=-&utmje=0&utmfl=-&utmdt=&utmhid=323969851&utmr=/&utmp=/&utmac=UA-18298709-8&utmcc=__utma%3D0.1766214910.1757117780.1757117780.1757117780.2%3B%2B__utmz%3D0.1757117780.1.1.utmcsr%3D%28direct%29%7Cutmccn%3D%7Cutmcmd%3D%3B&utme=5%28Funnel2%2AInstaller%20Launched%2A%29%28%29&gaq=1&utmt=event | US | image | 35 b | whitelisted |
4724 | OWInstaller.exe | GET | 200 | 18.245.38.41:80 | http://ocsp.rootca3.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRkNawYMzz%2BjKSfYbTyFR0AXuhs6QQUq7bb1waeN6wwhgeRcMecxBmxeMACEwdzEnA9eVH9TrLXPKuCavuqCA0%3D | US | binary | 851 b | whitelisted |
4724 | OWInstaller.exe | GET | 200 | 142.250.185.99:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
4724 | OWInstaller.exe | GET | 200 | 142.250.185.99:80 | http://c.pki.goog/r/r4.crl | US | binary | 530 b | whitelisted |
4724 | OWInstaller.exe | GET | 200 | 18.245.38.41:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | US | binary | 1.40 Kb | whitelisted |
4724 | OWInstaller.exe | GET | 200 | 142.250.185.99:80 | http://o.pki.goog/we2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEQCI6mHCdFWRJRAo5PR4%2Fqn6 | US | binary | 281 b | whitelisted |
4724 | OWInstaller.exe | GET | 200 | 142.250.185.99:80 | http://o.pki.goog/we2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEQCxXblMd1Bh9glV8CviEWkb | US | binary | 281 b | whitelisted |
3768 | dxdiag.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | DE | binary | 824 b | whitelisted |
3768 | dxdiag.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl%20 | QA | binary | 564 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6012 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4724 | OWInstaller.exe | 142.250.186.174:80 | www.google-analytics.com | GOOGLE | US | whitelisted |
4724 | OWInstaller.exe | 18.244.18.106:443 | analyticsnew.overwolf.com | — | US | unknown |
4724 | OWInstaller.exe | 18.245.86.78:443 | content.overwolf.com | — | US | whitelisted |
4724 | OWInstaller.exe | 18.245.38.41:80 | ocsp.rootca3.amazontrust.com | — | US | whitelisted |
4724 | OWInstaller.exe | 18.172.112.84:443 | storeapi.overwolf.com | — | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
analyticsnew.overwolf.com |
| unknown |
content.overwolf.com |
| whitelisted |
ocsp.rootca3.amazontrust.com |
| whitelisted |
storeapi.overwolf.com |
| shared |
console-apps.overwolf.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
c.pki.goog |
| unknown |
ocsp.rootca1.amazontrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Observed UA-CPU Header |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1712 | CurseForge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
1712 | CurseForge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
1712 | CurseForge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |