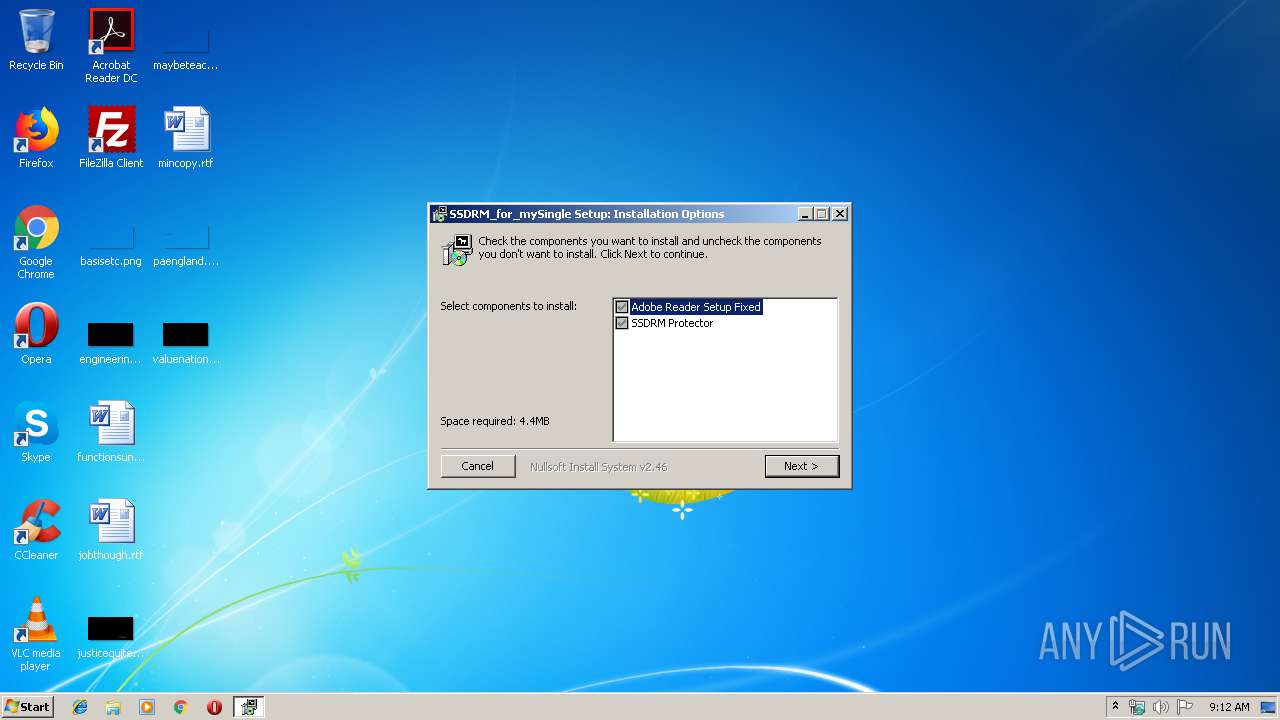
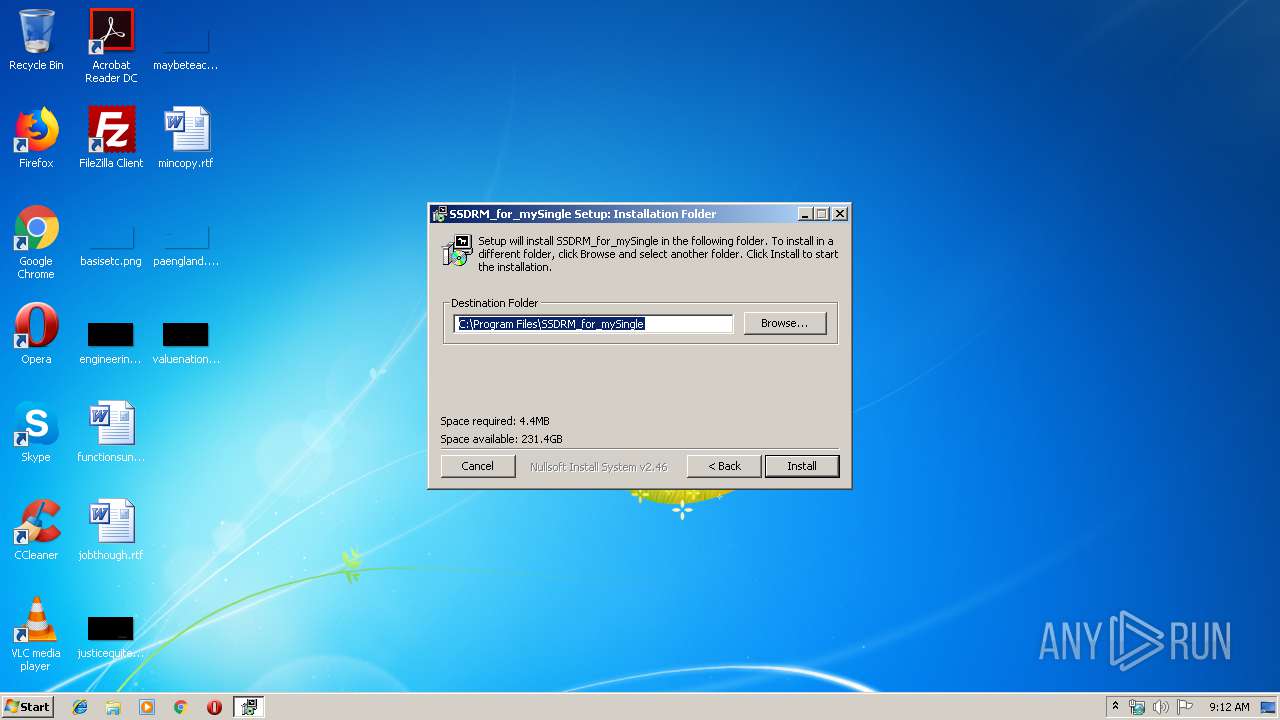
| File name: | SSDRM_for_mySingle.exe |
| Full analysis: | https://app.any.run/tasks/3e81f495-42a6-4f5f-9a47-41ade6a8ce0f |
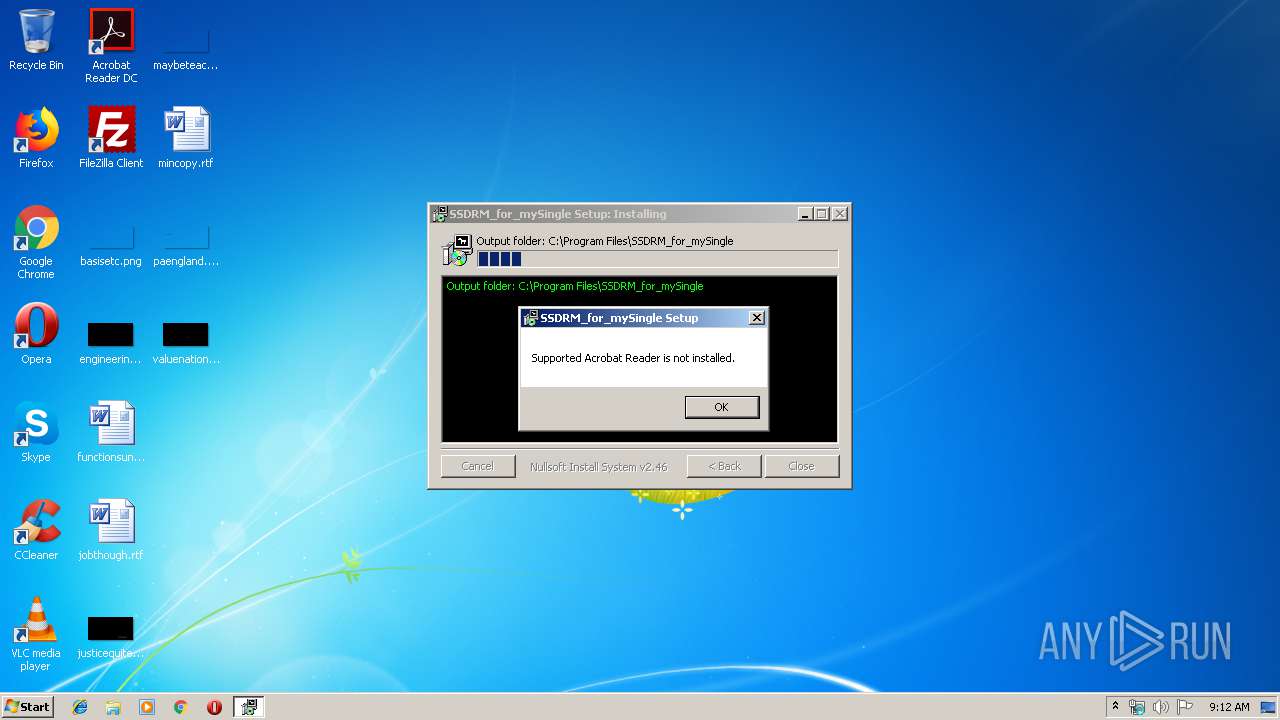
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 08:12:11 |
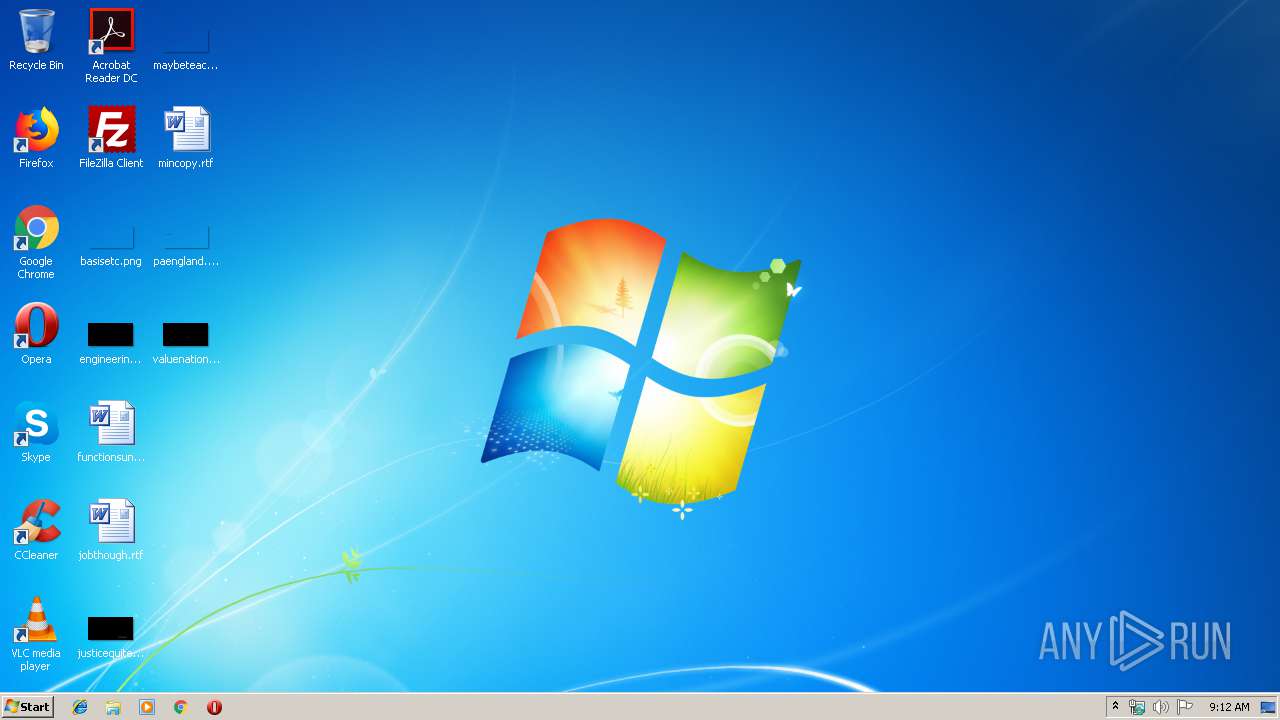
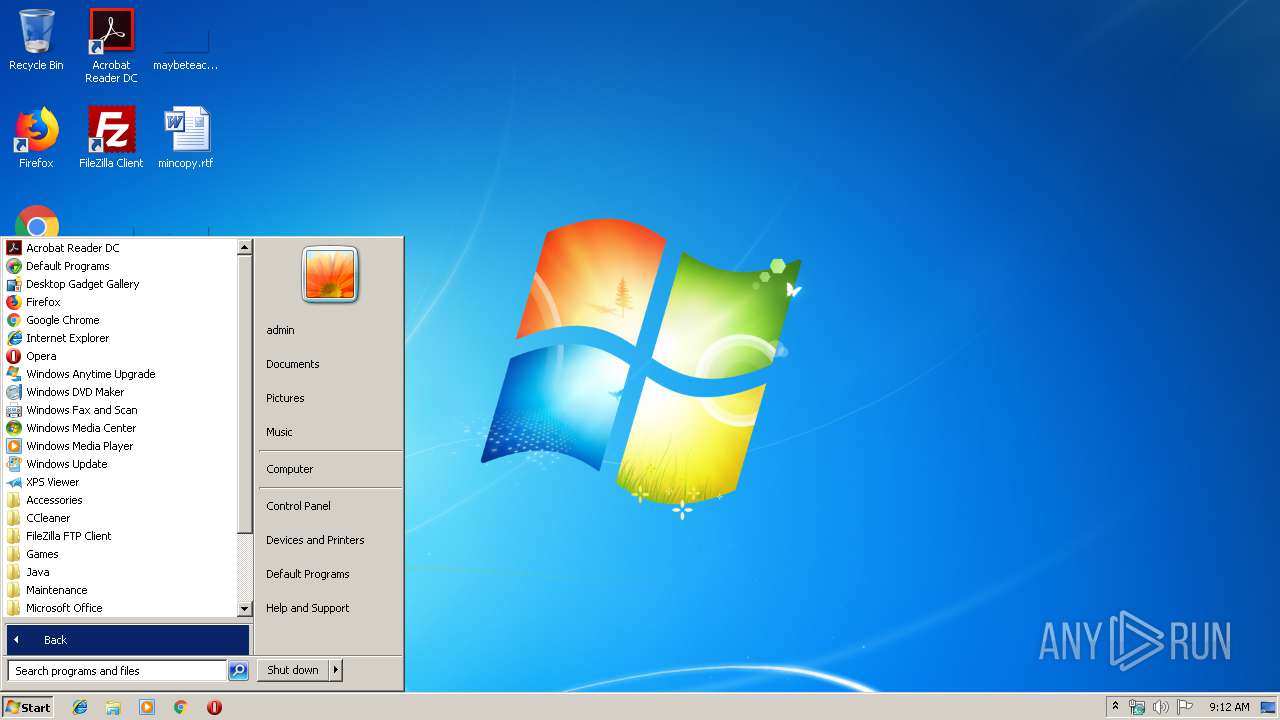
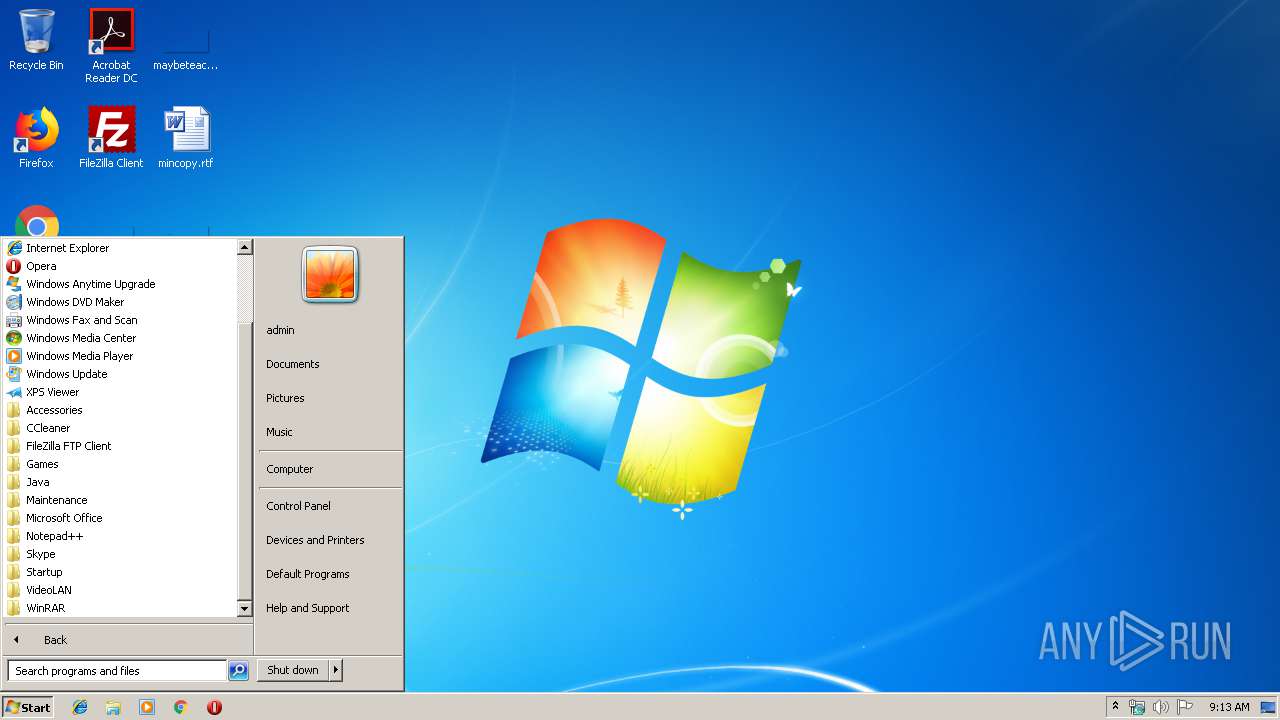
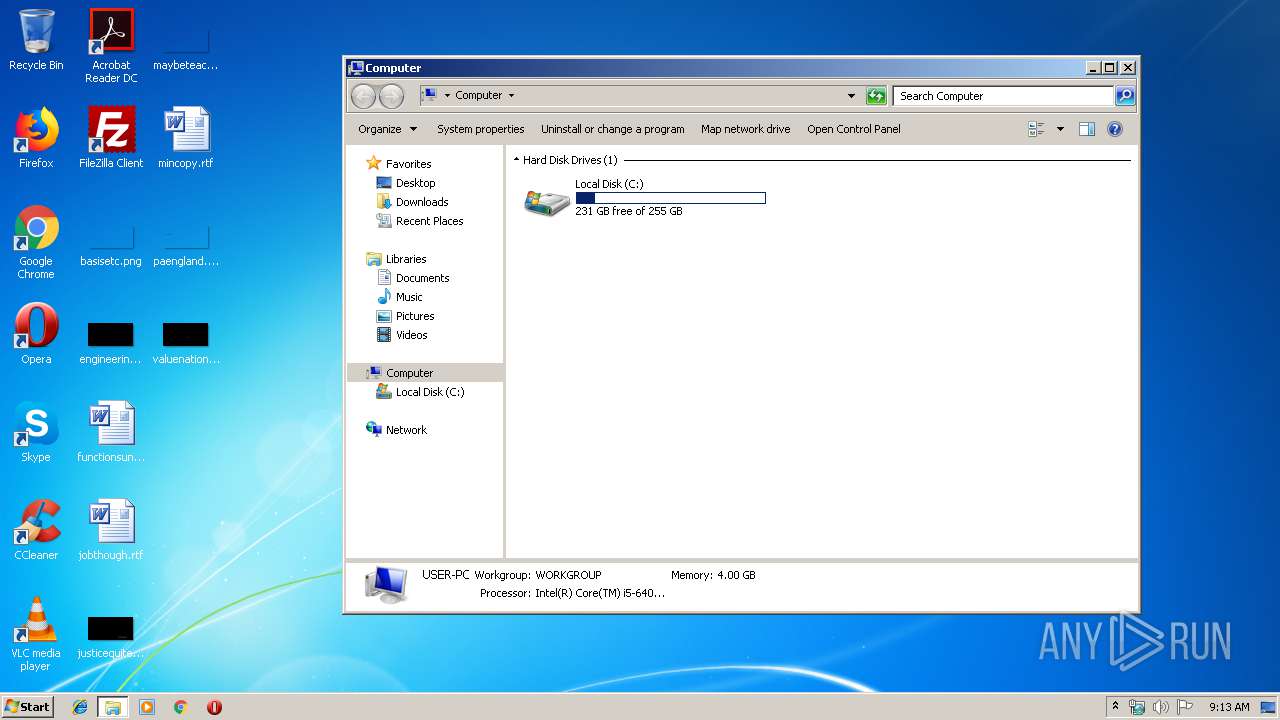
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4164D80ADE12FD8AA36FBAA4CC9C9740 |
| SHA1: | 5F85D1550D3D654AC16A9262555A586CCF167A0F |
| SHA256: | 88977075356DC9E4C81FF59E5FFC004AB3D62070C1062CE7B690A941D5328090 |
| SSDEEP: | 98304:v0kfXXnyek4Q7OWfjdZMX3PfKSu6vIxR1QtT29daNj1lk/va:ccW4c5fjdunPy/xLQtT29IDlkXa |
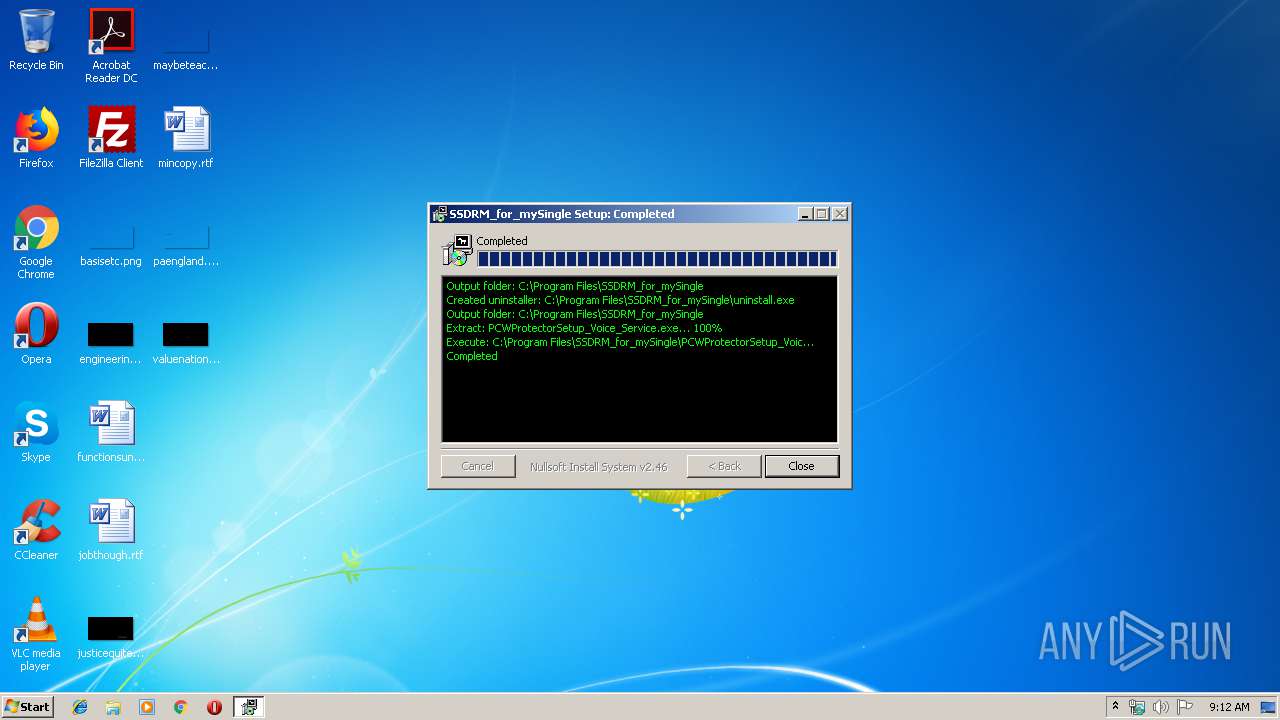
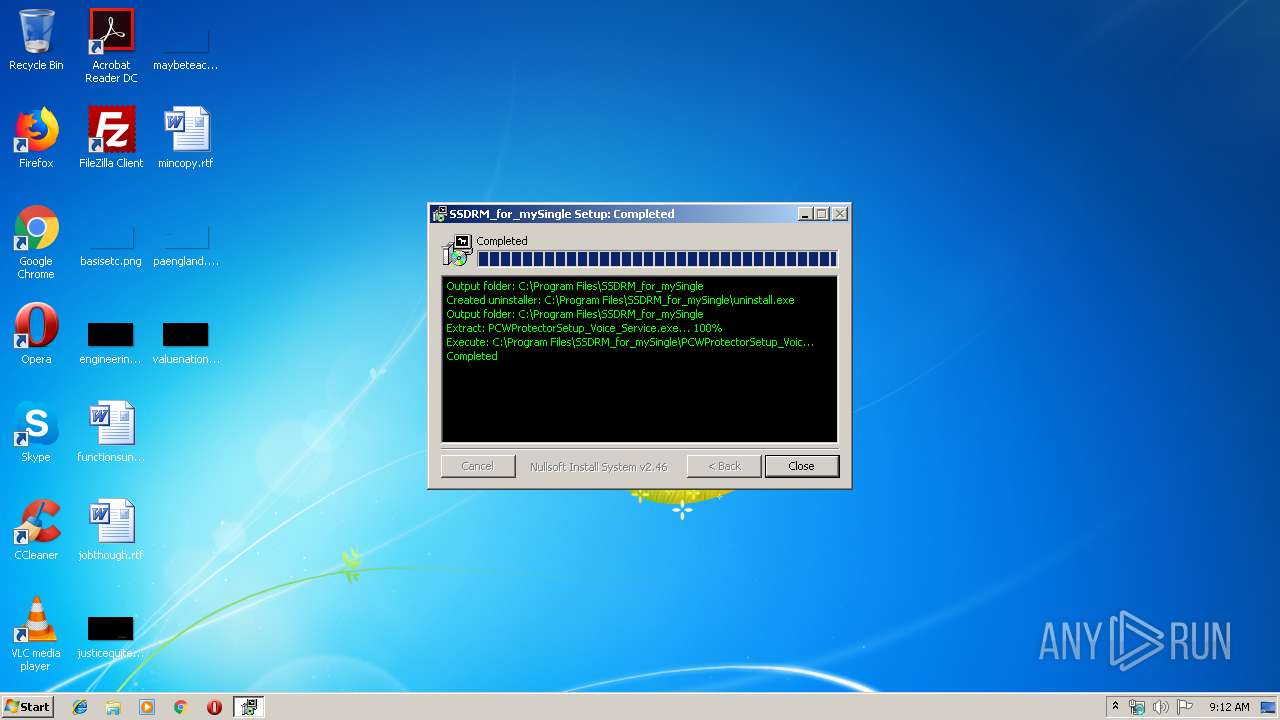
MALICIOUS
Loads dropped or rewritten executable
- SSDRM_for_mySingle.exe (PID: 2436)
- PCWProtectorSetup_Voice_Service.exe (PID: 2692)
- PCWProtectorService.exe (PID: 2828)
- regsvr32.exe (PID: 2368)
- PCWProtector.exe (PID: 3320)
- TsMng.exe (PID: 3292)
- TsService.exe (PID: 4080)
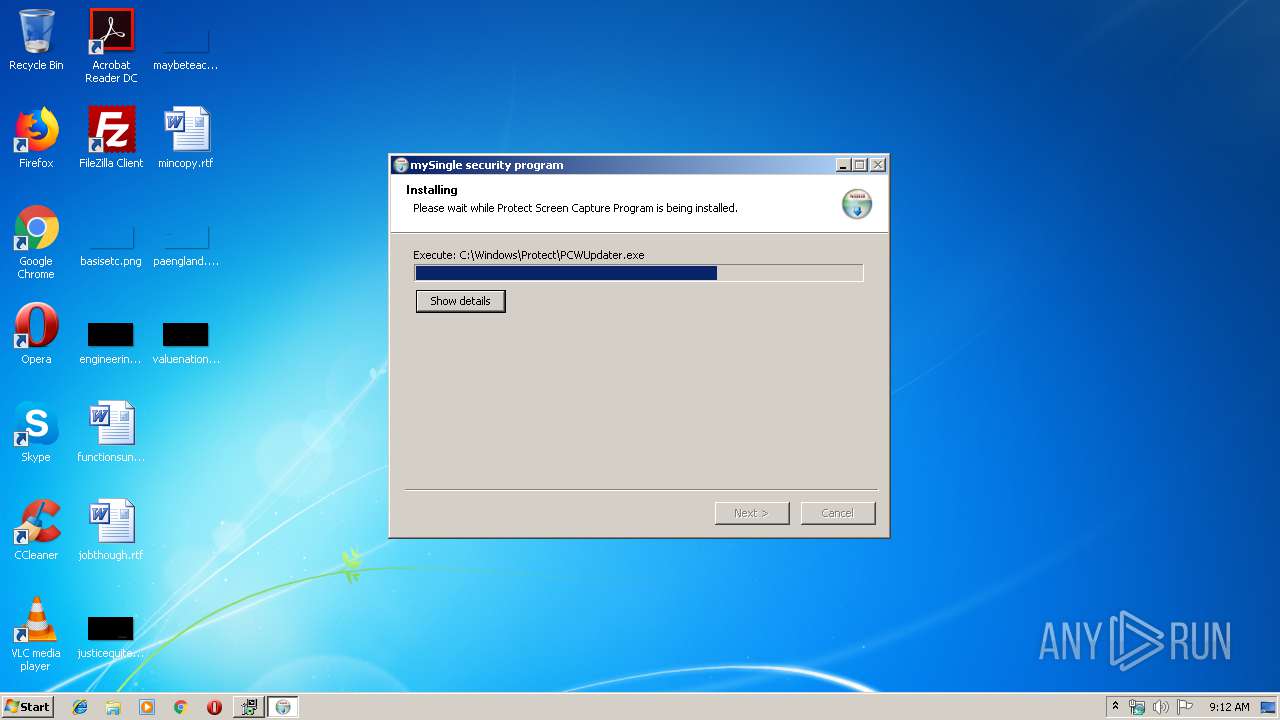
Application was dropped or rewritten from another process
- PCWProtectorSetup_Voice_Service.exe (PID: 2692)
- PCWProtectorDummy.exe (PID: 2324)
- PCWProtector.exe (PID: 3320)
- TsMng.exe (PID: 3292)
- PCWUpdater.exe (PID: 4032)
- PCWProtectorService.exe (PID: 2828)
- TsService.exe (PID: 4080)
Registers / Runs the DLL via REGSVR32.EXE
- PCWProtectorSetup_Voice_Service.exe (PID: 2692)
Changes internet zones settings
- PCWProtectorSetup_Voice_Service.exe (PID: 2692)
SUSPICIOUS
Executable content was dropped or overwritten
- SSDRM_for_mySingle.exe (PID: 2436)
- PCWProtectorSetup_Voice_Service.exe (PID: 2692)
- PCWUpdater.exe (PID: 4032)
- PCWProtectorService.exe (PID: 2828)
- TsMng.exe (PID: 3292)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2504)
- cmd.exe (PID: 3728)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 1920)
Starts CMD.EXE for commands execution
- SSDRM_for_mySingle.exe (PID: 2436)
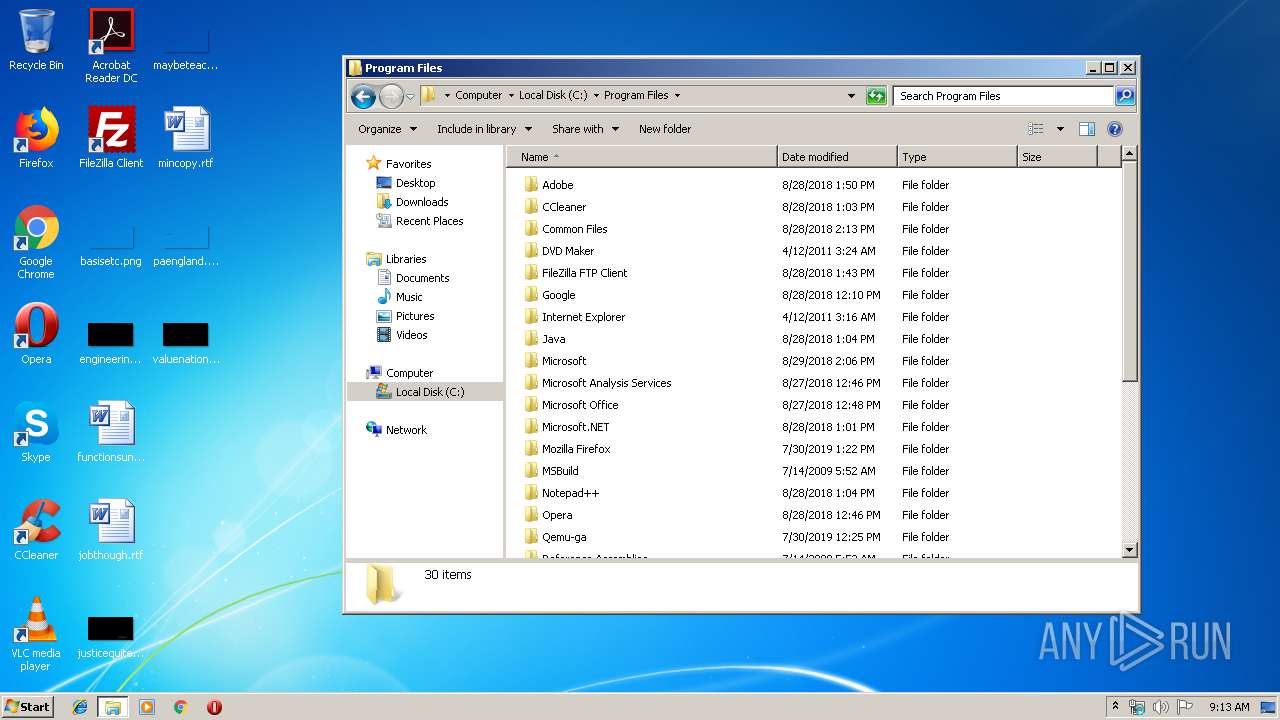
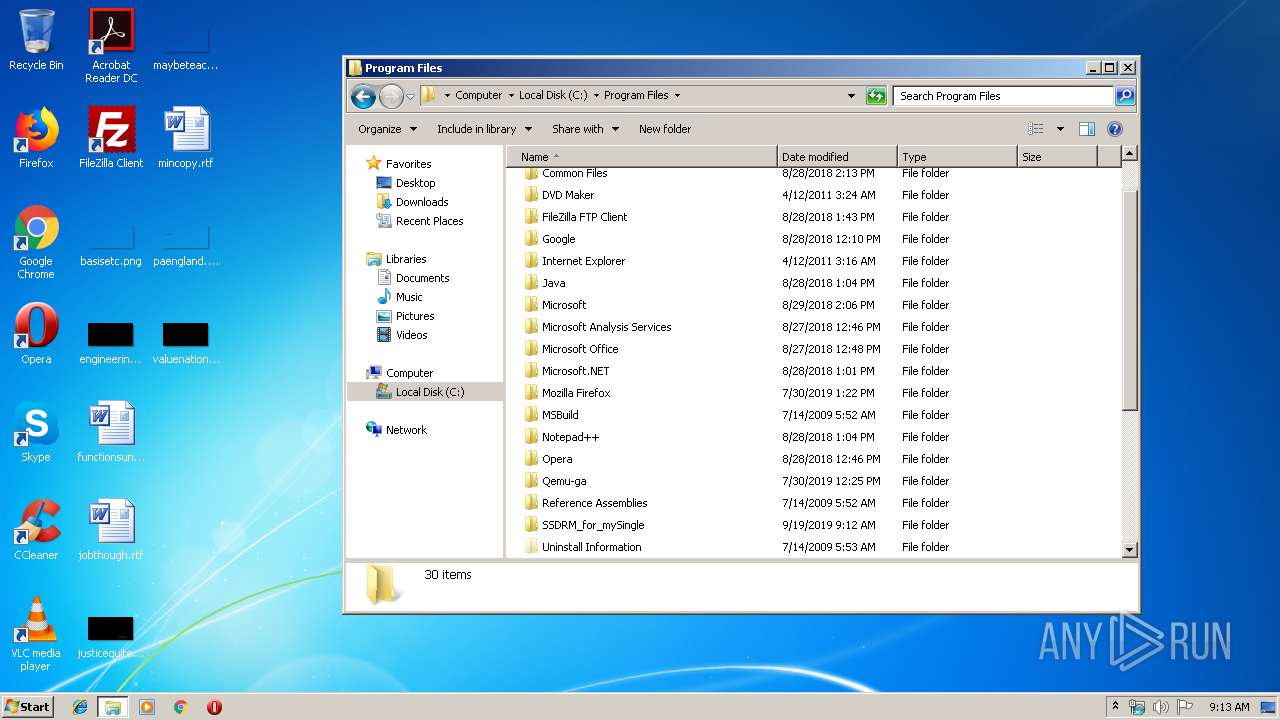
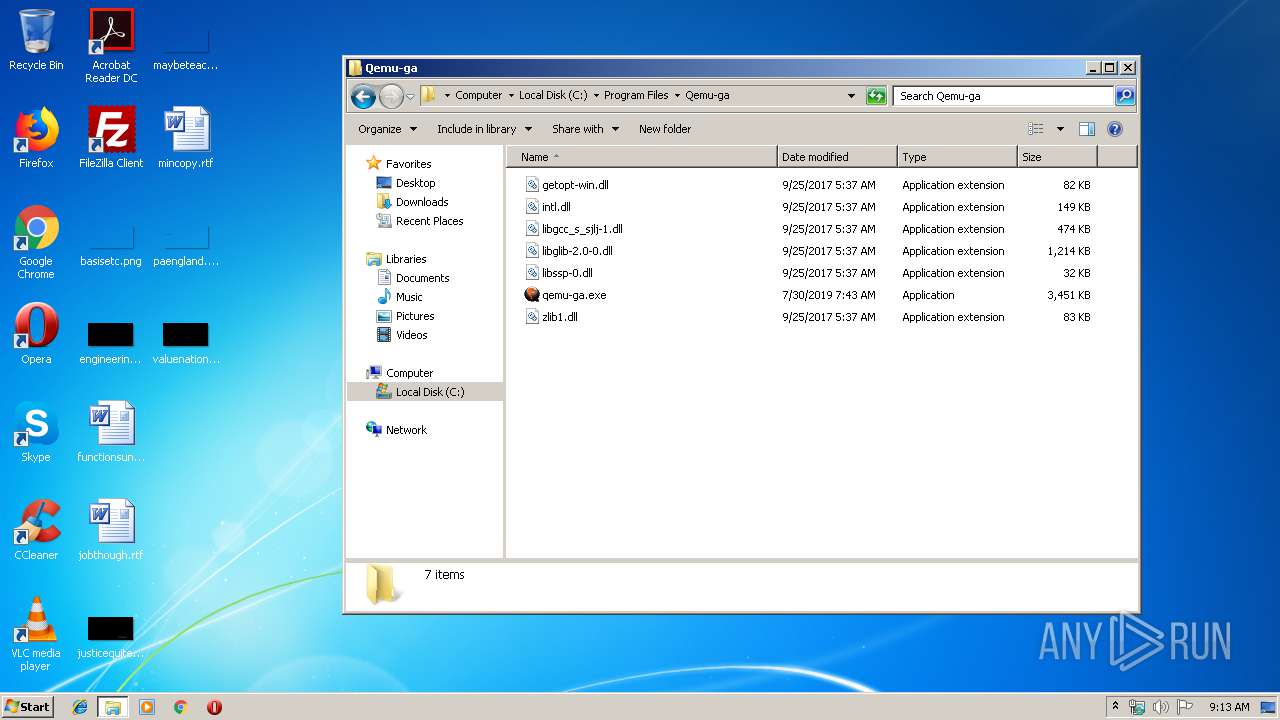
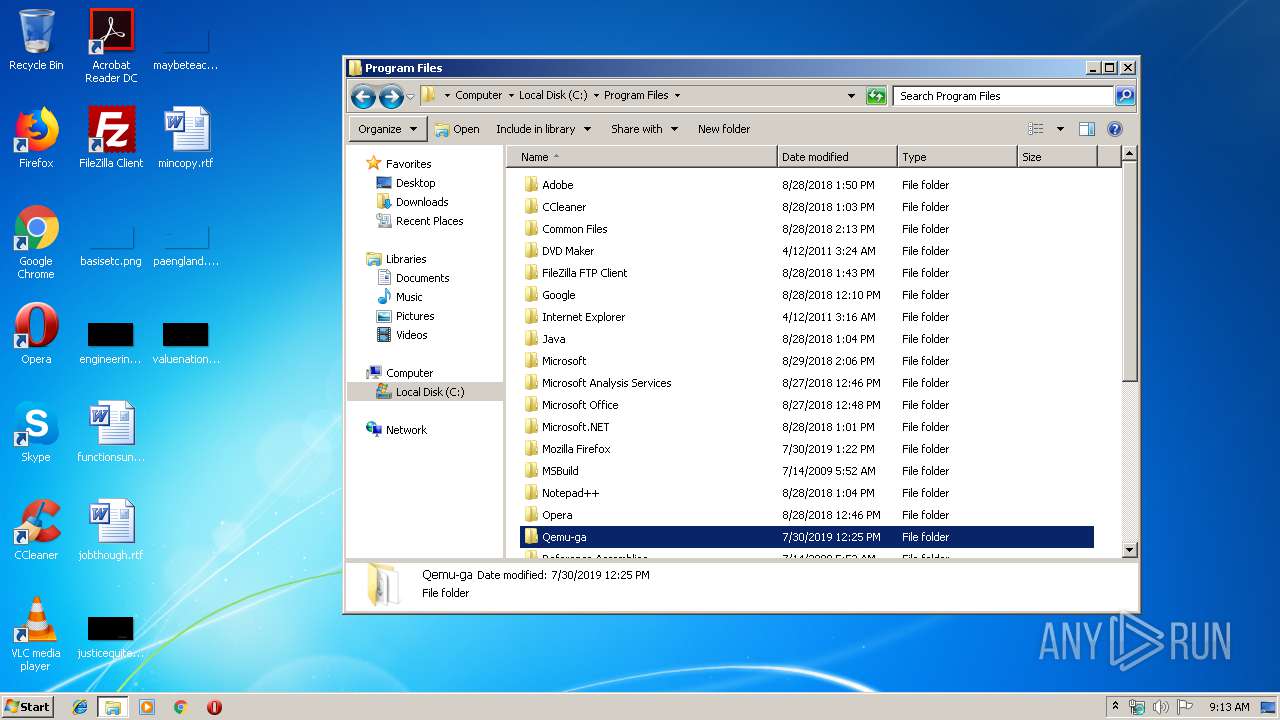
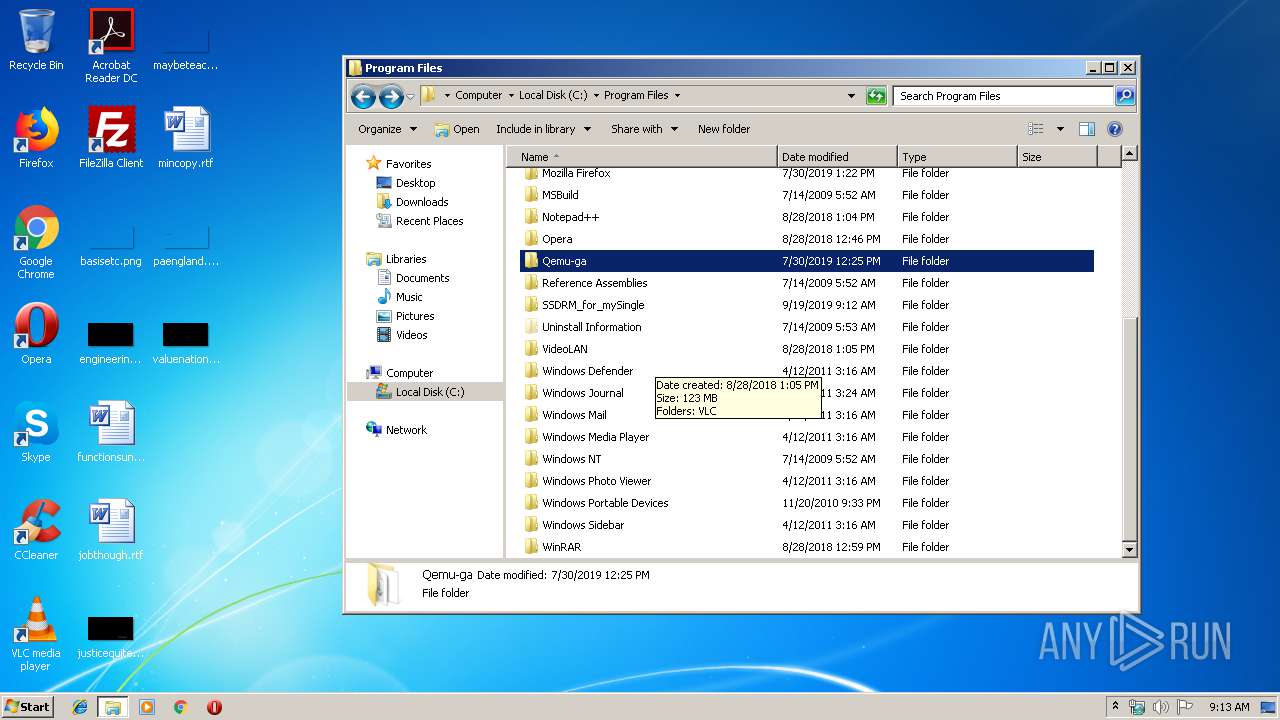
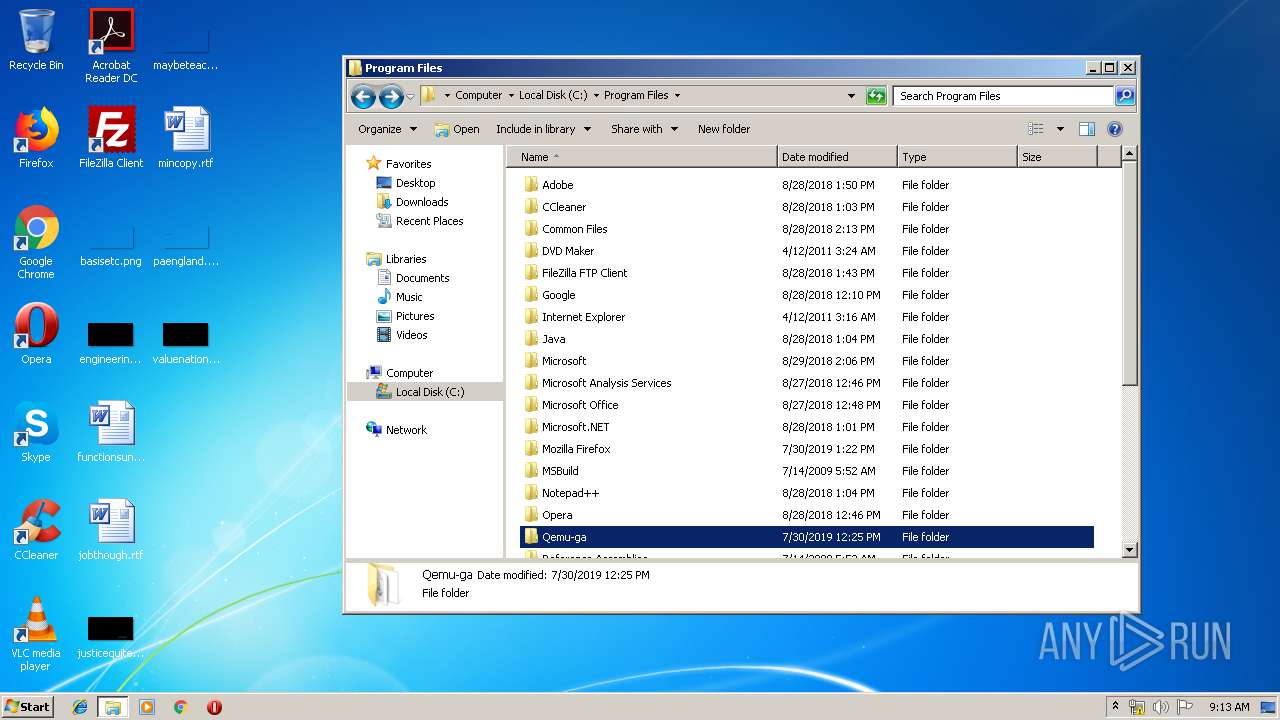
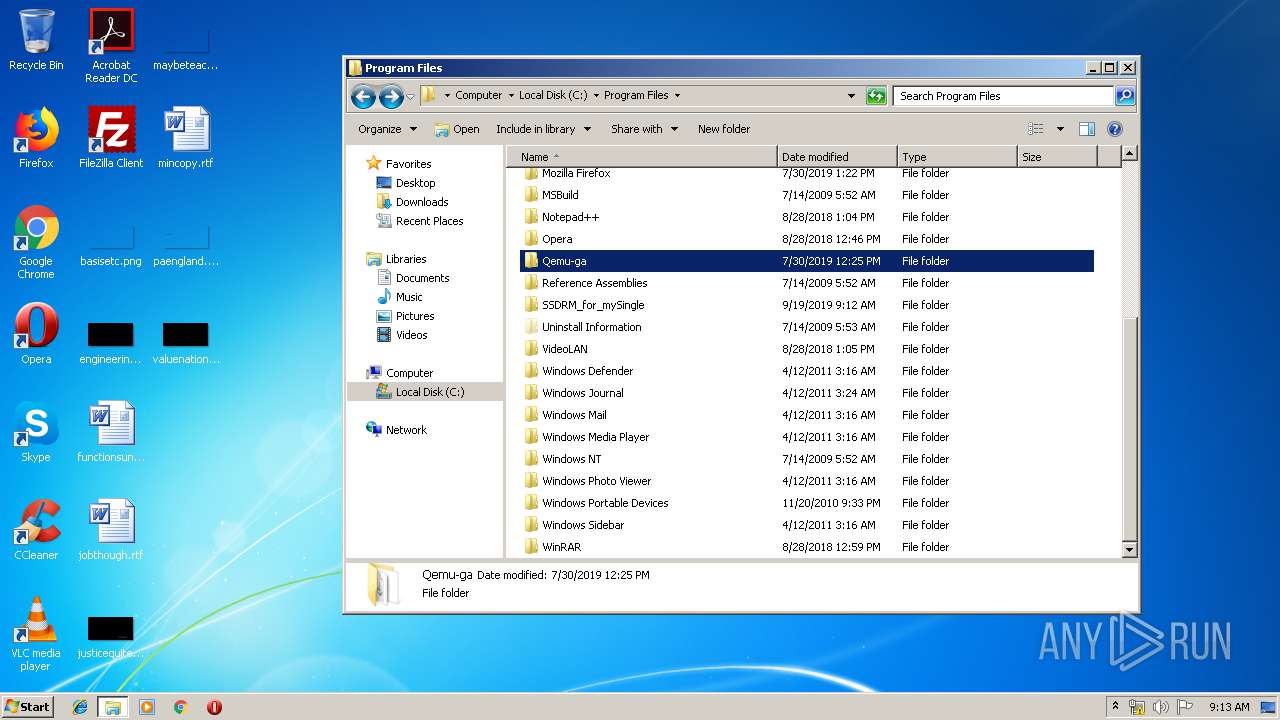
Creates files in the program directory
- SSDRM_for_mySingle.exe (PID: 2436)
Creates a software uninstall entry
- SSDRM_for_mySingle.exe (PID: 2436)
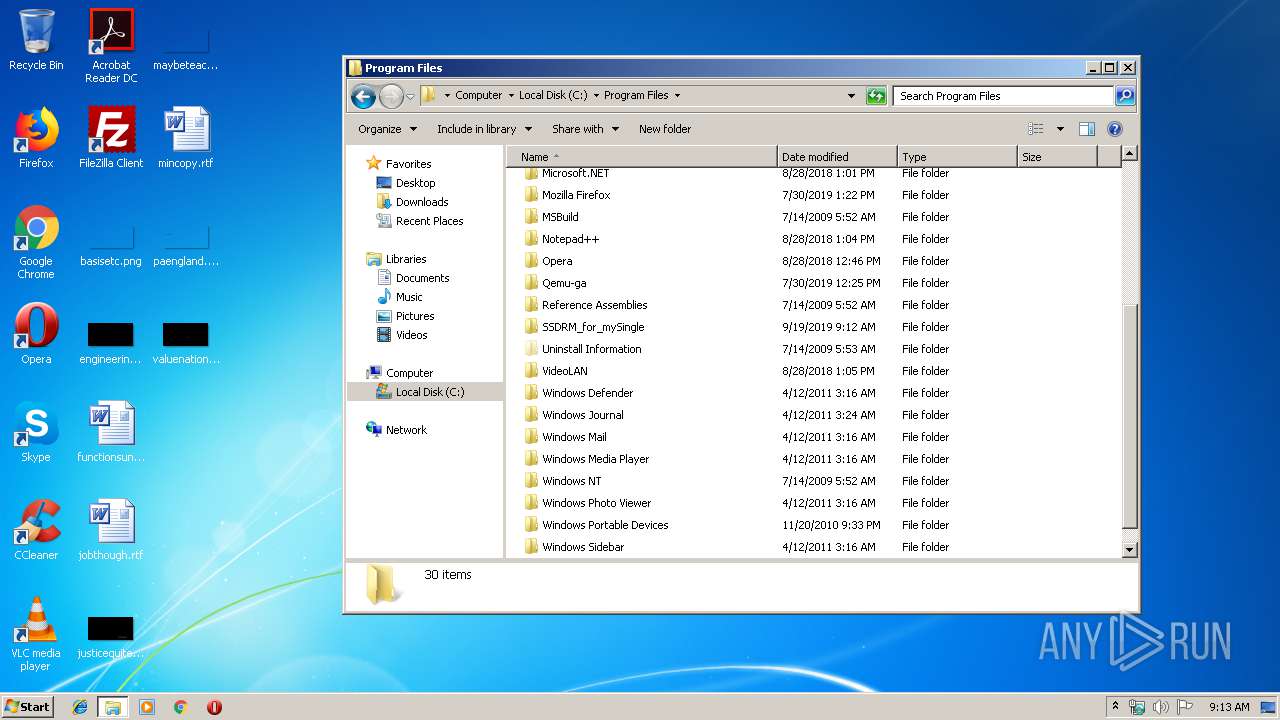
Creates files in the Windows directory
- PCWProtectorSetup_Voice_Service.exe (PID: 2692)
- PCWUpdater.exe (PID: 4032)
- TsMng.exe (PID: 3292)
- PCWProtectorService.exe (PID: 2828)
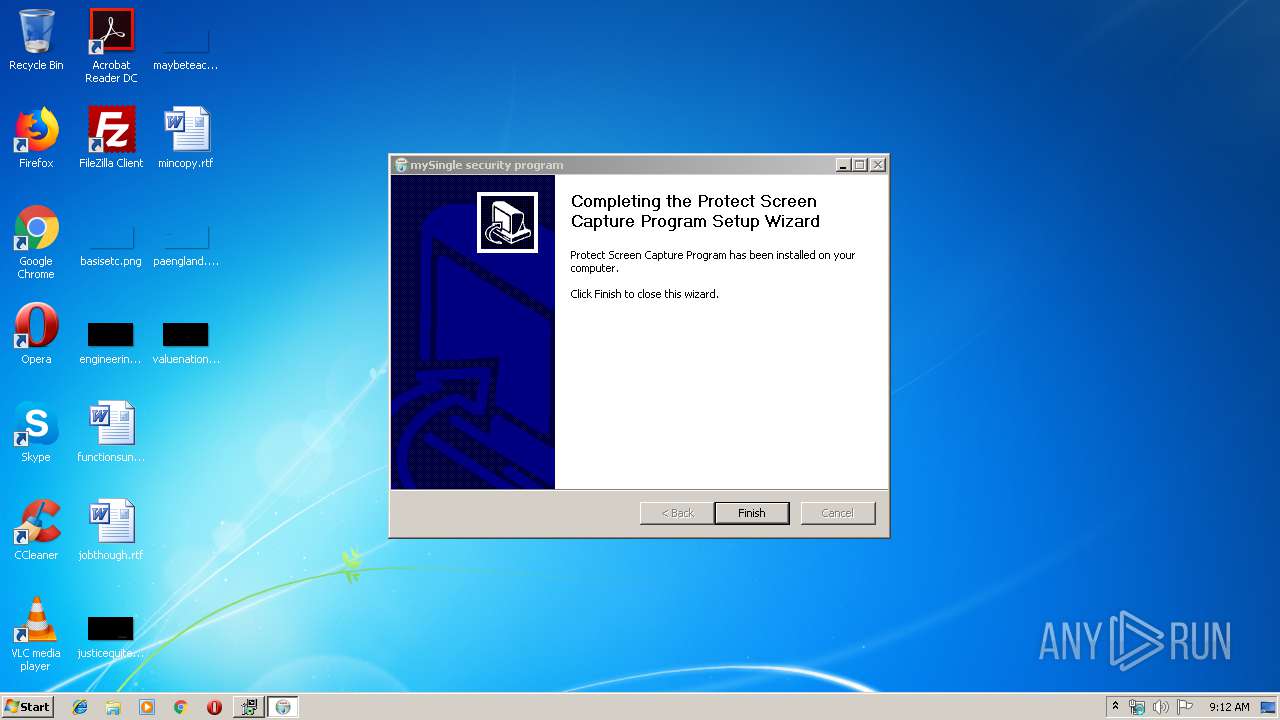
Executed as Windows Service
- PCWProtectorService.exe (PID: 2828)
- TsService.exe (PID: 4080)
Removes files from Windows directory
- PCWProtectorService.exe (PID: 2828)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x00001080 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.20014 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19512 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.6935 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
110 | 3.22336 | 872 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
68
Monitored processes
25
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1248 | C:\Windows\System32\tasklist /NH /FI "IMAGENAME eq VMwareView-rdeServer.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1920 | C:\Windows\system32\cmd.exe /C %SystemRoot%\System32\tasklist /NH /FI "IMAGENAME eq pcoip_server_win32.exe" | %SystemRoot%\System32\find /I "pcoip_server_win32.exe" | C:\Windows\system32\cmd.exe | — | SSDRM_for_mySingle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2008 | C:\Windows\System32\tasklist /NH /FI "IMAGENAME eq xenservice.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2056 | C:\Windows\System32\tasklist /NH /FI "IMAGENAME eq xensvc.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2188 | C:\Windows\System32\find /I "xenservice.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | C:\Windows\system32\cmd.exe /C %SystemRoot%\System32\tasklist /NH /FI "IMAGENAME eq WorkstationAgent.exe" | %SystemRoot%\System32\find /I "WorkstationAgent.exe" | C:\Windows\system32\cmd.exe | — | SSDRM_for_mySingle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2324 | C:\Windows\Protect\PCWProtectorDummy.exe 1 | C:\Windows\Protect\PCWProtectorDummy.exe | — | PCWProtectorService.exe | |||||||||||
User: SYSTEM Company: eSoft.inc Integrity Level: SYSTEM Description: PCWProtectorDummy.exe Exit code: 0 Version: 1.0.3.2 Modules
| |||||||||||||||
| 2368 | C:\Windows\system32\regsvr32.exe /s "C:\Windows\Protect\PCW.ocx" | C:\Windows\system32\regsvr32.exe | — | PCWProtectorSetup_Voice_Service.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | C:\Windows\System32\tasklist /NH /FI "IMAGENAME eq WorkstationAgent.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | C:\Windows\system32\cmd.exe /C %SystemRoot%\System32\tasklist /NH /FI "IMAGENAME eq VMwareView-rdeServer.exe" | %SystemRoot%\System32\find /I "VMwareView-rdeServer.exe" | C:\Windows\system32\cmd.exe | — | SSDRM_for_mySingle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
603
Read events
432
Write events
171
Delete events
0
Modification events
| (PID) Process: | (2436) SSDRM_for_mySingle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SSDRM_for_mySingle |
| Operation: | write | Name: | Install_Dir |
Value: C:\Program Files\SSDRM_for_mySingle | |||
| (PID) Process: | (2436) SSDRM_for_mySingle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SSDRM_for_mySingle |
| Operation: | write | Name: | DisplayName |
Value: SSDRM_for_mySingle | |||
| (PID) Process: | (2436) SSDRM_for_mySingle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SSDRM_for_mySingle |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\SSDRM_for_mySingle\uninstall.exe" | |||
| (PID) Process: | (2436) SSDRM_for_mySingle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SSDRM_for_mySingle |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (2436) SSDRM_for_mySingle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SSDRM_for_mySingle |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (2692) PCWProtectorSetup_Voice_Service.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\samsung.net |
| Operation: | write | Name: | https |
Value: 2 | |||
| (PID) Process: | (2692) PCWProtectorSetup_Voice_Service.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\samsung.net |
| Operation: | write | Name: | http |
Value: 2 | |||
| (PID) Process: | (2692) PCWProtectorSetup_Voice_Service.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2692) PCWProtectorSetup_Voice_Service.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2692) PCWProtectorSetup_Voice_Service.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | DisplayName |
Value: Trusted sites | |||
Executable files
38
Suspicious files
0
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | PCWProtectorSetup_Voice_Service.exe | C:\Users\admin\AppData\Local\Temp\nszB626.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2436 | SSDRM_for_mySingle.exe | C:\Program Files\SSDRM_for_mySingle\uninstall.exe | executable | |
MD5:2528F5C2C03C7D4F6B275189B68F787F | SHA256:10E53758628393A9B991015F18329D5C160AF6ED3EBC87C08219811A2E19E88B | |||
| 2692 | PCWProtectorSetup_Voice_Service.exe | C:\Users\admin\AppData\Local\Temp\nszB626.tmp\PCWProtector.log | text | |
MD5:FE66A57578E17AD360AB1A5EE9508730 | SHA256:226CA4CE9E25D28D691C3430A706D9A20095AEC6A2B479167A29CA2DBDCEB621 | |||
| 2692 | PCWProtectorSetup_Voice_Service.exe | C:\Users\admin\AppData\Local\Temp\nszB626.tmp\UserInfo.dll | executable | |
MD5:7579ADE7AE1747A31960A228CE02E666 | SHA256:564C80DEC62D76C53497C40094DB360FF8A36E0DC1BDA8383D0F9583138997F5 | |||
| 2692 | PCWProtectorSetup_Voice_Service.exe | C:\Windows\Protect\TDCommonLibup.dll | executable | |
MD5:AC67F6EFEFD9227789AEFA657264508B | SHA256:35A1FE7507C35696348FB28C6F3CB5E9C2FE1A8A6966B0A0B8FD469E521F384D | |||
| 2692 | PCWProtectorSetup_Voice_Service.exe | C:\Windows\Protect\T_Preventup.dll | executable | |
MD5:C84ED9FE6E818185B971A6D10F0C16B7 | SHA256:2A3324961C95098164646161108231510135F461D73E8FF07A1EE1216FFF286F | |||
| 2692 | PCWProtectorSetup_Voice_Service.exe | C:\Users\admin\AppData\Local\Temp\nszB626.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 2436 | SSDRM_for_mySingle.exe | C:\Users\admin\AppData\Local\Temp\nsnB06A.tmp\ExecCmd.dll | executable | |
MD5:B9380B0BEA8854FD9F93CC1FDA0DFEAC | SHA256:1F4BD9C9376FE1B6913BAECA7FB6DF6467126F27C9C2FE038206567232A0E244 | |||
| 2692 | PCWProtectorSetup_Voice_Service.exe | C:\Users\admin\AppData\Local\Temp\nszB626.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2692 | PCWProtectorSetup_Voice_Service.exe | C:\Windows\Protect\policy.ini | text | |
MD5:E3A57C8F51F8C65DCE2953825A351738 | SHA256:C5EE4C09ED74C916261A404CA229EB22CFA731C17C4A49F766FB17E61CB45546 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
TsService.exe | Tptm load
|
TsMng.exe | CTsMngApp::InitInstance
|