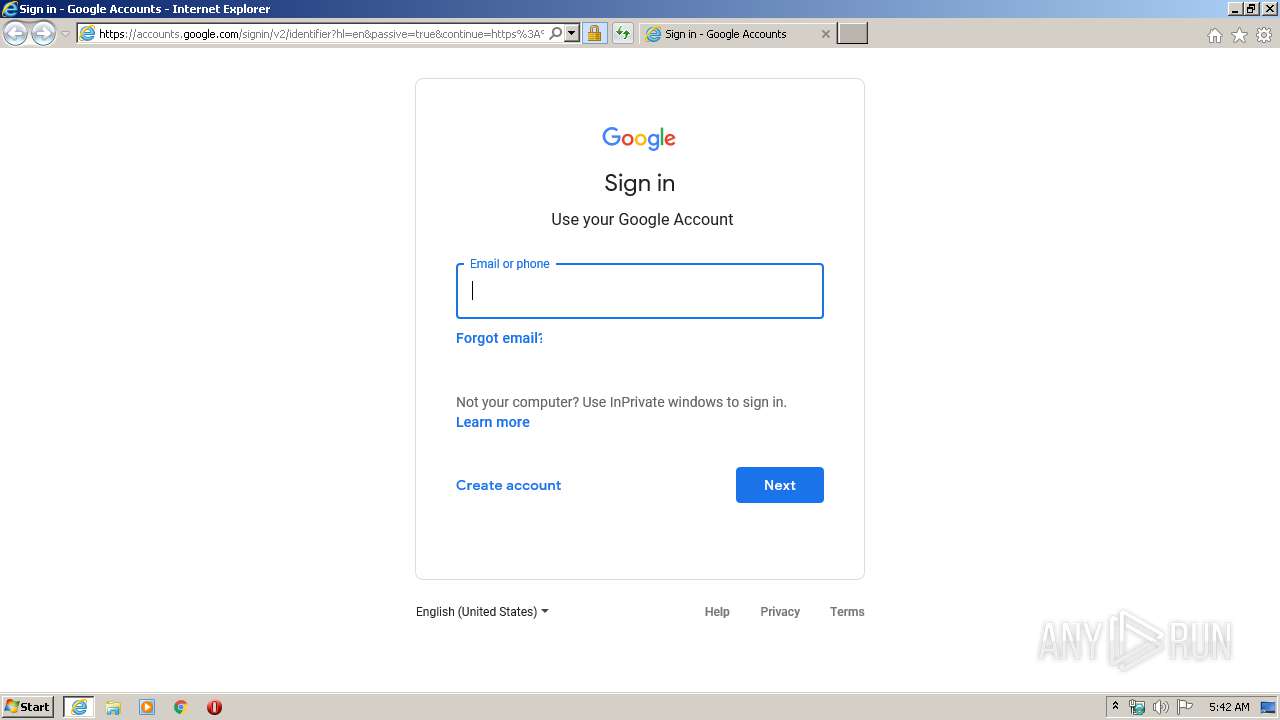
| URL: | https://accounts.google.com/signin/v2/identifier?hl=en&passive=true&continue=https%3A%2F%2Fwww.google.com%2F%3Fgws_rd%3Dssl&flowName=GlifWebSignIn&flowEntry=ServiceLogin |
| Full analysis: | https://app.any.run/tasks/083913b5-b89f-4986-a0e4-cd26ecb2dad7 |
| Verdict: | No threats detected |
| Analysis date: | April 22, 2020, 04:41:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EB9864118C8FECC8625C5A3ED2EA5EF2 |
| SHA1: | 36598A2F8E5F665144C3B4F5D4D90CDF8A3A3F00 |
| SHA256: | 889483CE2DA30D27C2861CA82859C28382FB228A8CC5E43E82DA7AAFBB0B48DE |
| SSDEEP: | 3:N8kKVJ3uwMC4LIaRwGJX/LTAGXLaURRWCXjjiSLAmvD7EIAYeAH2Mthu32pbK:2kw+wcLIaqeX/LMsmU1zjx0chAa2MtKD |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 304)
Reads Internet Cache Settings
- iexplore.exe (PID: 304)
- iexplore.exe (PID: 1064)
Changes internet zones settings
- iexplore.exe (PID: 304)
Creates files in the user directory
- iexplore.exe (PID: 1064)
Reads internet explorer settings
- iexplore.exe (PID: 1064)
Reads settings of System Certificates
- iexplore.exe (PID: 1064)
Changes settings of System certificates
- iexplore.exe (PID: 304)
Adds / modifies Windows certificates
- iexplore.exe (PID: 304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Internet Explorer\iexplore.exe" https://accounts.google.com/signin/v2/identifier?hl=en&passive=true&continue=https%3A%2F%2Fwww.google.com%2F%3Fgws_rd%3Dssl&flowName=GlifWebSignIn&flowEntry=ServiceLogin | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:304 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
4 107
Read events
476
Write events
2 442
Delete events
1 189
Modification events
| (PID) Process: | (1064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1064) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1752230890 | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30808160 | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
28
Text files
9
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF3CE.tmp | — | |
MD5:— | SHA256:— | |||
| 1064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF3DF.tmp | — | |
MD5:— | SHA256:— | |||
| 304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1064 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ServiceLogin[1].htm | html | |
MD5:— | SHA256:— | |||
| 1064 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1G23L19Q.txt | — | |
MD5:— | SHA256:— | |||
| 1064 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PJ5UD15E.txt | text | |
MD5:— | SHA256:— | |||
| 1064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BE8B021F9E811DFC8C8A28572A17C05A_BF2E7601425169245F1A9FAE99553FE2 | der | |
MD5:— | SHA256:— | |||
| 1064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 1064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_BF2E7601425169245F1A9FAE99553FE2 | binary | |
MD5:— | SHA256:— | |||
| 1064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_89601A5EE40FA97B49E5FF36C7B865F0 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
34
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1064 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEEw0ZZD0YkphCAAAAAA3kSg%3D | US | der | 471 b | whitelisted |
1064 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFf6pFEneJKLCAAAAAA3kVE%3D | US | der | 471 b | whitelisted |
304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1064 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEEw0ZZD0YkphCAAAAAA3kSg%3D | US | der | 471 b | whitelisted |
1064 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://crl.pki.goog/GTS1O1.crl | US | binary | 83.0 Kb | whitelisted |
304 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1064 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 950 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1064 | iexplore.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.206:443 | accounts.youtube.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1064 | iexplore.exe | 216.58.207.78:443 | play.google.com | Google Inc. | US | whitelisted |
1064 | iexplore.exe | 172.217.21.206:443 | accounts.youtube.com | Google Inc. | US | whitelisted |
304 | iexplore.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
1064 | iexplore.exe | 216.58.207.67:80 | crl.pki.goog | Google Inc. | US | whitelisted |
304 | iexplore.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
304 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1064 | iexplore.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
accounts.youtube.com |
| whitelisted |
play.google.com |
| whitelisted |
www.google.com |
| malicious |
crl.pki.goog |
| whitelisted |