| File name: | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe |
| Full analysis: | https://app.any.run/tasks/0f472ccc-35c0-41d2-83cd-b0748439626b |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2024, 14:11:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B3353FE84B5E8DE4E5E2E0E64B7CF625 |
| SHA1: | A8BB2D5917E61C566308CB68D80066A5E23450B9 |
| SHA256: | 888C74512D59E6F5890BFF6424E73D72245A3DF2BB6D2BD3A8B31D55E541D1AE |
| SSDEEP: | 49152:lh1JIGYsUlmFFkN1CrsrUXoaqUHtmmtNybxdKEd0tima5oUtJnfSf8wQpU5NjI1e:lh1JIGYvl4FkN1RA4a/HtmmXybxdL5PU |
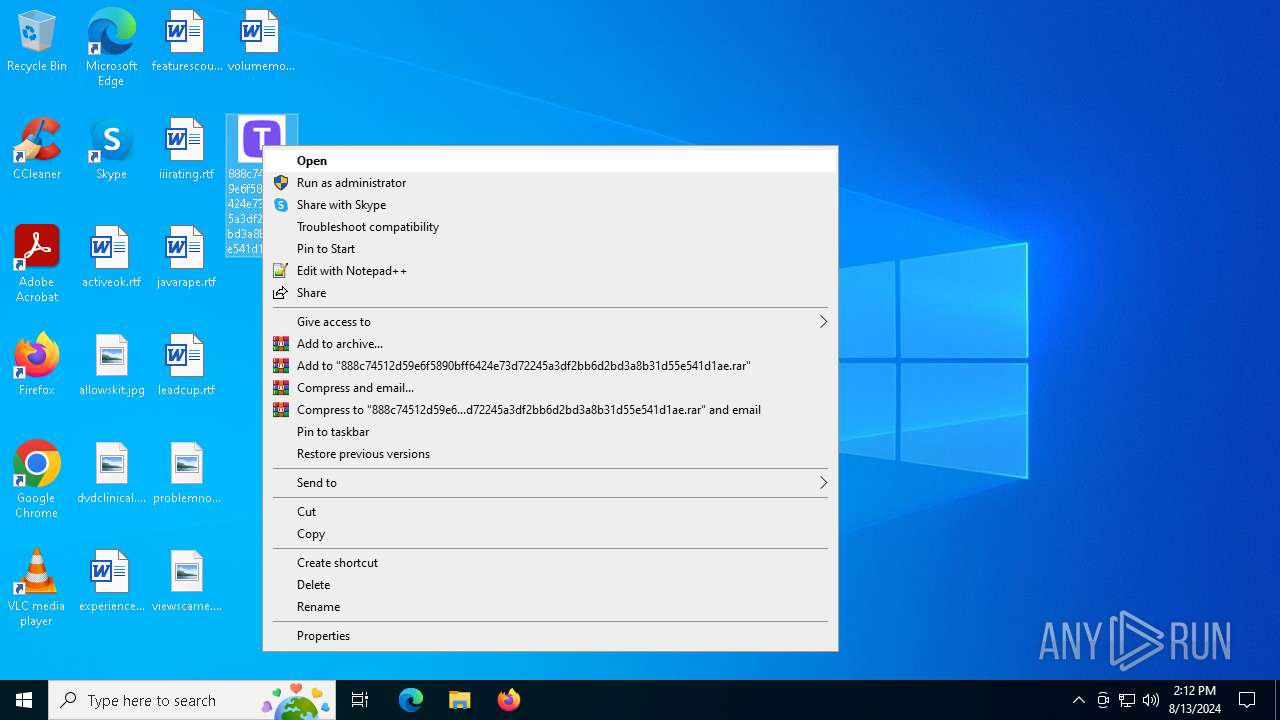
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 6712)
- findstr.exe (PID: 6832)
SUSPICIOUS
Reads the date of Windows installation
- 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe (PID: 6544)
Drops the executable file immediately after the start
- 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe (PID: 6544)
- cmd.exe (PID: 6624)
Reads security settings of Internet Explorer
- 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe (PID: 6544)
- Dive.pif (PID: 6228)
Starts CMD.EXE for commands execution
- 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe (PID: 6544)
- cmd.exe (PID: 6624)
Executing commands from ".cmd" file
- 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe (PID: 6544)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6624)
Get information on the list of running processes
- cmd.exe (PID: 6624)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 6624)
Application launched itself
- cmd.exe (PID: 6624)
The executable file from the user directory is run by the CMD process
- Dive.pif (PID: 7132)
Executable content was dropped or overwritten
- cmd.exe (PID: 6624)
Checks Windows Trust Settings
- Dive.pif (PID: 6228)
Starts application with an unusual extension
- cmd.exe (PID: 6624)
INFO
Process checks computer location settings
- 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe (PID: 6544)
Reads the computer name
- 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe (PID: 6544)
- Dive.pif (PID: 7132)
- Dive.pif (PID: 6228)
Checks supported languages
- 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe (PID: 6544)
- Dive.pif (PID: 7132)
- Dive.pif (PID: 6228)
Create files in a temporary directory
- 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe (PID: 6544)
Reads mouse settings
- Dive.pif (PID: 7132)
Manual execution by a user
- Dive.pif (PID: 6228)
Checks proxy server information
- Dive.pif (PID: 6228)
Reads the machine GUID from the registry
- Dive.pif (PID: 6228)
Reads the software policy settings
- Dive.pif (PID: 6228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 19:20:04+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 29696 |
| InitializedDataSize: | 491008 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x38af |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.0.726 |
| ProductVersionNumber: | 1.5.0.726 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | SHADOWDEFENDER.COM |
| FileDescription: | Shadow Defender Application |
| FileVersion: | 1.5.0.726 |
| InternalName: | Defender.exe |
| LegalCopyright: | Copyright (C) 2007-2020, SHADOWDEFENDER.COM. All rights reserved. |
| OriginalFileName: | Defender.exe |
| ProductName: | Shadow Defender |
| ProductVersion: | 1.5.0.726 |
Total processes
133
Monitored processes
14
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6228 | C:\Users\admin\AppData\Local\Temp\552459\Dive.pif | C:\Users\admin\AppData\Local\Temp\552459\Dive.pif | explorer.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Version: 3, 3, 15, 1 Modules
| |||||||||||||||
| 6240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Dive.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6460 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6544 | "C:\Users\admin\Desktop\888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe" | C:\Users\admin\Desktop\888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | — | explorer.exe | |||||||||||
User: admin Company: SHADOWDEFENDER.COM Integrity Level: MEDIUM Description: Shadow Defender Application Exit code: 0 Version: 1.5.0.726 Modules
| |||||||||||||||
| 6624 | "C:\Windows\System32\cmd.exe" /k move Centered Centered.cmd & Centered.cmd & exit | C:\Windows\SysWOW64\cmd.exe | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 9009 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6648 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6704 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6712 | findstr /I "wrsa.exe opssvc.exe" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6824 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6832 | findstr /I "avastui.exe avgui.exe bdservicehost.exe ekrn.exe nswscsvc.exe sophoshealth.exe" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 901
Read events
5 882
Write events
19
Delete events
0
Modification events
| (PID) Process: | (6544) 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6544) 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6544) 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6544) 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6228) Dive.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6228) Dive.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6228) Dive.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6228) Dive.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6228) Dive.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6228) Dive.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
1
Suspicious files
11
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6544 | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | C:\Users\admin\AppData\Local\Temp\Unusual | binary | |
MD5:2C9FB51DF51021989AACA1EDECF2C1F3 | SHA256:B0074BD7C32EEF4670B292641445D8E29522C028D124CBB324AB76024C8A3D38 | |||
| 6544 | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | C:\Users\admin\AppData\Local\Temp\Congo | binary | |
MD5:F1B31EF4ABA242A3B771A17E26BF2292 | SHA256:46E15D27891C23CDE64C1A08623635CC61CE8328A9E9FBA64E49D29E854107C6 | |||
| 6624 | cmd.exe | C:\Users\admin\AppData\Local\Temp\552459\Dive.pif | executable | |
MD5:49C35716DE5E35F61688E580E2C7F12A | SHA256:B43AEBBCF07C5A4DA89B0BCFB53FEF52D3D1B00CB52BA9B6596FDB57A070B13F | |||
| 6544 | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | C:\Users\admin\AppData\Local\Temp\Signing | binary | |
MD5:52B0E657DFC4CACFD969AA0FB078C6EA | SHA256:50836F76BECF1F9128A480E355B513942FAA5A44FD66C82C59C65008268ED09E | |||
| 6544 | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | C:\Users\admin\AppData\Local\Temp\Seeking | binary | |
MD5:A9FC4F9A828FEF13E1FC07DEF62624E0 | SHA256:EBACB5BDFEC14F1405EB85636621F7B423C0E395E5EE01DDD28F7F99A5B232C8 | |||
| 6544 | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | C:\Users\admin\AppData\Local\Temp\Median | binary | |
MD5:78F3EC02BBBE0184B9940BB638B76F37 | SHA256:51360C1A04A0EB2DFA42AB93601B397B1EFD64C2C4F41ECDF13DF5ACD58287AC | |||
| 6544 | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | C:\Users\admin\AppData\Local\Temp\Providence | binary | |
MD5:B2D67B8312D5E5C0BCAB6BFF228194C7 | SHA256:A8BAF58C072872FFB3395A2E2EC44DB115AD6F41CBB5A5C873C0E4498505F727 | |||
| 6544 | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | C:\Users\admin\AppData\Local\Temp\Ion | binary | |
MD5:7607F305E8DCA1834EFA39D70491CCFA | SHA256:091AEEA7B5BF473766F771DB79C592E6A048E9A3A1D88877B33319488AB737C9 | |||
| 6544 | 888c74512d59e6f5890bff6424e73d72245a3df2bb6d2bd3a8b31d55e541d1ae.exe | C:\Users\admin\AppData\Local\Temp\Committees | binary | |
MD5:6F9A0F23A5B4F13FAF934BD5430A7289 | SHA256:48347E33CD3F50E1B40B938E50F31E79191A72B4A00C2D56840C073002955C24 | |||
| 6624 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Centered.cmd | text | |
MD5:A561C17D4FB241DD4EA914FEF1A47BDB | SHA256:2BC6E4395C9F0925357D316A50A802496420C4AD0285B6AA6B8BEEE7688E1062 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
20
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 193.43.104.208:443 | https://dotnetisnotforchildren.com/api/kcehc | unknown | binary | 9 b | unknown |
— | — | POST | — | 193.43.104.208:443 | https://dotnetisnotforchildren.com/api/kcehc | unknown | — | — | unknown |
— | — | POST | 200 | 193.43.104.208:443 | https://dotnetisnotforchildren.com/api/time_check | unknown | ini | 2 b | unknown |
— | — | POST | 200 | 193.43.104.208:443 | https://dotnetisnotforchildren.com/api/time_check | unknown | ini | 2 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
2680 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2680 | svchost.exe | 52.137.106.217:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4324 | svchost.exe | 52.137.106.217:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6228 | Dive.pif | 193.43.104.208:443 | dotnetisnotforchildren.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
GWnedjqdKILRPXOoh.GWnedjqdKILRPXOoh |
| unknown |
dotnetisnotforchildren.com |
| unknown |