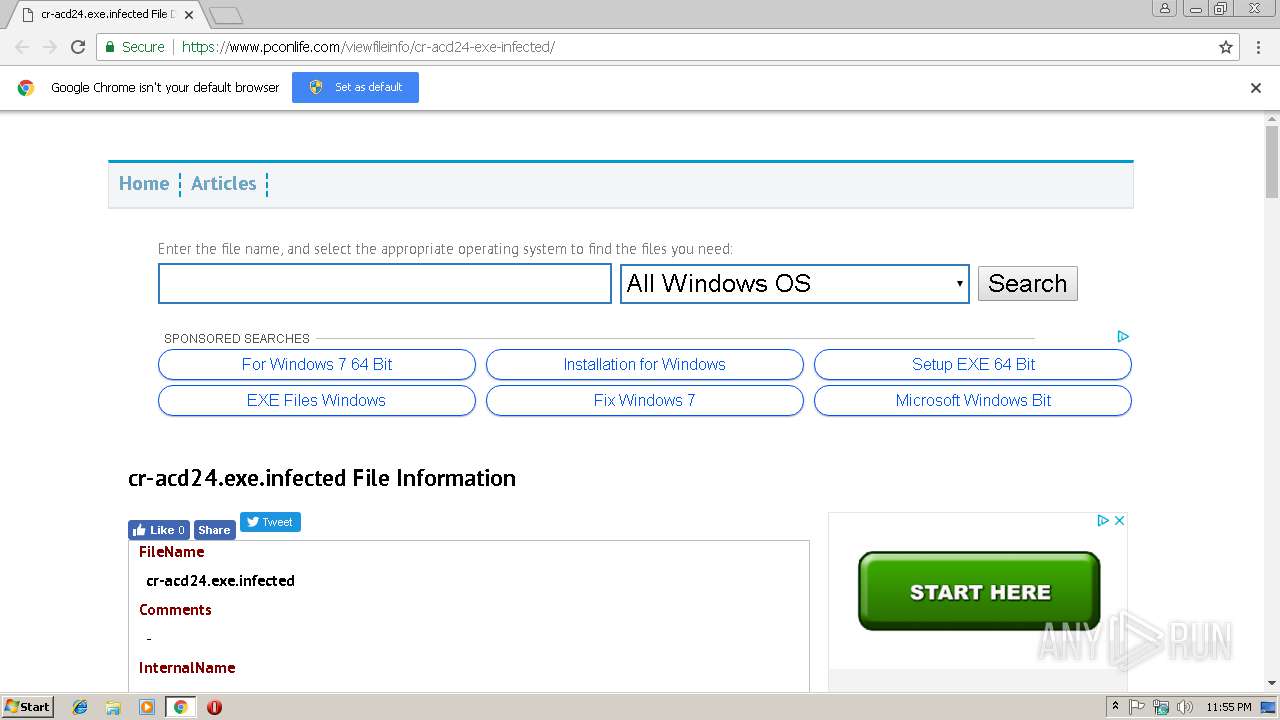
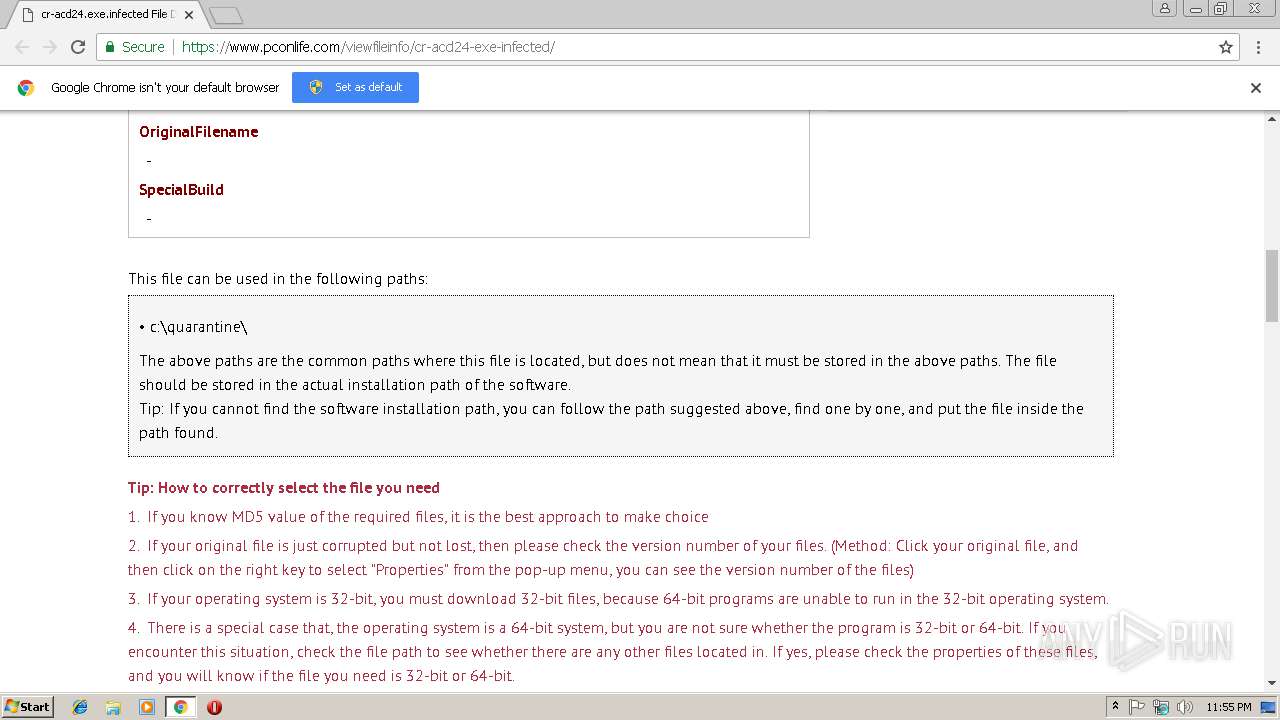
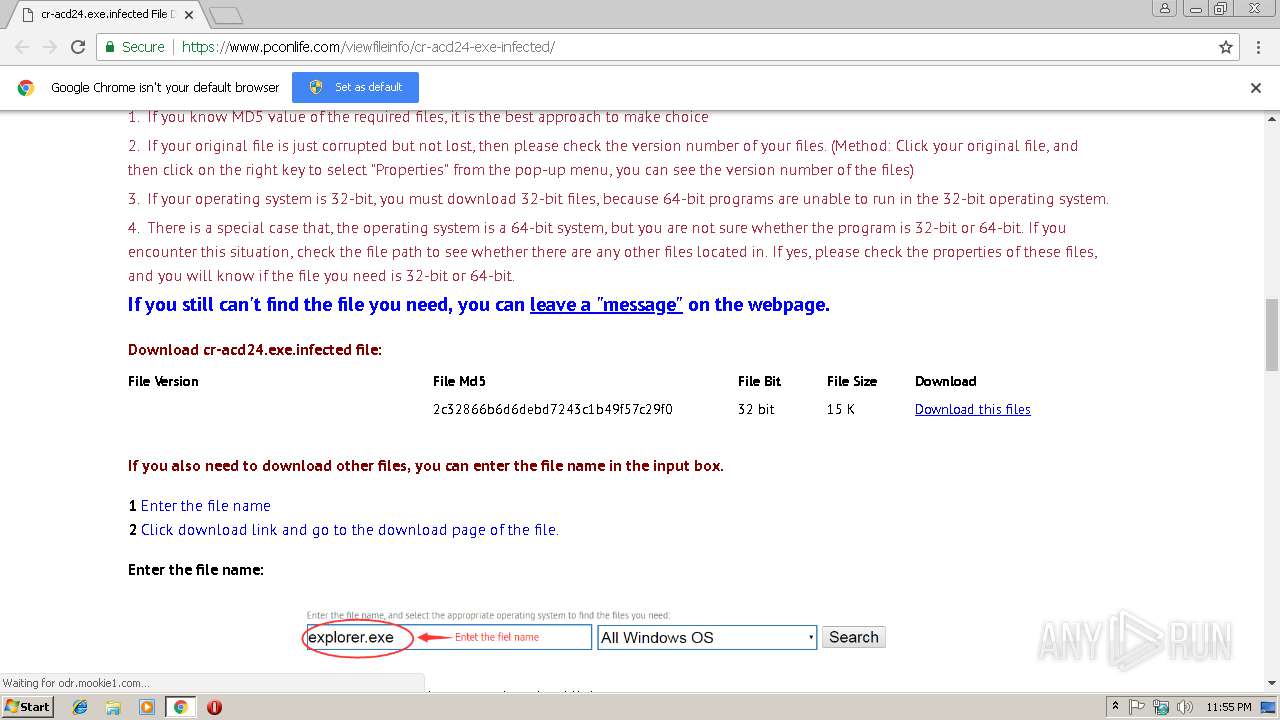
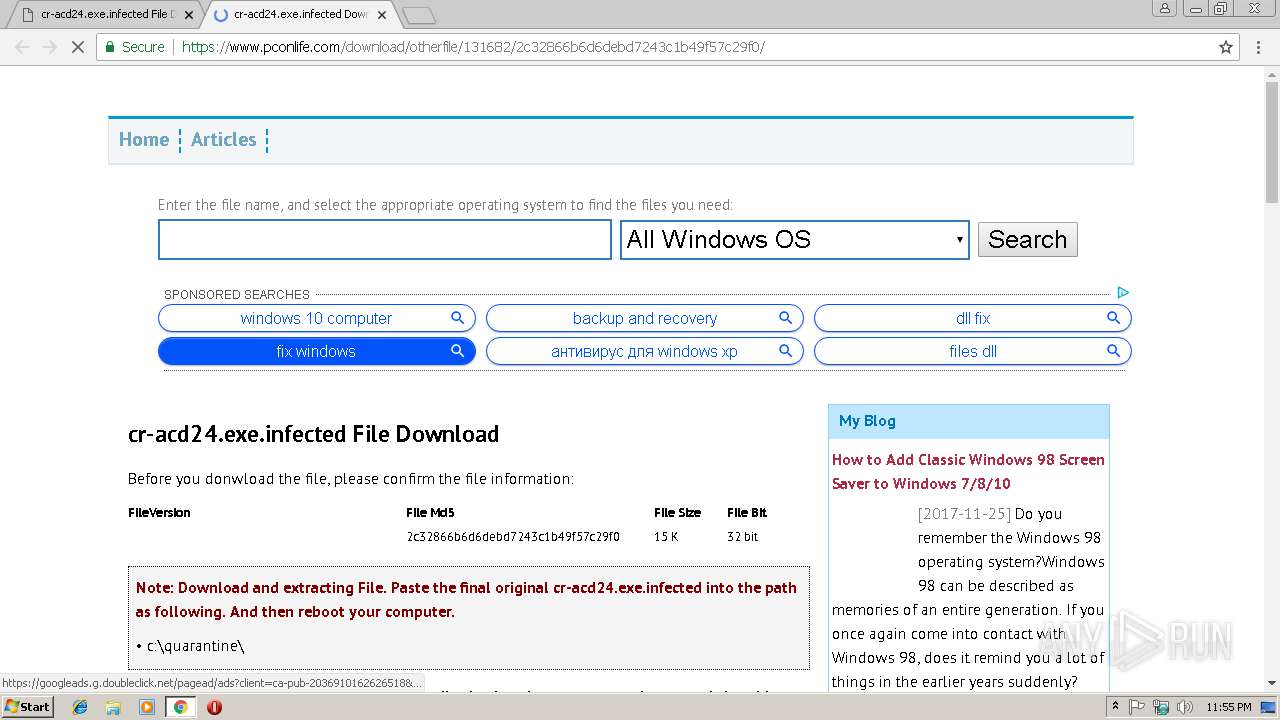
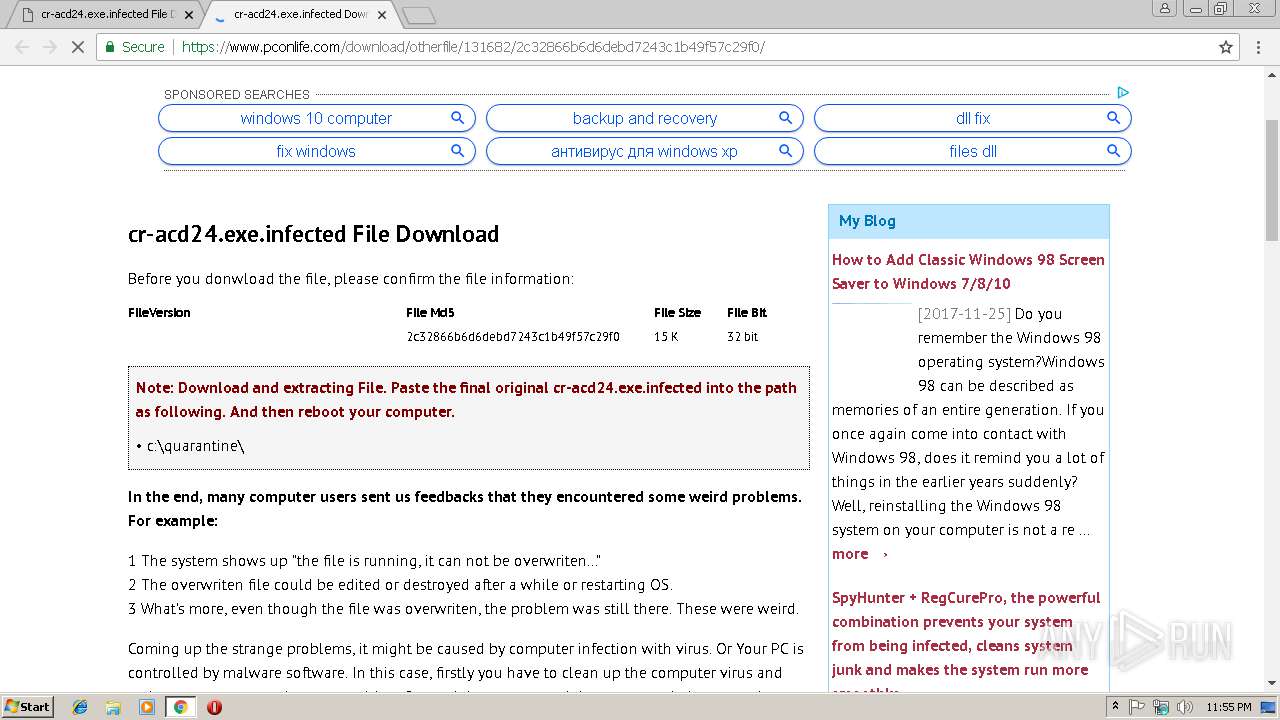
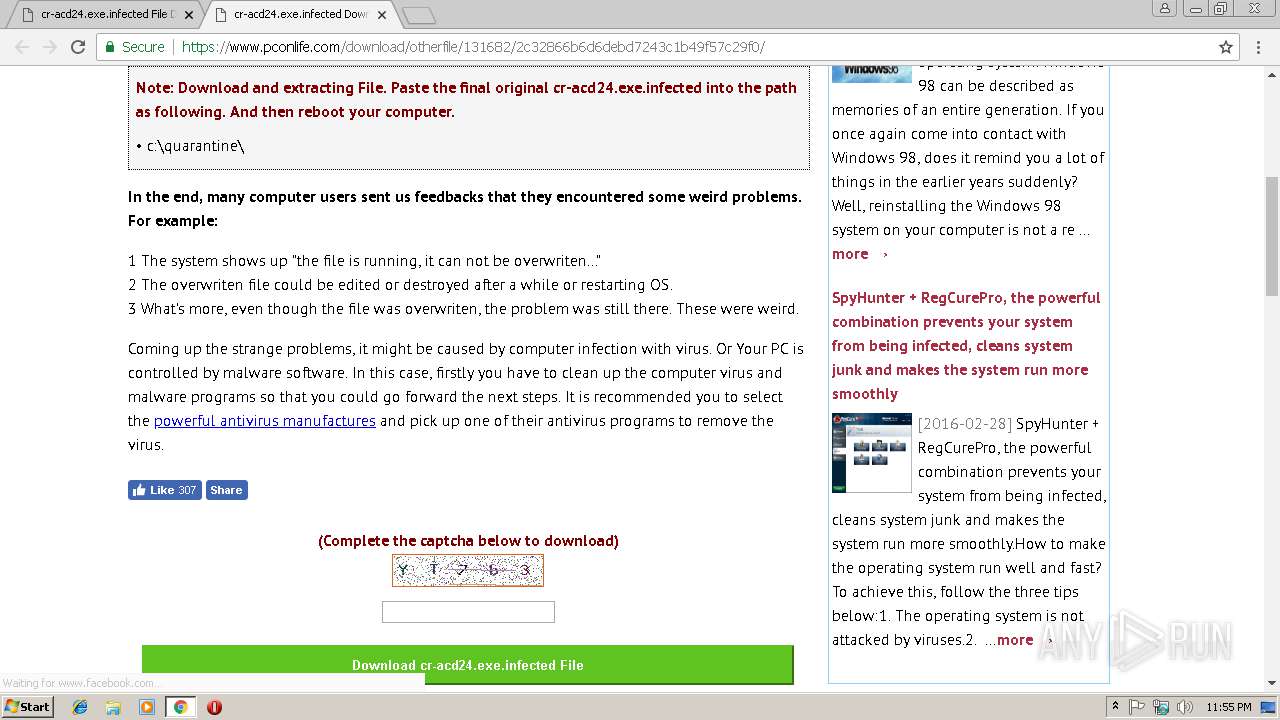
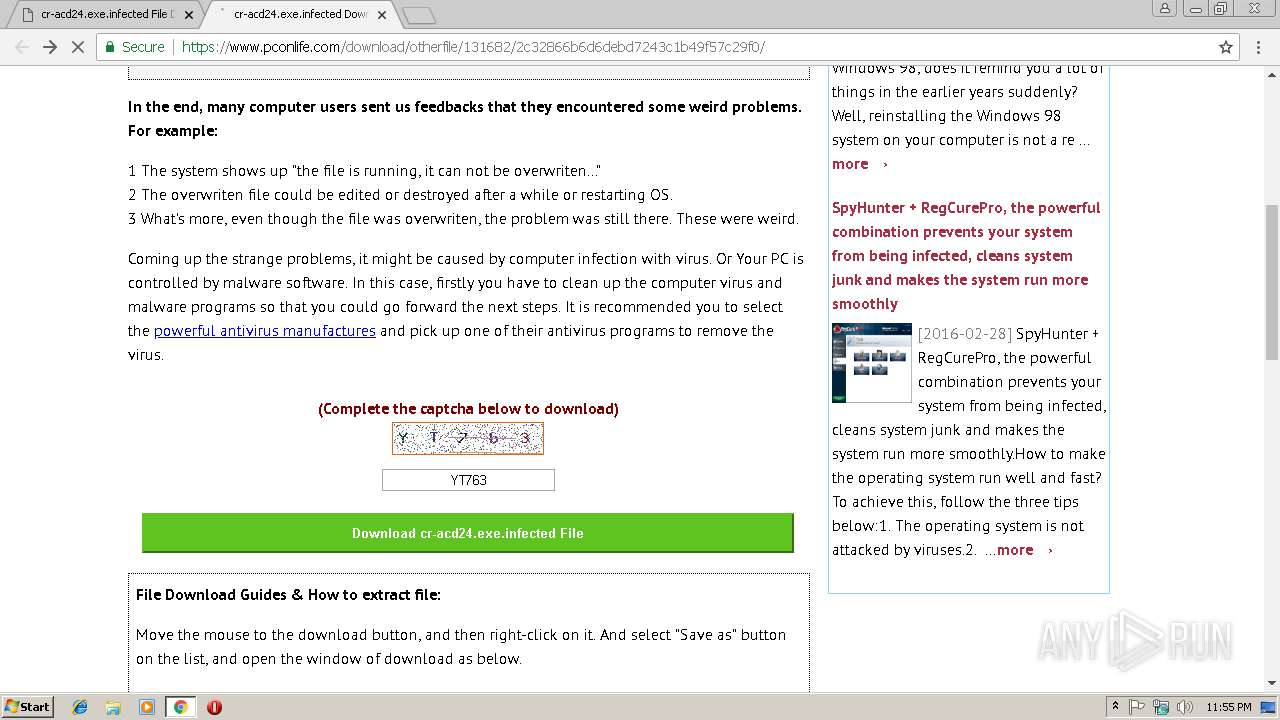
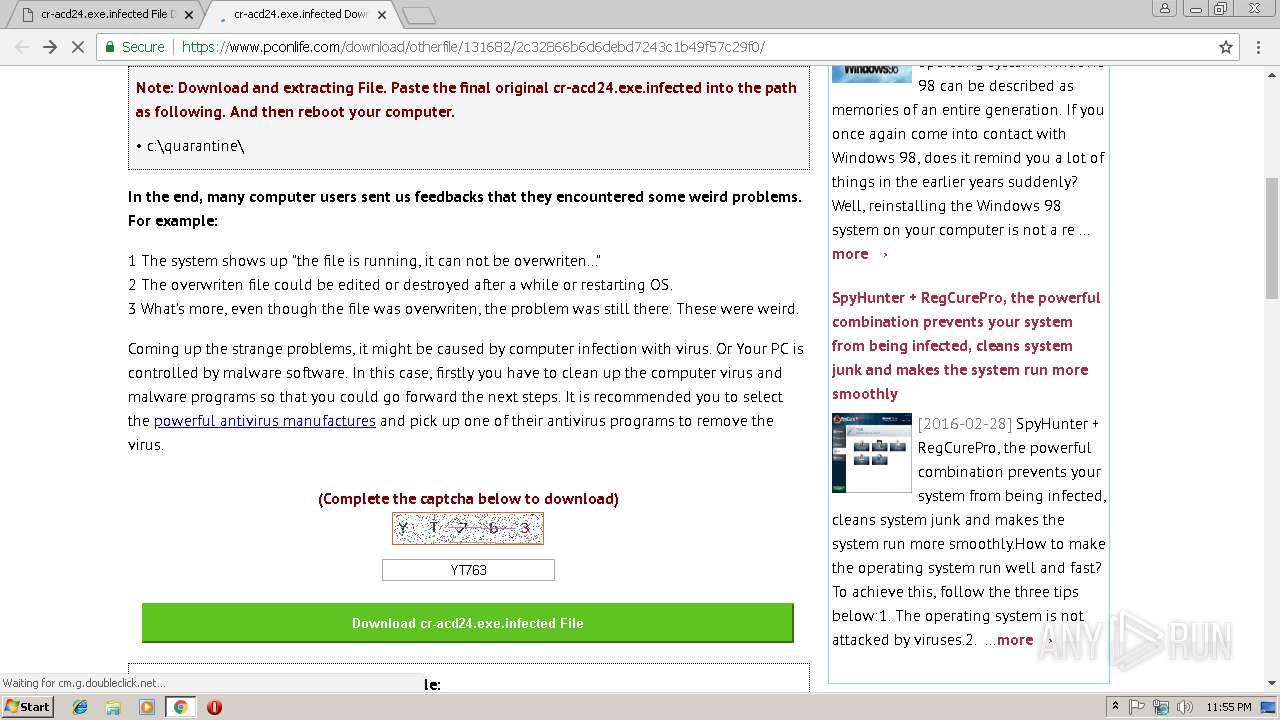
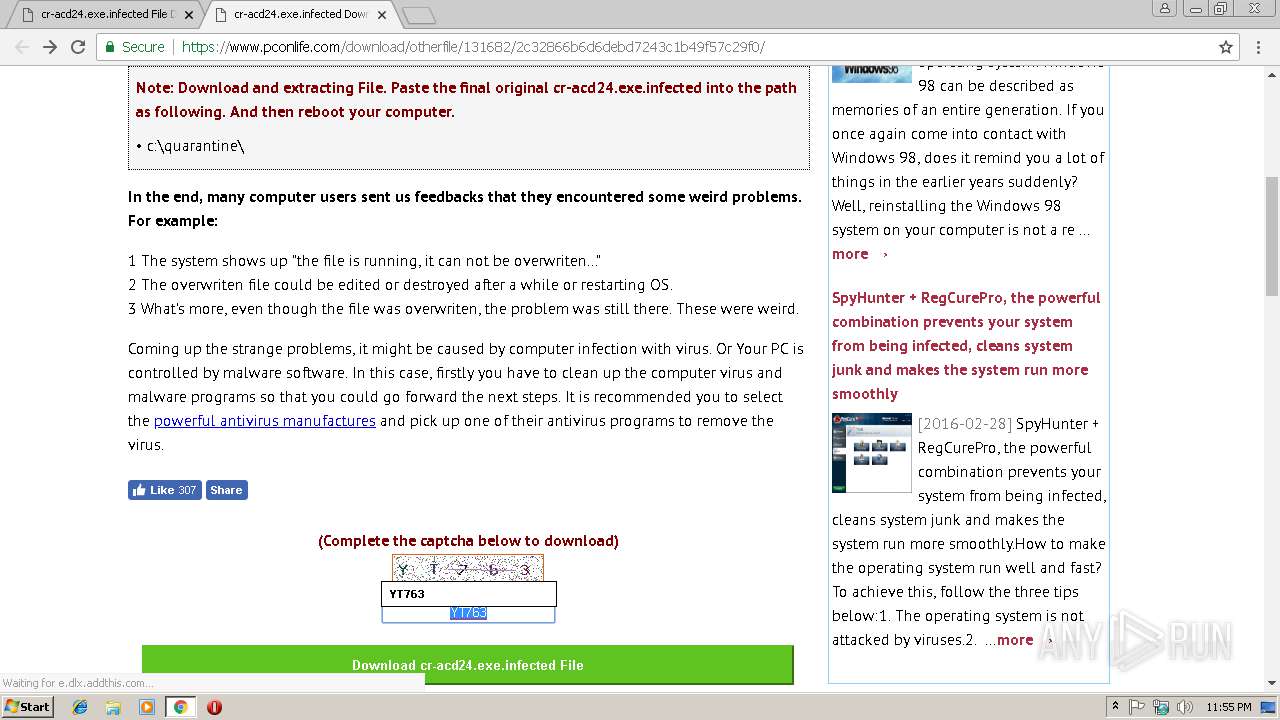
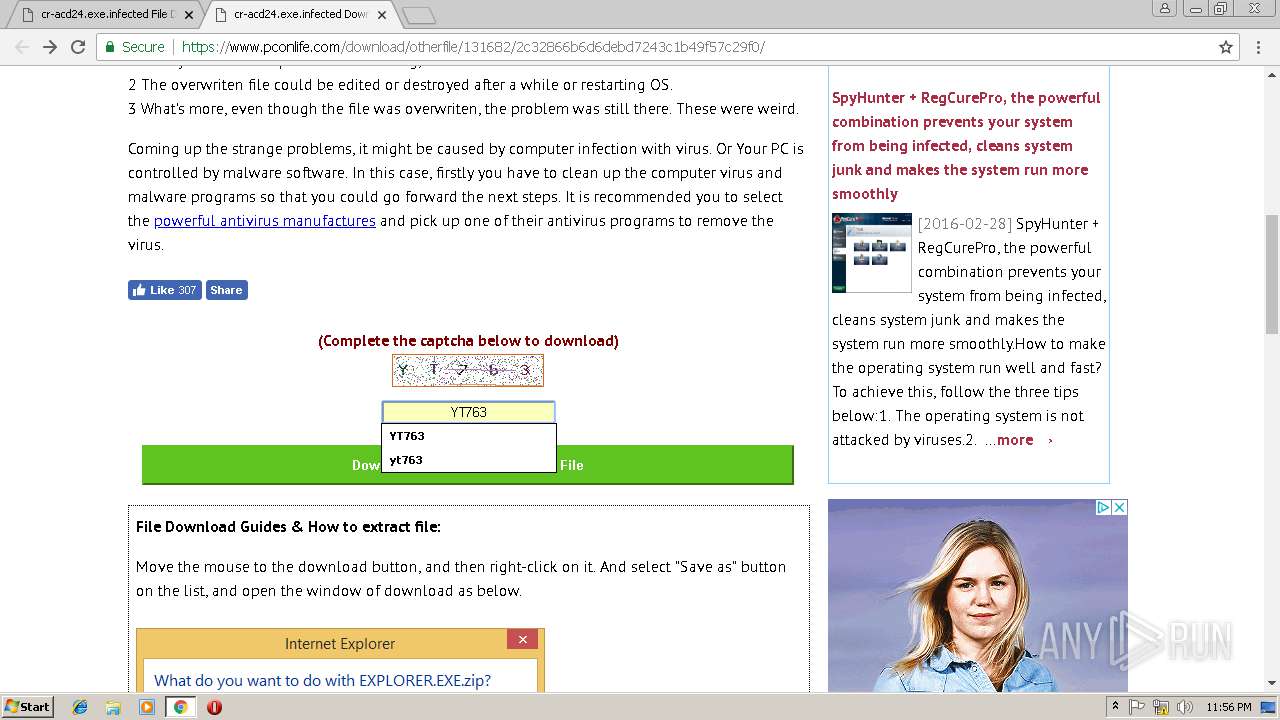
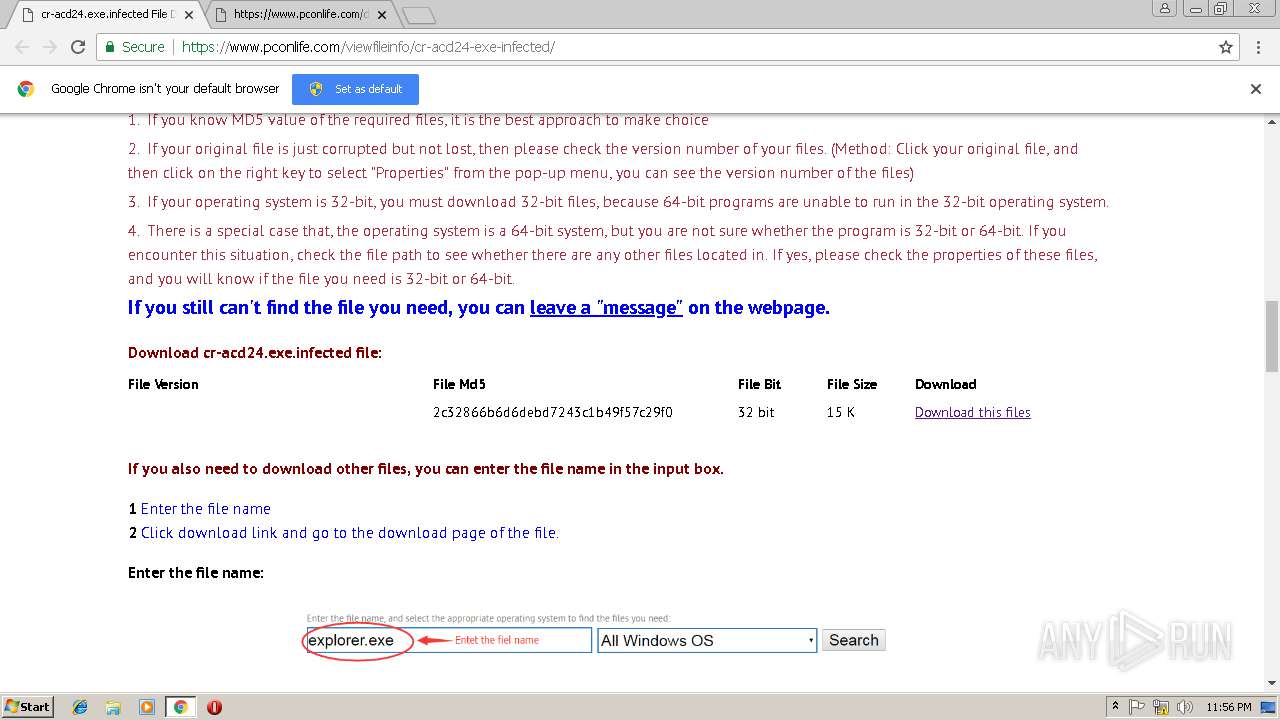
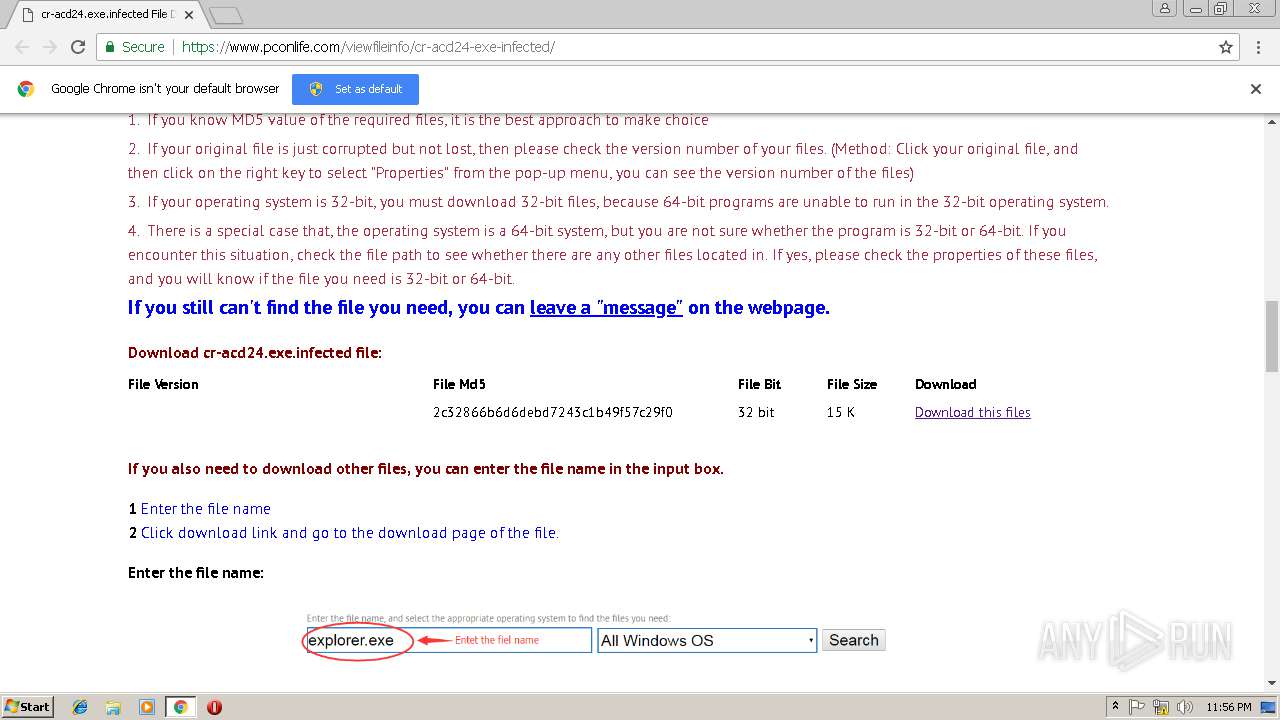
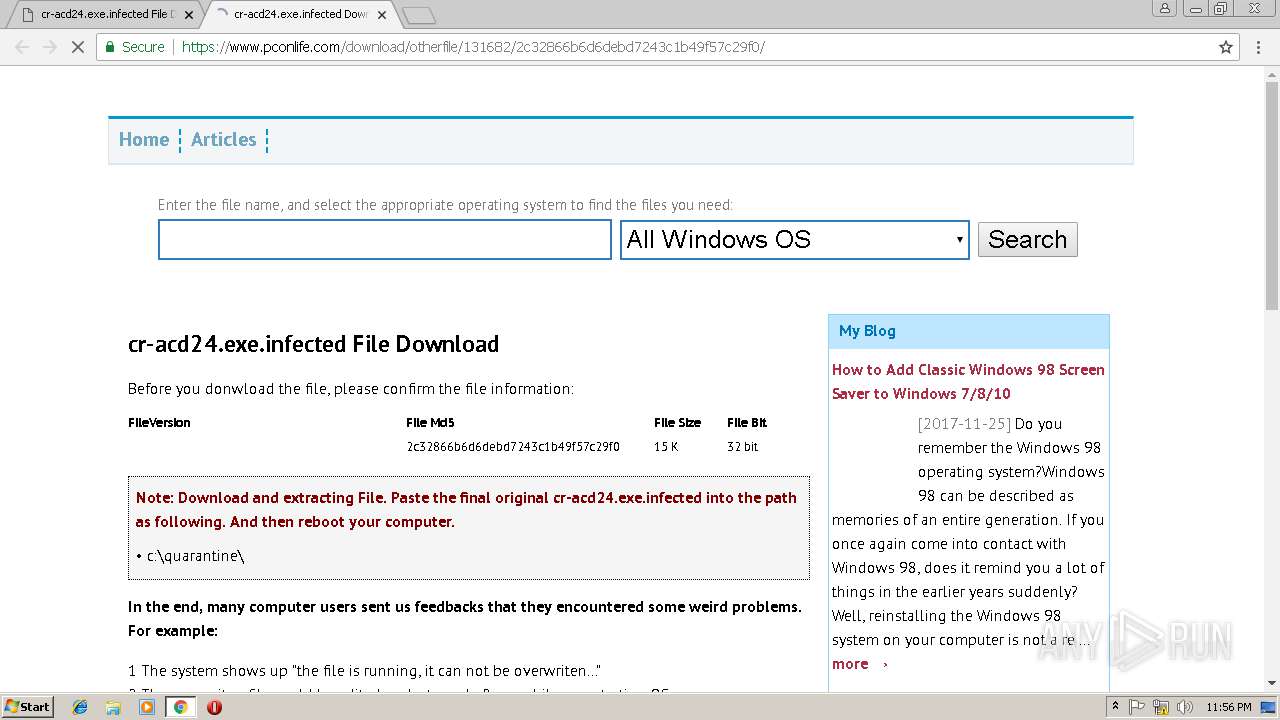
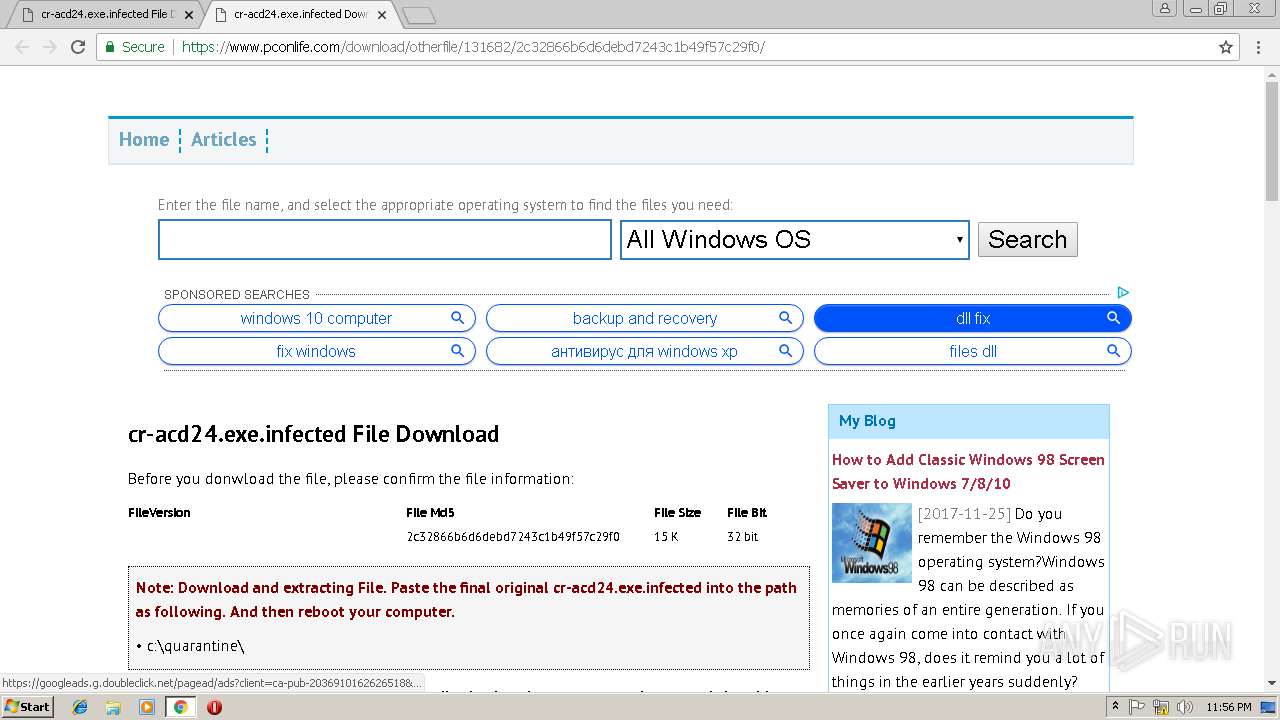
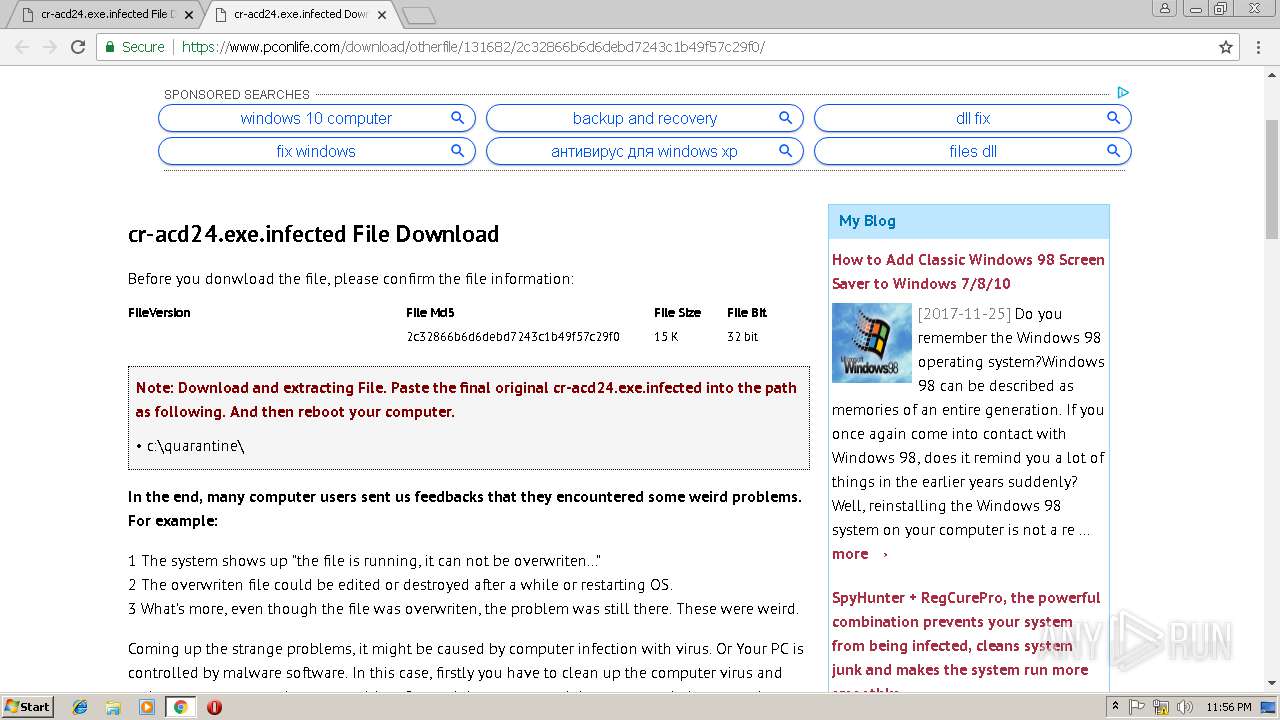
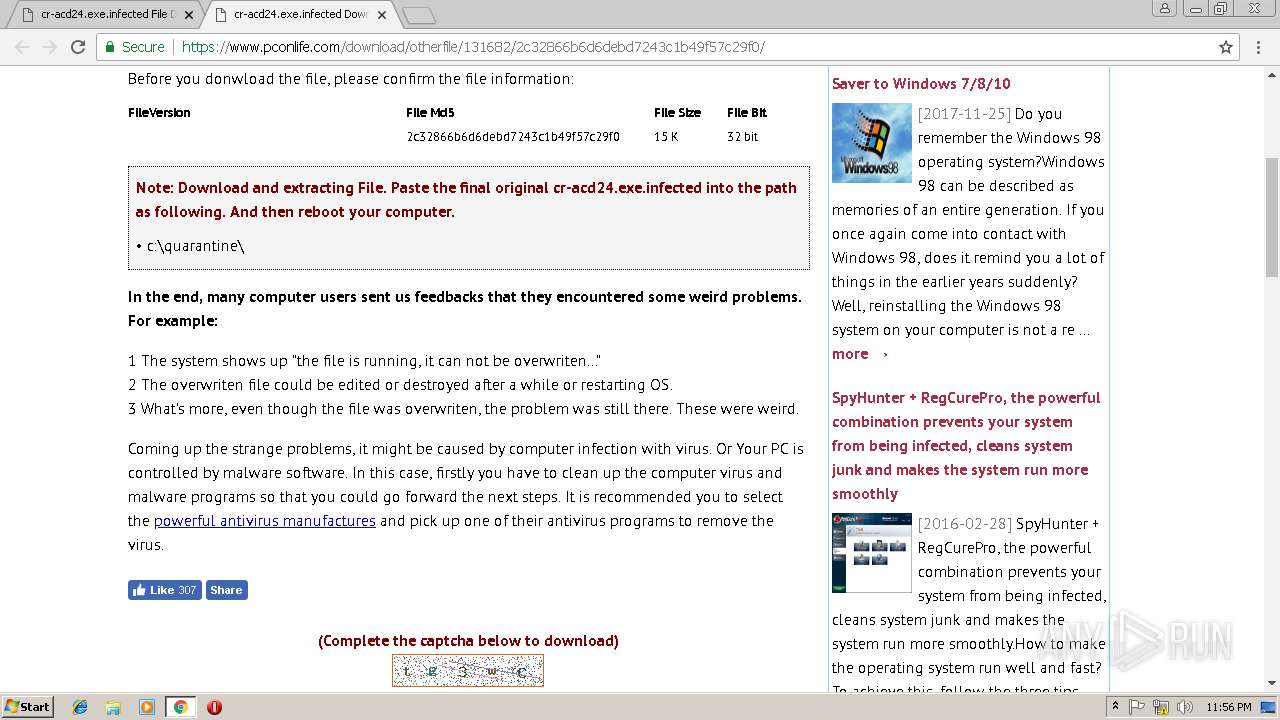
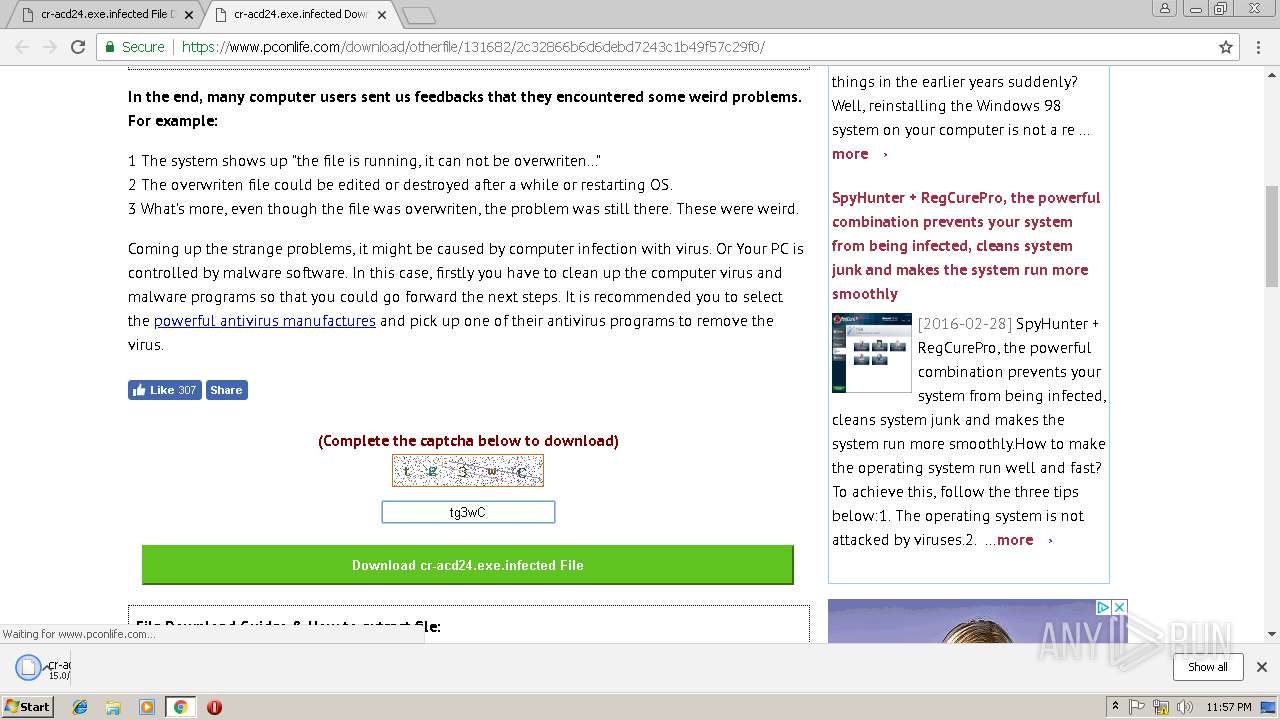
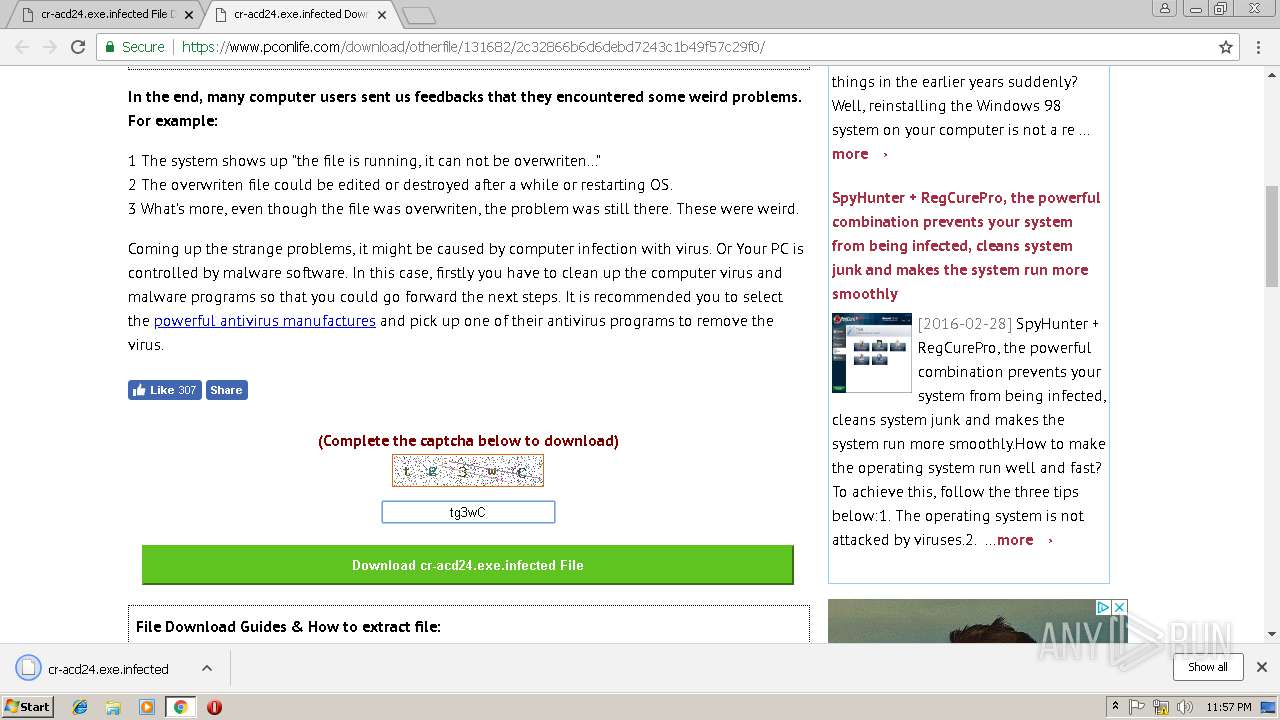
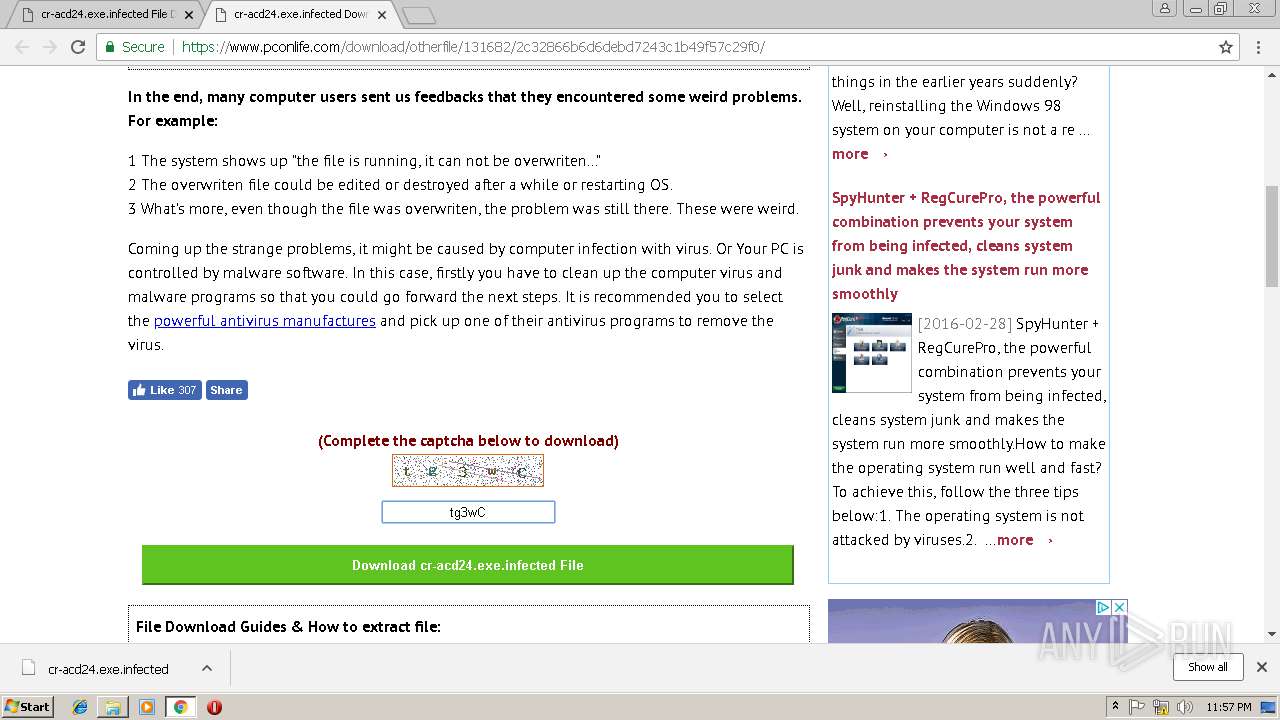
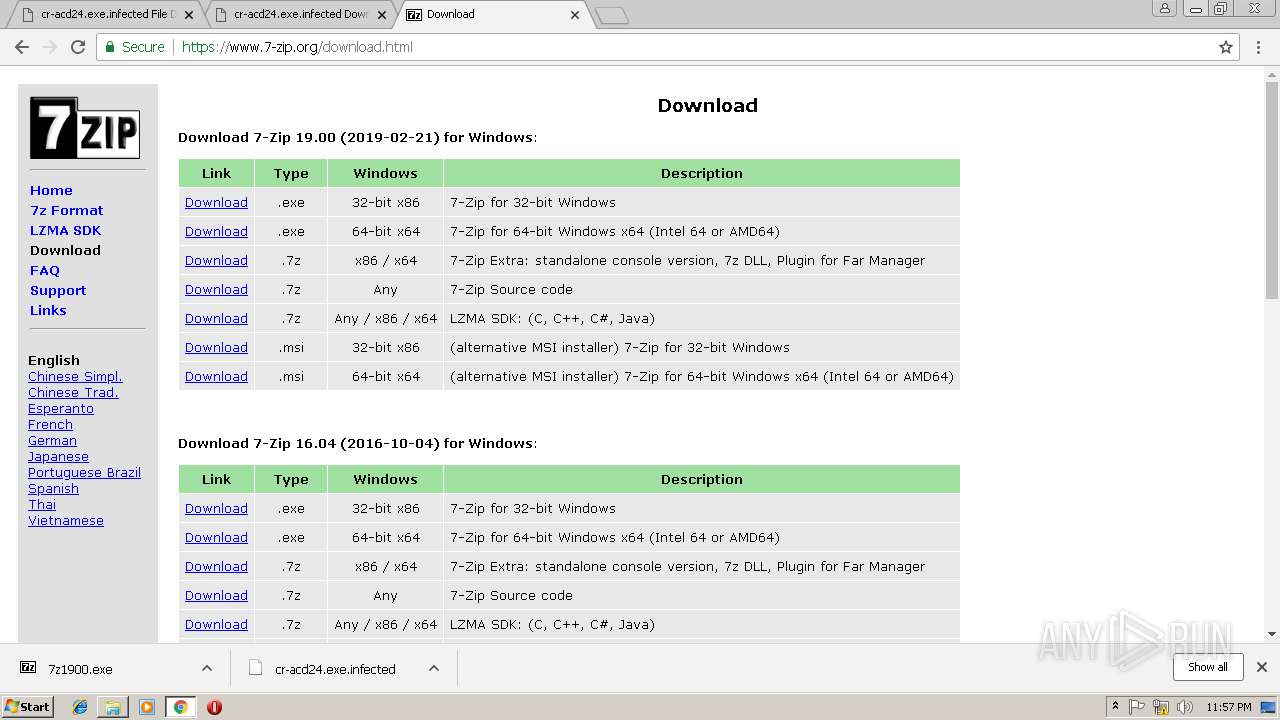
| URL: | https://www.pconlife.com/viewfileinfo/cr-acd24-exe-infected/ |
| Full analysis: | https://app.any.run/tasks/2e20316c-46cd-4024-be0f-62d1536e3026 |
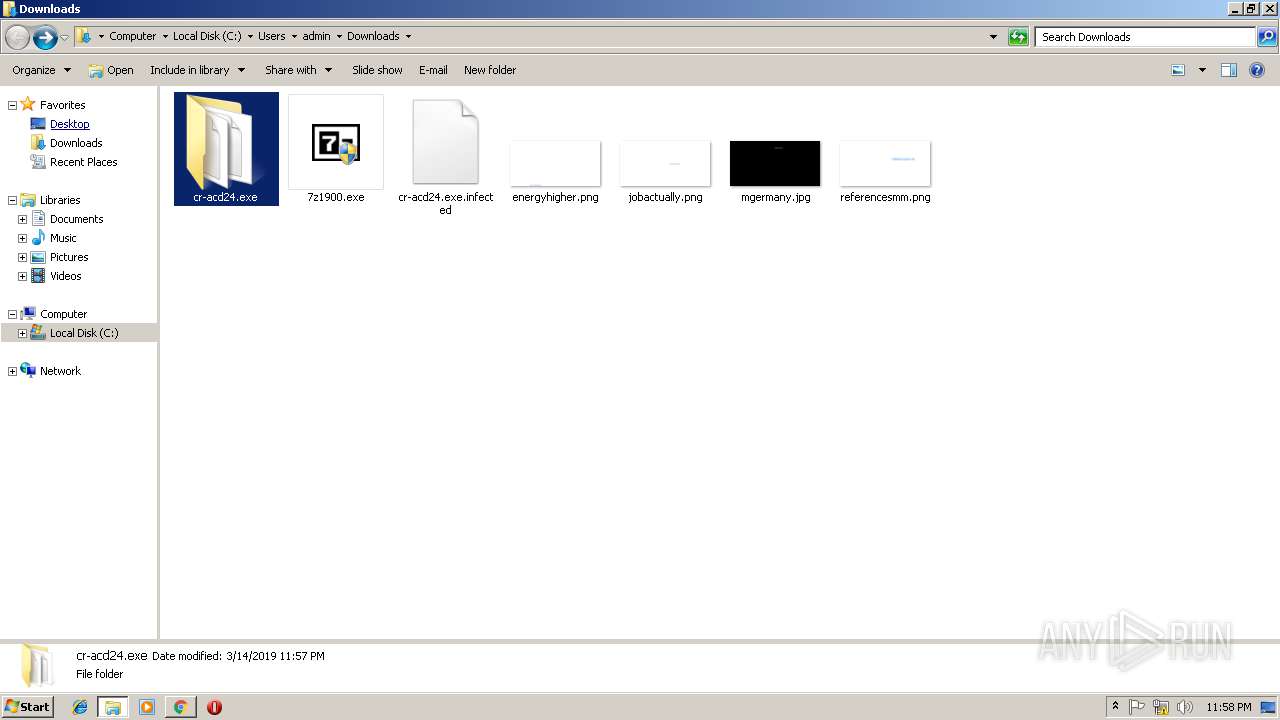
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 23:54:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A83B0B6DDAF1FC518A780034CD881401 |
| SHA1: | DCAF7D55B9B9C7ACD338194166700B90642AD6BF |
| SHA256: | 8884DE62CE474E9ED75B0F3EB75698D3EFBE4155839A78CFFA39E6D63CEAA05E |
| SSDEEP: | 3:N8DSLhDLGKjK9KWKhBB94wGD:2OLhW9ENhB/4ws |
MALICIOUS
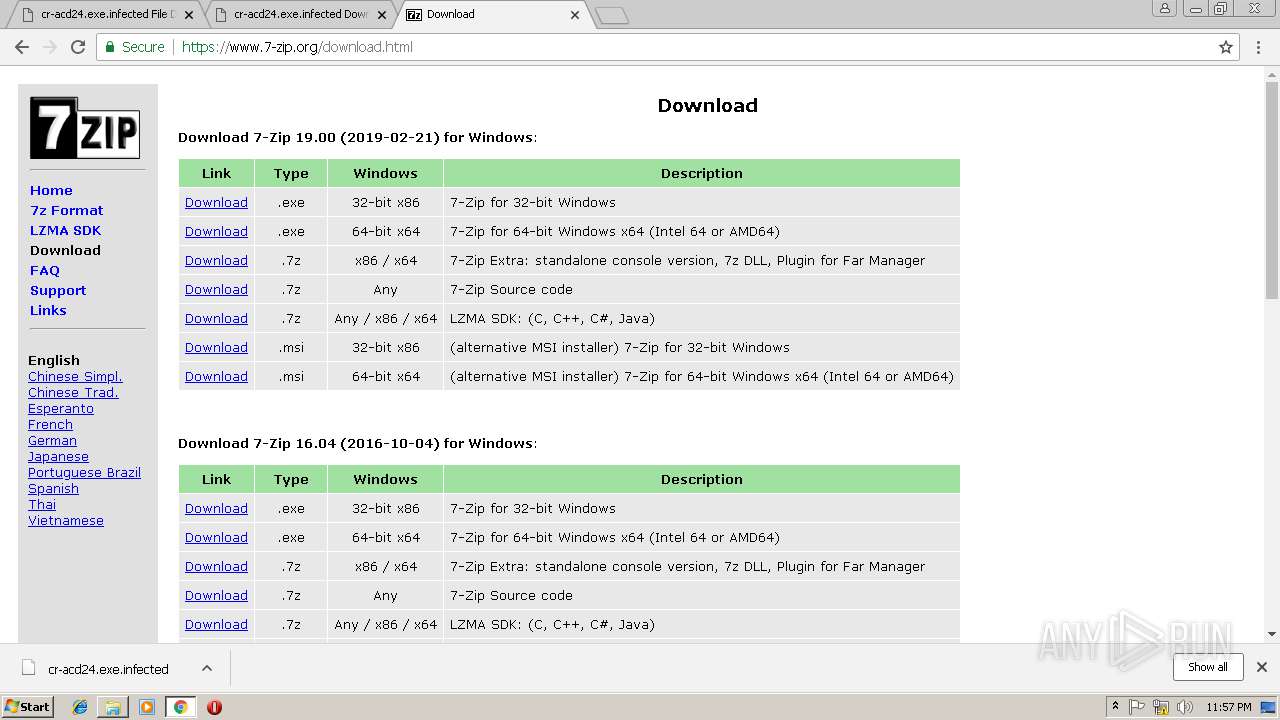
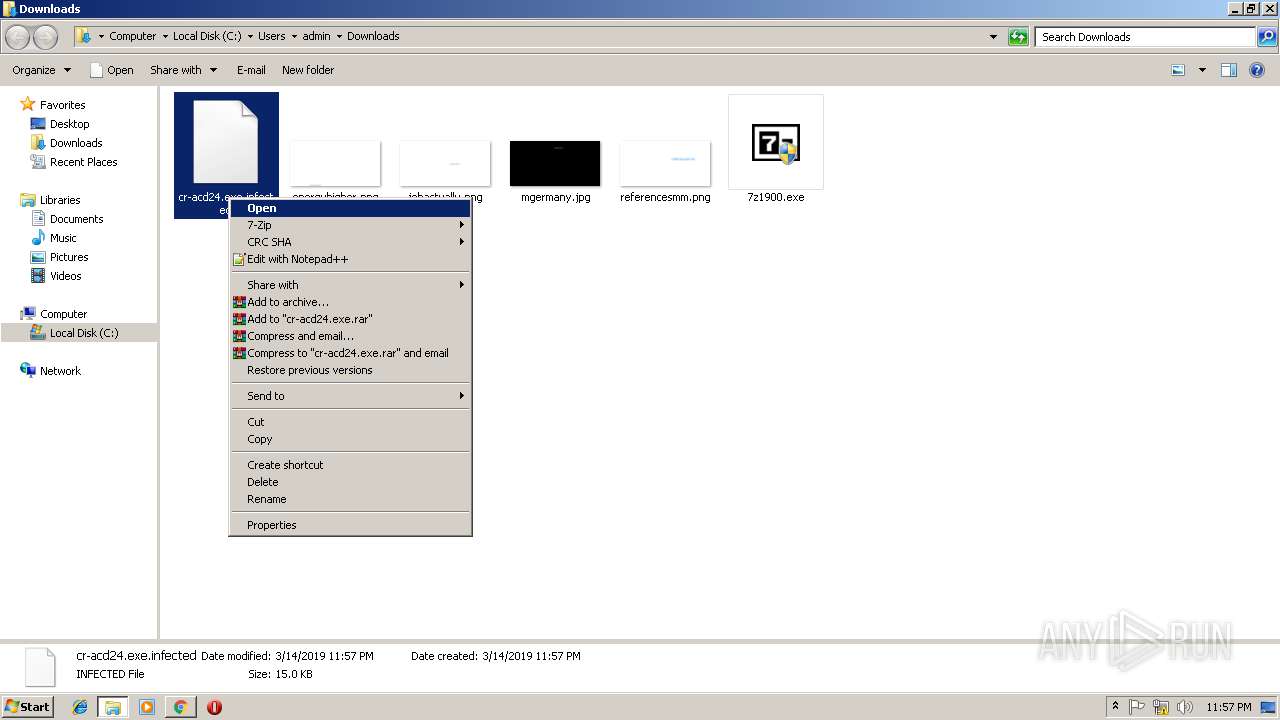
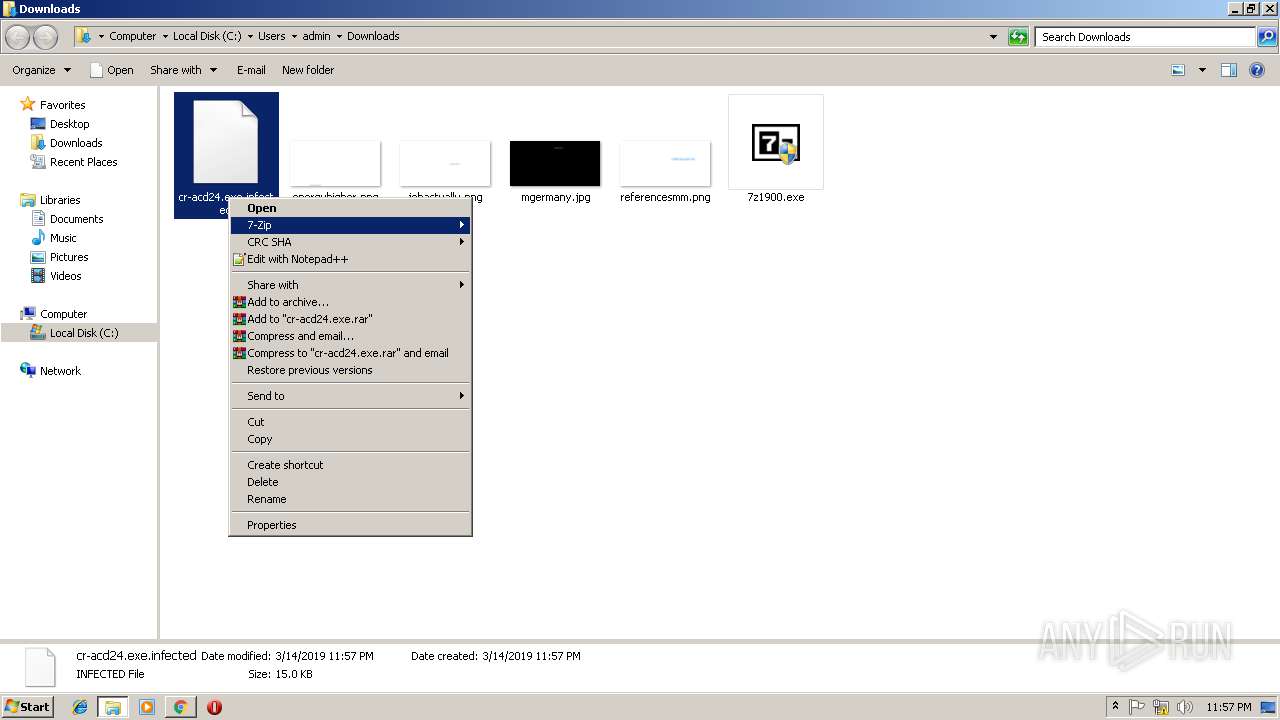
Application was dropped or rewritten from another process
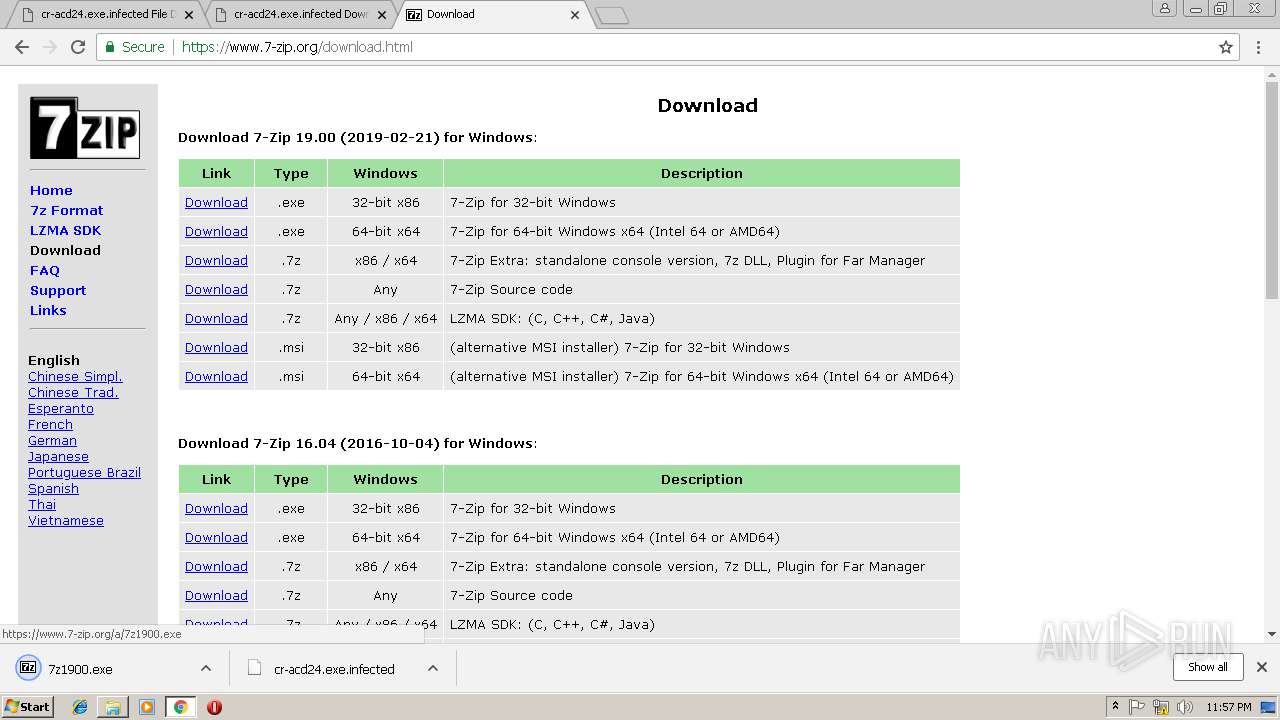
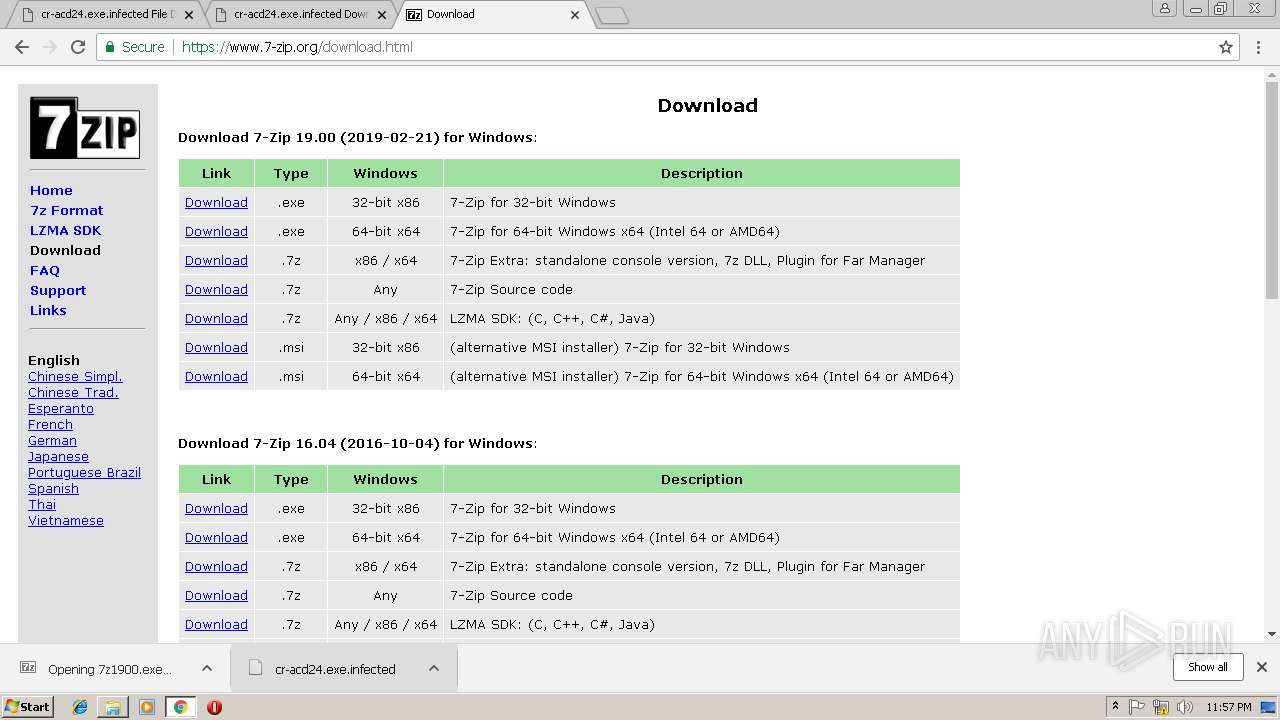
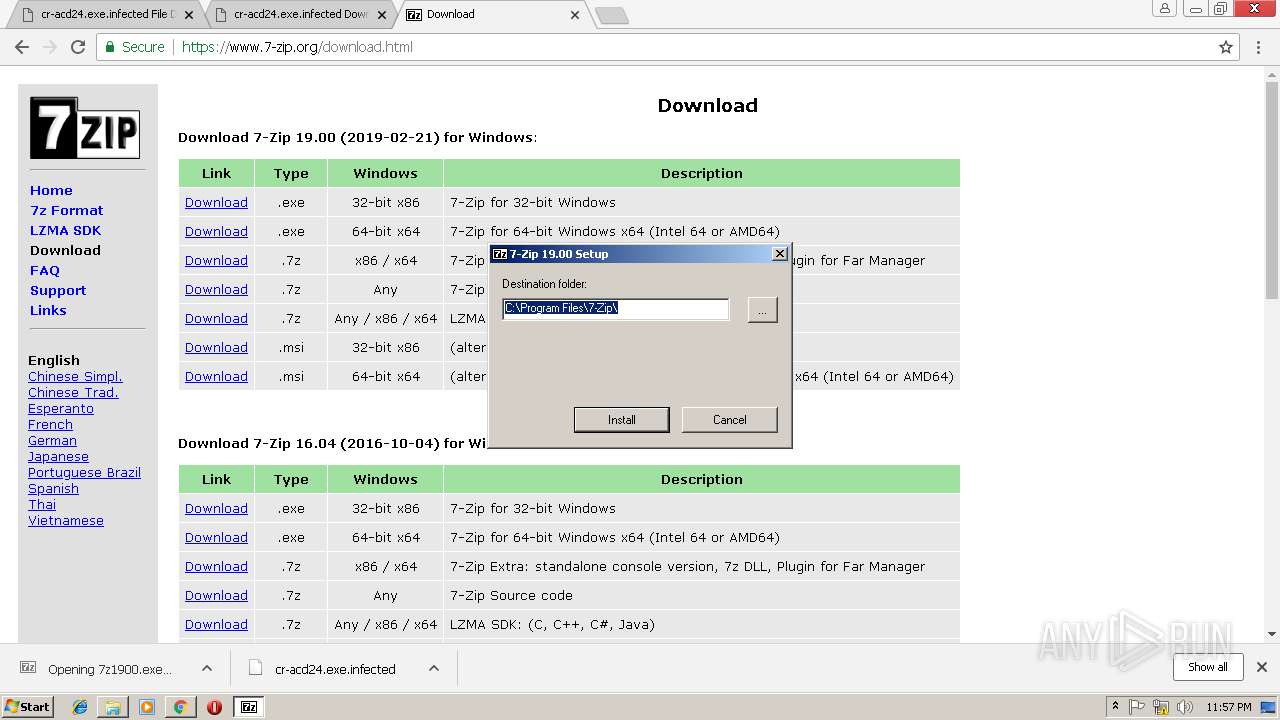
- 7z1900.exe (PID: 2456)
- 7zG.exe (PID: 1904)
- 7z1900.exe (PID: 2988)
Loads dropped or rewritten executable
- explorer.exe (PID: 284)
- 7zG.exe (PID: 1904)
- svchost.exe (PID: 848)
SUSPICIOUS
Executable content was dropped or overwritten
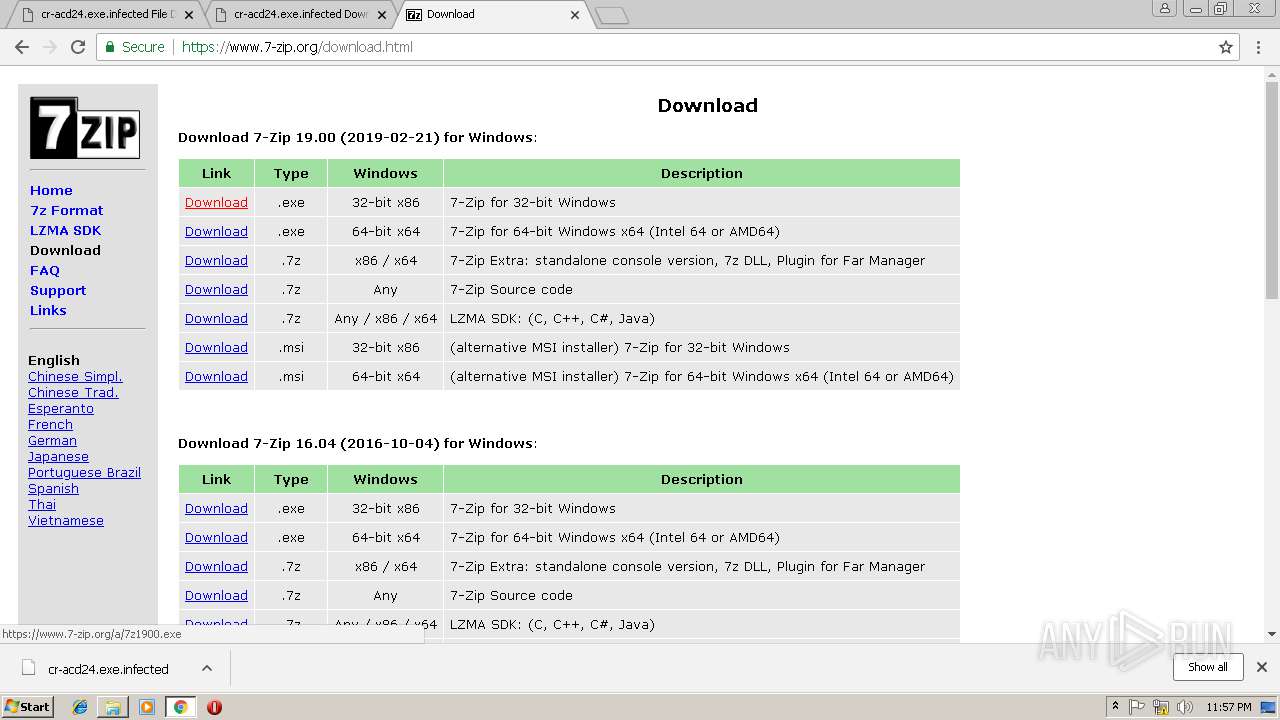
- 7z1900.exe (PID: 2456)
- chrome.exe (PID: 3012)
Creates COM task schedule object
- 7z1900.exe (PID: 2456)
Creates a software uninstall entry
- 7z1900.exe (PID: 2456)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 284)
Creates files in the user directory
- explorer.exe (PID: 284)
Creates files in the program directory
- 7z1900.exe (PID: 2456)
INFO
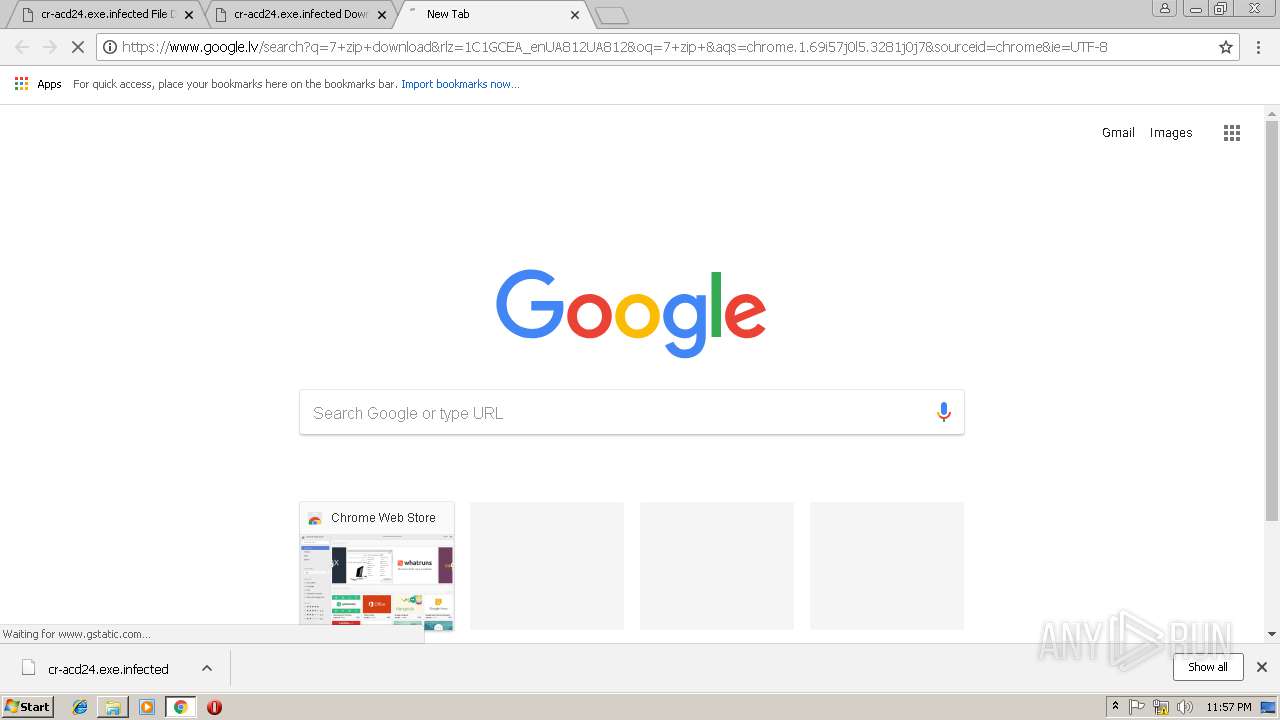
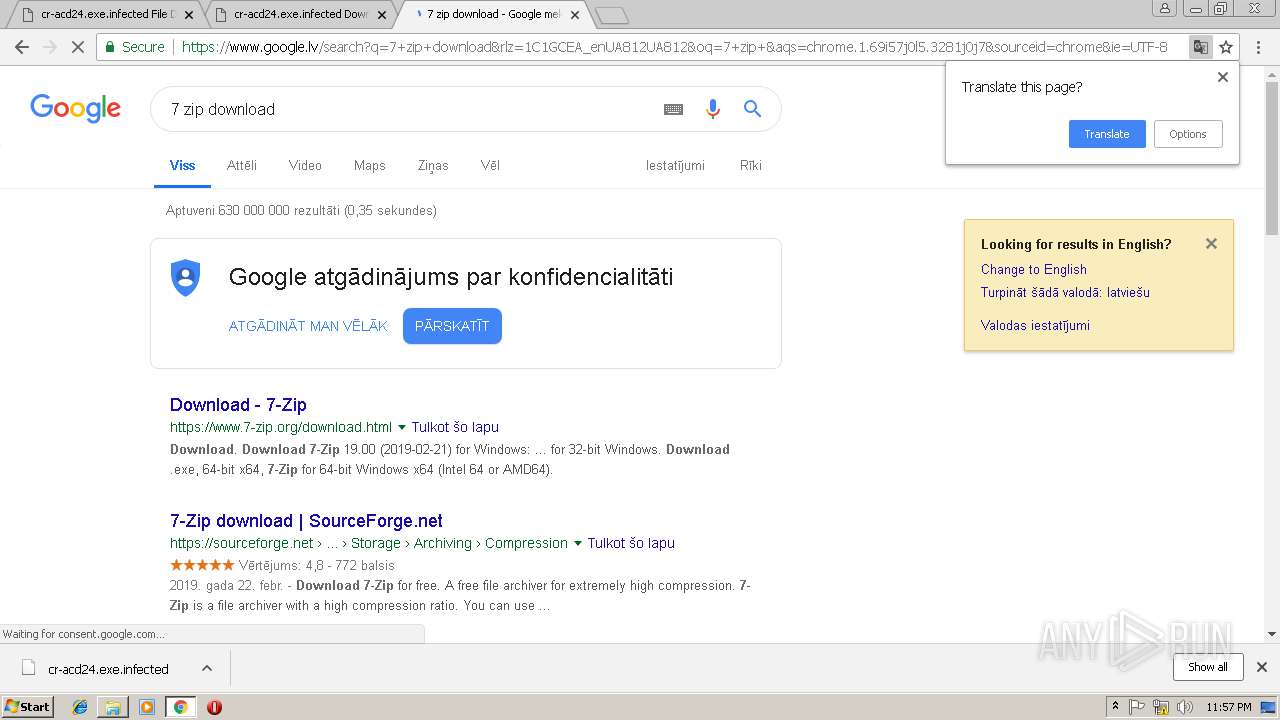
Application launched itself
- chrome.exe (PID: 3012)
Reads Internet Cache Settings
- chrome.exe (PID: 3012)
Dropped object may contain TOR URL's
- chrome.exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
24
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=1DF6CE24415C0D47DBDC682FF8E09CC1 --mojo-platform-channel-handle=924 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 848 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
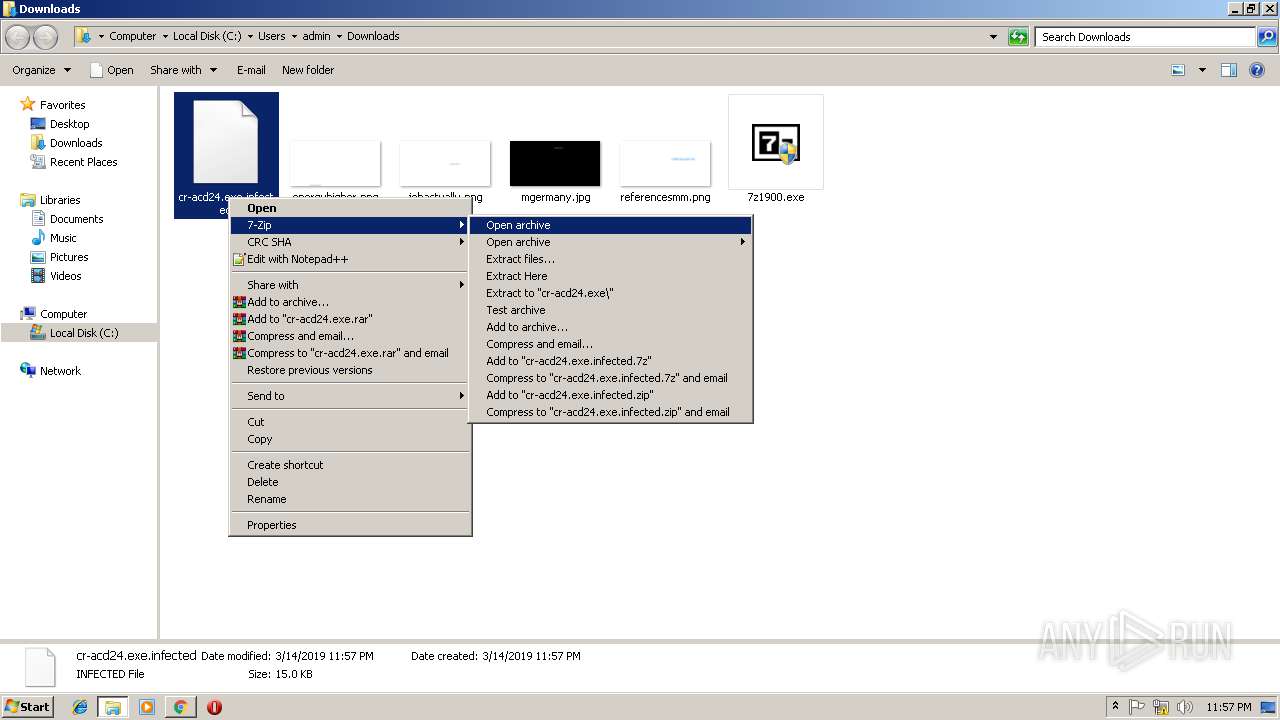
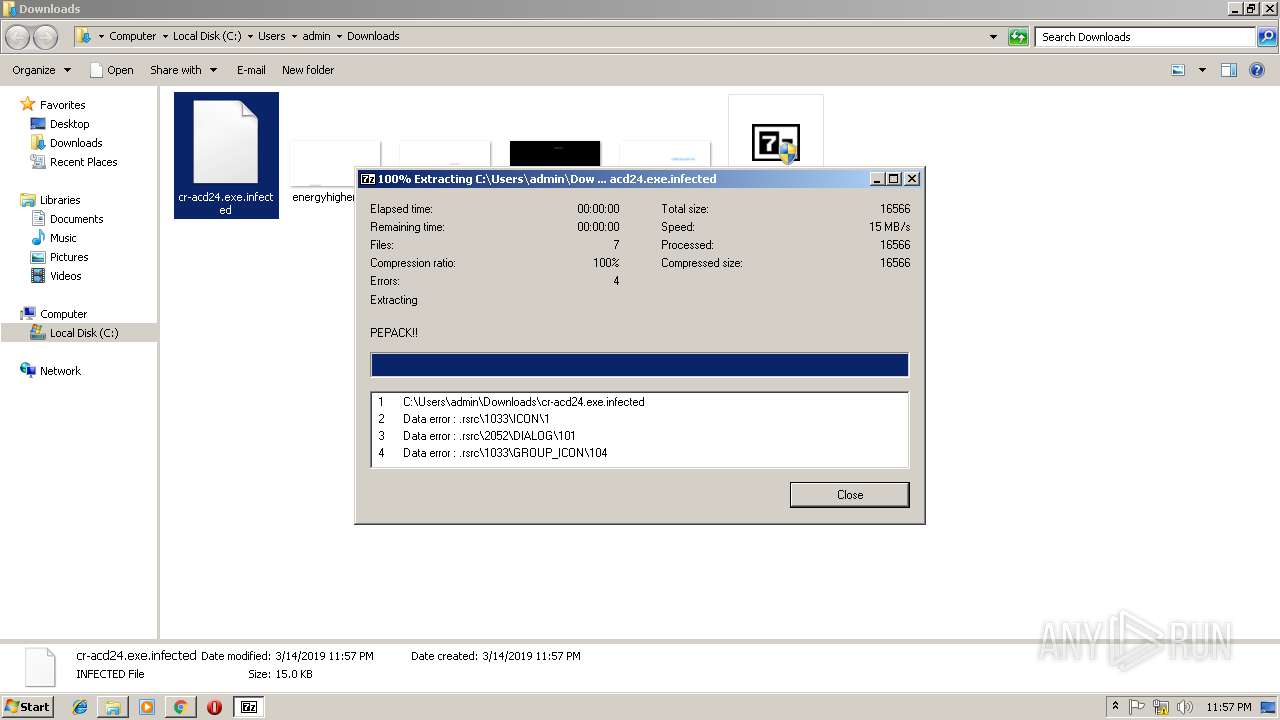
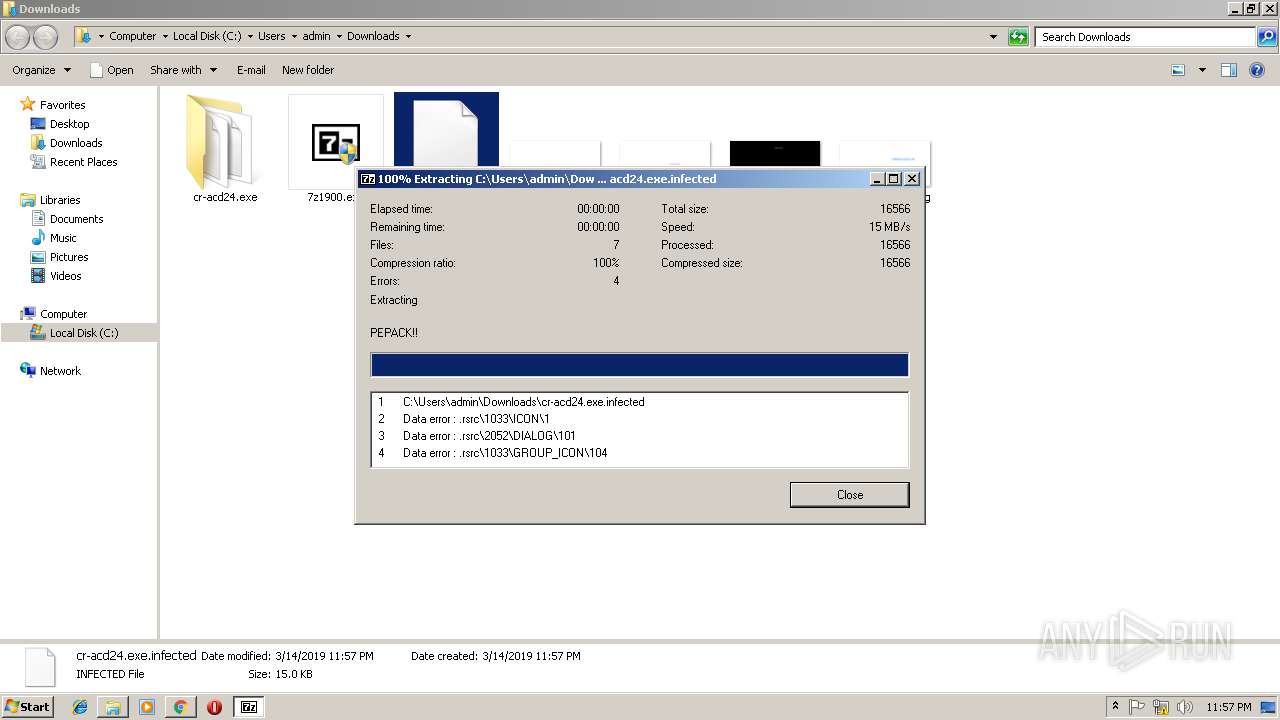
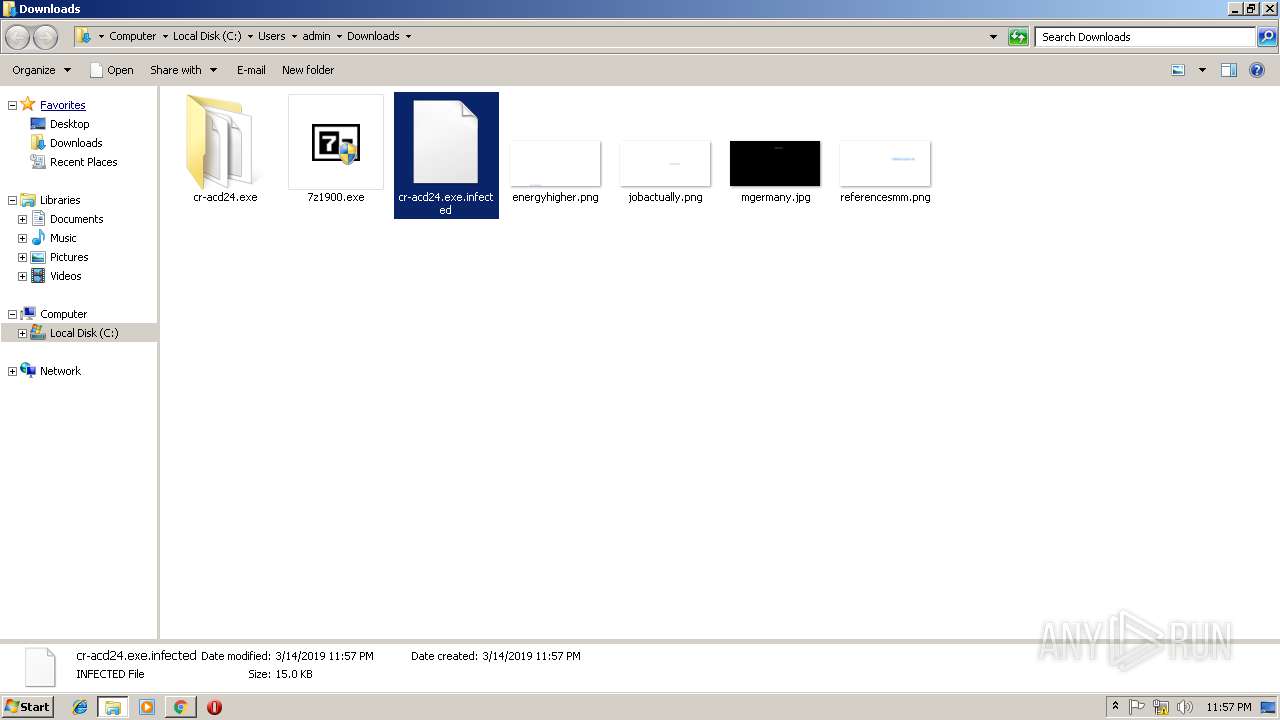
| 1904 | "C:\Program Files\7-Zip\7zG.exe" x -o"C:\Users\admin\Downloads\cr-acd24.exe\" -spe -an -ai#7zMap1117:96:7zEvent7302 | C:\Program Files\7-Zip\7zG.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip GUI Exit code: 2 Version: 19.00 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1ED39E316BBE5F45316BEDDA2EF54E3F --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
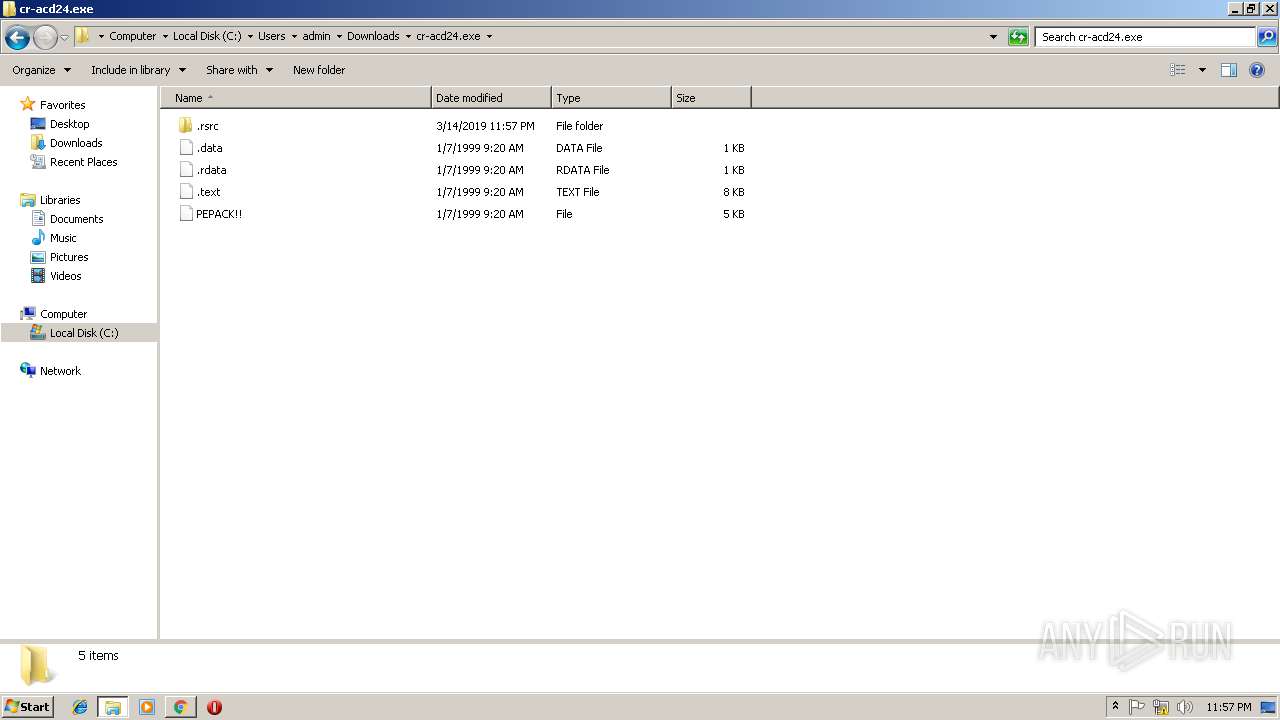
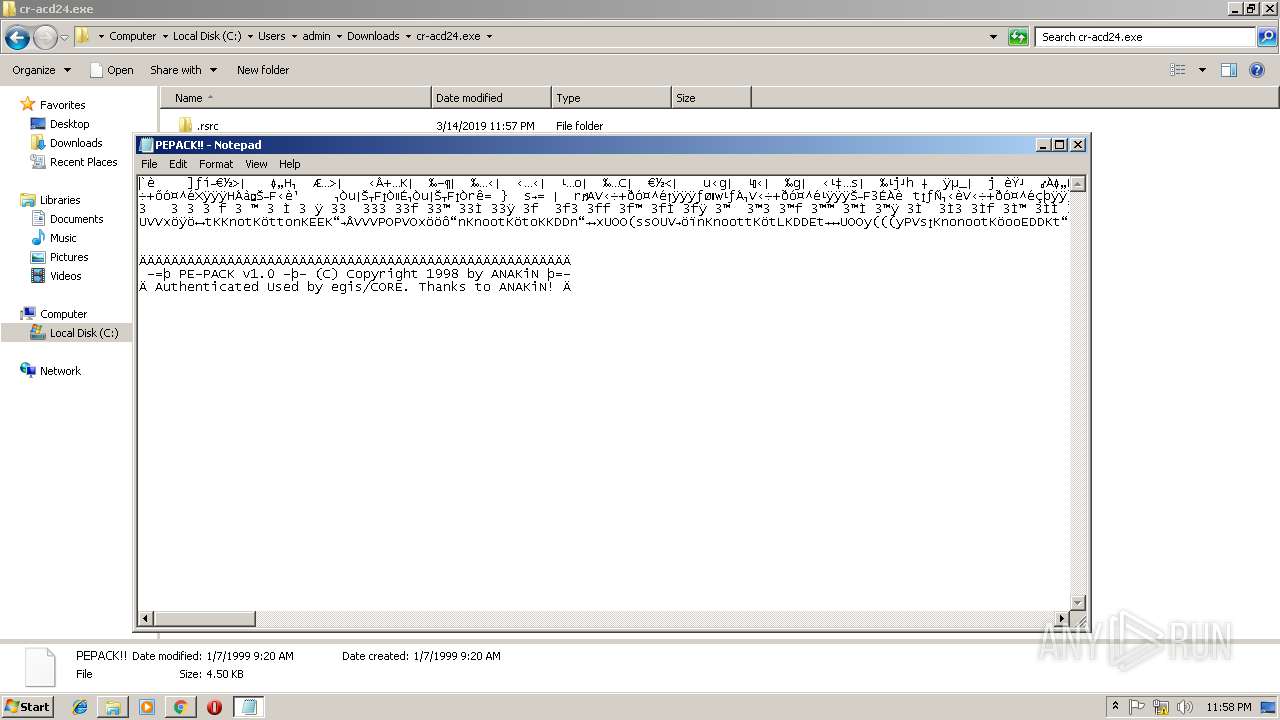
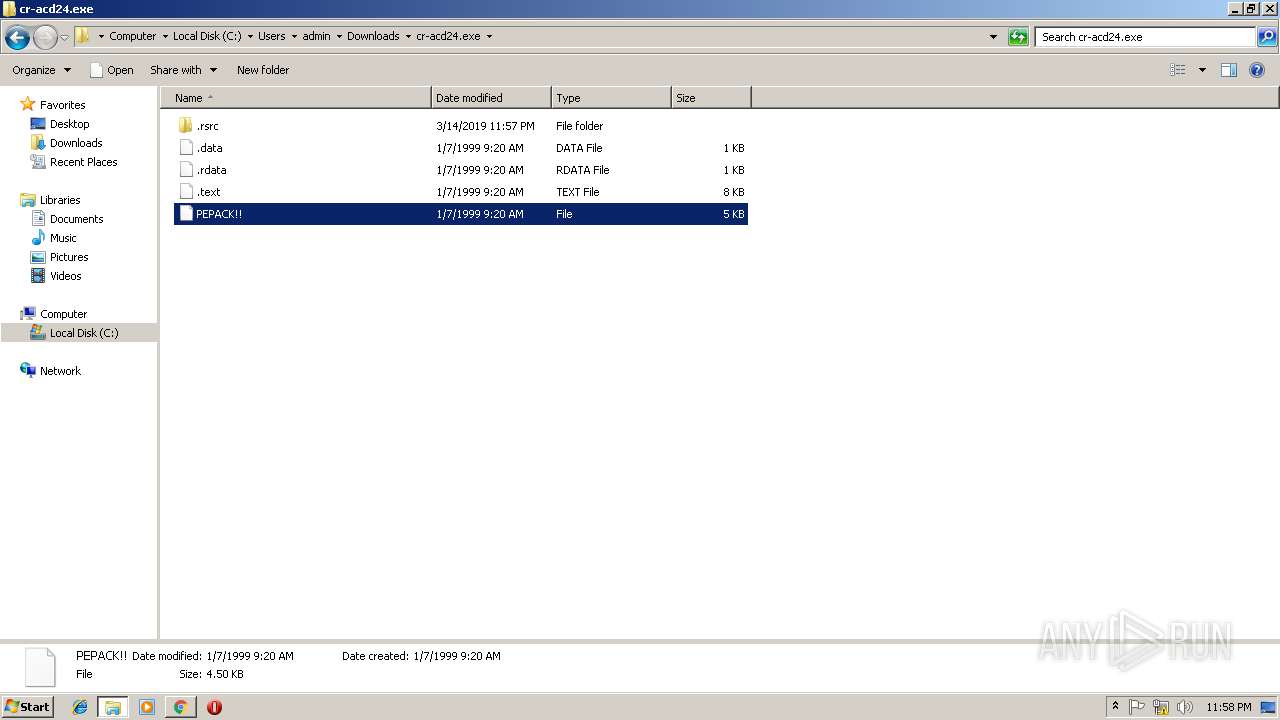
| 2108 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\cr-acd24.exe\PEPACK!! | C:\Windows\system32\NOTEPAD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=2D4FB5FDE2F0E05394D9C218E08B9903 --mojo-platform-channel-handle=4040 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\Downloads\7z1900.exe" | C:\Users\admin\Downloads\7z1900.exe | chrome.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5026F2F78FE1943B6F9551ABAE22CB99 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5026F2F78FE1943B6F9551ABAE22CB99 --renderer-client-id=11 --mojo-platform-channel-handle=4468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=98ADCE4DA78D20D5459DD02CC04A3B6A --mojo-platform-channel-handle=2460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
4 571
Read events
3 874
Write events
690
Delete events
7
Modification events
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3012-13197081314215500 |
Value: 259 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3012-13197081314215500 |
Value: 259 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
11
Suspicious files
92
Text files
225
Unknown types
10
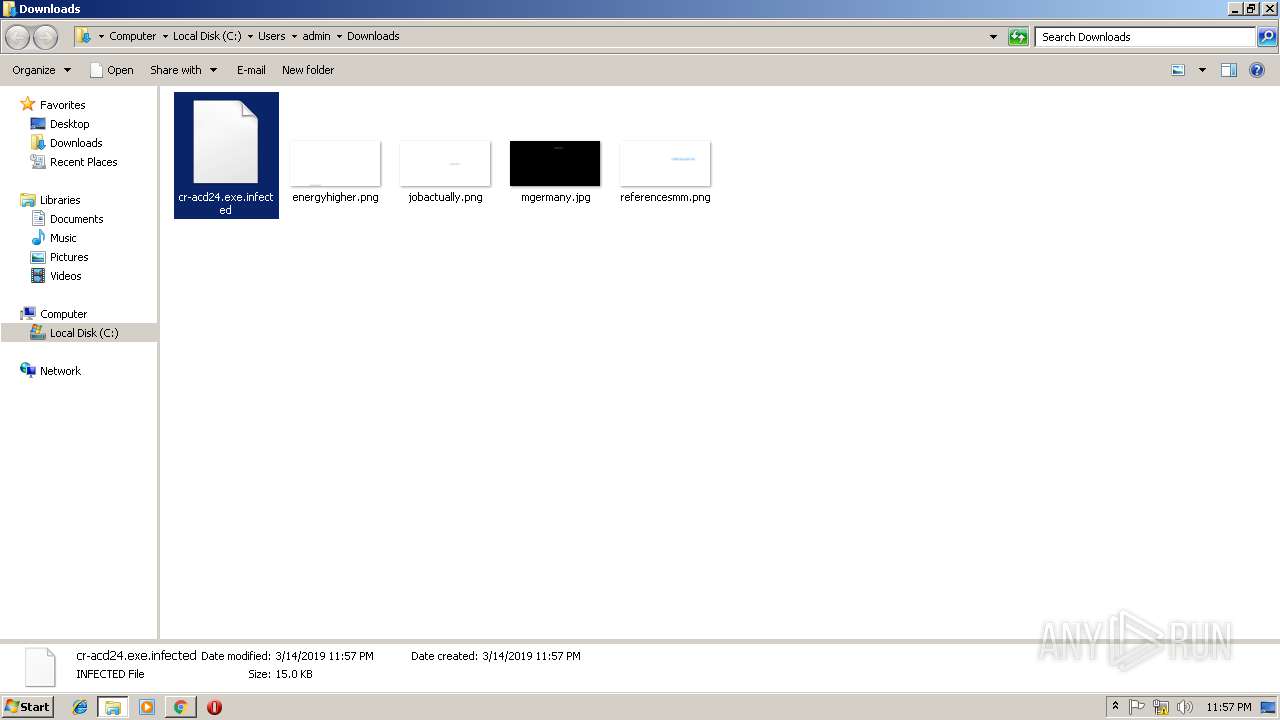
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dcfd86b2-7e45-4f66-a515-ff00ad73e7e1.tmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fe3a2ca9-f3a7-46f6-be81-b70161ab3abc.tmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF1ae010.TMP | text | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1ae001.TMP | text | |
MD5:— | SHA256:— | |||
| 848 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
70
DNS requests
44
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
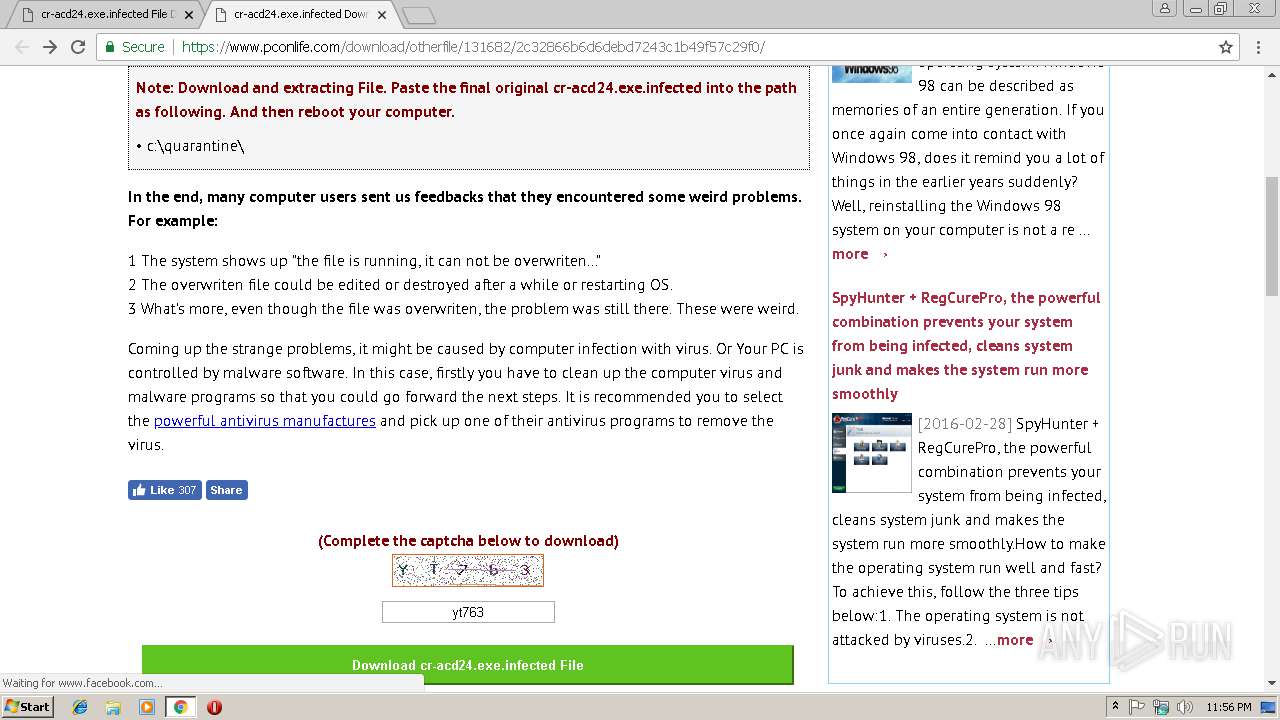
3012 | chrome.exe | 157.240.1.23:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
3012 | chrome.exe | 216.58.205.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 45.63.48.32:443 | www.pconlife.com | Choopa, LLC | US | unknown |
3012 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3012 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 216.58.208.34:443 | adservice.google.lv | Google Inc. | US | whitelisted |
3012 | chrome.exe | 172.217.16.130:443 | adservice.google.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 172.217.18.98:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.pconlife.com |
| unknown |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
apis.google.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
platform.twitter.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3012 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |