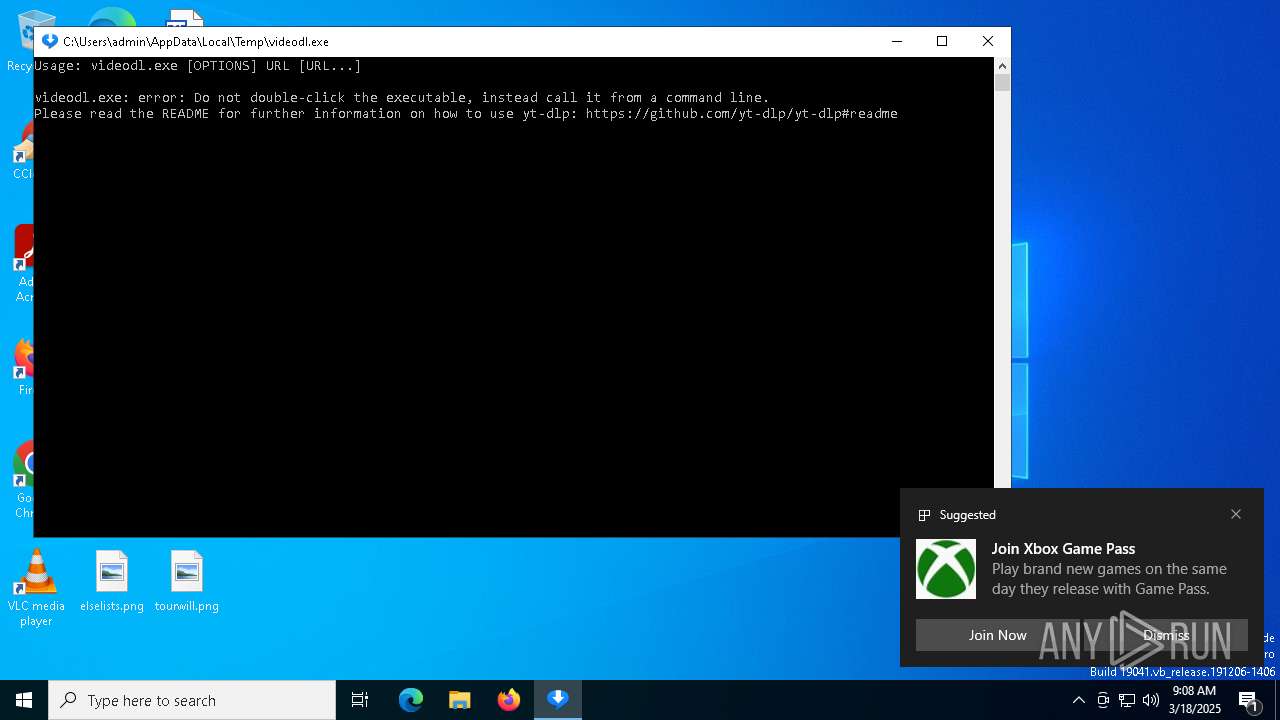
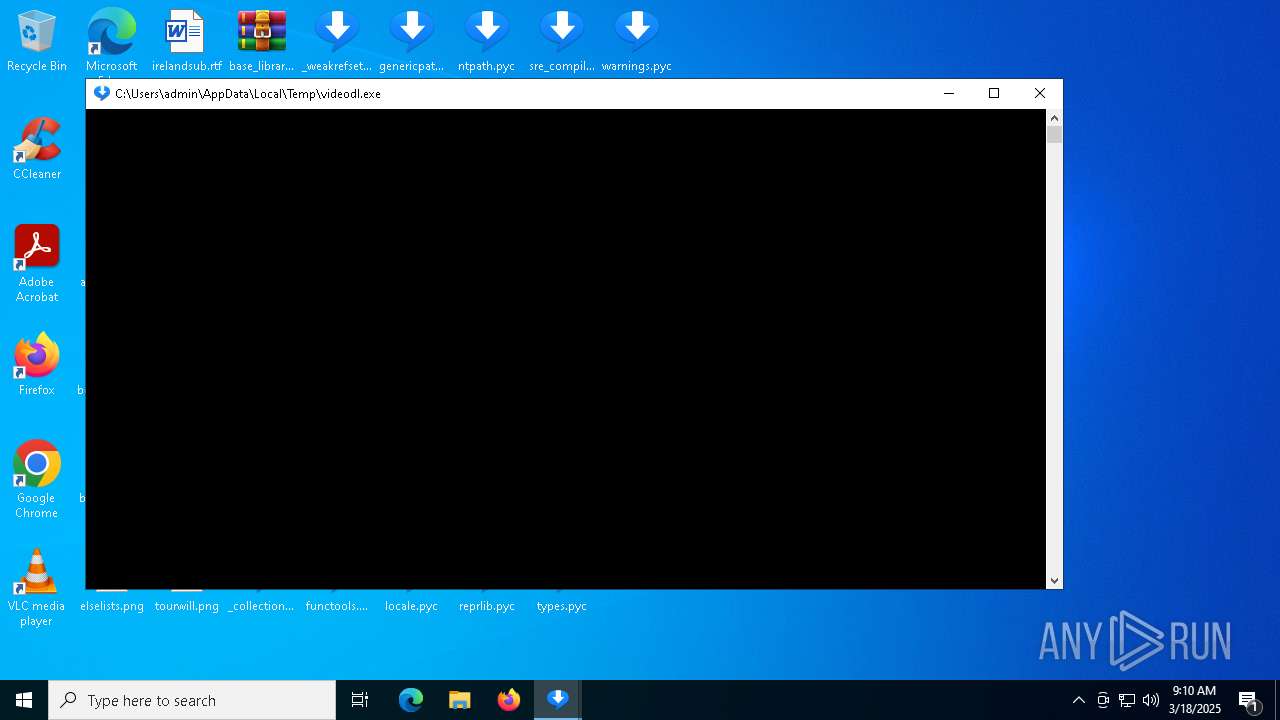
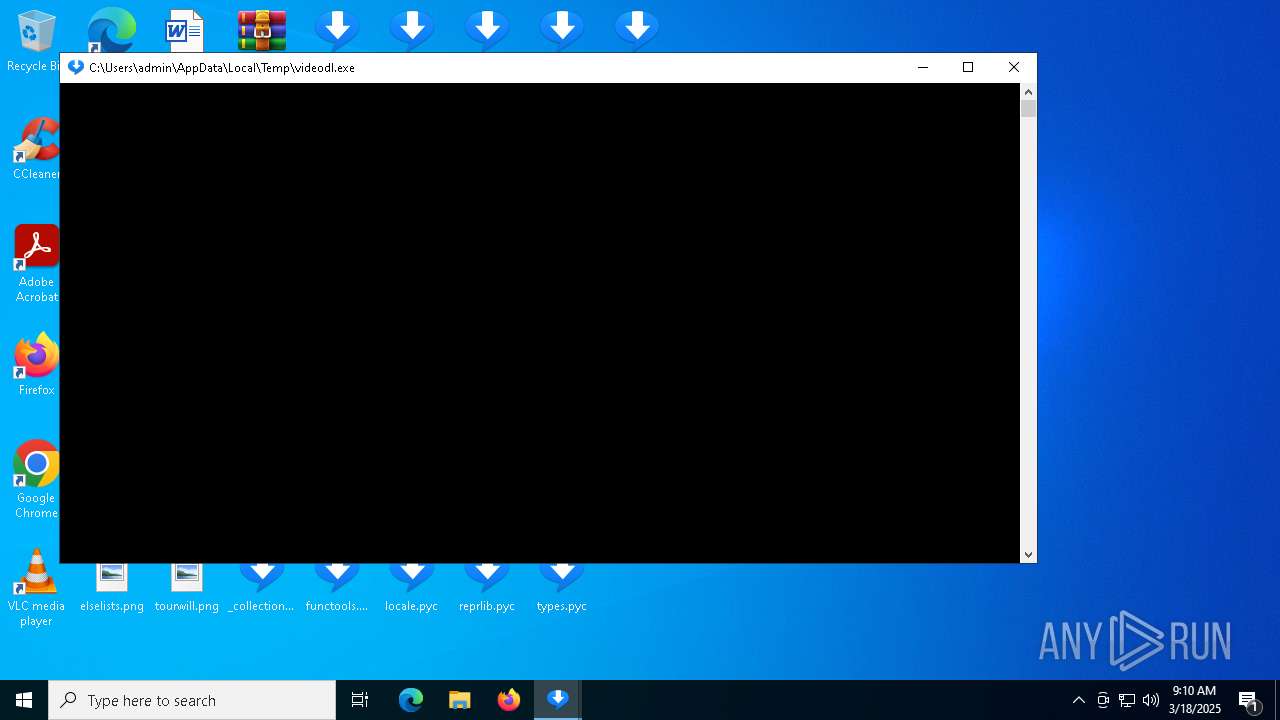
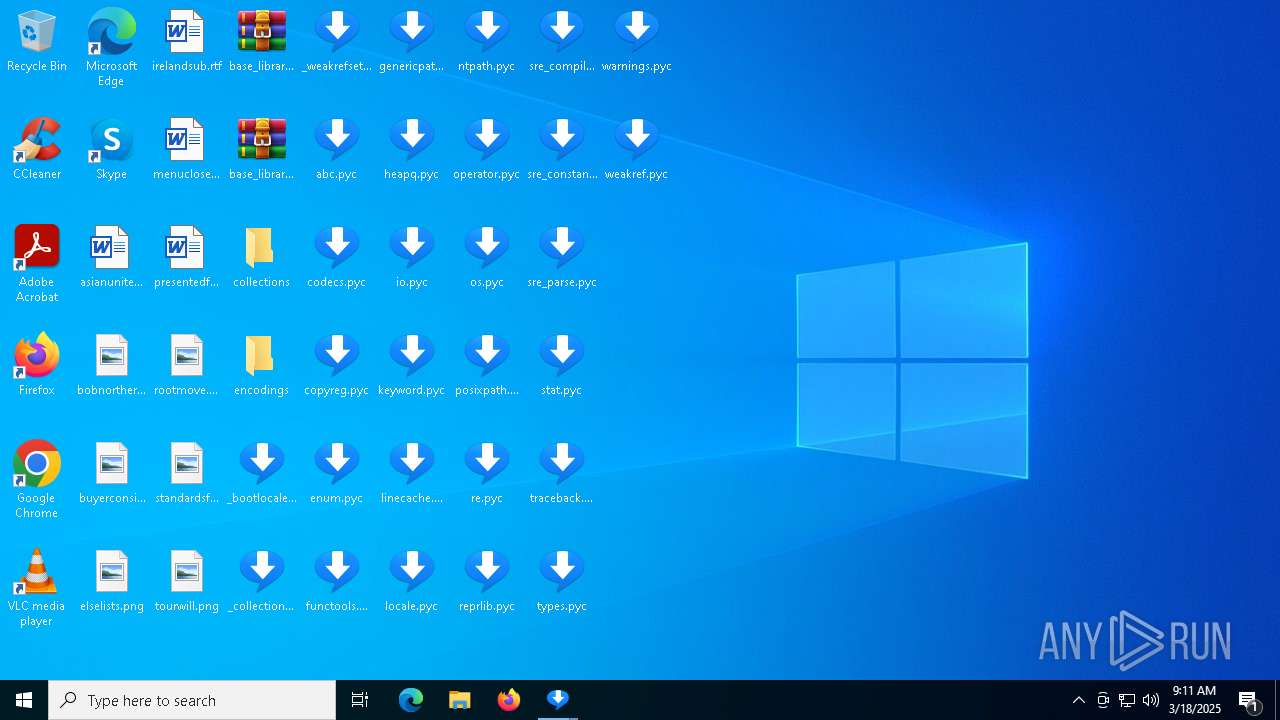
| File name: | videodl.exe |
| Full analysis: | https://app.any.run/tasks/f59bed30-dc15-42b2-b37e-23337d5dbf48 |
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2025, 09:07:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | 6999953923DD96FC332C7A434D865A07 |
| SHA1: | 36CF1193F34D554A73058CBEB063AB79E2187732 |
| SHA256: | 8873D25478AB8CDE2E41789A511AA7A769E3CF5009585CD3956841AFC30A8BC1 |
| SSDEEP: | 98304:CSFlJ5ZErF/X8Gh2XHvRvTuzXNF+UOH1g/6LYf4HUmnzza9lI///ALqq7i9hdQrc:+eg3DpDKuY69IdOrXoKWI/C |
MALICIOUS
No malicious indicators.SUSPICIOUS
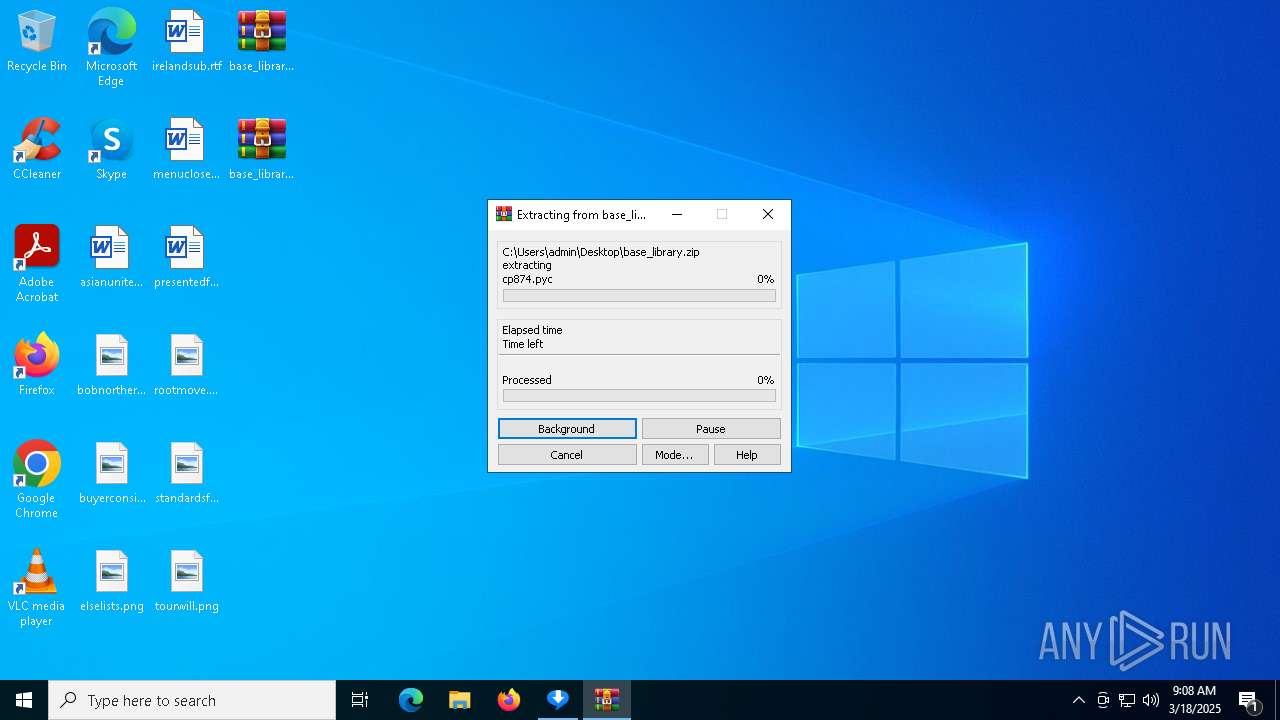
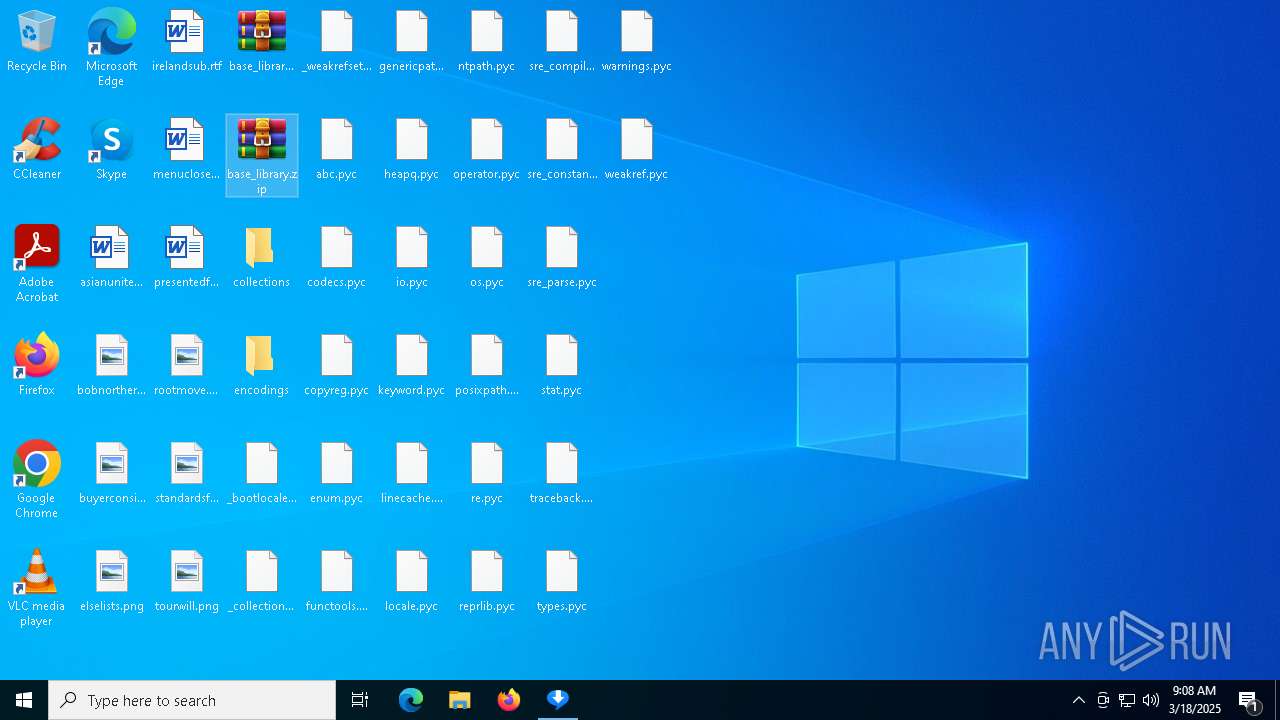
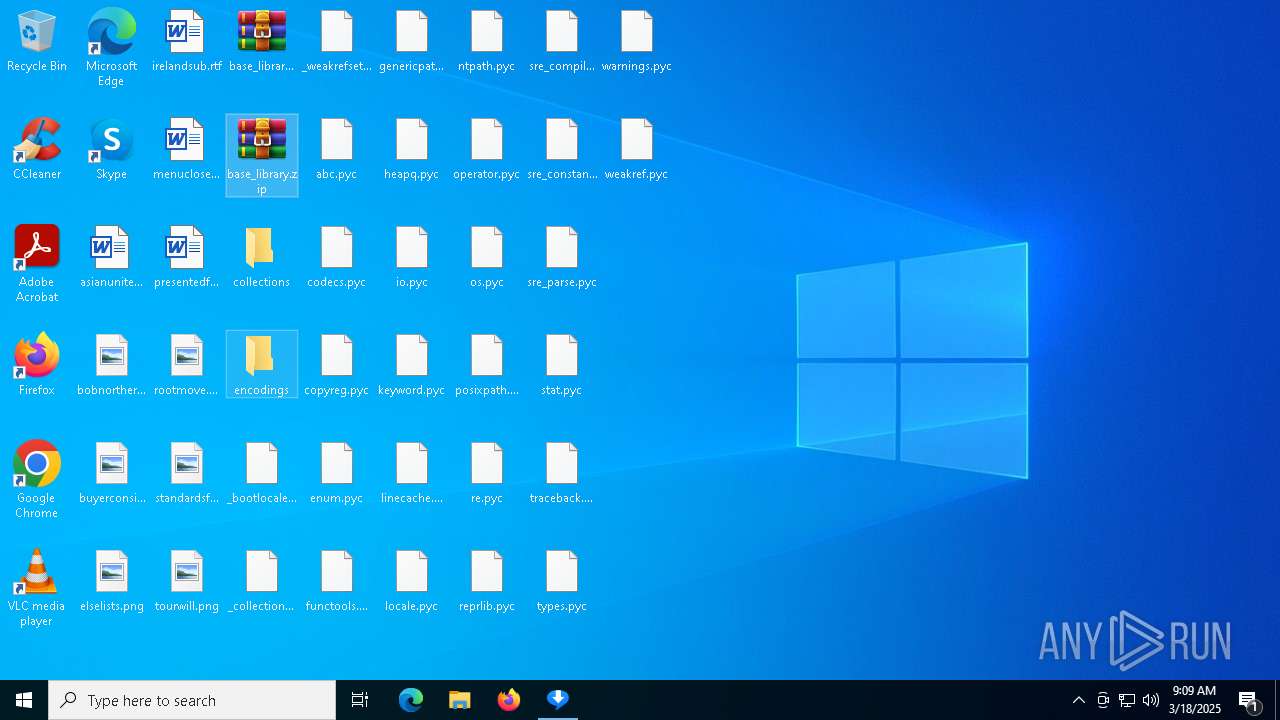
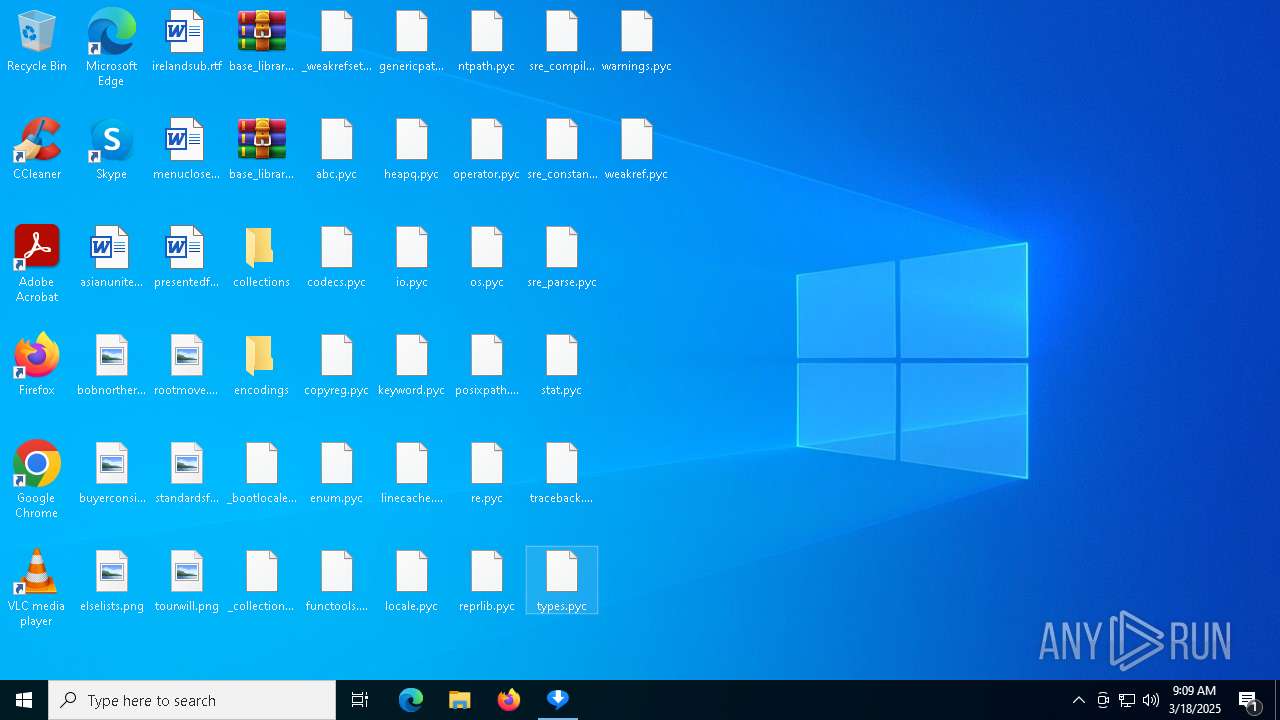
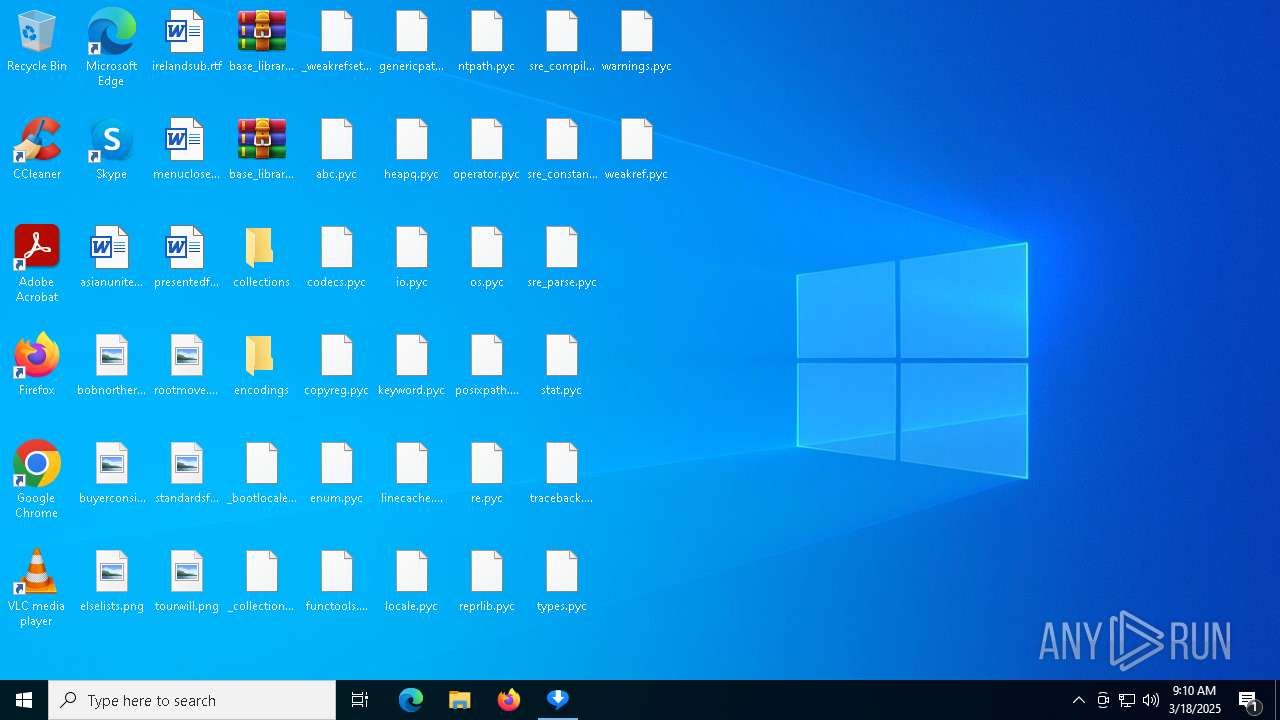
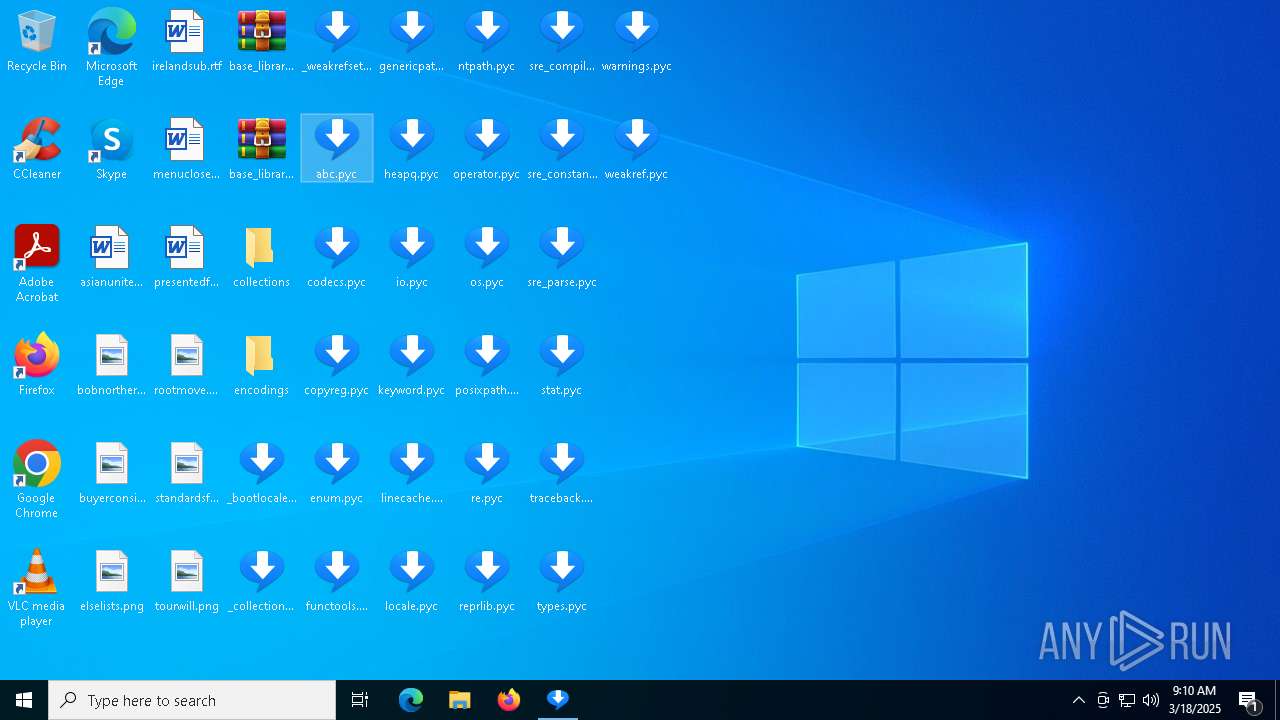
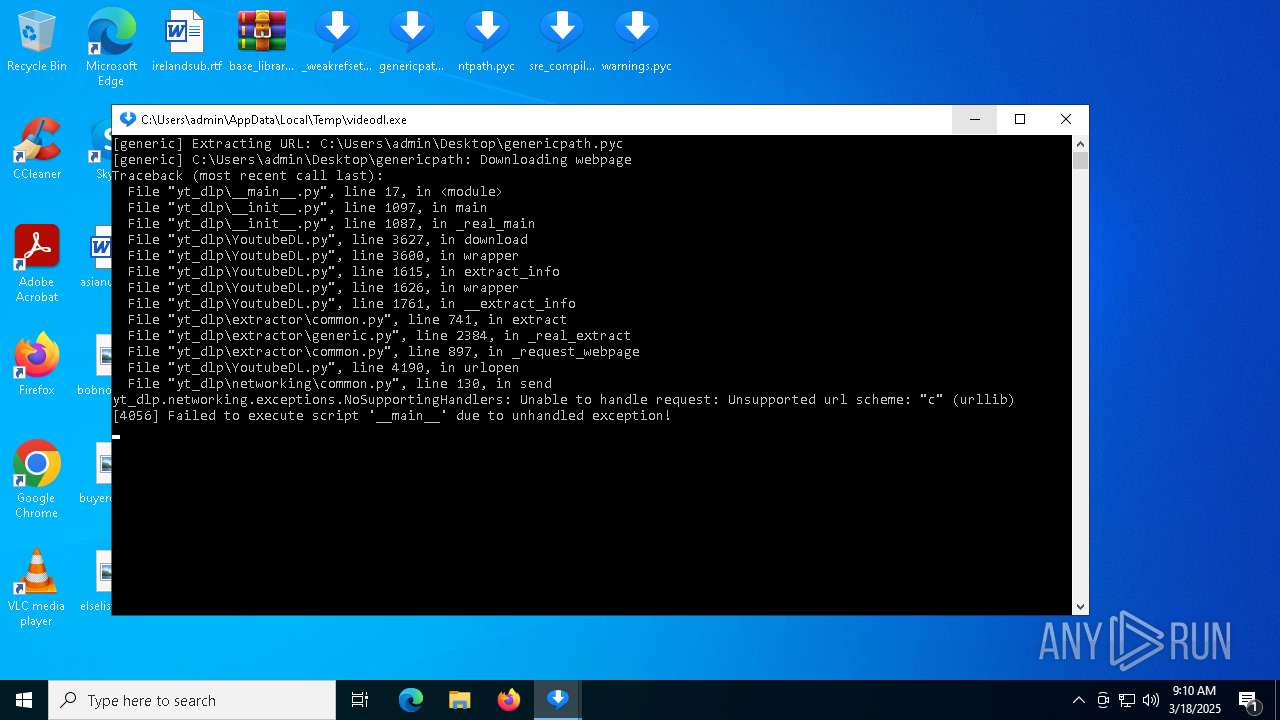
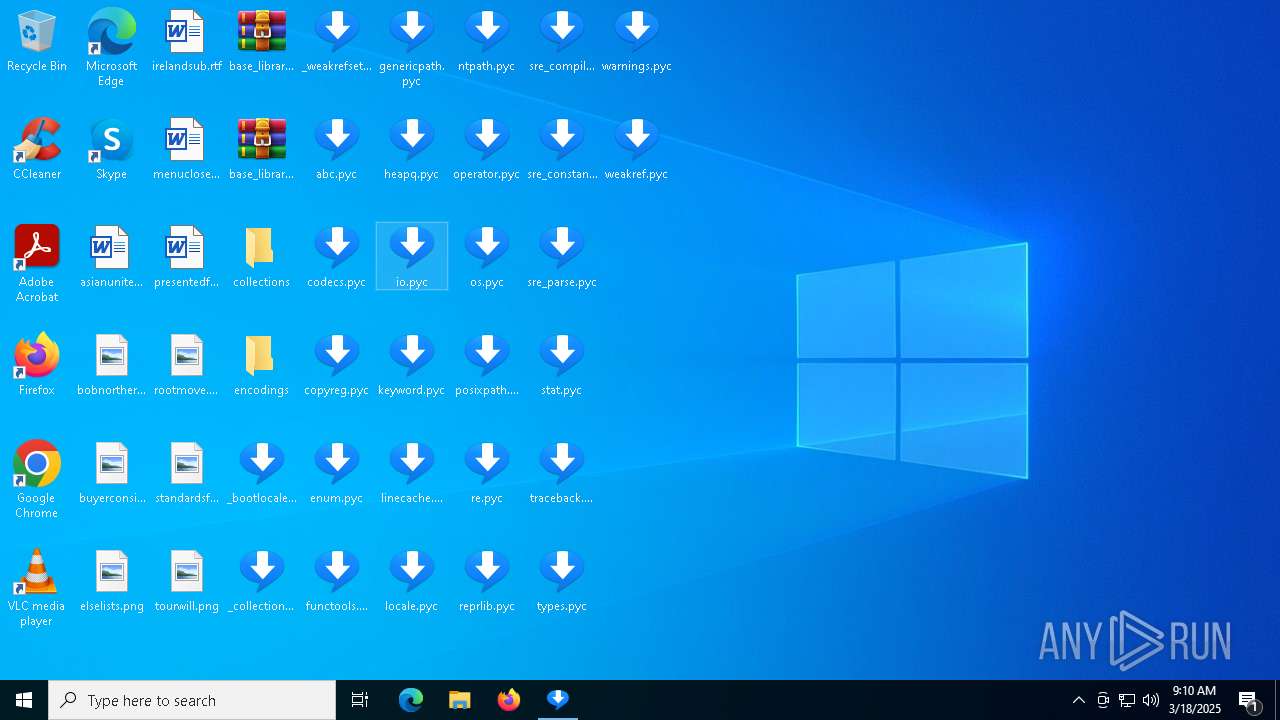
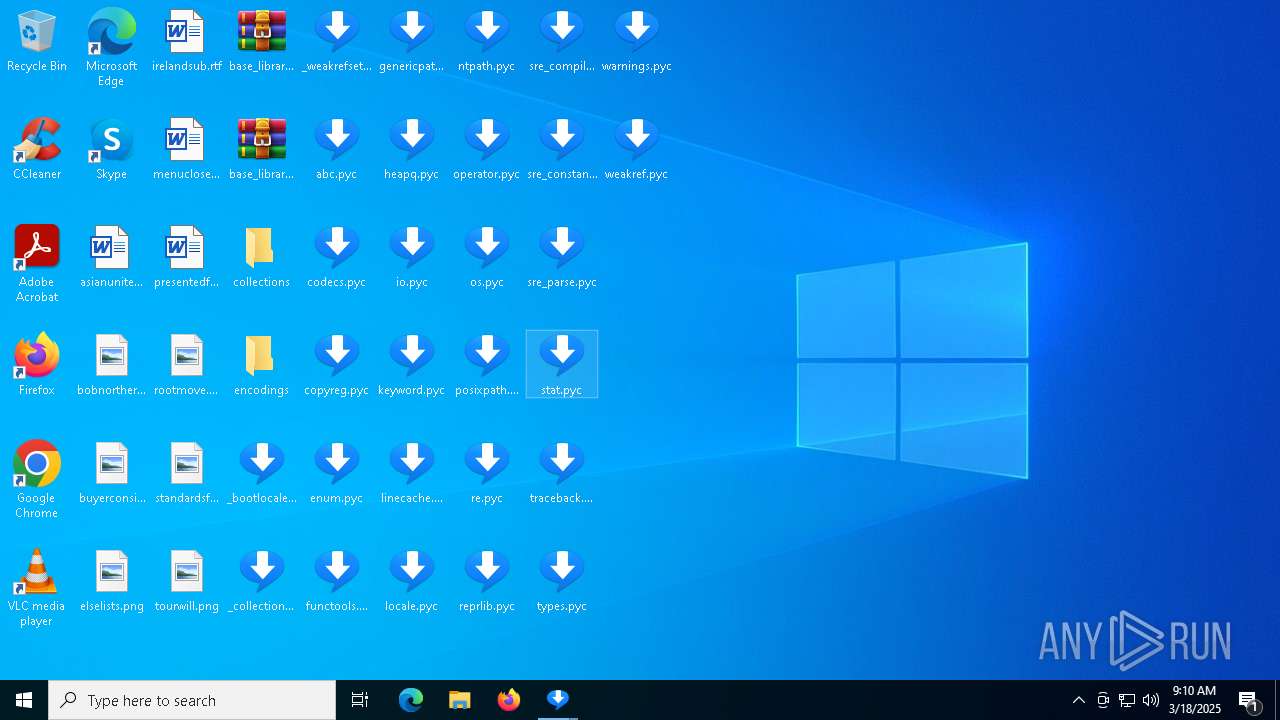
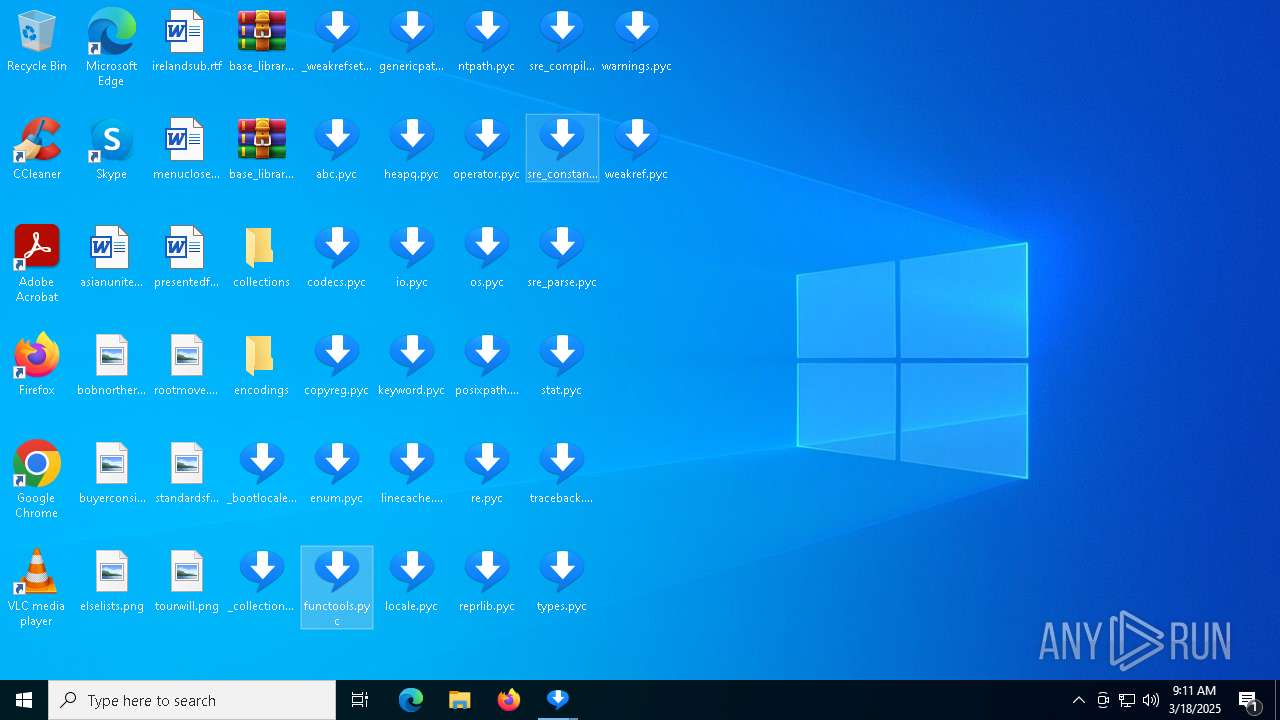
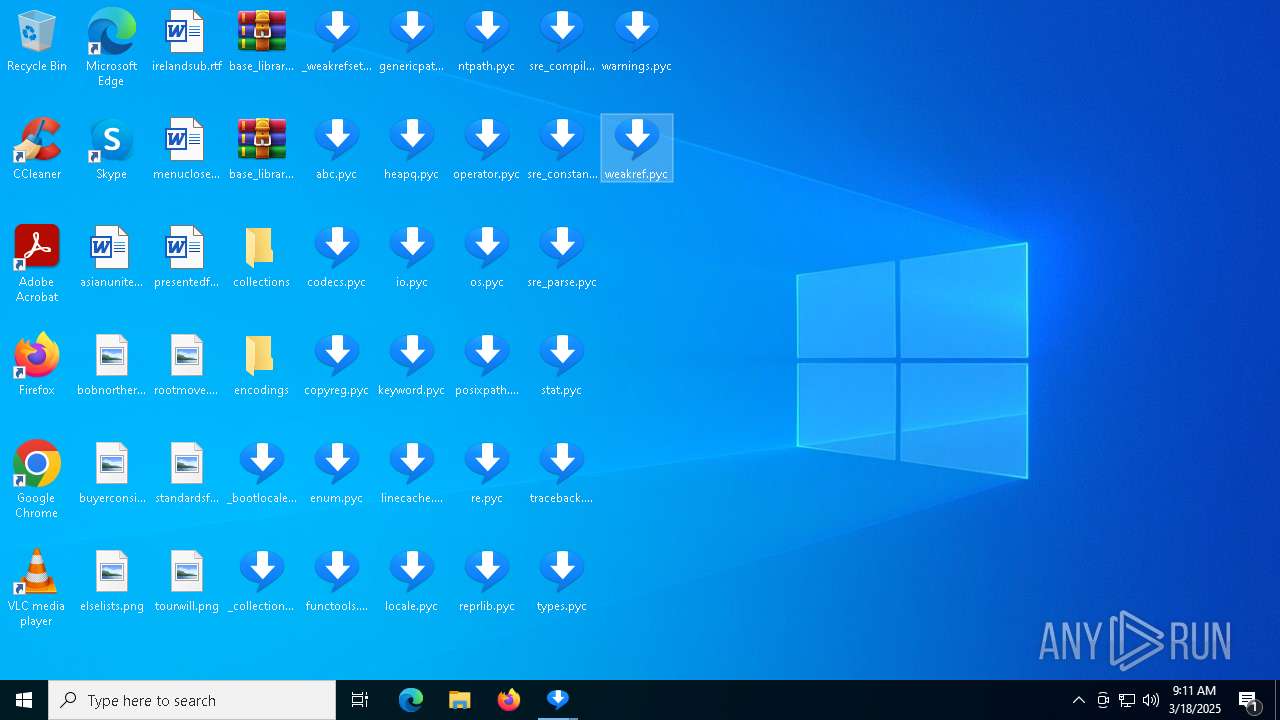
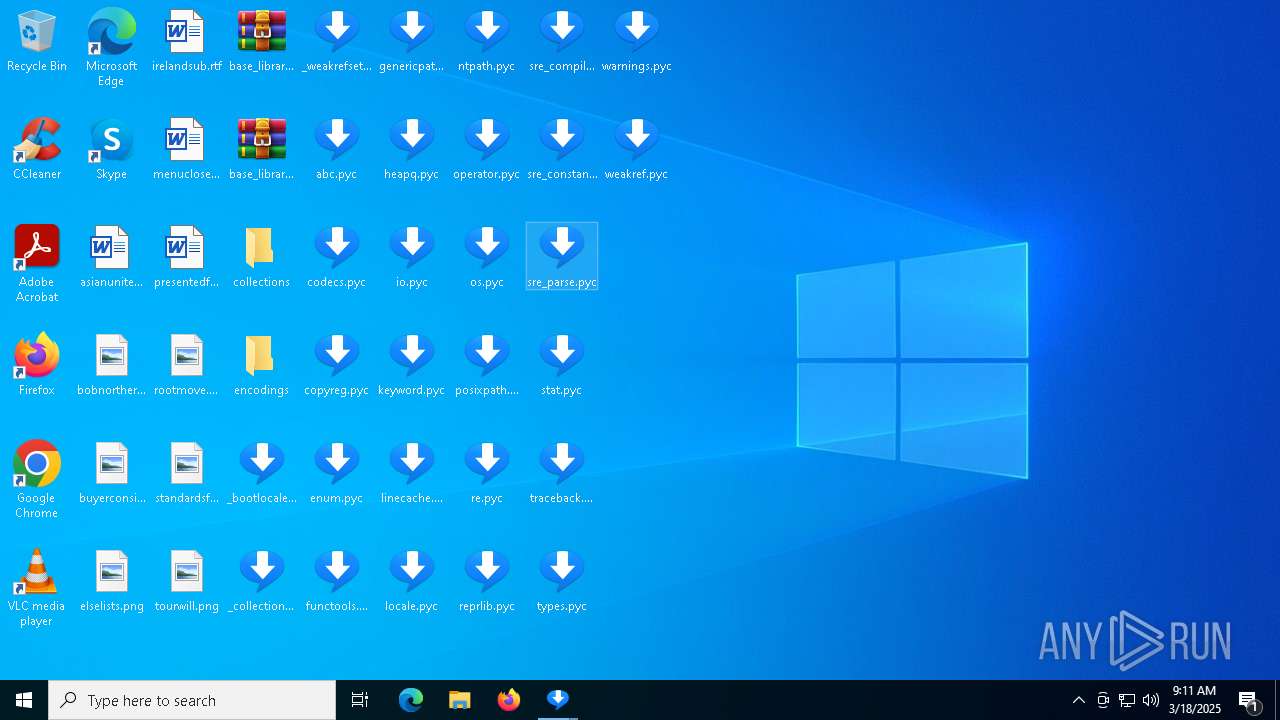
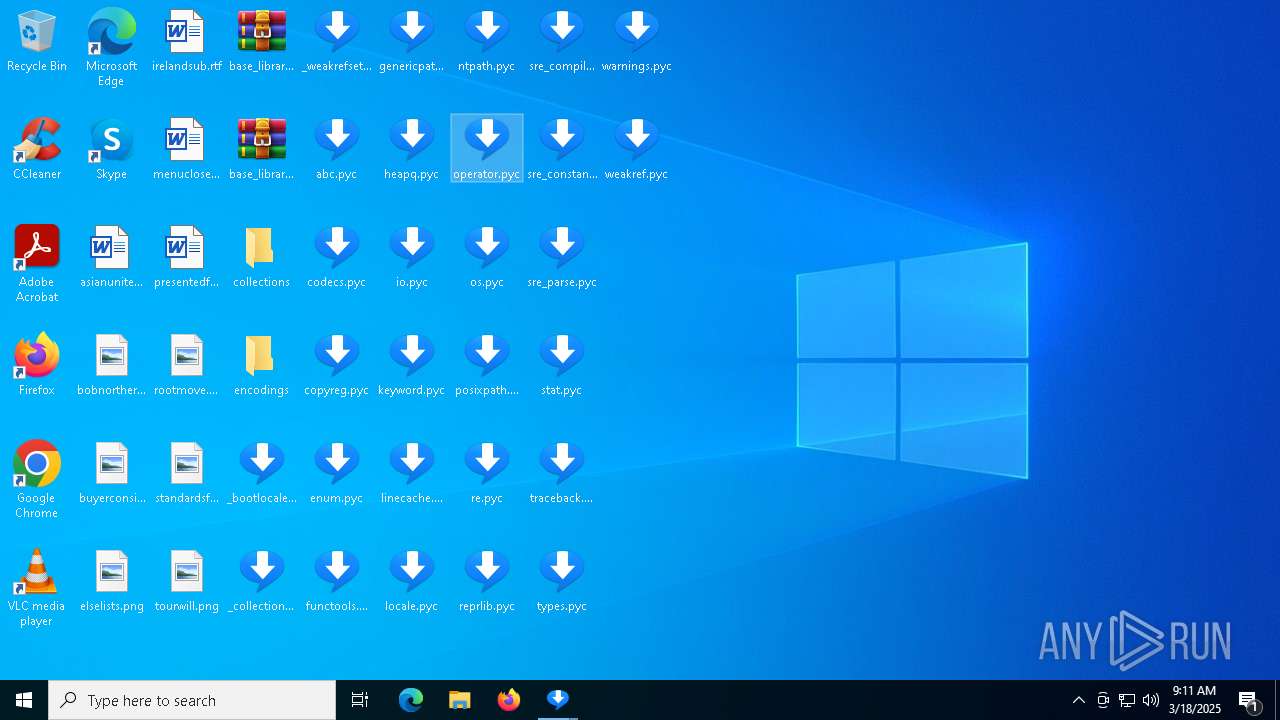
Executable content was dropped or overwritten
- videodl.exe (PID: 7440)
- videodl.exe (PID: 8160)
- videodl.exe (PID: 7380)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 6744)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 856)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 7500)
- videodl.exe (PID: 6108)
- videodl.exe (PID: 7136)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 5812)
Process drops legitimate windows executable
- videodl.exe (PID: 7440)
- videodl.exe (PID: 8160)
- videodl.exe (PID: 7380)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 6744)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 856)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 7500)
- videodl.exe (PID: 6108)
- videodl.exe (PID: 7136)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 5812)
The process drops C-runtime libraries
- videodl.exe (PID: 7440)
- videodl.exe (PID: 8160)
- videodl.exe (PID: 7380)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 6744)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 856)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 7500)
- videodl.exe (PID: 6108)
- videodl.exe (PID: 7136)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 5812)
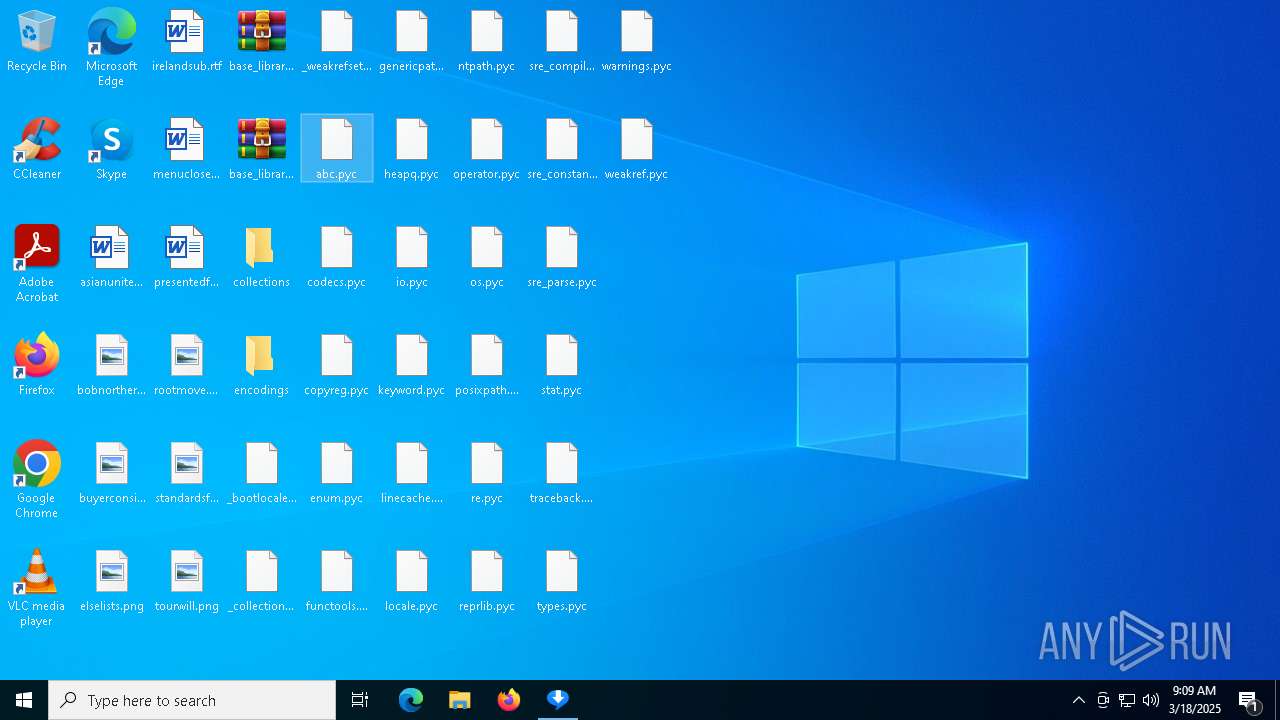
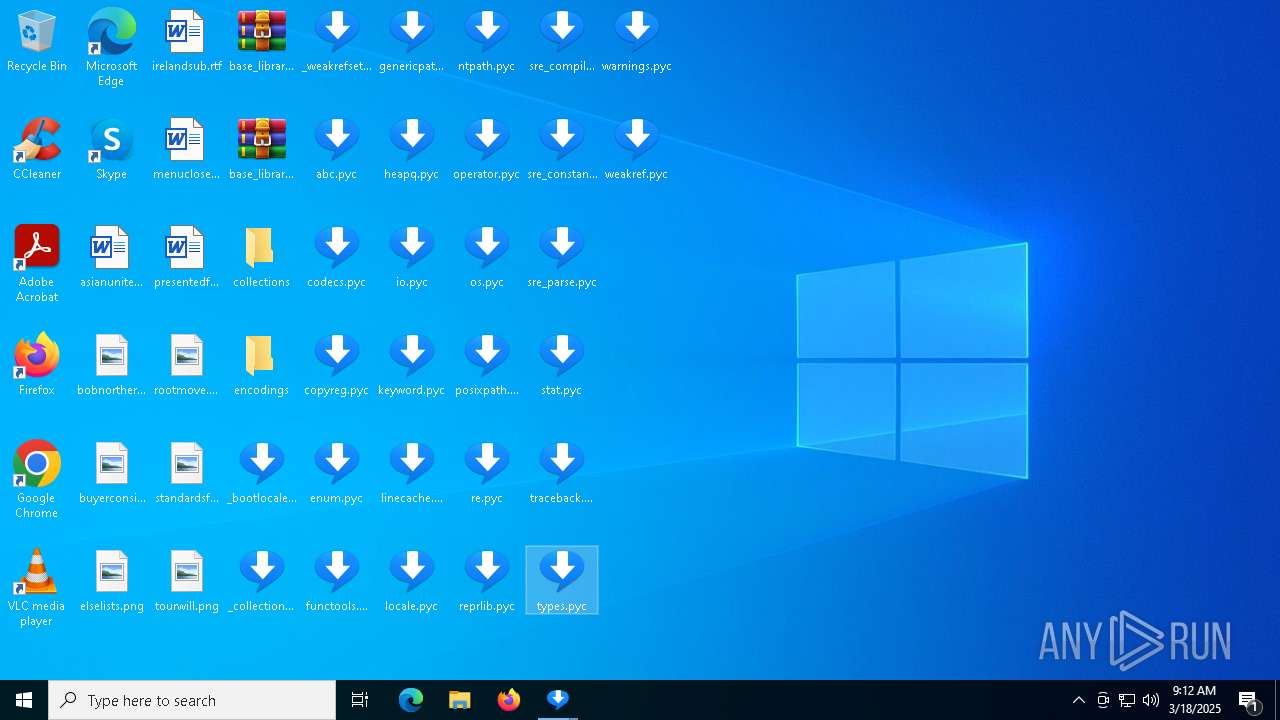
Process drops python dynamic module
- videodl.exe (PID: 7440)
- videodl.exe (PID: 8160)
- videodl.exe (PID: 7380)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 6744)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 856)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 7500)
- videodl.exe (PID: 7136)
- videodl.exe (PID: 6108)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 5812)
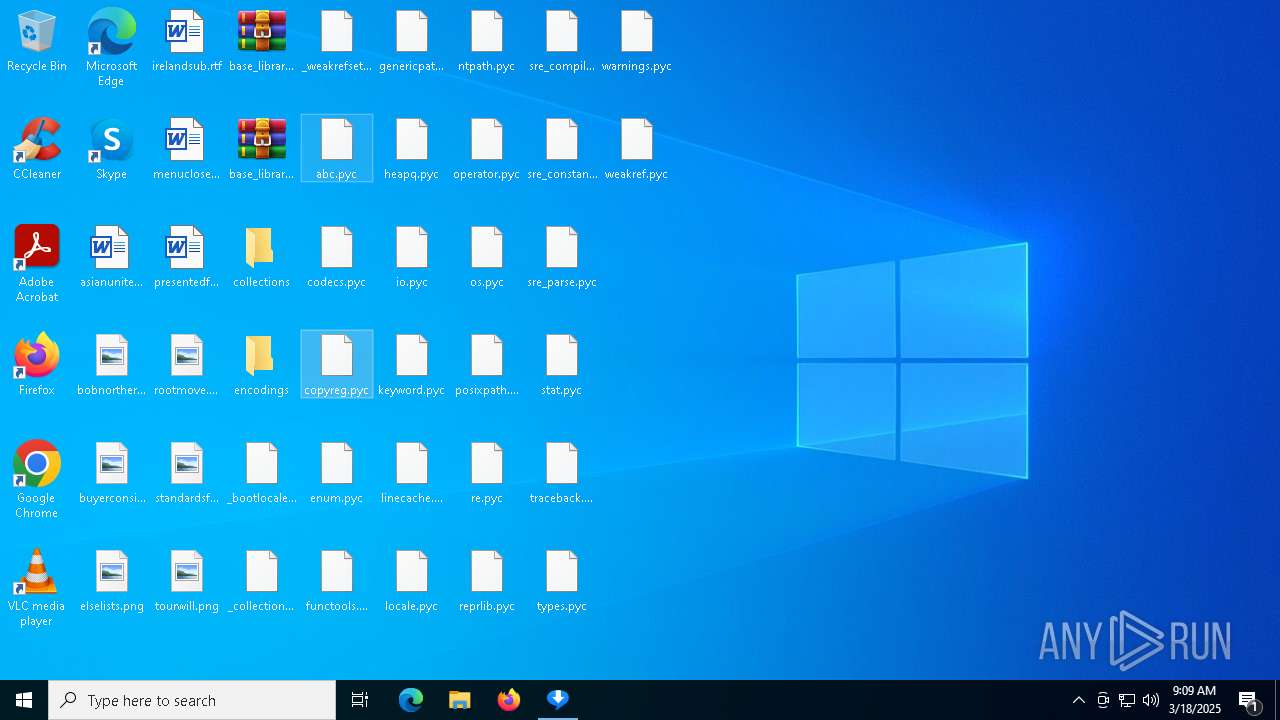
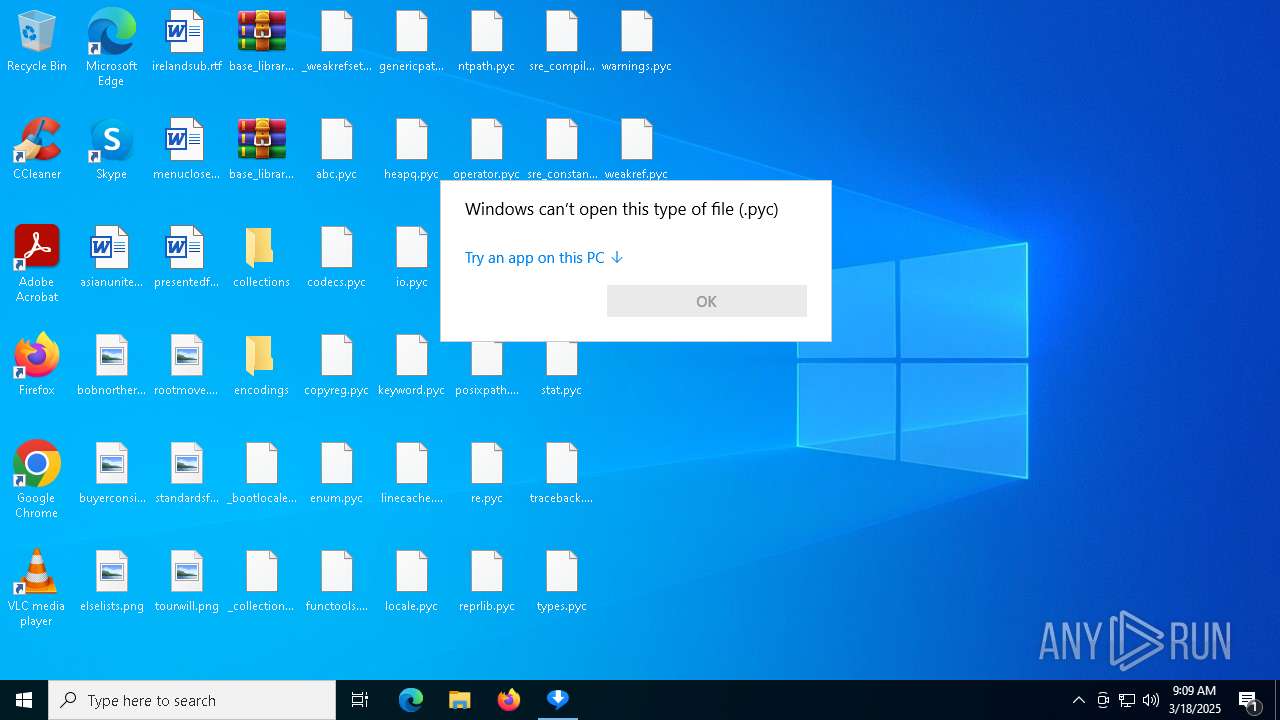
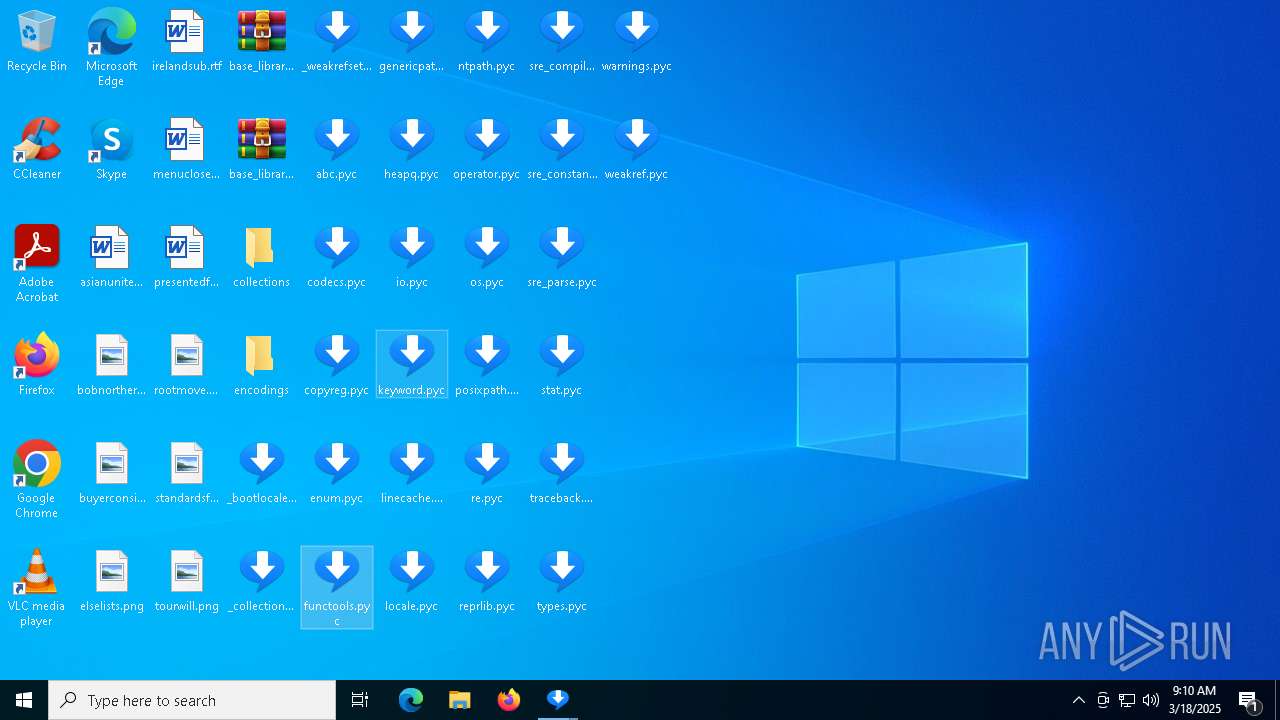
Application launched itself
- videodl.exe (PID: 7440)
- videodl.exe (PID: 8160)
- videodl.exe (PID: 7380)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 6744)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 856)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 7500)
- videodl.exe (PID: 6108)
- videodl.exe (PID: 7136)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 5812)
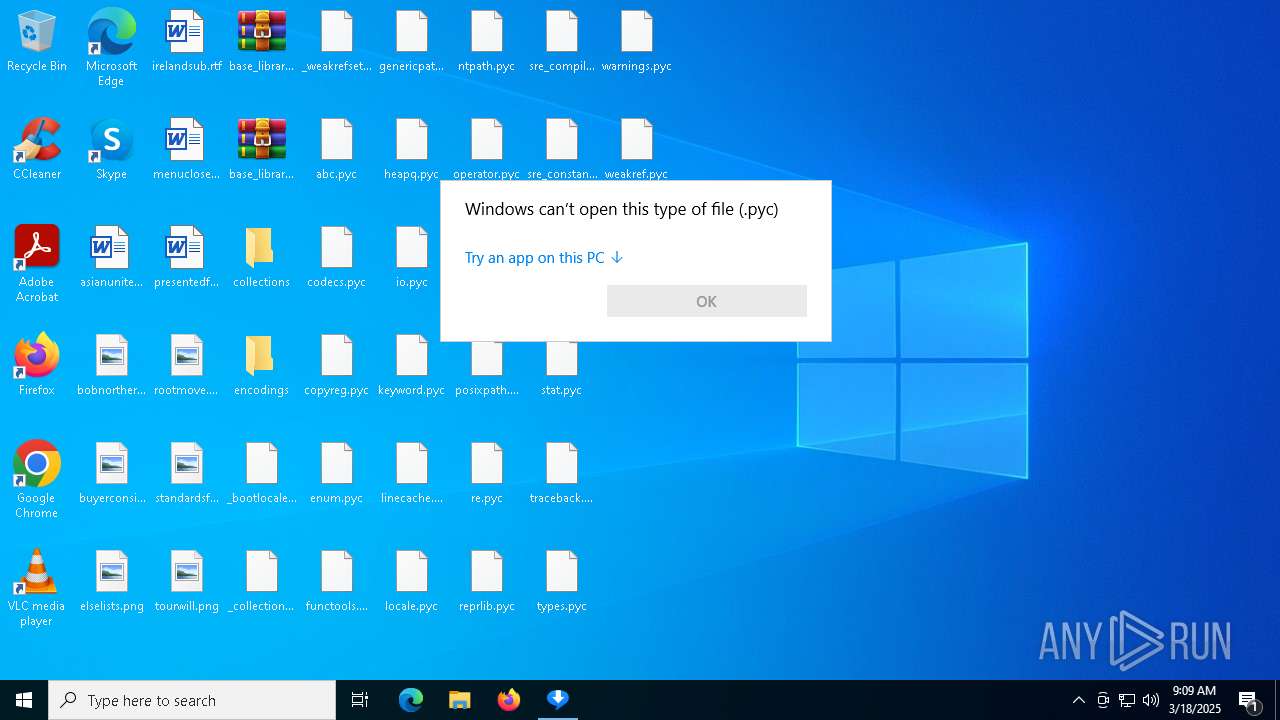
Loads Python modules
- videodl.exe (PID: 7536)
- videodl.exe (PID: 6800)
- videodl.exe (PID: 7292)
- videodl.exe (PID: 3364)
- videodl.exe (PID: 4056)
- videodl.exe (PID: 2896)
- videodl.exe (PID: 1128)
- videodl.exe (PID: 7356)
- videodl.exe (PID: 7456)
- videodl.exe (PID: 6752)
- videodl.exe (PID: 900)
- videodl.exe (PID: 7820)
- videodl.exe (PID: 7756)
- videodl.exe (PID: 6044)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 3028)
- videodl.exe (PID: 7520)
- videodl.exe (PID: 968)
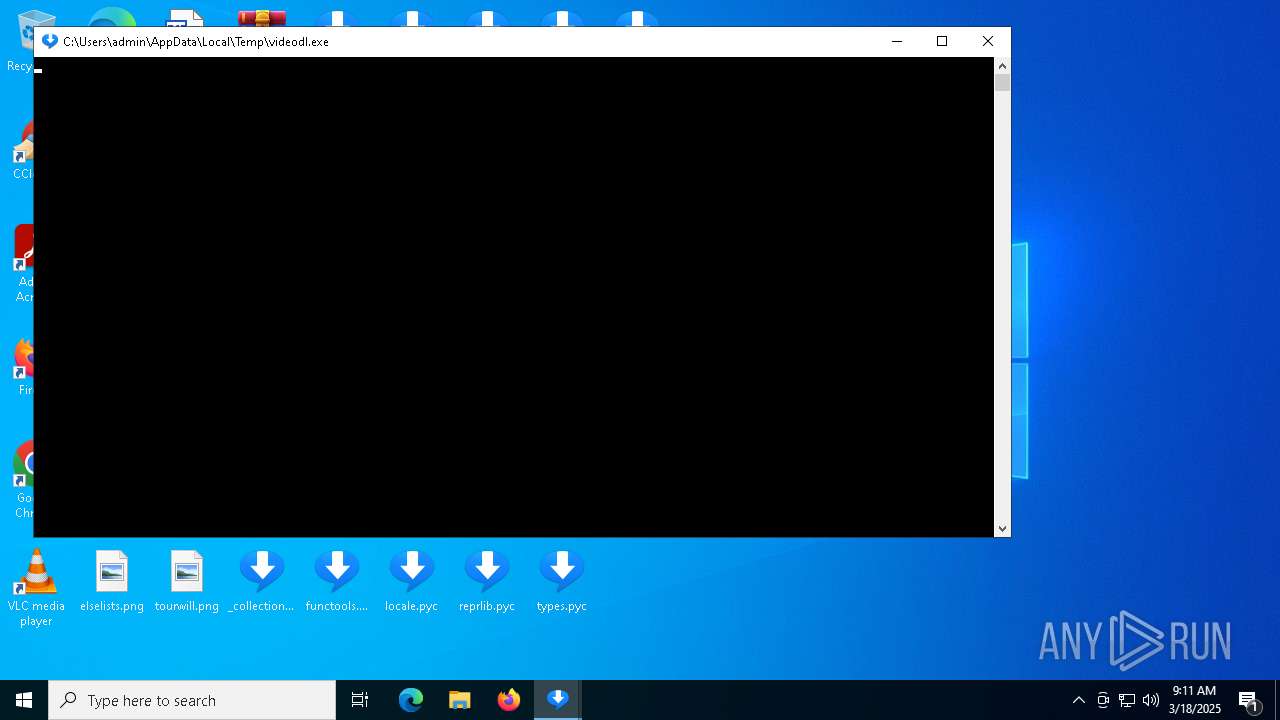
Starts CMD.EXE for commands execution
- videodl.exe (PID: 7536)
- videodl.exe (PID: 6800)
- videodl.exe (PID: 7292)
- videodl.exe (PID: 3364)
- videodl.exe (PID: 4056)
- videodl.exe (PID: 2896)
- videodl.exe (PID: 1128)
- videodl.exe (PID: 7356)
- videodl.exe (PID: 7456)
- videodl.exe (PID: 6752)
- videodl.exe (PID: 968)
- videodl.exe (PID: 900)
- videodl.exe (PID: 7820)
- videodl.exe (PID: 7756)
- videodl.exe (PID: 6044)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 3028)
- videodl.exe (PID: 7520)
Found regular expressions for crypto-addresses (YARA)
- videodl.exe (PID: 7536)
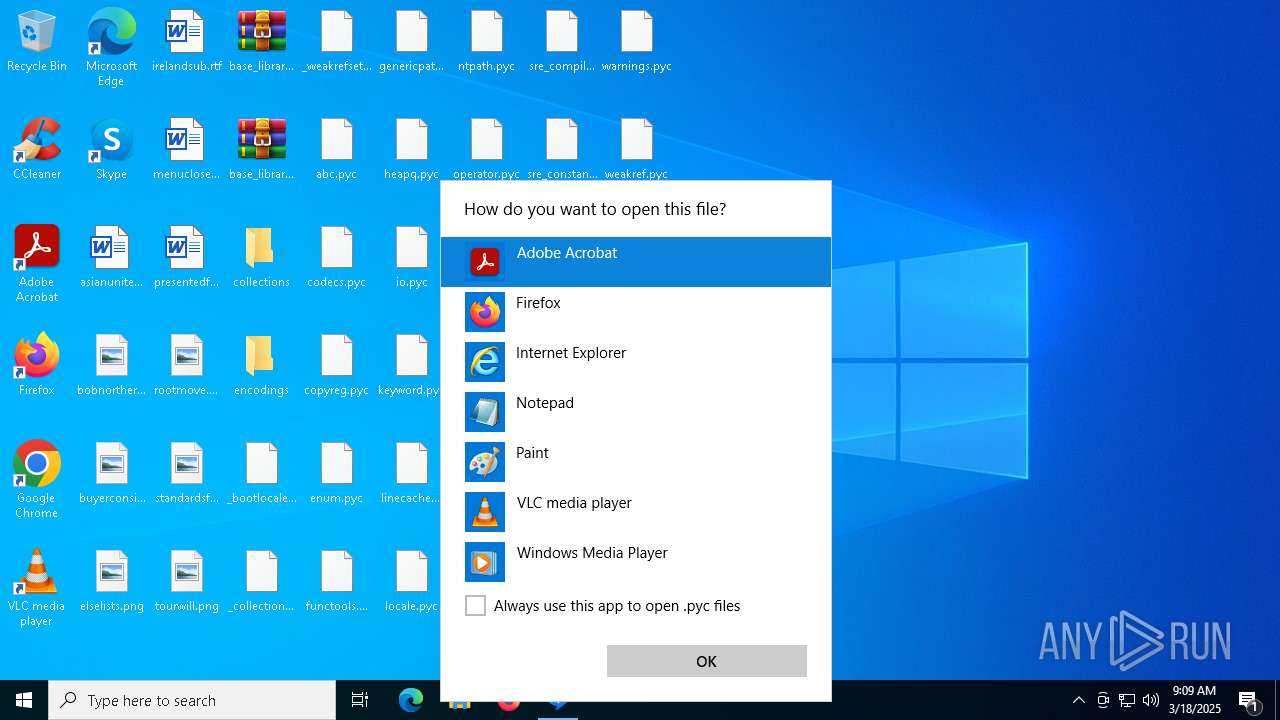
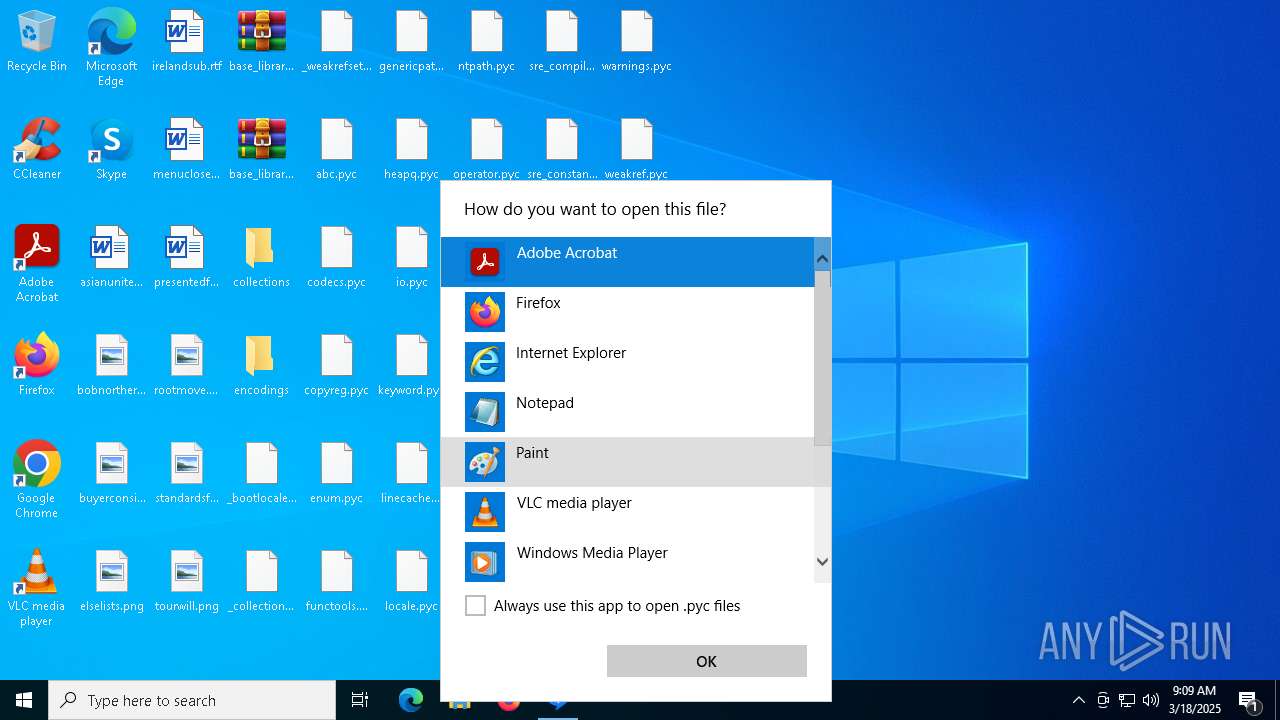
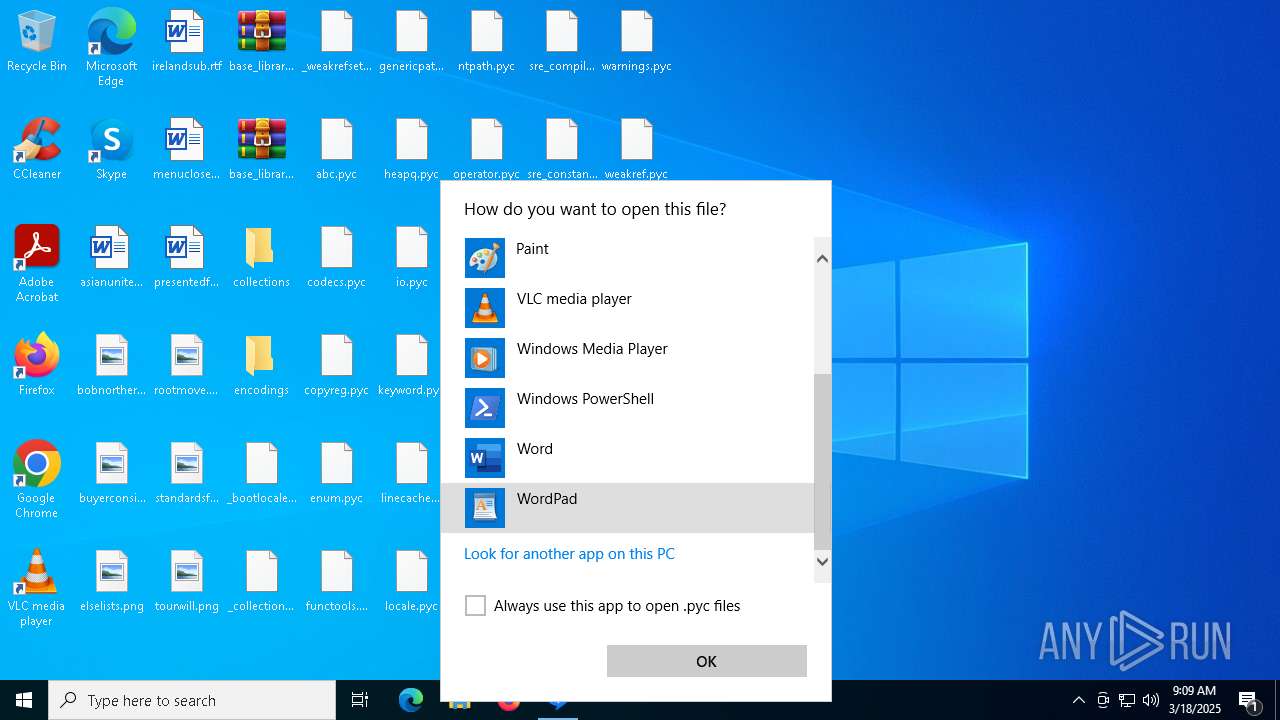
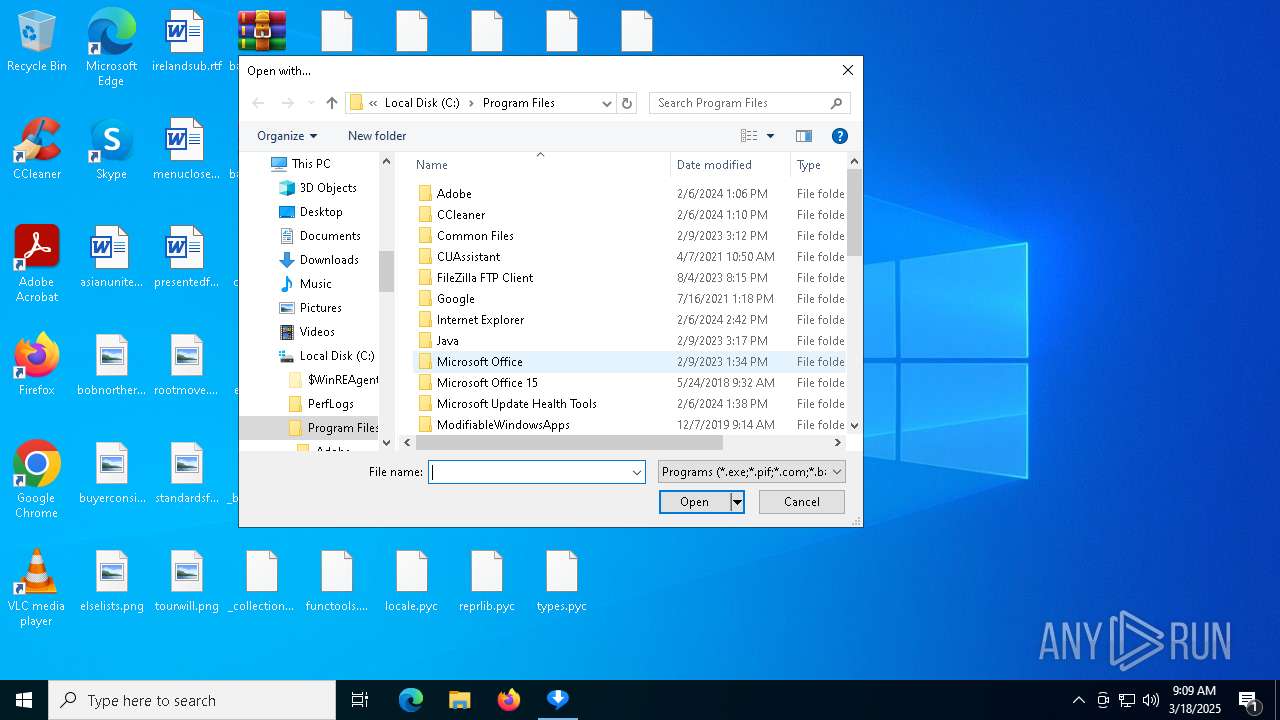
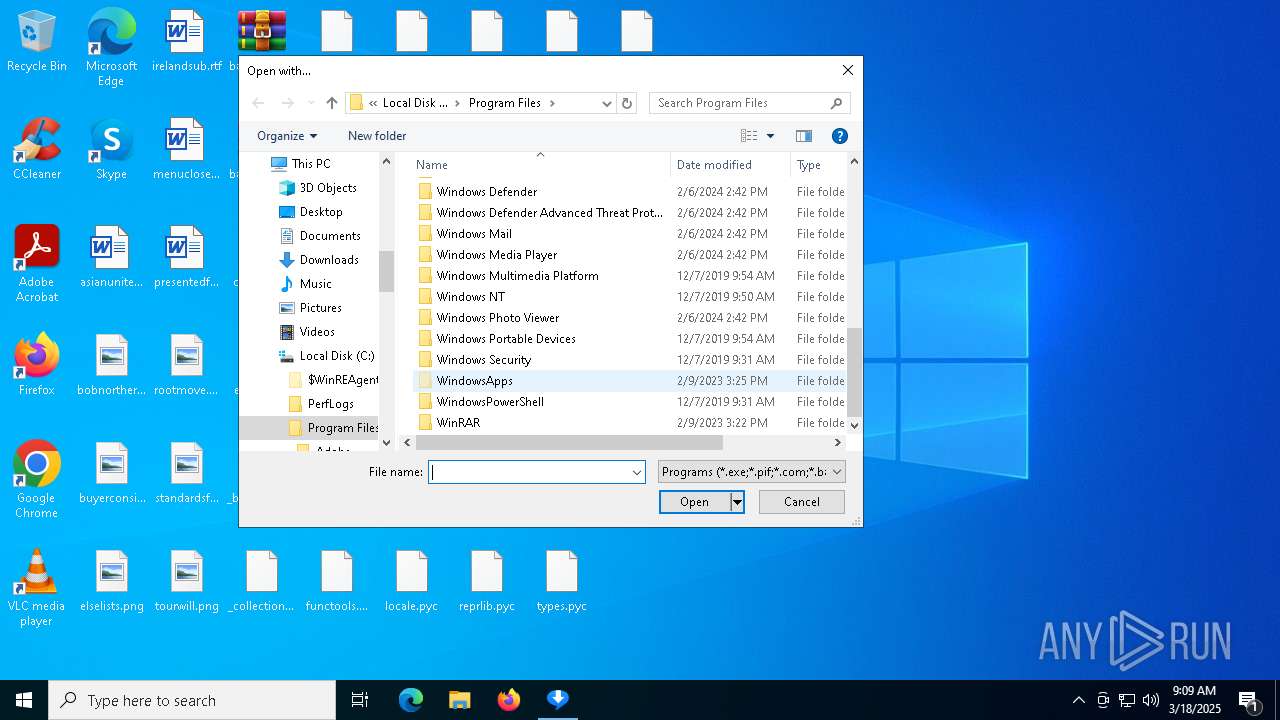
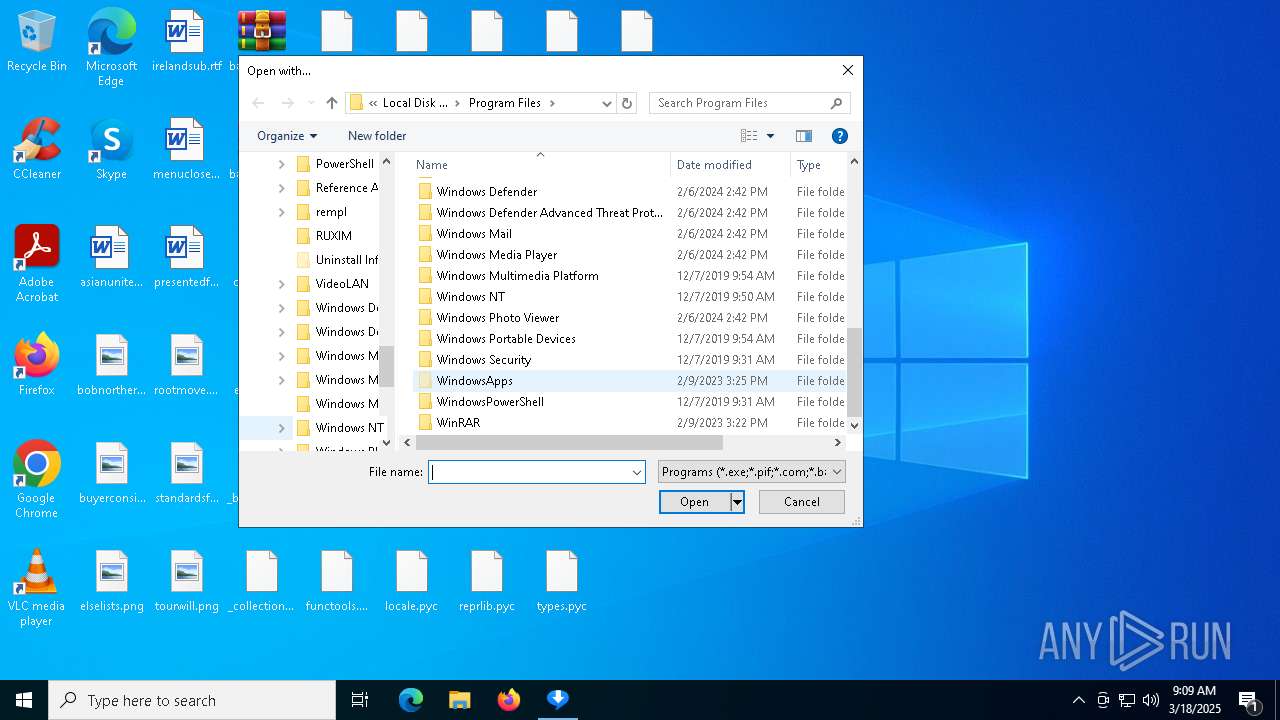
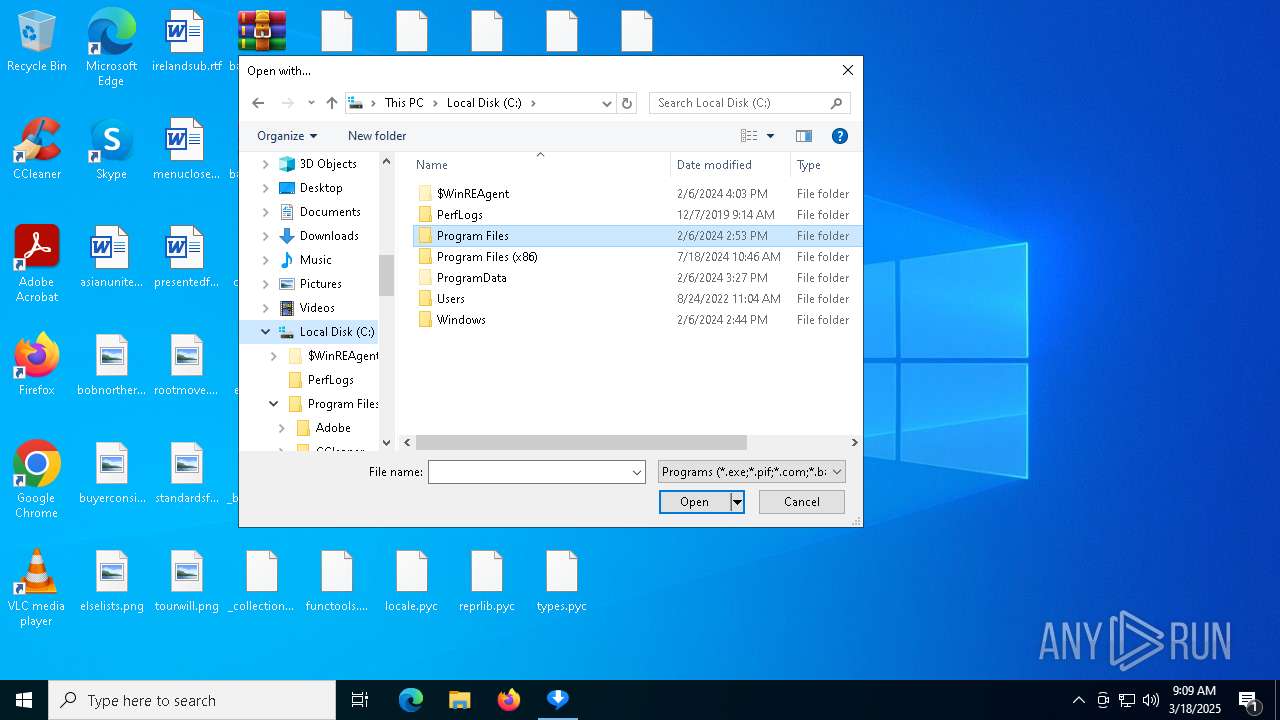
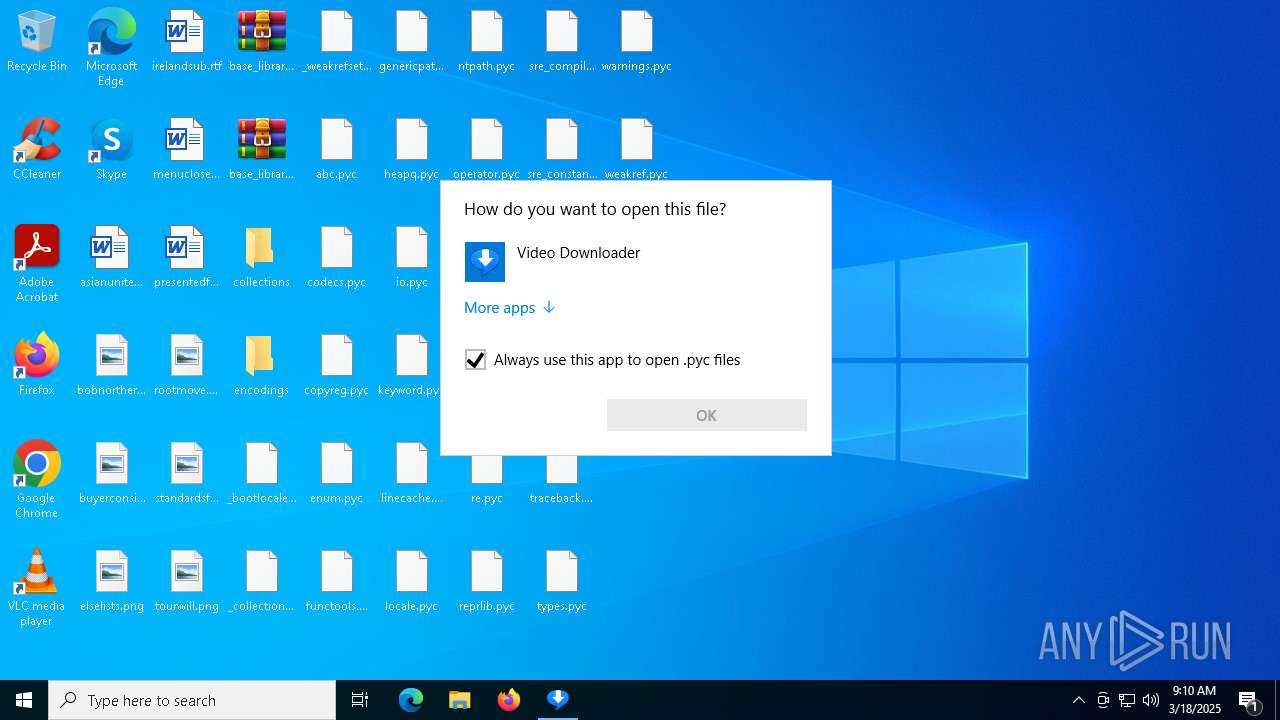
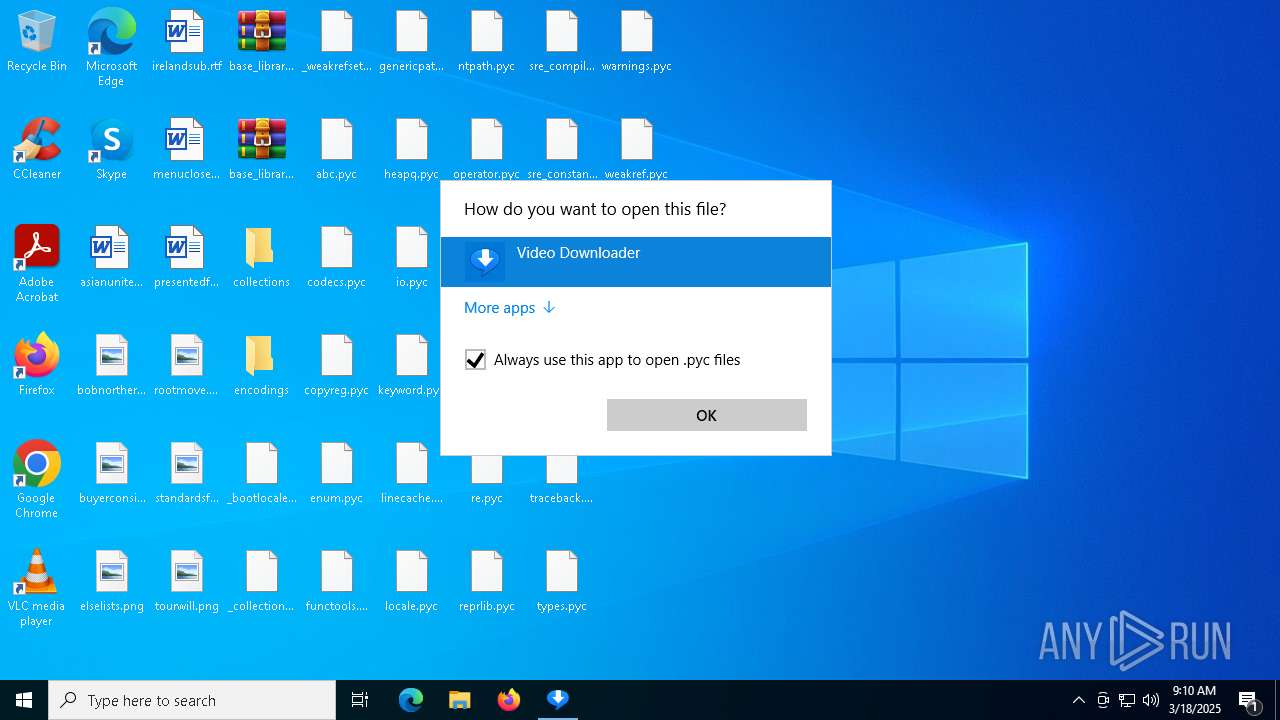
Creates file in the systems drive root
- OpenWith.exe (PID: 7916)
INFO
The sample compiled with english language support
- videodl.exe (PID: 7440)
- videodl.exe (PID: 8160)
- videodl.exe (PID: 7380)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 6744)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 856)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 7500)
- videodl.exe (PID: 6108)
- videodl.exe (PID: 7136)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 5812)
Checks supported languages
- videodl.exe (PID: 7440)
- videodl.exe (PID: 7536)
- ShellExperienceHost.exe (PID: 7084)
- videodl.exe (PID: 8160)
- videodl.exe (PID: 6800)
- videodl.exe (PID: 7292)
- videodl.exe (PID: 7380)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 3364)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 4056)
- videodl.exe (PID: 2896)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 1128)
- videodl.exe (PID: 856)
- videodl.exe (PID: 7356)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 7456)
- videodl.exe (PID: 6752)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 968)
- videodl.exe (PID: 900)
- videodl.exe (PID: 7820)
- videodl.exe (PID: 7756)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 5812)
- videodl.exe (PID: 3028)
- videodl.exe (PID: 7520)
Reads the computer name
- videodl.exe (PID: 7440)
- ShellExperienceHost.exe (PID: 7084)
- videodl.exe (PID: 7536)
- videodl.exe (PID: 8160)
- videodl.exe (PID: 6800)
- videodl.exe (PID: 7380)
- videodl.exe (PID: 7292)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 4056)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 856)
- videodl.exe (PID: 1128)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 7456)
- videodl.exe (PID: 6752)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 968)
- videodl.exe (PID: 900)
- videodl.exe (PID: 7820)
- videodl.exe (PID: 7756)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 6044)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 3028)
- videodl.exe (PID: 5812)
- videodl.exe (PID: 7520)
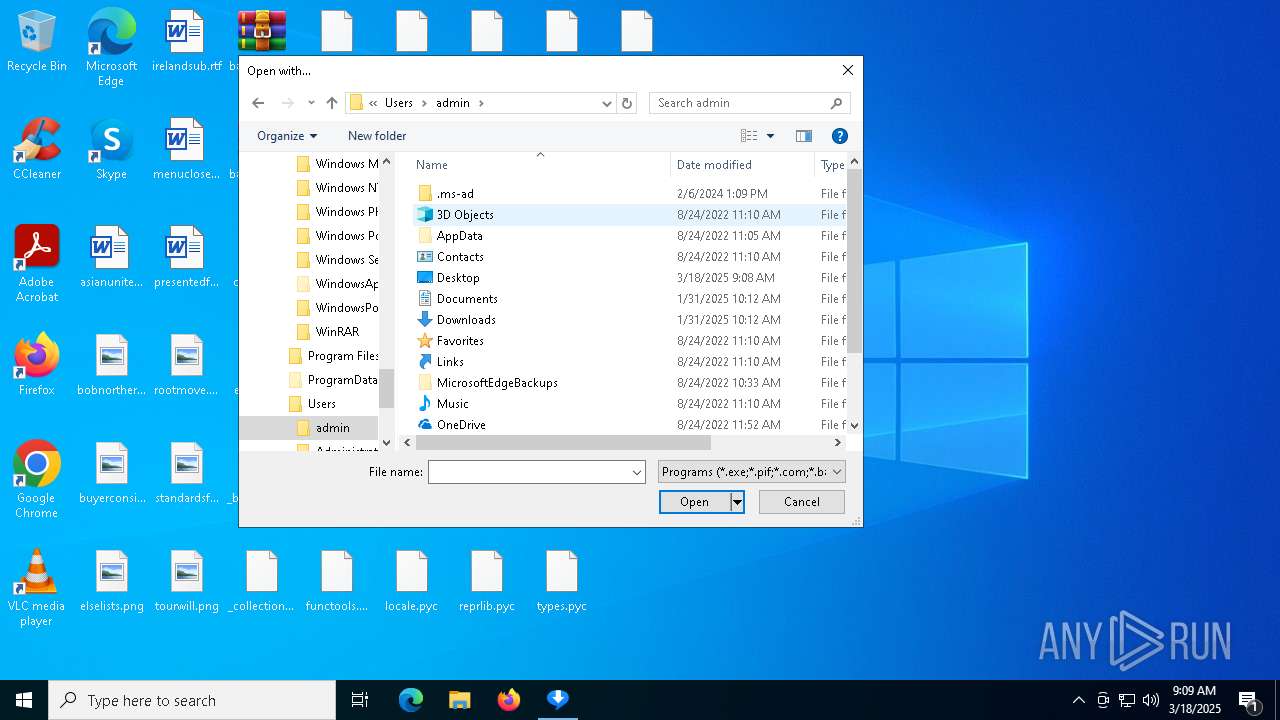
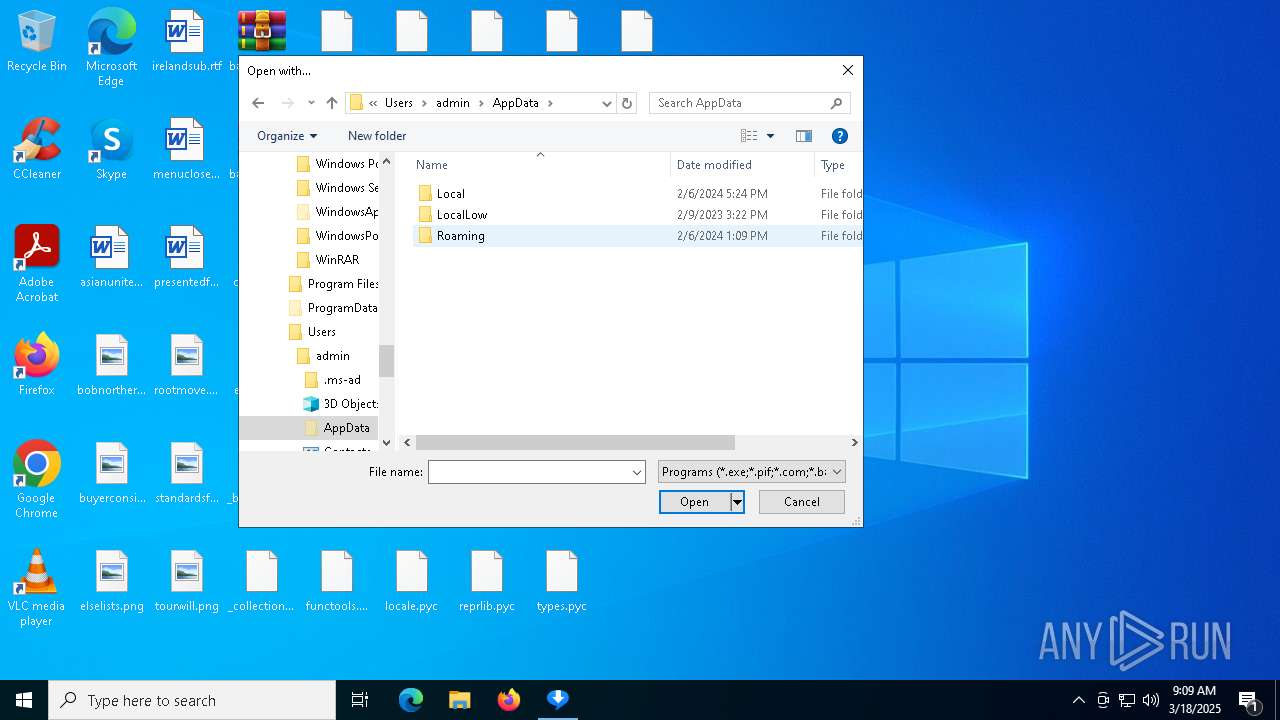
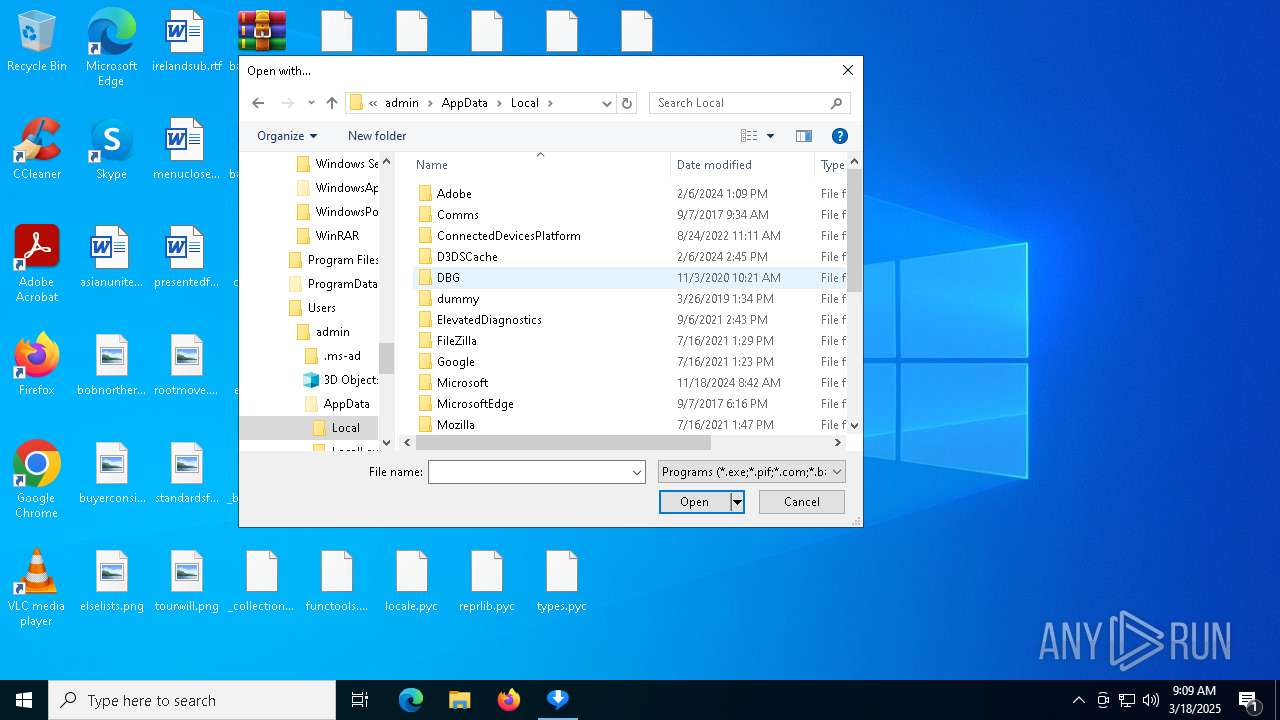
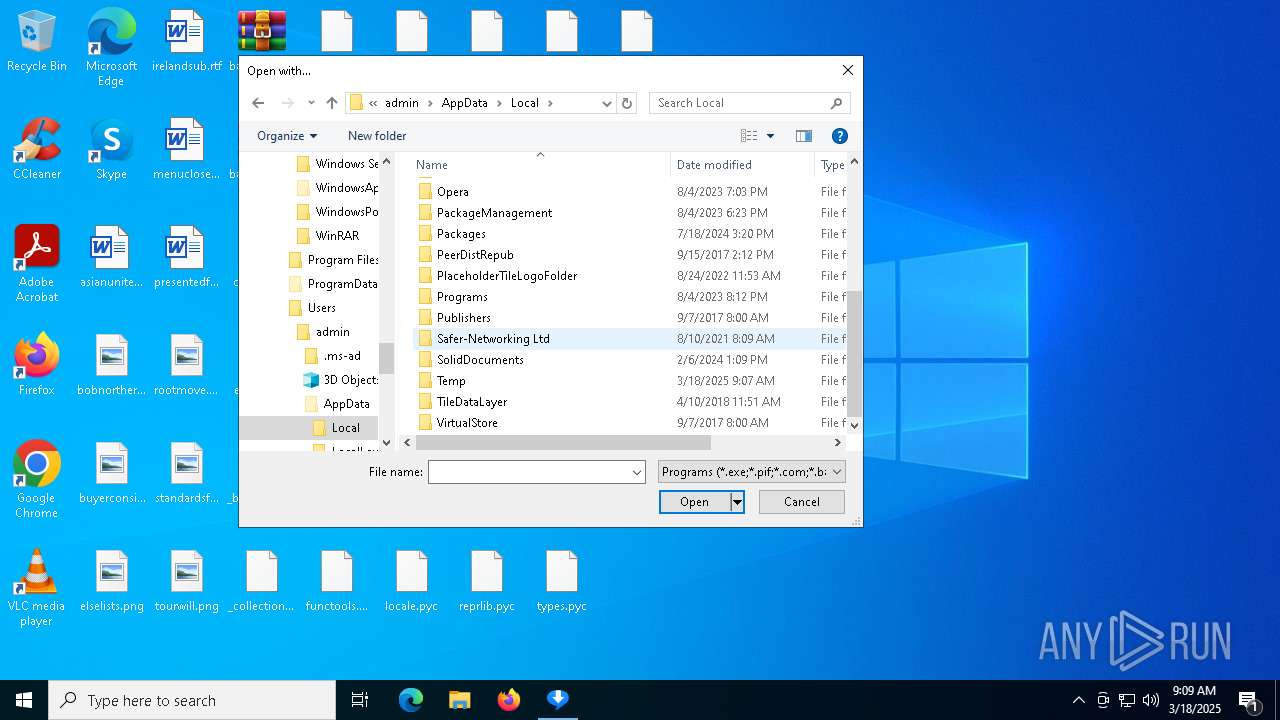
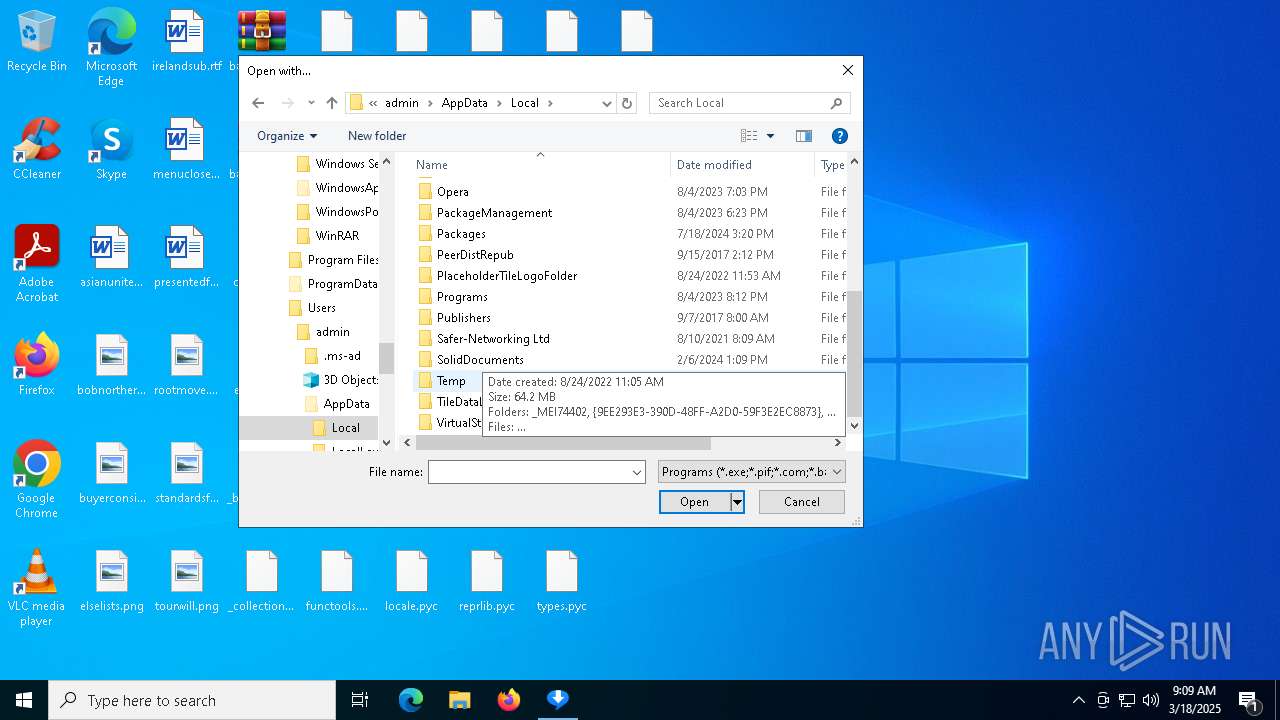
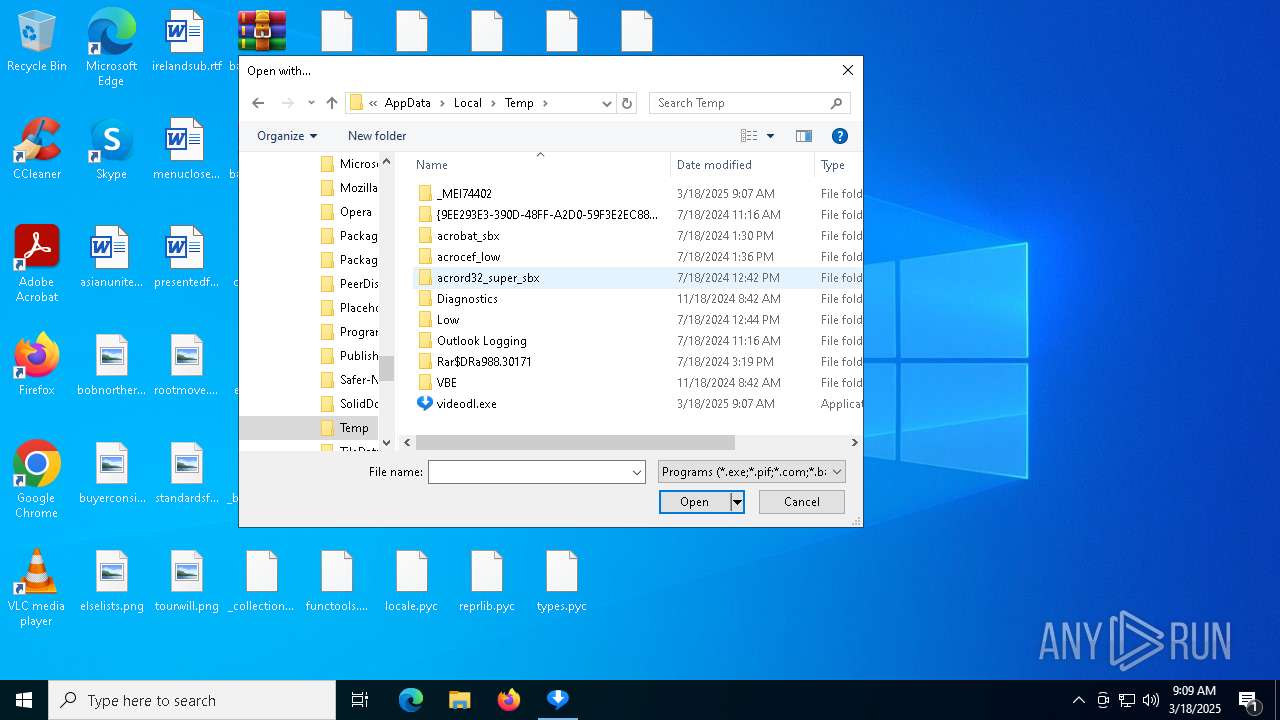
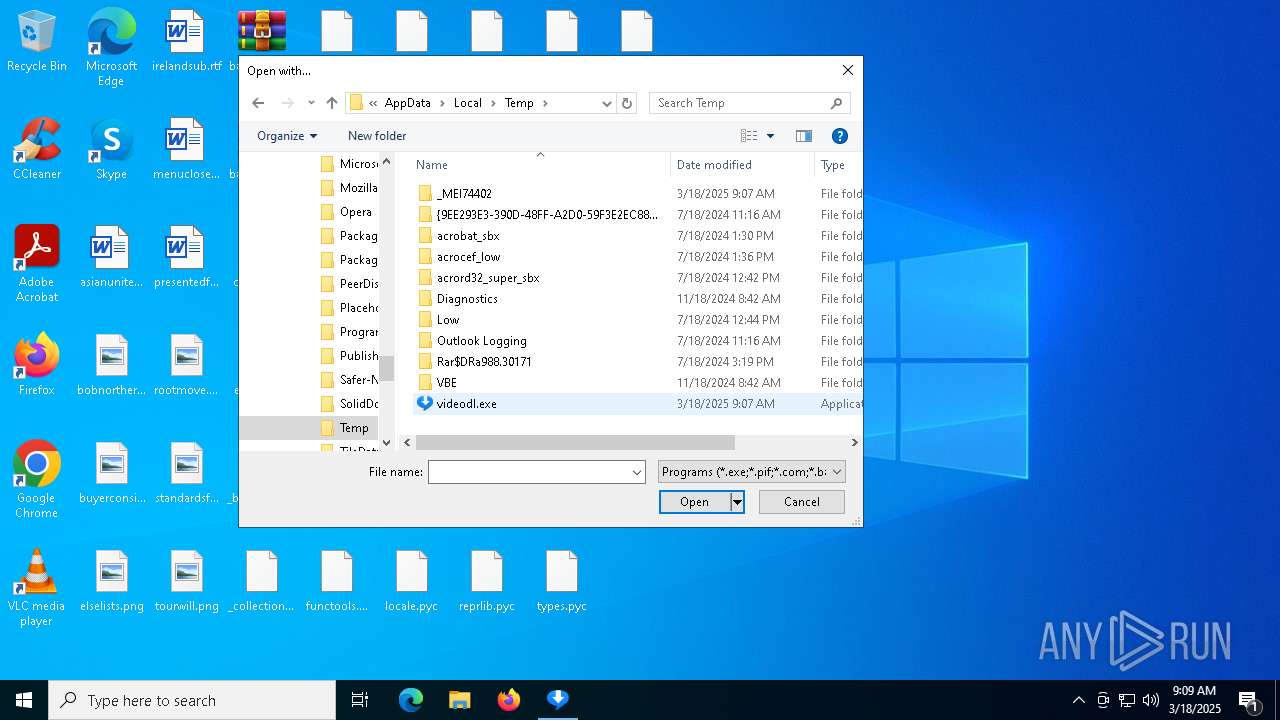
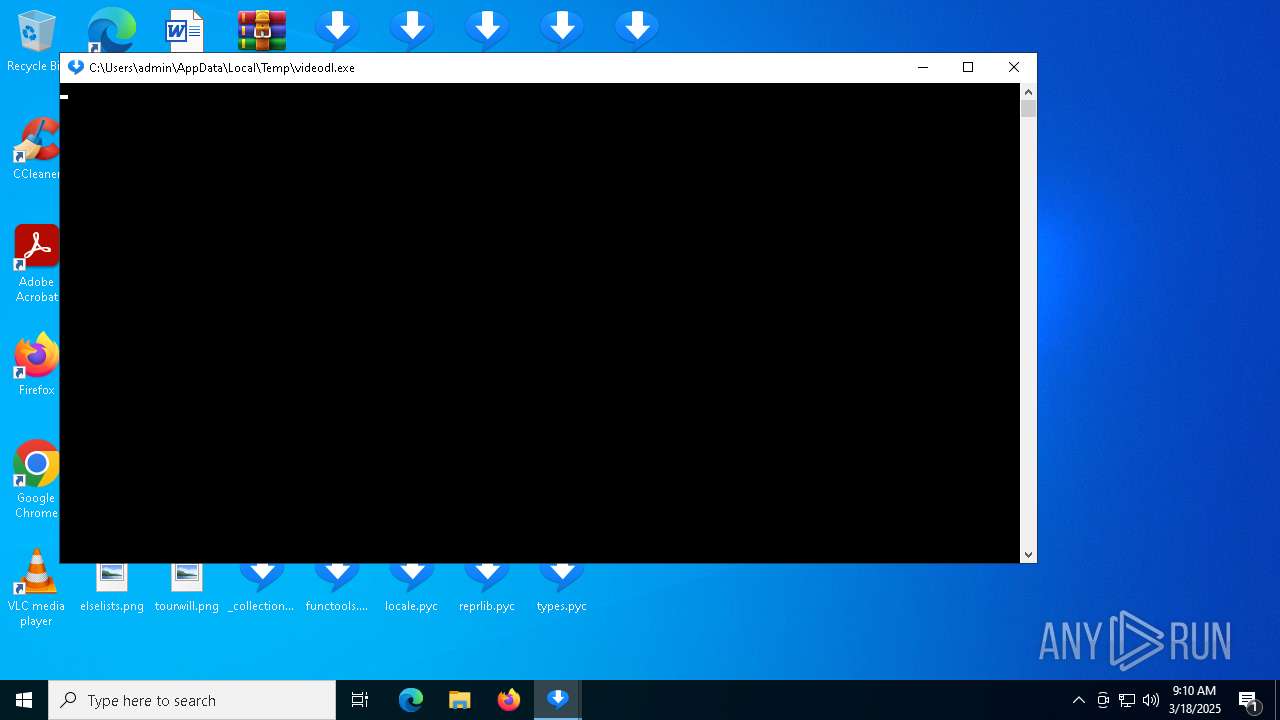
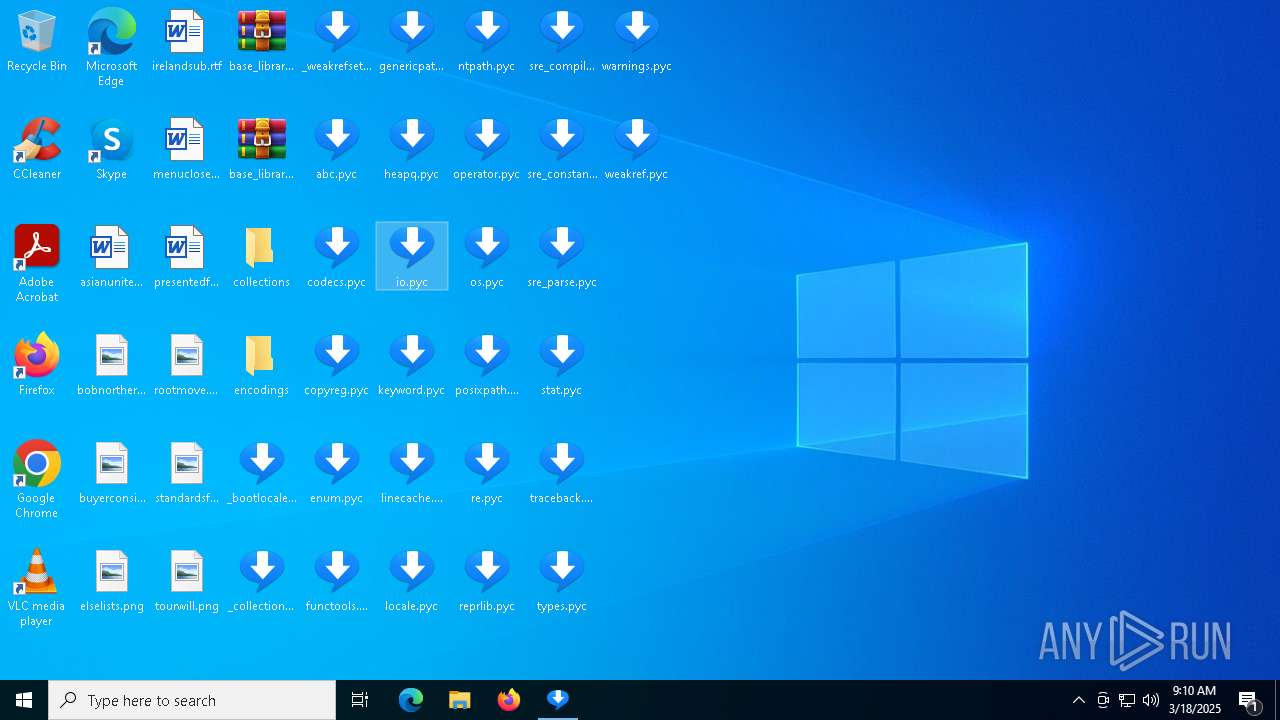
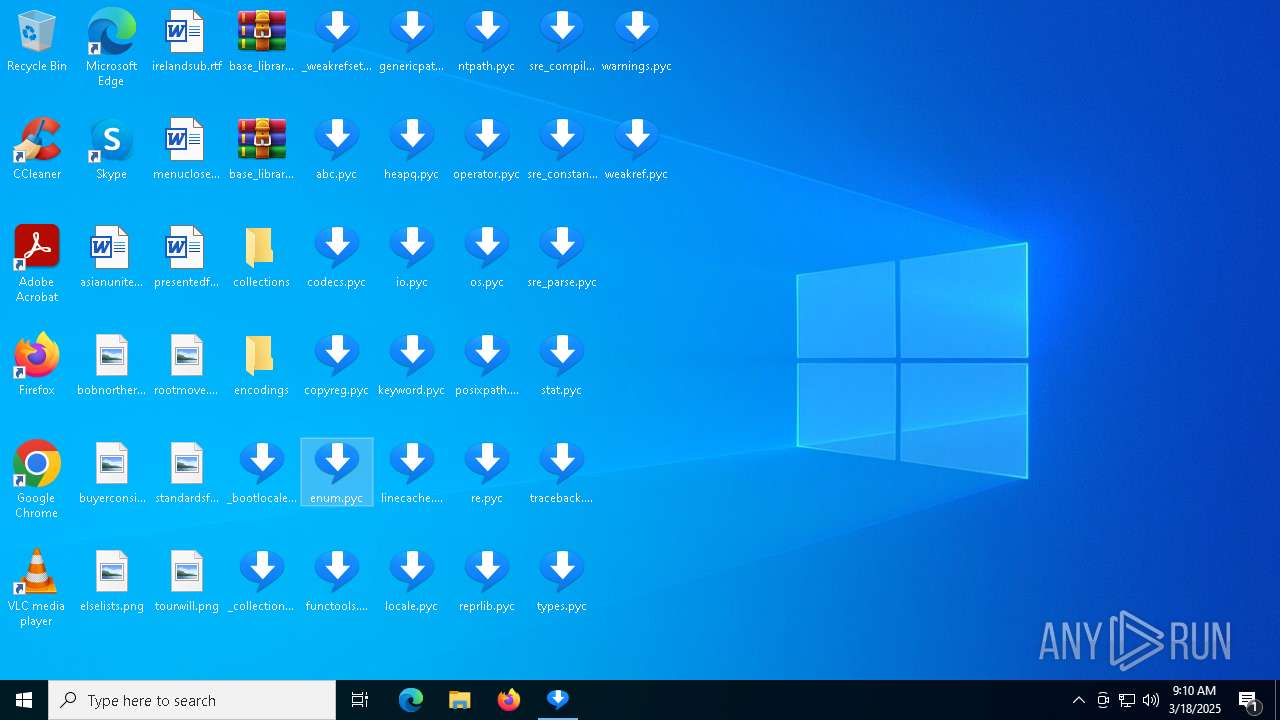
Create files in a temporary directory
- videodl.exe (PID: 7440)
- videodl.exe (PID: 7536)
- videodl.exe (PID: 8160)
- videodl.exe (PID: 6800)
- videodl.exe (PID: 7380)
- videodl.exe (PID: 7292)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 3364)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 4056)
- videodl.exe (PID: 2896)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 1128)
- videodl.exe (PID: 856)
- videodl.exe (PID: 7356)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 7456)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 6752)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 968)
- videodl.exe (PID: 7500)
- videodl.exe (PID: 7820)
- videodl.exe (PID: 6108)
- videodl.exe (PID: 7136)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 3028)
- videodl.exe (PID: 5812)
- videodl.exe (PID: 7520)
- videodl.exe (PID: 6744)
Reads the machine GUID from the registry
- videodl.exe (PID: 7536)
- videodl.exe (PID: 3364)
- videodl.exe (PID: 4056)
- videodl.exe (PID: 2896)
- videodl.exe (PID: 1128)
- videodl.exe (PID: 7456)
- videodl.exe (PID: 6752)
- videodl.exe (PID: 968)
- videodl.exe (PID: 900)
- videodl.exe (PID: 7820)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 3028)
- videodl.exe (PID: 7520)
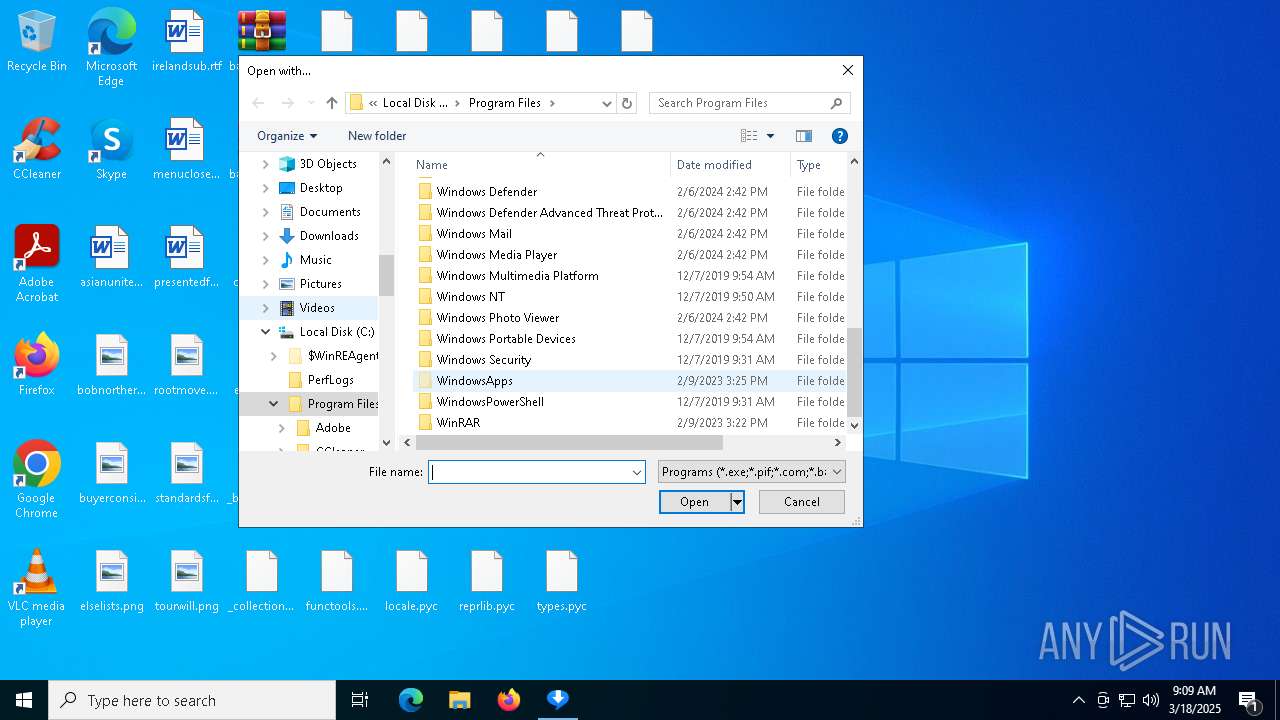
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 6564)
- BackgroundTransferHost.exe (PID: 1244)
- BackgroundTransferHost.exe (PID: 4000)
- BackgroundTransferHost.exe (PID: 5972)
- BackgroundTransferHost.exe (PID: 672)
- OpenWith.exe (PID: 7916)
- OpenWith.exe (PID: 5200)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 672)
- slui.exe (PID: 7648)
- slui.exe (PID: 6876)
PyInstaller has been detected (YARA)
- videodl.exe (PID: 7440)
- videodl.exe (PID: 7536)
- videodl.exe (PID: 856)
Checks operating system version
- videodl.exe (PID: 7536)
- videodl.exe (PID: 6800)
- videodl.exe (PID: 7292)
- videodl.exe (PID: 3364)
- videodl.exe (PID: 4056)
- videodl.exe (PID: 2896)
- videodl.exe (PID: 1128)
- videodl.exe (PID: 7356)
- videodl.exe (PID: 7456)
- videodl.exe (PID: 6752)
- videodl.exe (PID: 968)
- videodl.exe (PID: 900)
- videodl.exe (PID: 7820)
- videodl.exe (PID: 7756)
- videodl.exe (PID: 6044)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 3028)
- videodl.exe (PID: 7520)
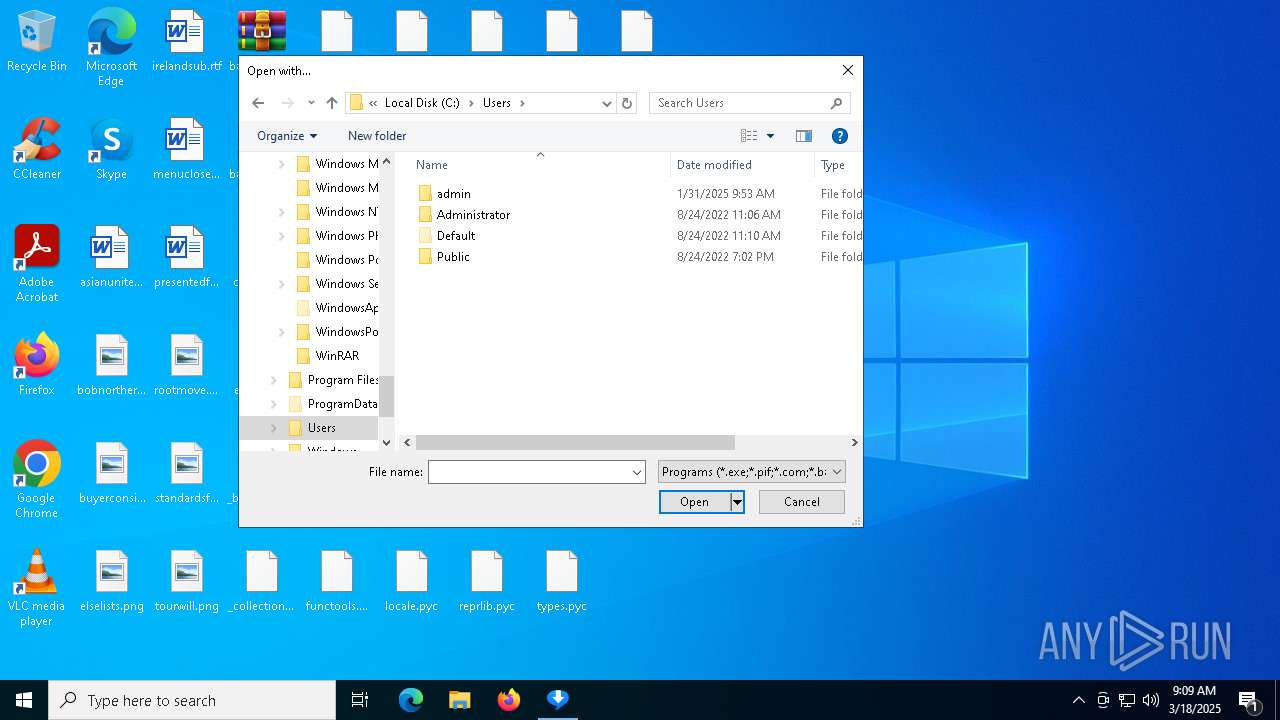
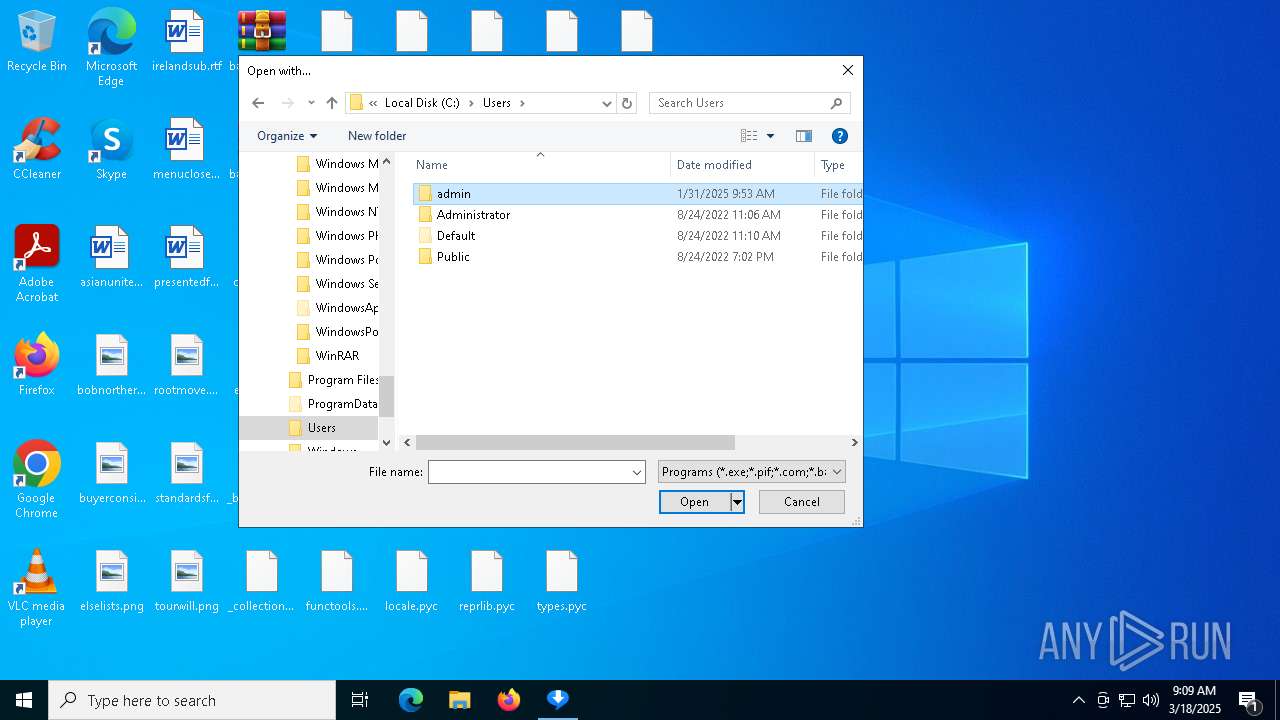
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 672)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 672)
- slui.exe (PID: 6876)
- videodl.exe (PID: 6800)
- videodl.exe (PID: 7292)
- videodl.exe (PID: 3364)
- videodl.exe (PID: 4056)
- videodl.exe (PID: 2896)
- videodl.exe (PID: 1128)
- videodl.exe (PID: 968)
- videodl.exe (PID: 900)
- videodl.exe (PID: 7820)
- videodl.exe (PID: 7756)
- videodl.exe (PID: 6044)
- videodl.exe (PID: 7520)
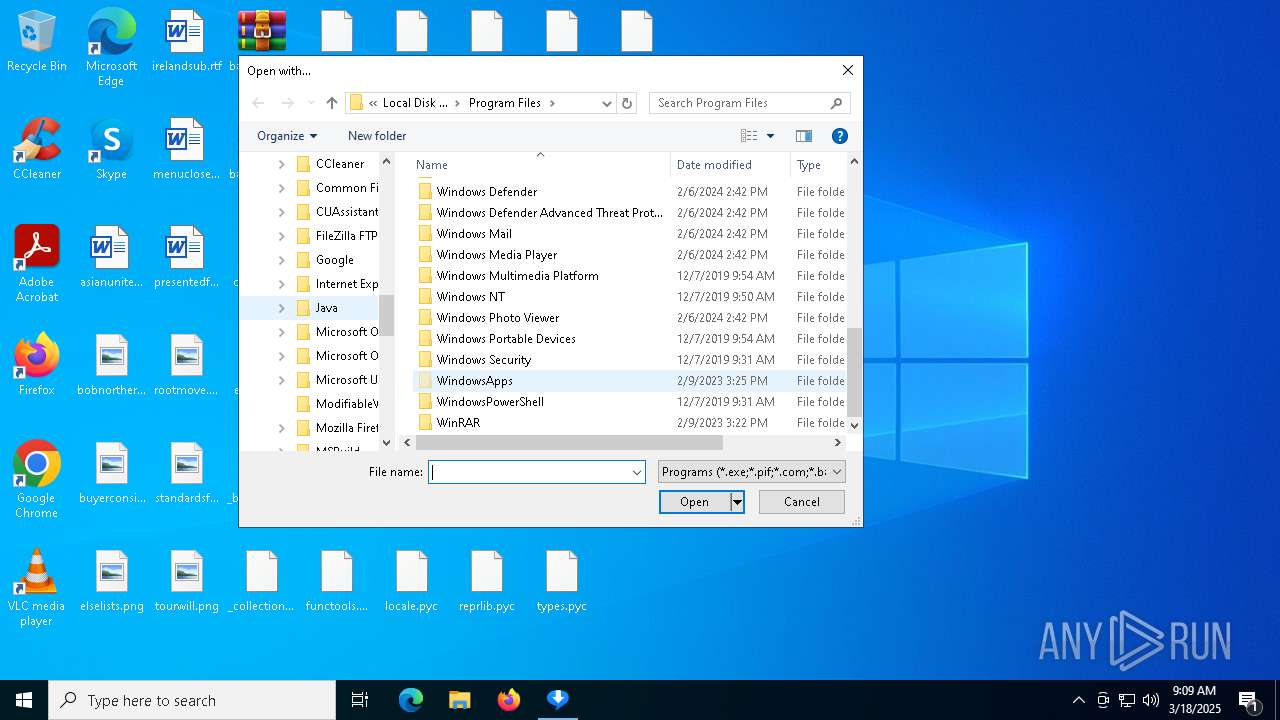
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7916)
- OpenWith.exe (PID: 7464)
- OpenWith.exe (PID: 5200)
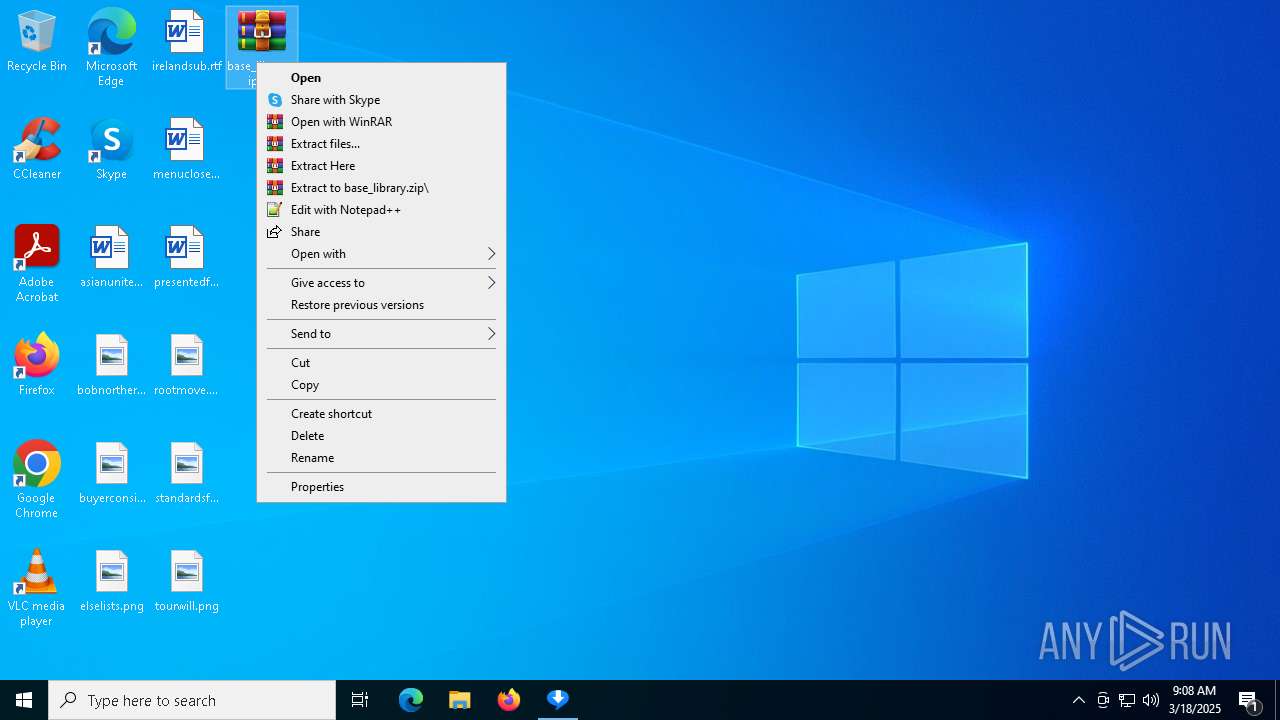
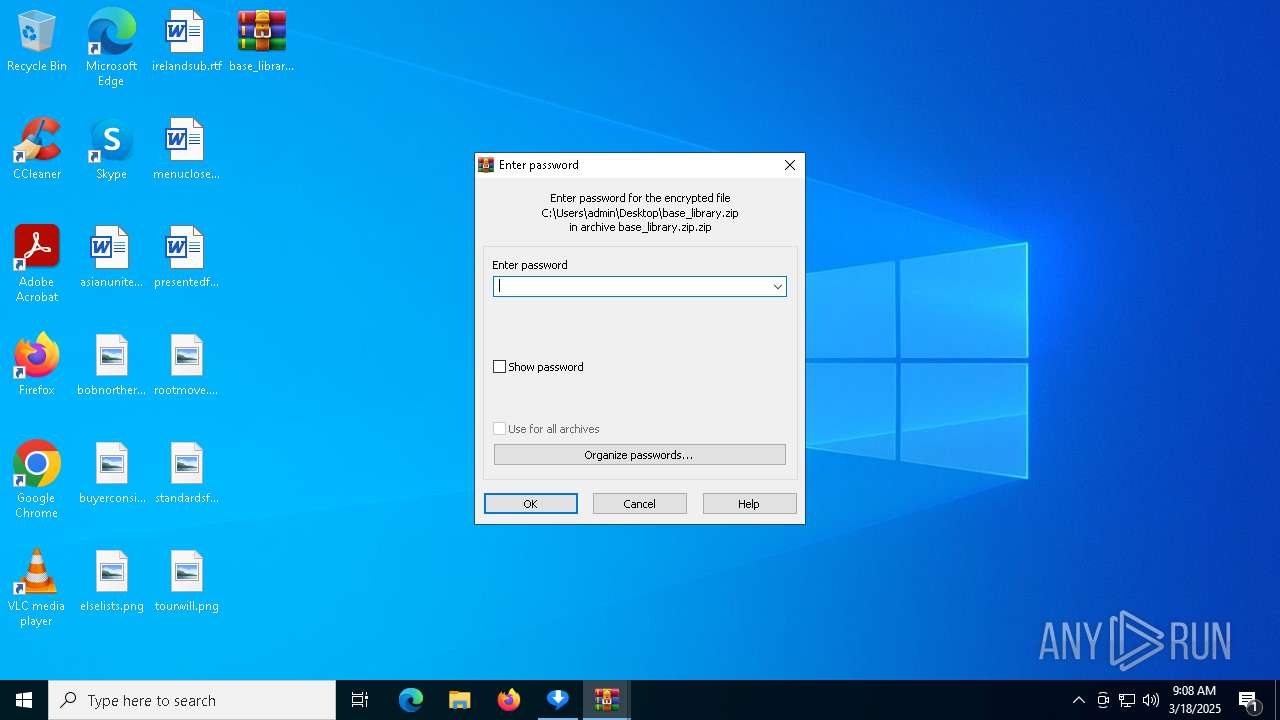
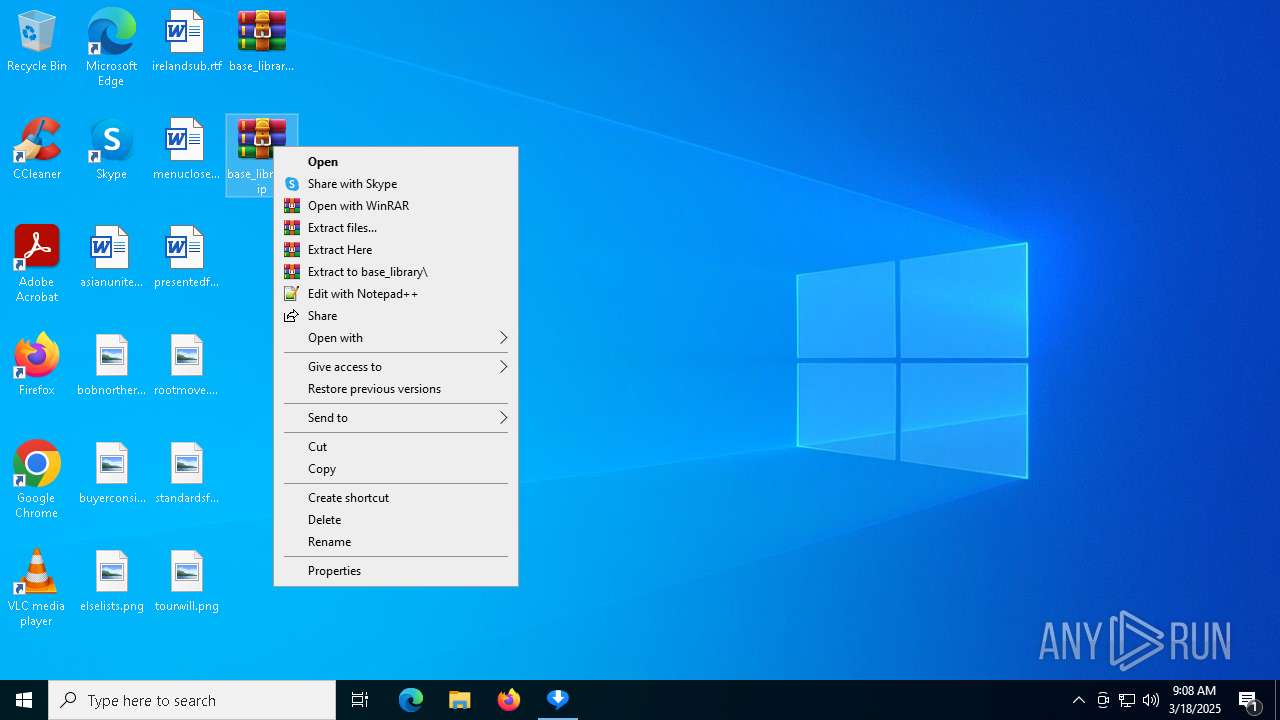
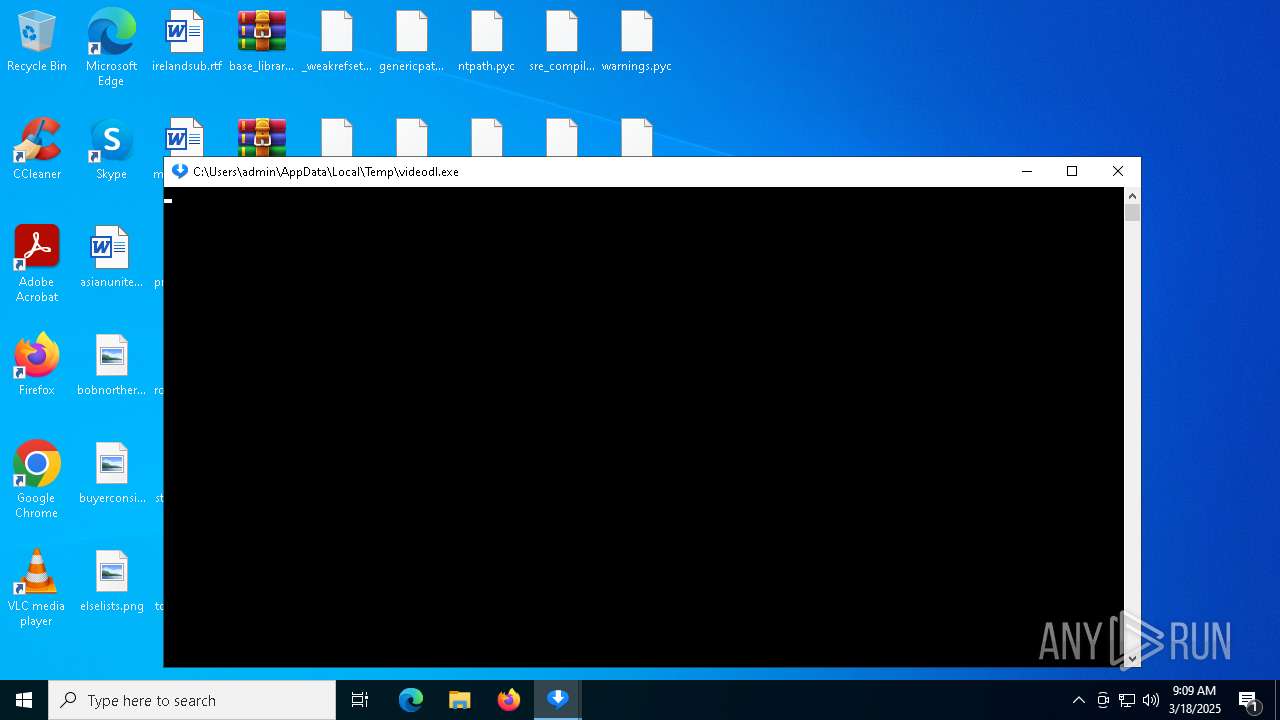
Manual execution by a user
- WinRAR.exe (PID: 5360)
- WinRAR.exe (PID: 4464)
- videodl.exe (PID: 6416)
- videodl.exe (PID: 6944)
- videodl.exe (PID: 6744)
- videodl.exe (PID: 7988)
- videodl.exe (PID: 6240)
- videodl.exe (PID: 856)
- videodl.exe (PID: 5176)
- videodl.exe (PID: 7208)
- videodl.exe (PID: 7500)
- videodl.exe (PID: 6108)
- videodl.exe (PID: 7136)
- videodl.exe (PID: 2772)
- videodl.exe (PID: 5964)
- videodl.exe (PID: 4016)
- videodl.exe (PID: 5812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:10:10 00:32:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 156672 |
| InitializedDataSize: | 108032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xab90 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 2024.10.7.0 |
| ProductVersionNumber: | 2024.10.7.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | RealNetworks, Inc. |
| FileDescription: | Video Downloader |
| InternalName: | VideoDL |
| ProductName: | RealNetworks Video Downloader |
| OriginalFileName: | VideoDL.exe |
| LegalCopyright: | Copyright © RealNetworks, Inc. 1995-2023 |
| FileVersion: | 2024.10.07.0 |
| ProductVersion: | 2024.10.07.0 |
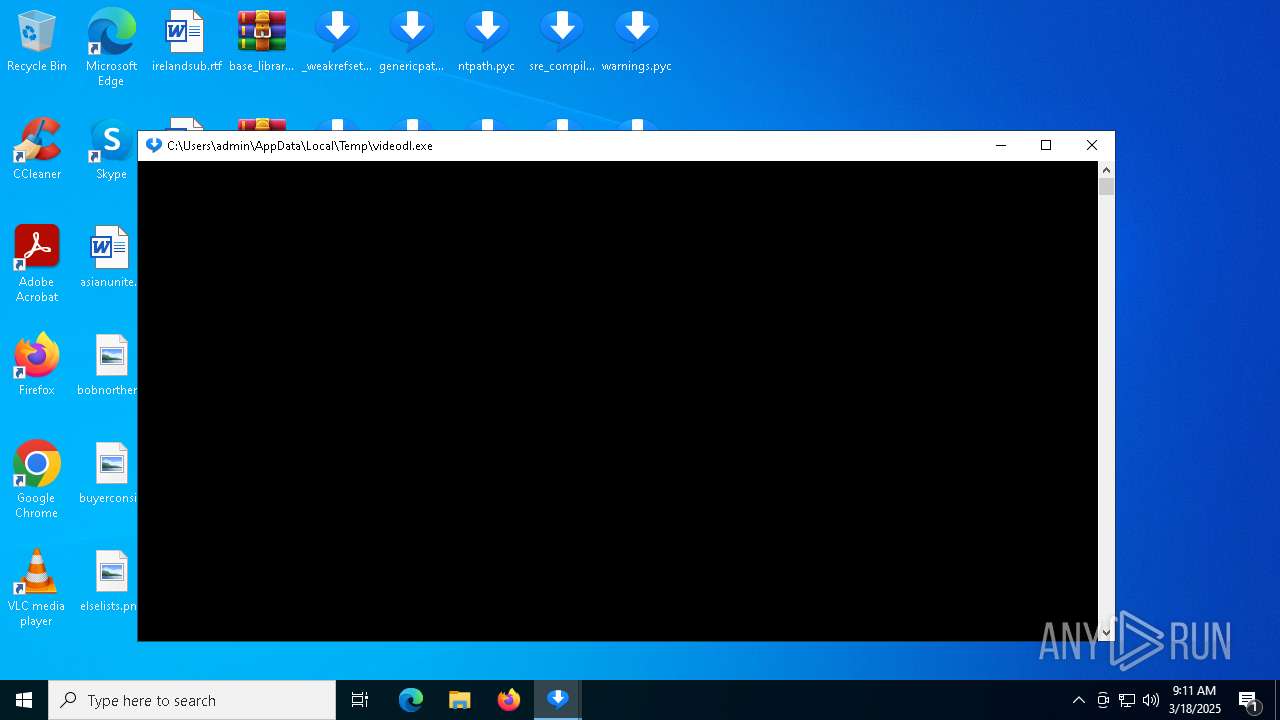
Total processes
262
Monitored processes
122
Malicious processes
3
Suspicious processes
35
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\SysWOW64\cmd.exe | — | videodl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\SysWOW64\cmd.exe | — | videodl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | videodl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
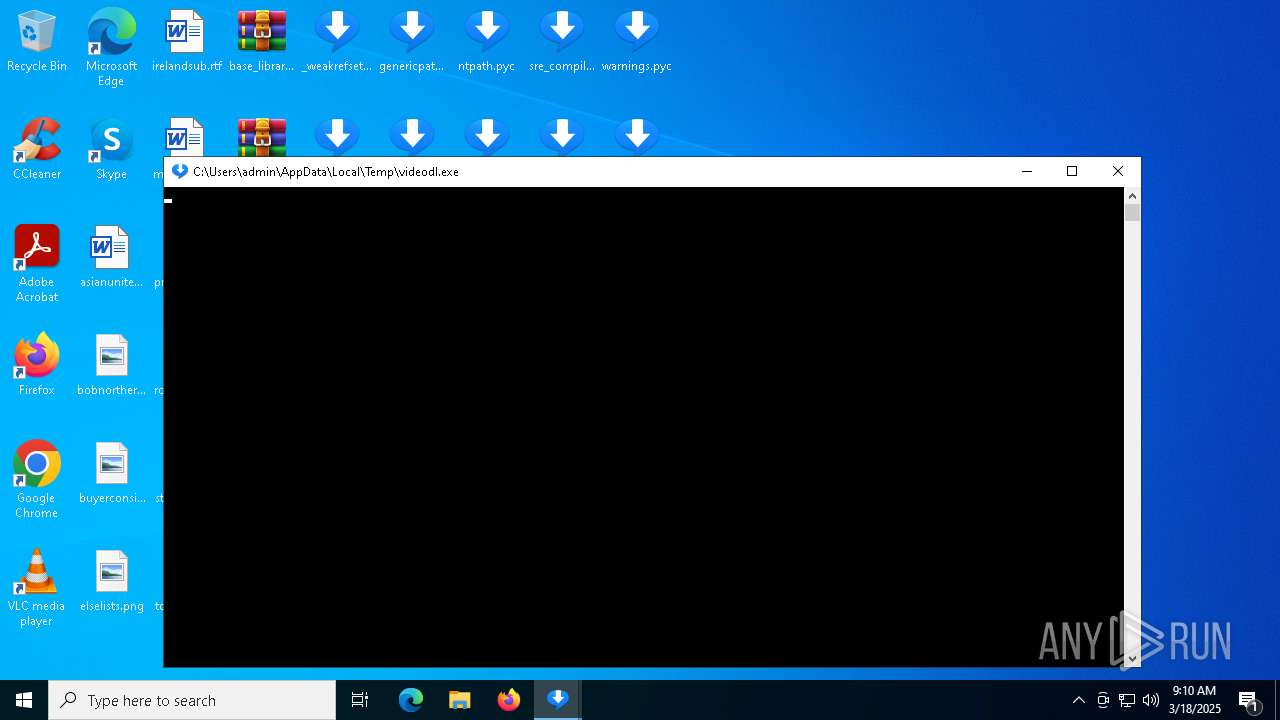
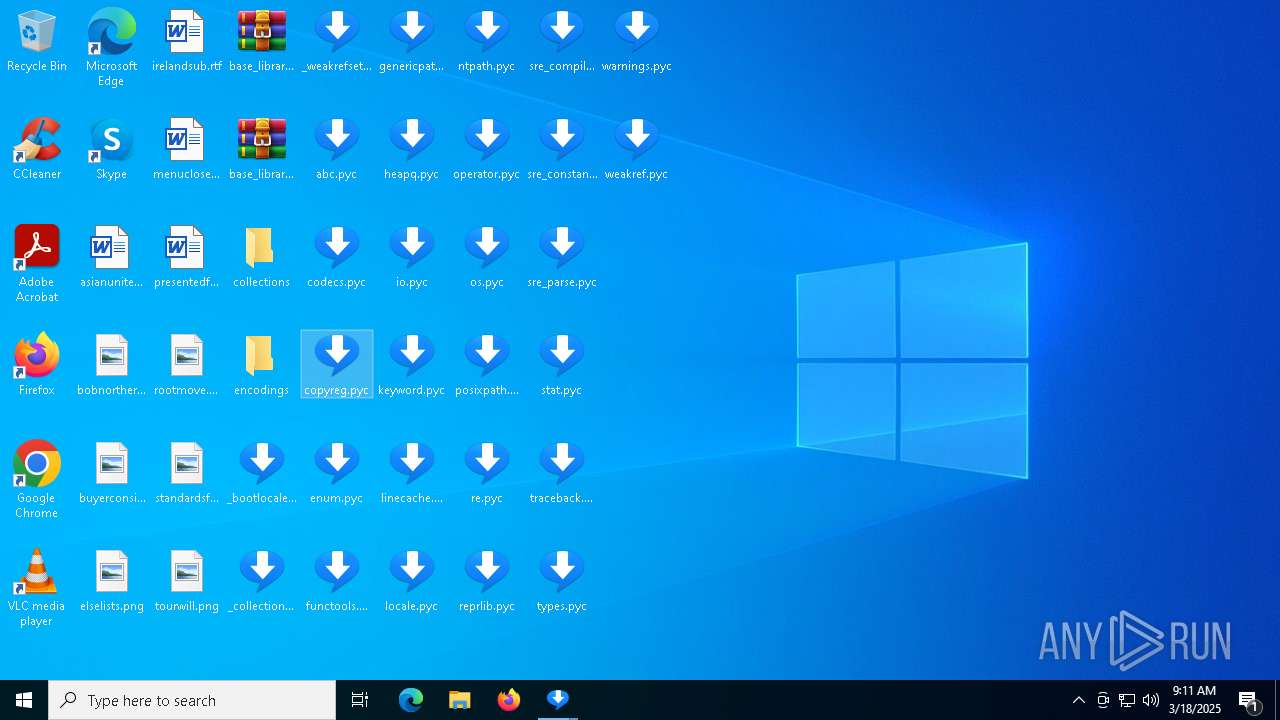
| 856 | "C:\Users\admin\AppData\Local\Temp\videodl.exe" "C:\Users\admin\Desktop\_bootlocale.pyc" | C:\Users\admin\AppData\Local\Temp\videodl.exe | explorer.exe | ||||||||||||
User: admin Company: RealNetworks, Inc. Integrity Level: MEDIUM Description: Video Downloader Version: 2024.10.07.0 Modules
| |||||||||||||||
| 900 | "C:\Users\admin\AppData\Local\Temp\videodl.exe" "C:\Users\admin\Desktop\copyreg.pyc" | C:\Users\admin\AppData\Local\Temp\videodl.exe | — | videodl.exe | |||||||||||
User: admin Company: RealNetworks, Inc. Integrity Level: MEDIUM Description: Video Downloader Exit code: 1 Version: 2024.10.07.0 Modules
| |||||||||||||||
| 924 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | videodl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\SysWOW64\cmd.exe | — | videodl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "C:\Users\admin\AppData\Local\Temp\videodl.exe" "C:\Users\admin\Desktop\warnings.pyc" | C:\Users\admin\AppData\Local\Temp\videodl.exe | — | videodl.exe | |||||||||||
User: admin Company: RealNetworks, Inc. Integrity Level: MEDIUM Description: Video Downloader Exit code: 1 Version: 2024.10.07.0 Modules
| |||||||||||||||
| 1128 | "C:\Users\admin\AppData\Local\Temp\videodl.exe" "C:\Users\admin\Desktop\enum.pyc" | C:\Users\admin\AppData\Local\Temp\videodl.exe | — | videodl.exe | |||||||||||
User: admin Company: RealNetworks, Inc. Integrity Level: MEDIUM Description: Video Downloader Exit code: 1 Version: 2024.10.07.0 Modules
| |||||||||||||||
Total events
17 703
Read events
17 473
Write events
223
Delete events
7
Modification events
| (PID) Process: | (5972) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5972) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5972) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (672) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (672) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (672) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6564) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6564) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6564) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1244) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
1 134
Suspicious files
177
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Cipher\_raw_cbc.pyd | executable | |
MD5:D942DB2187DBDDF6A691AF5A11EEA175 | SHA256:ECDF4E6C42CFA892E2D38E6D75CF95AC02136938DCC13858B14E688B0402B67E | |||
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Hash\_BLAKE2b.pyd | executable | |
MD5:E40EC56F8C44E6EC4D92B1F4AAC19A33 | SHA256:F0450C512BAB21B18EA47CE4586E19FA86D0DACB402A10D1006368CC2179CD90 | |||
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Cipher\_raw_cfb.pyd | executable | |
MD5:5F15FC832D76FE0704FAEB0A73E0AFD0 | SHA256:617E987BAA16BC7E669325C1AEFA68A17F7EDF016E1D610CFD07060A6D392D77 | |||
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Cipher\_raw_blowfish.pyd | executable | |
MD5:A3C1E2C641328F1B2936C86EFA4C2489 | SHA256:3E926770083D26B70A30B58D63EB6AC444B3F56628D2B3277C96139D781CCB32 | |||
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Cipher\_ARC4.pyd | executable | |
MD5:9E5A4C37ADDB7102F0BDA27A7F5BDD84 | SHA256:244CA3F07C8CCF251A3F0361E78F4454EFC82B58038A56F1B61F06539453221E | |||
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Cipher\_pkcs1_decode.pyd | executable | |
MD5:5652CD153BDF6E98542CCD5EA14DDBAC | SHA256:FA6C9EB27FD3517734FC84994DB64C067B04DD6DA6F43AD7533B51C9E47ED416 | |||
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Cipher\_Salsa20.pyd | executable | |
MD5:B655558CE6D1FF74A2210D59B2F00328 | SHA256:73DF3F11E522059134CD951CDFE5CF9FE890FBB487822BD8A498E72990BA860B | |||
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Cipher\_raw_cast.pyd | executable | |
MD5:2B9267062BE4B668937C921EDFBAF340 | SHA256:4EEF94469CE6D2CA28CD5D6252AFB50FCF0C5295CCB833BB41B5D11784C0CFC0 | |||
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Cipher\_raw_aesni.pyd | executable | |
MD5:D10B71D8D4044977C865DA1A4BD1AA35 | SHA256:BAB315B83DC13F02681B131531D3480B8315D6C1097D1005E6BB918CB5E6FD8C | |||
| 7440 | videodl.exe | C:\Users\admin\AppData\Local\Temp\_MEI74402\Cryptodome\Cipher\_chacha20.pyd | executable | |
MD5:38628F0BDFC5263719B95B1BE1A64A9E | SHA256:79BDB43EE852F052309D408FE4B893E3F3F42D14B94B35F5516F47A6C519367D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7772 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7148 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7148 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
672 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8176 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7772 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |