| File name: | DZClient.exe |
| Full analysis: | https://app.any.run/tasks/ab9e7228-5168-4dbd-a45a-11b3f340a1bc |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2020, 22:01:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 82598FE1EDE03223D9AFDA2EF7B06C82 |
| SHA1: | D1AF1731F4B5626DEB4DD375394A2974D450EE1D |
| SHA256: | 8863EC0489CCABC9C10D204F05B237CA866D96F70FCEF8BC04585708AA464D91 |
| SSDEEP: | 98304:h3GVvzSrBYKc4ZCSOpl43/F/5OcFTdOZgXWo8YI7pQq61LXn:lG1zSrOjYCqWydOhDYI7pQ |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 1396)
- DZClient.exe (PID: 1012)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 1352)
SUSPICIOUS
Low-level read access rights to disk partition
- DZClient.exe (PID: 1012)
- DZClient.exe (PID: 3240)
Starts itself from another location
- DZClient.exe (PID: 3240)
Reads Internet Cache Settings
- DZClient.exe (PID: 3240)
- DZClient.exe (PID: 1012)
Executable content was dropped or overwritten
- DZClient.exe (PID: 1012)
- DZClient.exe (PID: 3240)
Creates files in the program directory
- DZClient.exe (PID: 3240)
- DZClient.exe (PID: 1012)
Starts CMD.EXE for commands execution
- DZClient.exe (PID: 1012)
Creates COM task schedule object
- regsvr32.exe (PID: 1396)
Reads internet explorer settings
- DZClient.exe (PID: 1012)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:02 11:17:53+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 5615616 |
| InitializedDataSize: | 77824 |
| UninitializedDataSize: | 8962048 |
| EntryPoint: | 0xde6c00 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
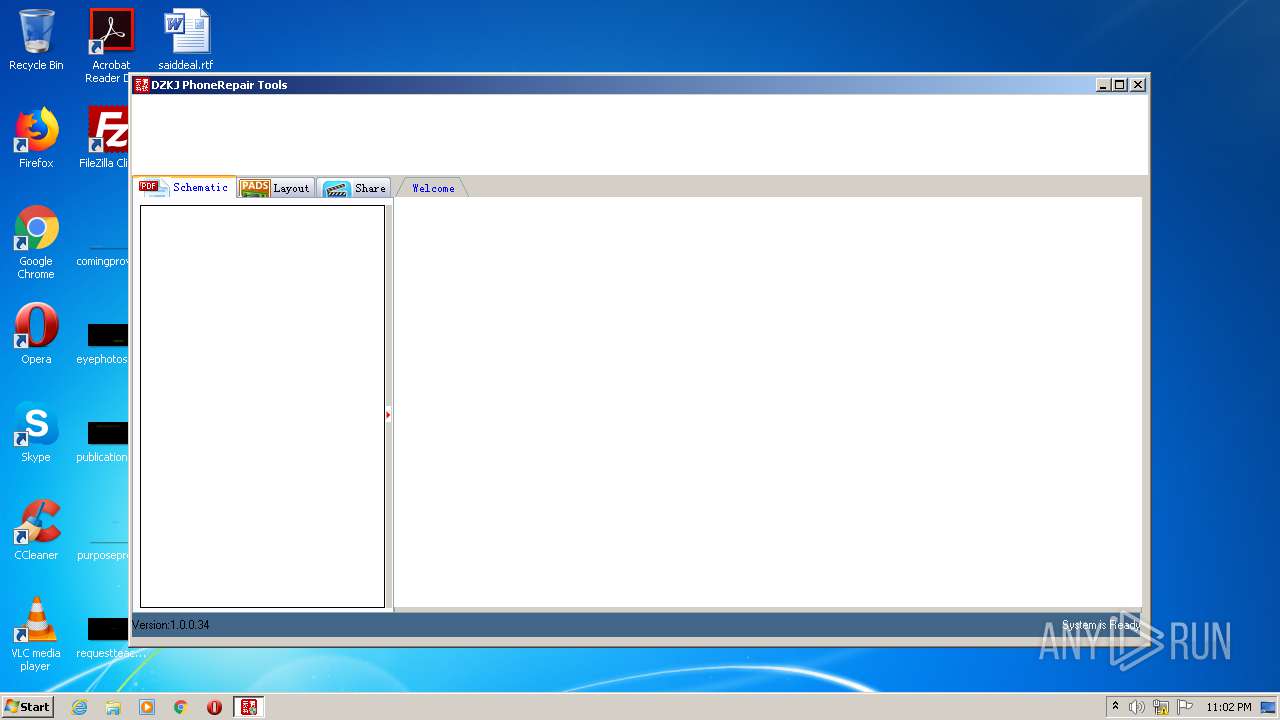
| FileVersionNumber: | 1.0.0.34 |
| ProductVersionNumber: | 1.0.0.34 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.34 |
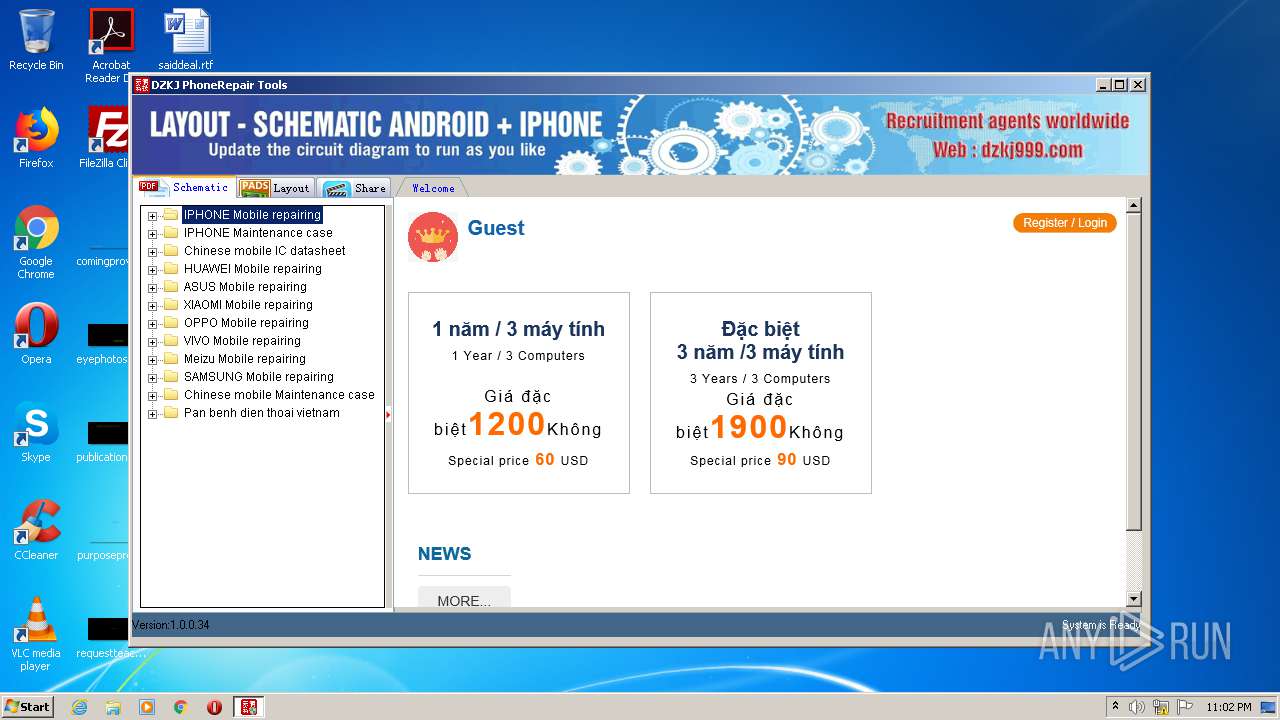
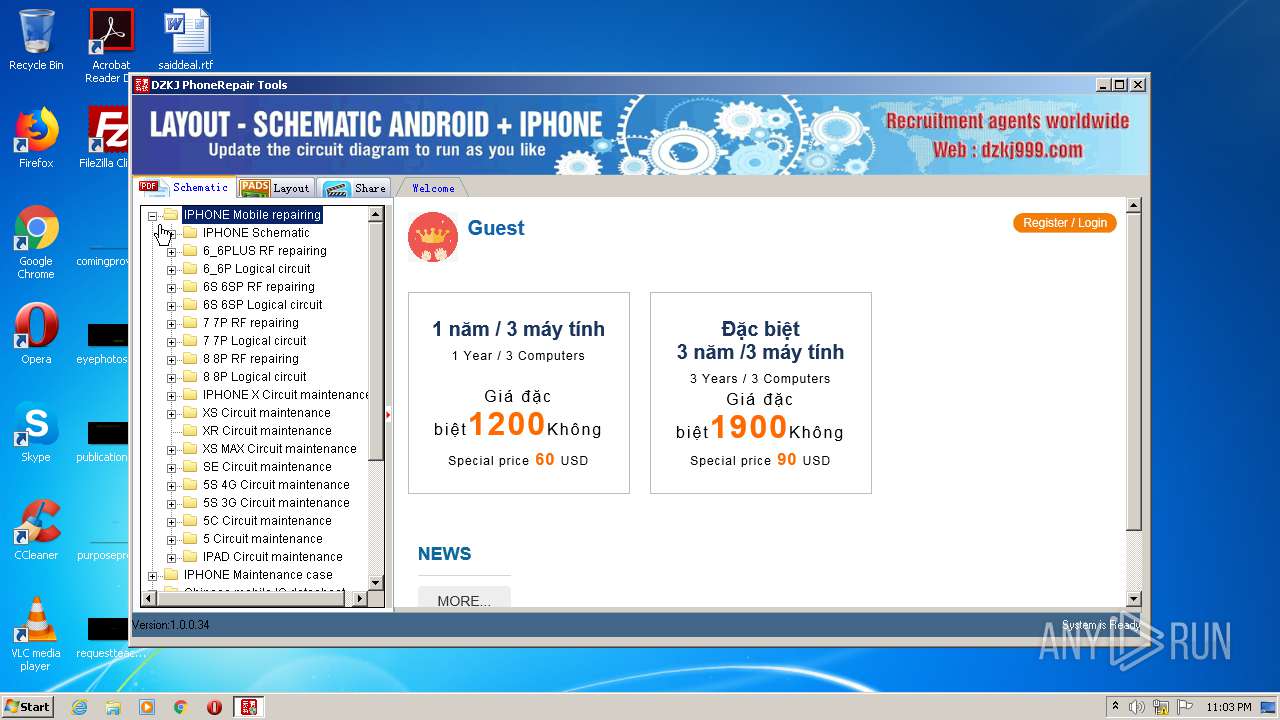
| FileDescription: | 东震科技电子图 |
| ProductName: | 东震科技电子图 |
| ProductVersion: | 1.0.0.34 |
| CompanyName: | DZKJ PhoneRepair Tools |
| LegalCopyright: | DZKJ PhoneRepair Tools |
| Comments: | DZKJ PhoneRepair Tools |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Aug-2020 09:17:53 |
| Detected languages: |
|
| FileVersion: | 1.0.0.34 |
| FileDescription: | 东震科技电子图 |
| ProductName: | 东震科技电子图 |
| ProductVersion: | 1.0.0.34 |
| CompanyName: | DZKJ PhoneRepair Tools |
| LegalCopyright: | DZKJ PhoneRepair Tools |
| Comments: | DZKJ PhoneRepair Tools |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 02-Aug-2020 09:17:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0088C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0088D000 | 0x0055B000 | 0x0055A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99996 |
.rsrc | 0x00DE8000 | 0x00013000 | 0x00012600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.83967 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02094 | 697 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 2.389 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.88744 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
5 | 7.29683 | 308 | Latin 1 / Western European | Italian - Italy | RT_CURSOR |
6 | 7.2916 | 308 | Latin 1 / Western European | Italian - Italy | RT_CURSOR |
7 | 7.32003 | 308 | Latin 1 / Western European | Italian - Italy | RT_CURSOR |
8 | 7.31962 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
9 | 7.35626 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
127 | 3.58496 | 12 | Latin 1 / Western European | Chinese - PRC | RT_MENU |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSIMG32.dll |
MSVFW32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Program Files\dz\DZClient.exe" | C:\Program Files\dz\DZClient.exe | DZClient.exe | ||||||||||||
User: admin Company: DZKJ PhoneRepair Tools Integrity Level: HIGH Description: 东震科技电子图 Exit code: 0 Version: 1.0.0.34 Modules
| |||||||||||||||
| 1352 | cmd.exe /c regsvr32 /s C:\Users\admin\AppData\Local\Temp\PDF.dll | C:\Windows\system32\cmd.exe | — | DZClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1396 | regsvr32 /s C:\Users\admin\AppData\Local\Temp\PDF.dll | C:\Windows\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\AppData\Local\Temp\DZClient.exe" | C:\Users\admin\AppData\Local\Temp\DZClient.exe | — | explorer.exe | |||||||||||
User: admin Company: DZKJ PhoneRepair Tools Integrity Level: MEDIUM Description: 东震科技电子图 Exit code: 3221226540 Version: 1.0.0.34 Modules
| |||||||||||||||
| 3240 | "C:\Users\admin\AppData\Local\Temp\DZClient.exe" | C:\Users\admin\AppData\Local\Temp\DZClient.exe | explorer.exe | ||||||||||||
User: admin Company: DZKJ PhoneRepair Tools Integrity Level: HIGH Description: 东震科技电子图 Exit code: 0 Version: 1.0.0.34 Modules
| |||||||||||||||
Total events
329
Read events
282
Write events
47
Delete events
0
Modification events
| (PID) Process: | (3240) DZClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3240) DZClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3240) DZClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3240) DZClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3240) DZClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3240) DZClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3240) DZClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3240) DZClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 74 | |||
| (PID) Process: | (1396) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{D519DF02-6454-416B-9B0C-8B8792ACBC2D}\1.0 |
| Operation: | write | Name: | (default) |
Value: SmartPDFLib | |||
| (PID) Process: | (1396) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{D519DF02-6454-416B-9B0C-8B8792ACBC2D}\1.0\FLAGS |
| Operation: | write | Name: | (default) |
Value: 2 | |||
Executable files
2
Suspicious files
3
Text files
16
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3240 | DZClient.exe | C:\Program Files\dz\DZClient.exe | executable | |
MD5:— | SHA256:— | |||
| 3240 | DZClient.exe | C:\Users\admin\Desktop\DZKJ Tools.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1012 | DZClient.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\top[1].gif | image | |
MD5:— | SHA256:— | |||
| 1012 | DZClient.exe | C:\Program Files\dz\down\pz\img\top.gif | image | |
MD5:— | SHA256:— | |||
| 1012 | DZClient.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\top[1].gif | image | |
MD5:— | SHA256:— | |||
| 1012 | DZClient.exe | C:\Users\admin\AppData\Local\Temp\PDF.dll | executable | |
MD5:— | SHA256:— | |||
| 1012 | DZClient.exe | C:\Program Files\dz\down\pz\pdf.xml | binary | |
MD5:— | SHA256:— | |||
| 1012 | DZClient.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\pdf[1].ini | text | |
MD5:— | SHA256:— | |||
| 1012 | DZClient.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\84[1].htm | html | |
MD5:— | SHA256:— | |||
| 1012 | DZClient.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\banner[1].htm | html | |
MD5:ACB8E8127FE99D33822896F8FF2BAA72 | SHA256:CA04643380643B3F9482E295A31AAAA380527E489611BE9DBB164BEEE3DE9890 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
7
DNS requests
5
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1012 | DZClient.exe | GET | 200 | 45.32.234.187:80 | http://www.dzkj16888.com/main/gg/84/img/top.gif | NL | image | 53.0 Kb | suspicious |
1012 | DZClient.exe | GET | 200 | 45.32.234.187:80 | http://www.dzkj16888.com/main/gg/84/img/top.gif | NL | image | 53.6 Kb | suspicious |
1012 | DZClient.exe | GET | 200 | 45.32.234.187:80 | http://www.dzkj16888.com/main/84.php?ver=34 | NL | html | 4.80 Kb | suspicious |
1012 | DZClient.exe | GET | 200 | 45.32.234.187:80 | http://down.dzkj16888.com/pz/pdf.ini | NL | text | 208 Kb | suspicious |
1012 | DZClient.exe | GET | 200 | 45.32.234.187:80 | http://www.dzkj16888.com/main/gg/84/banner.php | NL | html | 667 b | suspicious |
3240 | DZClient.exe | POST | 200 | 45.32.234.187:80 | http://www.dzkj16888.com/tg/jh.php | NL | text | 3 b | suspicious |
1012 | DZClient.exe | GET | 302 | 45.32.234.187:80 | http://www.dzkj16888.com/main/ad/banner.php?code=84 | NL | text | 23 b | suspicious |
1012 | DZClient.exe | GET | 200 | 45.32.234.187:80 | http://www.dzkj16888.com/main/gg/84/banner.php | NL | html | 372 b | suspicious |
1012 | DZClient.exe | GET | 302 | 45.32.234.187:80 | http://www.dzkj16888.com/main/ad/main.php?code=84&ver=34 | NL | text | 23 b | suspicious |
1012 | DZClient.exe | GET | 200 | 45.32.234.187:80 | http://www.dzkj16888.com/layui/css/layui.css | NL | text | 12.9 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1012 | DZClient.exe | 45.32.234.187:80 | www.dzkj16888.com | Choopa, LLC | NL | suspicious |
1012 | DZClient.exe | 152.199.19.160:80 | ajax.aspnetcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1012 | DZClient.exe | 150.109.56.118:80 | do.nanzhao.cn | — | US | unknown |
1012 | DZClient.exe | 58.215.157.250:443 | s23.cnzz.com | AS Number for CHINANET jiangsu province backbone | CN | unknown |
3240 | DZClient.exe | 45.32.234.187:80 | www.dzkj16888.com | Choopa, LLC | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dzkj16888.com |
| suspicious |
down.dzkj16888.com |
| suspicious |
ajax.aspnetcdn.com |
| whitelisted |
s23.cnzz.com |
| suspicious |
do.nanzhao.cn |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3240 | DZClient.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
1012 | DZClient.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |