| File name: | svchost.exe |
| Full analysis: | https://app.any.run/tasks/86e0ec64-32a1-4c97-a388-cc91396e5712 |
| Verdict: | Malicious activity |
| Analysis date: | August 27, 2024, 19:20:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 94638684AC85D0ECA576DB1A931AFEBC |
| SHA1: | 88BCC84BB6FA8AF3AF7AB7B07EB9E4ADE33CAEBF |
| SHA256: | 884E9AD0D6AF15061E86589EE986B12DE51069F7E191D9C11AD72E33A8652A79 |
| SSDEEP: | 3072:2mR57bXm8oDg9y5XyV3PJTh1ecaC7i5cVyKGuPTUhkm0+ej3u:tFbXHoDXKPtzejXqVLG/hkmje |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- svchost.exe (PID: 4128)
Executes application which crashes
- svchost.exe (PID: 4128)
The process creates files with name similar to system file names
- WerFault.exe (PID: 6752)
Checks for external IP
- svchost.exe (PID: 2256)
- svchost.exe (PID: 4128)
INFO
Checks supported languages
- svchost.exe (PID: 4128)
Reads the computer name
- svchost.exe (PID: 4128)
Reads Environment values
- svchost.exe (PID: 4128)
Disables trace logs
- svchost.exe (PID: 4128)
Reads the machine GUID from the registry
- svchost.exe (PID: 4128)
Checks proxy server information
- svchost.exe (PID: 4128)
- WerFault.exe (PID: 6752)
Reads the software policy settings
- WerFault.exe (PID: 6752)
Creates files or folders in the user directory
- WerFault.exe (PID: 6752)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5088)
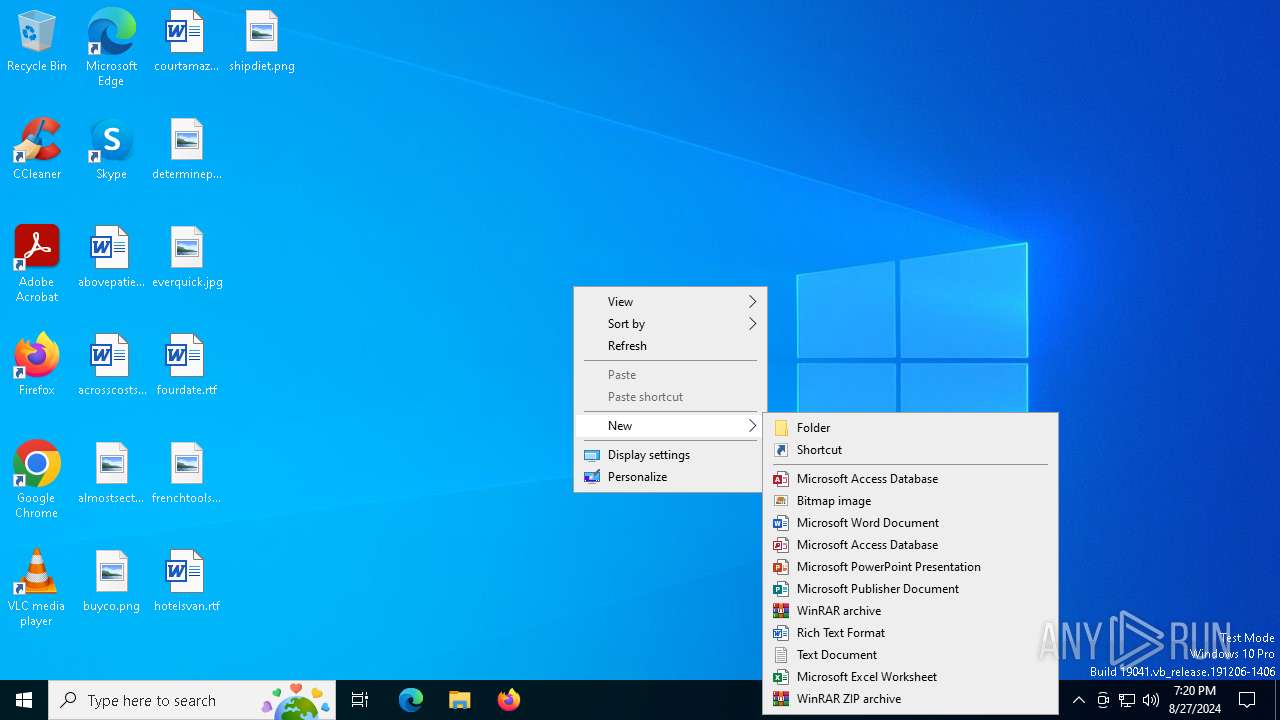
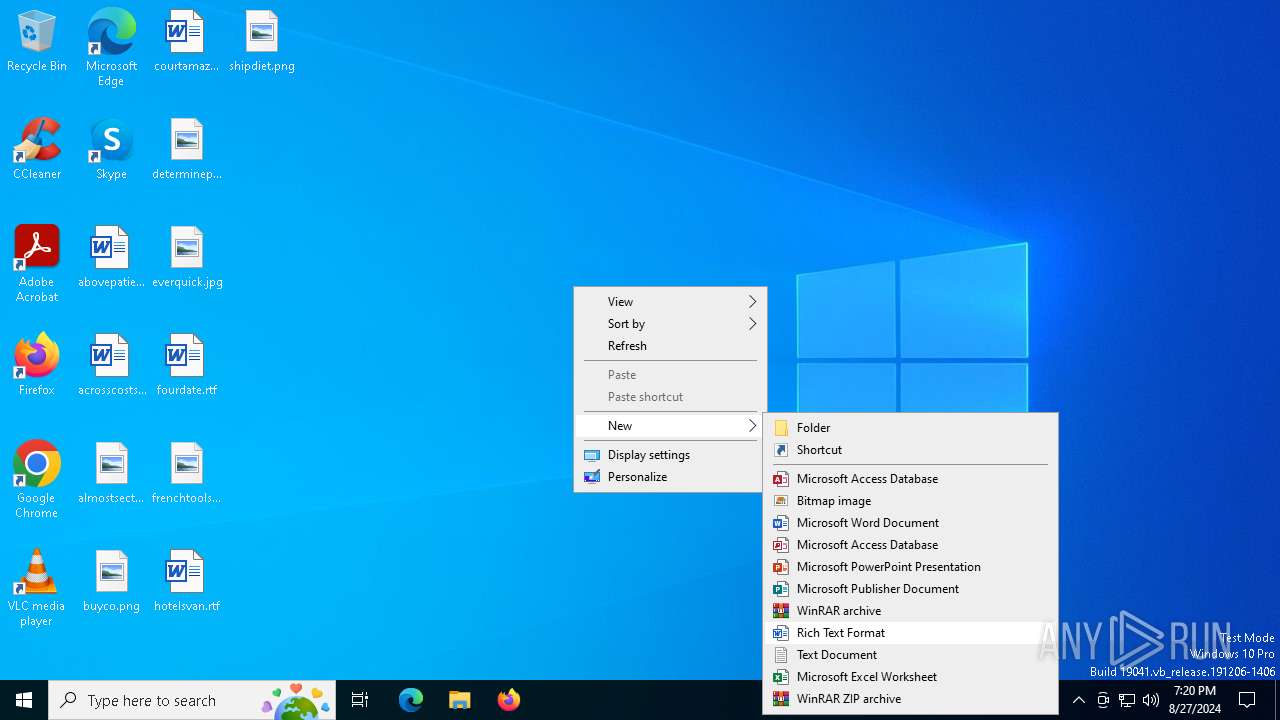
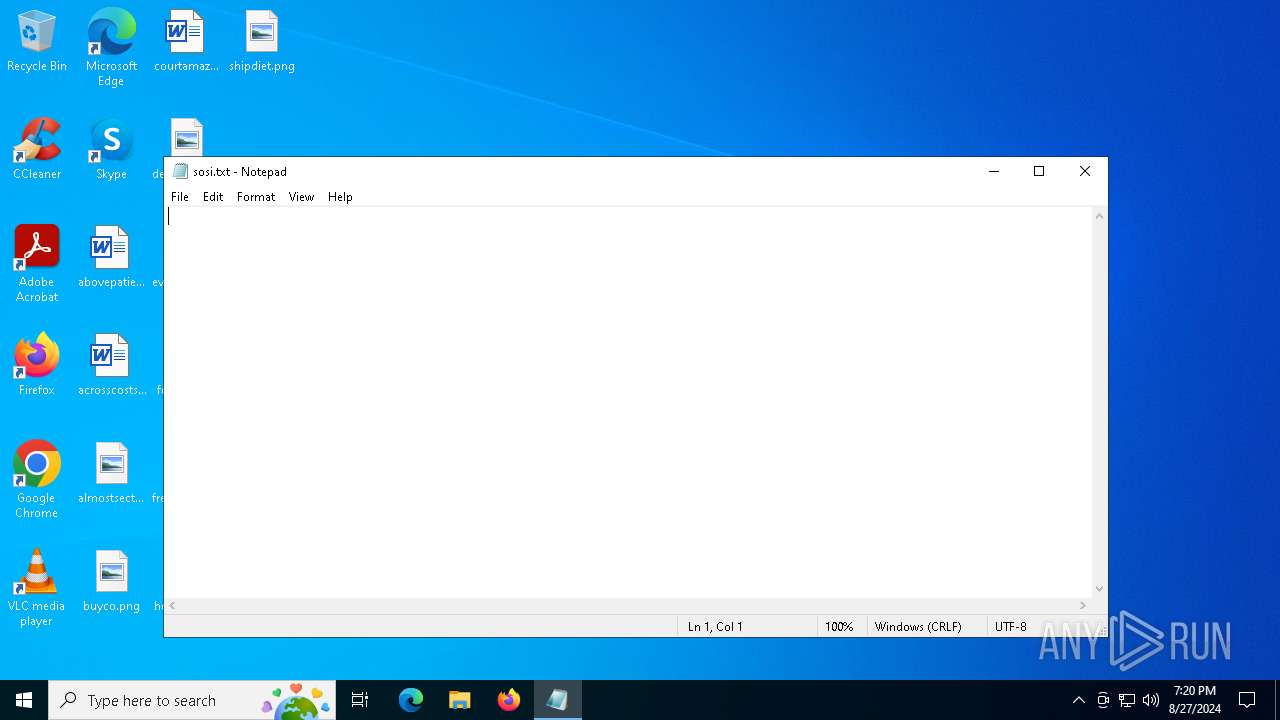
Manual execution by a user
- notepad.exe (PID: 5088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:08:26 09:50:21+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 122880 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ff9e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | svchost.exe |
| LegalCopyright: | |
| OriginalFileName: | svchost.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
132
Monitored processes
4
Malicious processes
0
Suspicious processes
1
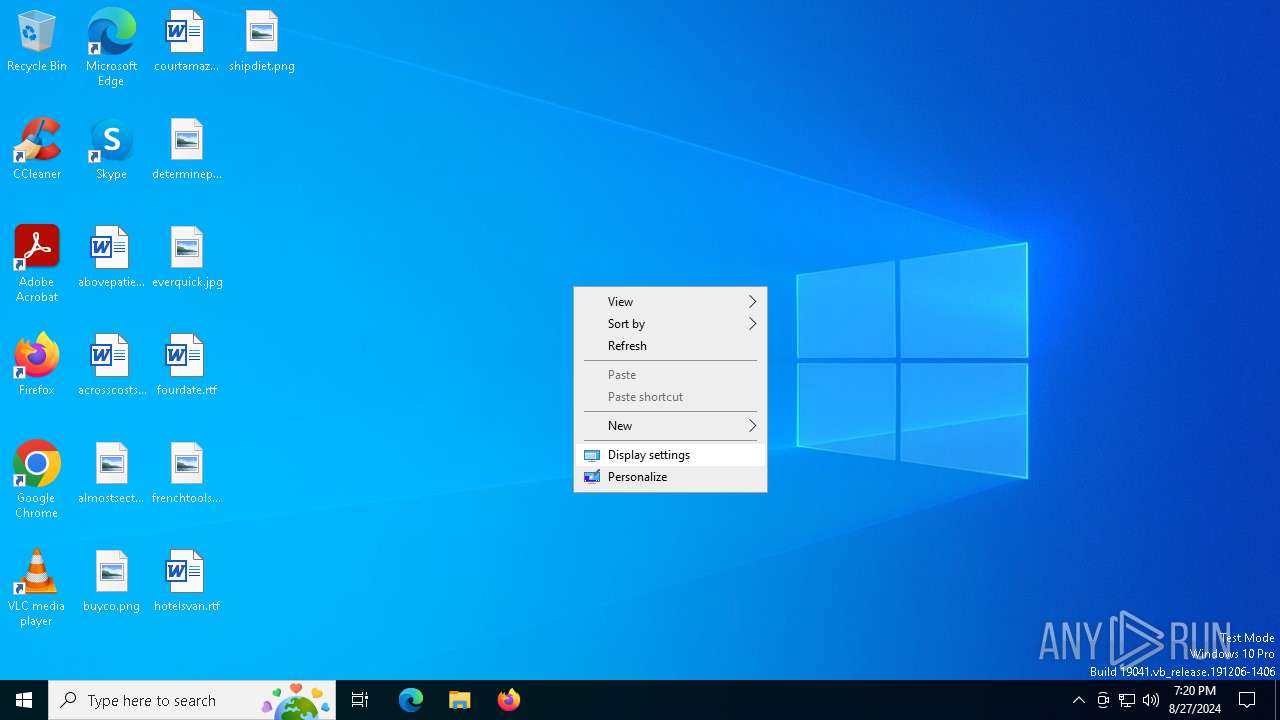
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4128 | "C:\Users\admin\AppData\Local\Temp\svchost.exe" | C:\Users\admin\AppData\Local\Temp\svchost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 2148734499 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5088 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\sosi.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6752 | C:\WINDOWS\system32\WerFault.exe -u -p 4128 -s 8784 | C:\Windows\System32\WerFault.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 662
Read events
5 662
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6752 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_svchost.exe_6599db96334276c9c89df7ed6010e9fe3a5c8c_9a1f5717_d506901f-c314-4637-bb15-72d6433e088c\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6752 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\svchost.exe.4128.dmp | — | |
MD5:— | SHA256:— | |||
| 6752 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:82C30E45BF5F93A5DB1D5E47F913053B | SHA256:2C6BBFF9207065E8800C4AF0CB2748818ABB3CFFC0D6D518FE17F76A232F8967 | |||
| 6752 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERB137.tmp.dmp | binary | |
MD5:6A2CF2C24D0693746086B5C416620934 | SHA256:AFD7440704550F46ECC2B5FA0CCAEF5B27AC27D6EAB77BEBAD835FBAFF1CA97F | |||
| 6752 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERB2BF.tmp.WERInternalMetadata.xml | xml | |
MD5:7D3C50D2E0754969C71EF63EEC9DDD4F | SHA256:2B4FC657E1905C6A0FCC77AE9466F54E73733F155F77AEF1A80EB196A42A774E | |||
| 6752 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERB2DF.tmp.xml | xml | |
MD5:A310BAF5408306378FFAA0A181470244 | SHA256:167A0702F07E30F254A828AC57A919A2301EECD1FC037038D38CC778BE219710 | |||
| 6752 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FB64A9EBEDF48D3895381D5B7D80743D | SHA256:EA21D495930AD76F267A33A0F593DBF0C7EA75E457FCAE49A29DAAD8BD920F42 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
14
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2036 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4128 | svchost.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
2636 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2636 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6424 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6020 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4128 | svchost.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | shared |
6752 | WerFault.exe | 20.189.173.21:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6020 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2036 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ip-api.com |
| shared |
watson.events.data.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
4128 | svchost.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
4128 | svchost.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
Process | Message |
|---|---|
svchost.exe | CLR: Managed code called FailFast without specifying a reason.
|