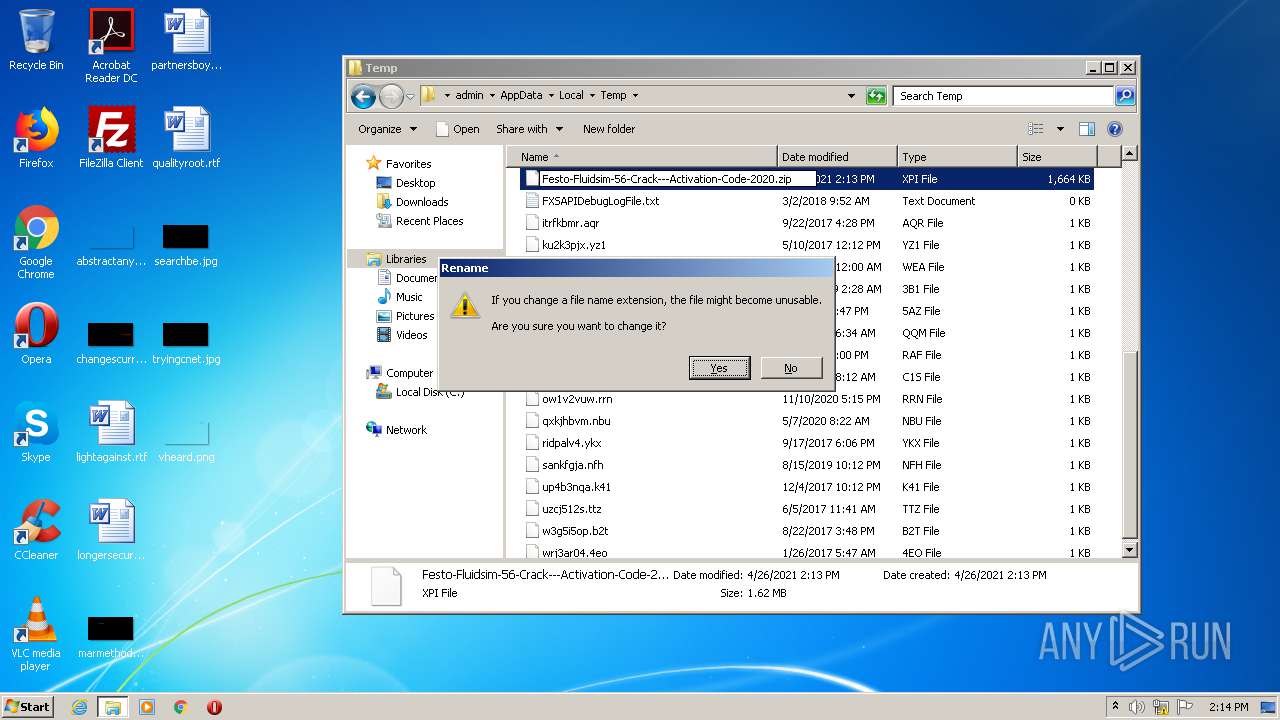
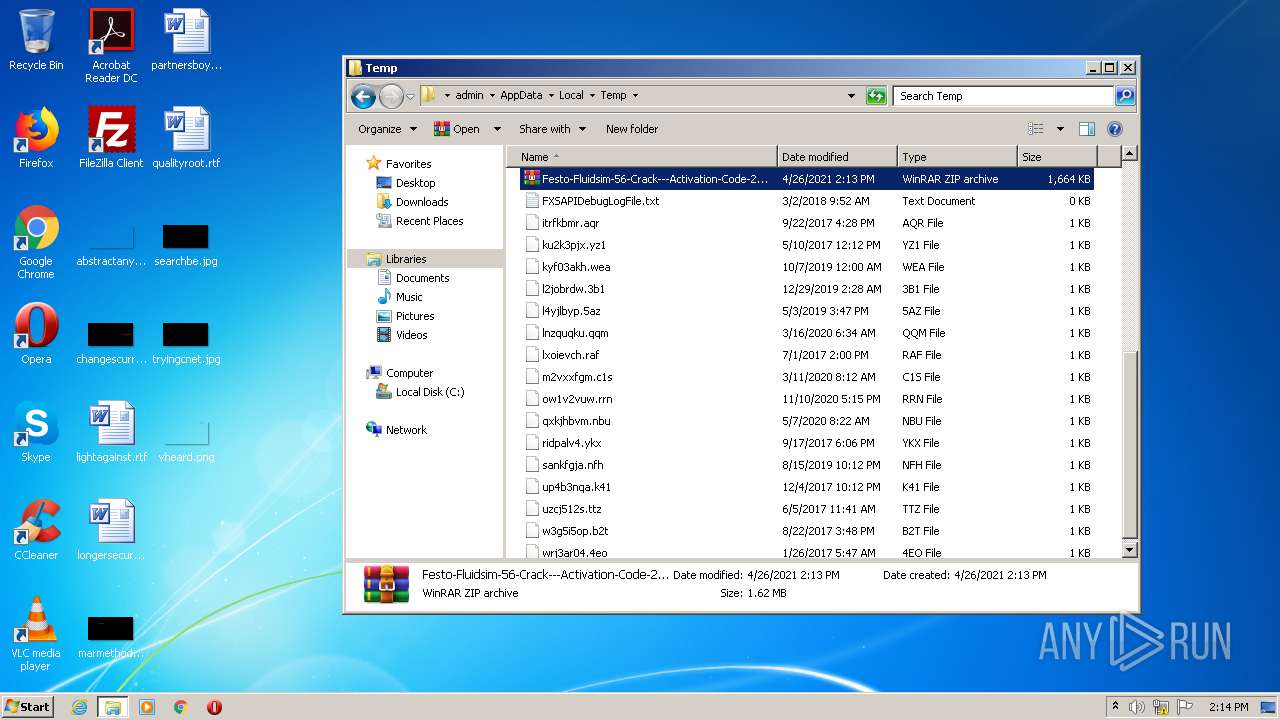
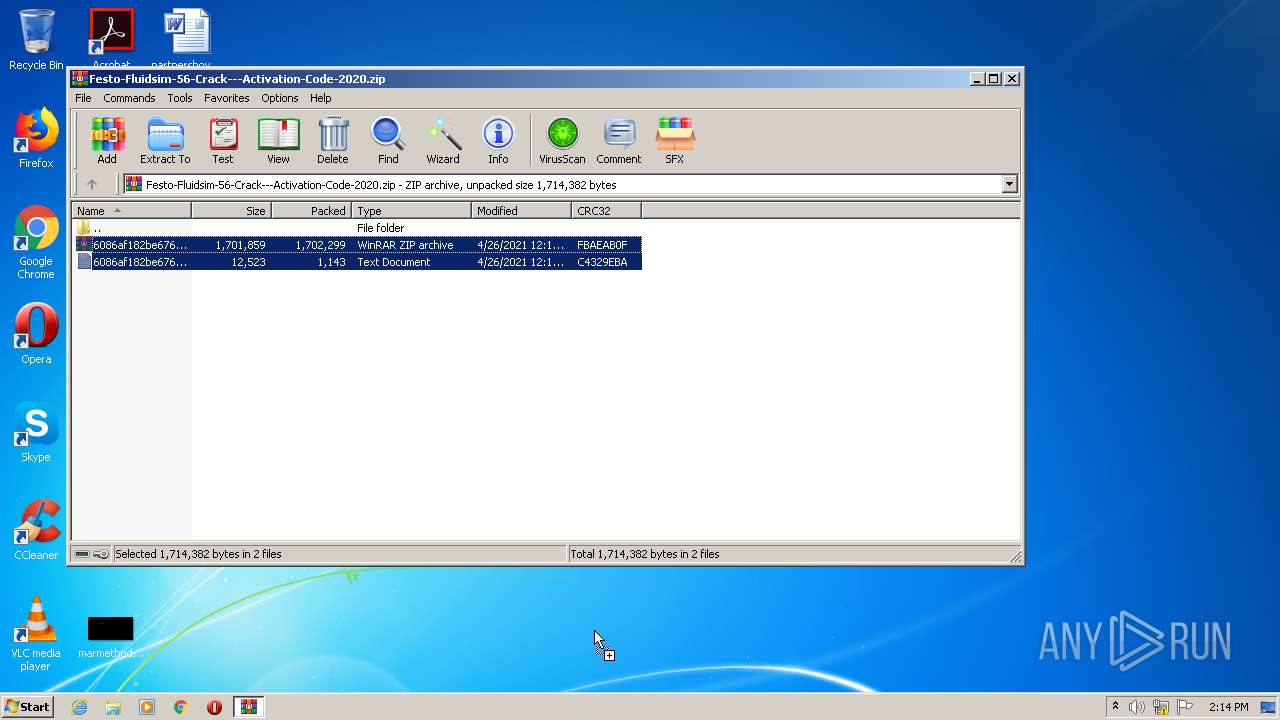
| File name: | Festo-Fluidsim-56-Crack---Activation-Code-2020.zip |
| Full analysis: | https://app.any.run/tasks/5fdb1a4c-c429-4f7b-8efe-96f8bddbffae |
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2021, 13:13:11 |
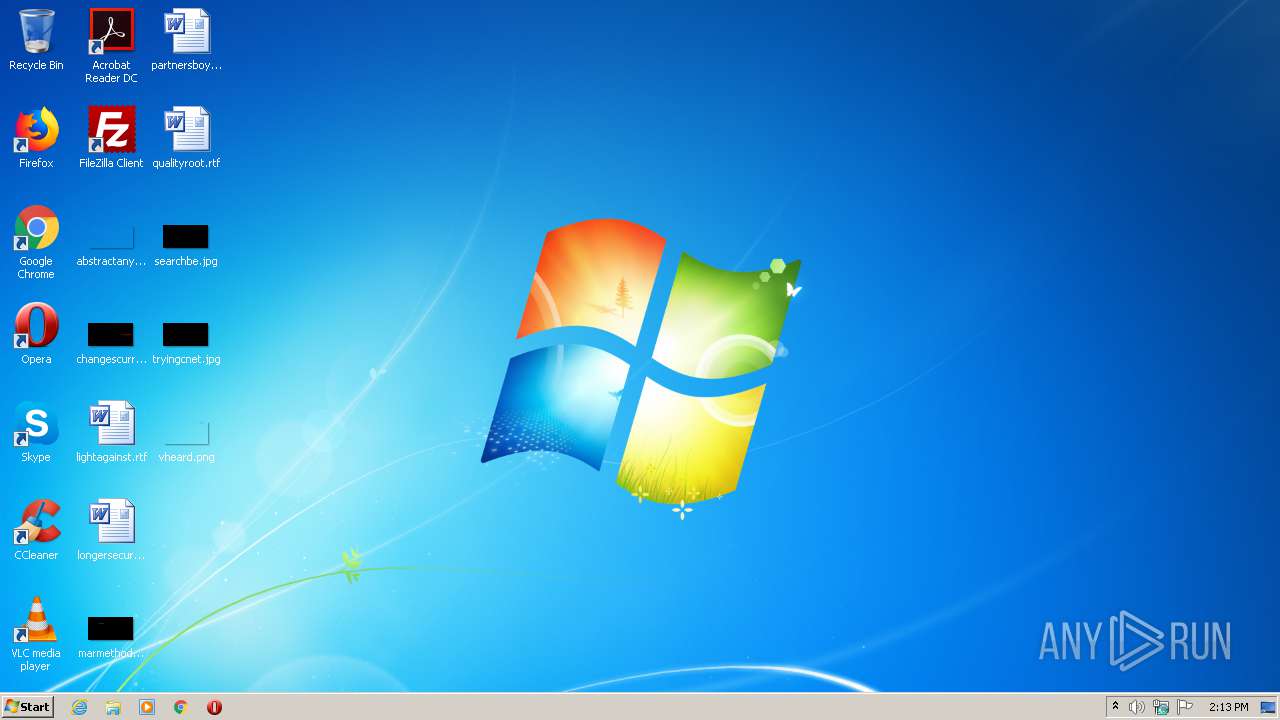
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1142C9ED3D708440AFEF00772507DAD0 |
| SHA1: | D76213784573B2B29D7AC14EE2BA9F0A4A97386D |
| SHA256: | 883E477BF30EFF8E9175EF377EC9E4230B2C4B1B0BF27E7BE893D5B9B5F5606C |
| SSDEEP: | 49152:0r5OqzjQa953z5hQi+a9FQZZ5YaqtxKCyk:YOu953oiRFQZZ55qAHk |
MALICIOUS
Application was dropped or rewritten from another process
- setup_x86_x64_install.exe (PID: 2692)
- San.exe.com (PID: 3292)
- San.exe.com (PID: 2844)
Runs app for hidden code execution
- cmd.exe (PID: 2472)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3416)
SUSPICIOUS
Starts CMD.EXE for commands execution
- setup_x86_x64_install.exe (PID: 2692)
- cmd.exe (PID: 2472)
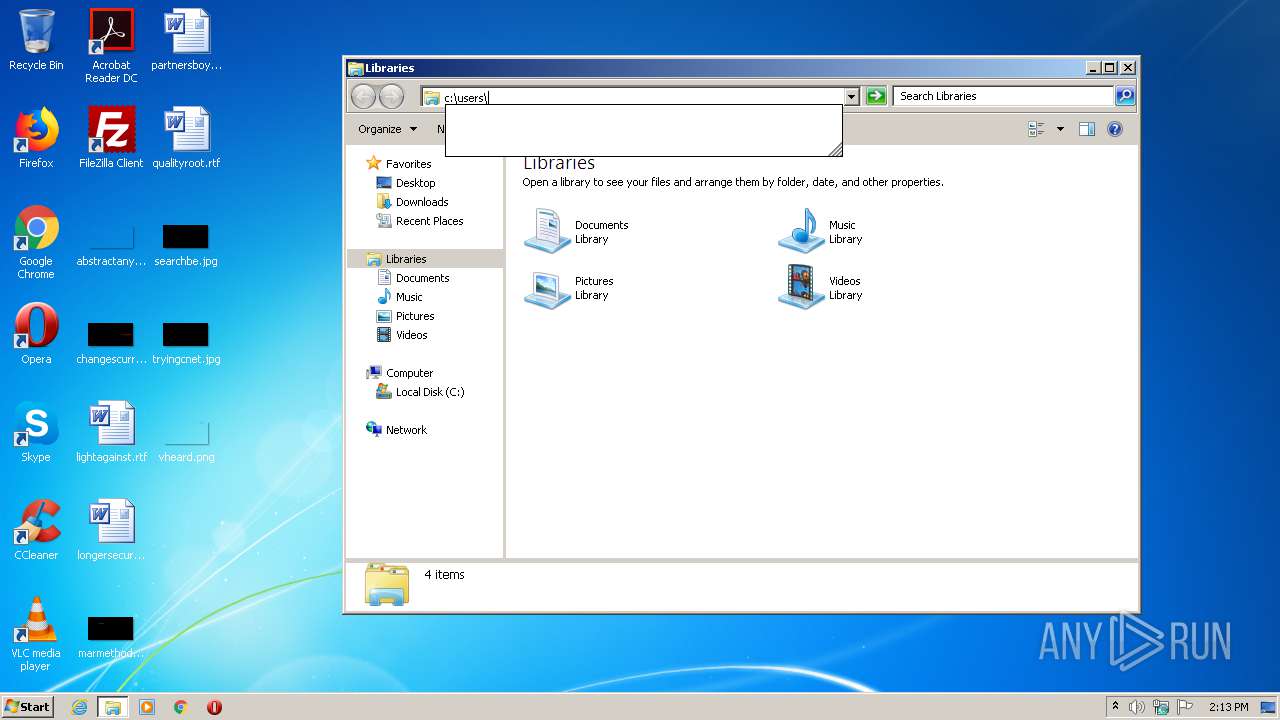
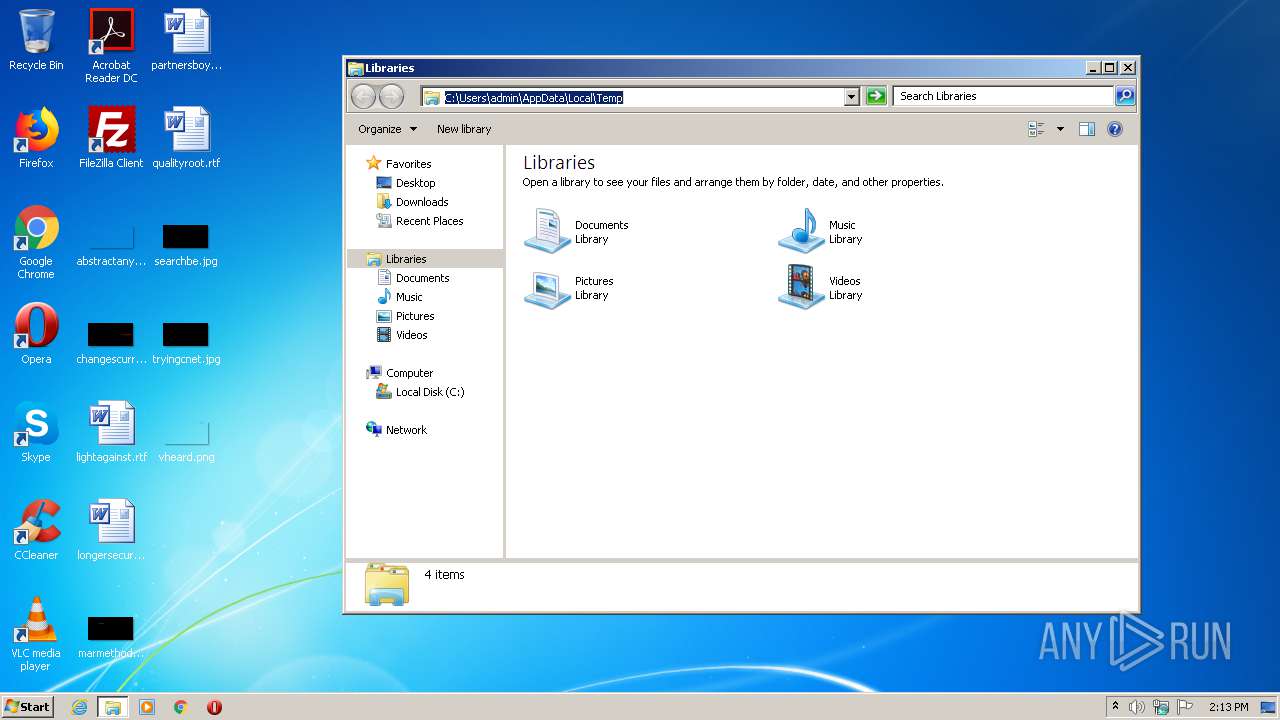
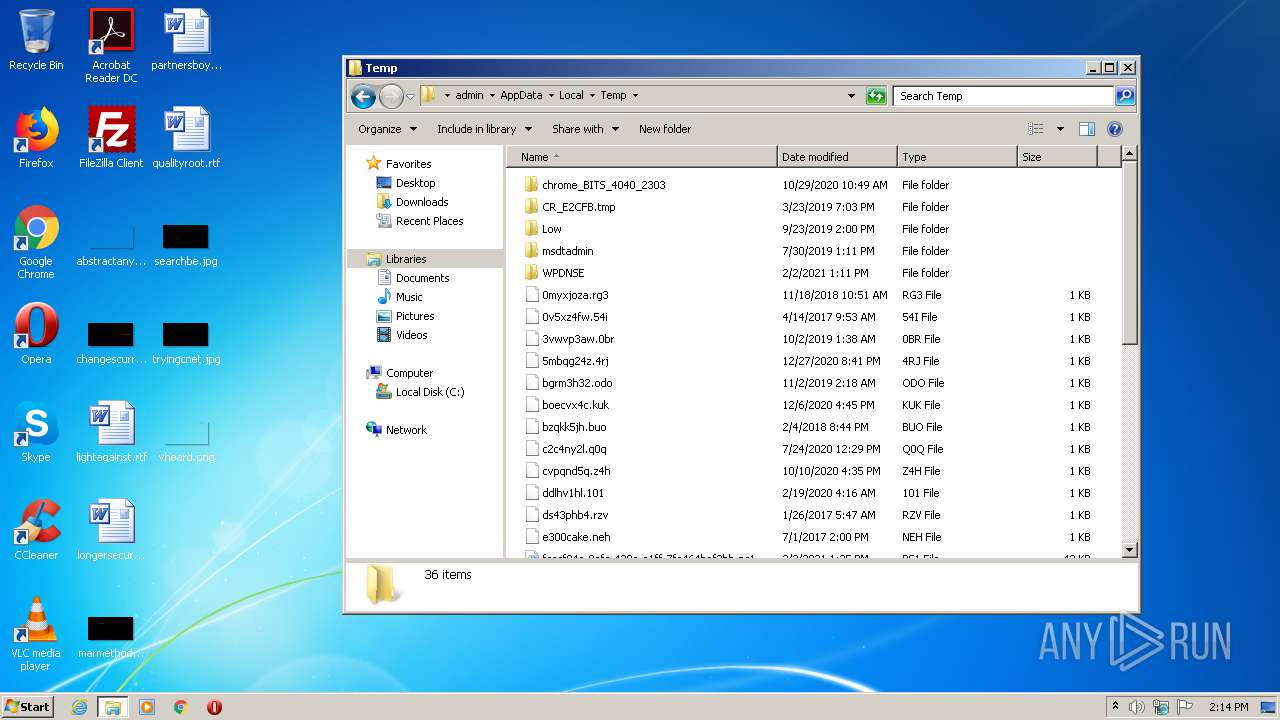
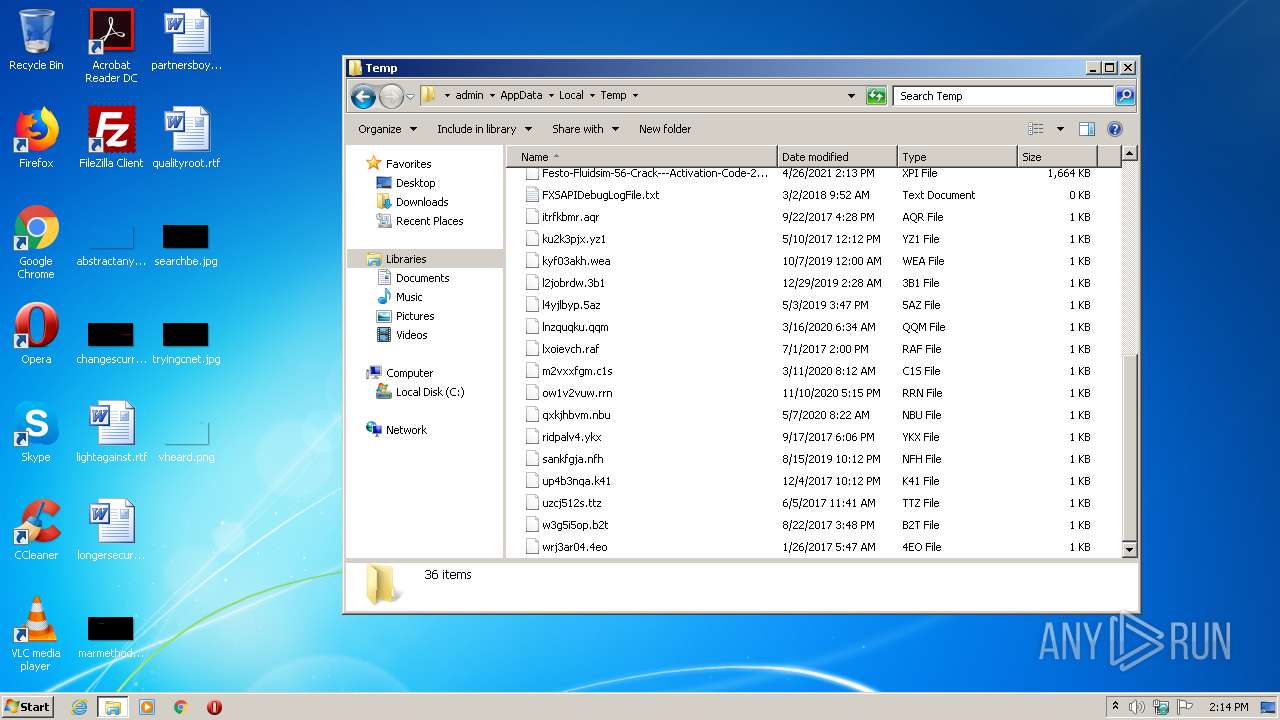
Creates files in the user directory
- setup_x86_x64_install.exe (PID: 2692)
- cmd.exe (PID: 3416)
Application launched itself
- cmd.exe (PID: 2472)
- San.exe.com (PID: 2844)
Drop AutoIt3 executable file
- cmd.exe (PID: 3416)
Executable content was dropped or overwritten
- cmd.exe (PID: 3416)
Starts application with an unusual extension
- cmd.exe (PID: 3416)
- San.exe.com (PID: 2844)
INFO
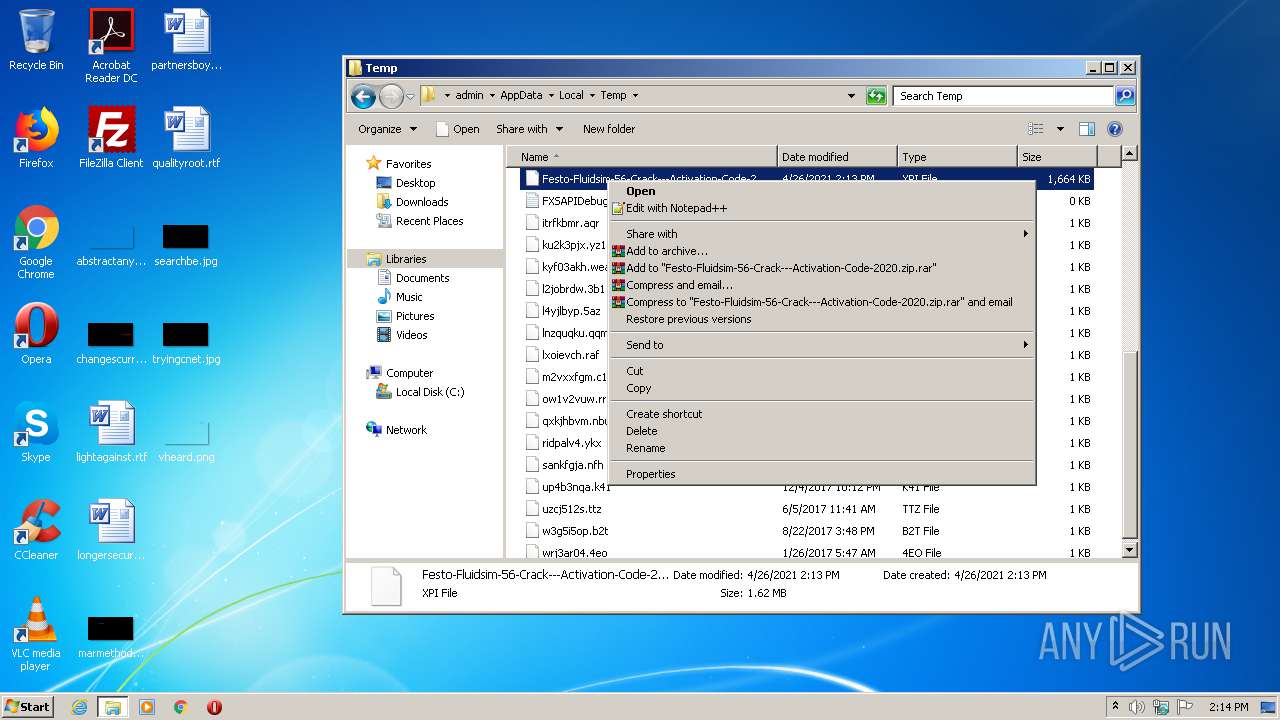
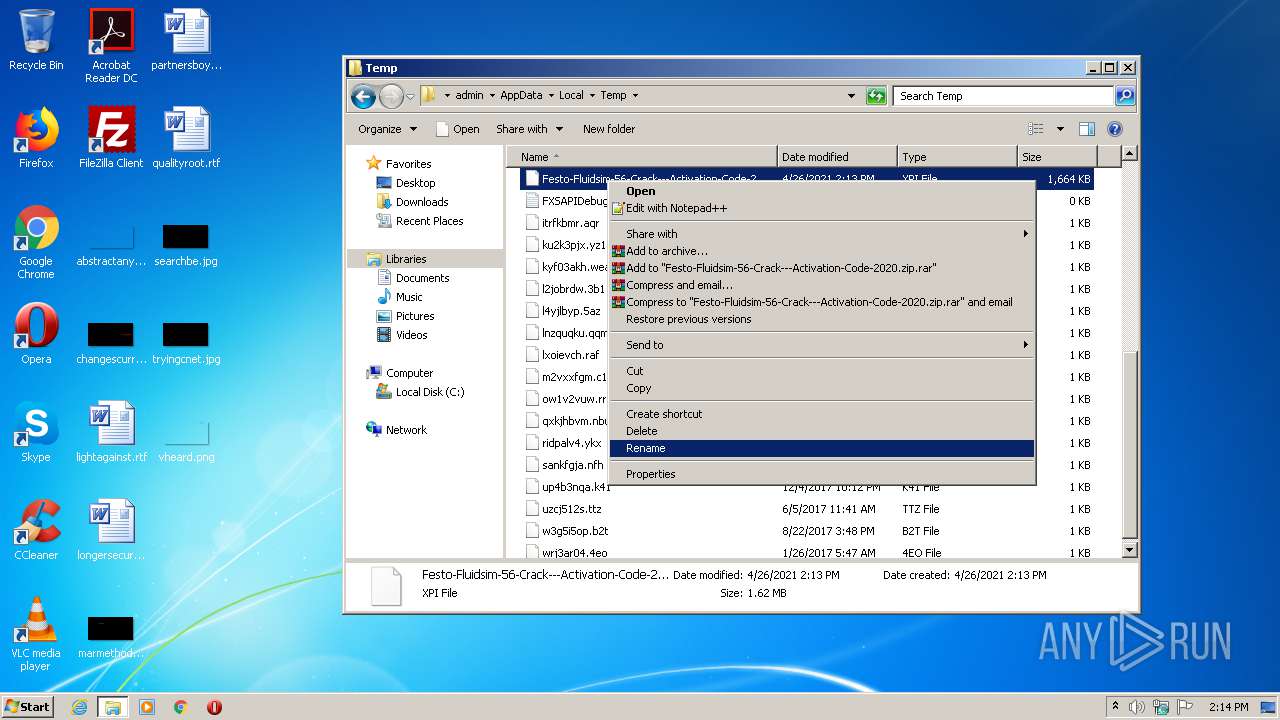
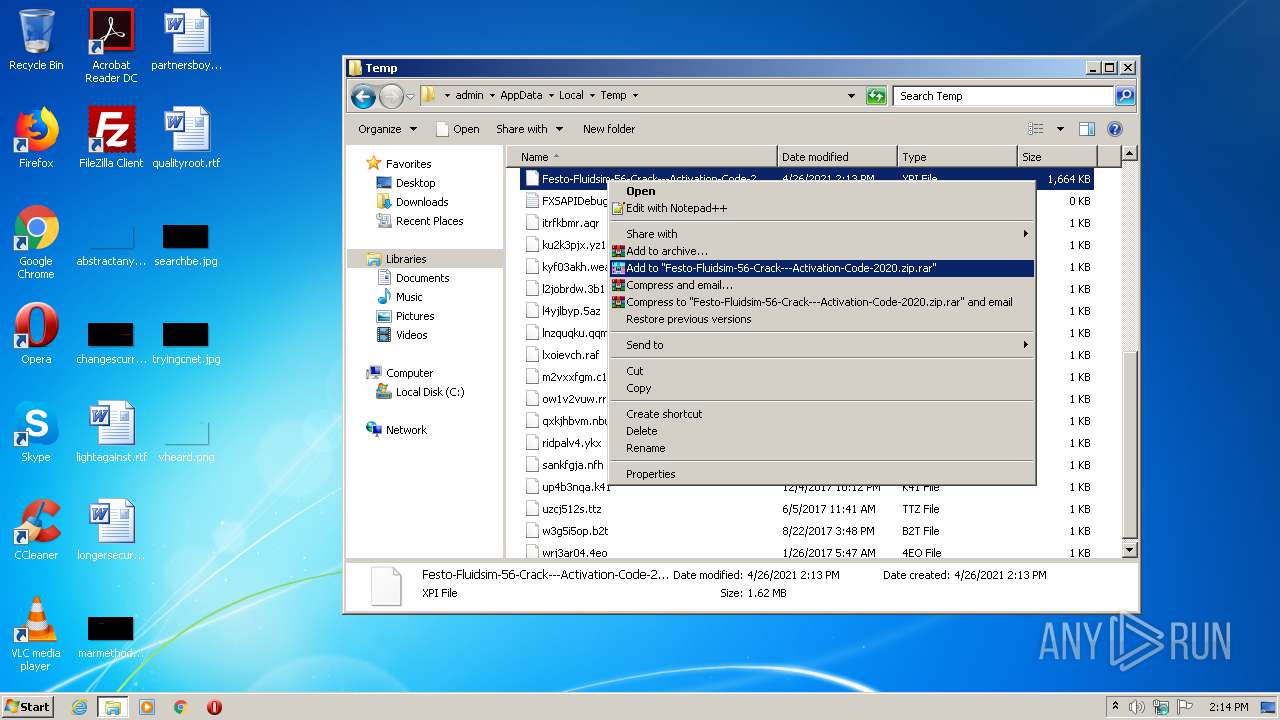
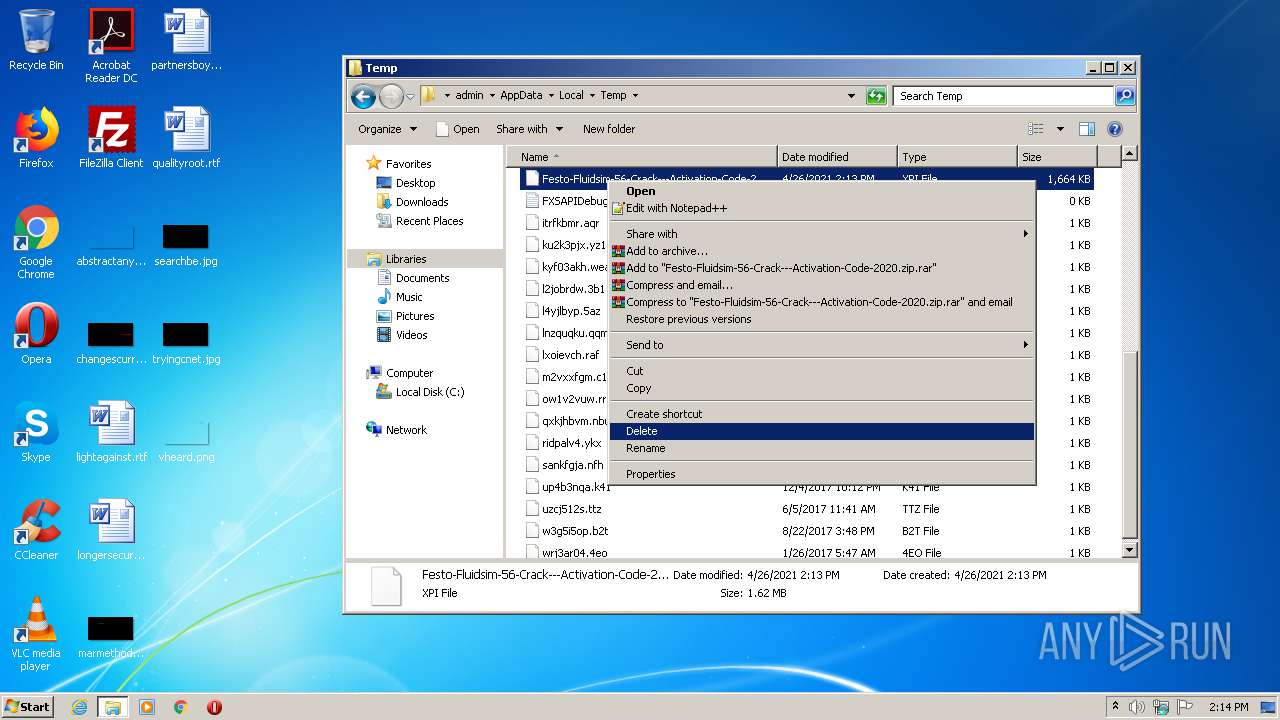
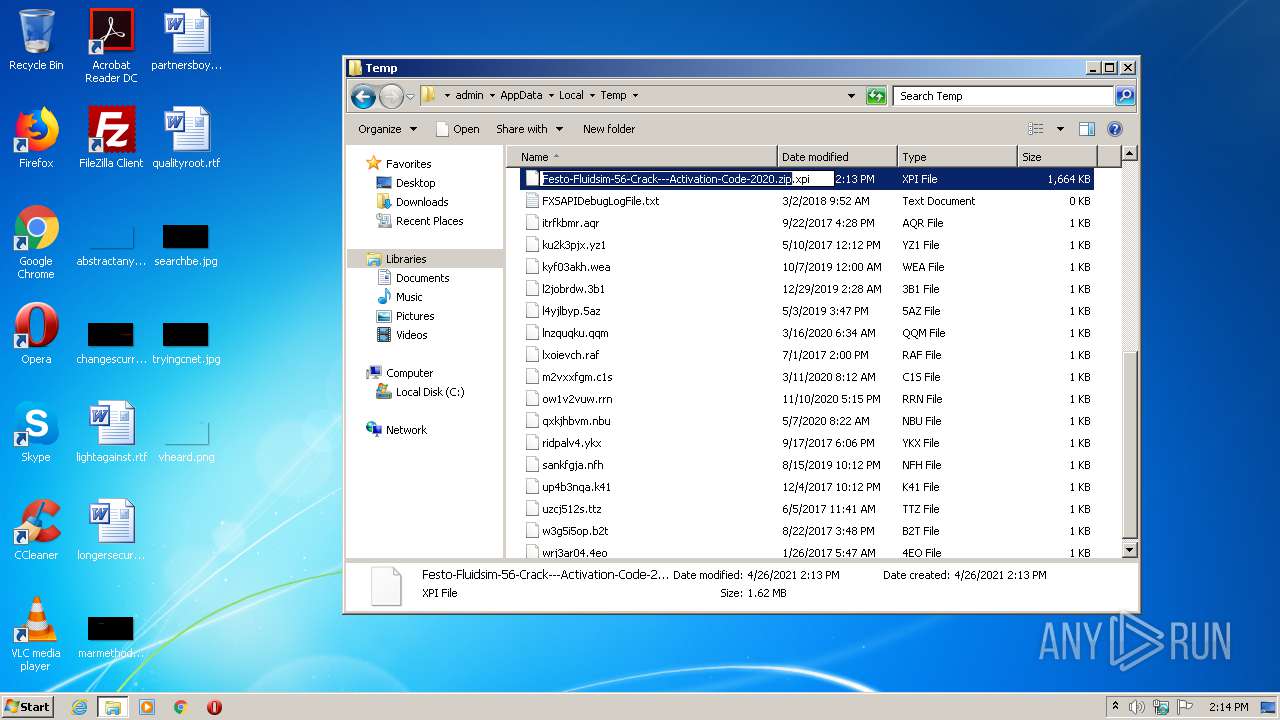
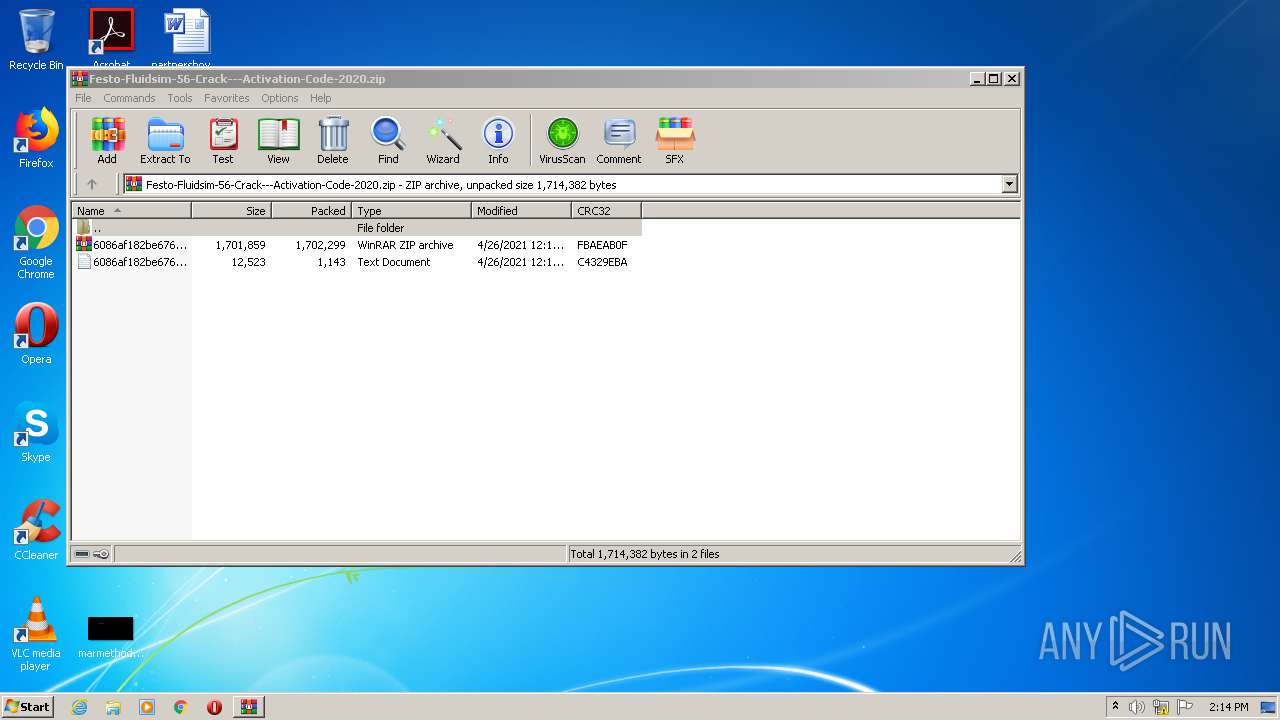
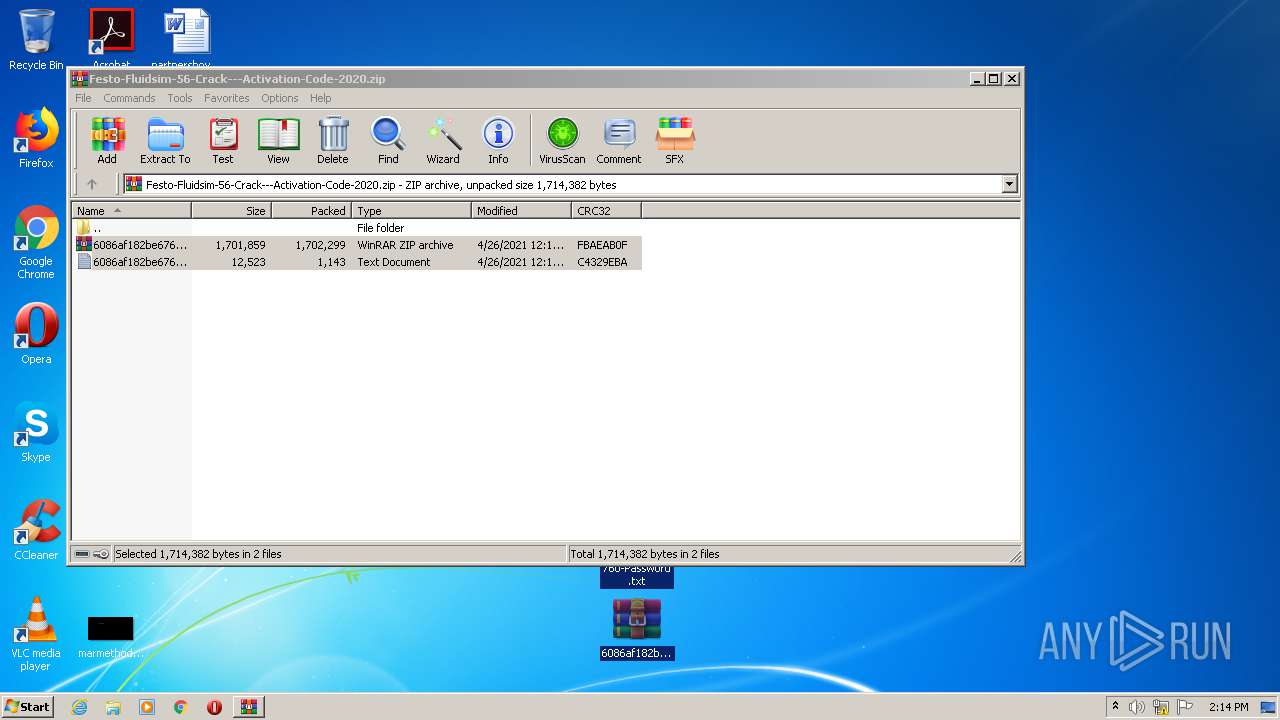
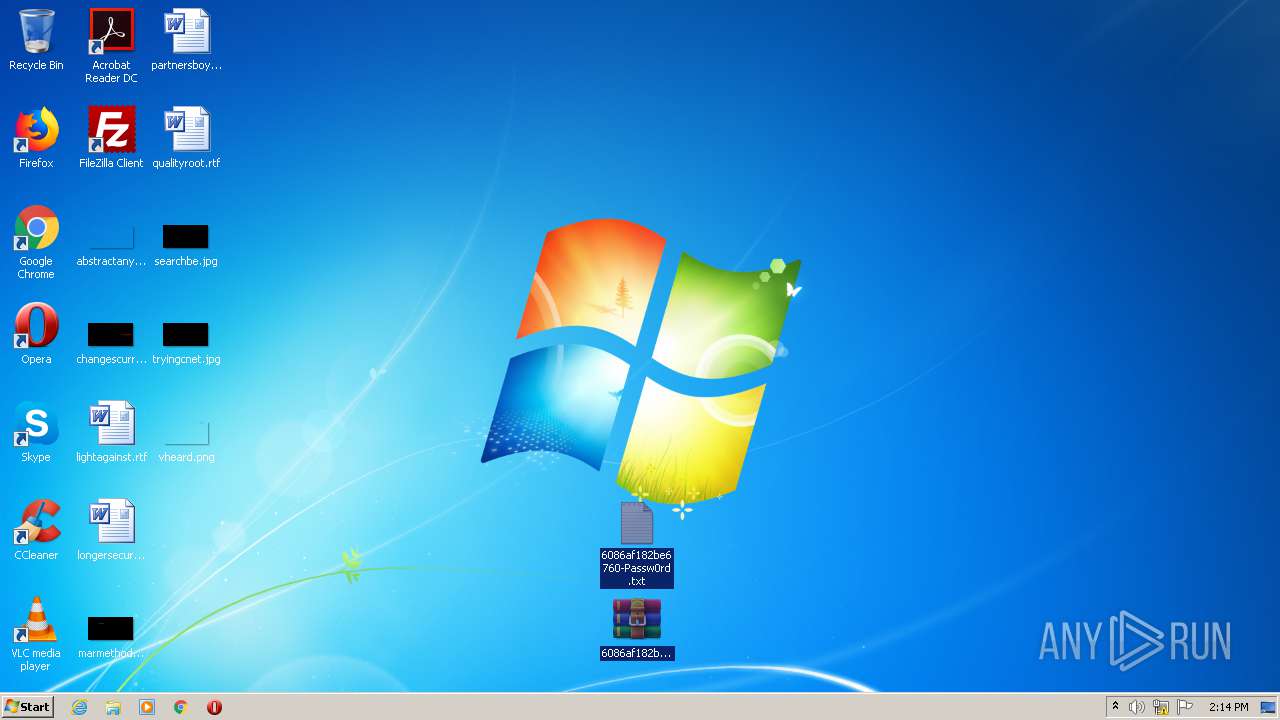
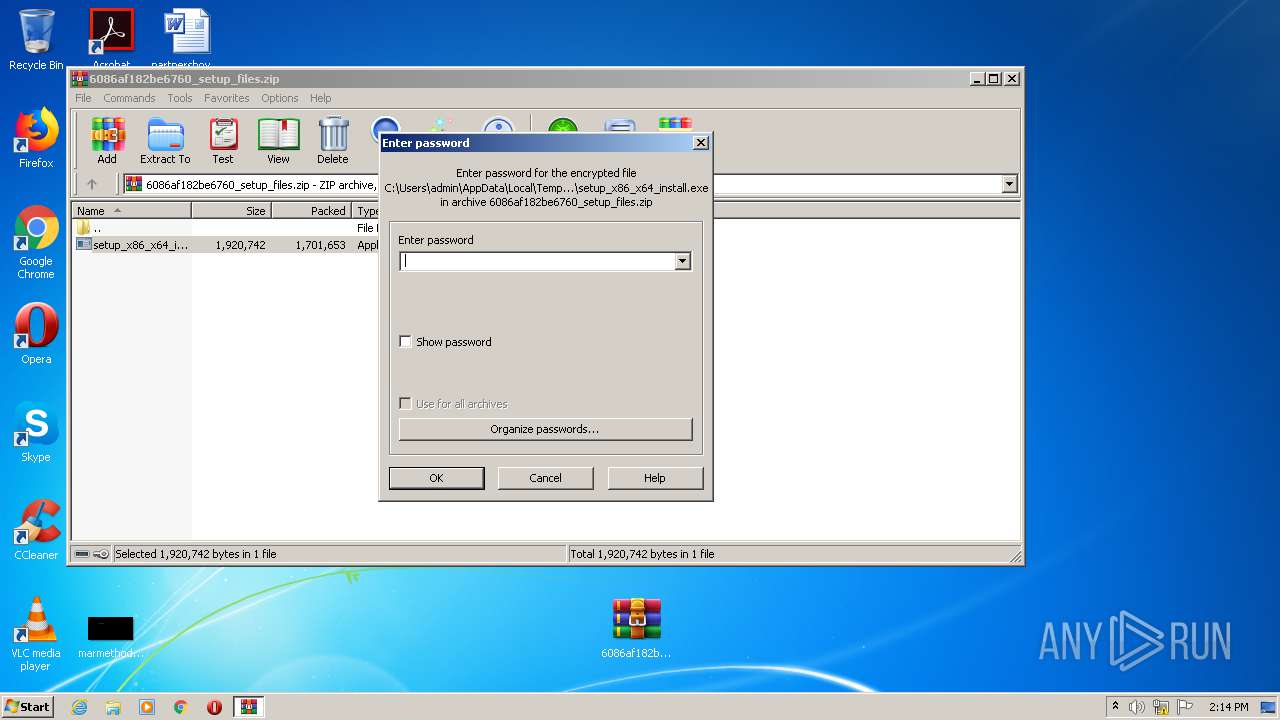
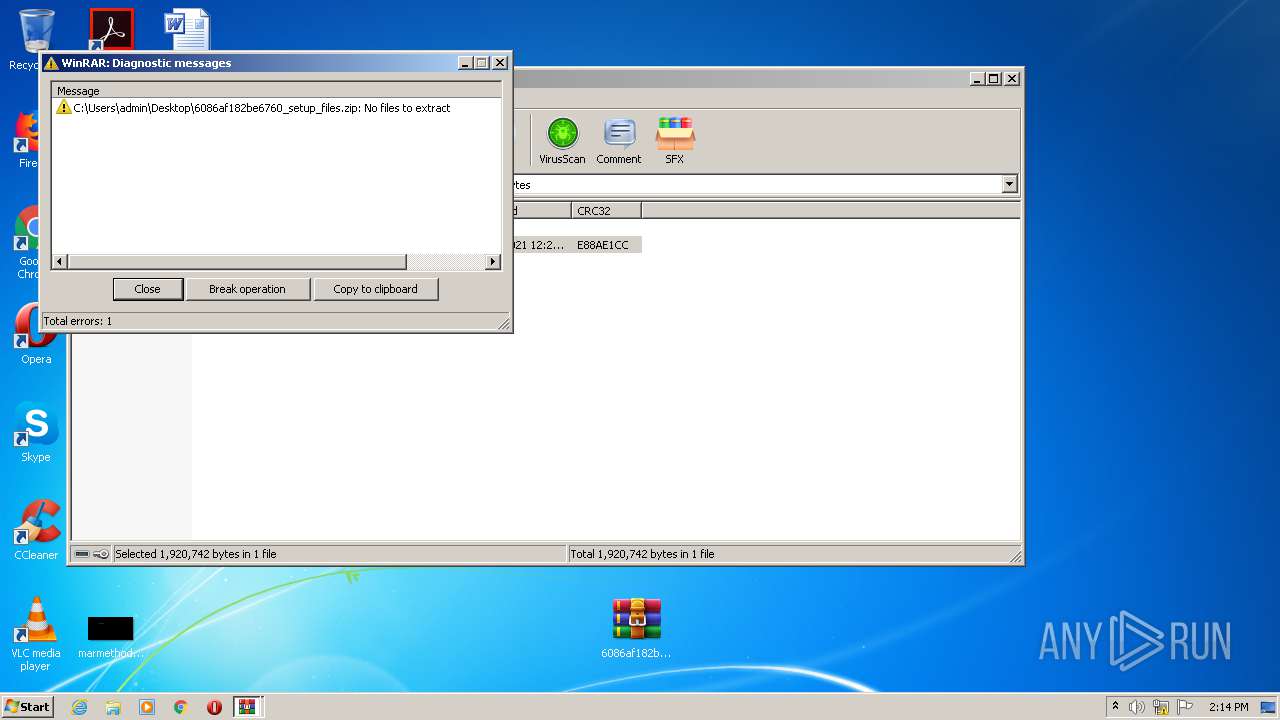
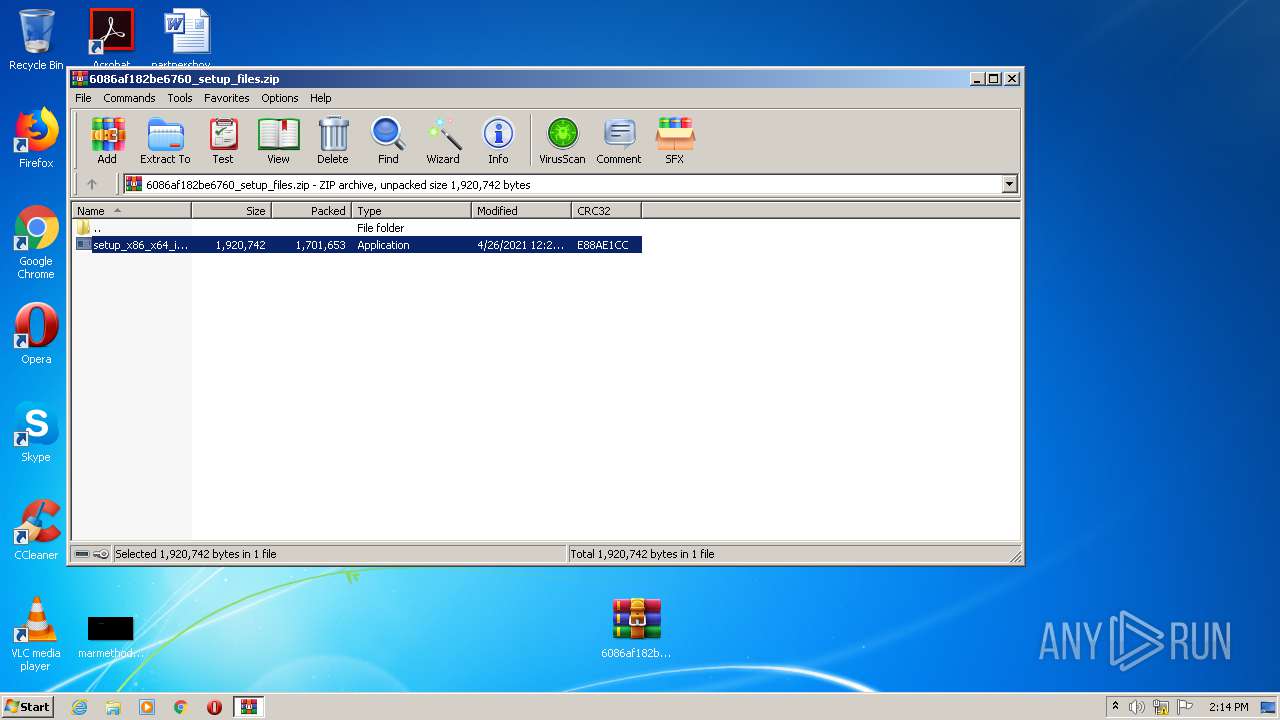
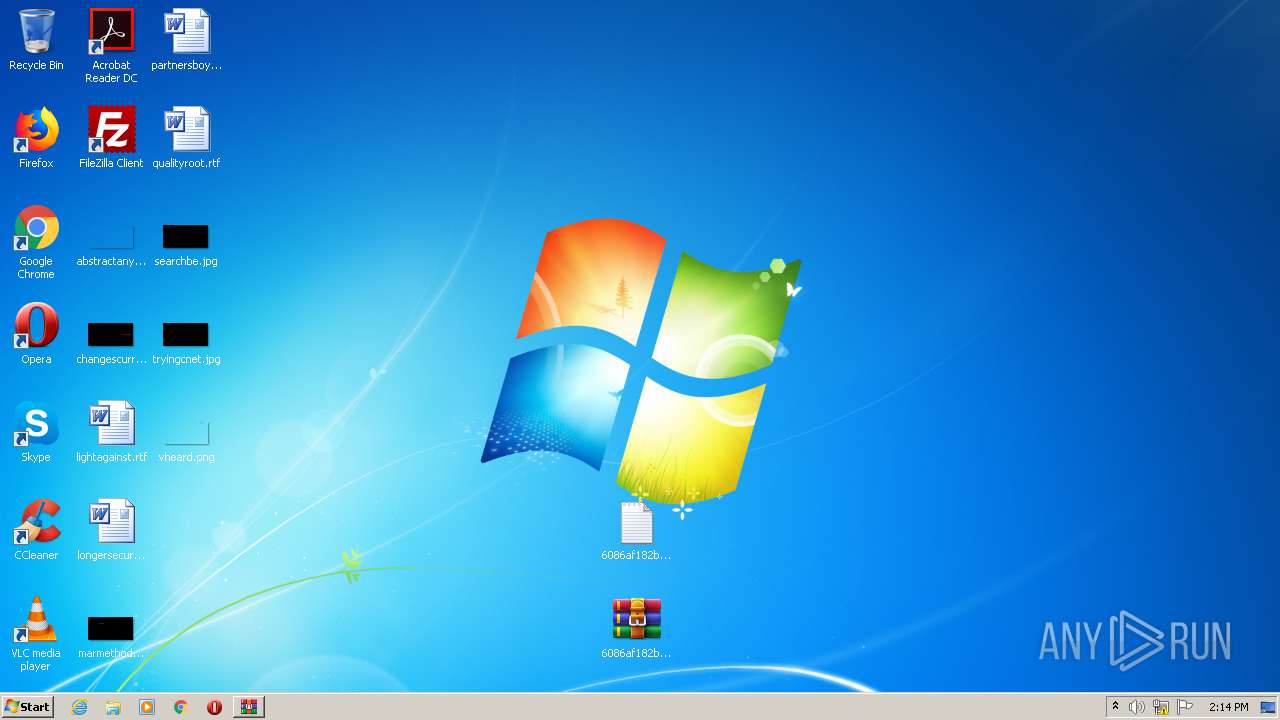
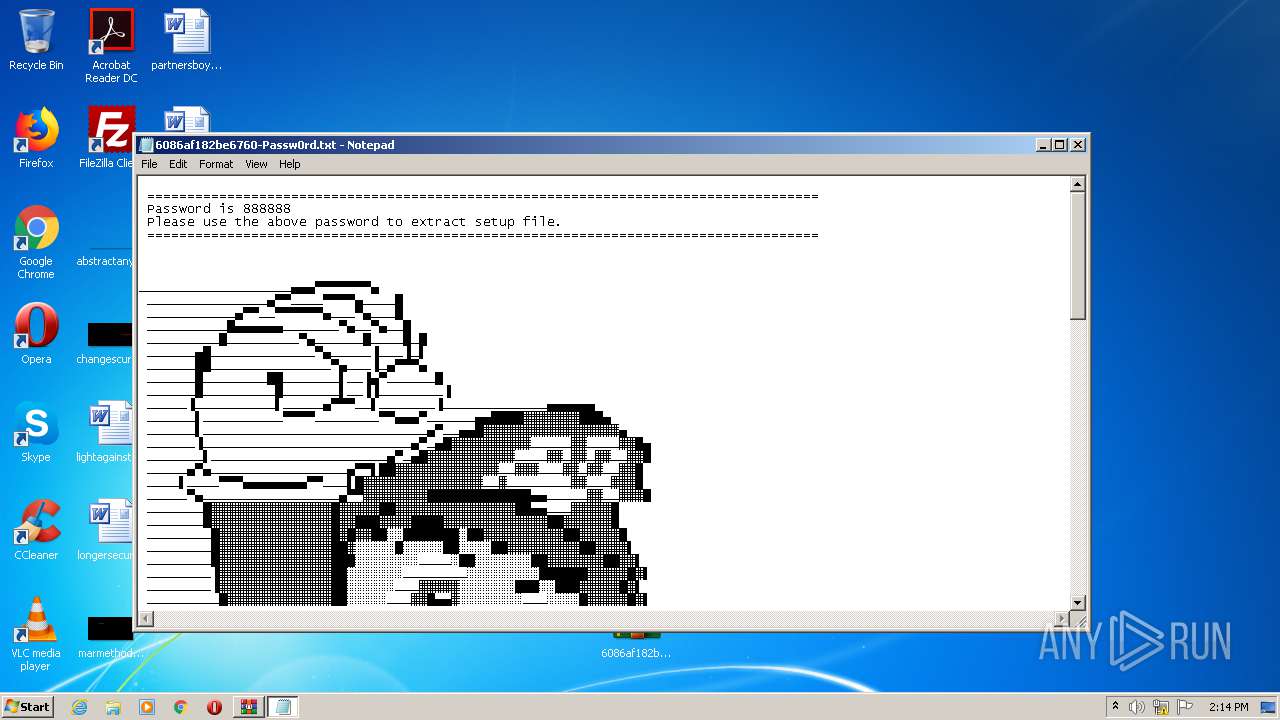
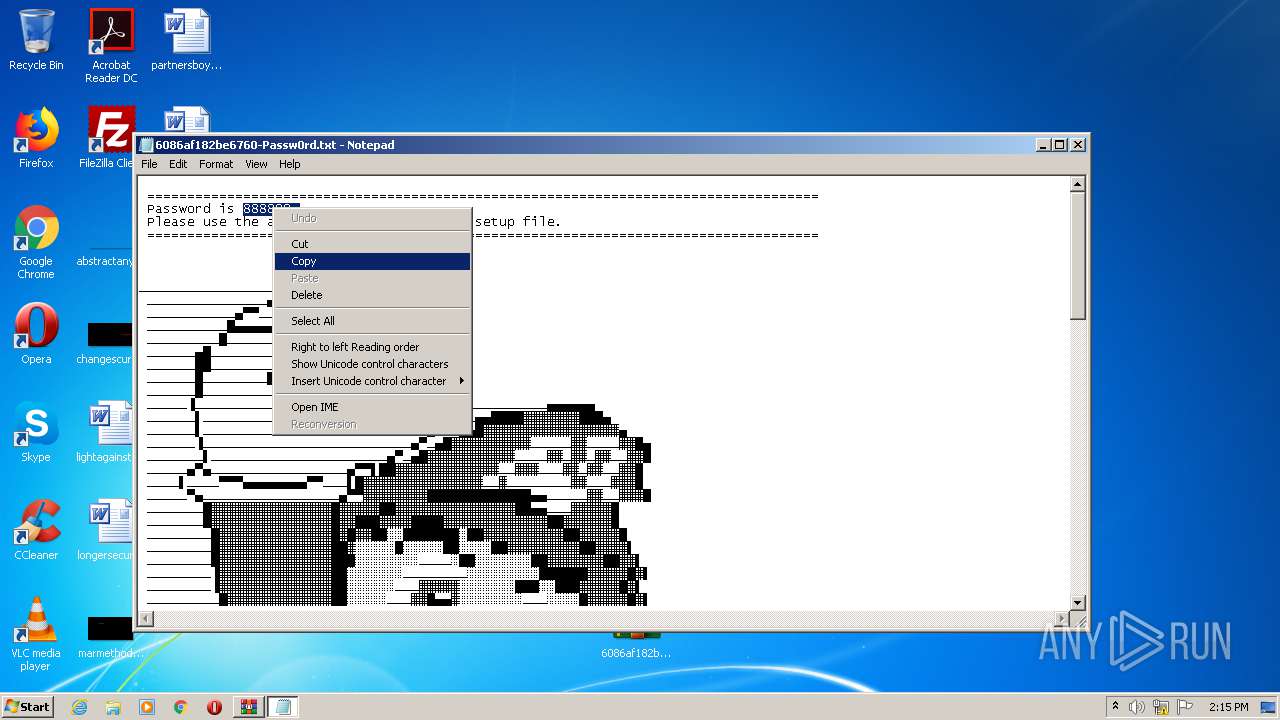
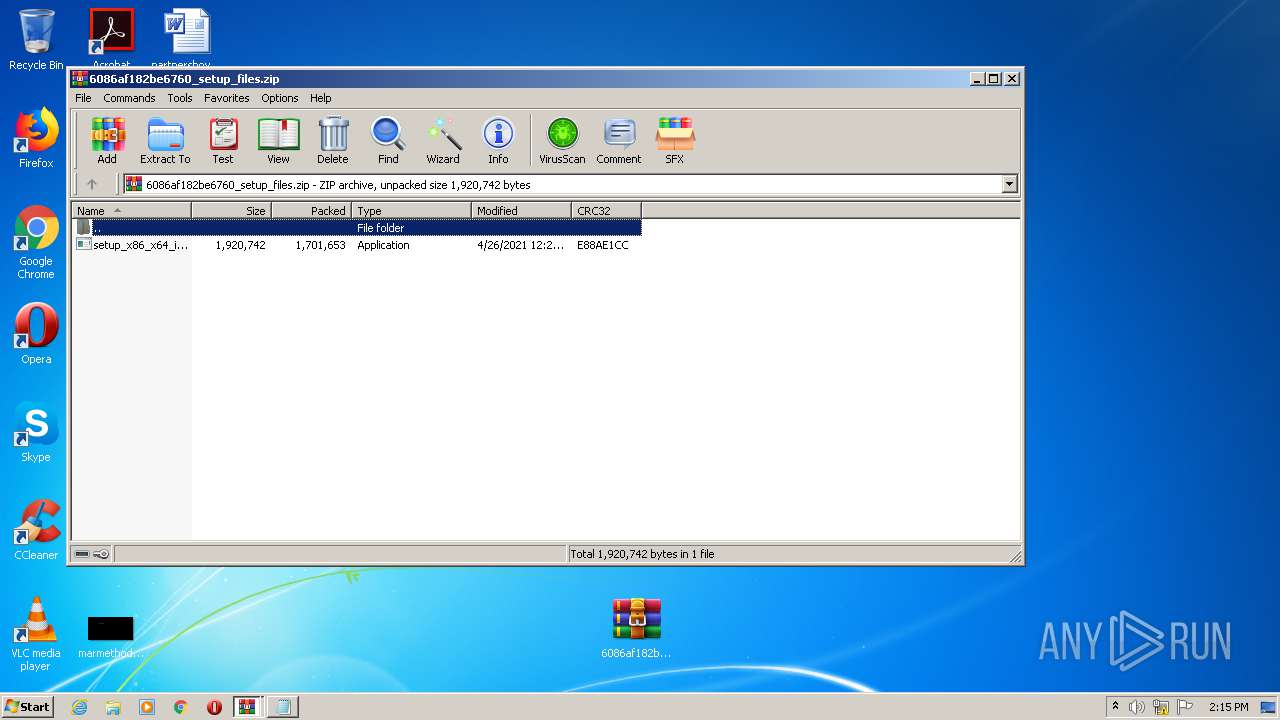
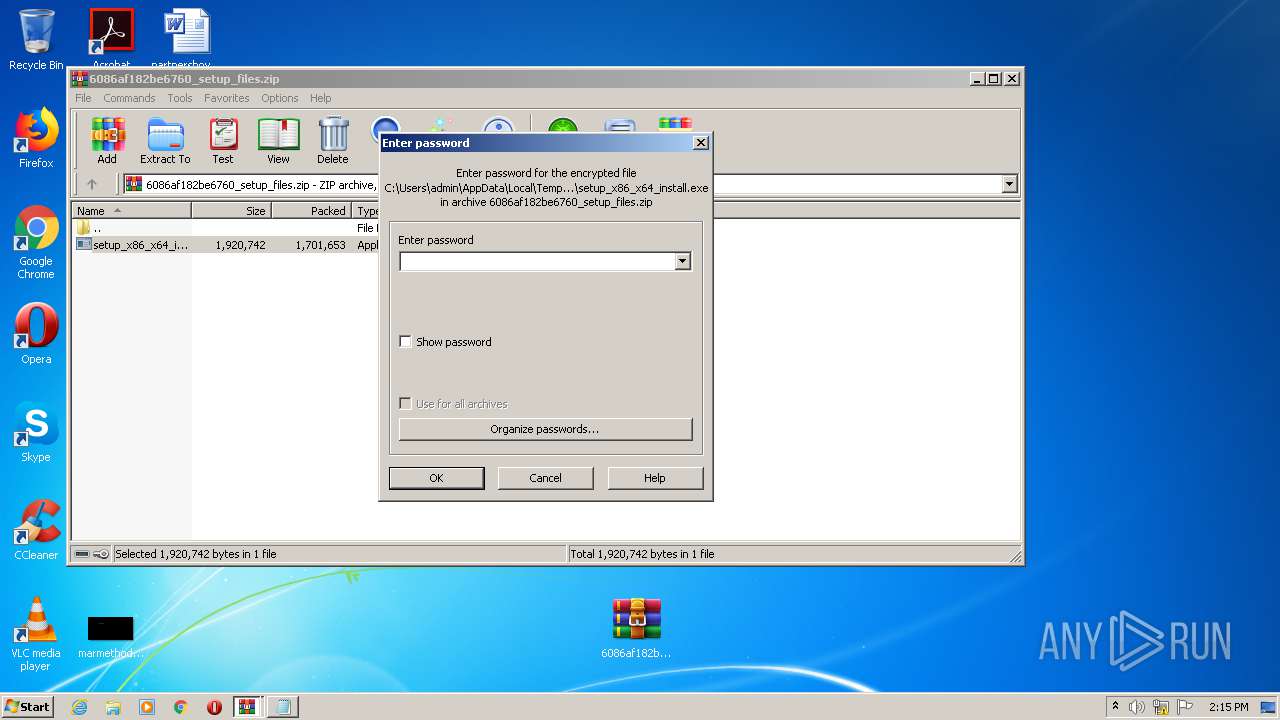
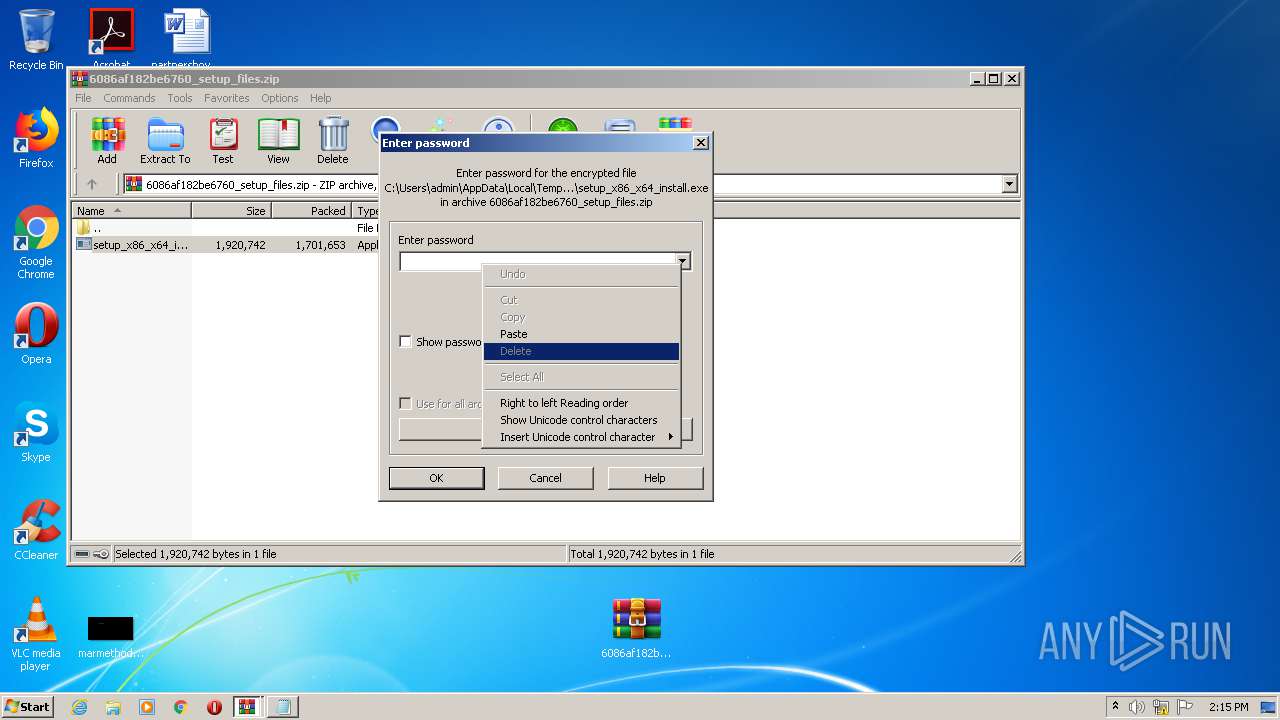
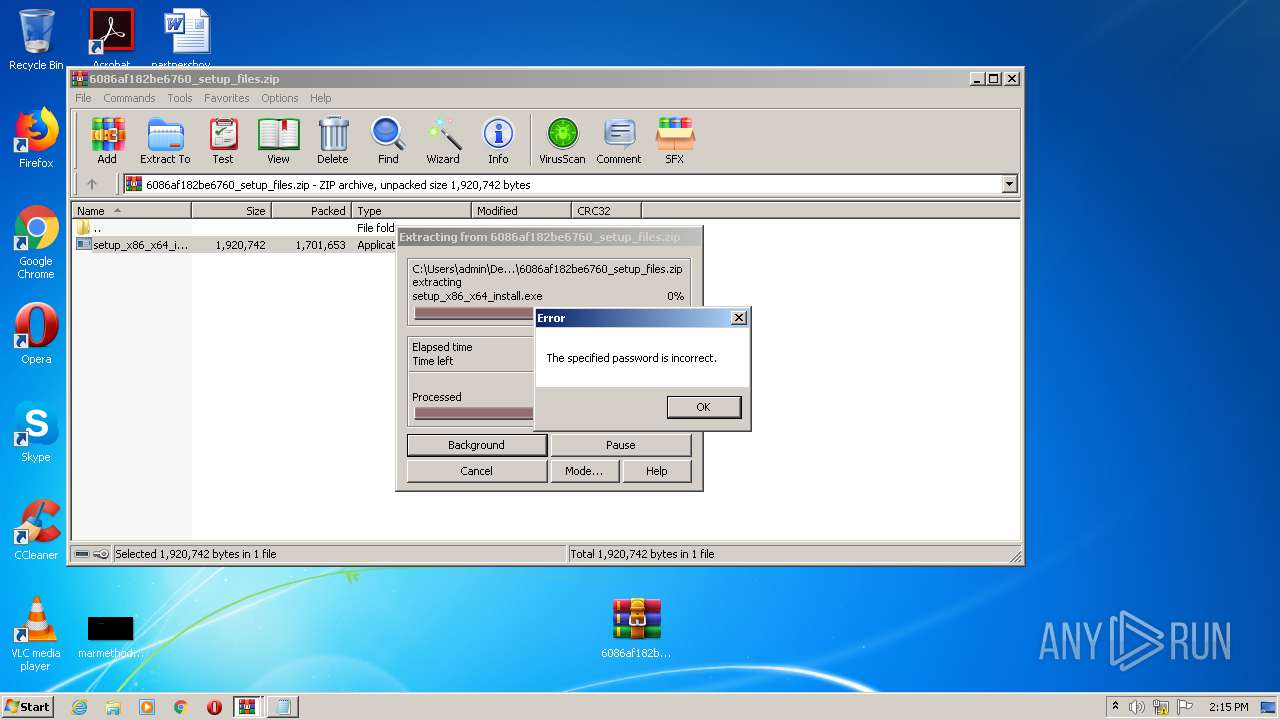
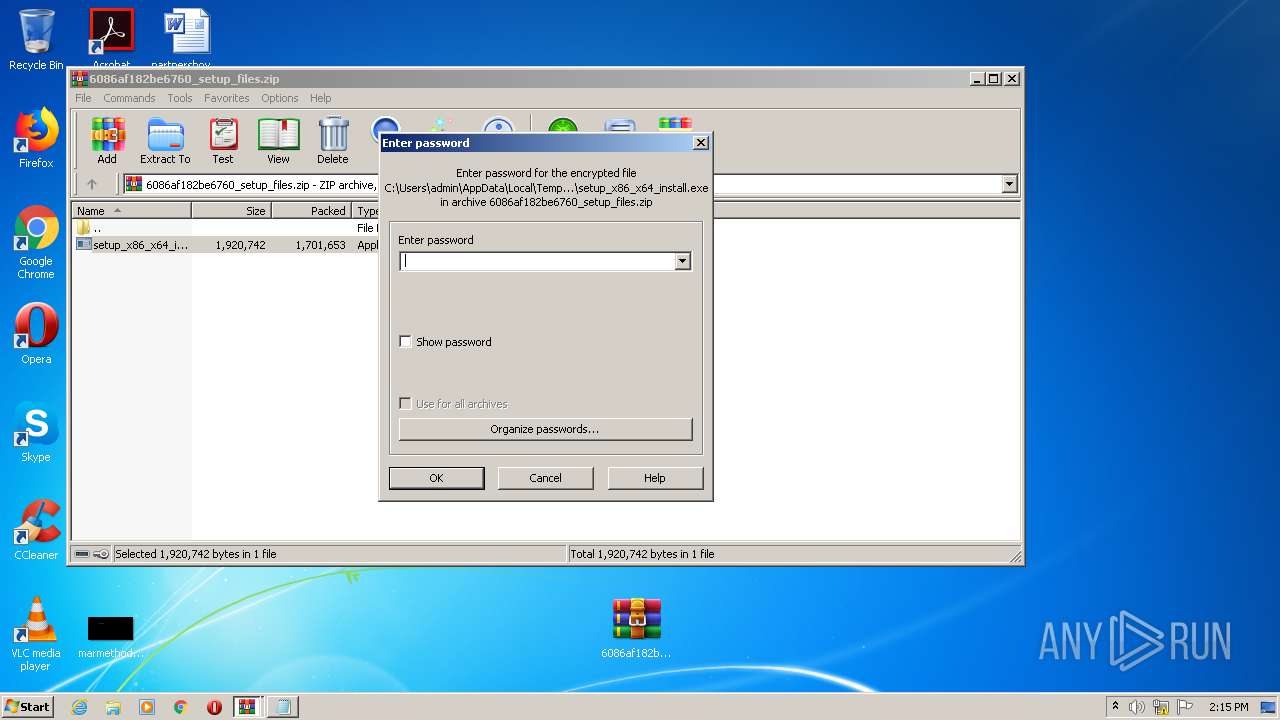
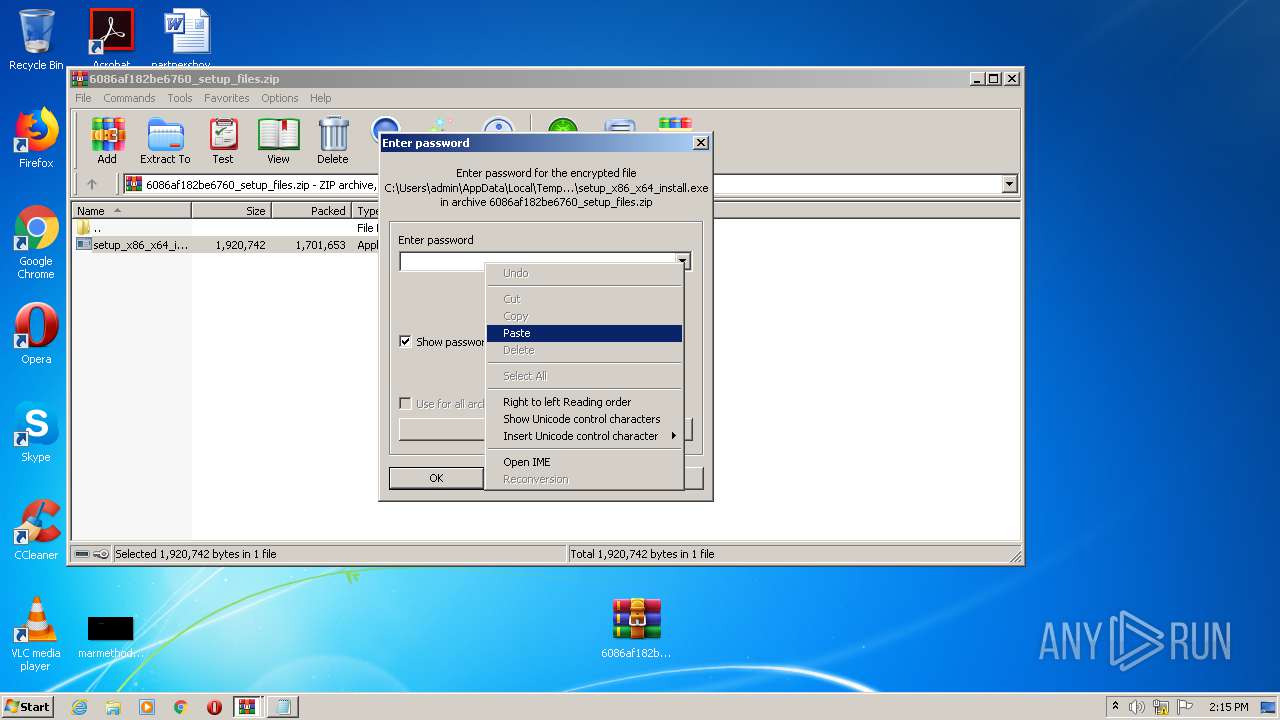
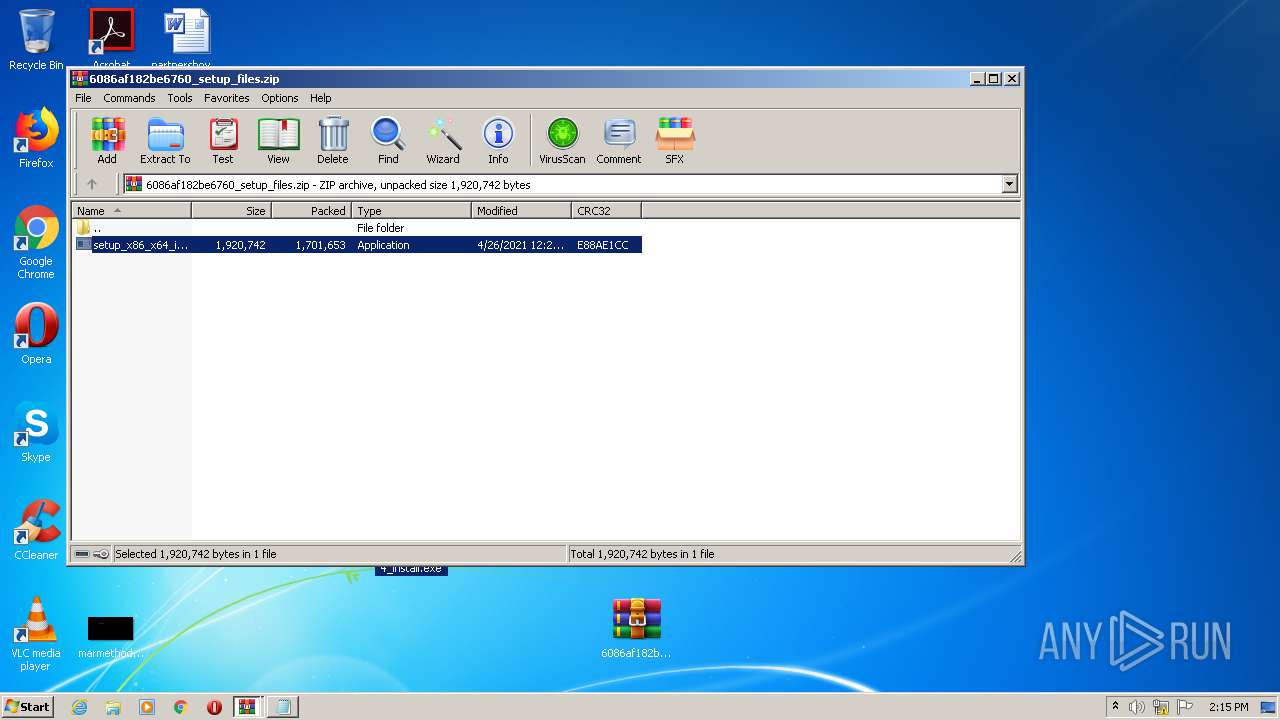
Manual execution by user
- NOTEPAD.EXE (PID: 3776)
- WinRAR.exe (PID: 3492)
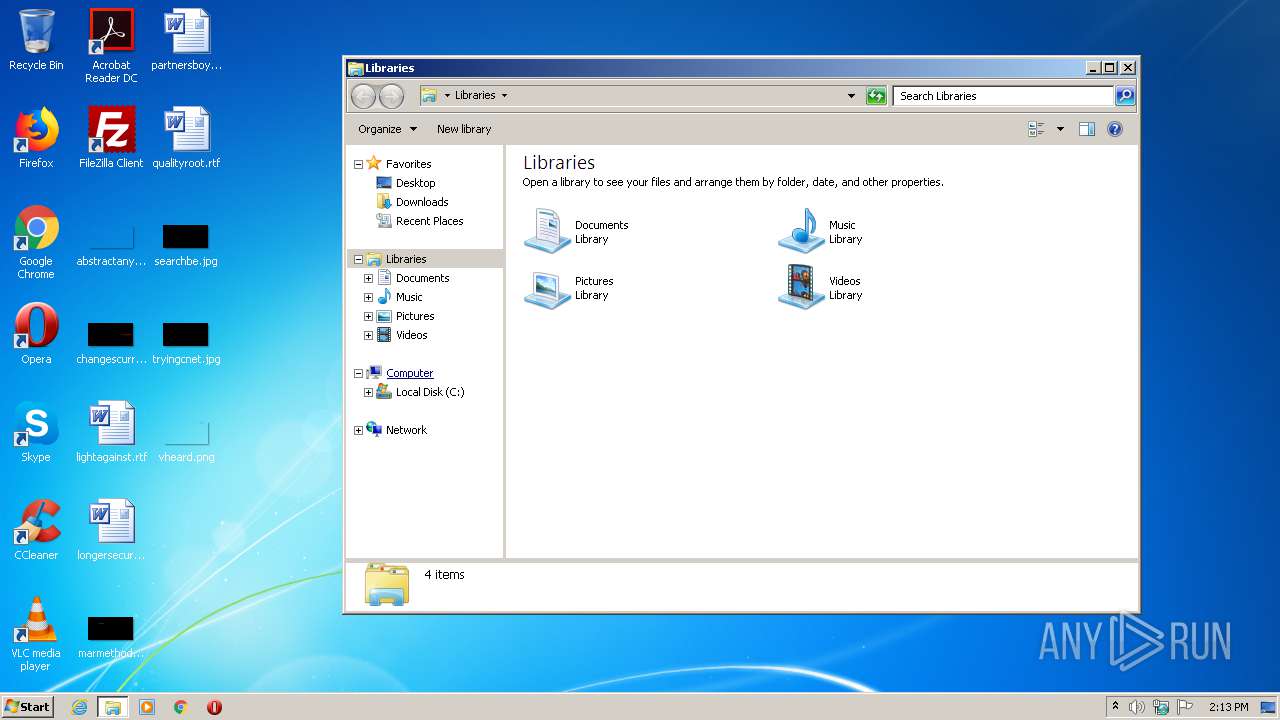
- explorer.exe (PID: 4080)
- WinRAR.exe (PID: 2468)
- setup_x86_x64_install.exe (PID: 2692)
- WinRAR.exe (PID: 3520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
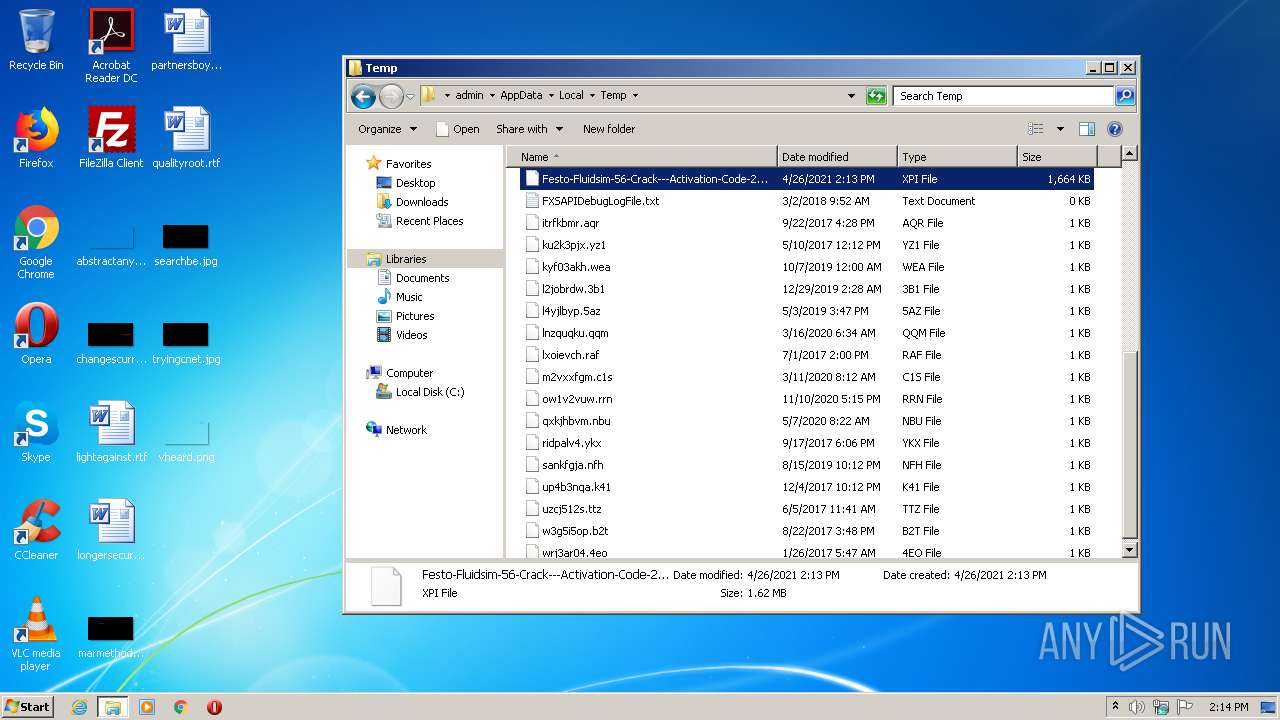
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipFileName: | 6086af182be6760-Passw0rd.txt |
|---|---|
| ZipUncompressedSize: | 12523 |
| ZipCompressedSize: | 1143 |
| ZipCRC: | 0xc4329eba |
| ZipModifyDate: | 2021:04:26 12:16:12 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0002 |
| ZipRequiredVersion: | 20 |
Total processes
57
Monitored processes
14
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1760 | "C:\Windows\System32\makecab.exe" | C:\Windows\System32\makecab.exe | — | setup_x86_x64_install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
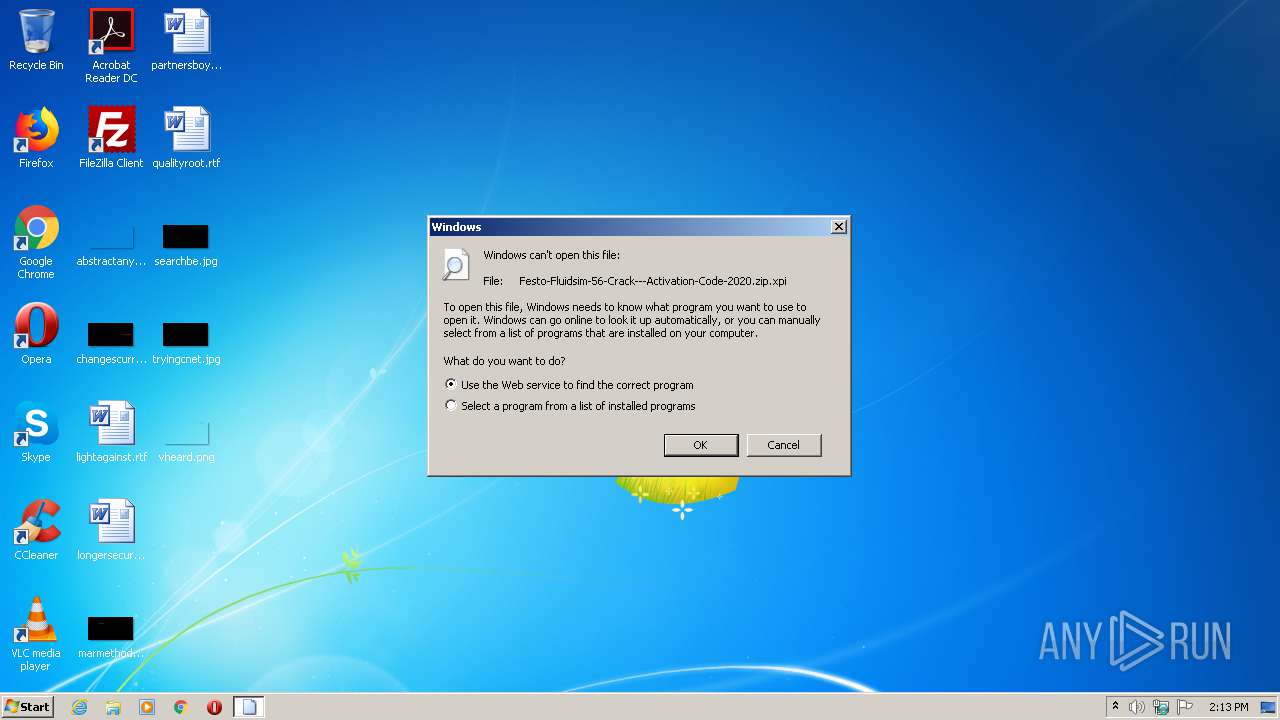
| 1768 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Festo-Fluidsim-56-Crack---Activation-Code-2020.zip.xpi | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2288 | ping 127.0.0.1 -n 30 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
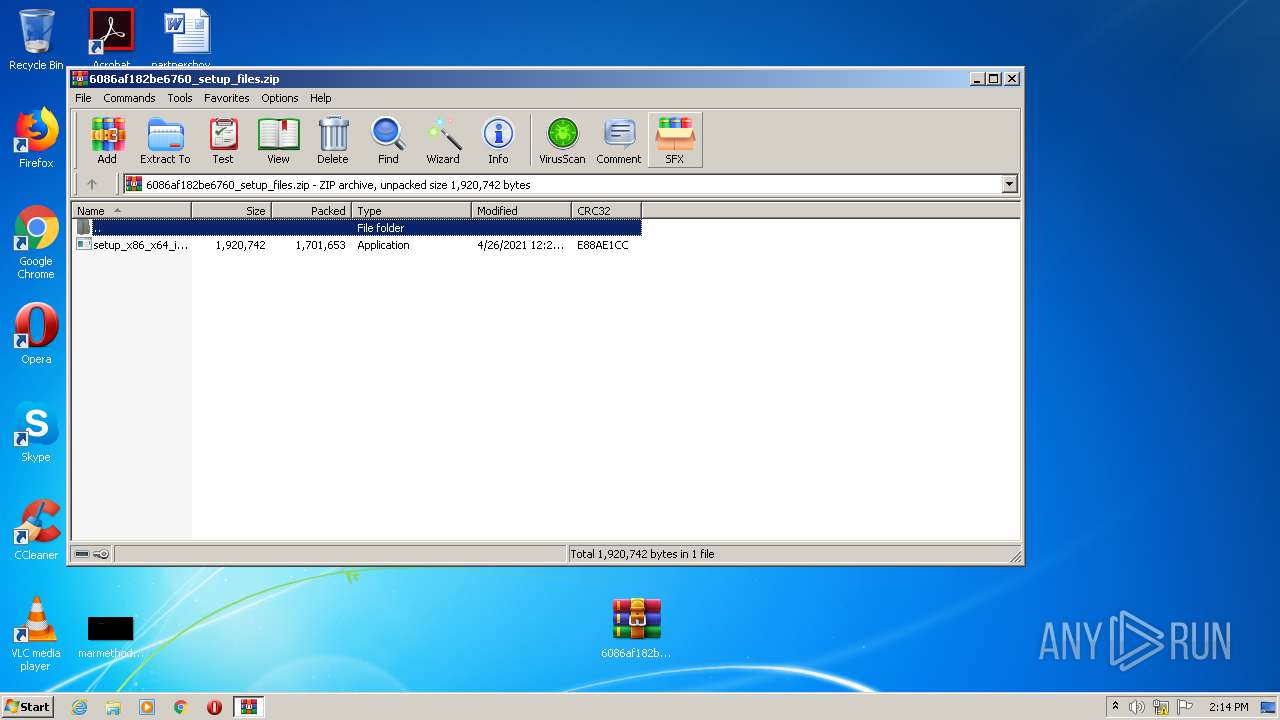
| 2468 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\6086af182be6760_setup_files.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2472 | "C:\Windows\System32\cmd.exe" /c cmd < Nobile.wks | C:\Windows\System32\cmd.exe | — | setup_x86_x64_install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2692 | "C:\Users\admin\Desktop\setup_x86_x64_install.exe" | C:\Users\admin\Desktop\setup_x86_x64_install.exe | — | explorer.exe | |||||||||||
User: admin Company: Oleg N. Scherbakov Integrity Level: MEDIUM Description: 7z Setup SFX (x86) Exit code: 0 Version: 1.7.0.3900 Modules
| |||||||||||||||
| 2844 | San.exe.com O | C:\Users\admin\AppData\Roaming\VnIRZCrXhHTFxrjgslBSeuQslVTqXPLBTjmYRNNPAAeSVQyfURDrPIdOHdHtIrqnWsMoEgbEbLs\San.exe.com | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 3 Modules
| |||||||||||||||
| 3292 | C:\Users\admin\AppData\Roaming\VnIRZCrXhHTFxrjgslBSeuQslVTqXPLBTjmYRNNPAAeSVQyfURDrPIdOHdHtIrqnWsMoEgbEbLs\San.exe.com O | C:\Users\admin\AppData\Roaming\VnIRZCrXhHTFxrjgslBSeuQslVTqXPLBTjmYRNNPAAeSVQyfURDrPIdOHdHtIrqnWsMoEgbEbLs\San.exe.com | — | San.exe.com | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 3 Modules
| |||||||||||||||
| 3416 | cmd | C:\Windows\system32\cmd.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3492 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\6086af182be6760_setup_files.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 391
Read events
1 335
Write events
56
Delete events
0
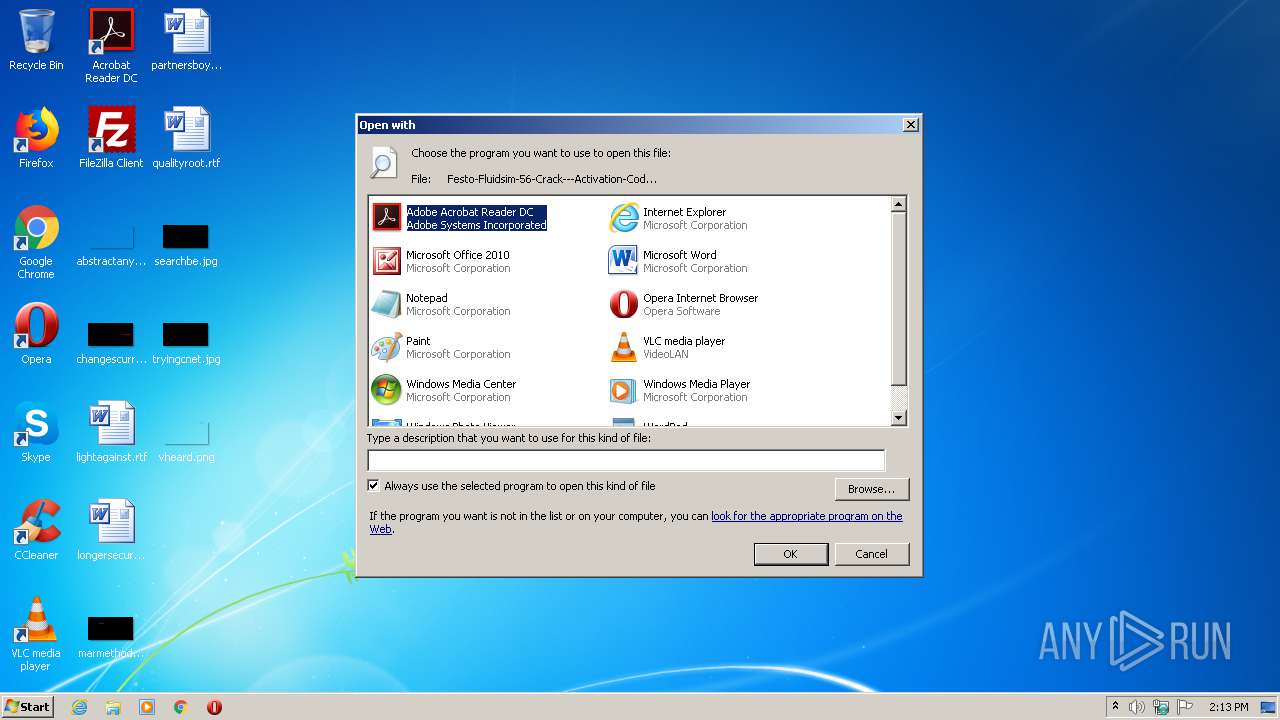
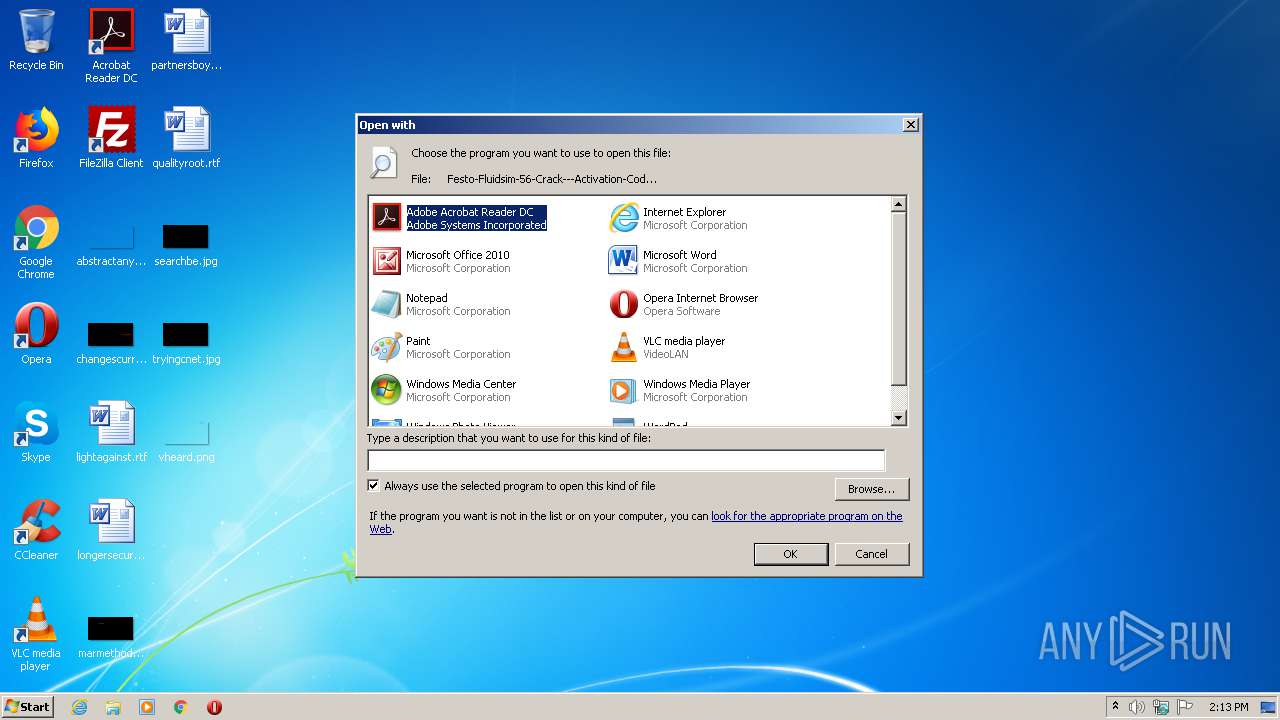
Modification events
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (1768) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3520 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3520.20283\6086af182be6760-Passw0rd.txt | — | |
MD5:— | SHA256:— | |||
| 3520 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3520.20283\6086af182be6760_setup_files.zip | — | |
MD5:— | SHA256:— | |||
| 2468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2468.24606\setup_x86_x64_install.exe | — | |
MD5:— | SHA256:— | |||
| 3416 | cmd.exe | C:\Users\admin\AppData\Roaming\VnIRZCrXhHTFxrjgslBSeuQslVTqXPLBTjmYRNNPAAeSVQyfURDrPIdOHdHtIrqnWsMoEgbEbLs\O | — | |
MD5:— | SHA256:— | |||
| 2692 | setup_x86_x64_install.exe | C:\Users\admin\AppData\Roaming\VnIRZCrXhHTFxrjgslBSeuQslVTqXPLBTjmYRNNPAAeSVQyfURDrPIdOHdHtIrqnWsMoEgbEbLs\Udi.wks | binary | |
MD5:C061093A65D6FC95BD92228C92465410 | SHA256:D1CA304FBBC6949424F6A5400FB82C858237A315E85E29A8715848442F7BE2FB | |||
| 2692 | setup_x86_x64_install.exe | C:\Users\admin\AppData\Roaming\VnIRZCrXhHTFxrjgslBSeuQslVTqXPLBTjmYRNNPAAeSVQyfURDrPIdOHdHtIrqnWsMoEgbEbLs\Roccia.wks | text | |
MD5:AE0F60AEB4512311580375E37DCEF6E6 | SHA256:2CD33E595449177BD2789093A5D81041CE366DC5D51BB90928C3A767FF45FE5D | |||
| 2692 | setup_x86_x64_install.exe | C:\Users\admin\AppData\Roaming\VnIRZCrXhHTFxrjgslBSeuQslVTqXPLBTjmYRNNPAAeSVQyfURDrPIdOHdHtIrqnWsMoEgbEbLs\Sembrava.wks | binary | |
MD5:7042B91459951CAA10D5A2FE0510EFBE | SHA256:D3AF50827E69C750215F5909FA182712555852D9DC7B47B8BCCAC9B5020F51C2 | |||
| 2692 | setup_x86_x64_install.exe | C:\Users\admin\AppData\Roaming\VnIRZCrXhHTFxrjgslBSeuQslVTqXPLBTjmYRNNPAAeSVQyfURDrPIdOHdHtIrqnWsMoEgbEbLs\Nobile.wks | text | |
MD5:5B3617416C03684C636506FE4600EB34 | SHA256:689908FA4894B05E374160DDACC7467064A447ECAF0BA2A211AA2768E9657896 | |||
| 3416 | cmd.exe | C:\Users\admin\AppData\Roaming\VnIRZCrXhHTFxrjgslBSeuQslVTqXPLBTjmYRNNPAAeSVQyfURDrPIdOHdHtIrqnWsMoEgbEbLs\San.exe.com | executable | |
MD5:78BA0653A340BAC5FF152B21A83626CC | SHA256:05D8CF394190F3A707ABFB25FB44D7DA9D5F533D7D2063B23C00CC11253C8BE7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
rPQhGbsCezZGIalgmIBVnKTu.rPQhGbsCezZGIalgmIBVnKTu |
| unknown |