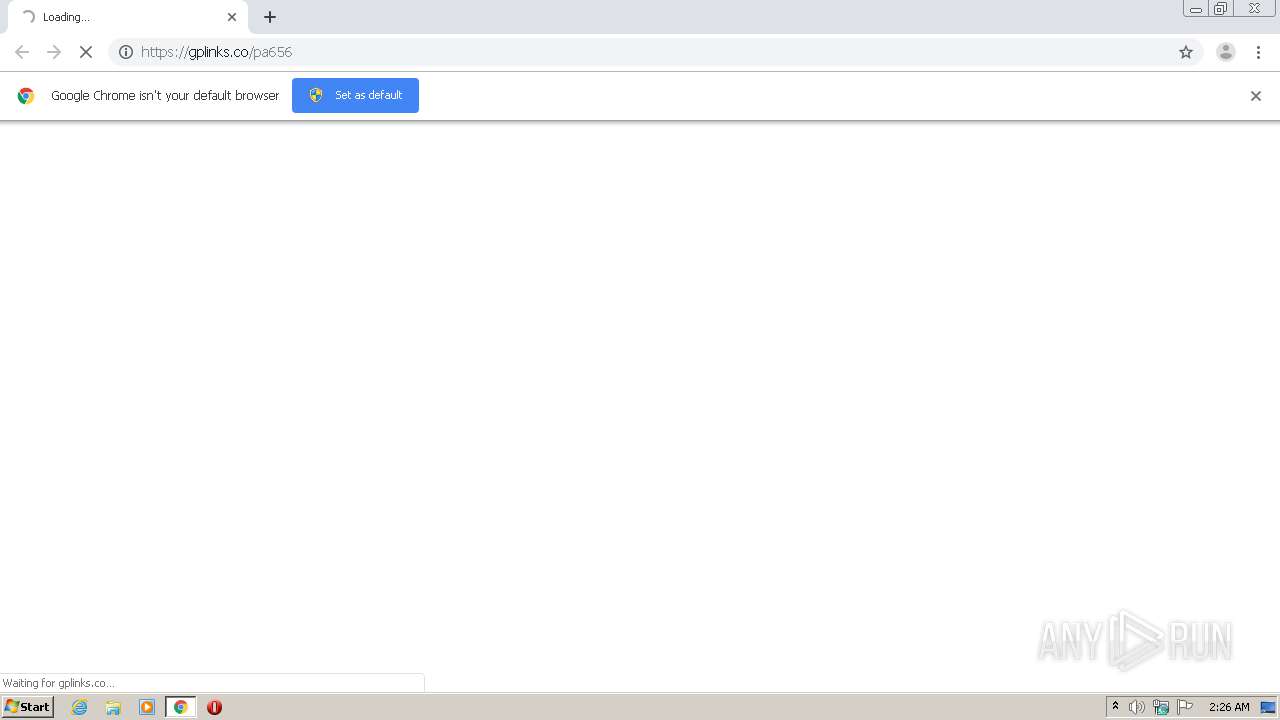
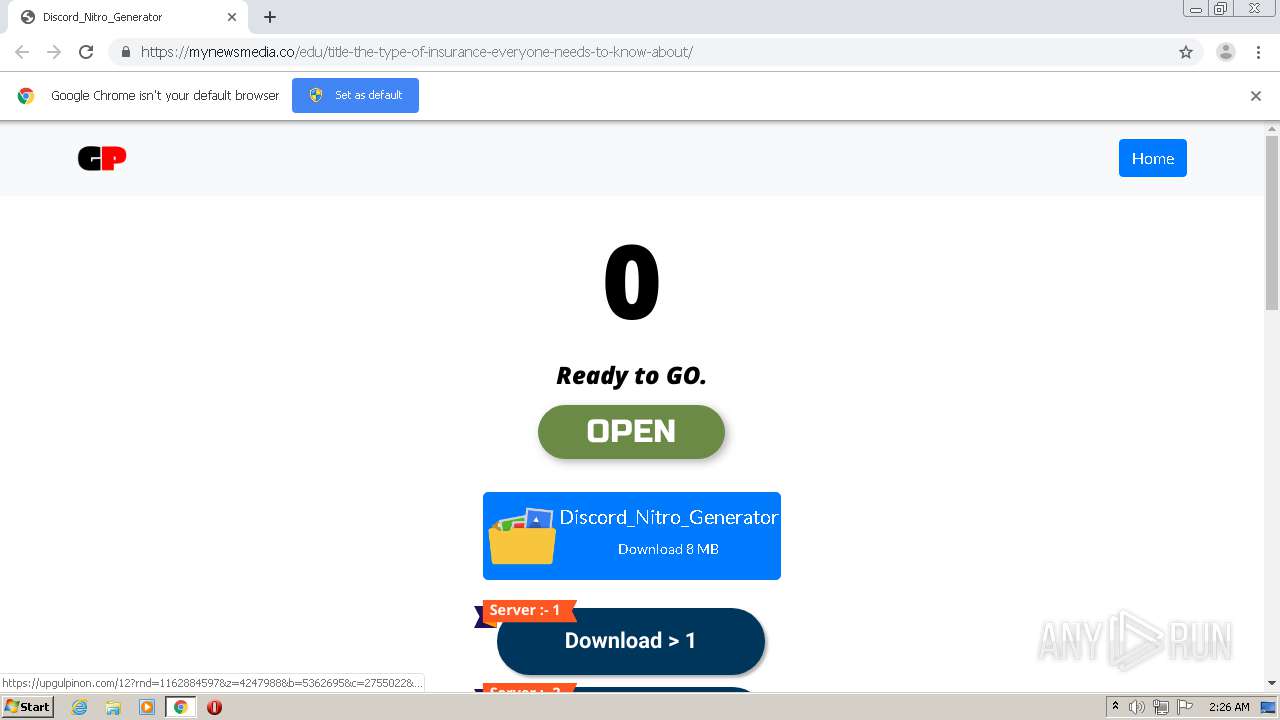
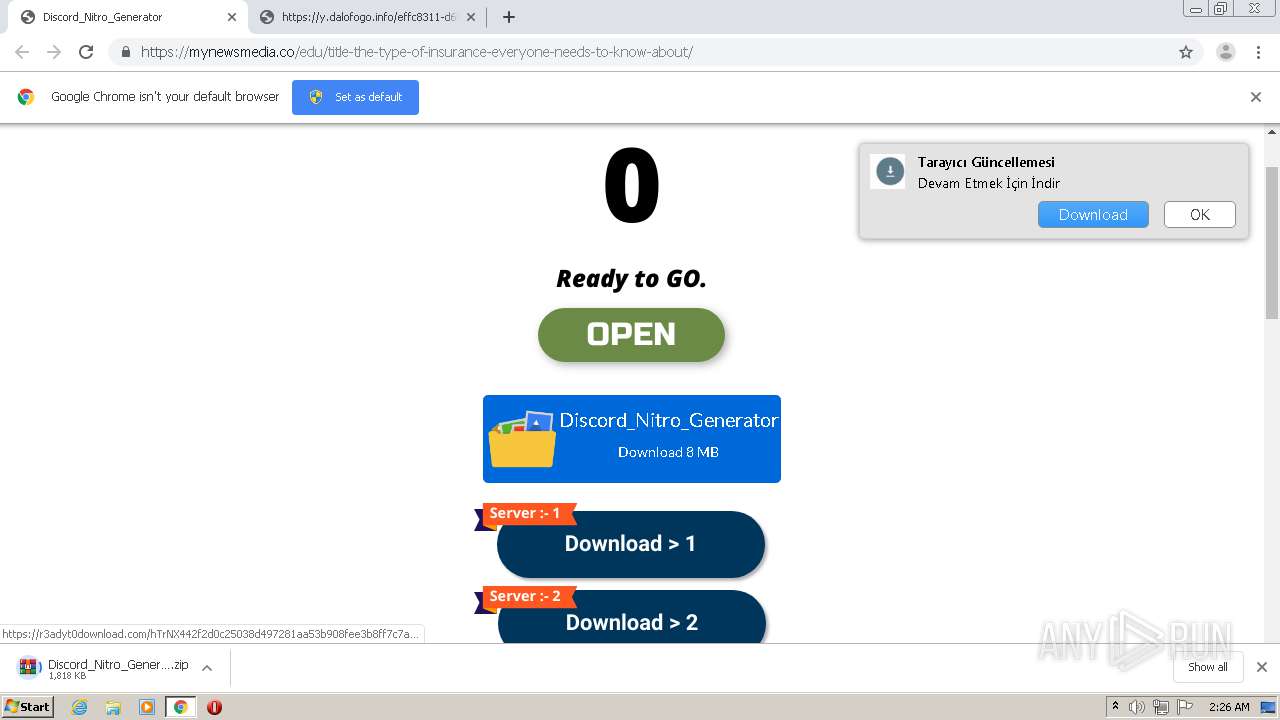
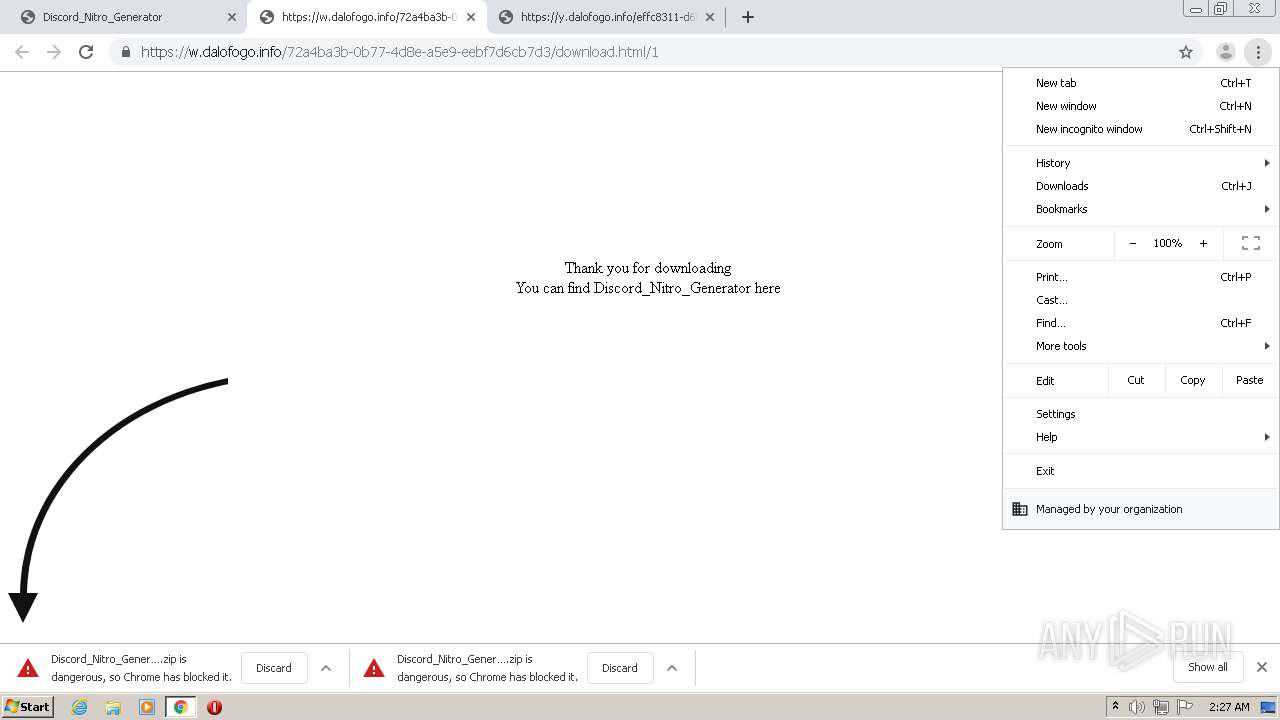
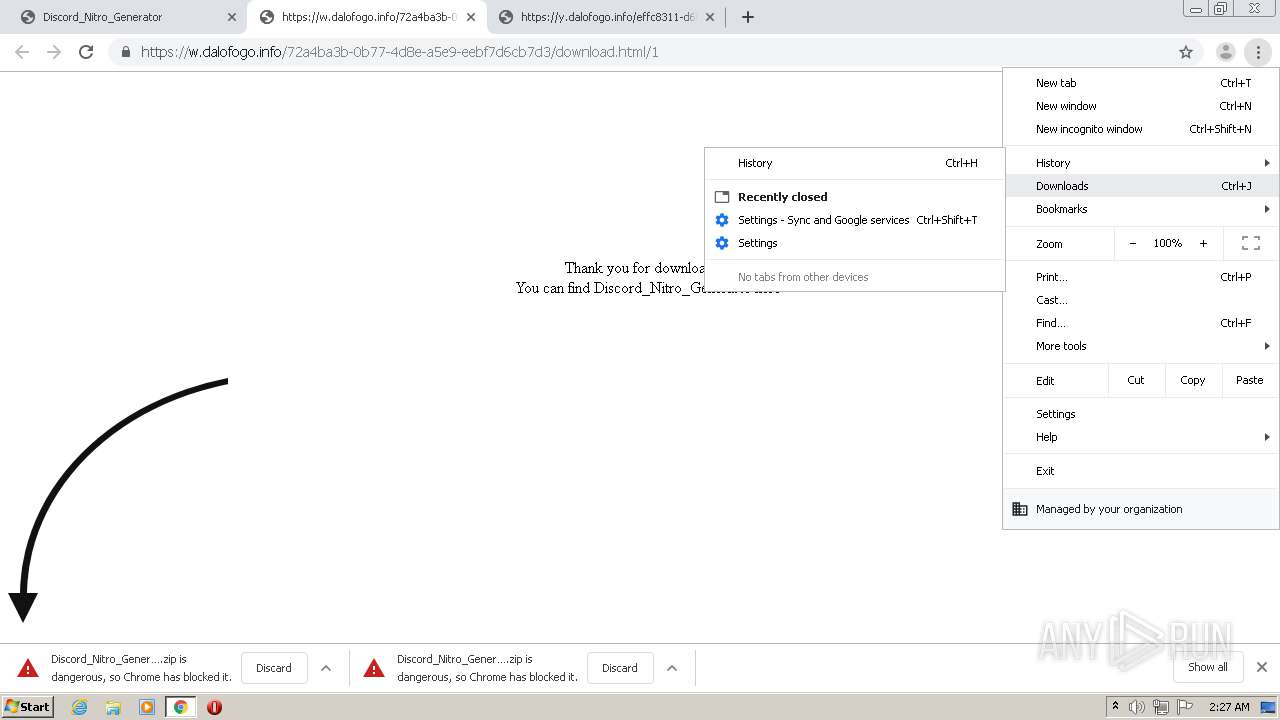
| URL: | https://gplinks.co/pa656 |
| Full analysis: | https://app.any.run/tasks/cb84a0c8-99eb-447a-9673-502310955d53 |
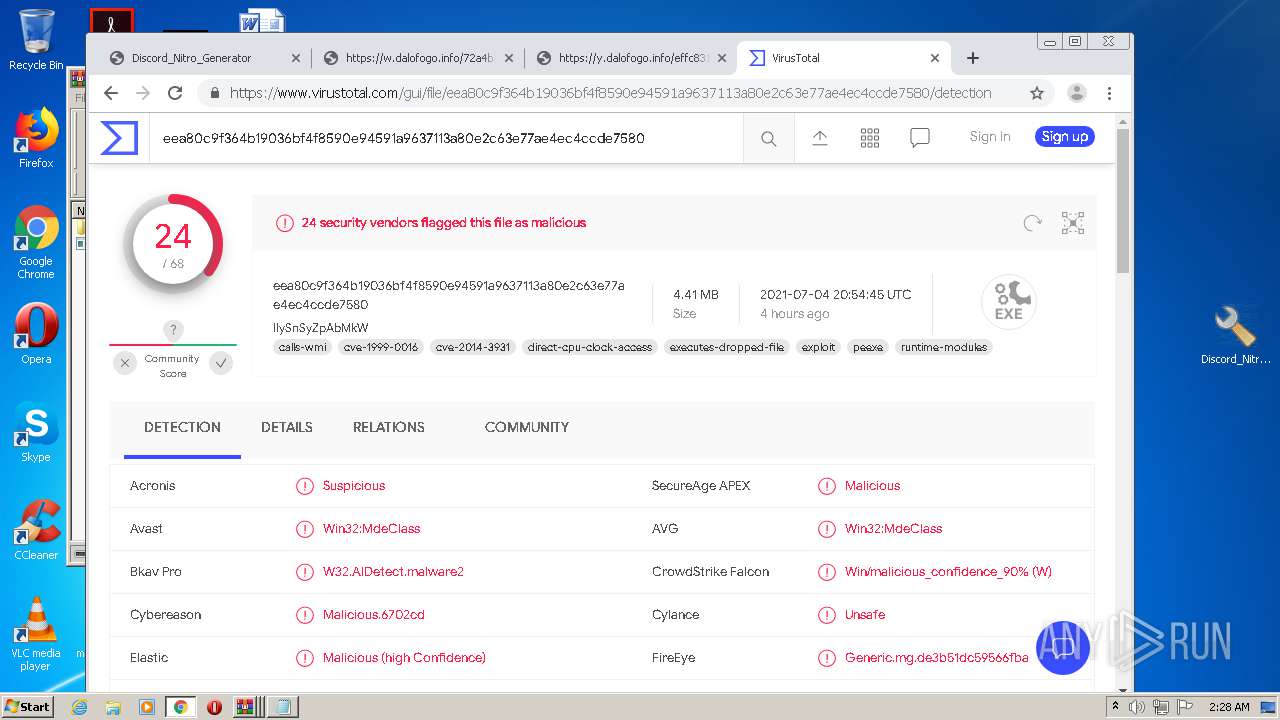
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2021, 01:26:13 |
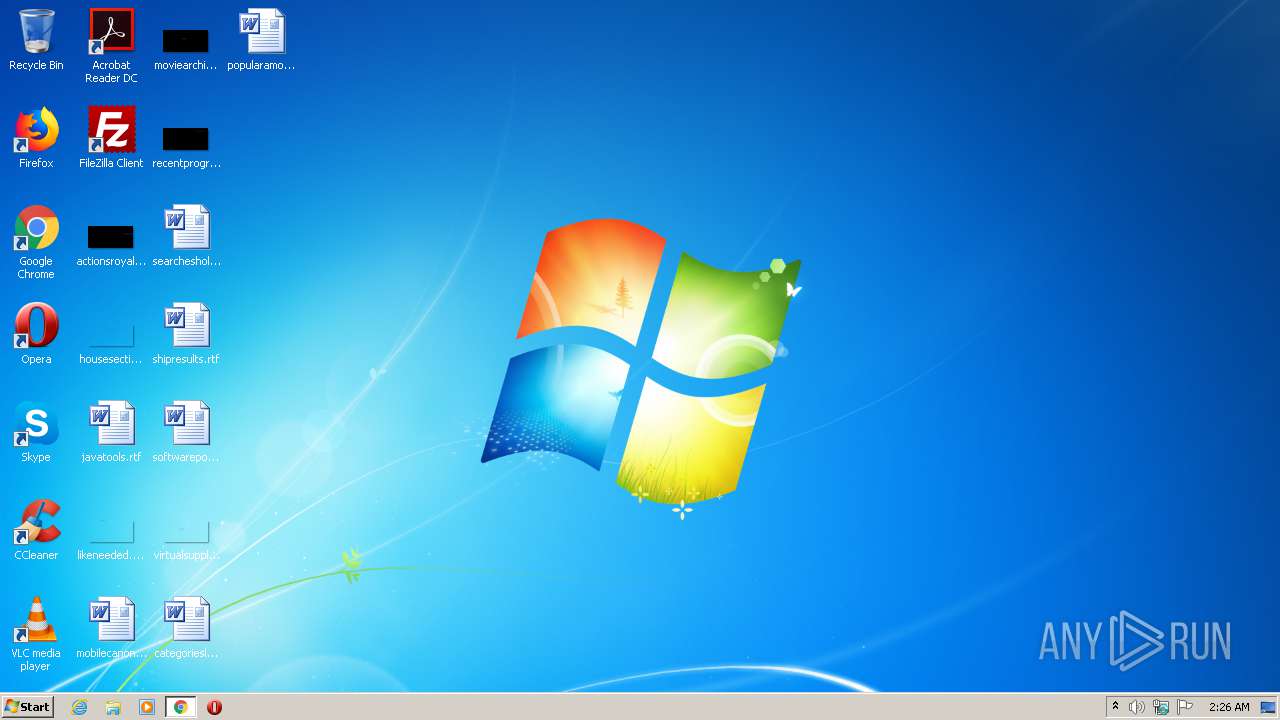
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 97A5279A939AA7222C0206E02408DB58 |
| SHA1: | D334742AA1750DEA4D54E2198F8EBA4799CBC4B5 |
| SHA256: | 883A1EC6F106AF49892C781B3A742DCA68B488BE7BD36C0202E64192AC2C7446 |
| SSDEEP: | 3:N80Irm:20Wm |
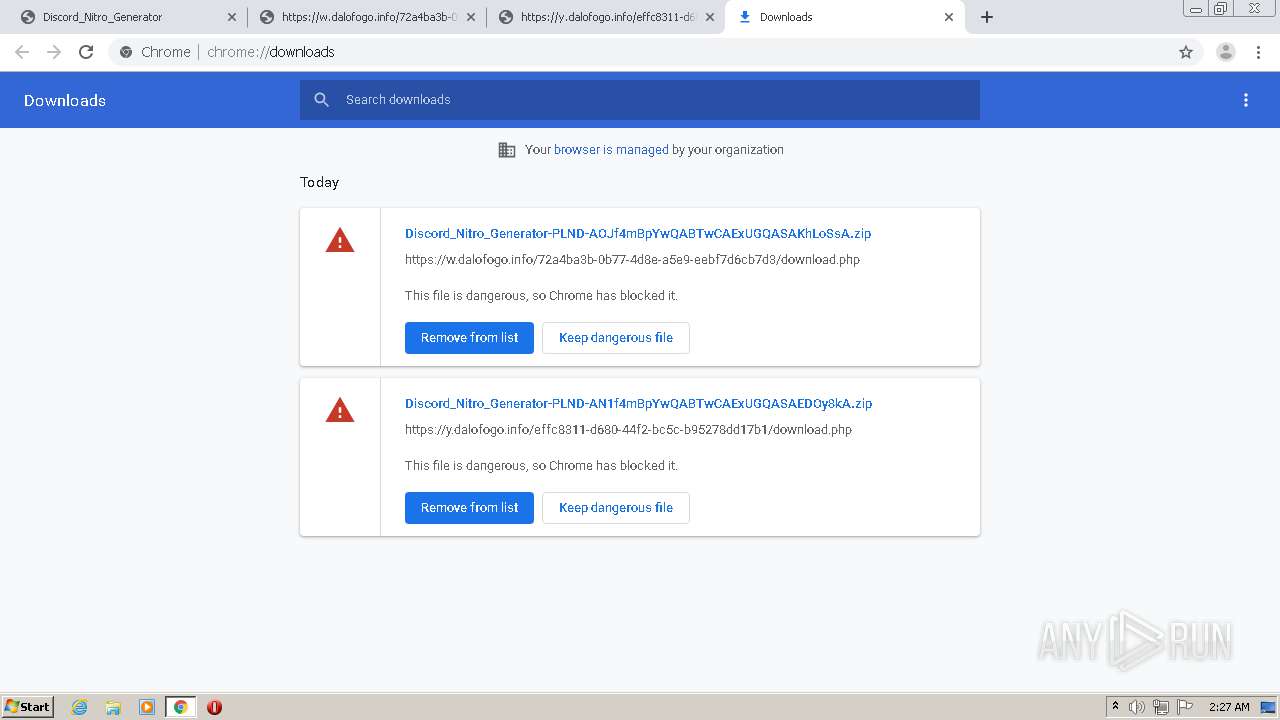
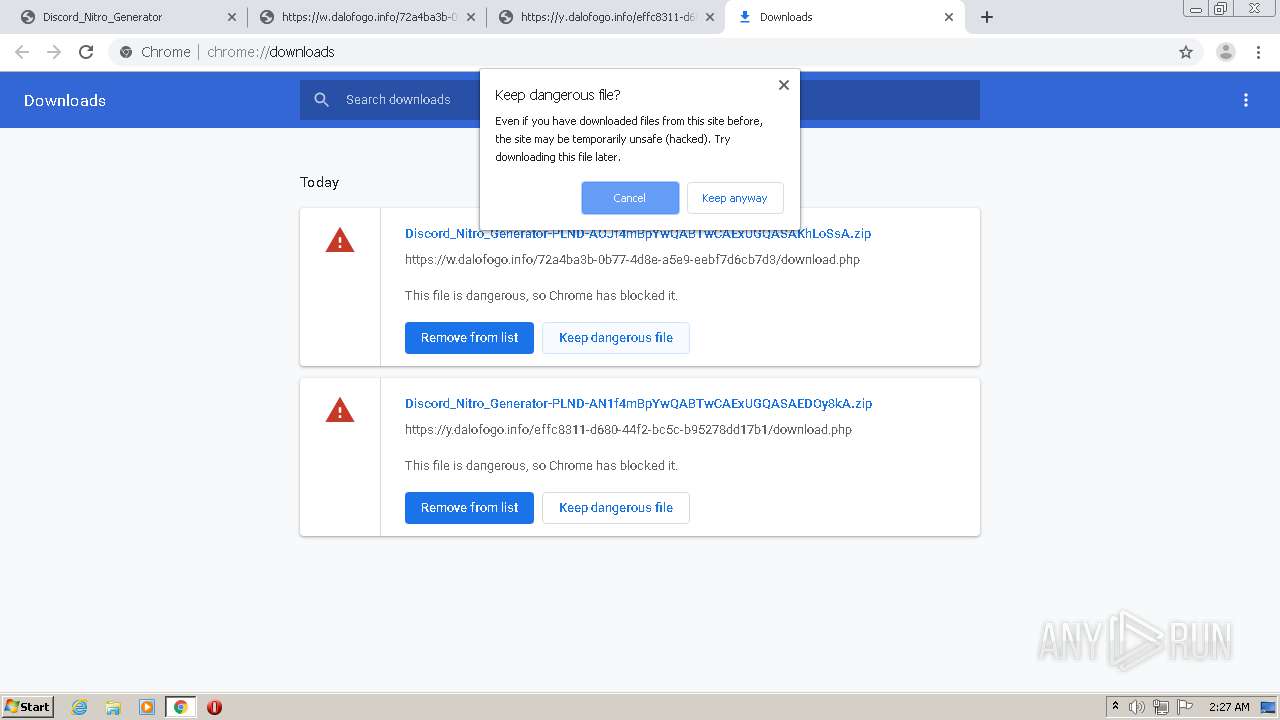
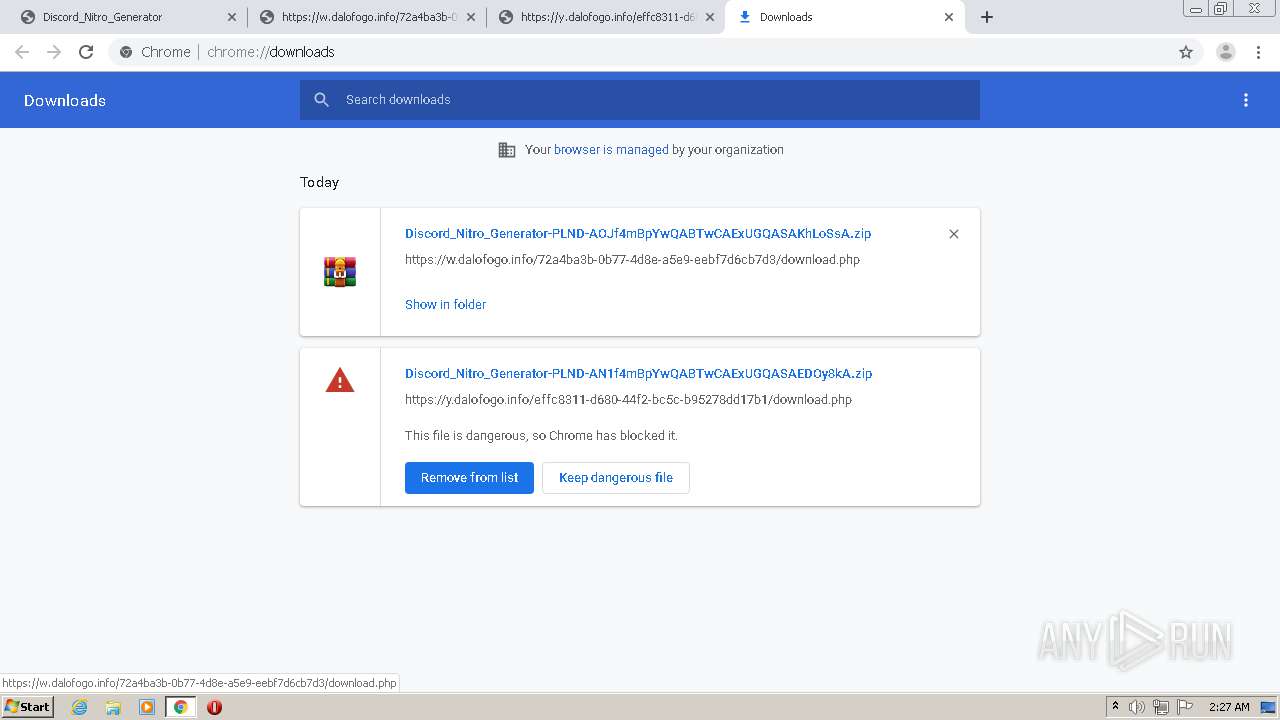
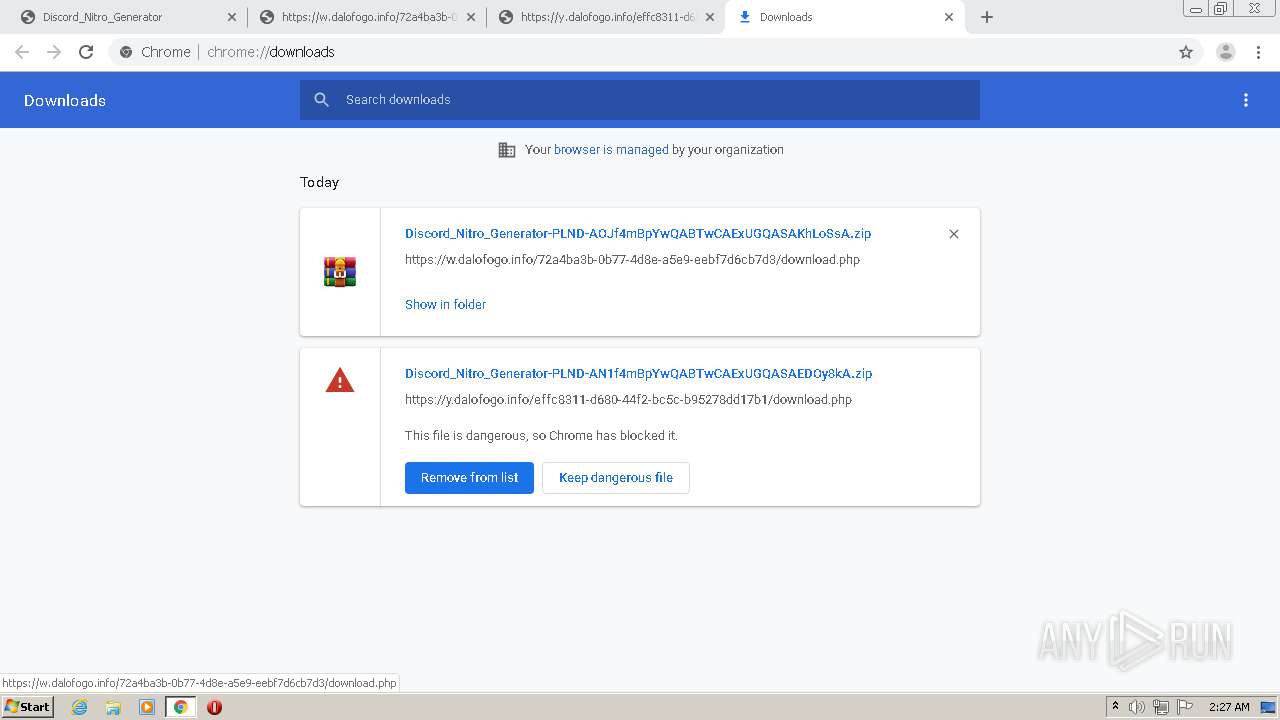
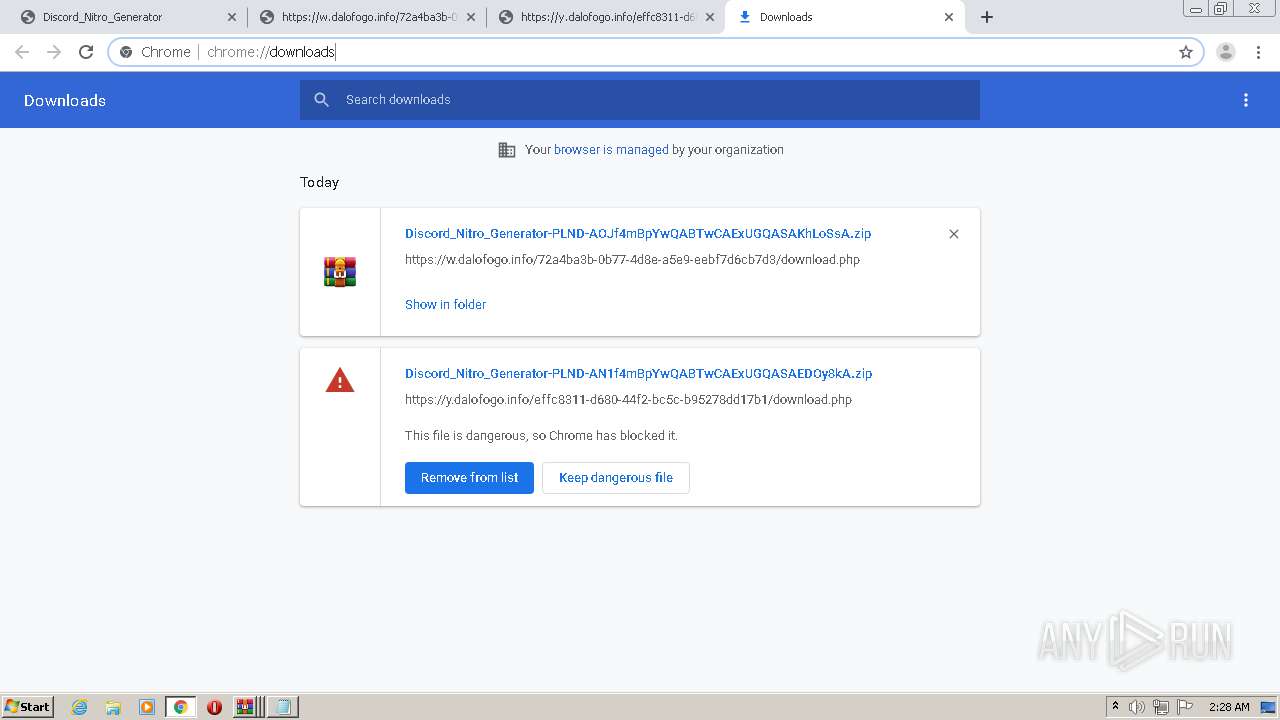
MALICIOUS
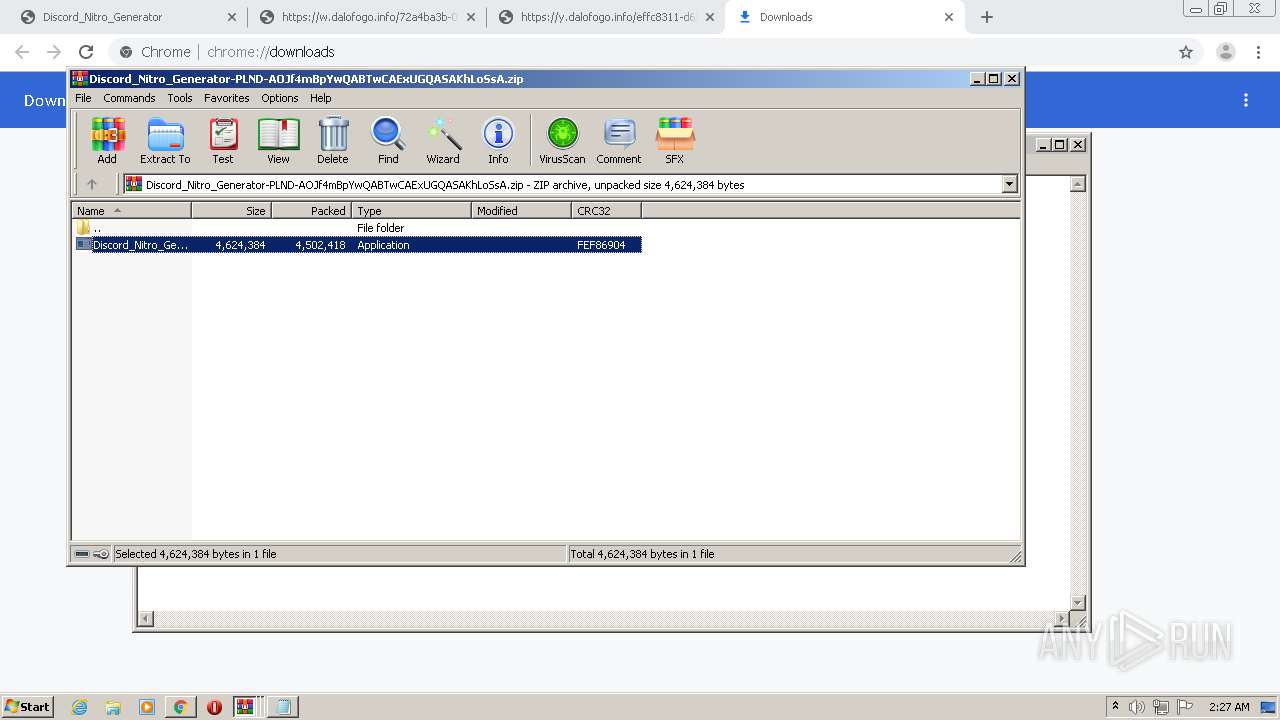
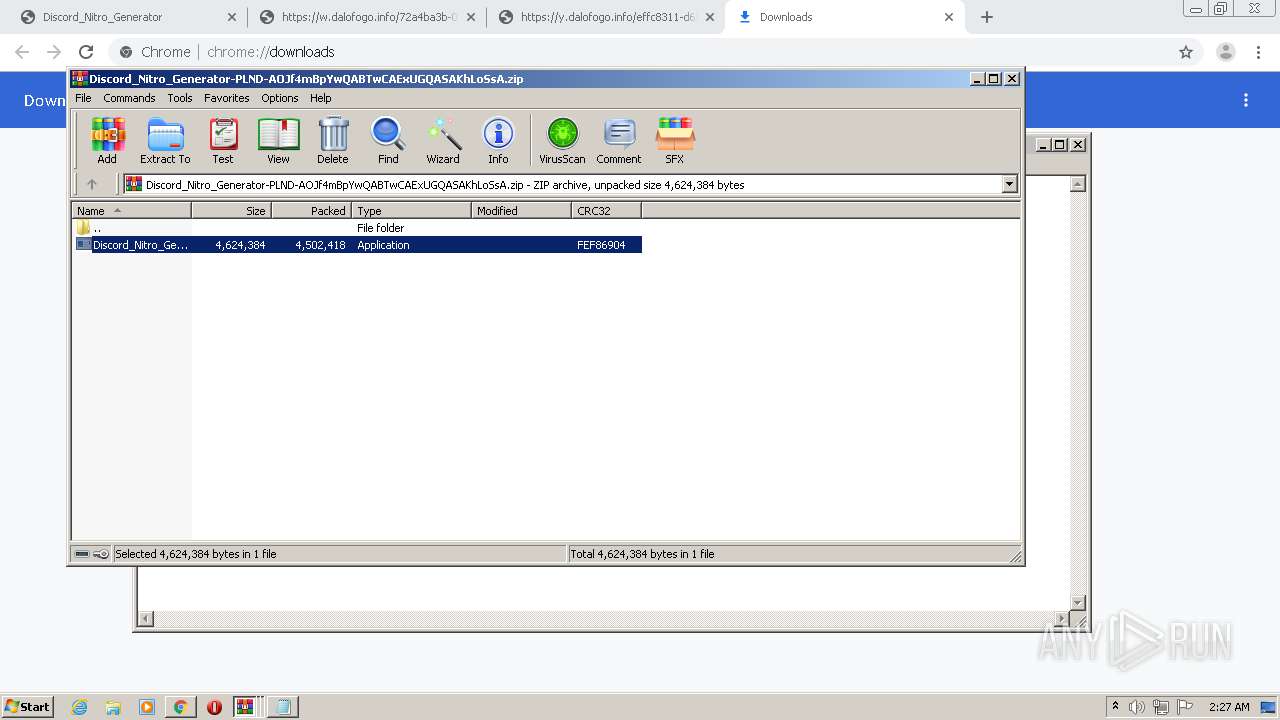
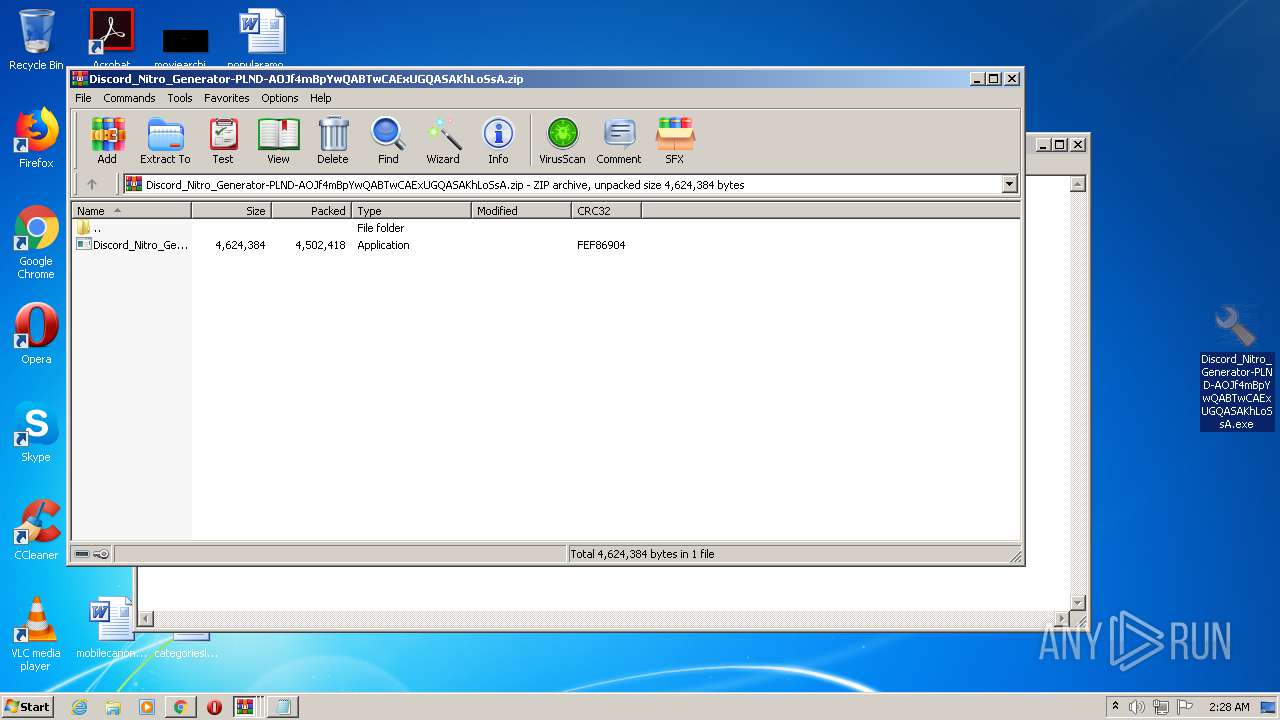
Application was dropped or rewritten from another process
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3624)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3928)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3632)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 1360)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3712)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 1836)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3012)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3288)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 2252)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 692)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 312)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 632)
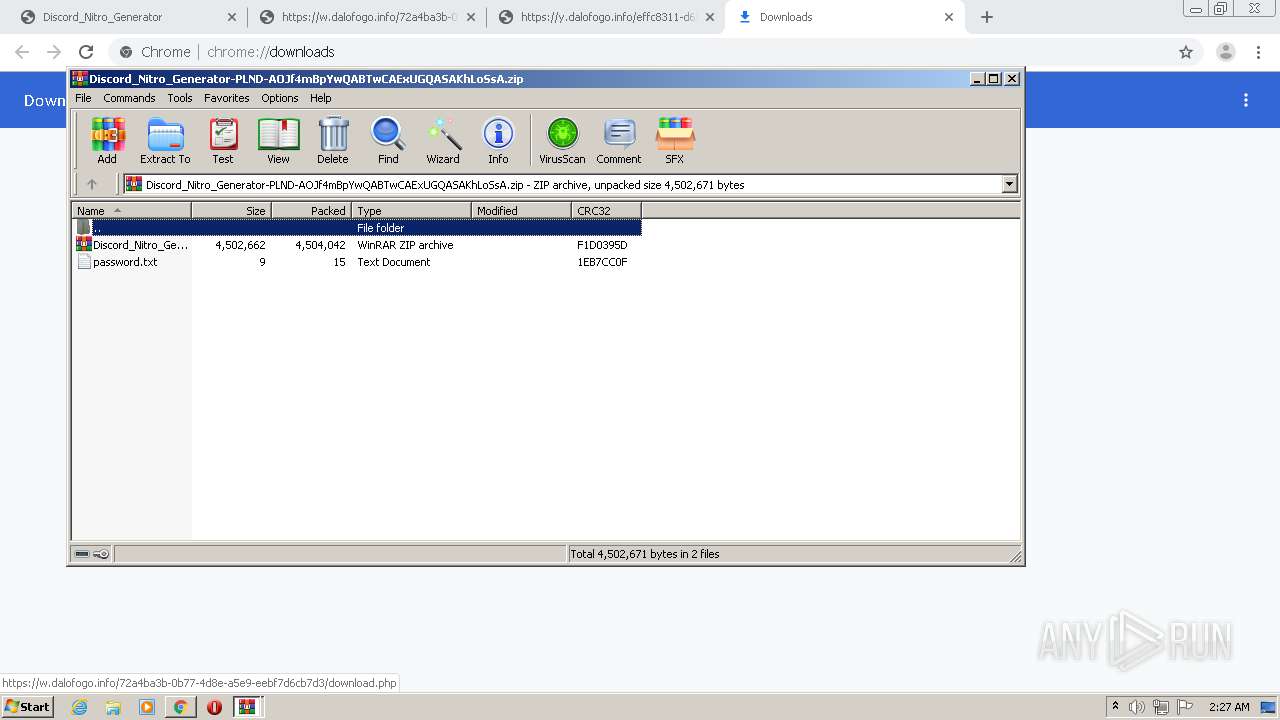
SUSPICIOUS
Application launched itself
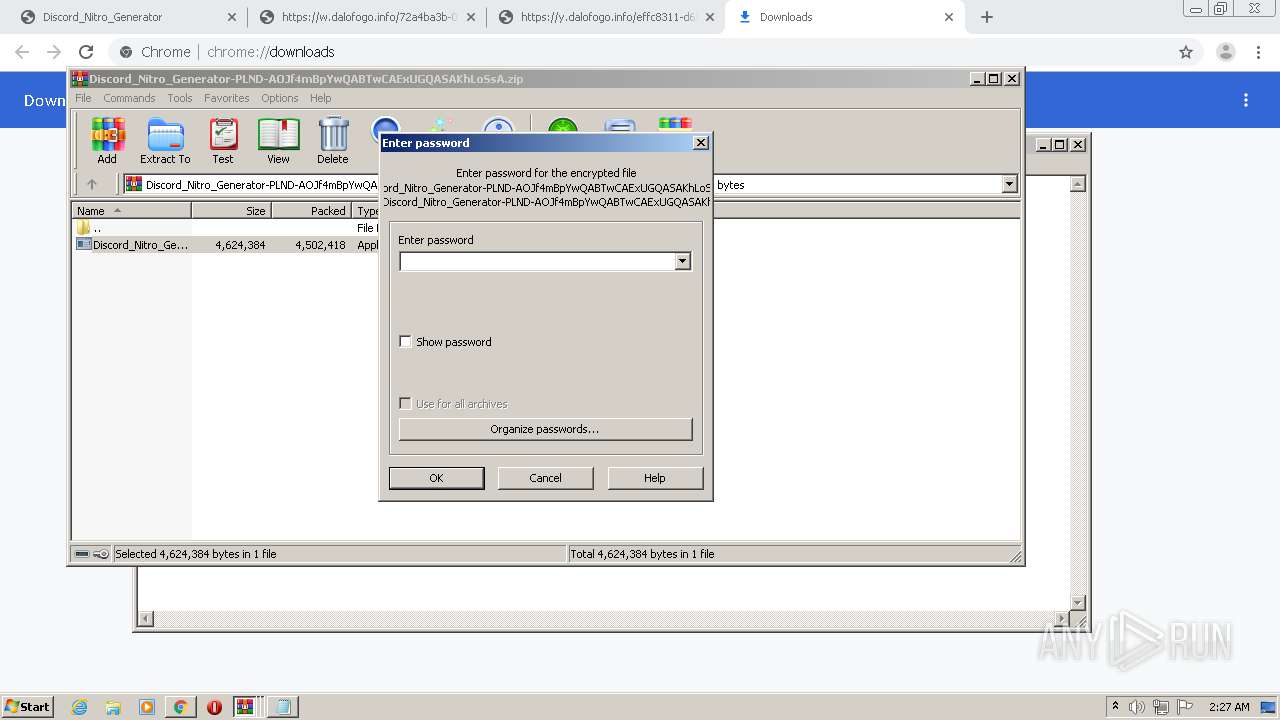
- WinRAR.exe (PID: 2156)
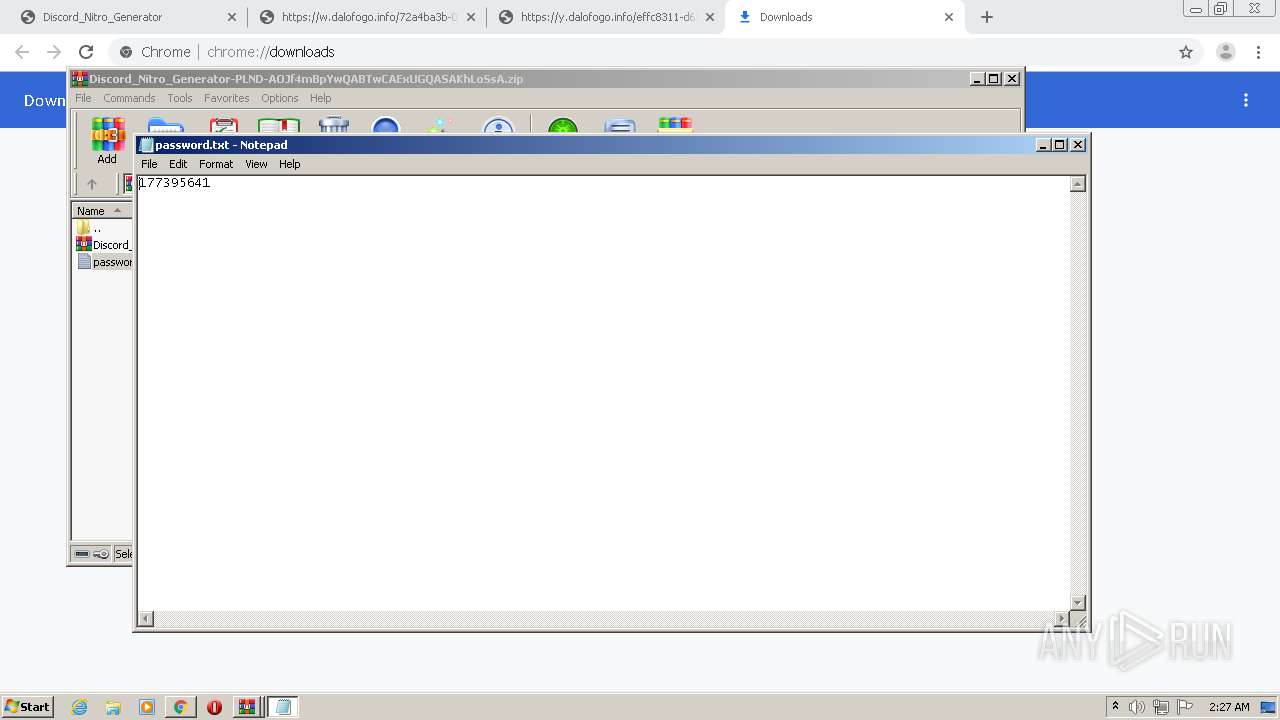
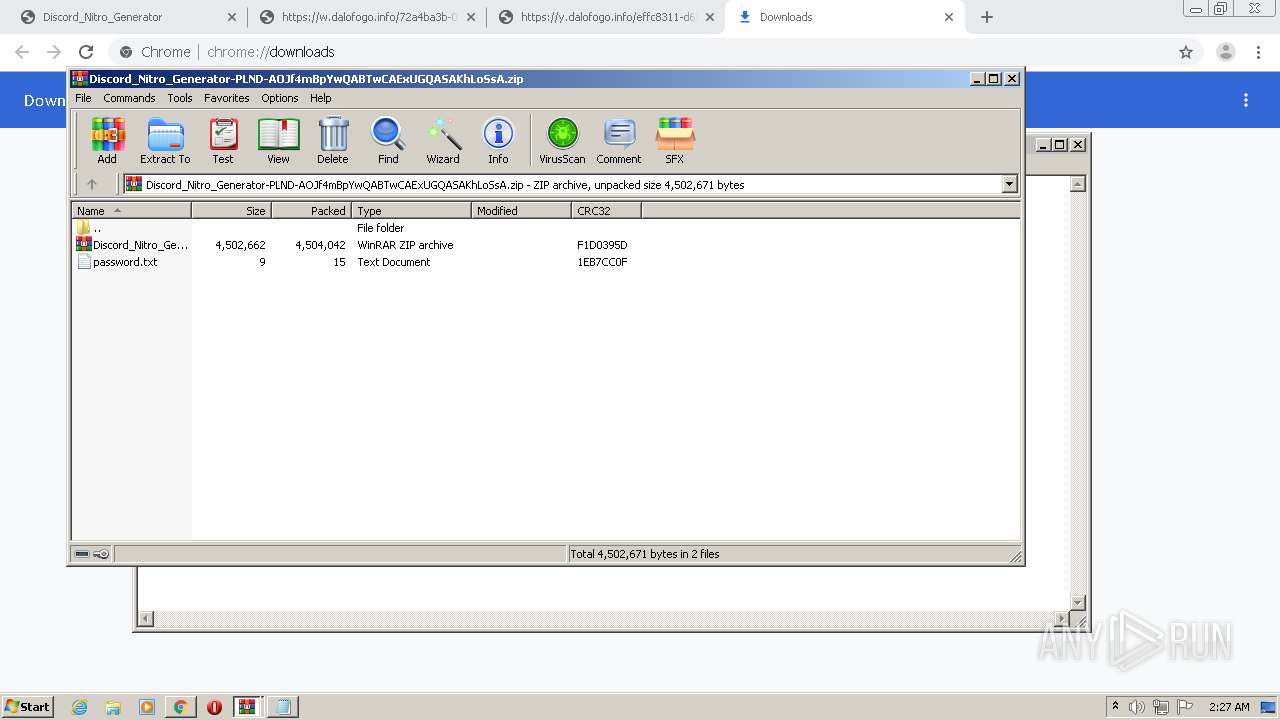
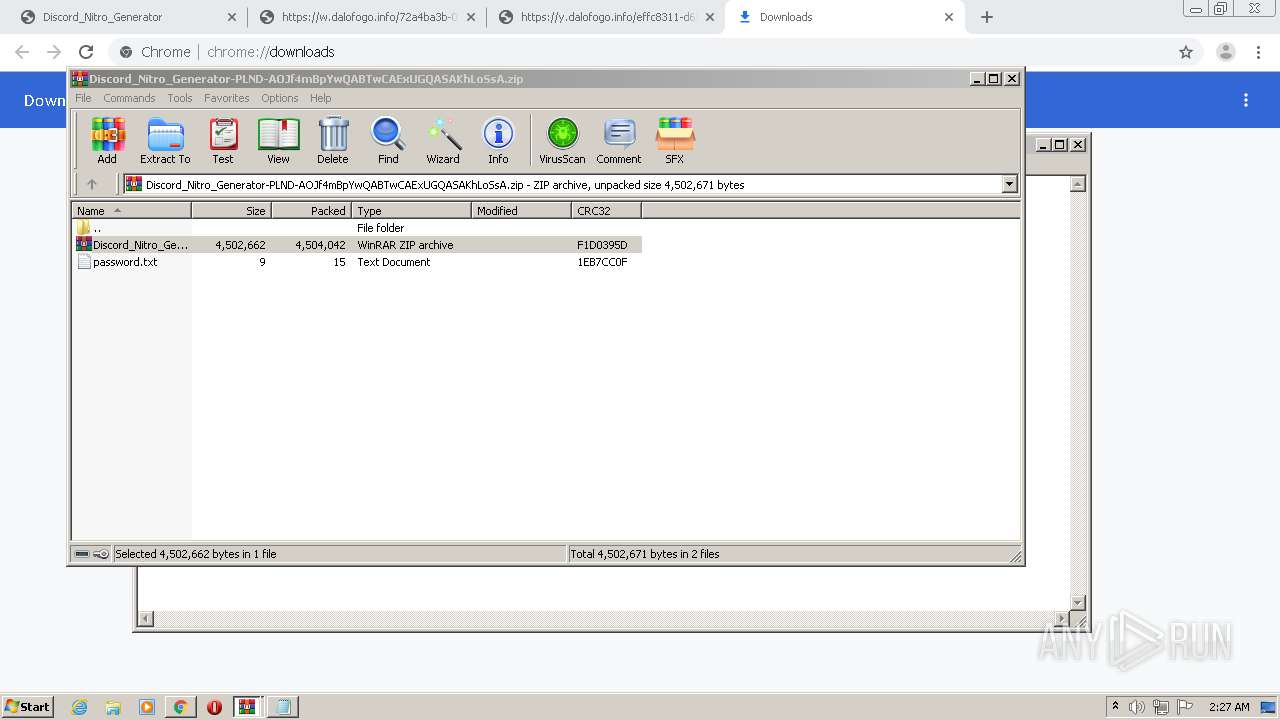
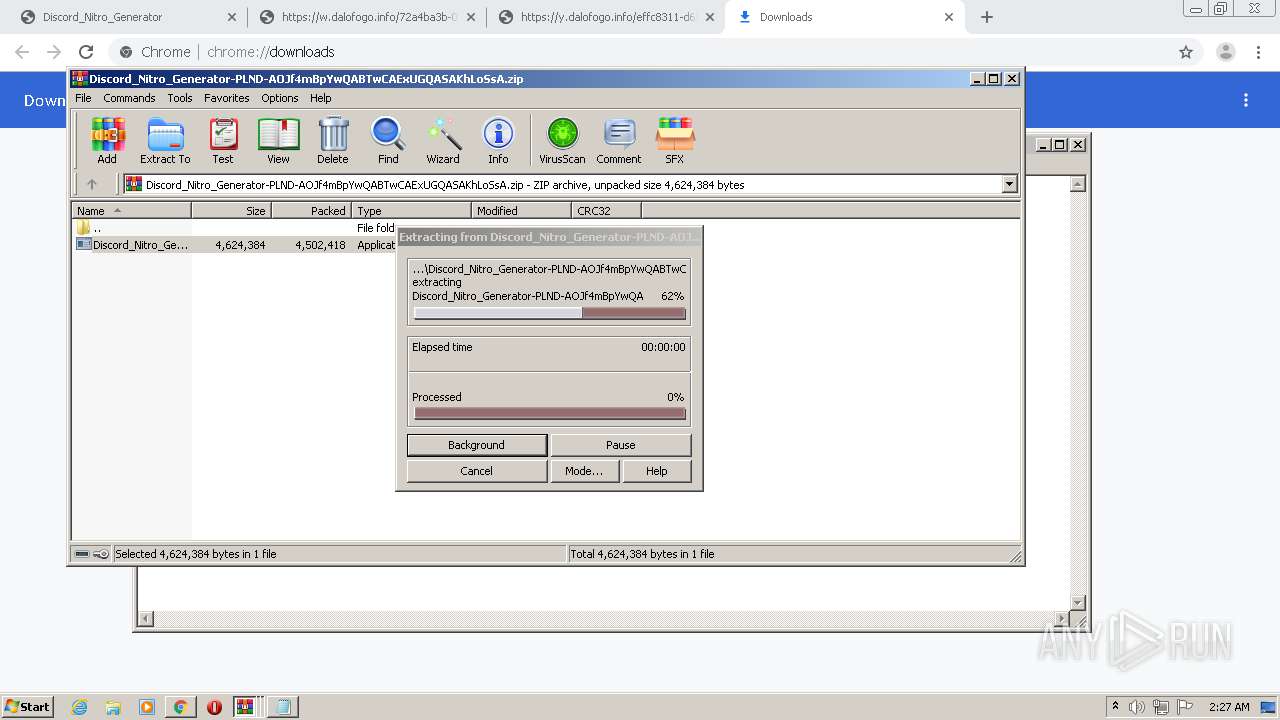
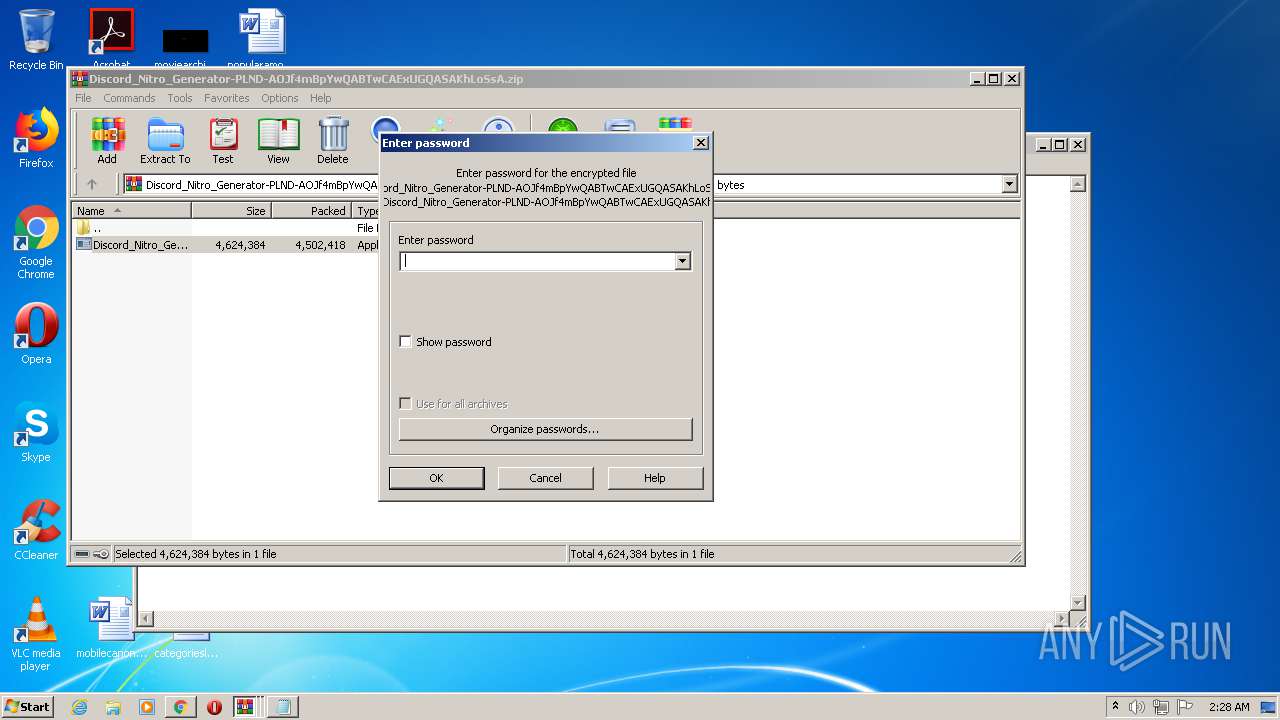
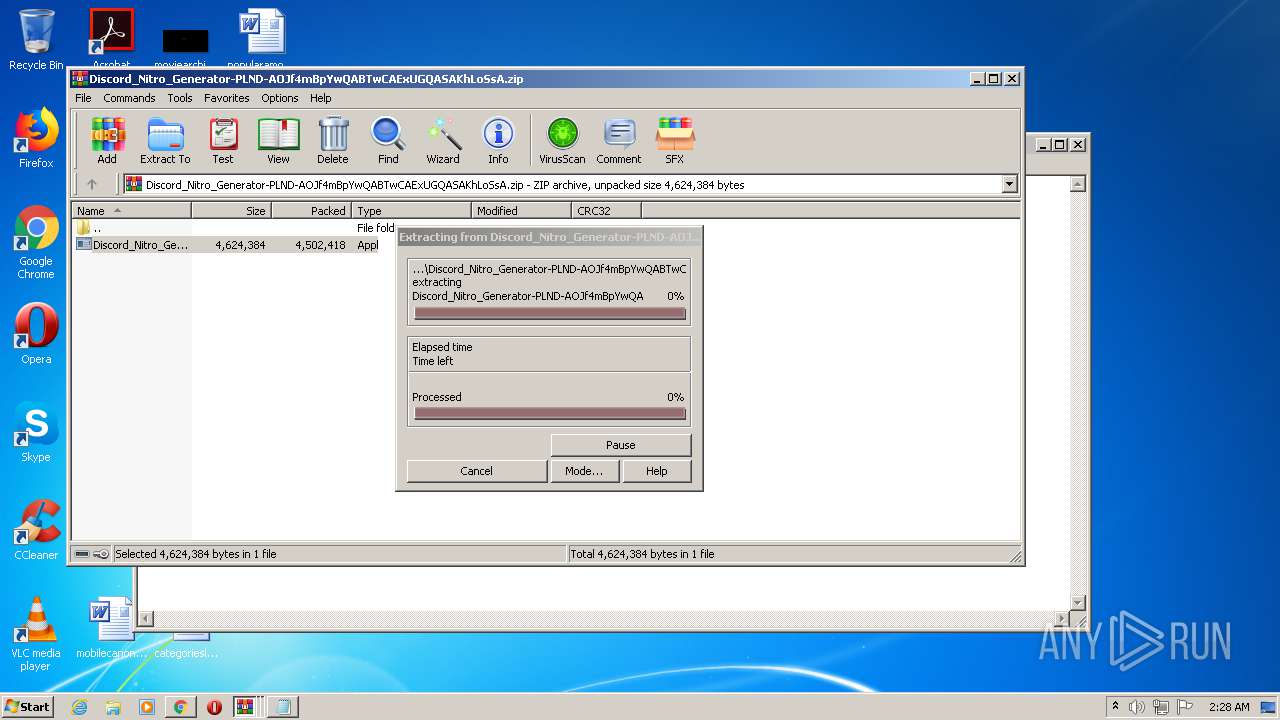
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2432)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2432)
INFO
Application launched itself
- chrome.exe (PID: 1504)
Reads the hosts file
- chrome.exe (PID: 1504)
- chrome.exe (PID: 2640)
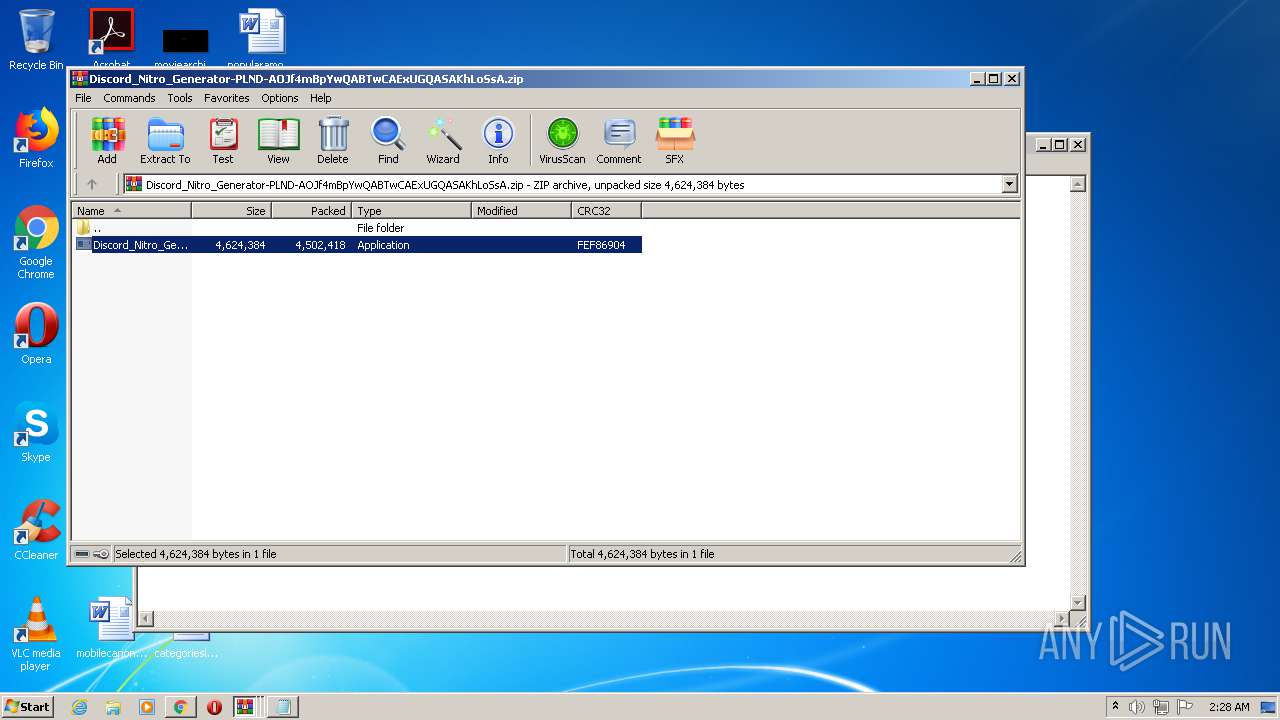
Manual execution by user
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3928)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3632)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 1360)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3712)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 1836)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3012)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 3288)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 692)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 312)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 2252)
- Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe (PID: 632)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
41
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Users\admin\Desktop\Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe" | C:\Users\admin\Desktop\Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,218637319945098761,9810336343855403186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7142379358140677457 --mojo-platform-channel-handle=4256 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 632 | "C:\Users\admin\Desktop\Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe" | C:\Users\admin\Desktop\Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 692 | "C:\Users\admin\Desktop\Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe" | C:\Users\admin\Desktop\Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,218637319945098761,9810336343855403186,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7122160807835694521 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1360 | "C:\Users\admin\Desktop\Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe" | C:\Users\admin\Desktop\Discord_Nitro_Generator-PLND-AOJf4mBpYwQABTwCAExUGQASAKhLoSsA.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,218637319945098761,9810336343855403186,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10457812293866440377 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,218637319945098761,9810336343855403186,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18364825832397171870 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://gplinks.co/pa656" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,218637319945098761,9810336343855403186,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6693849348123229498 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 734
Read events
2 617
Write events
114
Delete events
3
Modification events
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1504-13269921985074500 |
Value: 259 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
70
Text files
160
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60E25FC1-5E0.pma | — | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cf921269-383c-4e69-9437-3c999938bda1.tmp | — | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF18a18a.TMP | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:E815400F953EA8DB8A98D52737C9A50D | SHA256:E9F064927A191500B7365F51C9CD0763A6A8E68A8B866ACED39AA0E72C3EAD85 | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18a340.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
83
DNS requests
50
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
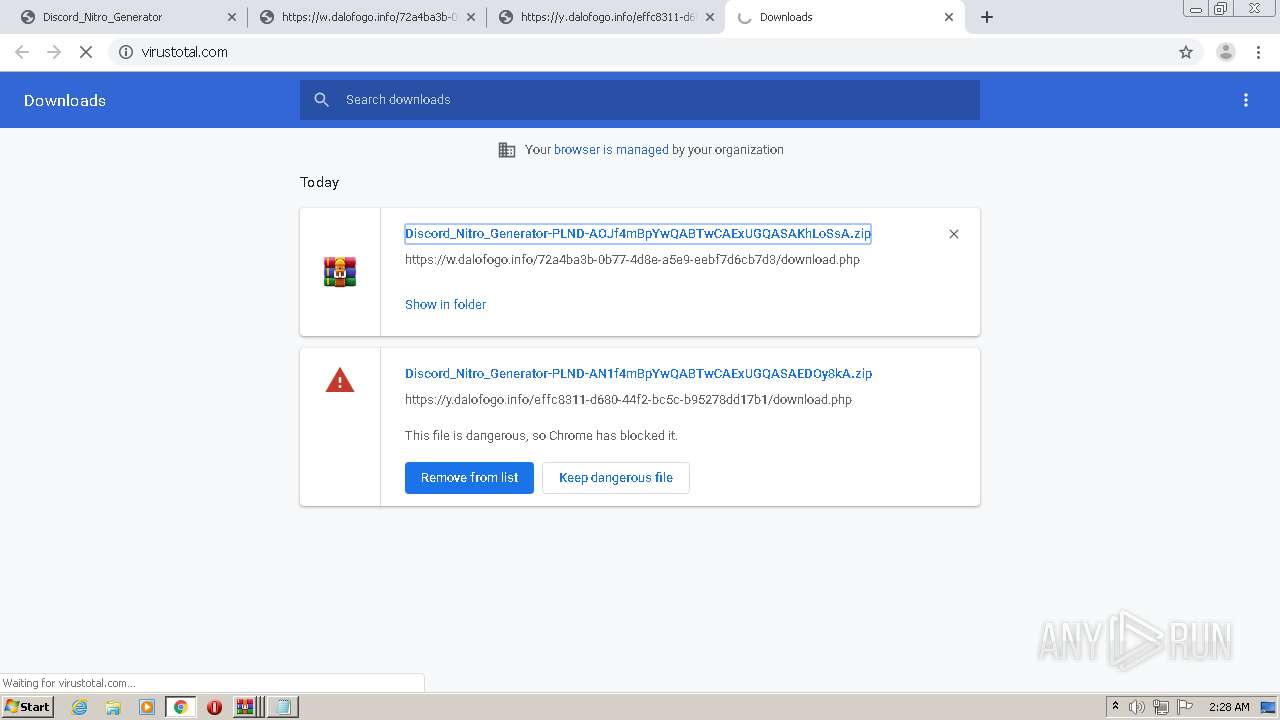
2640 | chrome.exe | GET | 302 | 216.239.38.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
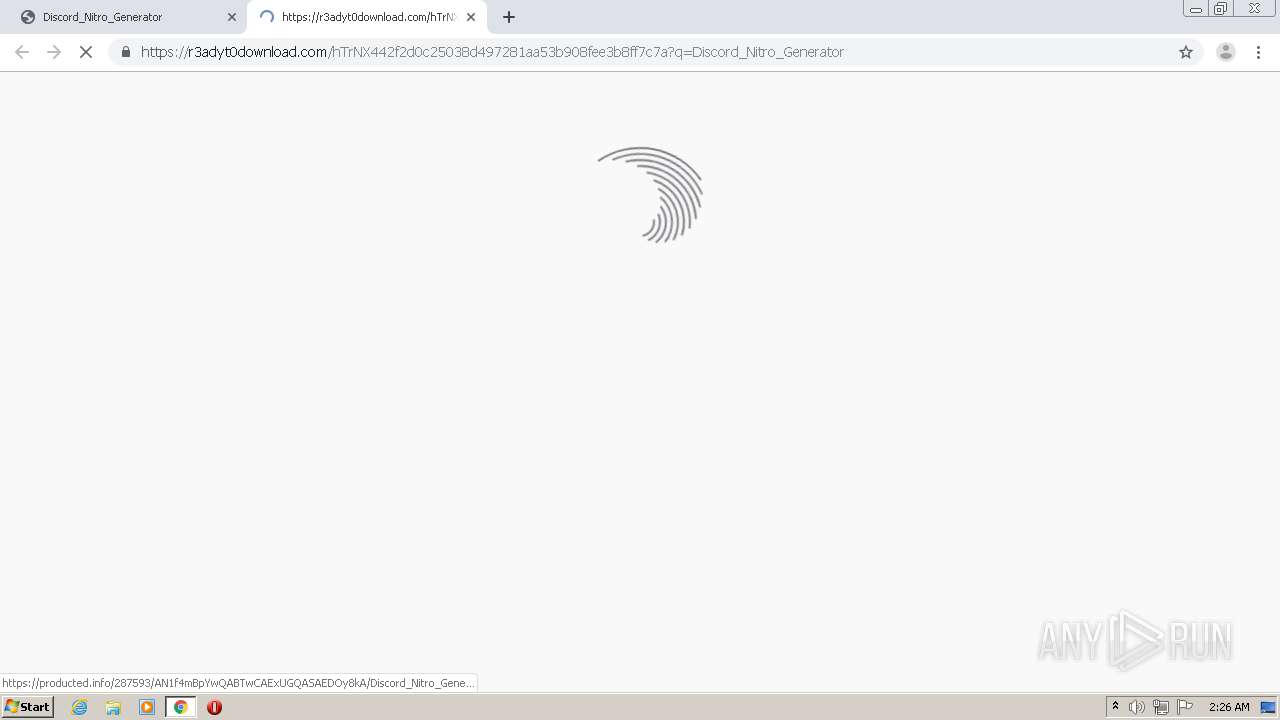
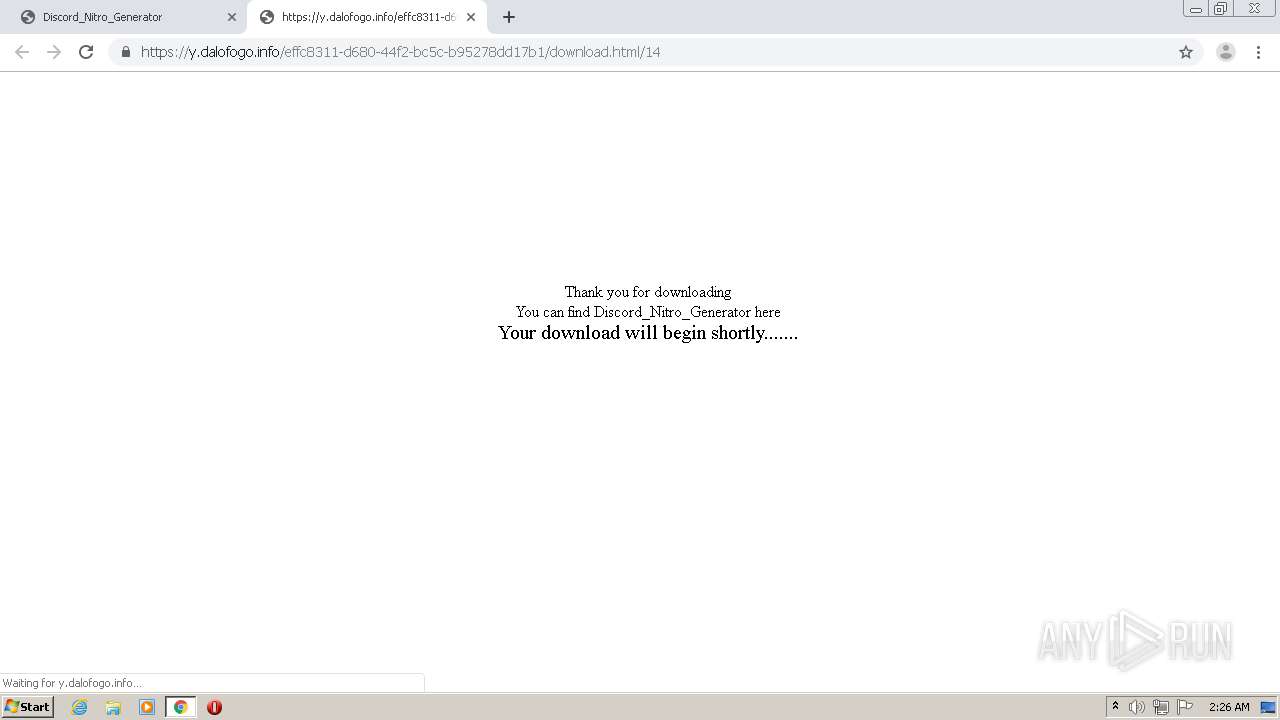
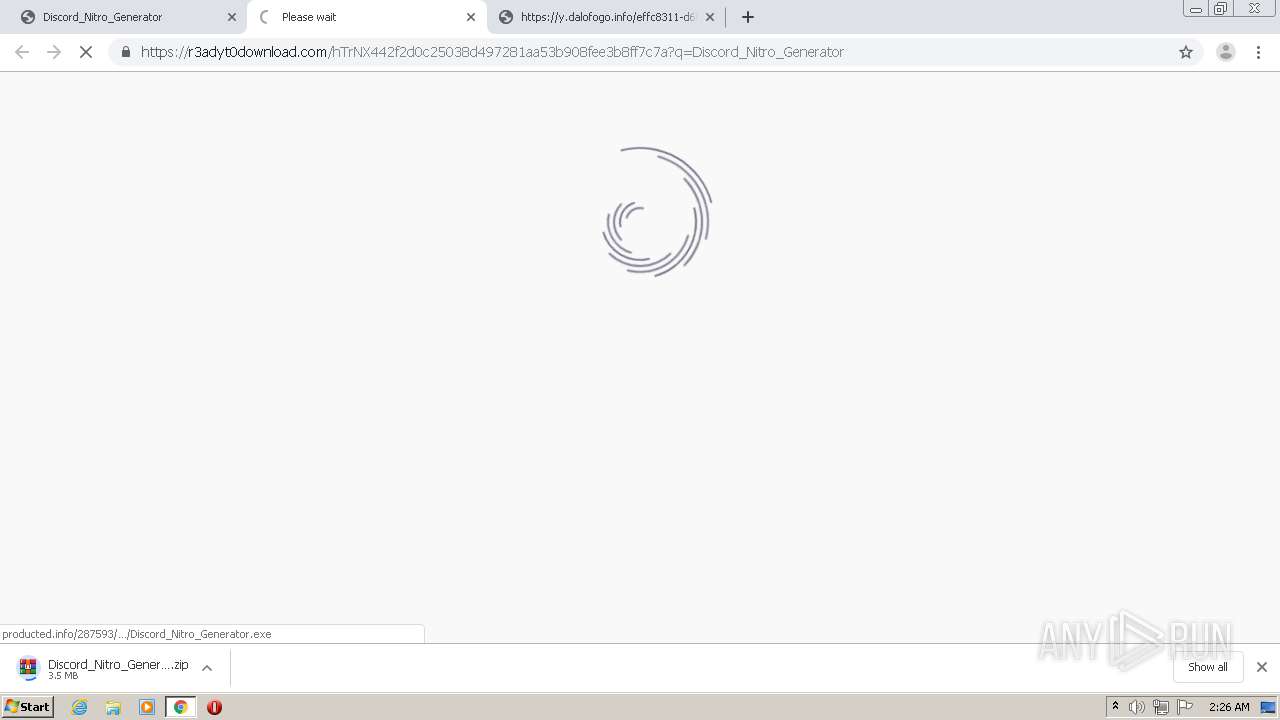
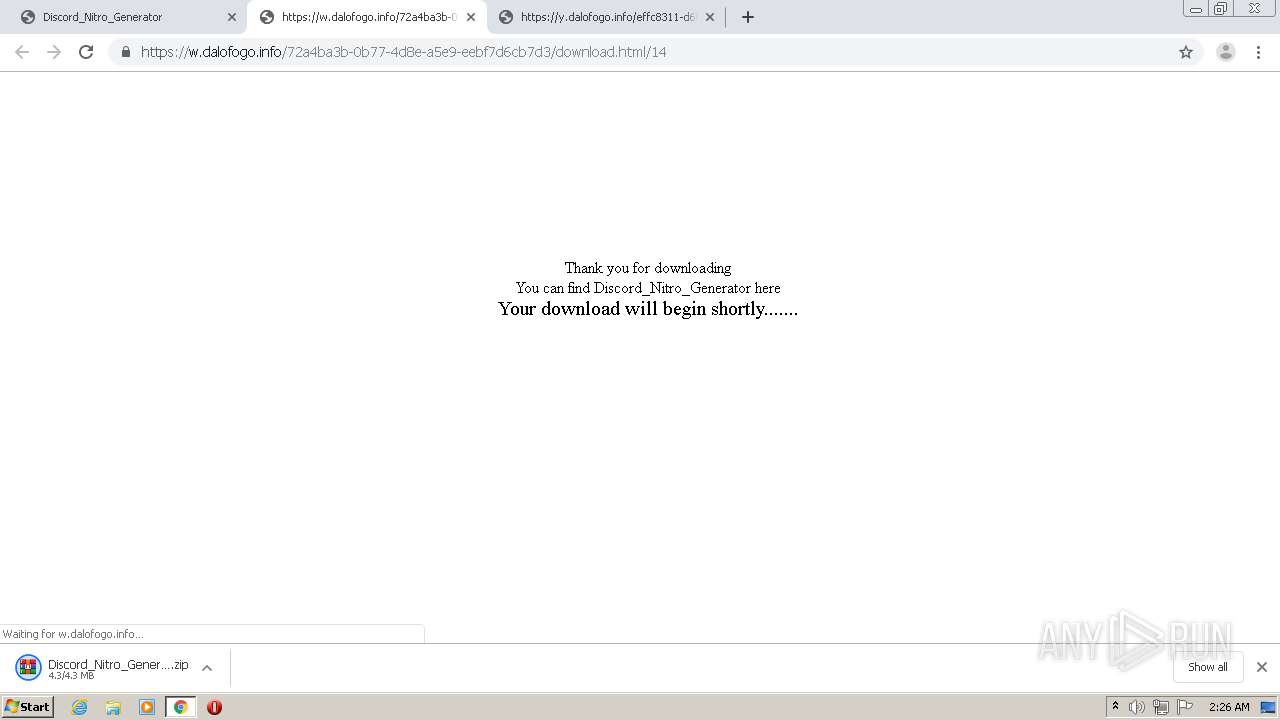
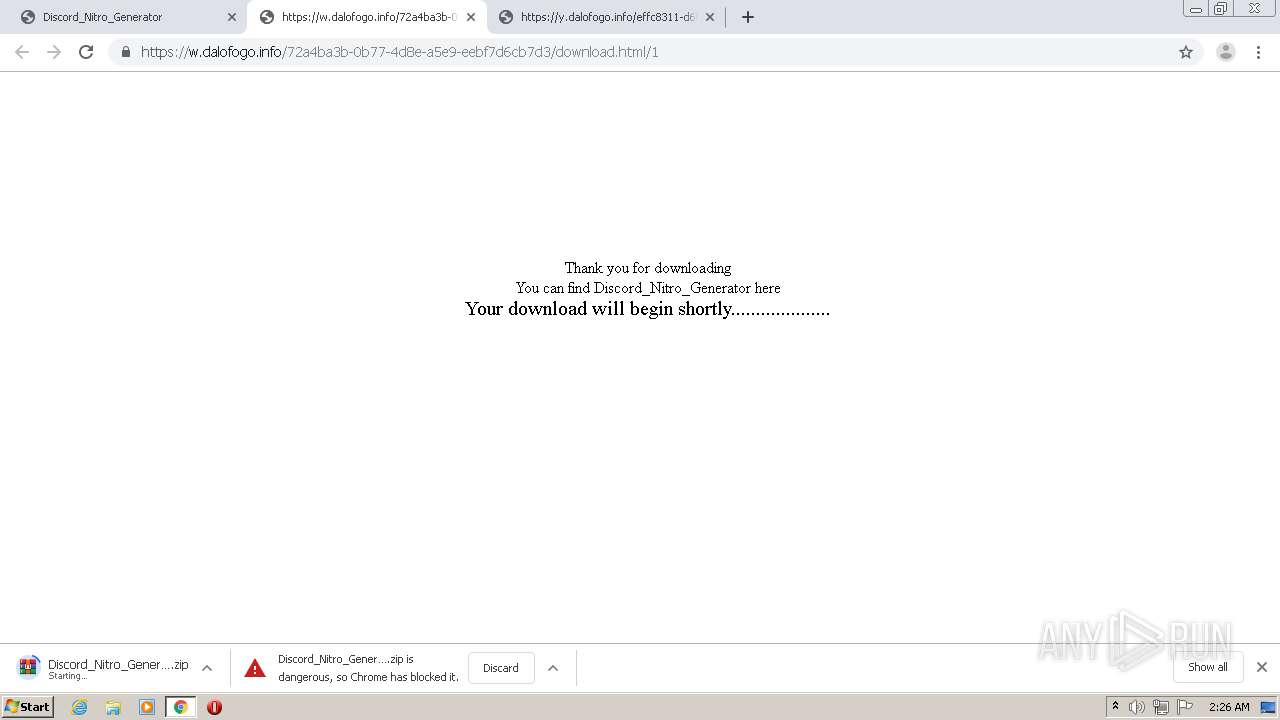
2640 | chrome.exe | 104.21.13.253:443 | gplinks.co | Cloudflare Inc | US | unknown |
2640 | chrome.exe | 142.250.185.237:443 | accounts.google.com | Google Inc. | US | suspicious |
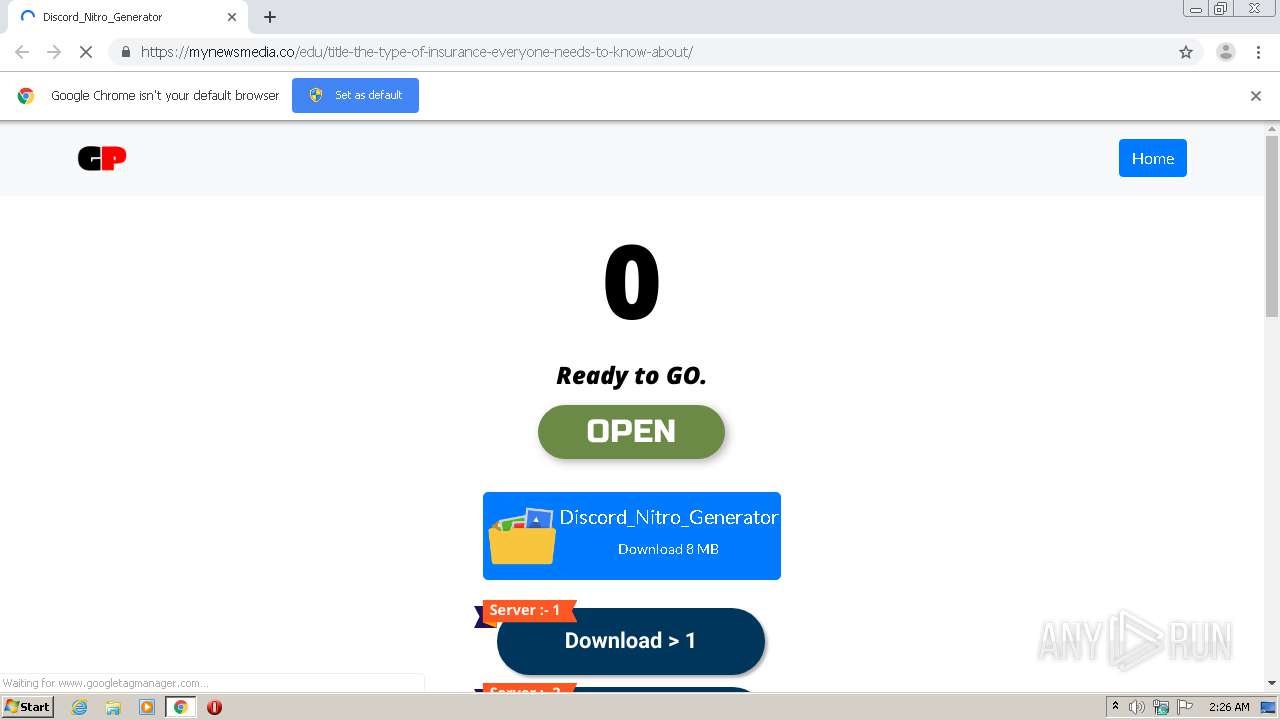
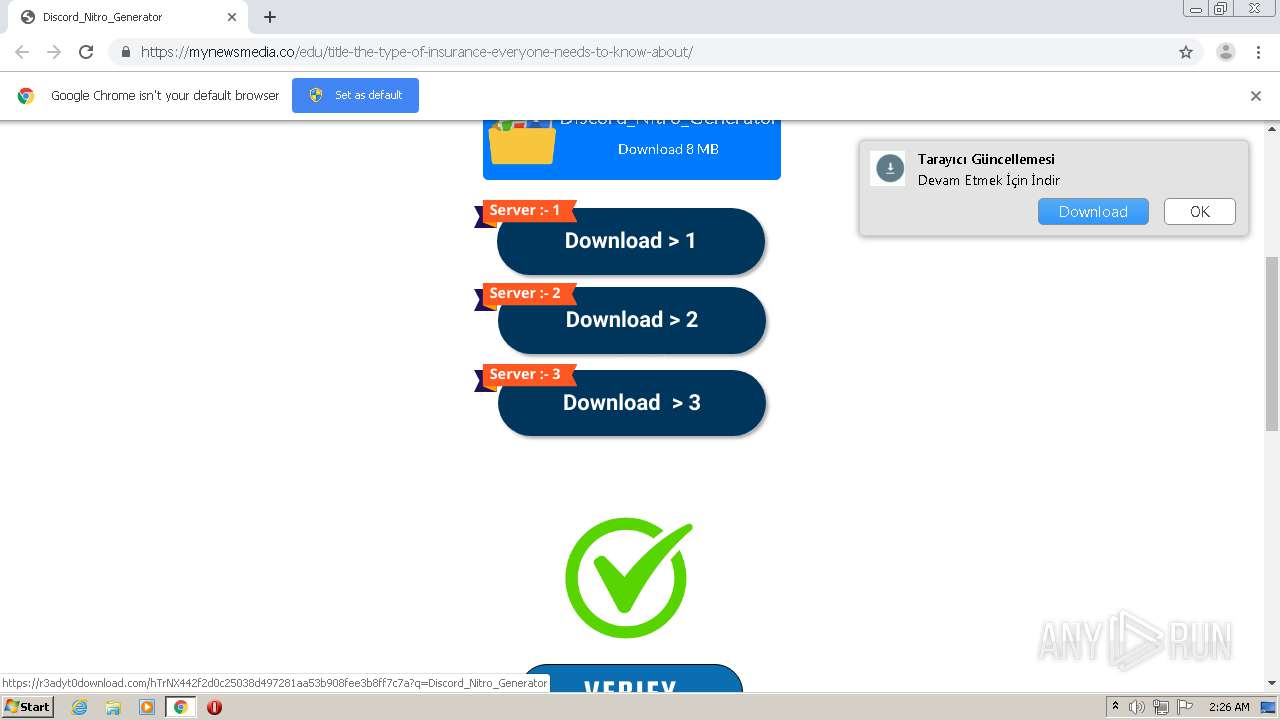
2640 | chrome.exe | 104.21.51.98:443 | mynewsmedia.co | Cloudflare Inc | US | unknown |
2640 | chrome.exe | 142.250.186.40:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2640 | chrome.exe | 51.68.161.26:443 | joyhaftsyears.com | — | GB | unknown |
2640 | chrome.exe | 23.109.82.239:443 | lawscagetroy.com | — | NL | unknown |
2640 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
2640 | chrome.exe | 142.250.186.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2640 | chrome.exe | 69.16.175.10:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
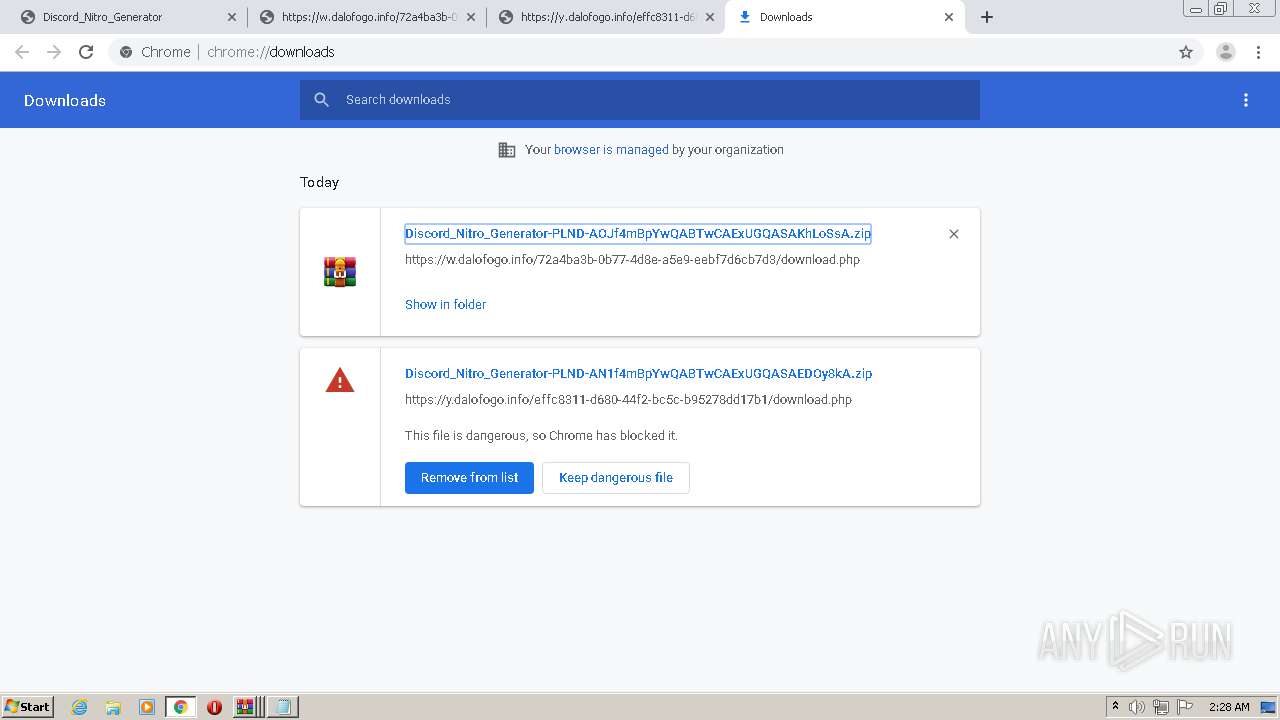
gplinks.co |
| malicious |
accounts.google.com |
| shared |
mynewsmedia.co |
| malicious |
www.googletagmanager.com |
| whitelisted |
joyhaftsyears.com |
| suspicious |
lawscagetroy.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
code.jquery.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2640 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |