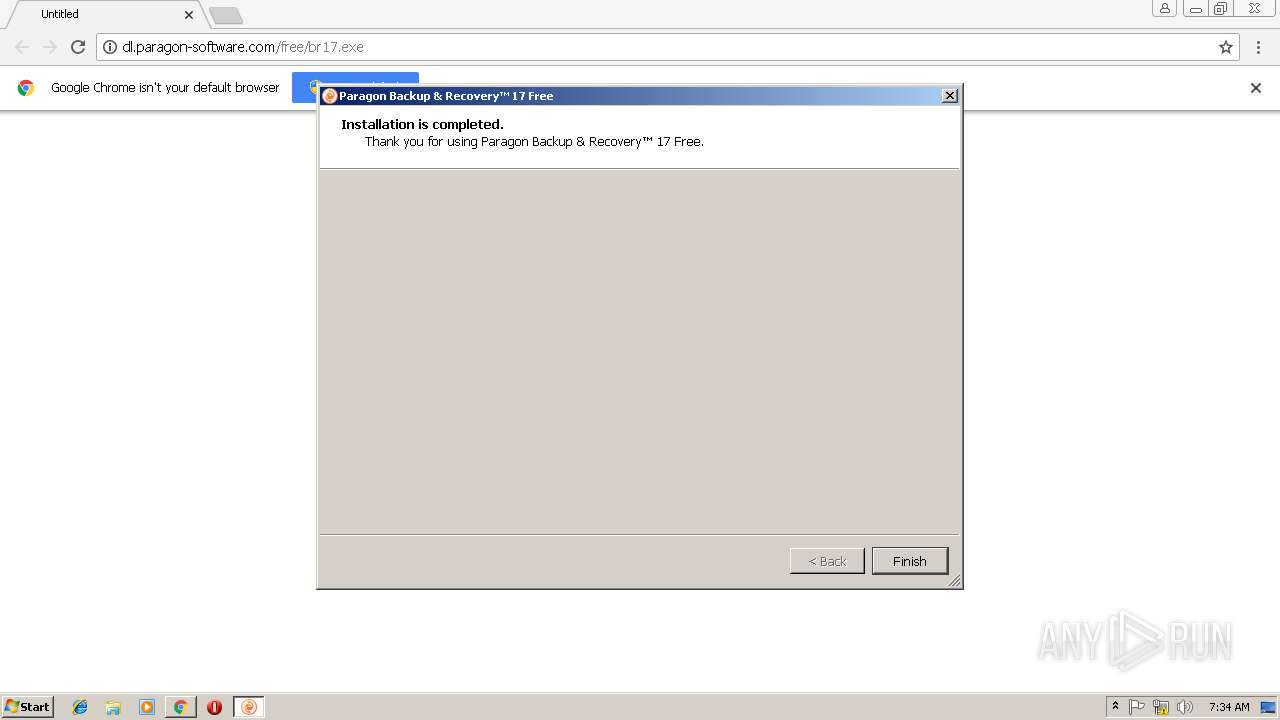
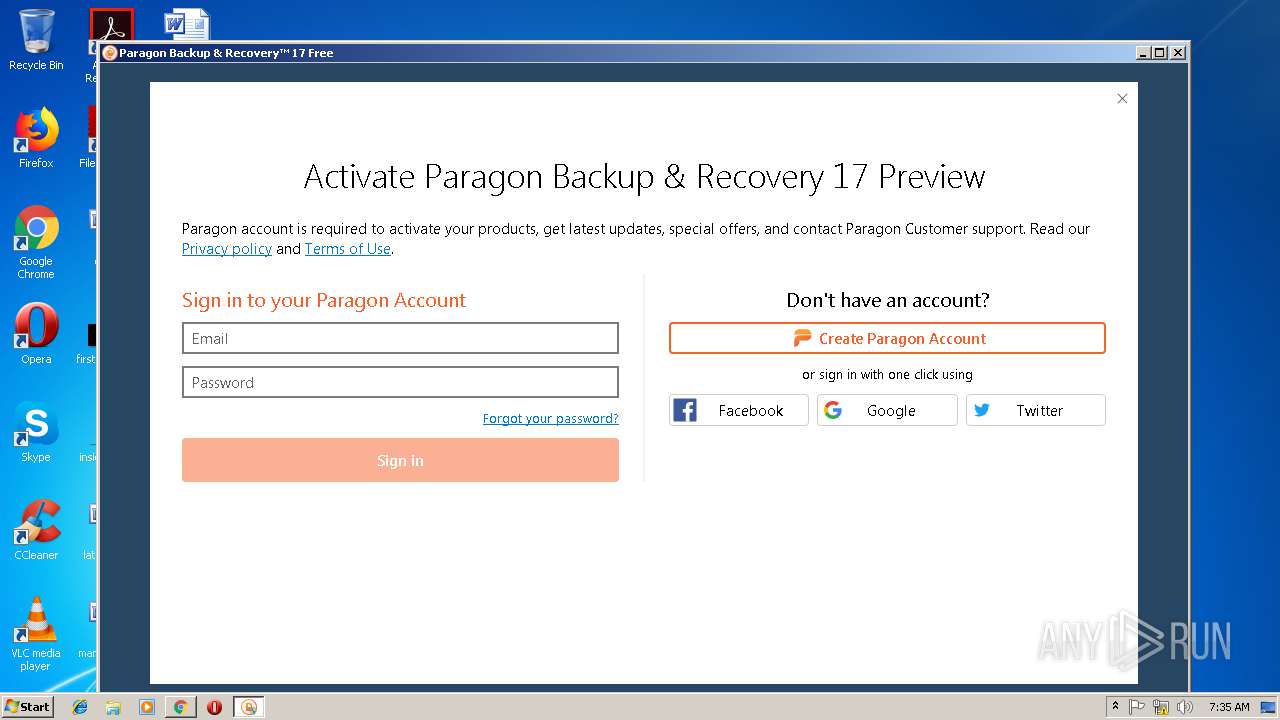
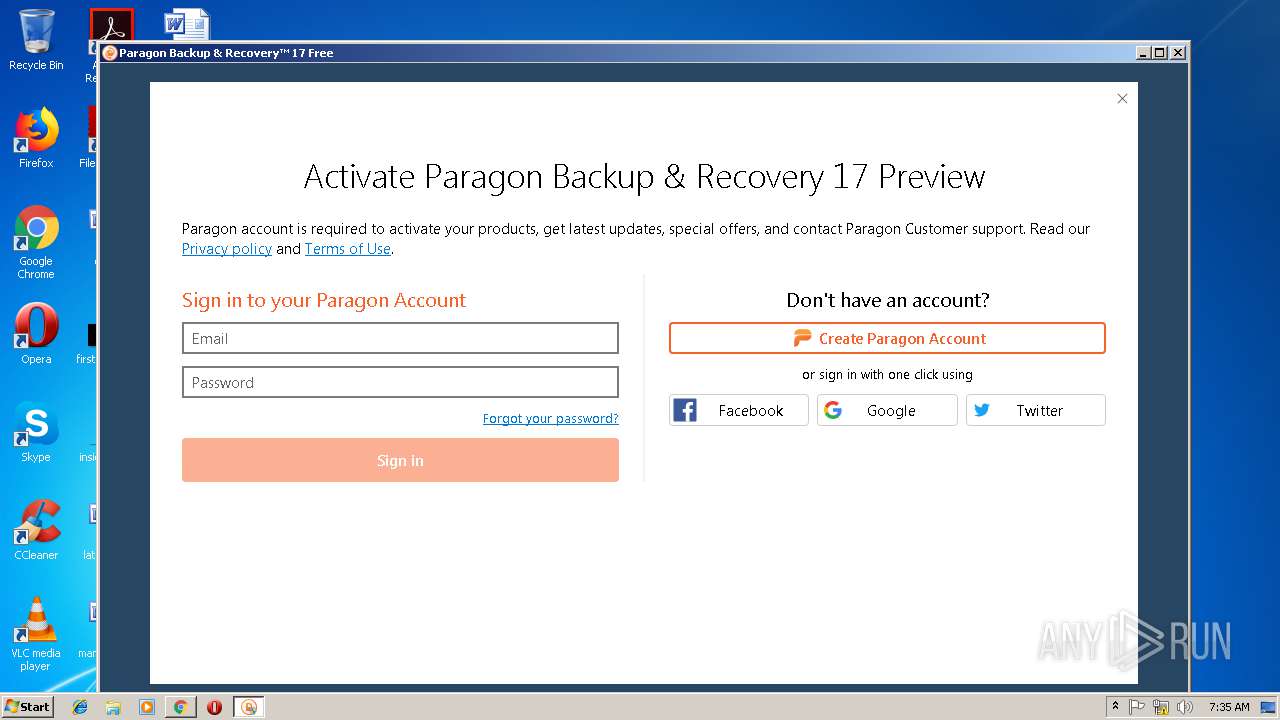
| URL: | http://dl.paragon-software.com/free/br17.exe |
| Full analysis: | https://app.any.run/tasks/710dc314-e93a-4703-950f-697a4fc7d77d |
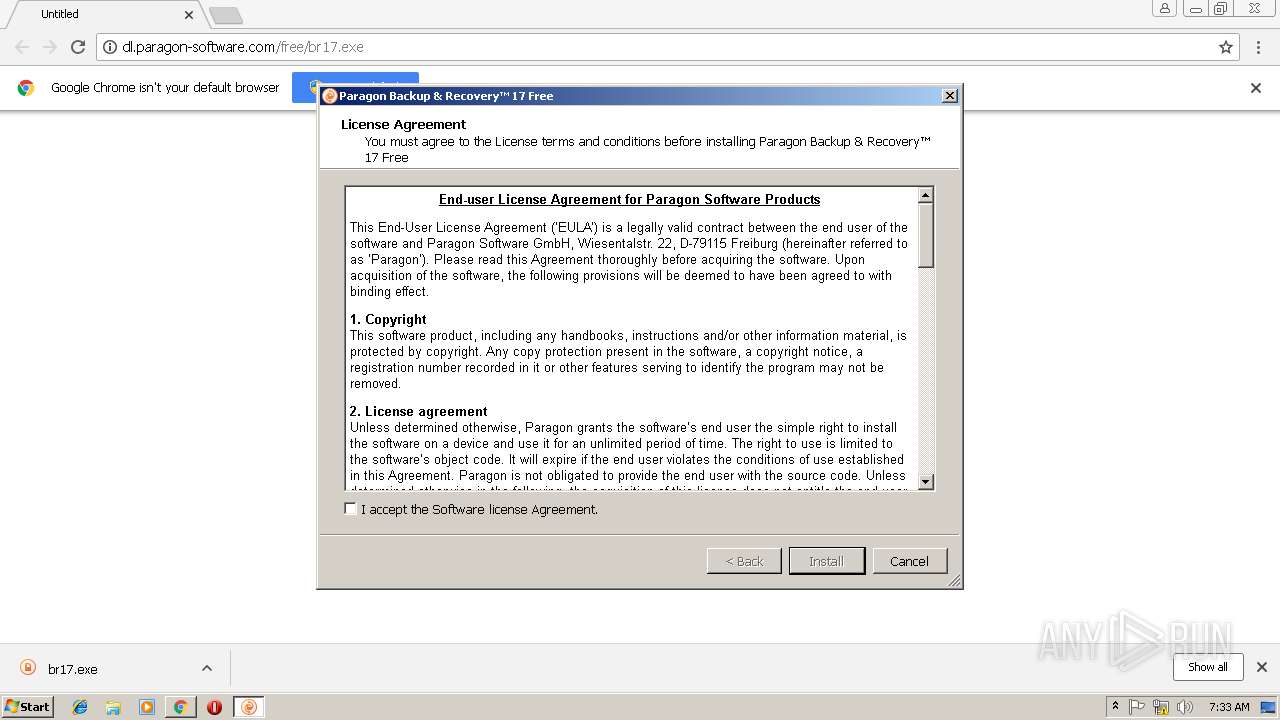
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2019, 07:31:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F0F33CBCEBFBDCC6029B67D1165055BD |
| SHA1: | 738E59AAFE68D78070B4A2B353171B876A21F59F |
| SHA256: | 8824ADB039BE4E467163B138968AE32D99C7E4106CC790A18A6439D77563B753 |
| SSDEEP: | 3:N1KaJSXeHFzQfX/Nn:CaJkH/F |
MALICIOUS
Application was dropped or rewritten from another process
- br17.exe (PID: 920)
- br17.exe (PID: 2556)
- br17_x86.exe (PID: 2640)
- winfuse_uimsetup.exe (PID: 3372)
- br17.exe (PID: 2984)
- hdm17.exe (PID: 3084)
- hdm17.exe (PID: 2328)
- hdm17.exe (PID: 872)
- QtWebEngineProcess.exe (PID: 1924)
- hdm17.exe (PID: 3944)
- QtWebEngineProcess.exe (PID: 3536)
Loads dropped or rewritten executable
- br17.exe (PID: 920)
- DrvInst.exe (PID: 584)
- WUDFHost.exe (PID: 2324)
- winfuse_uimsetup.exe (PID: 3372)
- hdm17.exe (PID: 2328)
- QtWebEngineProcess.exe (PID: 1924)
- hdm17.exe (PID: 3944)
- QtWebEngineProcess.exe (PID: 3536)
Changes the autorun value in the registry
- br17_x86.exe (PID: 2640)
Changes settings of System certificates
- MsiExec.exe (PID: 2220)
- winfuse_uimsetup.exe (PID: 3372)
Loads the Task Scheduler COM API
- hdm17.exe (PID: 2328)
- hdm17.exe (PID: 3944)
SUSPICIOUS
Executable content was dropped or overwritten
- br17.exe (PID: 920)
- br17_x86.exe (PID: 2640)
- chrome.exe (PID: 2736)
- DrvInst.exe (PID: 1144)
- br17.exe (PID: 2556)
- msiexec.exe (PID: 2972)
- DrvInst.exe (PID: 584)
- DrvInst.exe (PID: 3972)
- DrvInst.exe (PID: 3600)
- DrvInst.exe (PID: 2156)
- winfuse_uimsetup.exe (PID: 3372)
- DrvInst.exe (PID: 2056)
Creates files in the Windows directory
- br17.exe (PID: 920)
- winfuse_uimsetup.exe (PID: 3372)
- DrvInst.exe (PID: 1144)
- br17.exe (PID: 2556)
- WUDFHost.exe (PID: 2324)
- msiexec.exe (PID: 2972)
- DrvInst.exe (PID: 584)
- DrvInst.exe (PID: 2056)
- DrvInst.exe (PID: 3600)
- DrvInst.exe (PID: 3972)
- DrvInst.exe (PID: 2156)
- hdm17.exe (PID: 2328)
- hdm17.exe (PID: 3944)
Starts itself from another location
- br17.exe (PID: 920)
Creates files in the program directory
- br17_x86.exe (PID: 2640)
- hdm17.exe (PID: 2328)
- hdm17.exe (PID: 3944)
Creates a software uninstall entry
- br17_x86.exe (PID: 2640)
Adds / modifies Windows certificates
- MsiExec.exe (PID: 2220)
- winfuse_uimsetup.exe (PID: 3372)
Creates files in the driver directory
- DrvInst.exe (PID: 1144)
- DrvInst.exe (PID: 584)
- DrvInst.exe (PID: 2056)
- DrvInst.exe (PID: 3972)
- DrvInst.exe (PID: 3600)
- DrvInst.exe (PID: 2156)
Removes files from Windows directory
- DrvInst.exe (PID: 1144)
- DrvInst.exe (PID: 584)
- DrvInst.exe (PID: 2056)
- DrvInst.exe (PID: 2156)
- DrvInst.exe (PID: 3600)
- DrvInst.exe (PID: 3972)
- br17.exe (PID: 920)
- br17.exe (PID: 2556)
- hdm17.exe (PID: 2328)
- hdm17.exe (PID: 3944)
Searches for installed software
- DrvInst.exe (PID: 1144)
- DrvInst.exe (PID: 2056)
- DrvInst.exe (PID: 3972)
Low-level read access rights to disk partition
- hdm17.exe (PID: 2328)
- vds.exe (PID: 2060)
- vds.exe (PID: 2452)
- hdm17.exe (PID: 3944)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2736)
Application launched itself
- msiexec.exe (PID: 2972)
- chrome.exe (PID: 2736)
Reads settings of System Certificates
- chrome.exe (PID: 2736)
- hdm17.exe (PID: 2328)
- hdm17.exe (PID: 3944)
Dropped object may contain Bitcoin addresses
- br17.exe (PID: 920)
- msiexec.exe (PID: 2972)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2948)
Creates files in the program directory
- msiexec.exe (PID: 2972)
Creates a software uninstall entry
- msiexec.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
43
Malicious processes
17
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | DrvInst.exe "2" "211" "ROOT\PARAGONBLOCKDEVICE\0000" "C:\Windows\INF\oem4.inf" "winfuse_blockmounter.inf:Paragon.NTx86:blockmounter:24.13.0.0:wudf\paragonblockdev" "67370f437" "000003A8" "000005CC" "000005DC" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
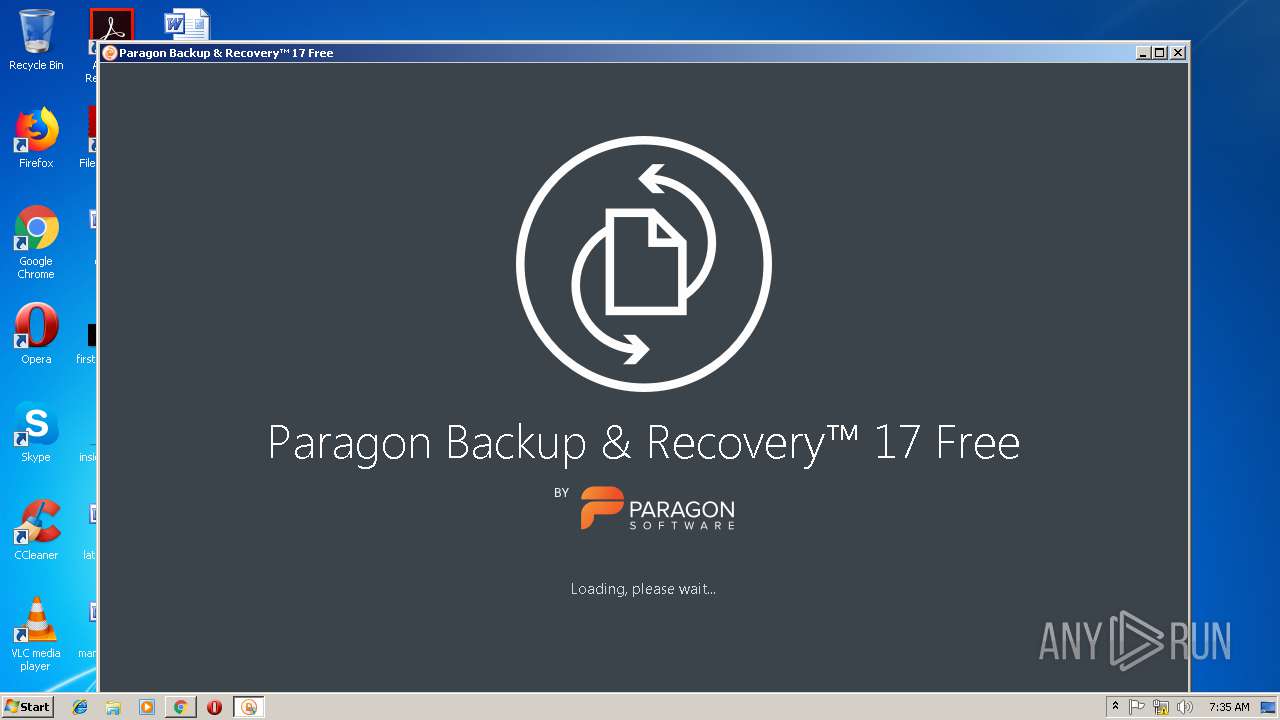
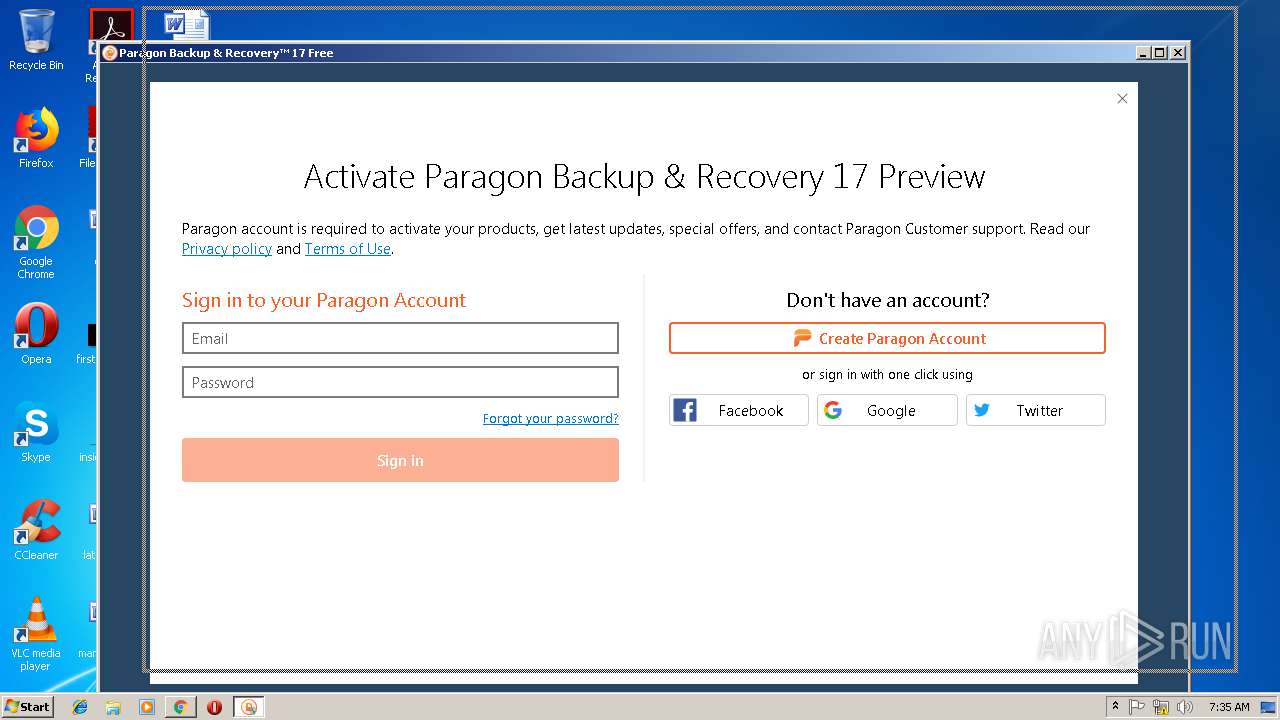
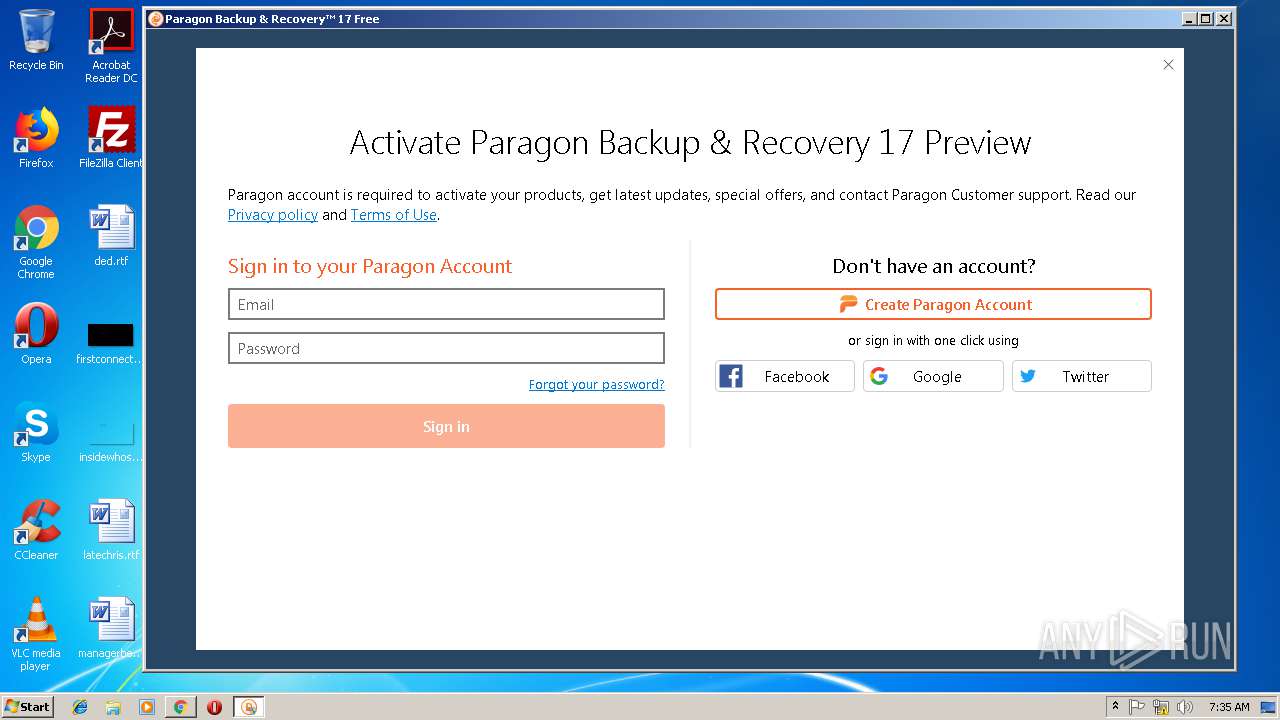
| 872 | "C:\Program Files\Paragon Software\Backup and Recovery 17 Free\program\hdm17.exe" | C:\Program Files\Paragon Software\Backup and Recovery 17 Free\program\hdm17.exe | — | explorer.exe | |||||||||||
User: admin Company: Paragon Software GmbH Integrity Level: MEDIUM Description: A part of Paragon System Utilities Exit code: 3221226540 Modules
| |||||||||||||||
| 920 | "C:\Windows\Temp\{9BF76151-FA92-410D-938F-4F1744D4E3AF}\.cr\br17.exe" -burn.clean.room="C:\Users\admin\Downloads\br17.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Windows\Temp\{9BF76151-FA92-410D-938F-4F1744D4E3AF}\.cr\br17.exe | br17.exe | ||||||||||||
User: admin Company: Paragon Software GmbH Integrity Level: HIGH Description: Paragon Backup & Recovery™ 17 Free Exit code: 0 Version: 10.4.0.3533 Modules
| |||||||||||||||
| 1144 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{13600b50-ca6b-5df4-c522-b82c2b358f7d}\winfuse_blockmounter.inf" "0" "67370f437" "000003A8" "WinSta0\Default" "00000298" "208" "c:\program files\paragon software\universal image mounter" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1244 | C:\Windows\system32\MsiExec.exe -Embedding 81DBC129171876C0B61B9F030EC70EAF M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Paragon Software\Backup and Recovery 17 Free\program\QtWebEngineProcess.exe" --type=renderer --disable-gpu-memory-buffer-video-frames --disable-shared-workers --enable-threaded-compositing --disable-mojo-local-storage --no-sandbox --enable-features=AllowContentInitiatedDataUrlNavigations --service-pipe-token=FBBFED96177BF3222D6BD97CEF39A310 --lang=en-US --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=FBBFED96177BF3222D6BD97CEF39A310 --renderer-client-id=2 --mojo-platform-channel-handle=2596 /prefetch:1 | C:\Program Files\Paragon Software\Backup and Recovery 17 Free\program\QtWebEngineProcess.exe | hdm17.exe | ||||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: HIGH Description: Qt Qtwebengineprocess Exit code: 0 Version: 5.10.1.0 Modules
| |||||||||||||||
| 2056 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{082421fe-c63b-27c0-8809-bb4d30c4c964}\uimbus.inf" "0" "648d7e42b" "0000048C" "WinSta0\Default" "000005B4" "208" "c:\program files\paragon software\universal image mounter" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2060 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | DrvInst.exe "2" "211" "ROOT\UIM\0001" "C:\Windows\INF\oem6.inf" "uimdevim.inf:UIM_Plugin.NTx86:Plugin_Inst:0.6.0.0:uim\plugin_devim" "68ba390a3" "0000049C" "000003A8" "000005DC" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 588
Read events
1 860
Write events
1 698
Delete events
30
Modification events
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2736-13196849521838375 |
Value: 259 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
177
Suspicious files
106
Text files
896
Unknown types
126
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\65029c96-846f-4dd4-ab32-20633c8c6645.tmp | — | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f41c3653-12f8-48ed-91a6-c0f19443d19f.tmp | — | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e10f2be5-9c51-46d3-b2a7-eb0083a8ed49.tmp | — | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\Downloads\1b9bc1f5-00fc-472a-a8f0-82f6715a29ff.tmp | executable | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF20d92e.TMP | text | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
5
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2736 | chrome.exe | GET | — | 13.32.223.214:80 | http://dl.paragon-software.com/free/br17.exe | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2736 | chrome.exe | 13.32.223.214:80 | dl.paragon-software.com | Amazon.com, Inc. | US | suspicious |
2736 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2736 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2736 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2736 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
dl.paragon-software.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2736 | chrome.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
2736 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2736 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2736 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
Process | Message |
|---|---|
DrvInst.exe | WudfUpdate: installing version (1,9,0,7600).
|
DrvInst.exe | WudfUpdate: Checking for presence of previous UMDF installation.
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\drivers\wudfrd.sys version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\drivers\wudfpf.sys version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfhost.exe version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfsvc.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfx.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfplatform.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfcoinstaller.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: UMDF installation is newer than update.
|