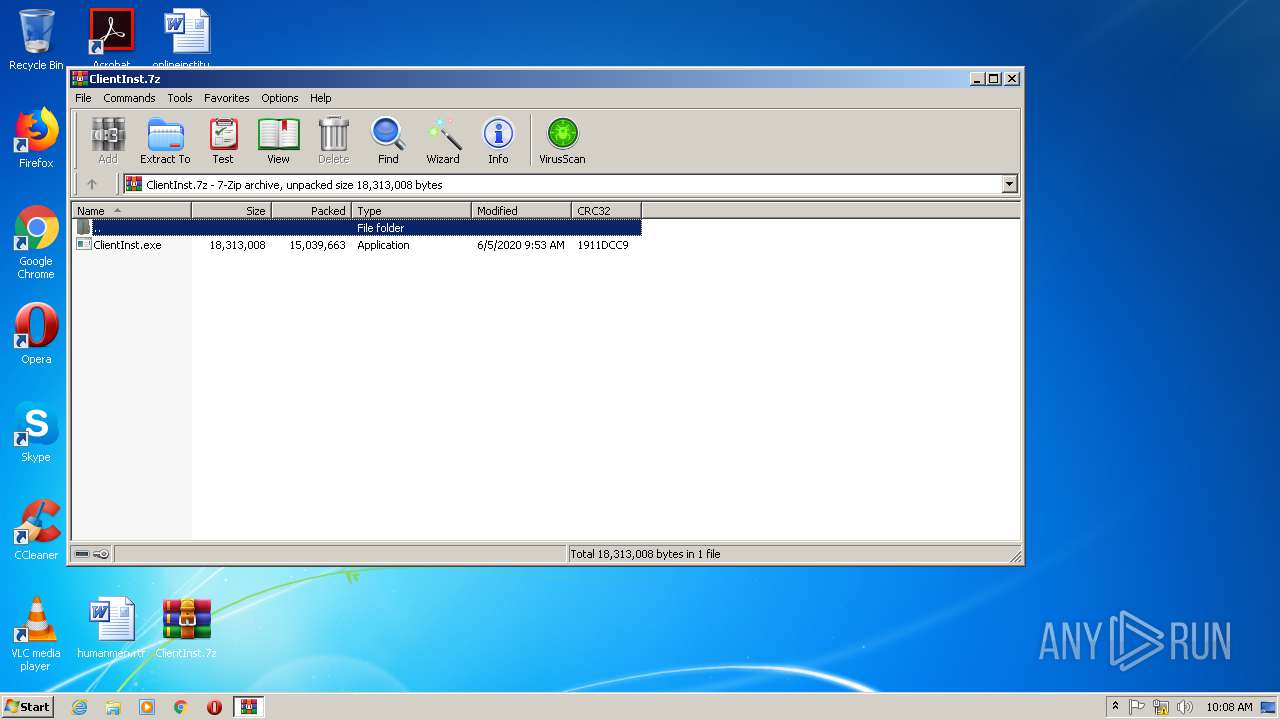
| File name: | ClientInst.7z |
| Full analysis: | https://app.any.run/tasks/4394e8be-0215-4502-a123-348e556c5152 |
| Verdict: | Malicious activity |
| Analysis date: | June 05, 2020, 09:08:35 |
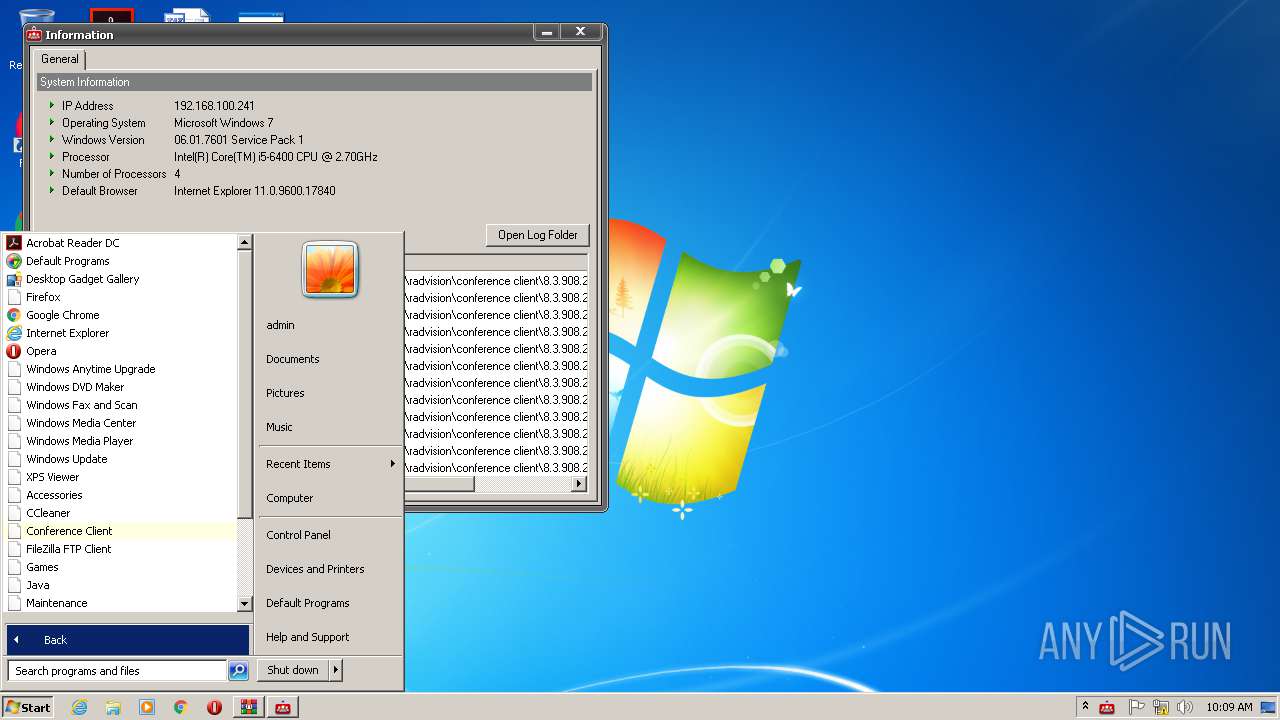
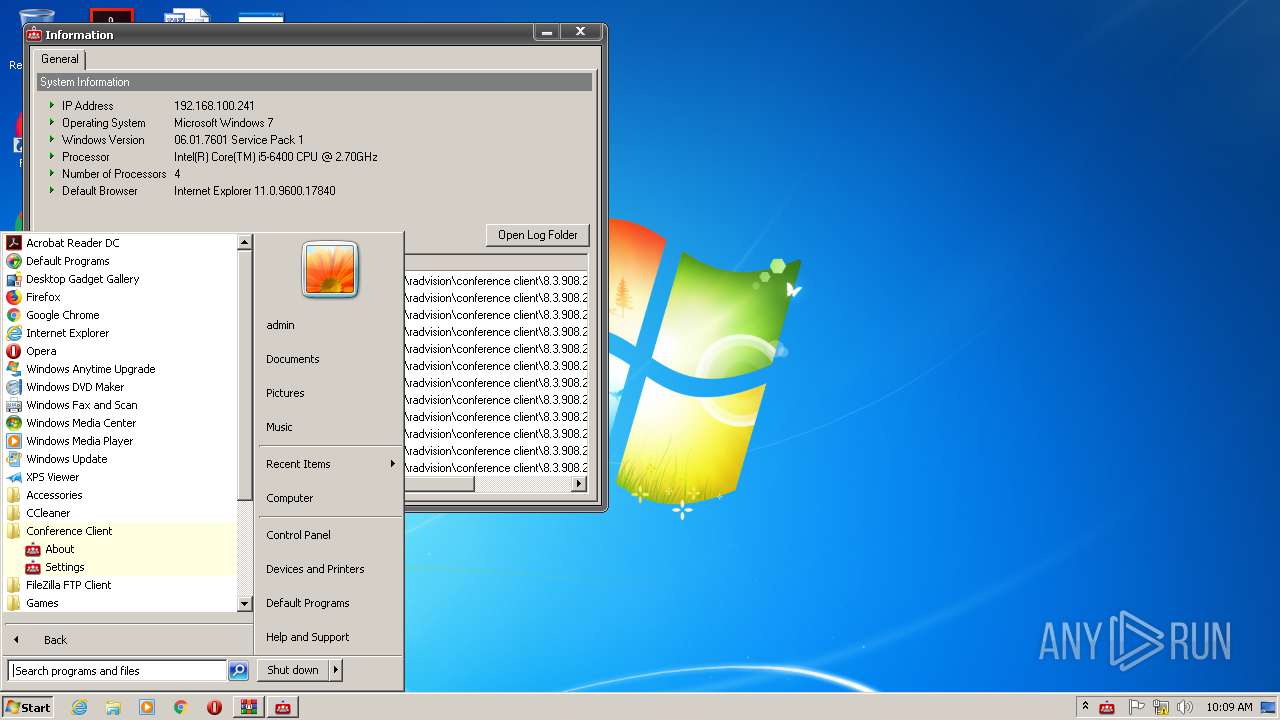
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 5390E93D50FBCF710949E79F03420066 |
| SHA1: | D37AA17EDB3EAE4ED597B27B2858A6BE957F295A |
| SHA256: | 880613AE08CF9616E398CAAC9088A8D867B68A205637B2D0C504F117D7F8A990 |
| SSDEEP: | 393216:0DCZxKaPCAC9Npg0po6N5pquyx+wqn9GqfZwxij:tIVAC/60poOrquyx+wq9GWQij |
MALICIOUS
Application was dropped or rewritten from another process
- ClientInst.exe (PID: 2352)
- cucore.exe (PID: 2496)
- ConfAgent.exe (PID: 1844)
Loads dropped or rewritten executable
- cucore.exe (PID: 2496)
- explorer.exe (PID: 1784)
- ClientInst.exe (PID: 2352)
- ConfAgent.exe (PID: 1844)
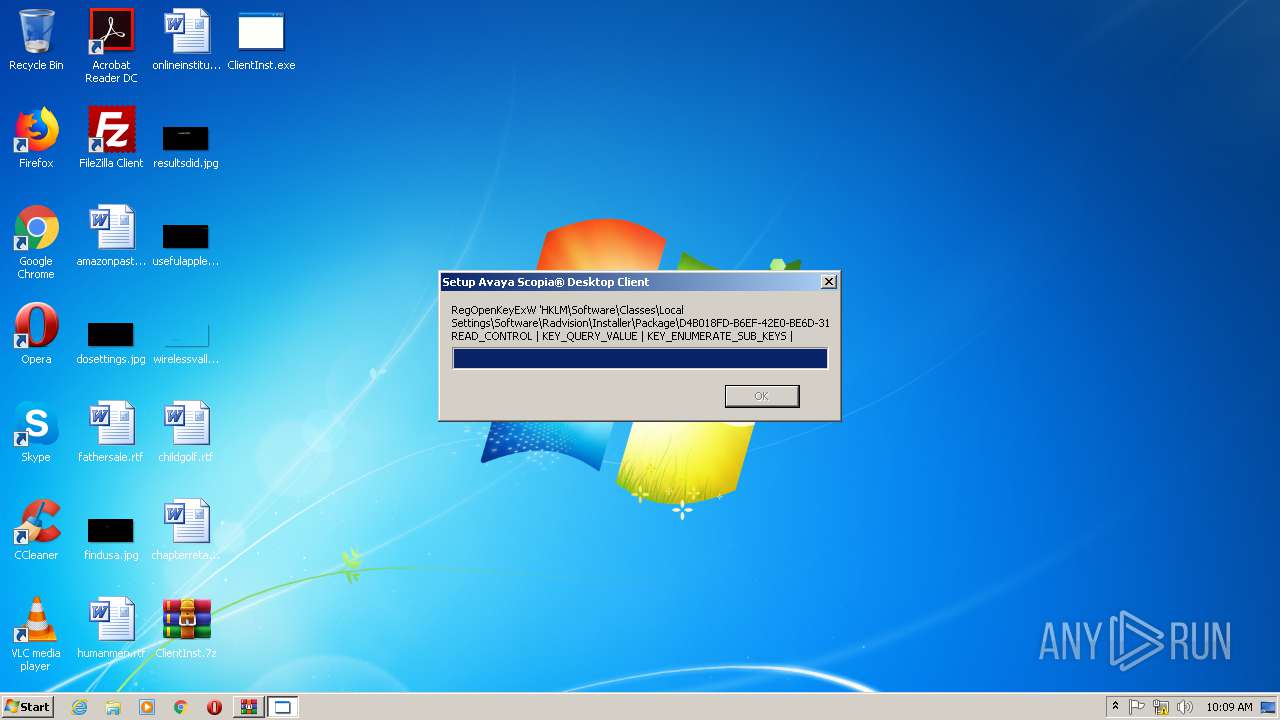
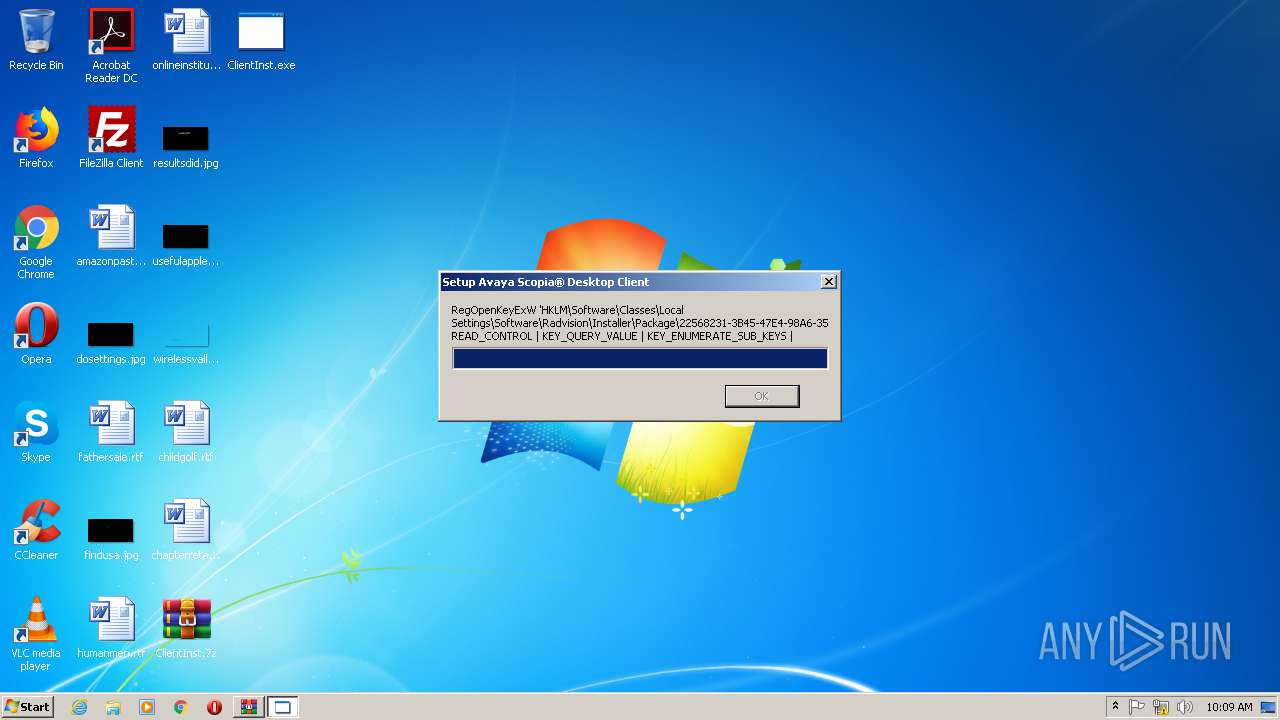
Changes the autorun value in the registry
- cucore.exe (PID: 2496)
SUSPICIOUS
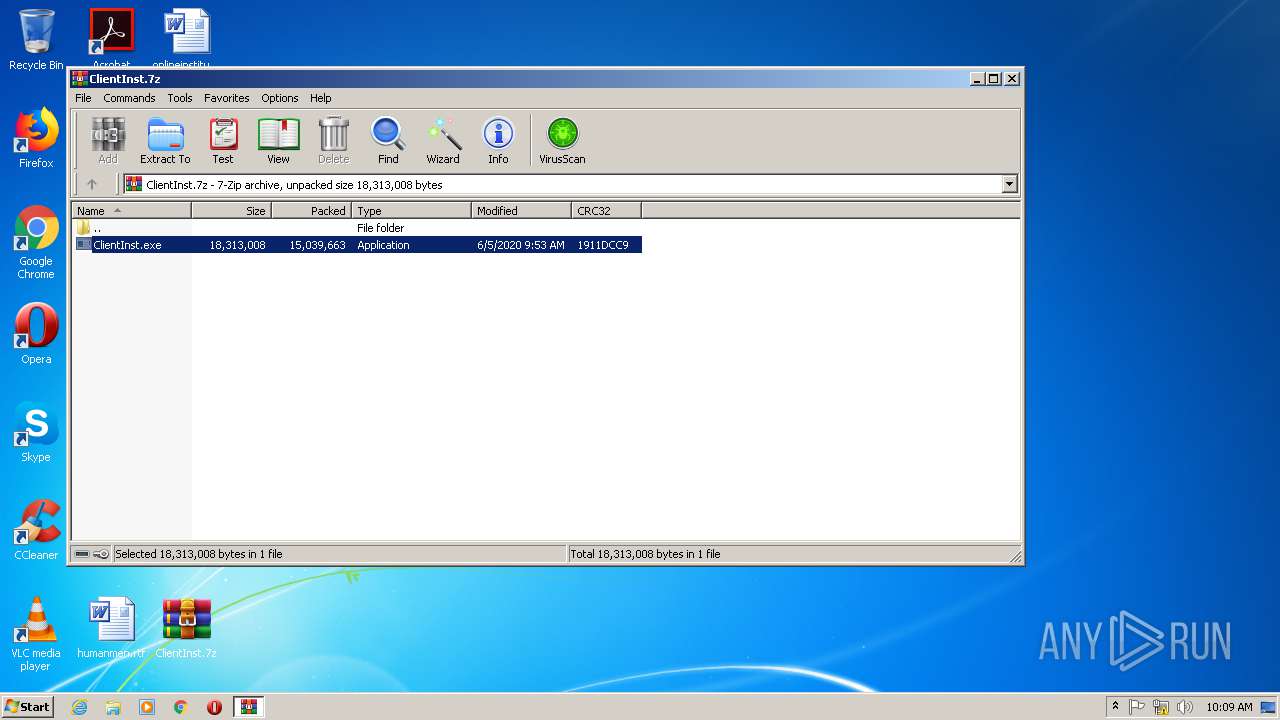
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3824)
- ClientInst.exe (PID: 2352)
Modifies the open verb of a shell class
- ClientInst.exe (PID: 2352)
Creates files in the user directory
- explorer.exe (PID: 1784)
- ClientInst.exe (PID: 2352)
Creates a software uninstall entry
- ClientInst.exe (PID: 2352)
INFO
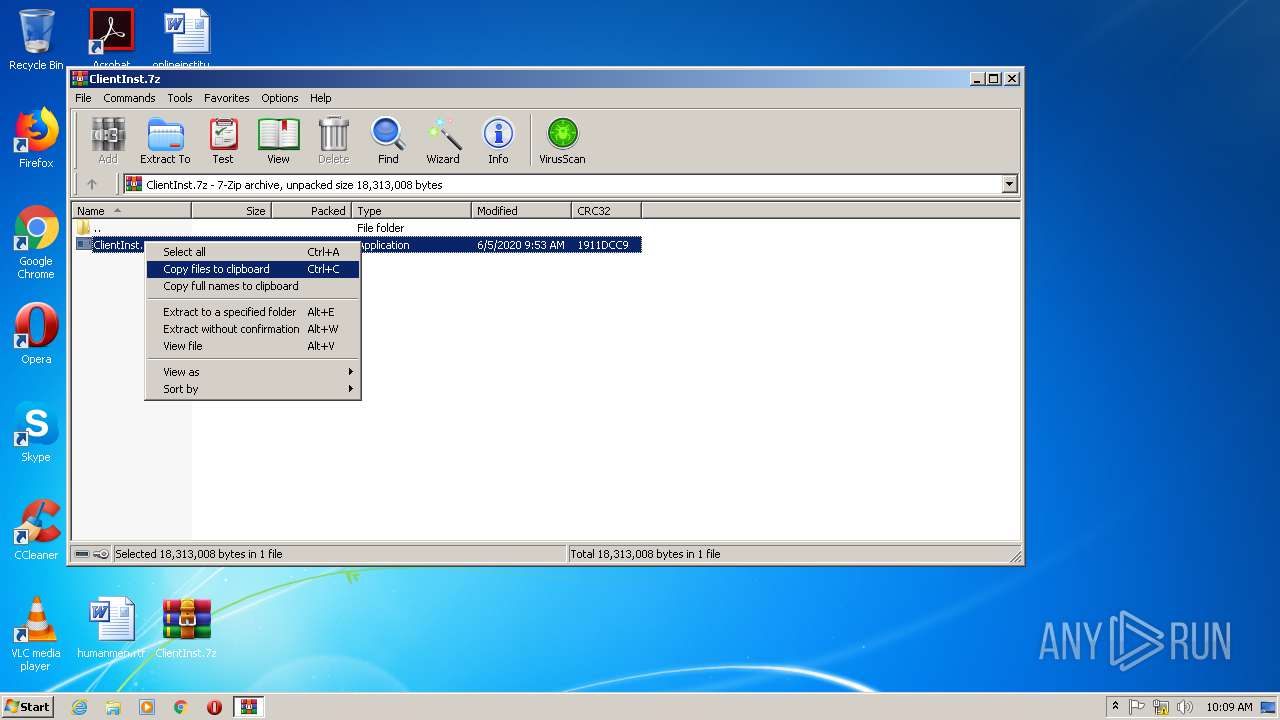
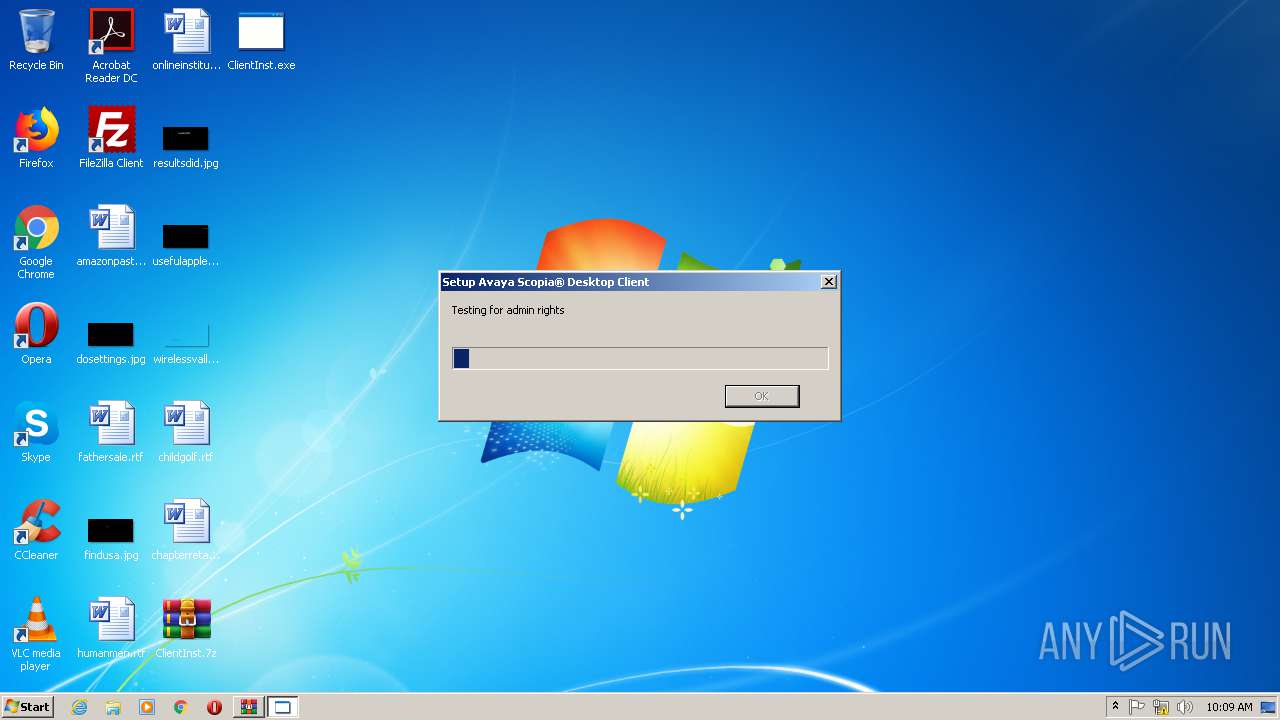
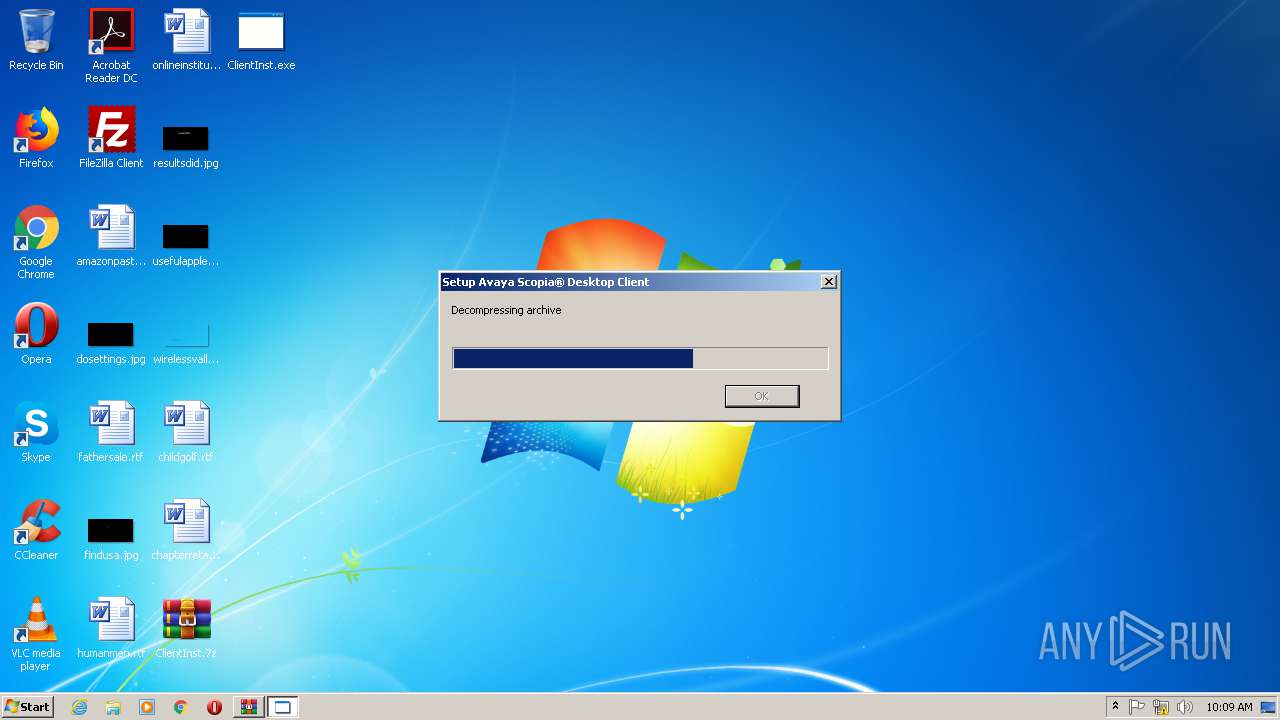
Manual execution by user
- ClientInst.exe (PID: 2352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
42
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1784 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
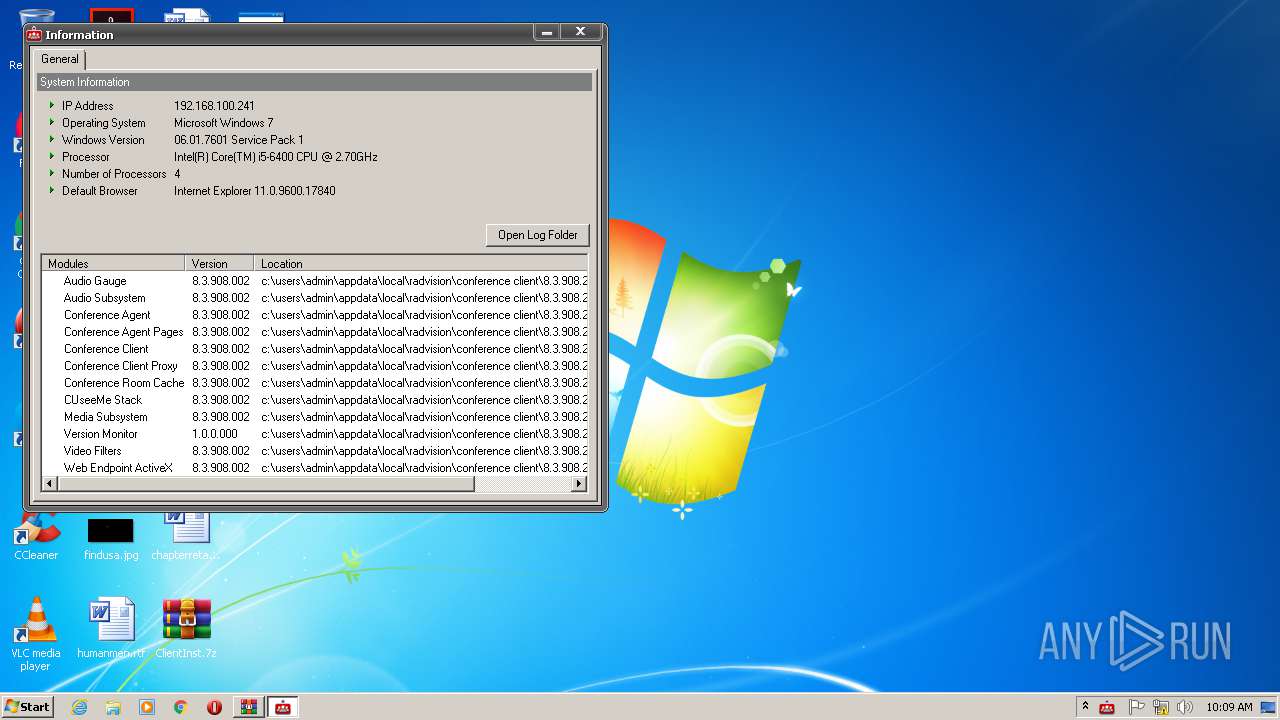
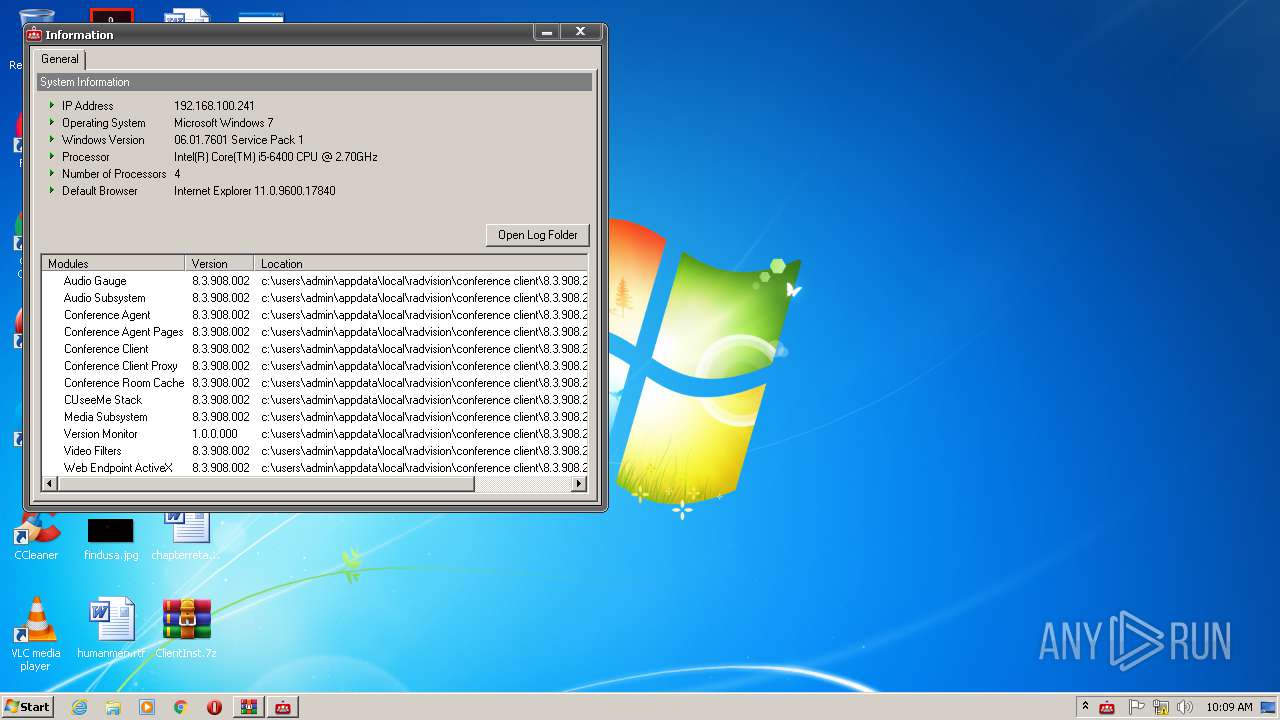
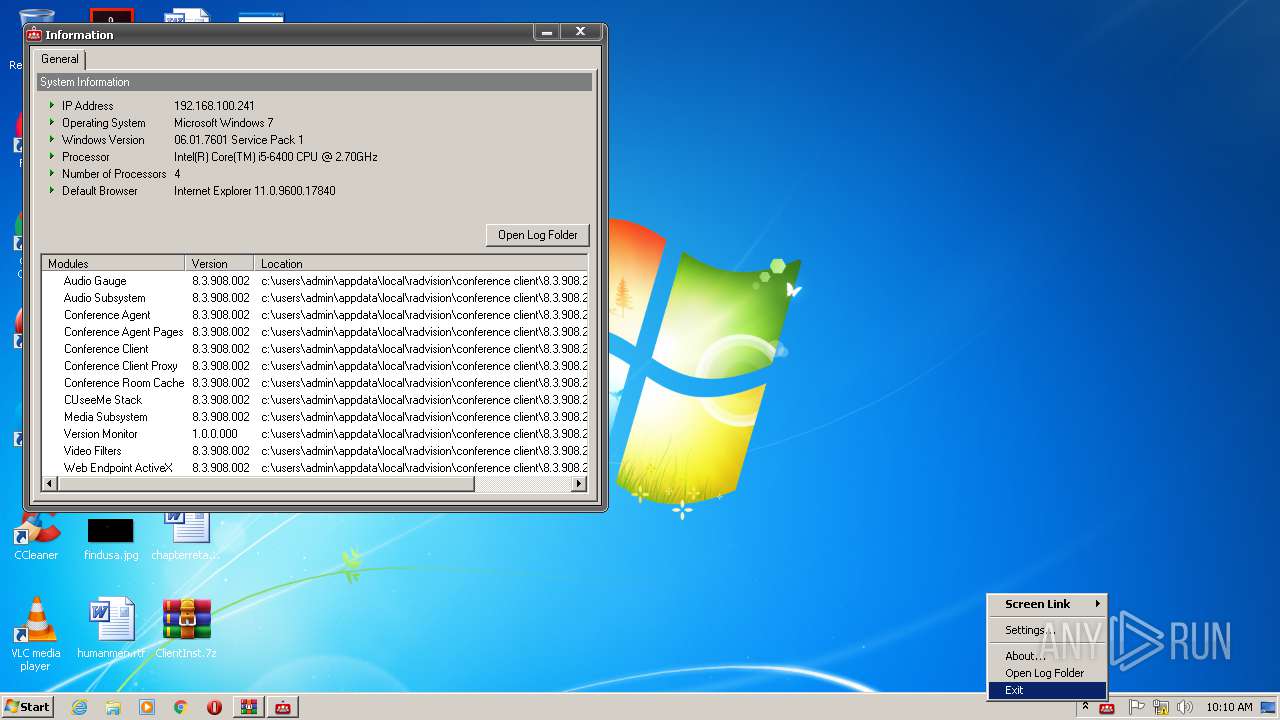
| 1844 | "C:\Users\admin\AppData\Local\Radvision\Conference Client\8.3.908.2\ConfAgent.exe" about | C:\Users\admin\AppData\Local\Radvision\Conference Client\8.3.908.2\ConfAgent.exe | — | explorer.exe | |||||||||||
User: admin Company: Avaya, Inc. Integrity Level: MEDIUM Description: Conference Agent Exit code: 0 Version: 8.3.908.2 Modules
| |||||||||||||||
| 2352 | "C:\Users\admin\Desktop\ClientInst.exe" | C:\Users\admin\Desktop\ClientInst.exe | explorer.exe | ||||||||||||
User: admin Company: Avaya, Inc. Integrity Level: MEDIUM Description: Client Exit code: 37 Version: 8.3.908.2 Modules
| |||||||||||||||
| 2496 | "C:\Users\admin\AppData\Local\Radvision\Conference Client\8.3.908.2\cucore.exe" | C:\Users\admin\AppData\Local\Radvision\Conference Client\8.3.908.2\cucore.exe | ClientInst.exe | ||||||||||||
User: admin Company: Avaya, Inc. Integrity Level: MEDIUM Description: Conference Client Exit code: 0 Version: 8.3.908.2 Modules
| |||||||||||||||
| 3824 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ClientInst.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
7 001
Read events
5 127
Write events
1 872
Delete events
2
Modification events
| (PID) Process: | (3824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3824) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3824) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ClientInst.7z | |||
| (PID) Process: | (3824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1784) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.7z\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
52
Suspicious files
1
Text files
18
Unknown types
49
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2352 | ClientInst.exe | C:\Users\admin\AppData\Local\Radvision\Conference Client\8.3.908.2\client.zip | — | |
MD5:— | SHA256:— | |||
| 2352 | ClientInst.exe | C:\Users\admin\AppData\Local\Radvision\Installer\1.5.5.6\cliinstmgr.zip | compressed | |
MD5:— | SHA256:— | |||
| 1784 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\ClientInst.7z.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2352 | ClientInst.exe | C:\Users\admin\AppData\Local\Radvision\Installer\Package\ClientInst.exe | executable | |
MD5:— | SHA256:— | |||
| 2352 | ClientInst.exe | C:\Users\admin\AppData\Local\Radvision\Installer\1.5.5.6\npClientInstMgr.dll | executable | |
MD5:— | SHA256:— | |||
| 1784 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2352 | ClientInst.exe | C:\Users\admin\AppData\Local\Radvision\Installer\Package\ClientInst0.pkg | executable | |
MD5:— | SHA256:— | |||
| 2352 | ClientInst.exe | C:\Users\admin\AppData\Local\Radvision\Conference Client\8.3.908.2\wcc\1.0\assets\bundles\de_DE.swf | swf | |
MD5:— | SHA256:— | |||
| 2352 | ClientInst.exe | C:\Users\admin\AppData\Local\Radvision\Installer\1.5.5.6\ClientInstMgr.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | WinRAR.exe | C:\Users\admin\Desktop\ClientInst.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
cucore.exe | 10:09:28.587 CWPThread::CallThread(dwRequestValue[0x00000000]) CPU Monitor threadId[2972], MsgsProcessedCount[0], lMsgProcessedCountTotal[0], lPostedMsgProcessedCount[0], lPostedMsgProcessedCountTotal[0]
|
cucore.exe | 10:09:29.874 CWPThread::CallThread(dwRequestValue[0x00000008]) Radvision H.26X Decoder threadId[3736], MsgsProcessedCount[0], lMsgProcessedCountTotal[0], lPostedMsgProcessedCount[0], lPostedMsgProcessedCountTotal[0]
|
cucore.exe | 10:09:29.977 CWPThread::CallThread(dwRequestValue[0x0000000d]) Radvision H.26X Encoder threadId[3972], MsgsProcessedCount[0], lMsgProcessedCountTotal[0], lPostedMsgProcessedCount[0], lPostedMsgProcessedCountTotal[0]
|
cucore.exe | m_pVoEBase->RegisterVoicf |
cucore.exe | m_pVoEBase->Init
|
cucore.exe | m_pVoEBase->RegisterVoiceEngineObserver
|
cucore.exe | VoiceEngine::Create
|
cucore.exe | m_pVoEHardware->GetNumOfRecordingDevices
|
cucore.exe | m_pVoEHardware->GetRecordingDeviceName
|
cucore.exe | m_pVoEHardware->GetRecordingDeviceName
|