| File name: | 87fd7d86d4f6c878eb0df22916dbbffedaabe6097649d42e0ce371e75f95be5d |
| Full analysis: | https://app.any.run/tasks/06155b3f-620f-4c22-88b6-c48440126ef4 |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2020, 04:13:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | BDB41AB09C3E1649F6C4882388091FD0 |
| SHA1: | 3CD12DFDBF02789C6F035EAE4CED061567CD4AE8 |
| SHA256: | 87FD7D86D4F6C878EB0DF22916DBBFFEDAABE6097649D42E0CE371E75F95BE5D |
| SSDEEP: | 1536:mCgt3dFSHBoO3ag6s55gprhi6WEwaZMLbBWf62BBZe/gYPr:mjJPSh3qs+FiRLbEy/fPr |
MALICIOUS
Loads dropped or rewritten executable
- tasklist.exe (PID: 3556)
- reg.exe (PID: 3860)
- wmiprvse.exe (PID: 4008)
- windanr.exe (PID: 2568)
- regsvr32.exe (PID: 2620)
- extrac32.exe (PID: 1940)
- find.exe (PID: 1256)
- find.exe (PID: 3316)
- regsvr32.exe (PID: 880)
- regsvr32.exe (PID: 2868)
- findstr.exe (PID: 604)
- DllHost.exe (PID: 3804)
- 87fd7d86d4f6c878eb0df22916dbbffedaabe6097649d42e0ce371e75f95be5d.exe (PID: 3792)
- conhost.exe (PID: 2800)
- regsvr32.exe (PID: 3820)
- regsvr32.exe (PID: 1232)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 3552)
- regsvr32.exe (PID: 2780)
- findstr.exe (PID: 1008)
- cmd.exe (PID: 940)
- findstr.exe (PID: 3144)
- svchost.exe (PID: 756)
- svchost.exe (PID: 860)
- svchost.exe (PID: 796)
- explorer.exe (PID: 372)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 2668)
Application was dropped or rewritten from another process
- DllHost.exe (PID: 3804)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 3552)
- conhost.exe (PID: 2800)
- cmd.exe (PID: 940)
- regsvr32.exe (PID: 3820)
- find.exe (PID: 3316)
- find.exe (PID: 1256)
- findstr.exe (PID: 604)
- findstr.exe (PID: 1008)
- regsvr32.exe (PID: 2868)
- findstr.exe (PID: 3144)
- regsvr32.exe (PID: 2620)
- regsvr32.exe (PID: 880)
- regsvr32.exe (PID: 1232)
- svchost.exe (PID: 796)
- regsvr32.exe (PID: 2780)
- reg.exe (PID: 3860)
- svchost.exe (PID: 756)
- extrac32.exe (PID: 1940)
- windanr.exe (PID: 2568)
- svchost.exe (PID: 860)
- tasklist.exe (PID: 3556)
SUSPICIOUS
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2668)
Changes IE settings (feature browser emulation)
- reg.exe (PID: 3860)
Starts CMD.EXE for commands execution
- 87fd7d86d4f6c878eb0df22916dbbffedaabe6097649d42e0ce371e75f95be5d.exe (PID: 3792)
- cmd.exe (PID: 2668)
Application launched itself
- cmd.exe (PID: 2668)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2668)
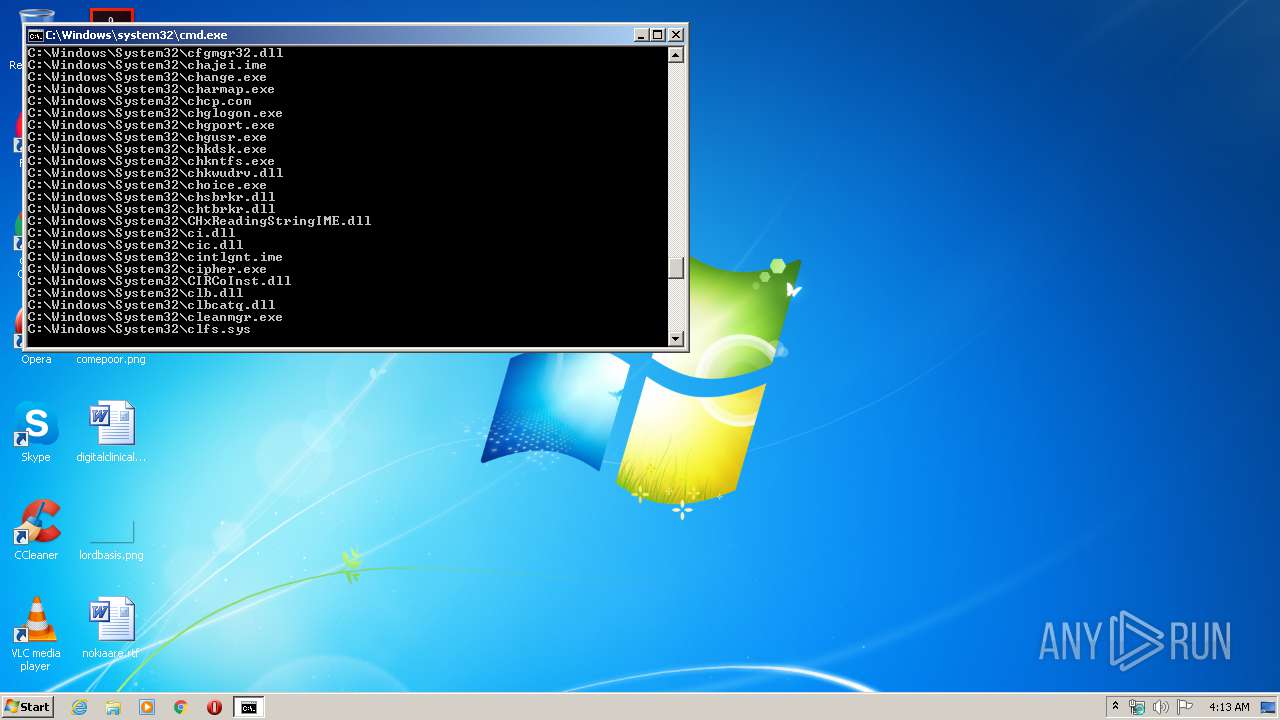
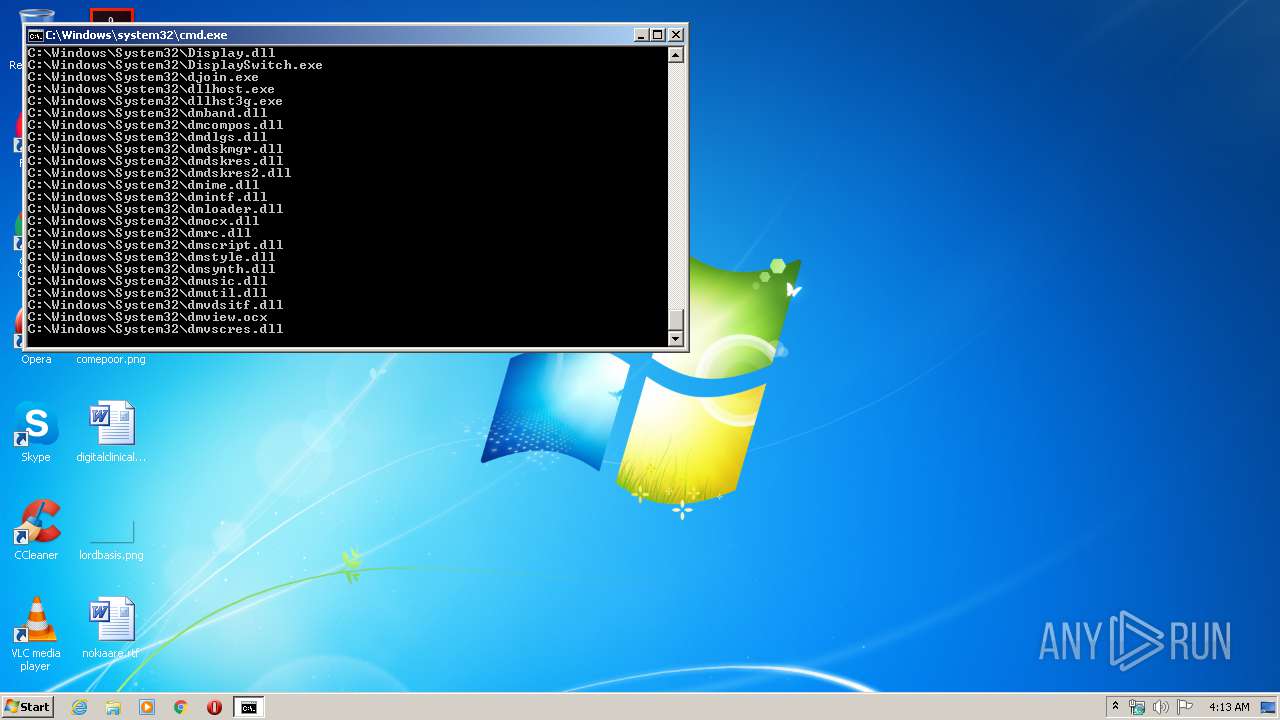
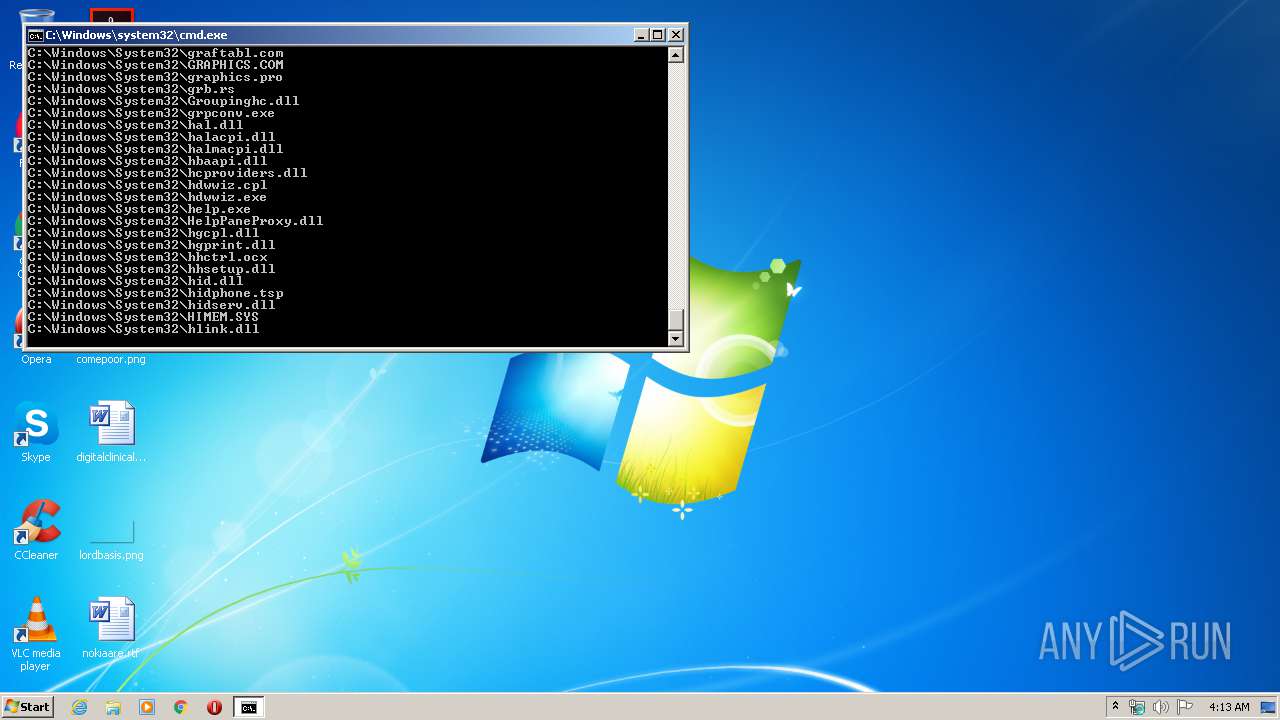
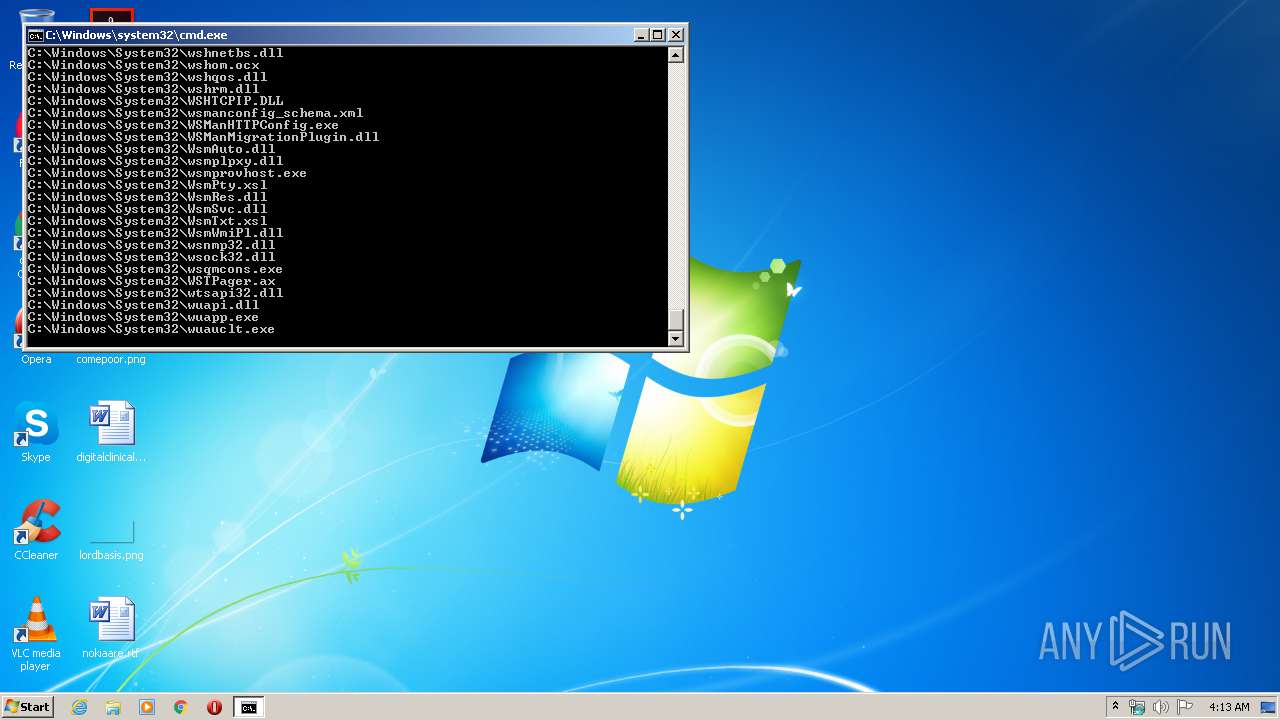
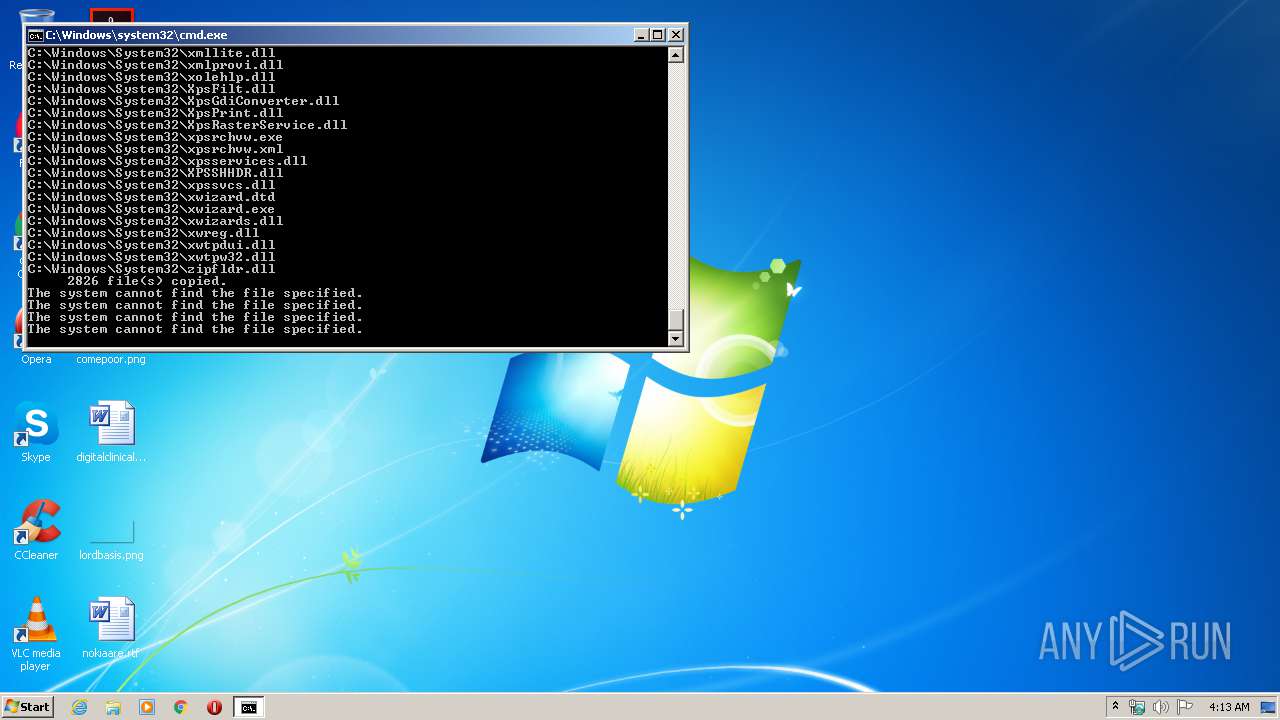
Creates executable files which already exist in Windows
- cmd.exe (PID: 2668)
Searches for installed software
- svchost.exe (PID: 796)
Executable content was dropped or overwritten
- cmd.exe (PID: 2668)
INFO
Dropped object may contain Bitcoin addresses
- cmd.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:10:04 17:12:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 69632 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 69632 |
| EntryPoint: | 0x22140 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.4.0.0 |
| ProductVersionNumber: | 16.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 16.04 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2016 Igor Pavlov |
| OriginalFileName: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 16.04 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Oct-2016 15:12:31 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 16.04 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2016 Igor Pavlov |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 16.04 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Oct-2016 15:12:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00011000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00012000 | 0x00011000 | 0x00010400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.65372 |
.rsrc | 0x00023000 | 0x00001000 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.54681 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.45504 | 700 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.18403 | 296 | UNKNOWN | English - United States | RT_ICON |
97 | 5.97677 | 184 | UNKNOWN | English - United States | RT_DIALOG |
188 | 5.92196 | 84 | UNKNOWN | English - United States | RT_STRING |
207 | 5.20987 | 52 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.DLL |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
58
Monitored processes
27
Malicious processes
24
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | findstr HEM_OCX_H264.ocx temp.txt | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 796 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | C:\Windows\System32\regsvr32.exe /s C:\Windows\System32\ | C:\Windows\System32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | C:\Windows\system32\cmd.exe /c FINDSTR "HEM_OCX.._H264.ocx" temp.txt | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1008 | FINDSTR "IE.._H264.ocx" temp.txt | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1232 | C:\Windows\System32\regsvr32.exe /s C:\Windows\System32\HEM_COMM.ax | C:\Windows\System32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1256 | find /i "SelfPlayer.exe" temp.txt | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
947
Read events
912
Write events
35
Delete events
0
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (796) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\{4D36E972-E325-11CE-BFC1-08002BE10318}\{4040CF00-1B3E-486A-B407-FA14C56B6FC0}\Connection |
| Operation: | write | Name: | PnpInstanceID |
Value: PCI\VEN_8086&DEV_100E&SUBSYS_11001AF4&REV_03\3&13C0B0C5&0&18 | |||
| (PID) Process: | (2568) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2568) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2568) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2568) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2568) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2568) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2568) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2568) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
2 580
Suspicious files
152
Text files
72
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7zS0DE19146\temp.txt | — | |
MD5:— | SHA256:— | |||
| 860 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3792 | 87fd7d86d4f6c878eb0df22916dbbffedaabe6097649d42e0ce371e75f95be5d.exe | C:\Users\admin\AppData\Local\Temp\7zS0DE19146\Setup.bat | text | |
MD5:— | SHA256:— | |||
| 2668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7zS0DE19146\IEPlugin\aaclient.dll | executable | |
MD5:— | SHA256:— | |||
| 2668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7zS0DE19146\IEPlugin\accessibilitycpl.dll | executable | |
MD5:45C0DF404182850C21749AF7763C095F | SHA256:BFA71A592476BF399E420FF9BCED8554C448A04A7586C8E8CA4C19CBCD2FC5F1 | |||
| 2668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7zS0DE19146\IEPlugin\temp.txt | text | |
MD5:A642F6E5B4B18A2DDE1615804F8099D5 | SHA256:C05ED275142C84C110D0C583DD901FCF31538A84F2AD982E761B31AE7E7FF5EF | |||
| 2668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7zS0DE19146\IEPlugin\12520437.cpx | text | |
MD5:0A0FEB9EB28BDE8CD835716343B03B14 | SHA256:81EA3CF30A5B6DB6BDFA0C71E3ED952C48FD72249E28E11465C6EB4FBA49A41C | |||
| 2668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7zS0DE19146\IEPlugin\acledit.dll | executable | |
MD5:76828928A893D595EF5CA2C53B2B48C0 | SHA256:7FC551E7874FE11563805D205630ADC2B88CB9B9FCC83B020A313108A5F3929A | |||
| 2668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7zS0DE19146\IEPlugin\ActionQueue.dll | executable | |
MD5:97BAF1DE66F886D8292AED040B8CC281 | SHA256:A2F0E585728672281202E8DCAA4DF7AA6DD493120DB32C2601932ADAC1C2527E | |||
| 2668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7zS0DE19146\IEPlugin\12520850.cpx | text | |
MD5:D69AE057CD82D04EE7D311809ABEFB2A | SHA256:DF45B91D9BDD852F49CF043CBD2408C8E139643B413071FF2FA87BFB45940216 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report