| File name: | MemeSense.exe |
| Full analysis: | https://app.any.run/tasks/486b8242-902e-4151-83ed-b2c10d4677ee |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2025, 23:32:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, 4 sections |
| MD5: | 20ACA6048570DEFA05629A00C680AAC0 |
| SHA1: | 1DF4DBC8458A2CDE492282DDDF0BB8963277B9DA |
| SHA256: | 87D0E829168B5A3F992C85E99DF935C14CA0DA95899B85FE9371CC85E52CA879 |
| SSDEEP: | 98304:MpkTXPyx6mudubXjgnru/IZcpHrm5+lGsKHkw7epfydbIzYfgauRHk6AlaMGDsv3:760G4y/uc165+VikwaIdbeMjuRH5Q |
MALICIOUS
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 3288)
- cmd.exe (PID: 5916)
Adds extension to the Windows Defender exclusion list
- updater.exe (PID: 6428)
- MemeSense.exe (PID: 6536)
SUSPICIOUS
Reads security settings of Internet Explorer
- MemeSense.exe (PID: 6432)
Starts POWERSHELL.EXE for commands execution
- MemeSense.exe (PID: 6432)
- MemeSense.exe (PID: 6536)
- updater.exe (PID: 6428)
BASE64 encoded PowerShell command has been detected
- MemeSense.exe (PID: 6432)
Executable content was dropped or overwritten
- MemeSense.exe (PID: 6432)
- MemeSense.exe (PID: 6536)
- updater.exe (PID: 6428)
Base64-obfuscated command line is found
- MemeSense.exe (PID: 6432)
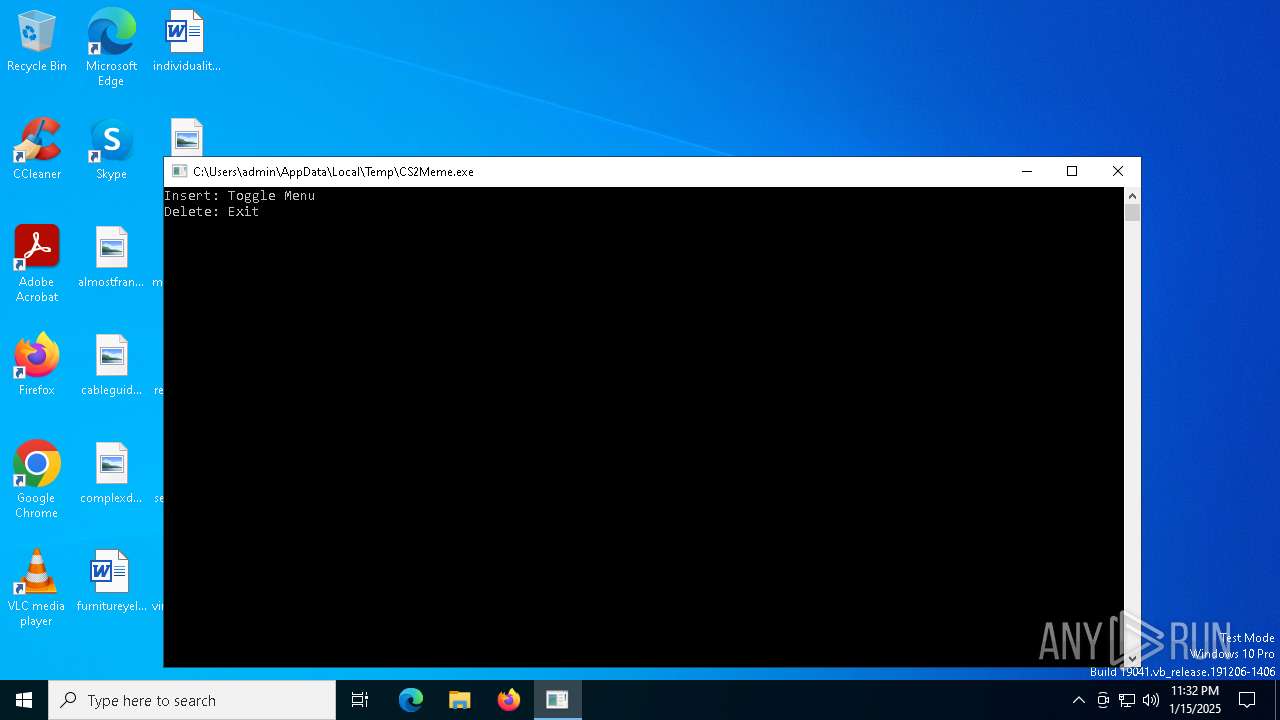
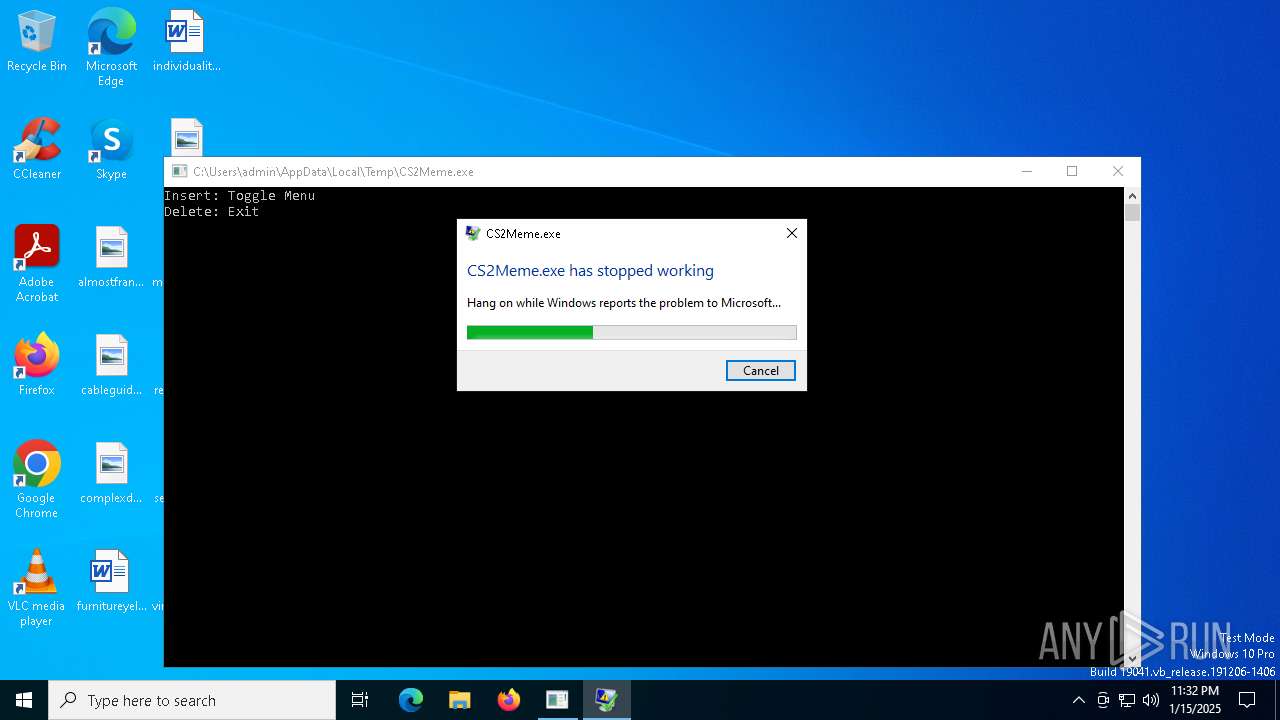
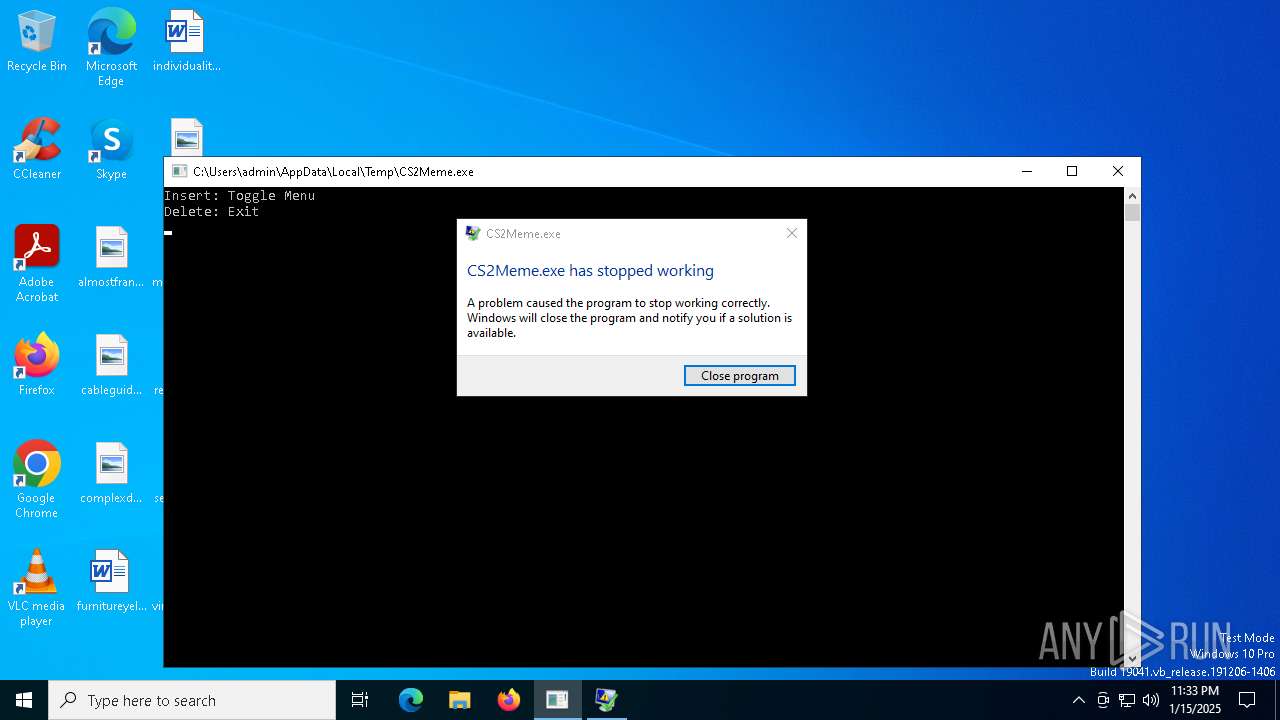
Executes application which crashes
- CS2Meme.exe (PID: 6560)
Script adds exclusion extension to Windows Defender
- MemeSense.exe (PID: 6536)
- updater.exe (PID: 6428)
Manipulates environment variables
- powershell.exe (PID: 836)
- powershell.exe (PID: 1140)
Process uninstalls Windows update
- wusa.exe (PID: 1988)
- wusa.exe (PID: 6544)
Starts SC.EXE for service management
- MemeSense.exe (PID: 6536)
Starts CMD.EXE for commands execution
- MemeSense.exe (PID: 6536)
- updater.exe (PID: 6428)
Windows service management via SC.EXE
- sc.exe (PID: 6276)
- sc.exe (PID: 6776)
Creates a new Windows service
- sc.exe (PID: 7032)
Stops a currently running service
- sc.exe (PID: 7088)
Executes as Windows Service
- updater.exe (PID: 6428)
Script adds exclusion path to Windows Defender
- updater.exe (PID: 6428)
- MemeSense.exe (PID: 6536)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 6428)
Connects to unusual port
- svchost.exe (PID: 6728)
INFO
Checks supported languages
- MemeSense.exe (PID: 6432)
- MemeSense.exe (PID: 6536)
- CS2Meme.exe (PID: 6560)
- updater.exe (PID: 6428)
Reads the computer name
- MemeSense.exe (PID: 6432)
- CS2Meme.exe (PID: 6560)
The sample compiled with english language support
- MemeSense.exe (PID: 6432)
- MemeSense.exe (PID: 6536)
Reads the software policy settings
- WerFault.exe (PID: 6756)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6488)
- powershell.exe (PID: 836)
- powershell.exe (PID: 1140)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6488)
- powershell.exe (PID: 836)
- powershell.exe (PID: 1140)
Checks proxy server information
- WerFault.exe (PID: 6756)
The sample compiled with japanese language support
- updater.exe (PID: 6428)
The process uses the downloaded file
- powershell.exe (PID: 1140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 2048 |
| InitializedDataSize: | 5931008 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14d1 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
160
Monitored processes
29
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe Add-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramData) -ExclusionExtension '.exe' -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | MemeSense.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe Add-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramData) -ExclusionExtension '.exe' -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1988 | wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\wusa.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3288 | C:\WINDOWS\system32\cmd.exe /c wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\cmd.exe | — | MemeSense.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4912 | C:\WINDOWS\system32\conhost.exe | C:\Windows\System32\conhost.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4932 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5916 | C:\WINDOWS\system32\cmd.exe /c wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\cmd.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6228 | "C:\Users\admin\AppData\Local\Temp\MemeSense.exe" | C:\Users\admin\AppData\Local\Temp\MemeSense.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 409
Read events
20 382
Write events
24
Delete events
3
Modification events
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile\cs2meme.exe|dbd4d1d40a2e62c4 |
| Operation: | write | Name: | ProgramId |
Value: 0006fc12102139b109b770a6be9a73dd6bfa0000ffff | |||
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile\cs2meme.exe|dbd4d1d40a2e62c4 |
| Operation: | write | Name: | FileId |
Value: 00003a28cc8fb8b845c0c5f35c0b94e3e8939c8a8cc2 | |||
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile\cs2meme.exe|dbd4d1d40a2e62c4 |
| Operation: | write | Name: | LowerCaseLongPath |
Value: c:\users\admin\appdata\local\temp\cs2meme.exe | |||
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile\cs2meme.exe|dbd4d1d40a2e62c4 |
| Operation: | write | Name: | LongPathHash |
Value: cs2meme.exe|dbd4d1d40a2e62c4 | |||
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile\cs2meme.exe|dbd4d1d40a2e62c4 |
| Operation: | write | Name: | Name |
Value: CS2Meme.exe | |||
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile\cs2meme.exe|dbd4d1d40a2e62c4 |
| Operation: | write | Name: | OriginalFileName |
Value: | |||
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile\cs2meme.exe|dbd4d1d40a2e62c4 |
| Operation: | write | Name: | Publisher |
Value: | |||
| (PID) Process: | (6756) WerFault.exe | Key: | \REGISTRY\A\{7442e59f-bad1-eae6-ee61-c8ca311150e0}\Root\InventoryApplicationFile\cs2meme.exe|dbd4d1d40a2e62c4 |
| Operation: | write | Name: | Version |
Value: | |||
Executable files
4
Suspicious files
9
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6756 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_CS2Meme.exe_70842639819443612e668873df97bc987c486ca_bc470869_6106a40f-77b2-4913-a759-8bd85678bbe7\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6432 | MemeSense.exe | C:\Users\admin\AppData\Roaming\MemeSense.exe | executable | |
MD5:1AA21BFAC88449ACCC68DF9B8A510FDE | SHA256:655830948EF3D97ADEE36DFAF18B9AA8716795A853F375D6E827093E8BD9B728 | |||
| 6756 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:51D884E4BD4D3218242657CC94CCD810 | SHA256:7105BBB7D6243EF15CDEFAFE8183DC366A714D8A1B0B8CD8234E749105D43ADE | |||
| 6756 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FA84E4BCC92AA5DB735AB50711040CDE | SHA256:6D7205E794FDE4219A62D9692ECDDF612663A5CF20399E79BE87B851FCA4CA33 | |||
| 6756 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:F6F53CD09A41E968C363419B279D3112 | SHA256:6D2BB01CC7A9BADE2113B219CAC1BDA86B2733196B7E1BD0C807CE1E396B1892 | |||
| 6488 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zmsdql0c.fzm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6488 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a2uddxjy.gcn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6488 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2siywdni.ira.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6756 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5CAA.tmp.dmp | binary | |
MD5:ADF3322EF2768EE9D7FB247589EDA5FA | SHA256:9A27AC6271CF440552BA8121E418F55C8BA7AD113B9C2953173BAA8333622703 | |||
| 6756 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5E32.tmp.xml | xml | |
MD5:214555C3AD8190A85FD70922C3BC1F3C | SHA256:D84FA1D257782AB85FD2DC589DA7B9C30F4E90D241F6077542328AD87570DC92 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
38
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
6756 | WerFault.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
6756 | WerFault.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
4816 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
6176 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
4816 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1412 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.65.132:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
gulf.moneroocean.stream |
| shared |