| File name: | 87c06023a062f0ae515fb03014748a0b51d5e8011f573073224728c6c942b89e.exe |
| Full analysis: | https://app.any.run/tasks/572f0421-49bf-4774-8f56-921f51f6a6ea |
| Verdict: | Malicious activity |
| Analysis date: | May 06, 2024, 08:46:01 |
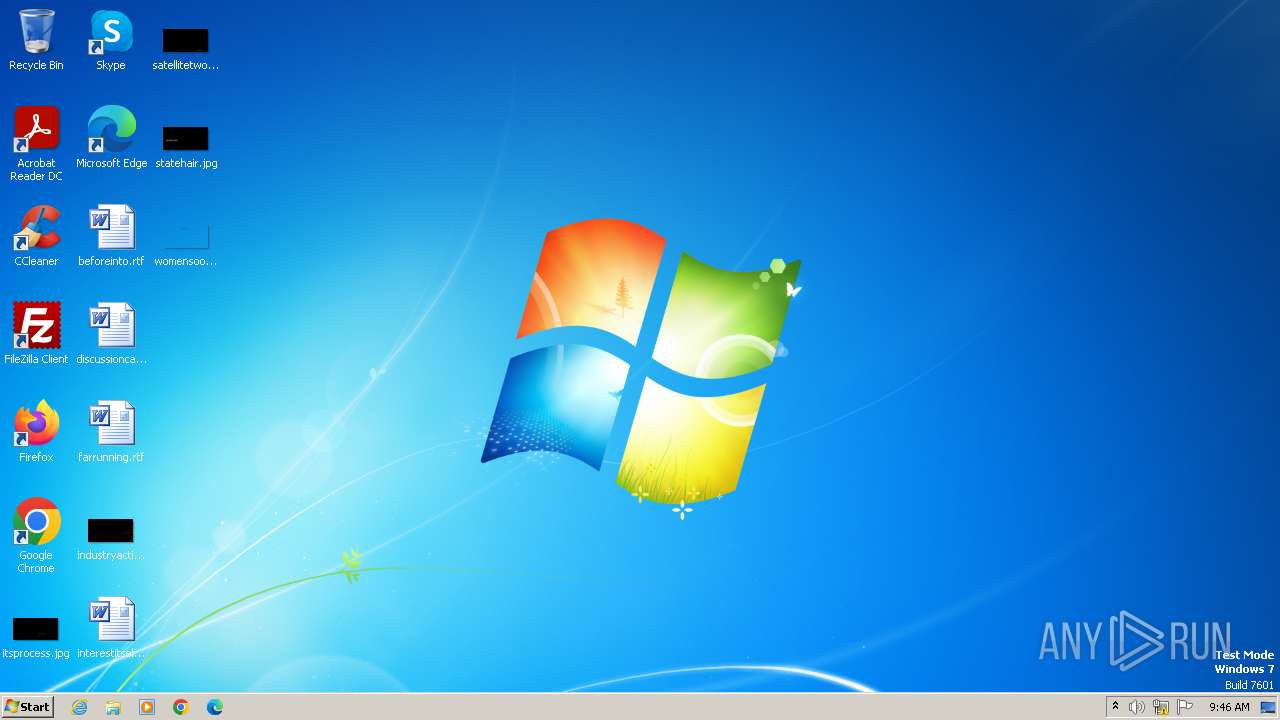
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 06C758C576DE9E18DB3394F1044B27AE |
| SHA1: | 083FD8B33D74E8B52E3847709B086166BA9D2ECA |
| SHA256: | 87C06023A062F0AE515FB03014748A0B51D5E8011F573073224728C6C942B89E |
| SSDEEP: | 12288:kYngrypv+QSphd3nVbdxXP9MErTWn0rqk:kYnIypGQMhpdPXP9MErin0rT |
MALICIOUS
Drops the executable file immediately after the start
- 87c06023a062f0ae515fb03014748a0b51d5e8011f573073224728c6c942b89e.exe (PID: 3976)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 4000)
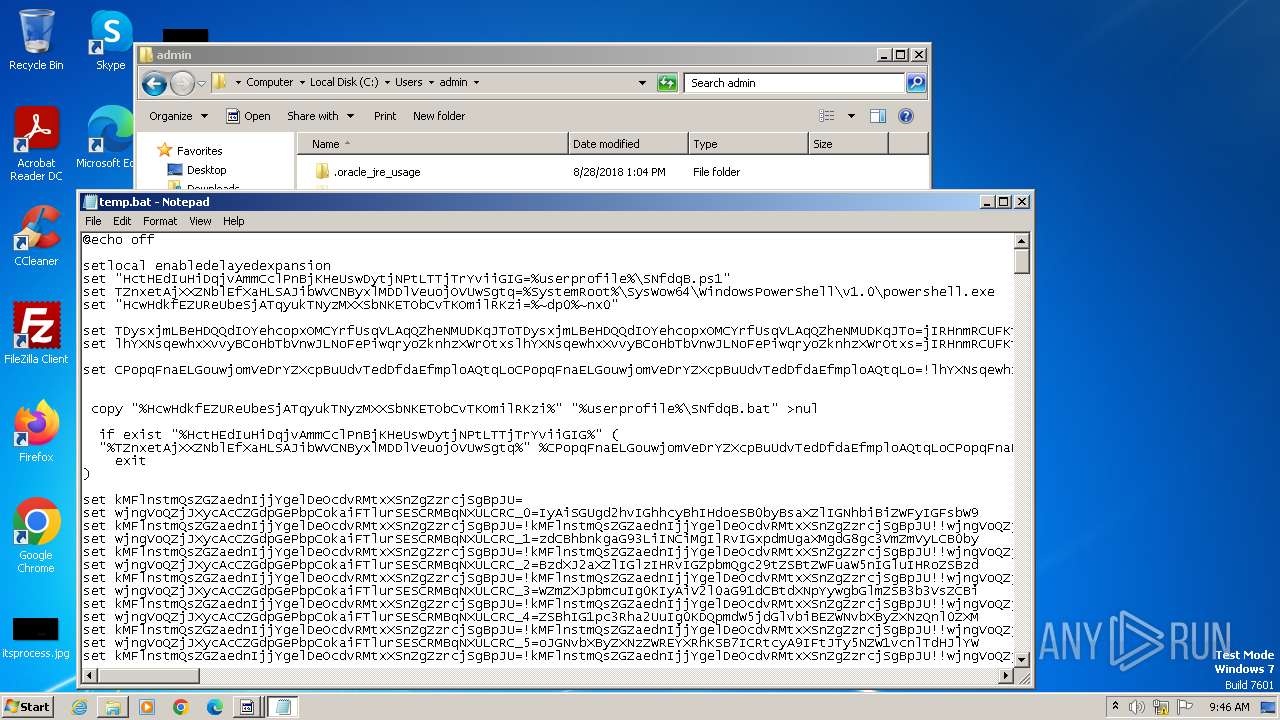
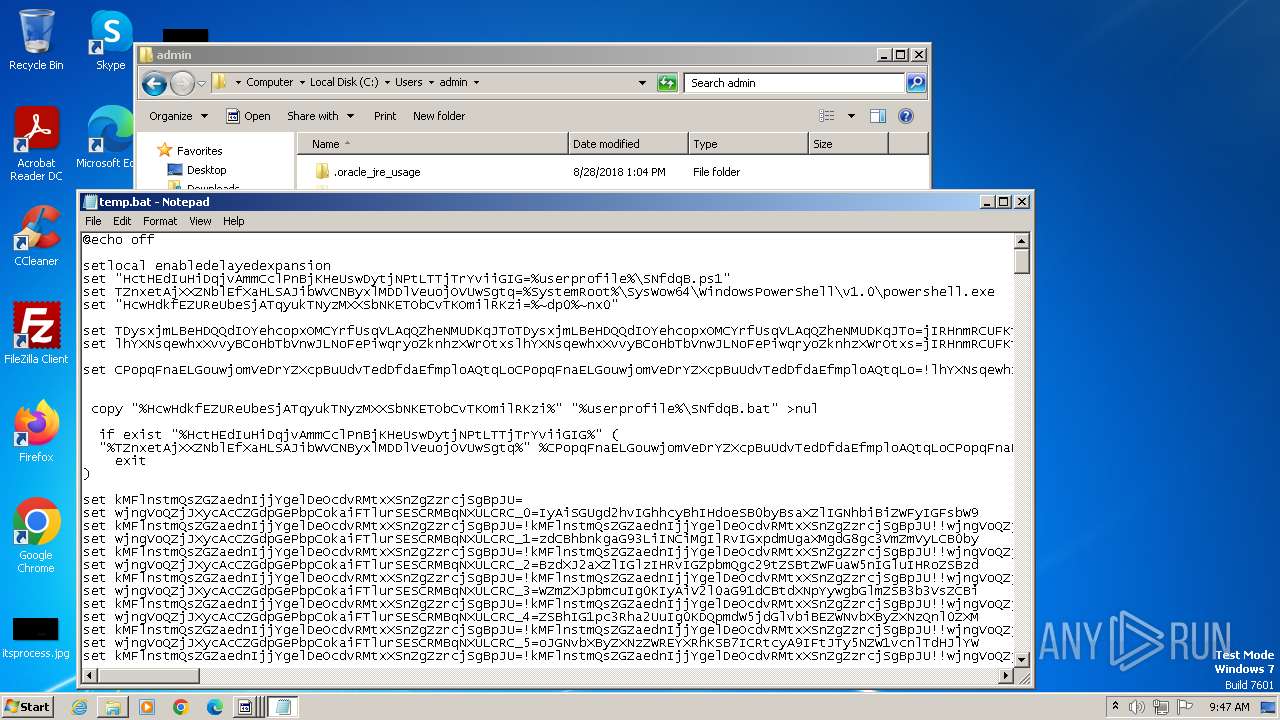
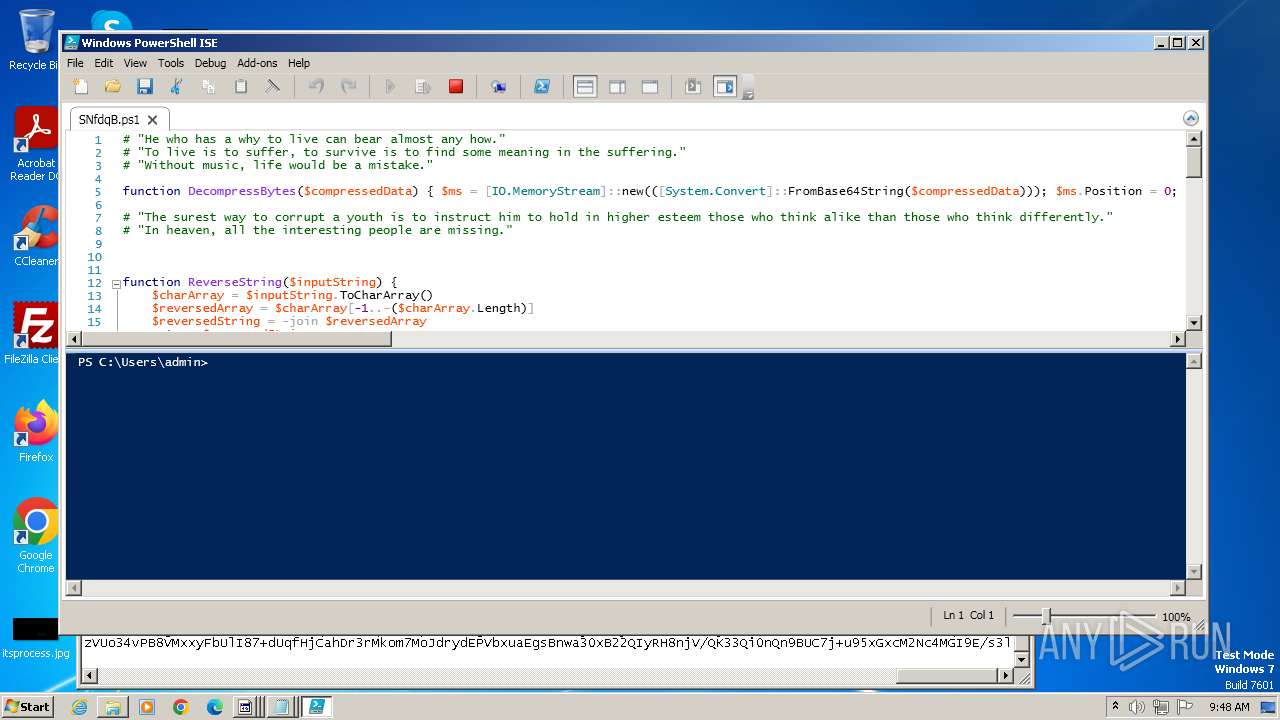
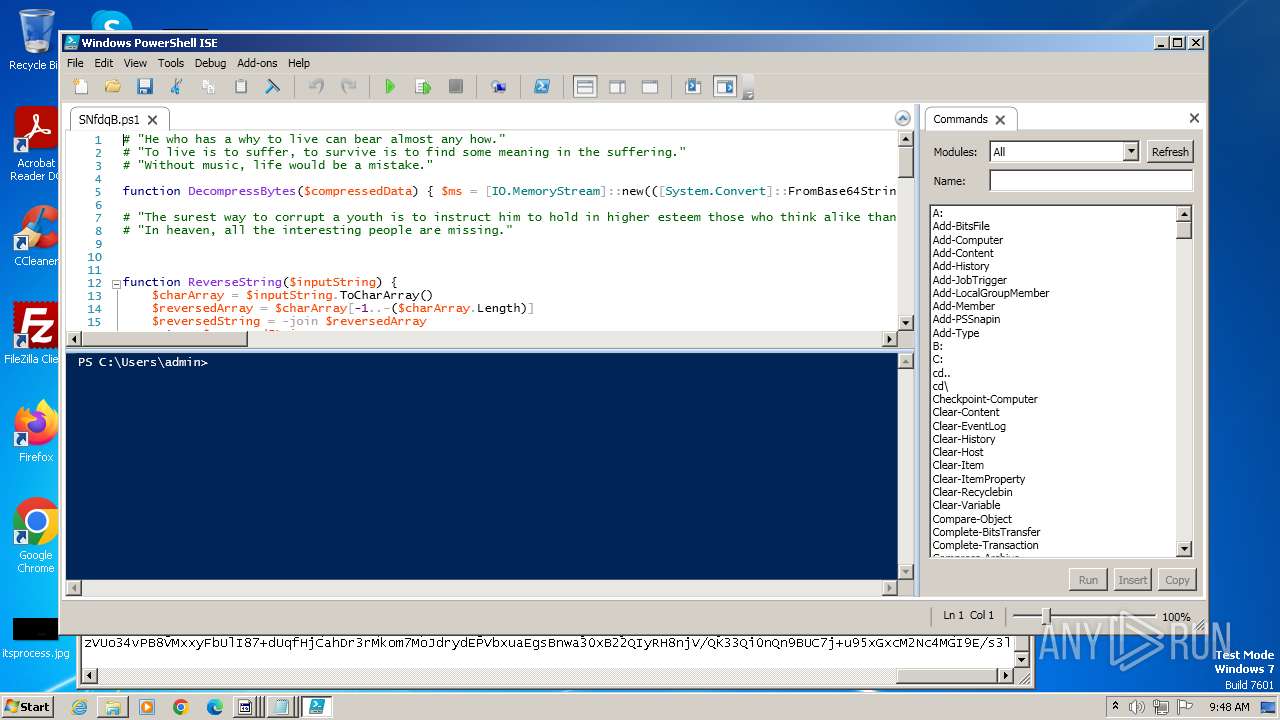
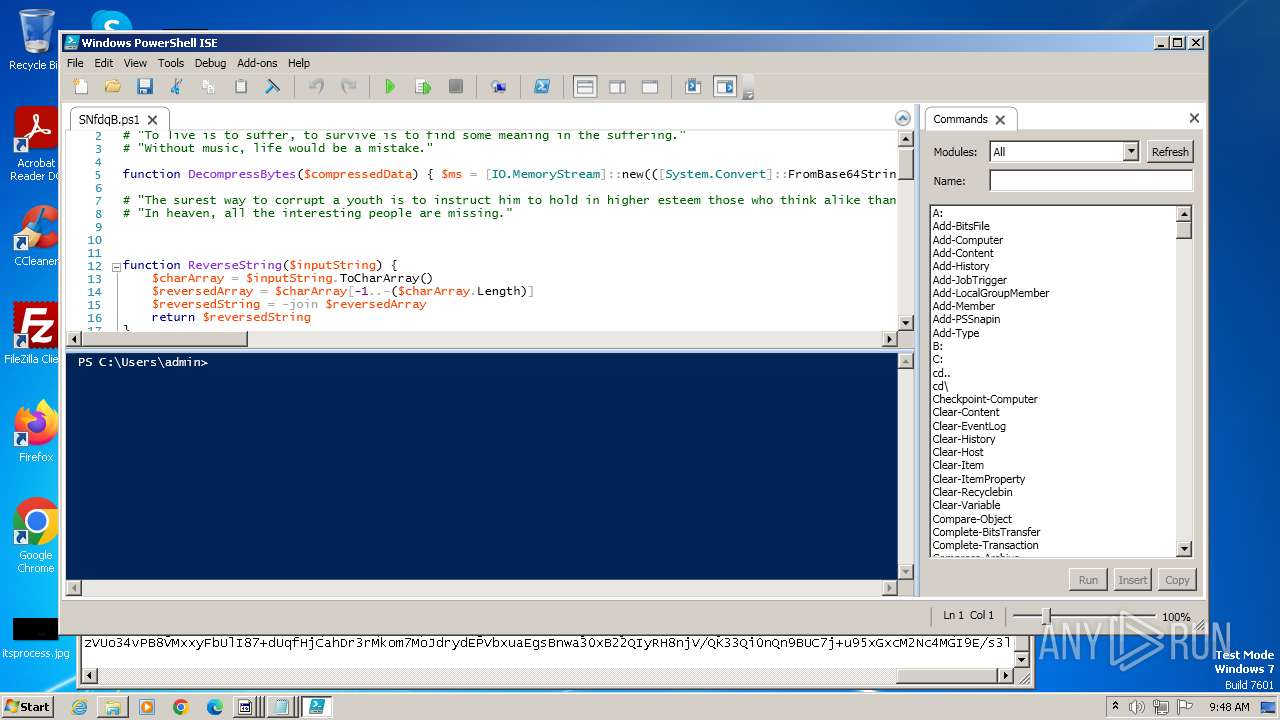
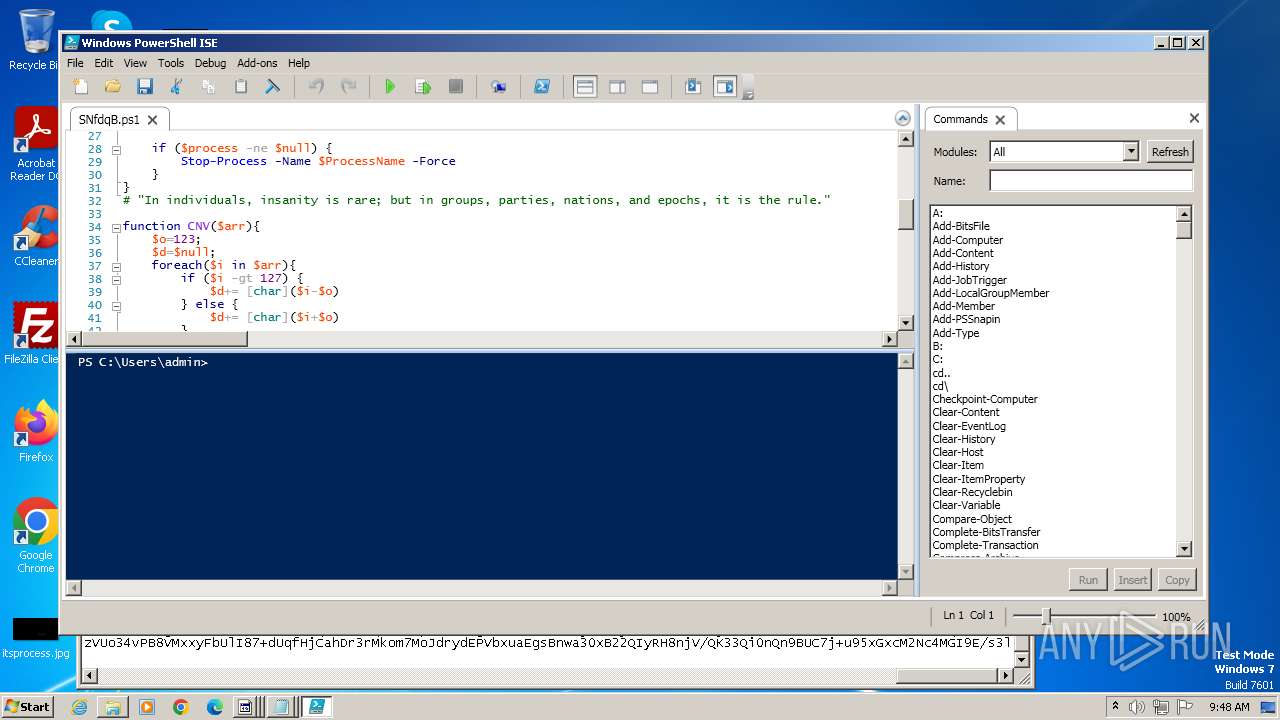
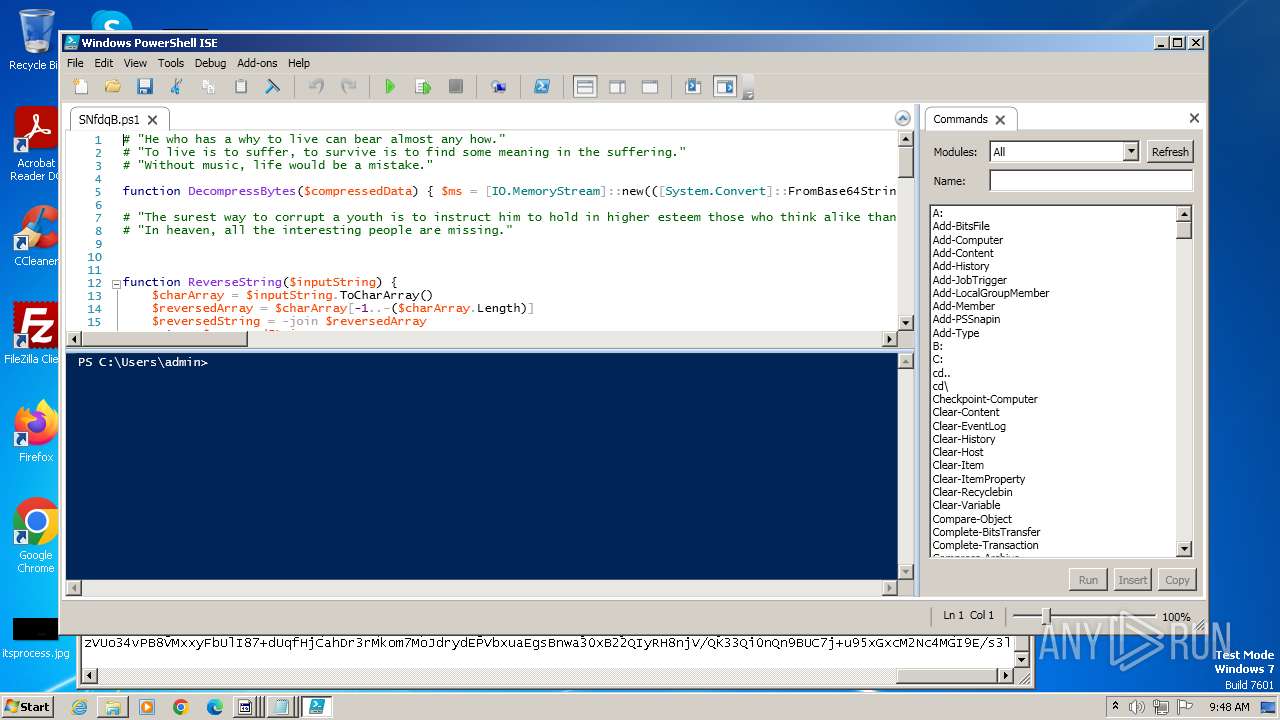
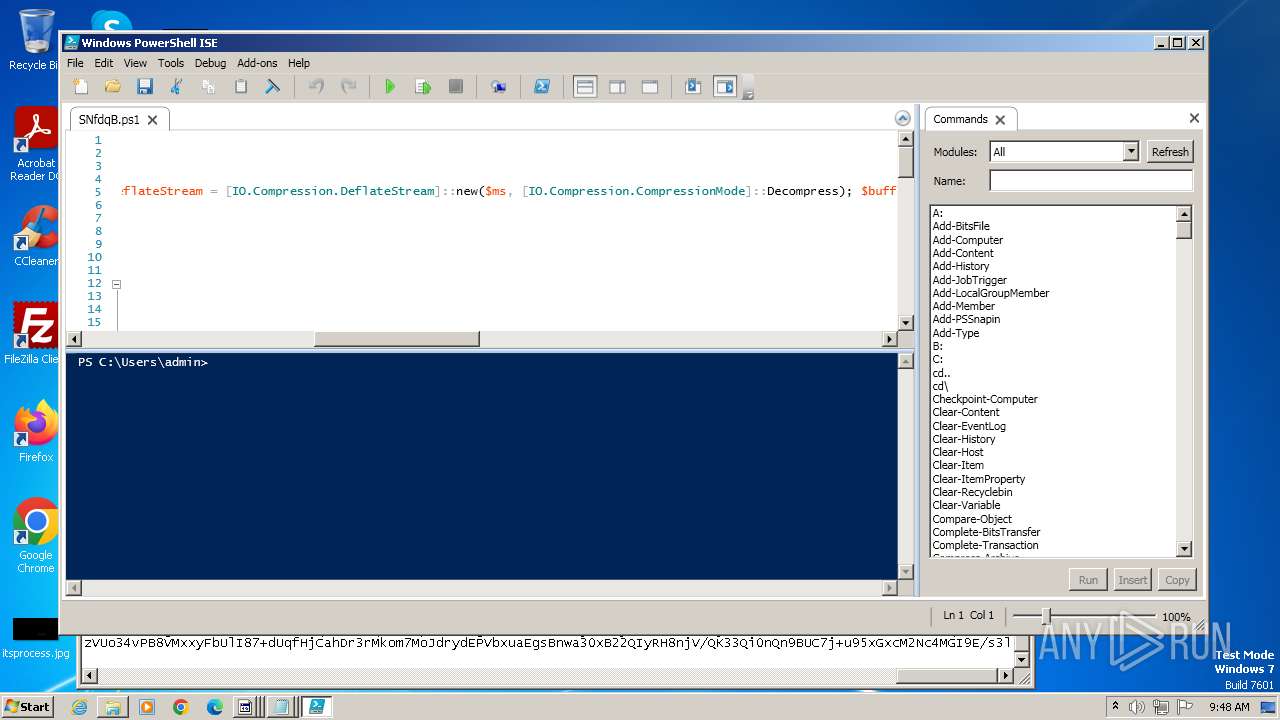
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 4040)
Bypass execution policy to execute commands
- powershell.exe (PID: 1064)
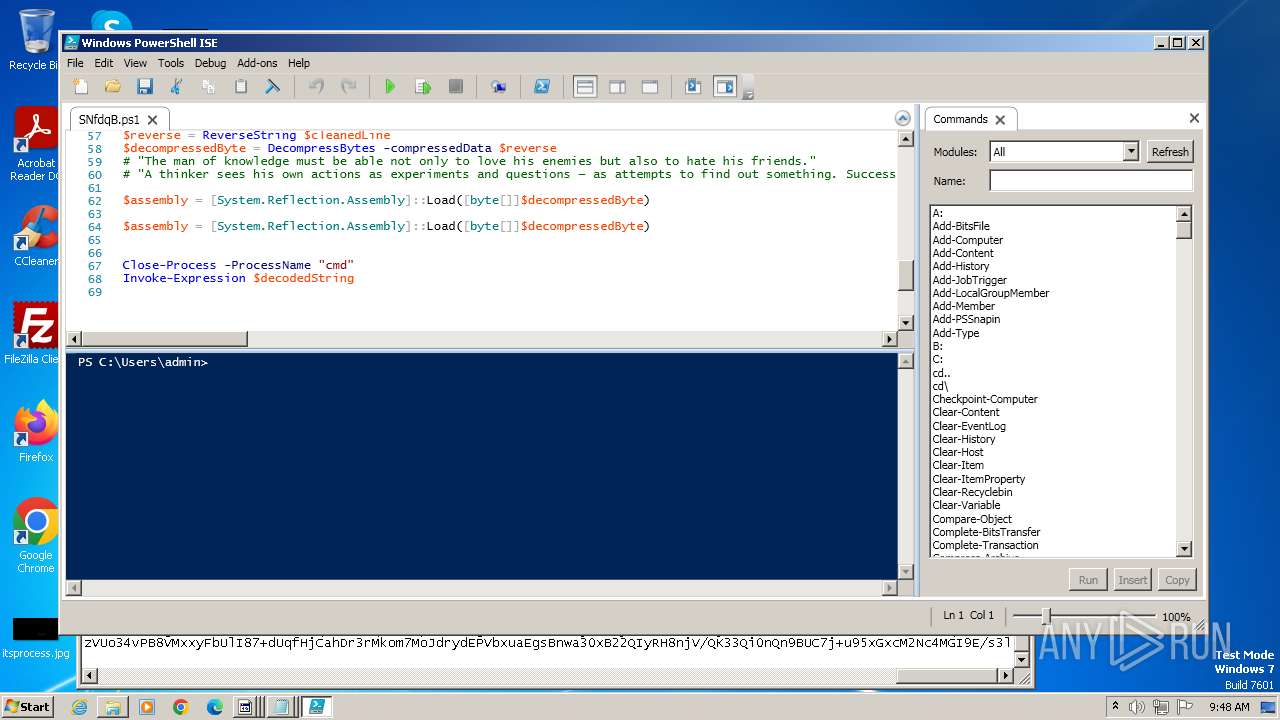
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 1064)
SUSPICIOUS
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 4000)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4000)
Reads the Internet Settings
- wscript.exe (PID: 4000)
- powershell_ise.exe (PID: 1380)
The process executes Powershell scripts
- cmd.exe (PID: 4040)
The process executes VB scripts
- 87c06023a062f0ae515fb03014748a0b51d5e8011f573073224728c6c942b89e.exe (PID: 3976)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4040)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 4000)
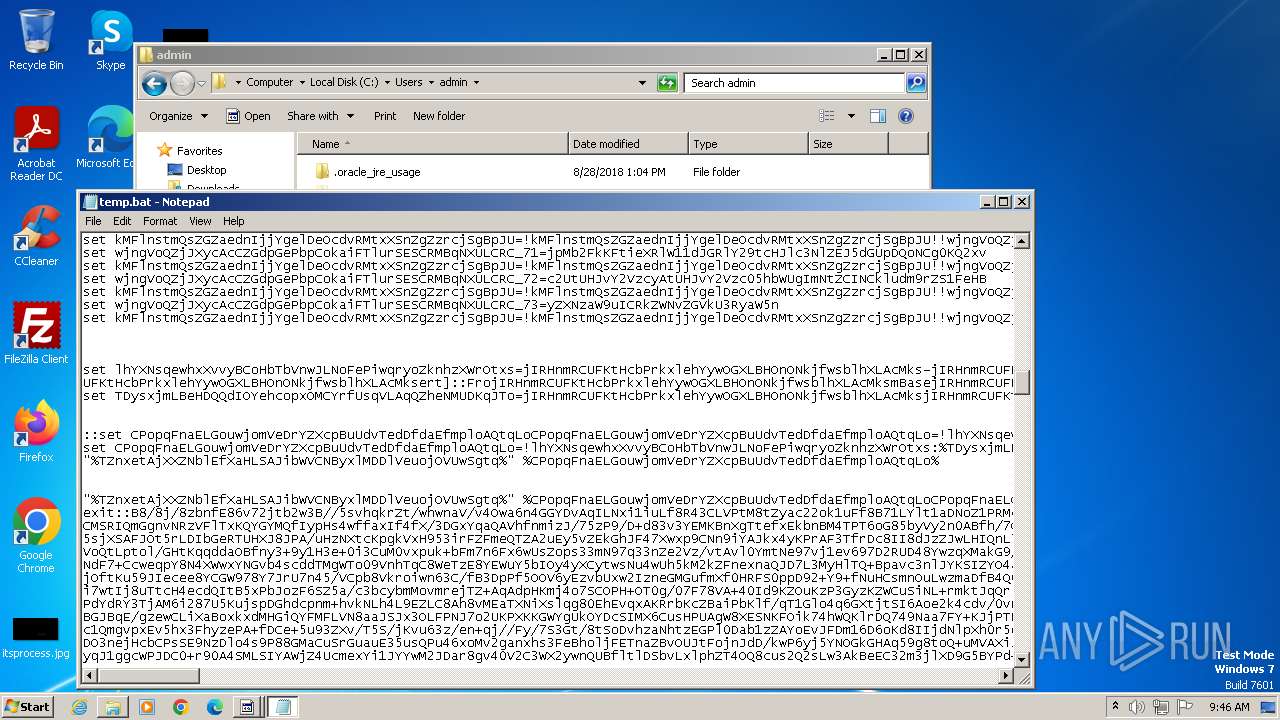
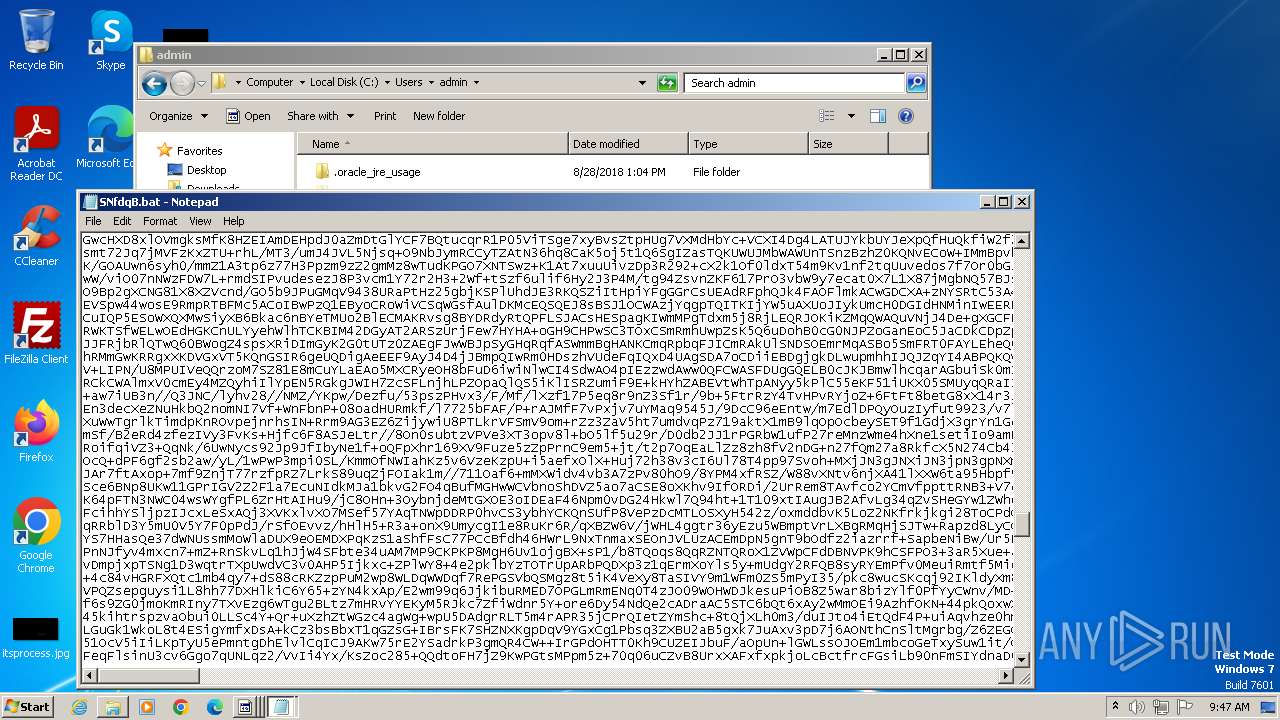
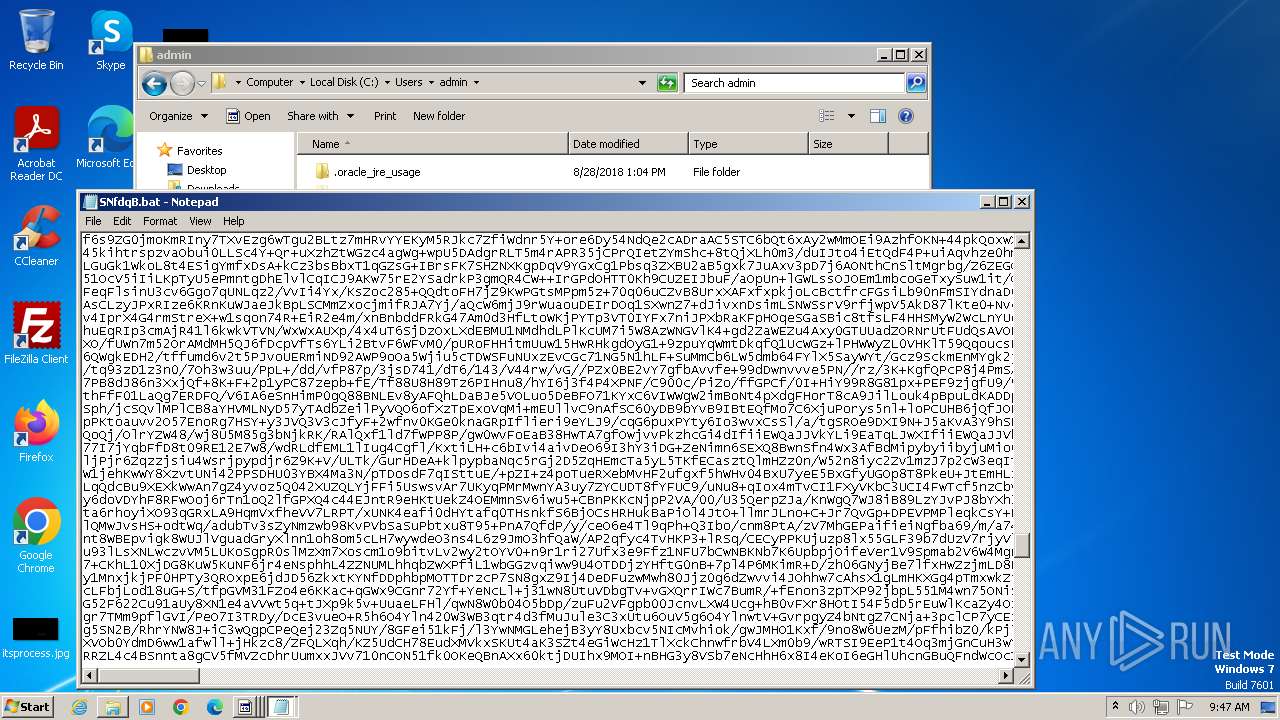
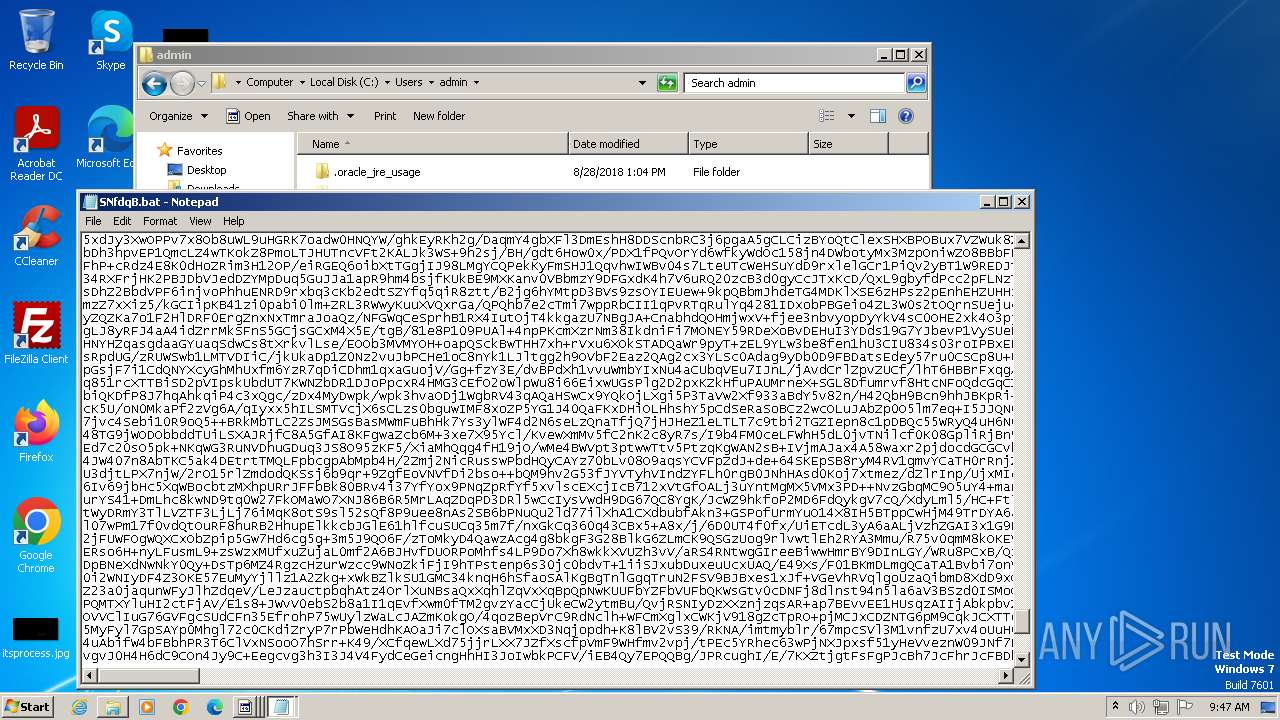
Base64-obfuscated command line is found
- cmd.exe (PID: 4040)
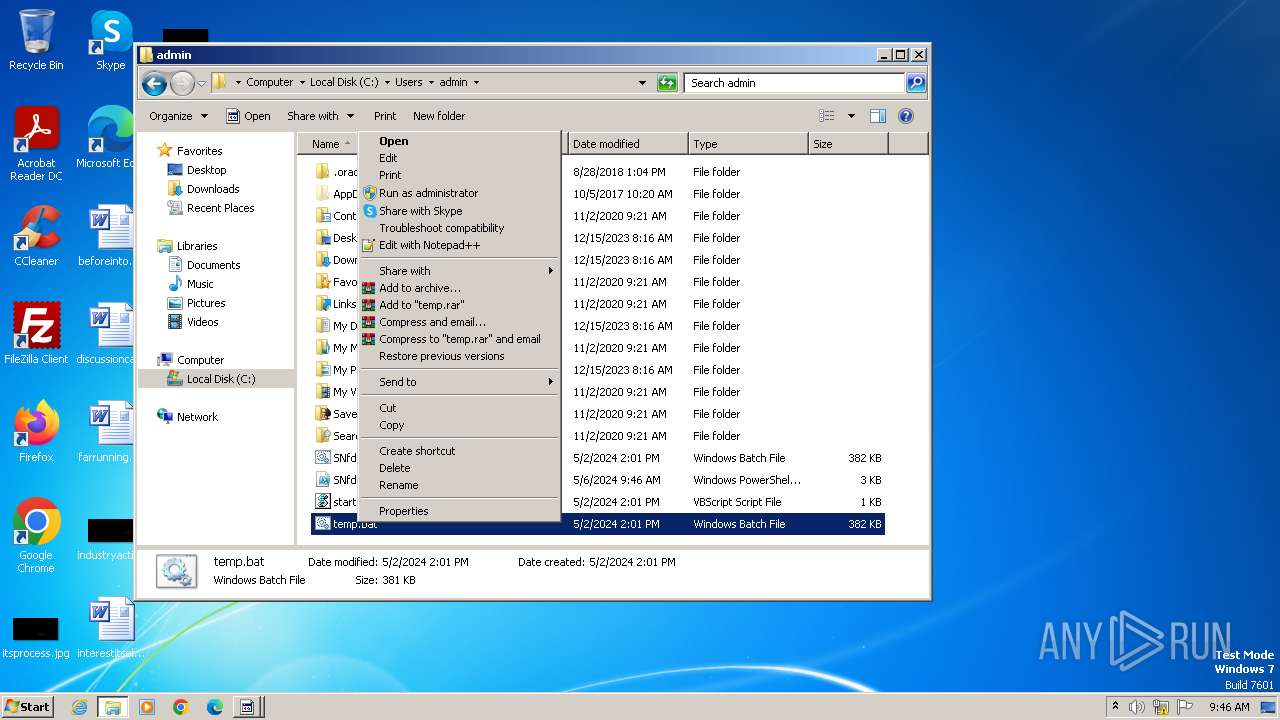
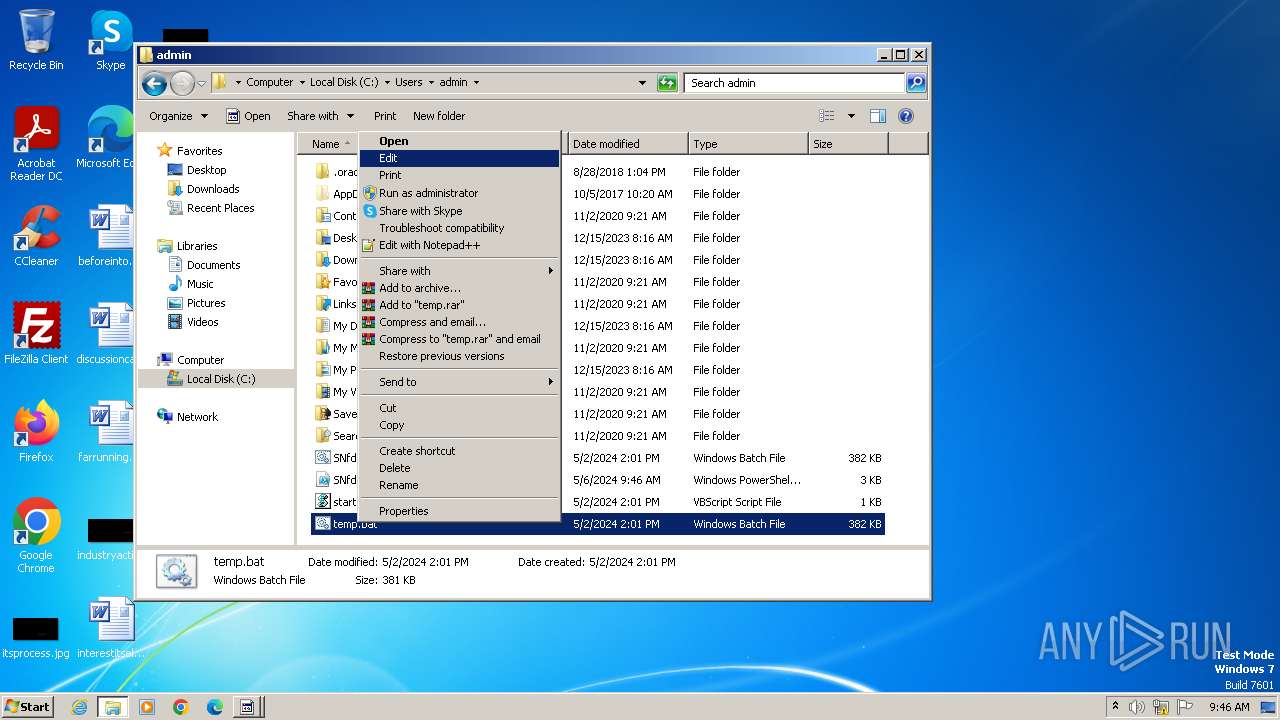
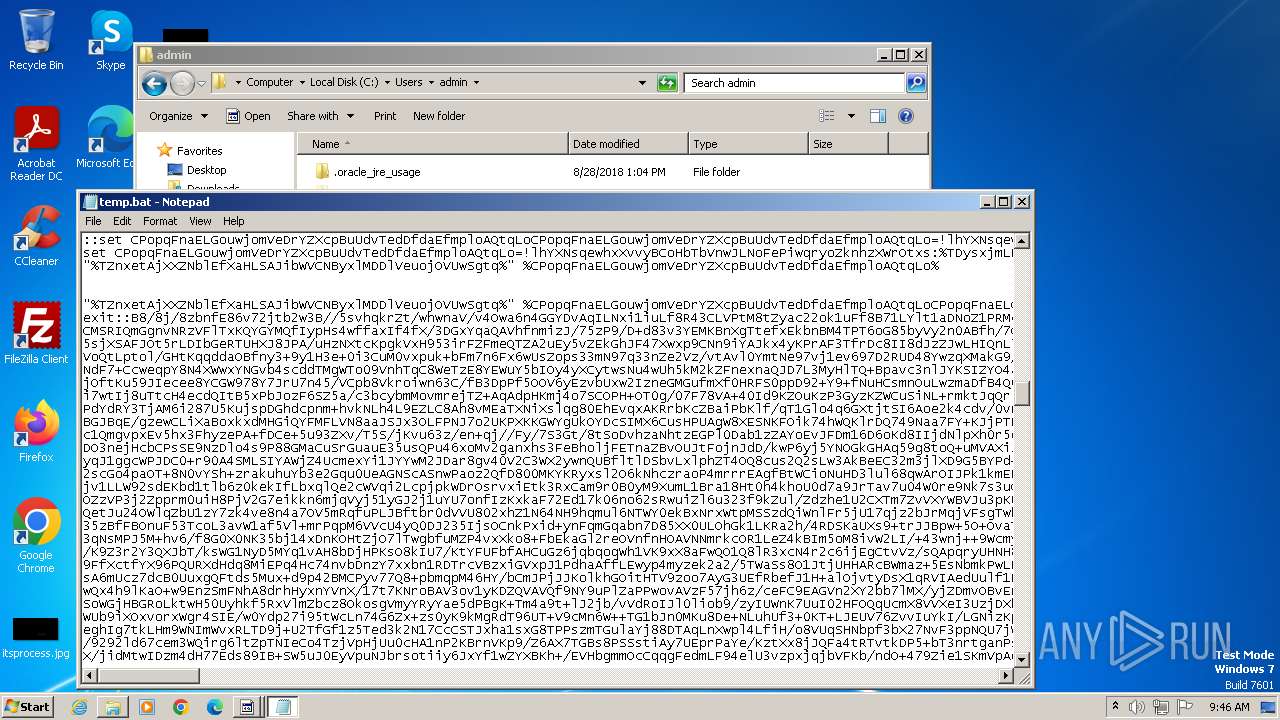
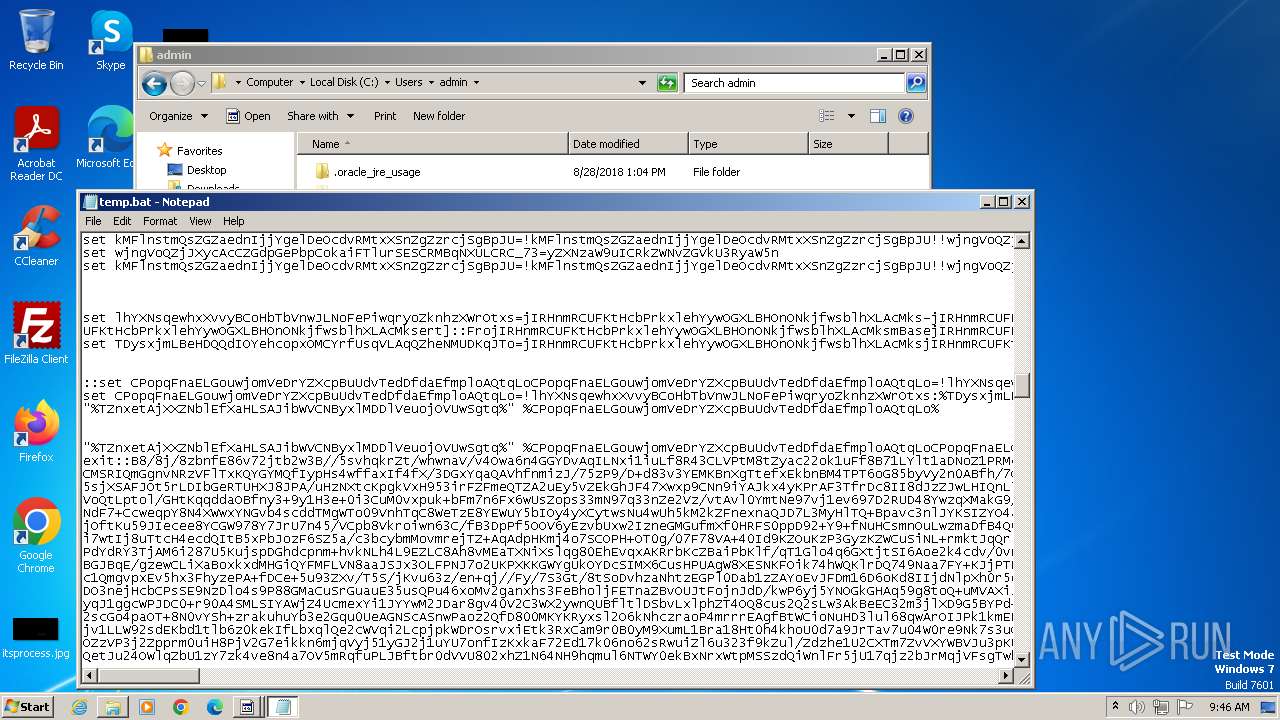
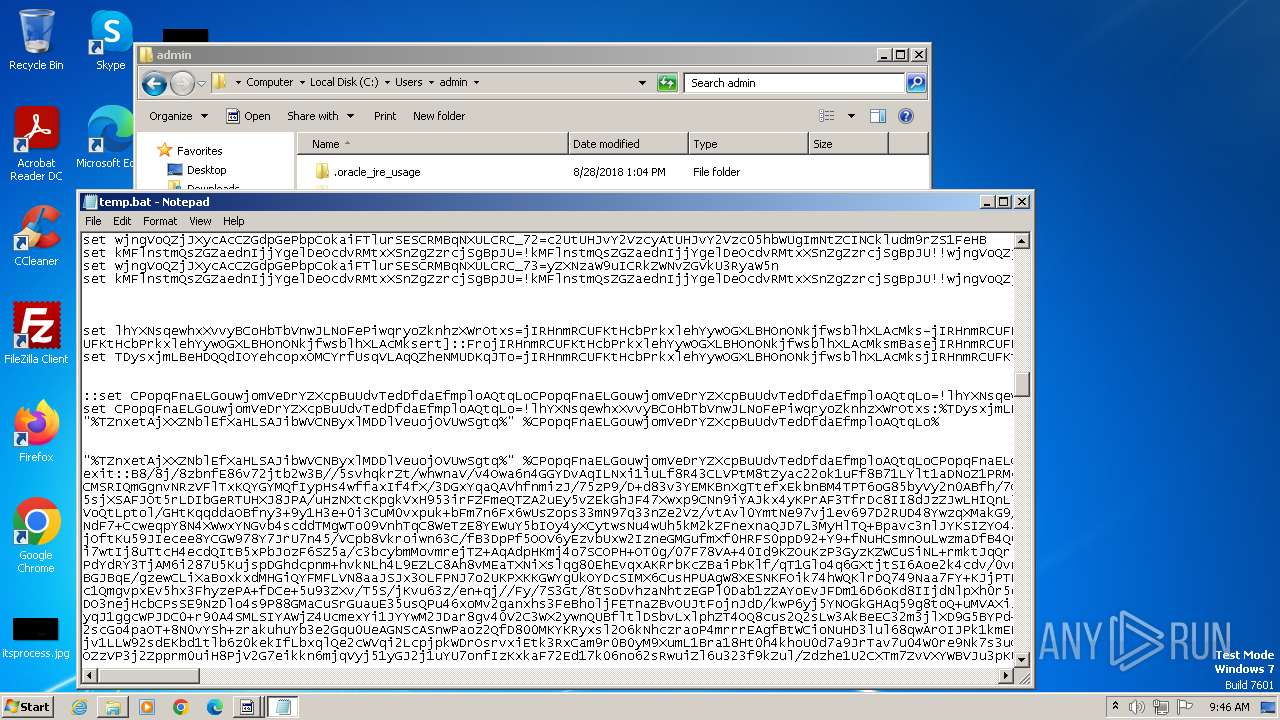
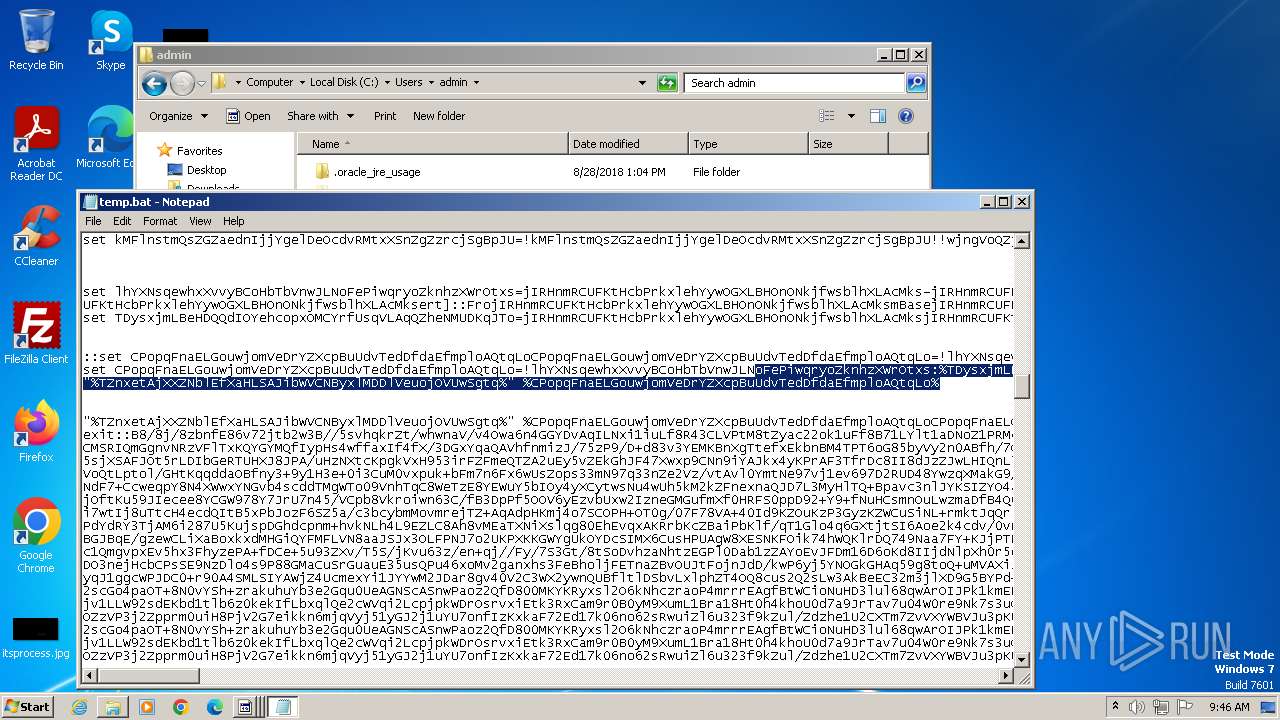
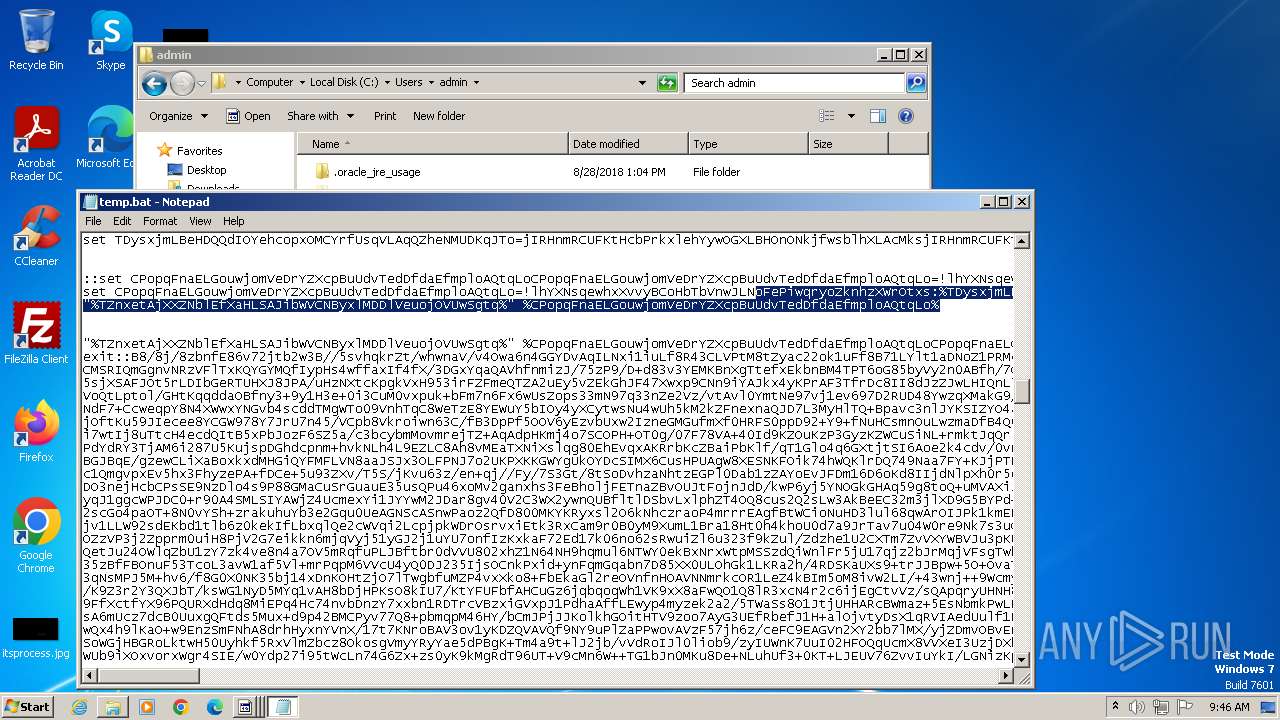
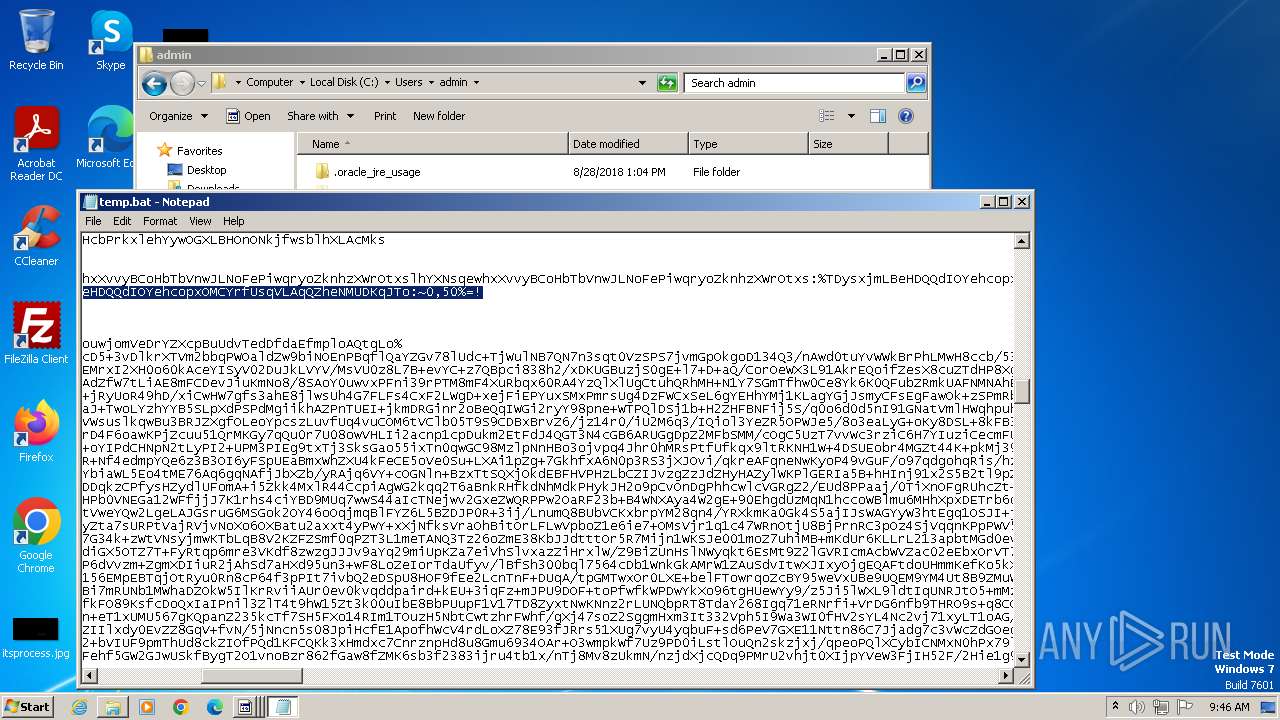
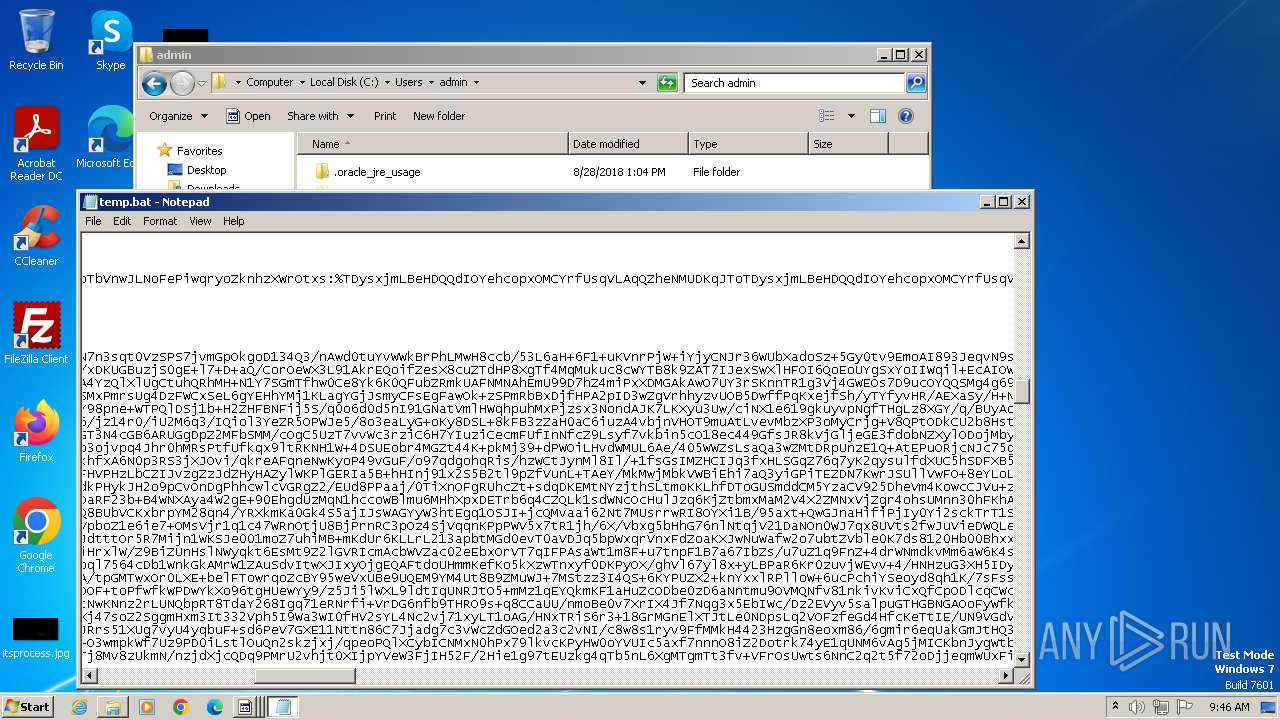
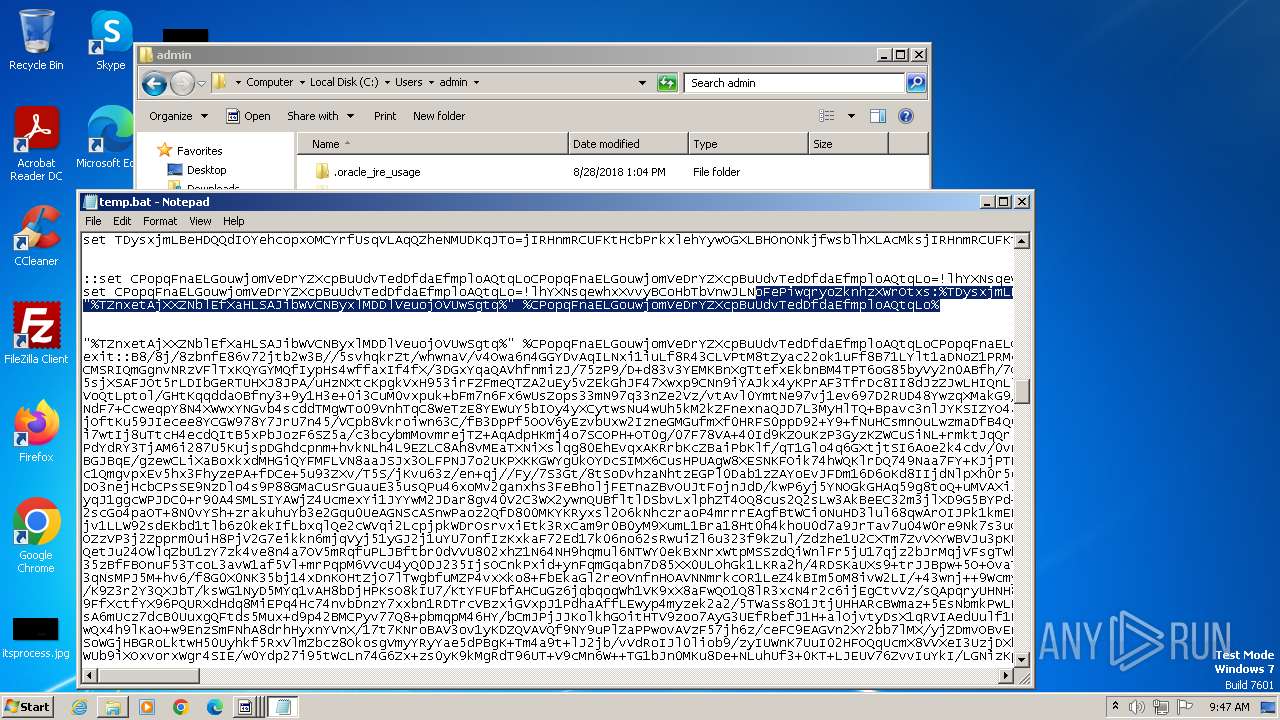
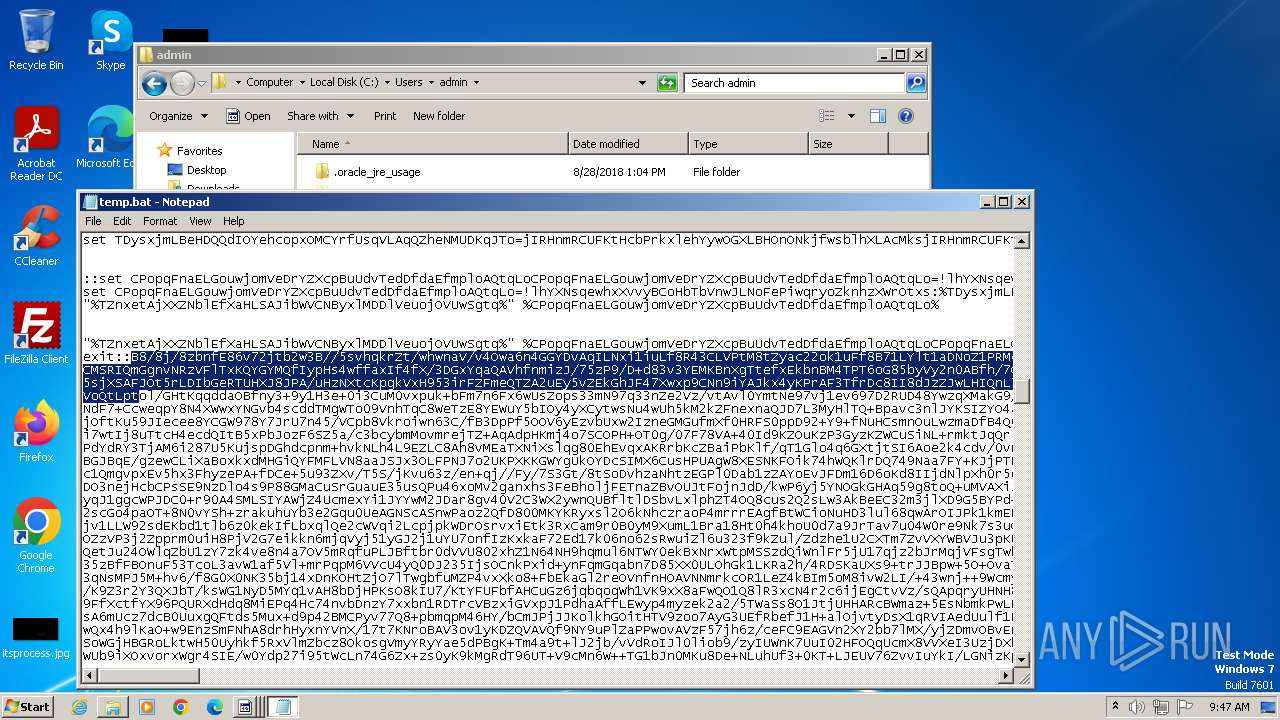
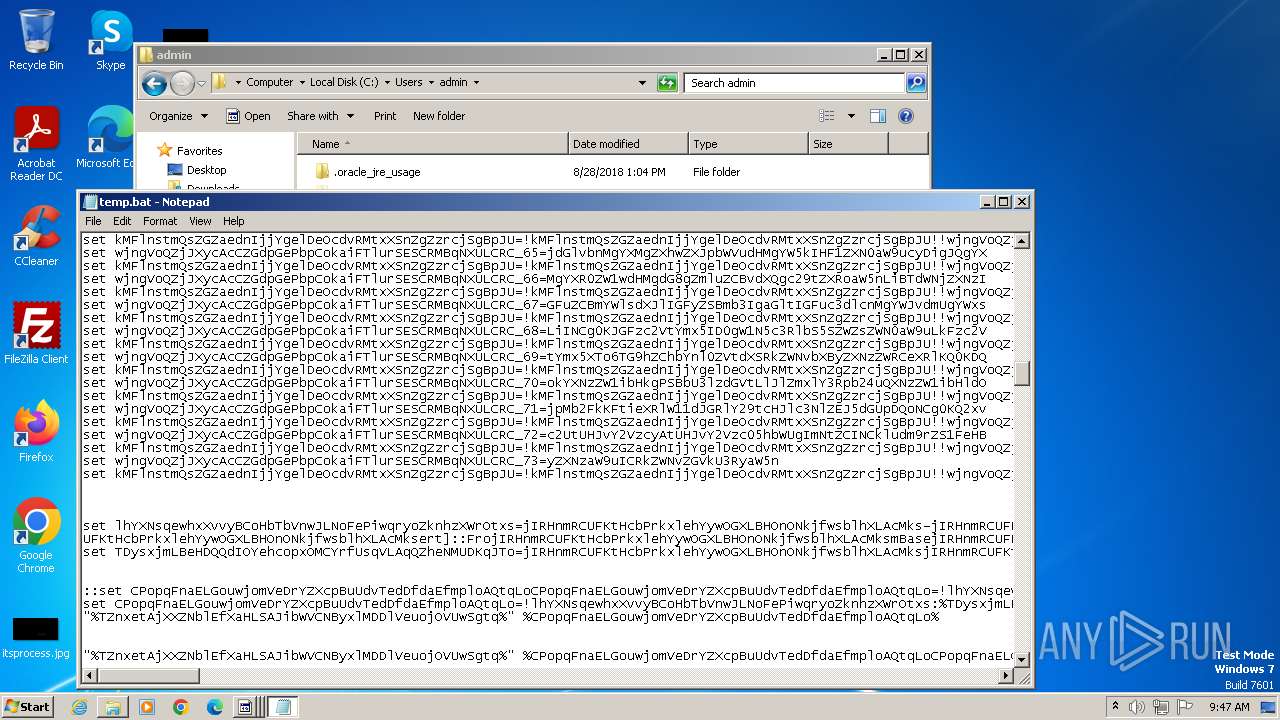
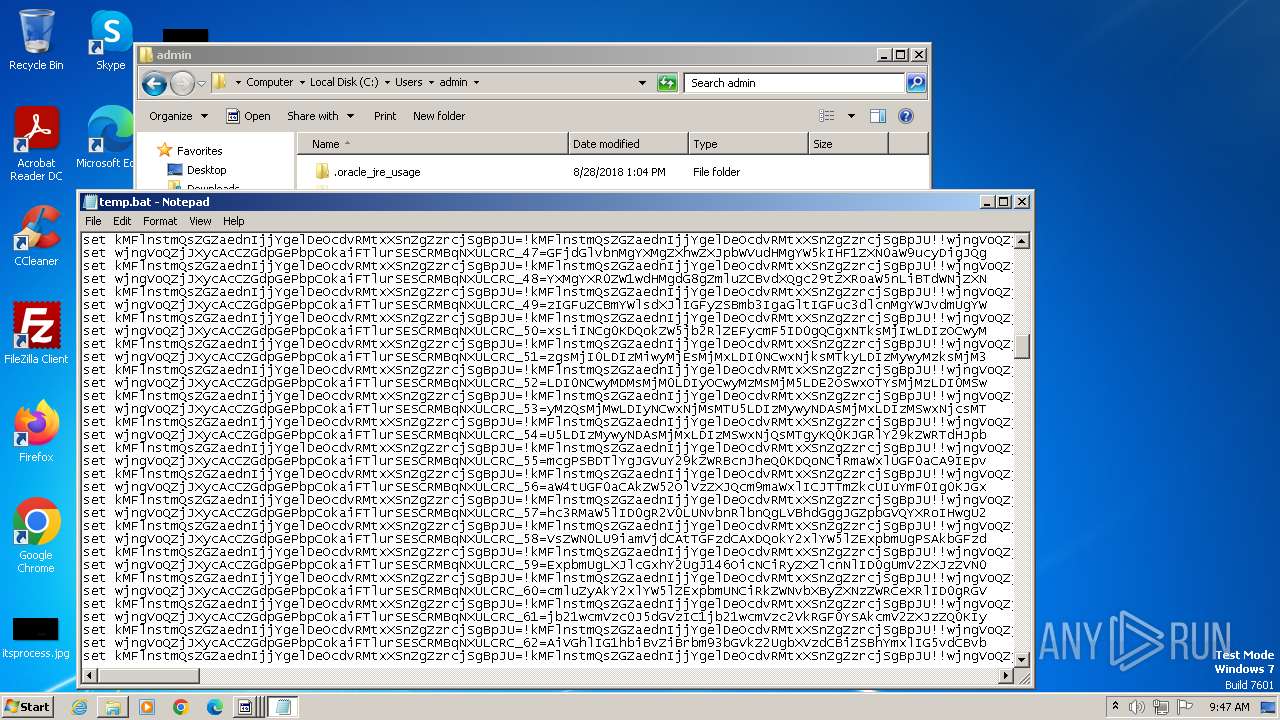
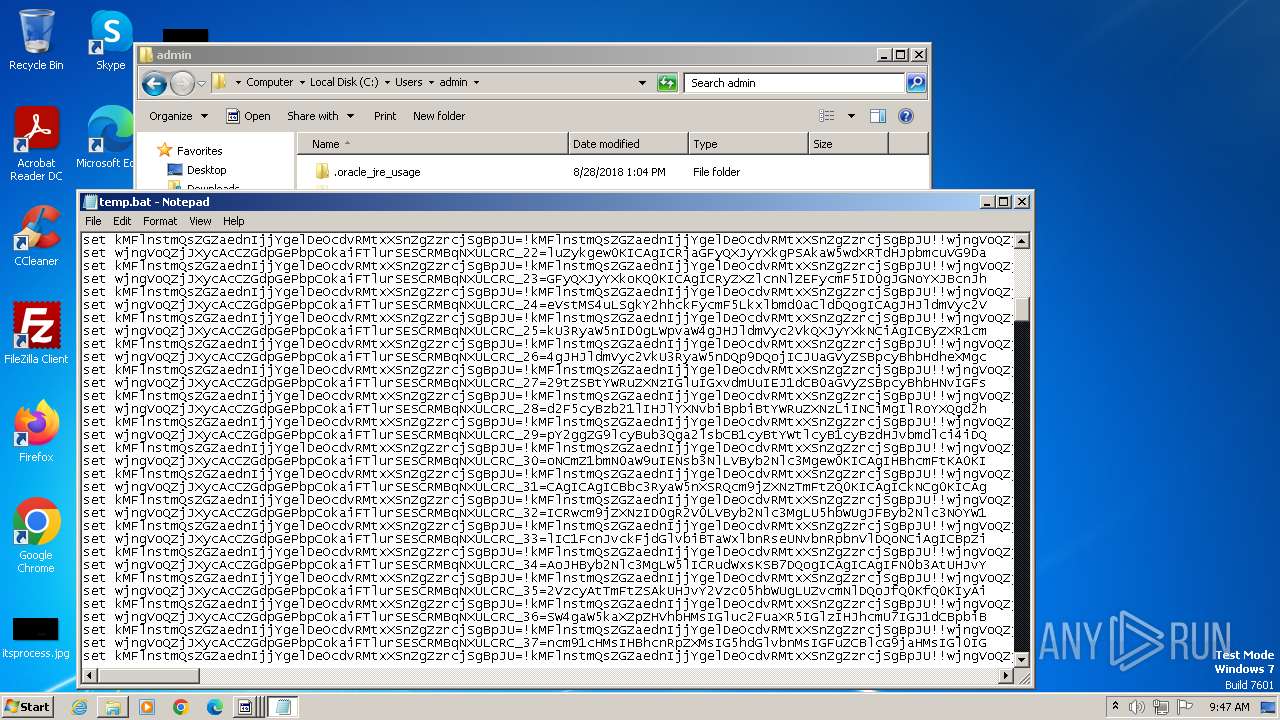
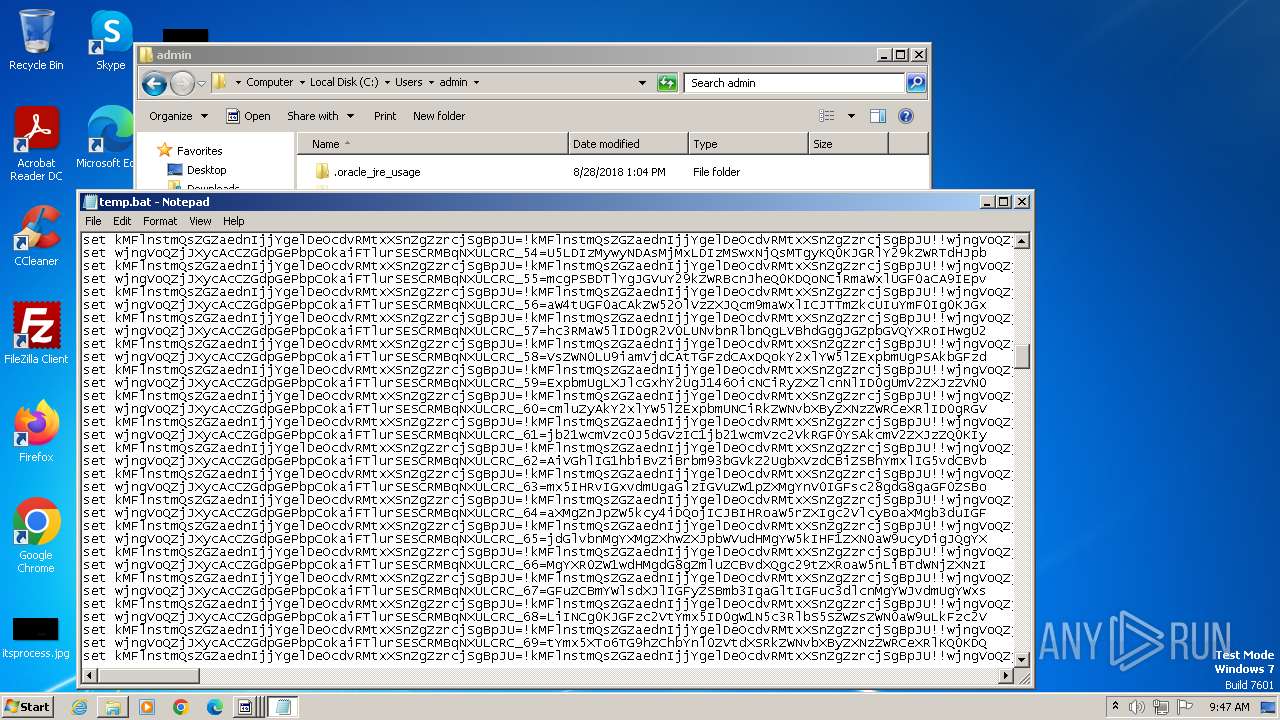
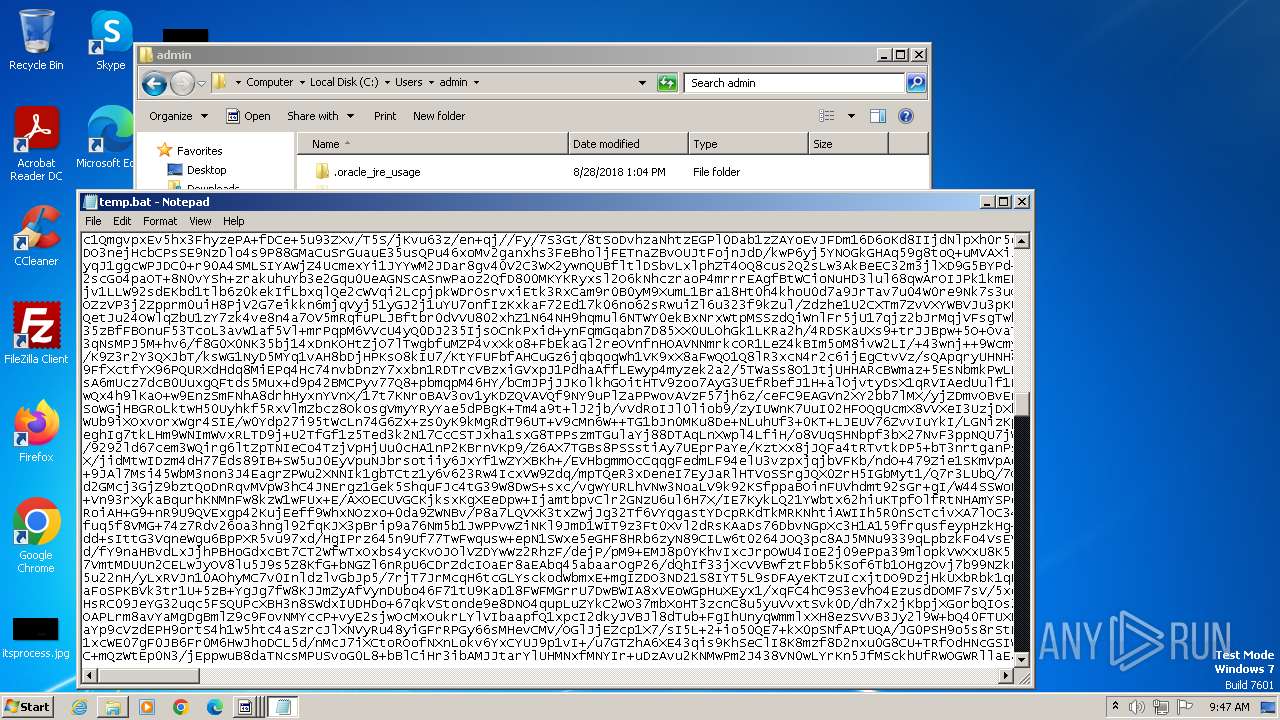
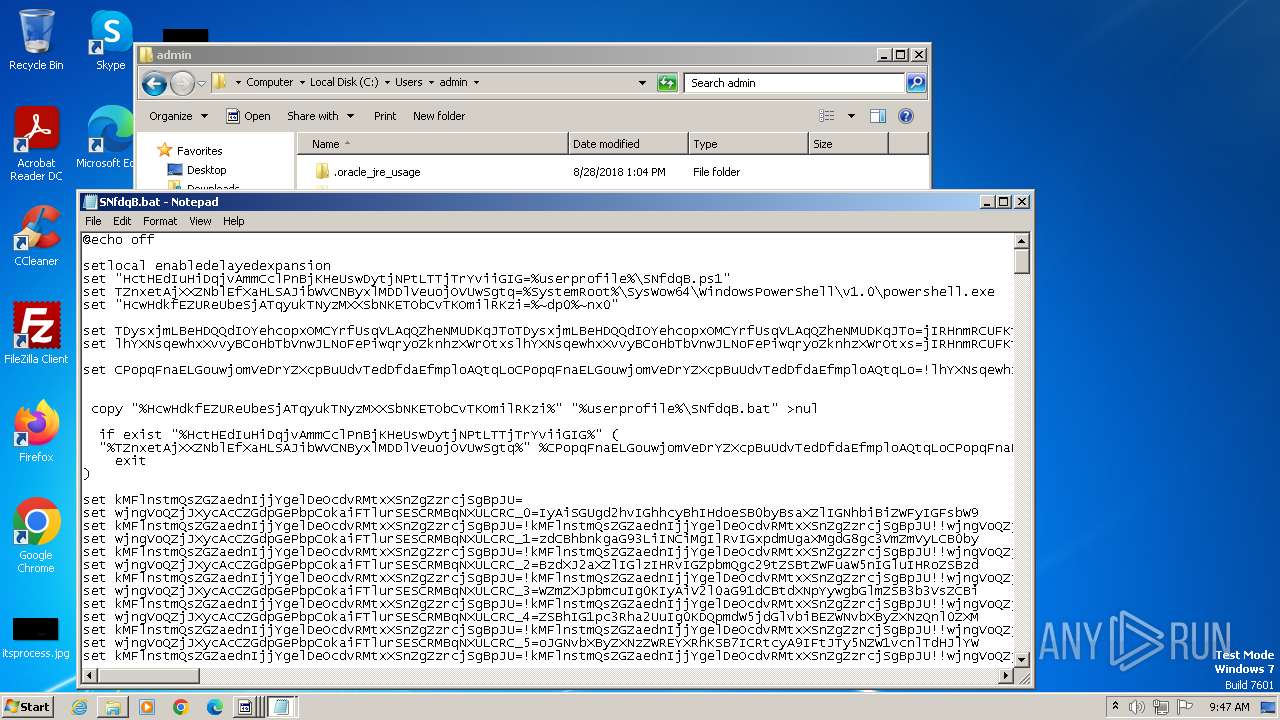
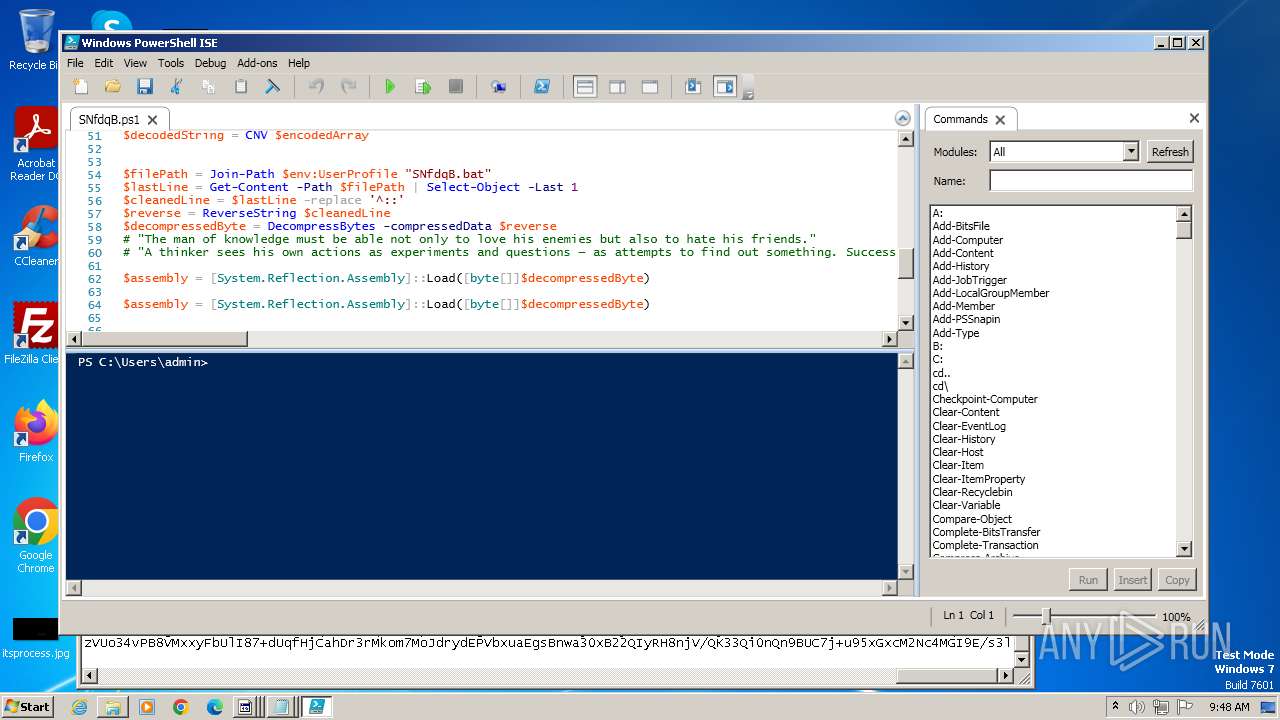
Executing commands from a ".bat" file
- wscript.exe (PID: 4000)
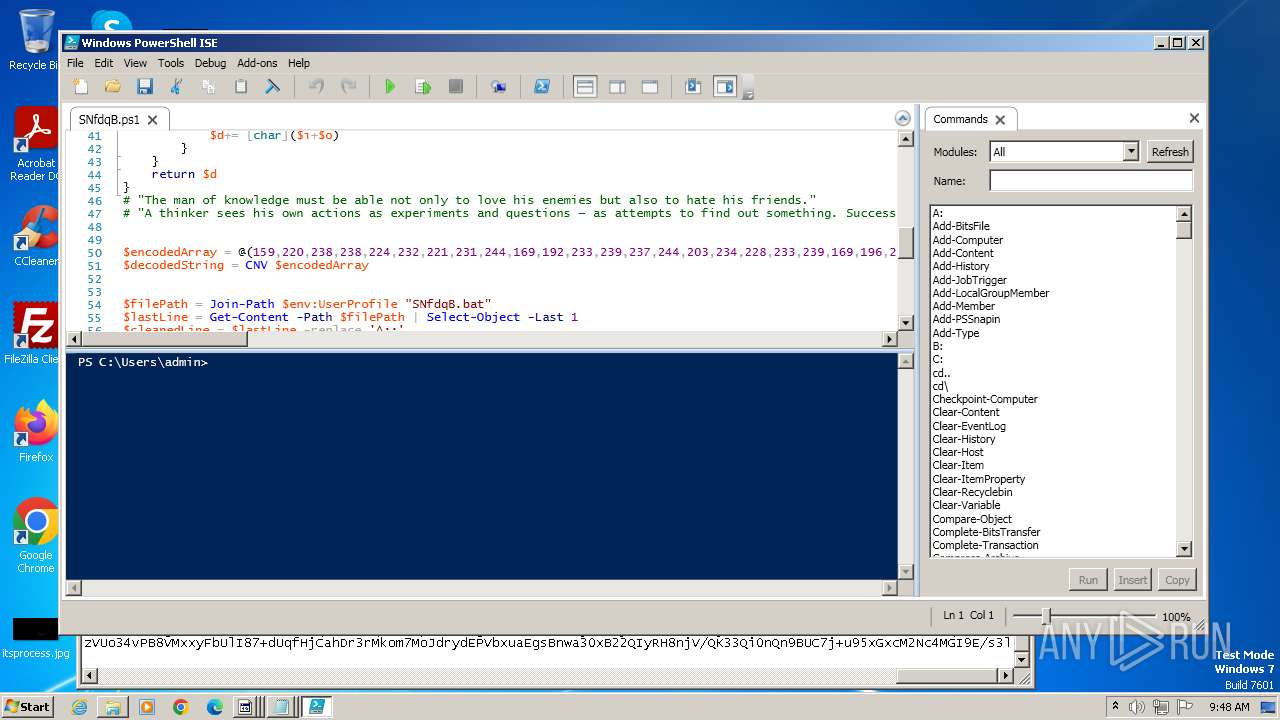
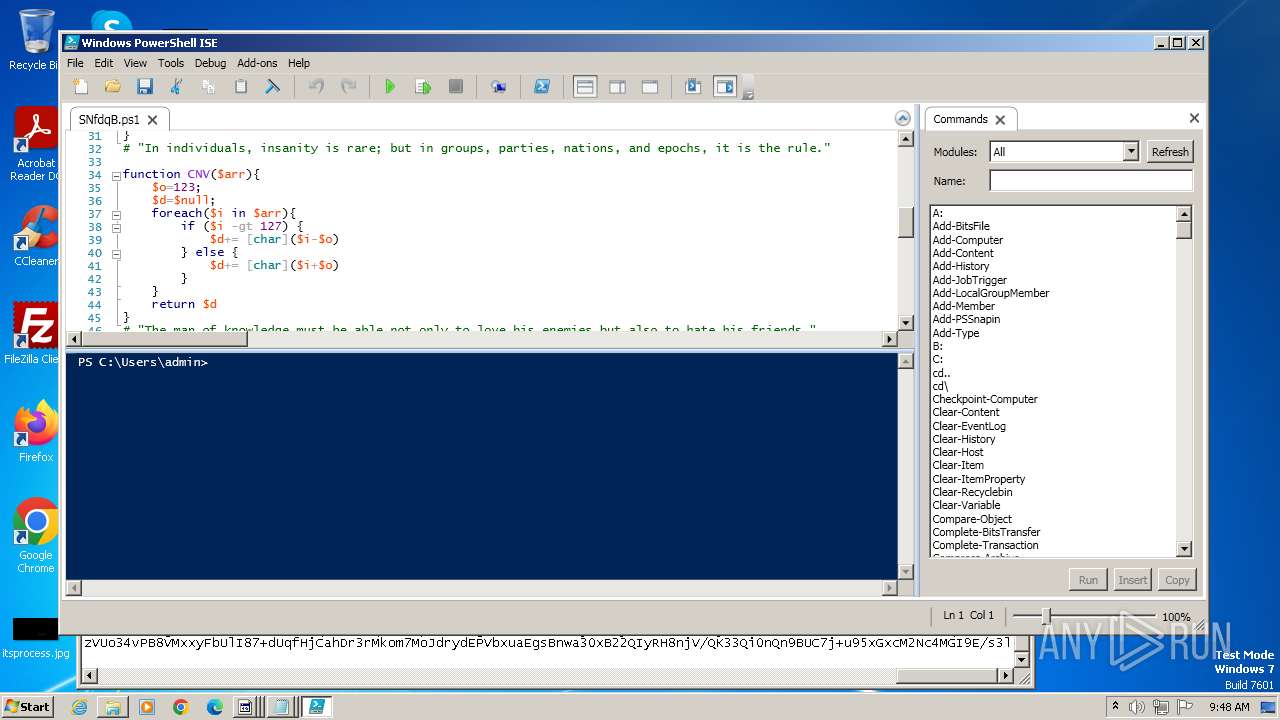
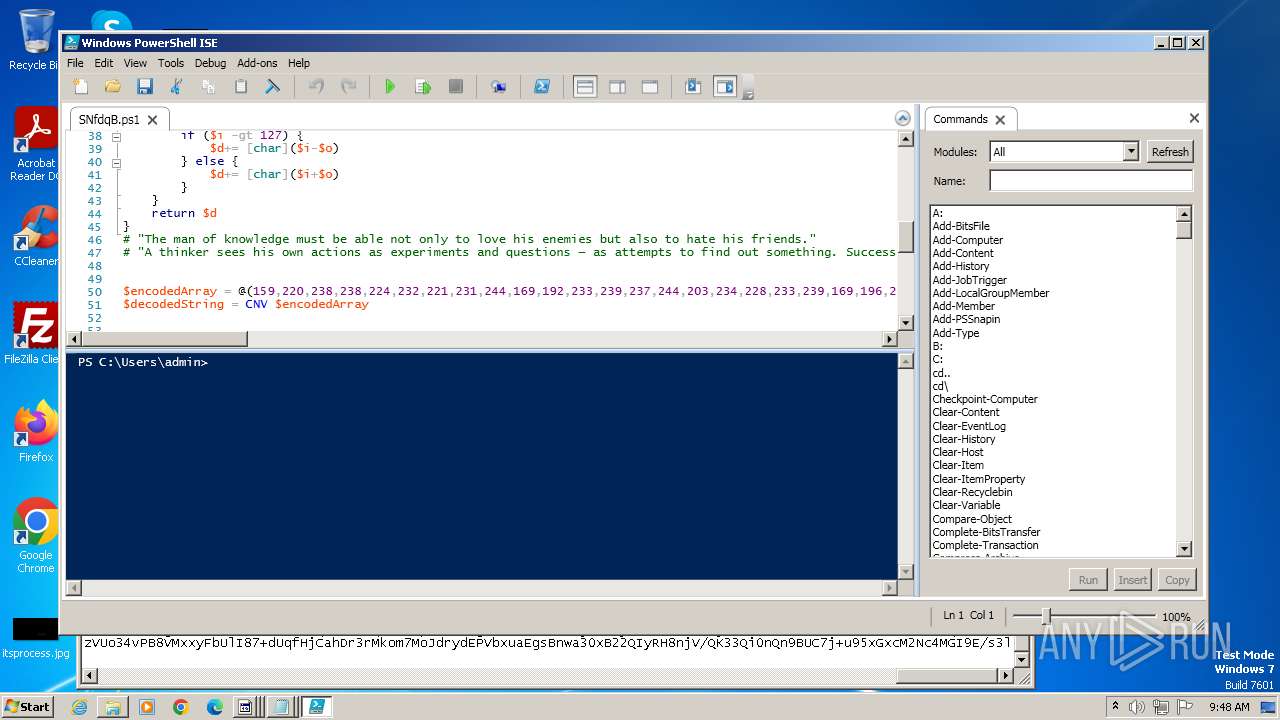
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 1064)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4072)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 1064)
Connects to unusual port
- RegAsm.exe (PID: 1932)
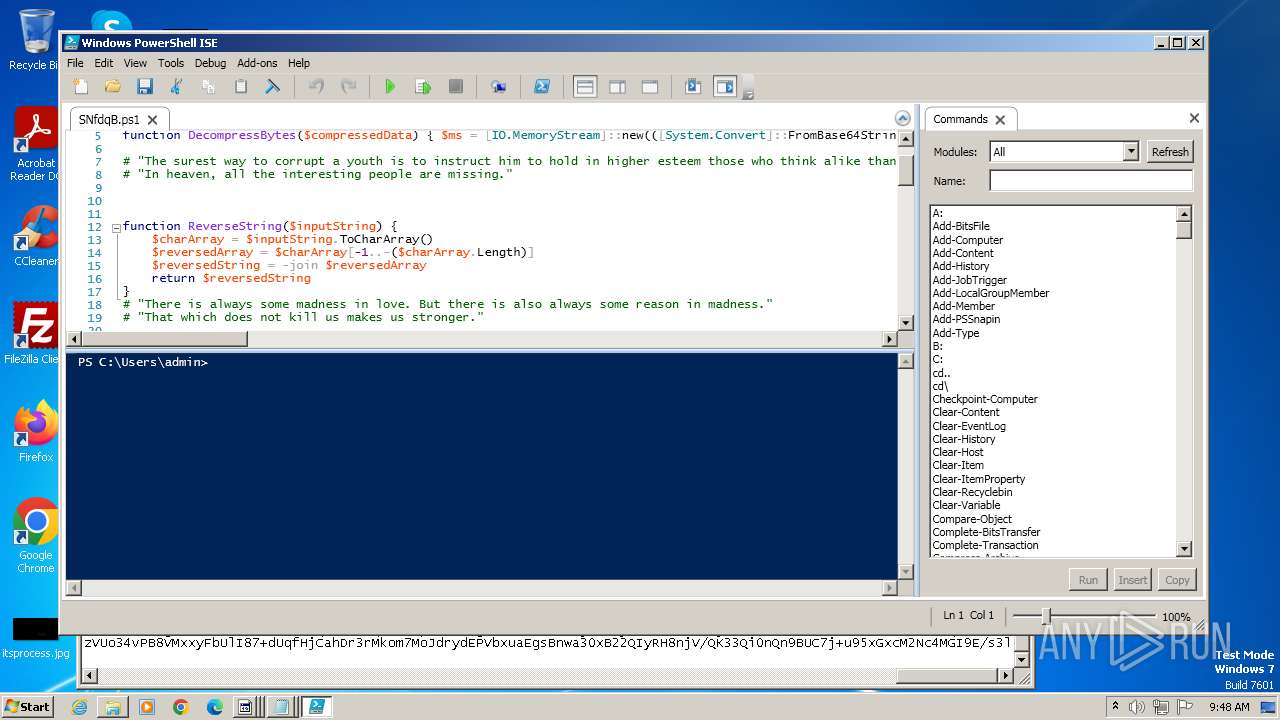
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 1064)
Reads settings of System Certificates
- powershell_ise.exe (PID: 1380)
INFO
Reads the computer name
- 87c06023a062f0ae515fb03014748a0b51d5e8011f573073224728c6c942b89e.exe (PID: 3976)
- RegAsm.exe (PID: 1932)
- wmpnscfg.exe (PID: 2336)
Checks supported languages
- 87c06023a062f0ae515fb03014748a0b51d5e8011f573073224728c6c942b89e.exe (PID: 3976)
- RegAsm.exe (PID: 1932)
- wmpnscfg.exe (PID: 2336)
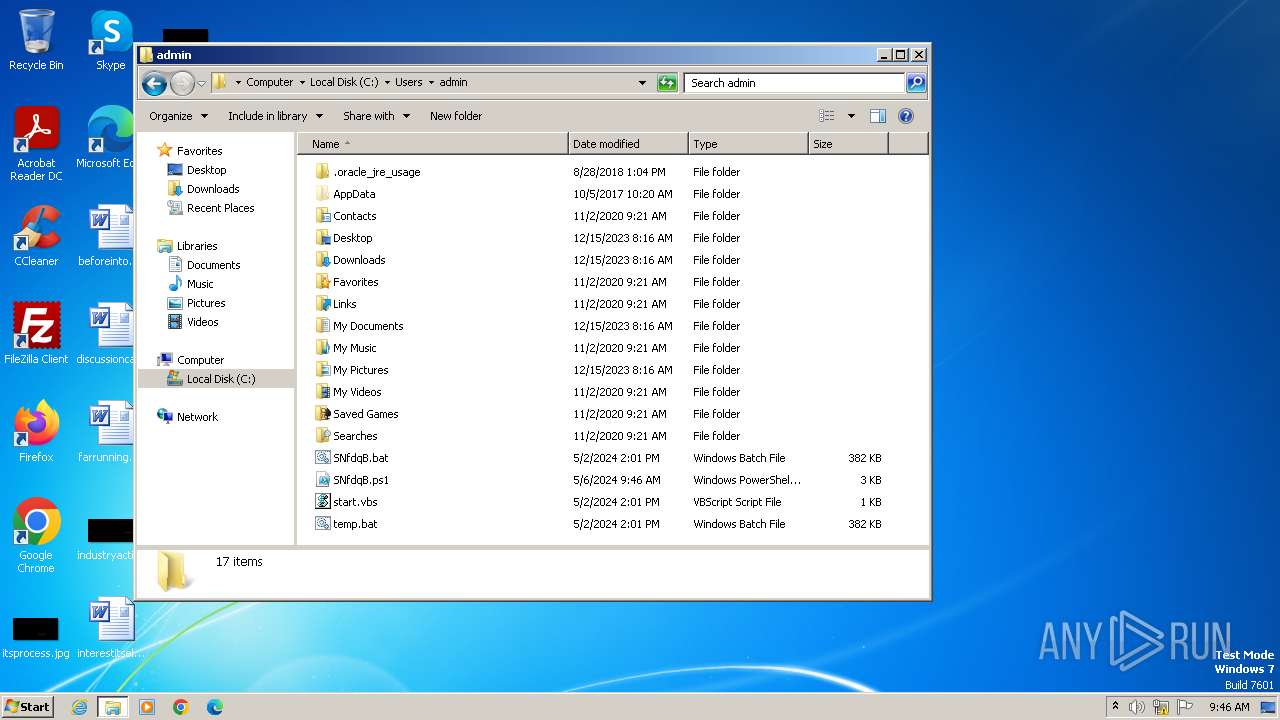
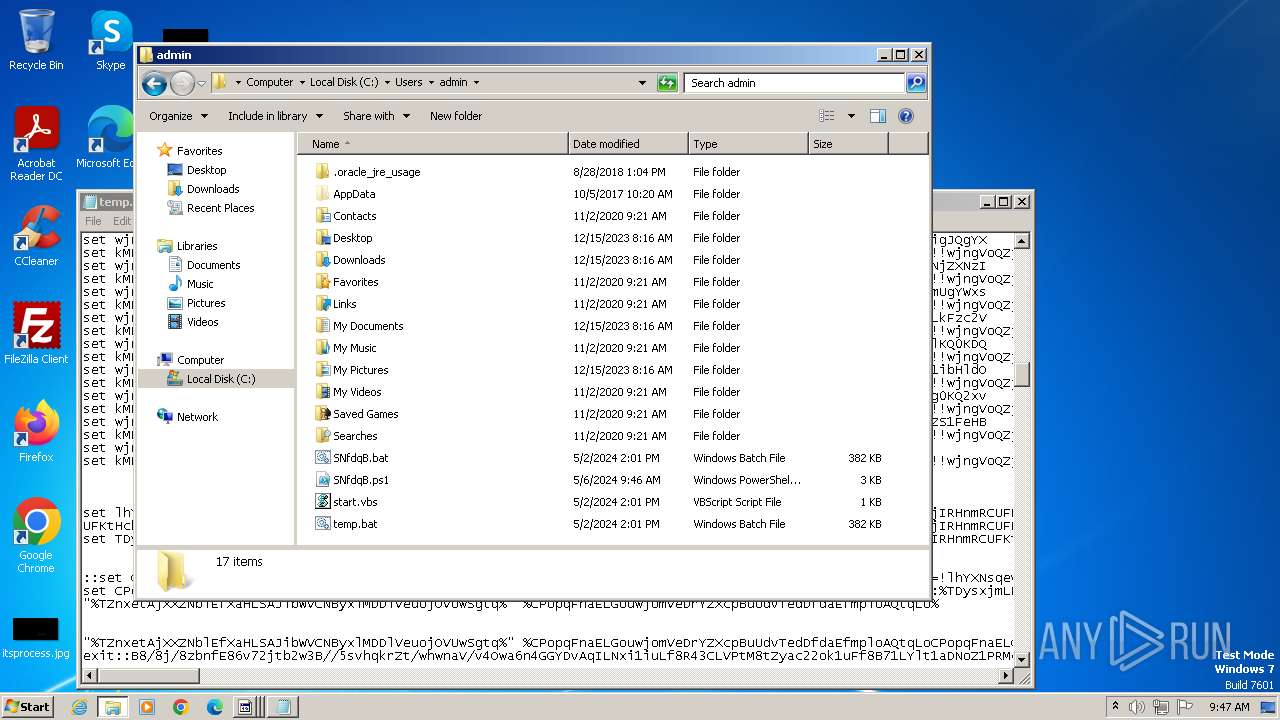
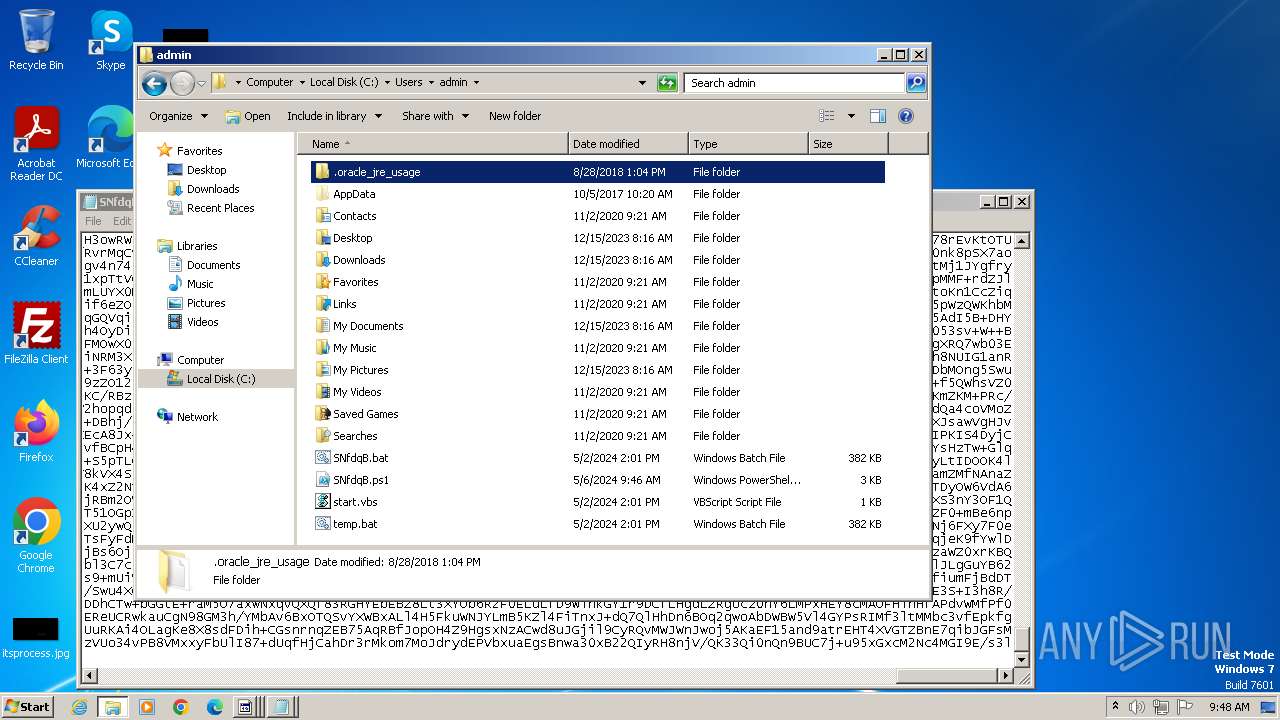
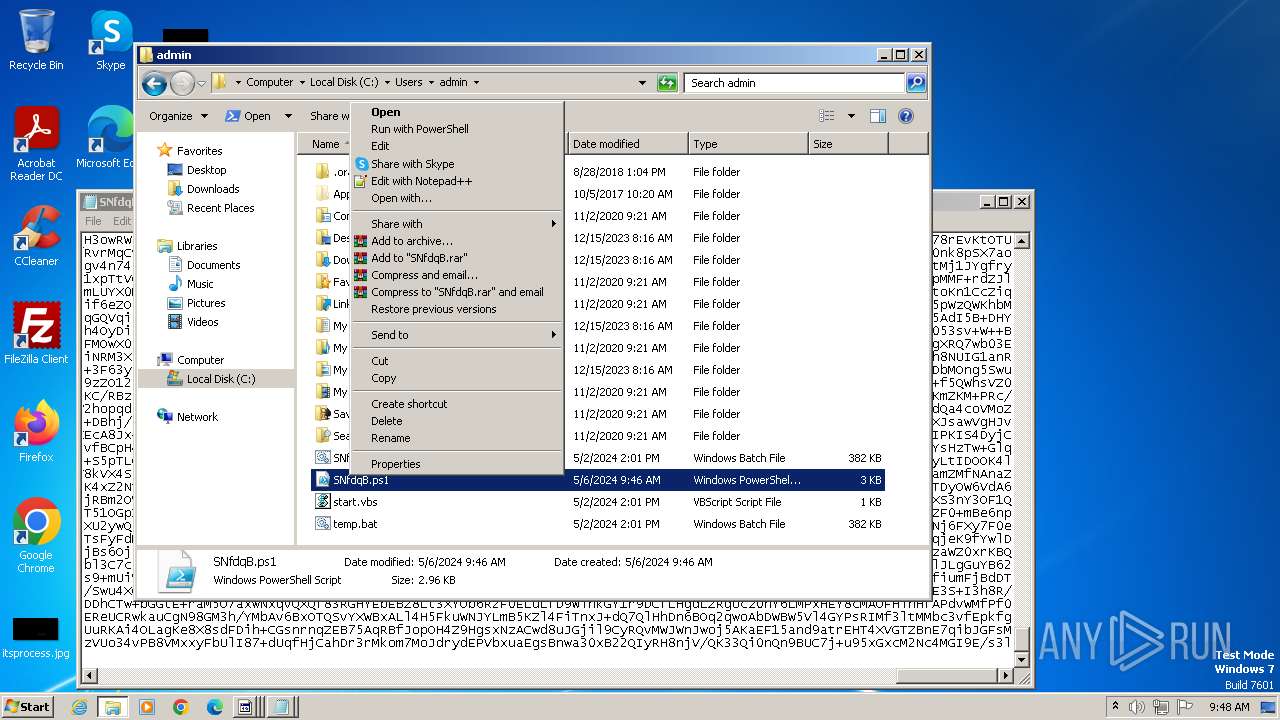
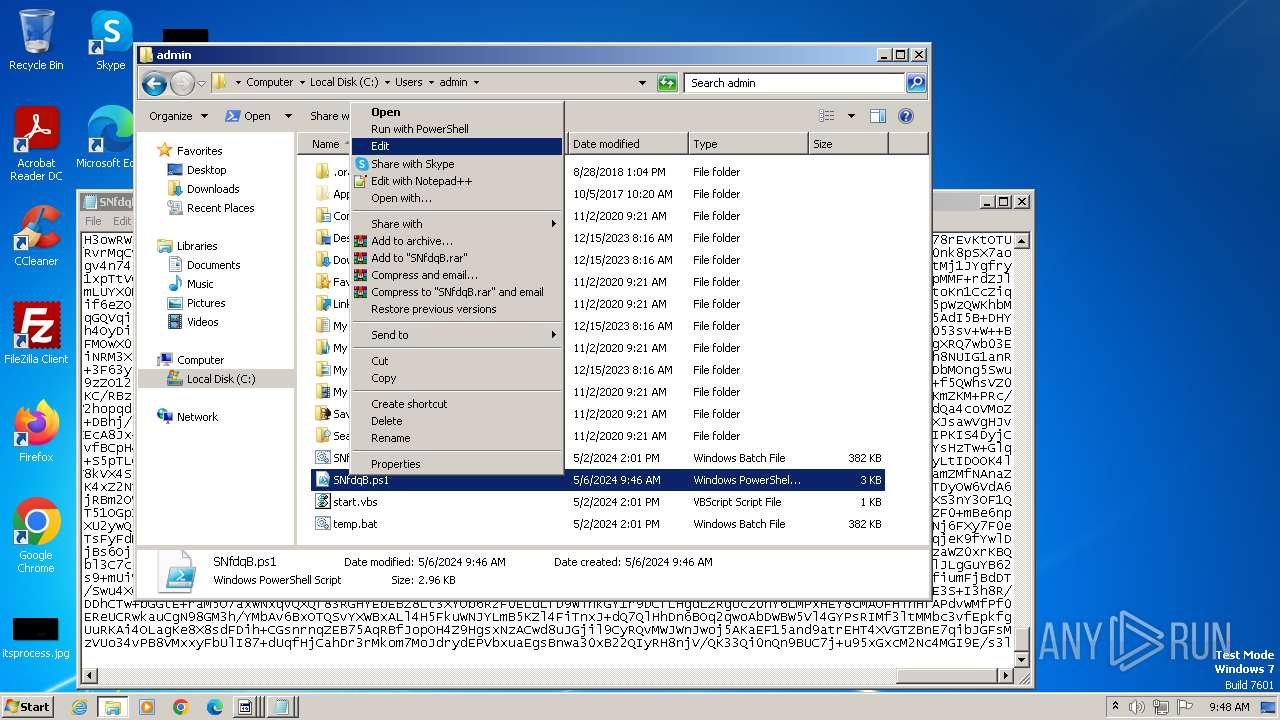
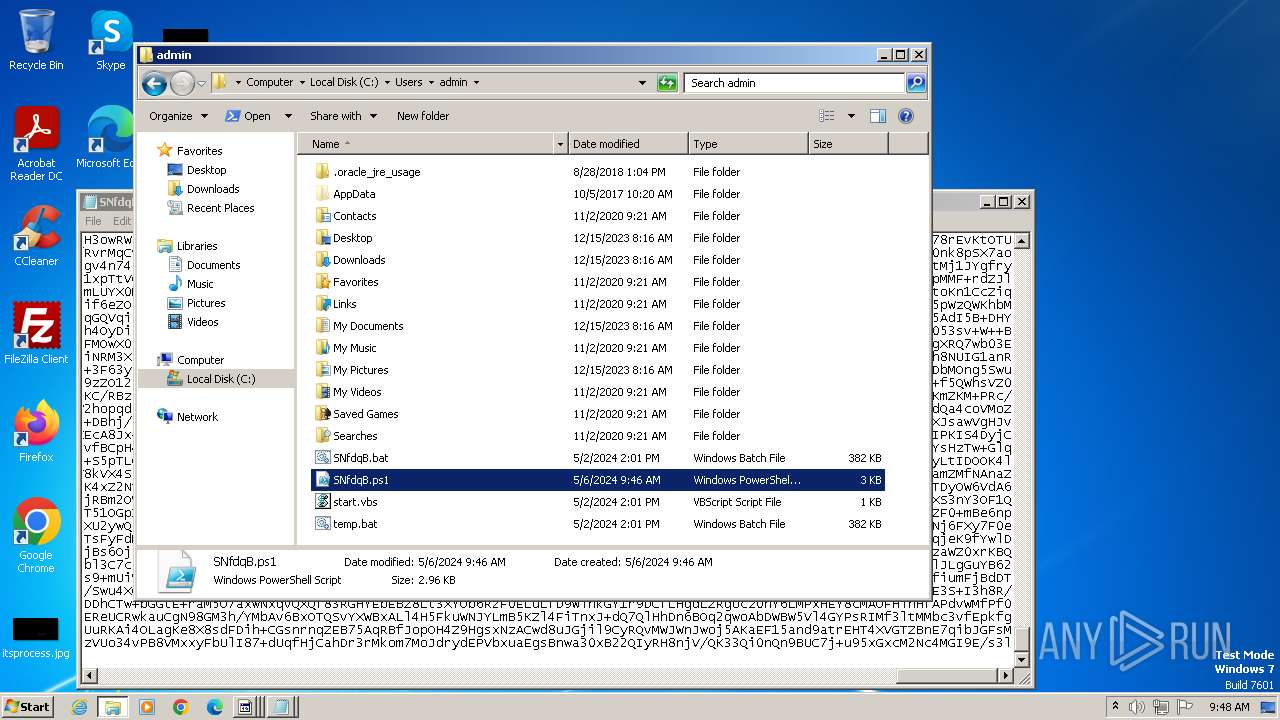
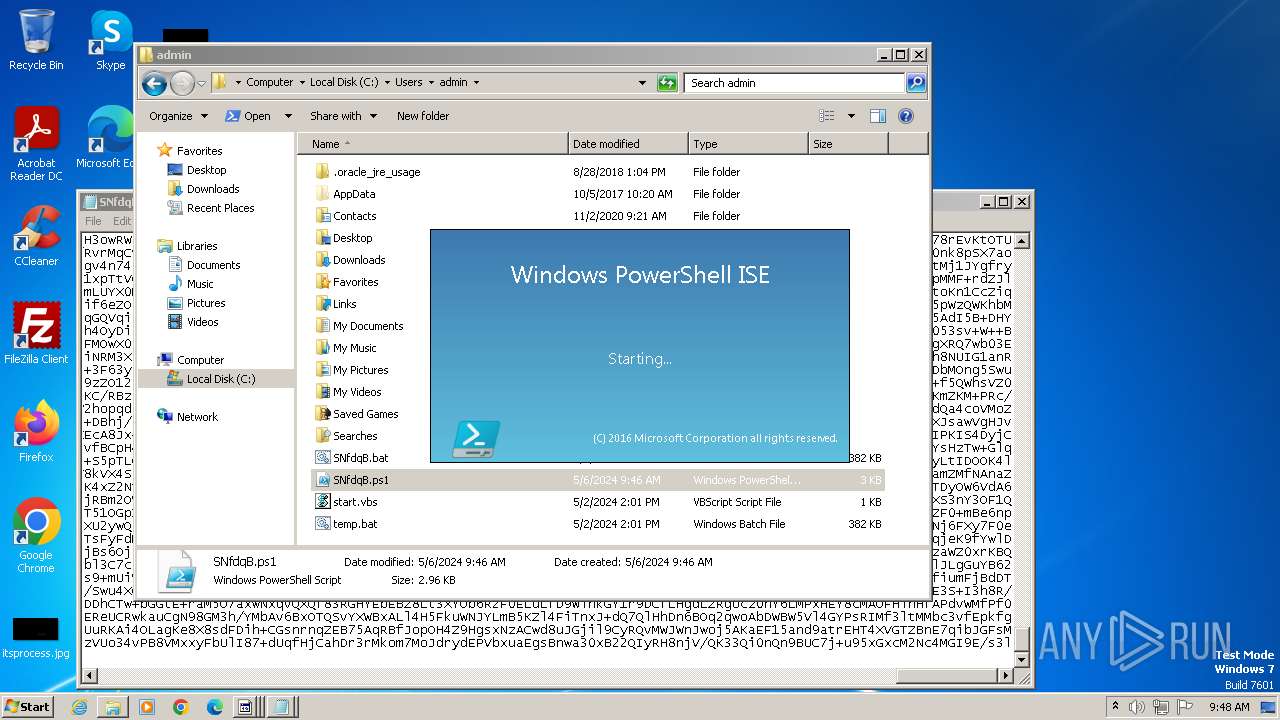
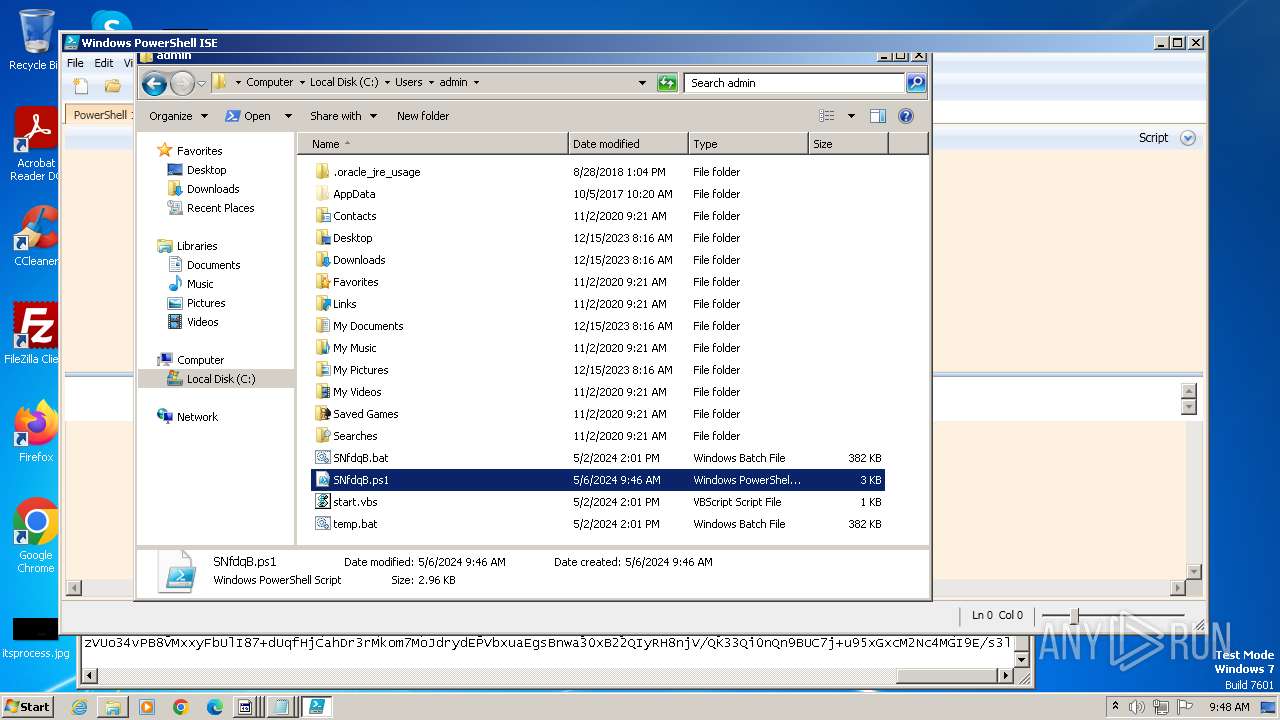
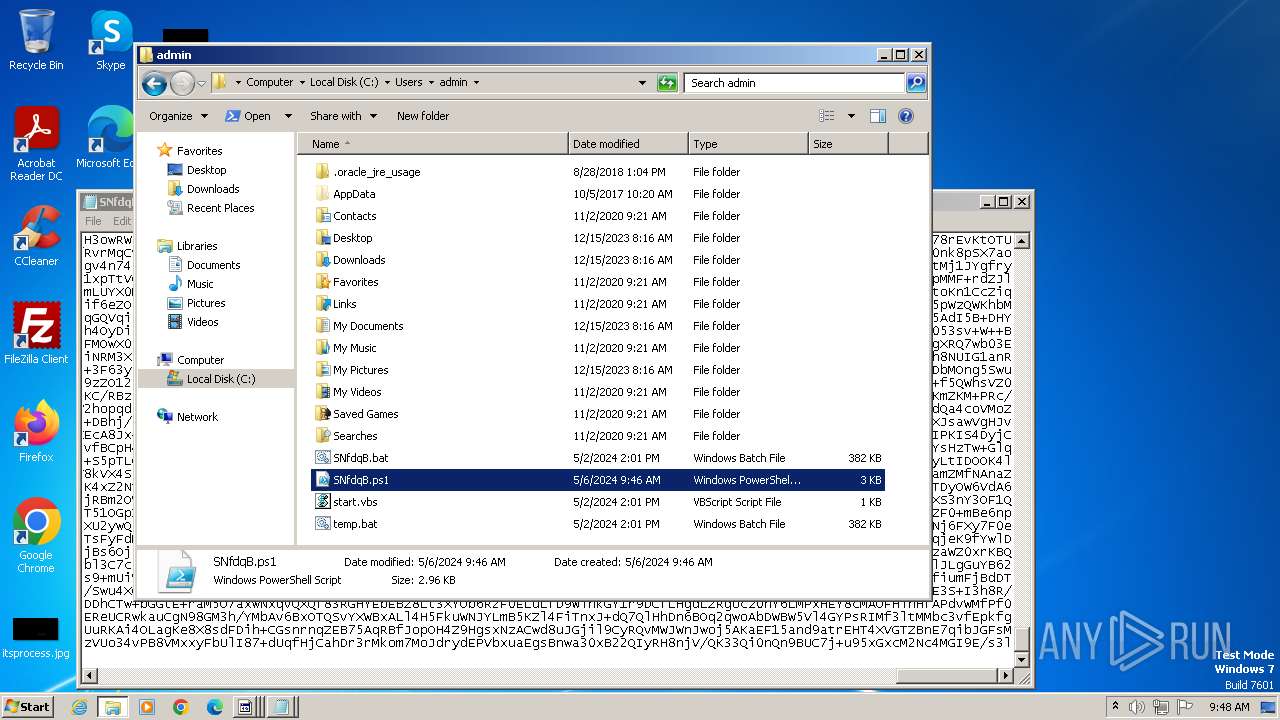
Manual execution by a user
- explorer.exe (PID: 2040)
- notepad.exe (PID: 1940)
- wmpnscfg.exe (PID: 2336)
- notepad.exe (PID: 1244)
- powershell_ise.exe (PID: 1380)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1064)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 1932)
Create files in a temporary directory
- powershell_ise.exe (PID: 1380)
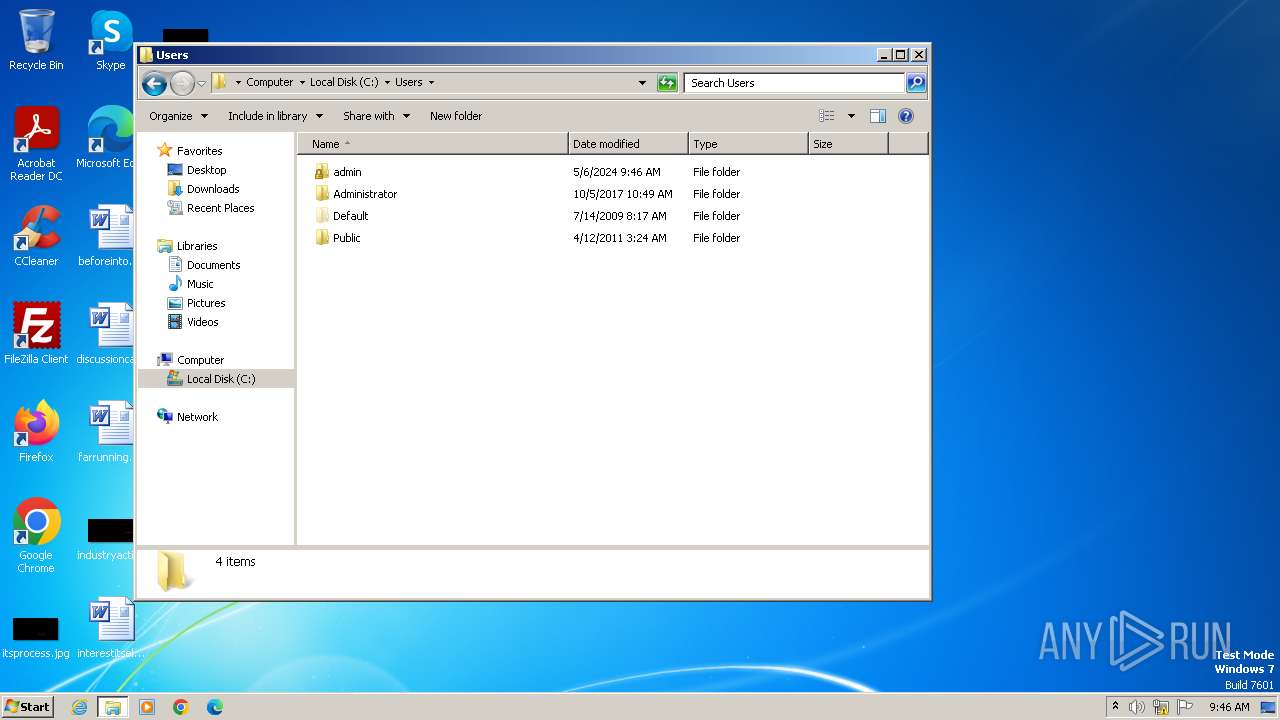
Creates files or folders in the user directory
- powershell_ise.exe (PID: 1380)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 1380)
Reads the software policy settings
- powershell_ise.exe (PID: 1380)
Checks current location (POWERSHELL)
- powershell_ise.exe (PID: 1380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:02 02:09:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 184832 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3532 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.353.12 |
| ProductVersionNumber: | 4.0.353.12 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Manages xml links efficiently |
| CompanyName: | xmlLink |
| FileDescription: | xmlLink |
| FileVersion: | 2.3.0.0 |
| InternalName: | xmlLink.exe |
| LegalCopyright: | (c) 2024 xmlLink. All rights reserved. |
| OriginalFileName: | xmlLink.exe |
| ProductName: | xmlLink |
| ProductVersion: | 2.3.0.0 |
| SpecialBuild: | Pro Edition |
Total processes
49
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | "C:\Windows\SysWow64\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -File "C:\Users\admin\SNfdqB.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
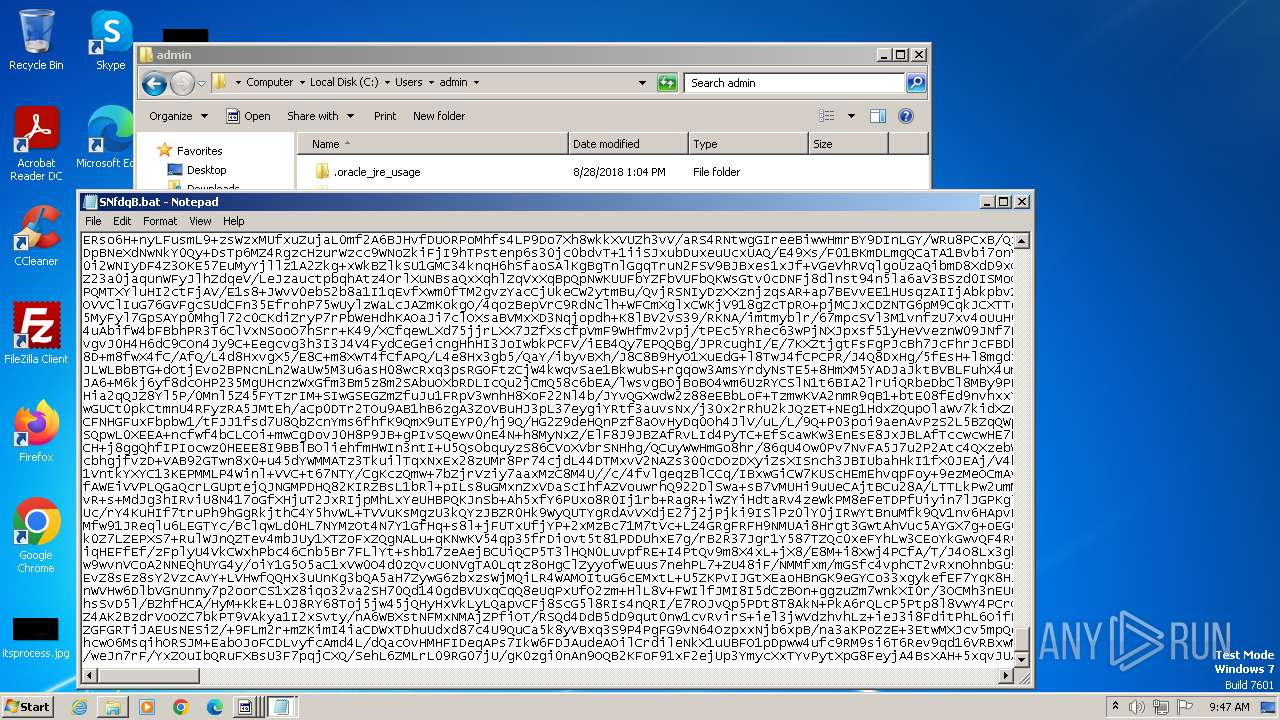
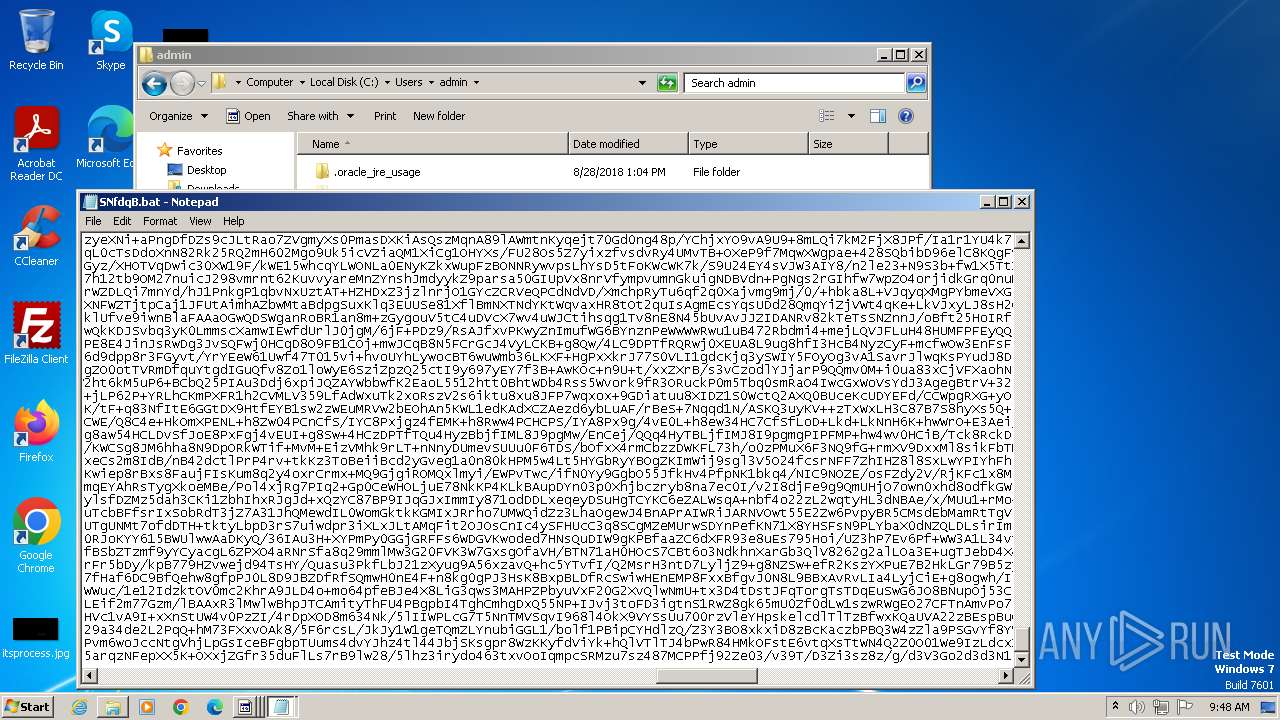
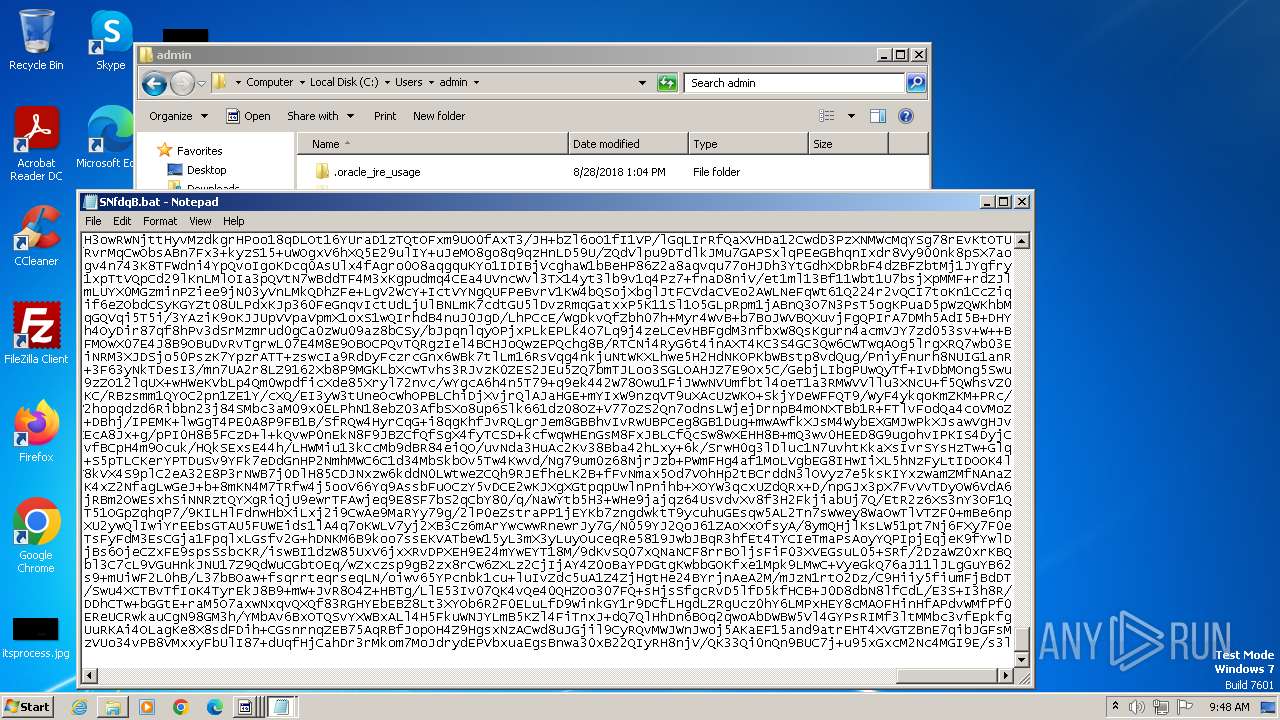
| 1244 | "C:\Windows\System32\NOTEPAD.EXE" C:\Users\admin\SNfdqB.bat | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" "C:\Users\admin\SNfdqB.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1932 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1940 | "C:\Windows\System32\NOTEPAD.EXE" C:\Users\admin\temp.bat | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2040 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\AppData\Local\Temp\87c06023a062f0ae515fb03014748a0b51d5e8011f573073224728c6c942b89e.exe" | C:\Users\admin\AppData\Local\Temp\87c06023a062f0ae515fb03014748a0b51d5e8011f573073224728c6c942b89e.exe | — | explorer.exe | |||||||||||
User: admin Company: xmlLink Integrity Level: MEDIUM Description: xmlLink Exit code: 0 Version: 2.3.0.0 Modules
| |||||||||||||||
| 4000 | "wscript.exe" "C:\Users\admin\start.vbs" | C:\Windows\System32\wscript.exe | — | 87c06023a062f0ae515fb03014748a0b51d5e8011f573073224728c6c942b89e.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 4040 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\temp.bat" " | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
17 443
Read events
17 412
Write events
31
Delete events
0
Modification events
| (PID) Process: | (4000) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4000) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4000) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4000) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1380) powershell_ise.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1380) powershell_ise.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1380) powershell_ise.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1380) powershell_ise.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1380) powershell_ise.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: powershell_ise.exe | |||
| (PID) Process: | (1380) powershell_ise.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
9
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4072 | powershell.exe | C:\Users\admin\AppData\Local\Temp\q0ekoin4.rvr.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4072 | powershell.exe | C:\Users\admin\AppData\Local\Temp\fdte5muf.vbh.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
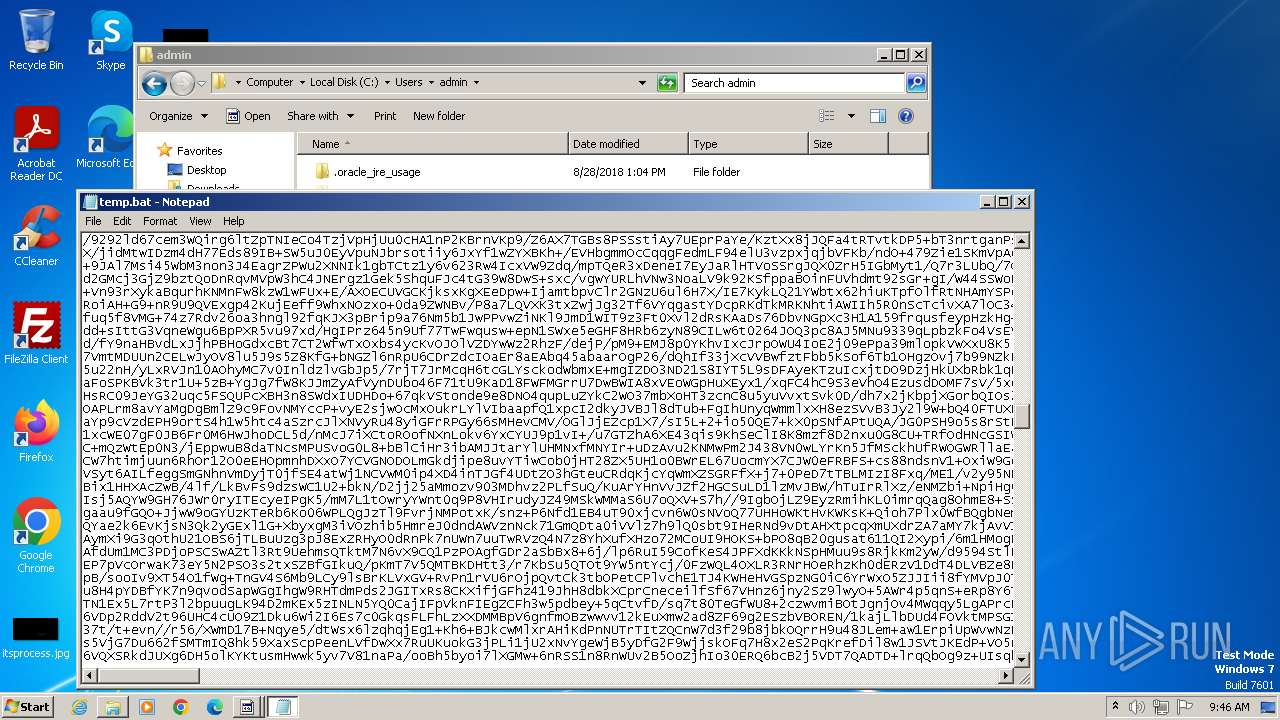
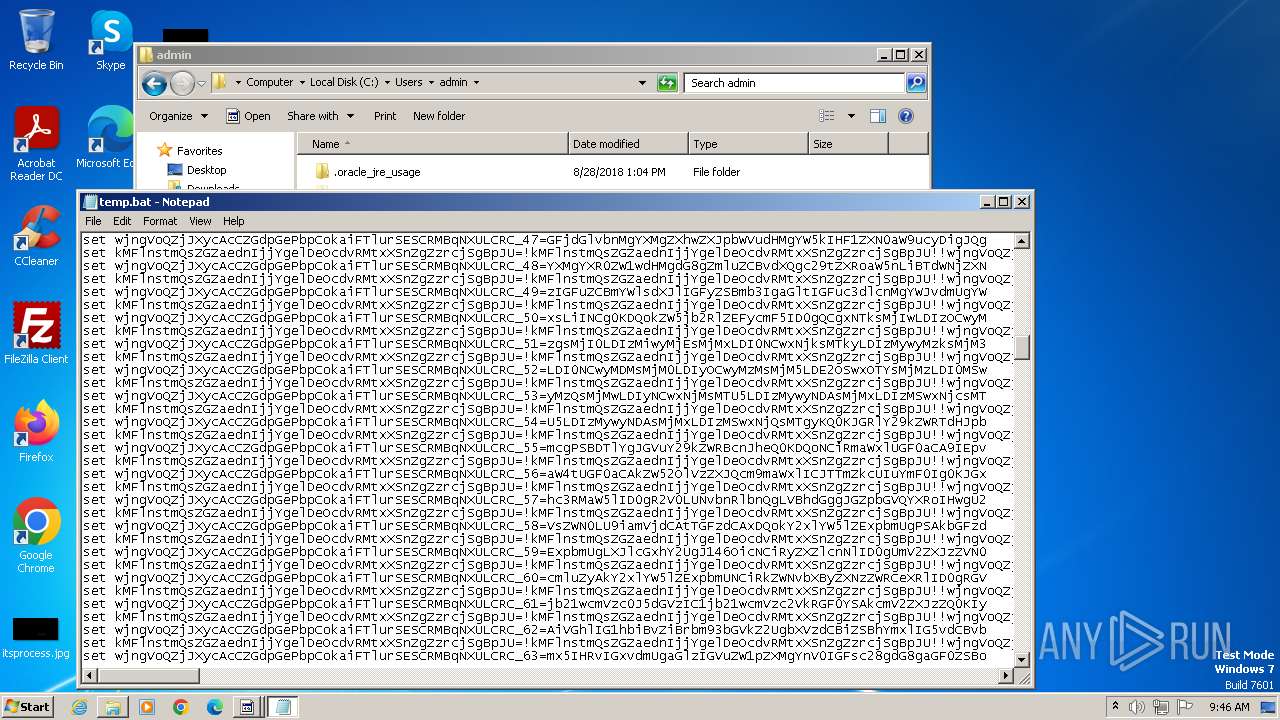
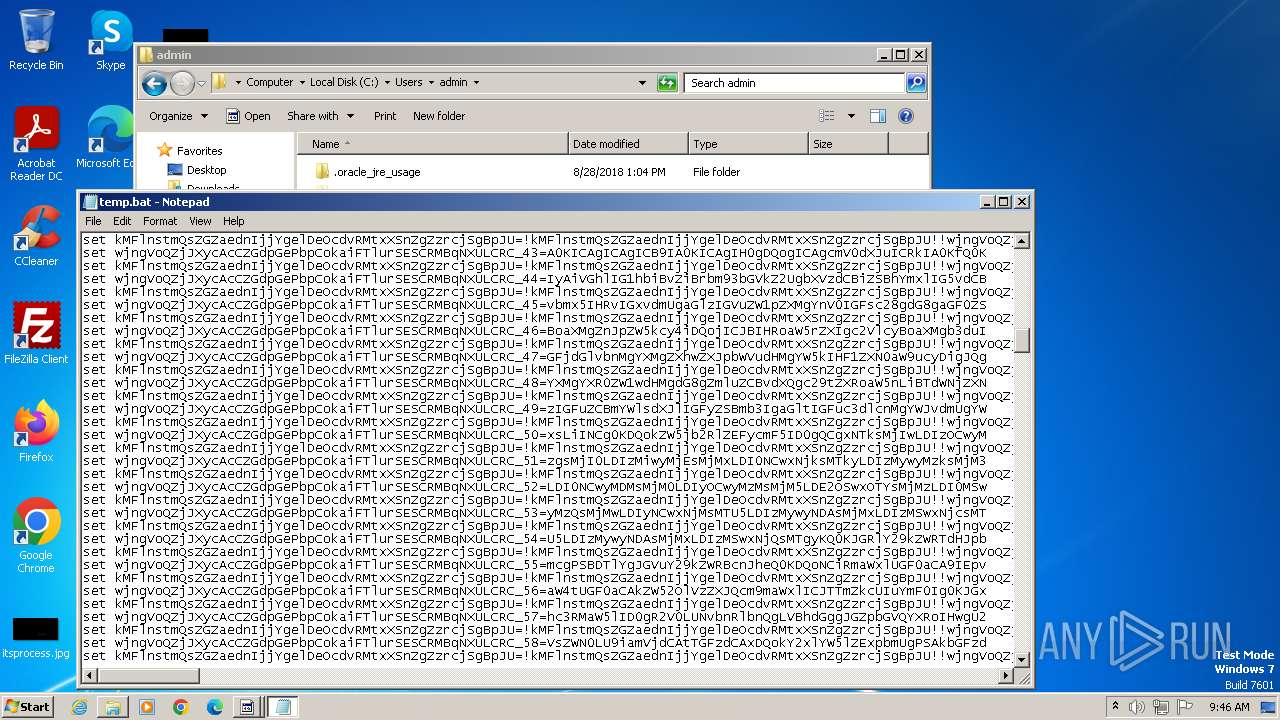
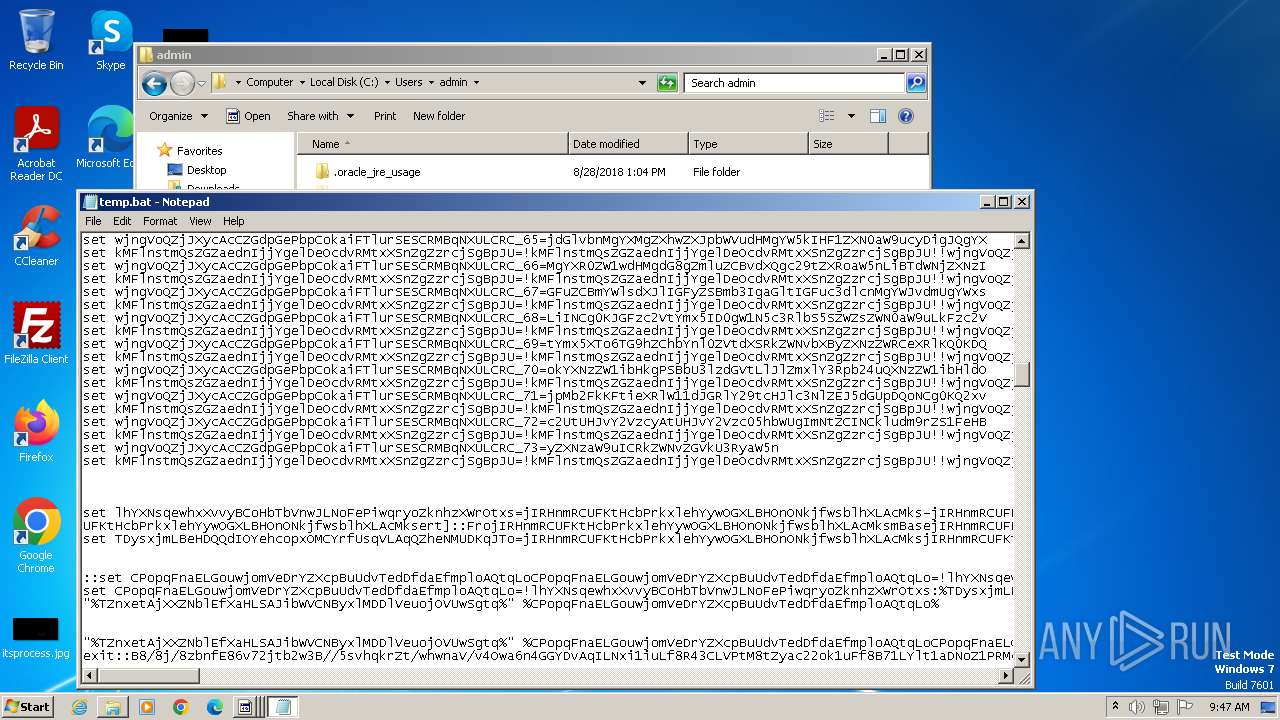
| 3976 | 87c06023a062f0ae515fb03014748a0b51d5e8011f573073224728c6c942b89e.exe | C:\Users\admin\temp.bat | text | |
MD5:487351746395290271A9EF2025DD712E | SHA256:0012252B4890DF66253E626518E2EFE59900652E7DAE02CB30BB7F4293D2E40E | |||
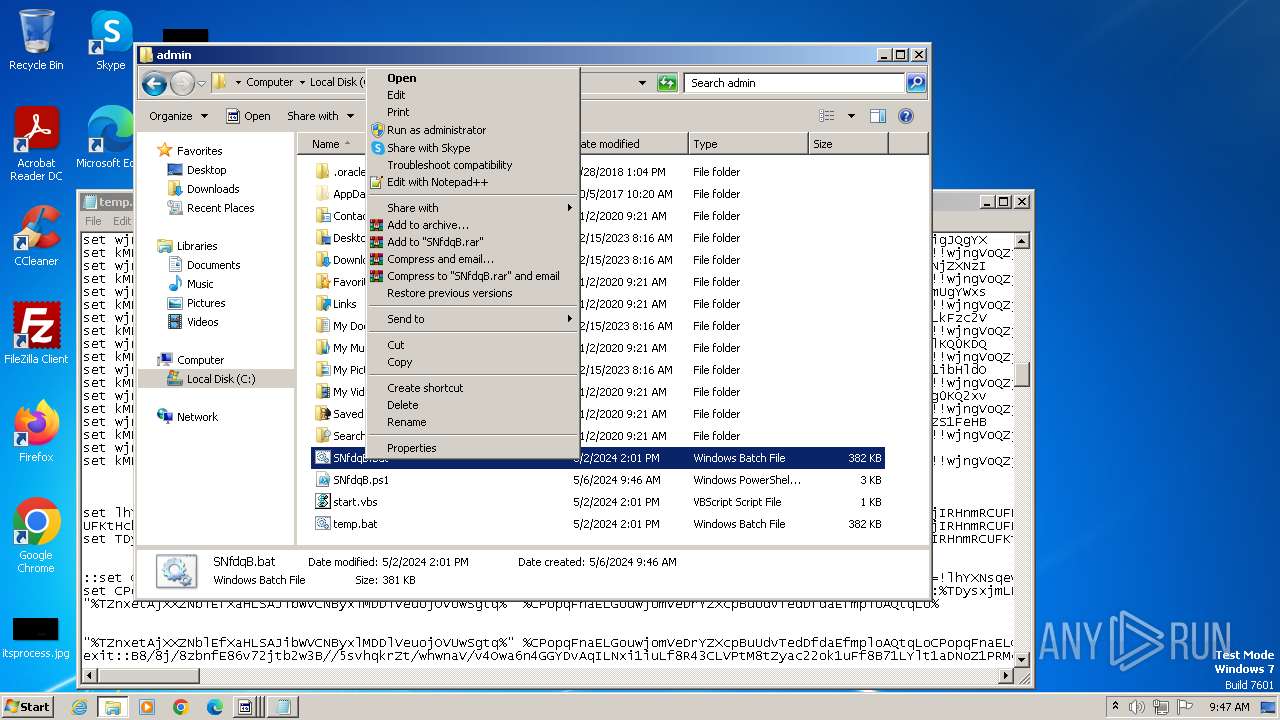
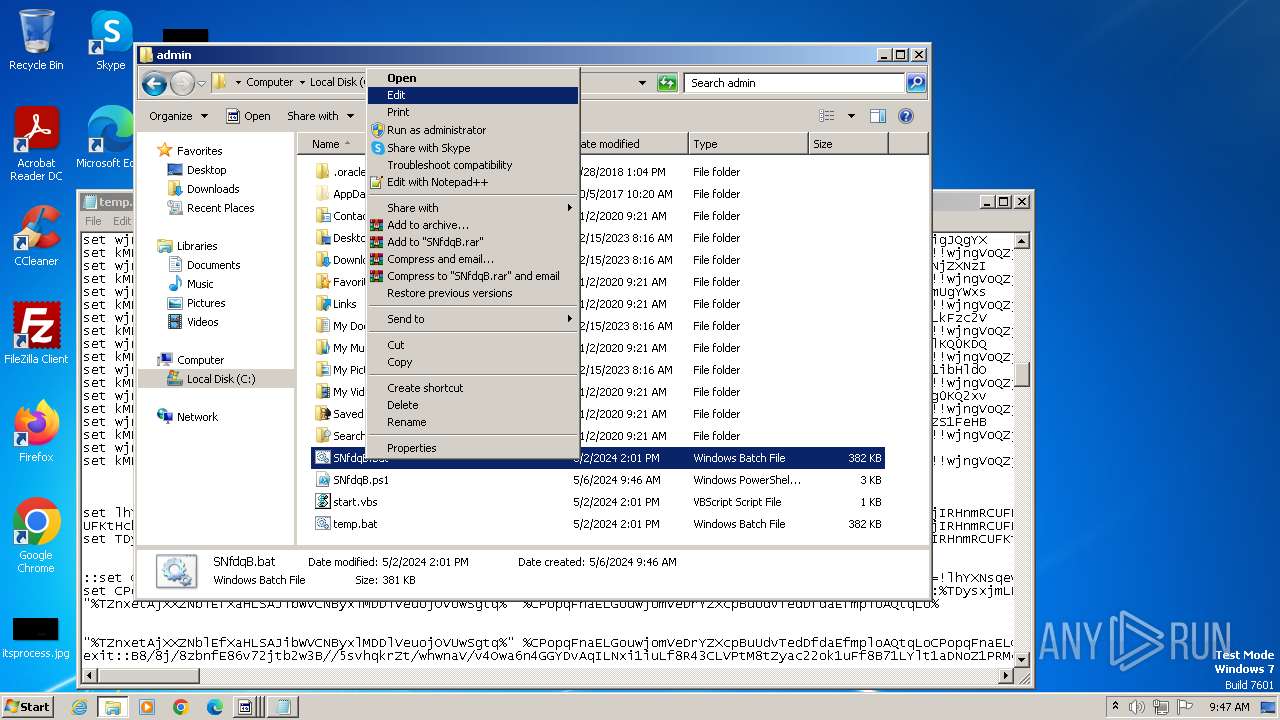
| 4040 | cmd.exe | C:\Users\admin\SNfdqB.bat | text | |
MD5:487351746395290271A9EF2025DD712E | SHA256:0012252B4890DF66253E626518E2EFE59900652E7DAE02CB30BB7F4293D2E40E | |||
| 4072 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\rkzv3j4n.q4z.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\13fd3vaz.3sz.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4072 | powershell.exe | C:\Users\admin\SNfdqB.ps1 | text | |
MD5:EACBACC4A220D5CED053DCA200D2A2B0 | SHA256:2245B8B1431F4DAD8CFCC2E59C80F7921107CA96A28142E86418A1D532B9E5BB | |||
| 1380 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ISE\S-1-5-5-0-69873\PowerShellISEPipeName_0_67f94b49-b18d-4609-b028-f1bab5c4c55e | text | |
MD5:A5EA0AD9260B1550A14CC58D2C39B03D | SHA256:F1B2F662800122BED0FF255693DF89C4487FBDCF453D3524A42D4EC20C3D9C04 | |||
| 1380 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\qveeyejm.5ai.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1932 | RegAsm.exe | 135.181.119.247:26827 | — | Hetzner Online GmbH | FI | unknown |